4fa2a04209e785dff3dc6a4aa9d55992.ppt
- Количество слайдов: 89

Zombie-nets, Pop-ups, and Spam By Bill and Lorette Cheswick ches@cheswick. com lepac@cheswick. com http: //www. cheswick. com
Definition: internet • A collection of interacting networks that support TCP/IP 01/19/05 Zombie-nets, Pop-ups, and Spam 2 of 45

01/19/05 Zombie-nets, Pop-ups, and Spam 3 of 45


TCP/IP • A set of protocols for connecting computers via a network – Almost nobody needs to know the details • Designed in the early 1980 s • One design goal: end-to-end connectivity – We have learned better: firewalls break this idea 01/19/05 Zombie-nets, Pop-ups, and Spam 5 of 45
Internet design: Smarts at the edge of the network • Unlike the phone system, the “center” of the network is pretty stupid • New services are designed and implemented at the edge of the network • No permission or special arrangements are needed 01/19/05 Zombie-nets, Pop-ups, and Spam 6 of 45

209. 123. 16. 98 64. 10. 0. 3

Clients and servers • Clients initiate connections to servers • Servers tend to be publicly-known and accessible – Web services like www. amazon. com • There is seldom any good reason for a home or corporate computer to offer network services – But they do anyway. A lot of them 01/19/05 Zombie-nets, Pop-ups, and Spam 8 of 45

209. 123. 16. 104 (client) 164. 109. 96. 222 (server) (www. budweiser. com)
TCP connections include a port number • TCP ports are numbers between 0 and 65535, inclusive • The client and server need only agree on which number to use • There is a long list of standard services and their TCP port numbers – World wide web (HTTP) port 80 – Email (SMTP) port 25 – thousands more

Server ports • Each TCP service available on a computer is serviced by a program • If that program has a serious bug, someone far away may be able to compromise that computer, and inject their own software to “own” your computer • If you are running Windows, this has probably already happened to you
How can we see these TCP services on a Windows computer? • Start -> All Programs -> Accessories -> Command Prompt • Run: netstat –a
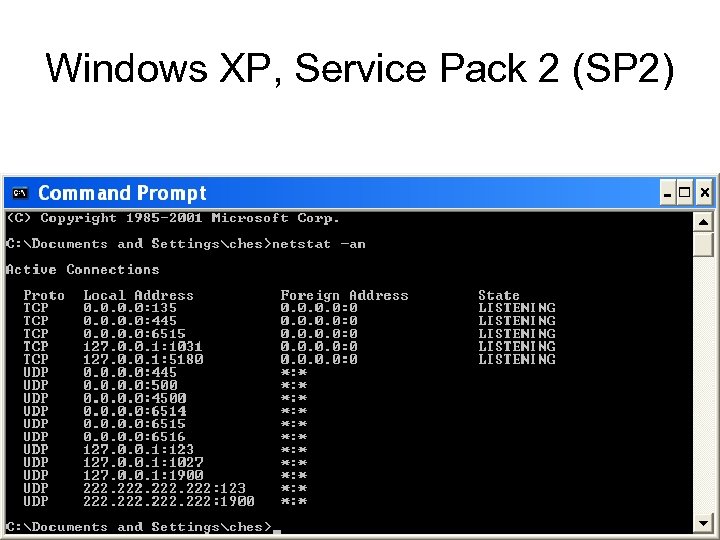
Windows XP, Service Pack 2 (SP 2)
A Few Sample port listener profiles
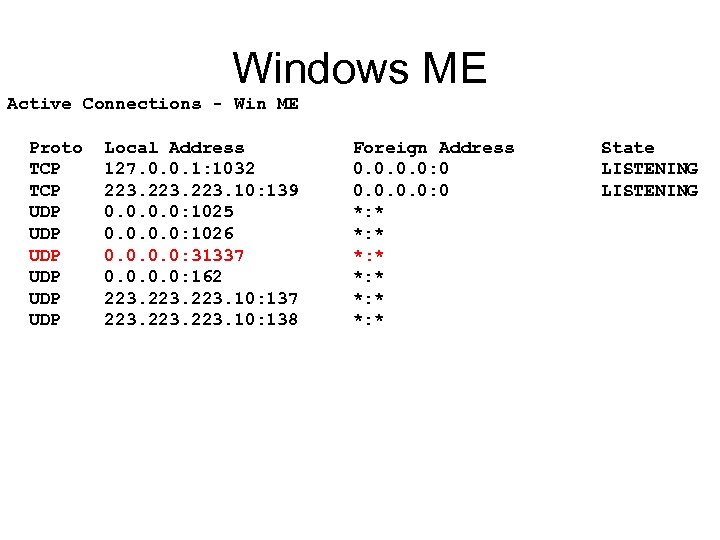
Windows ME Active Connections - Win ME Proto TCP UDP UDP UDP Local Address 127. 0. 0. 1: 1032 223. 10: 139 0. 0: 1025 0. 0: 1026 0. 0: 31337 0. 0: 162 223. 10: 137 223. 10: 138 Foreign Address 0. 0: 0 *: * *: * State LISTENING

Windows 2000 Proto TCP TCP TCP UDP UDP Local Address 0. 0: 135 0. 0: 445 0. 0: 1029 0. 0: 1036 0. 0: 1078 0. 0: 1080 0. 0: 1086 0. 0: 6515 127. 0. 0. 1: 139 0. 0: 445 0. 0: 1038 0. 0: 6514 0. 0: 6515 127. 0. 0. 1: 1108 223. 96: 500 223. 96: 4500 Foreign Address 0. 0: 0 0. 0: 0 *: * *: * State LISTENING LISTENING LISTENING

Windows XP, this laptop Proto TCP TCP TCP TCP UDP UDP UDP UDP Local Address ches-pc: epmap ches-pc: microsoft-ds ches-pc: 1025 ches-pc: 1036 ches-pc: 3115 ches-pc: 3118 ches-pc: 3470 ches-pc: 3477 ches-pc: 5000 ches-pc: 6515 ches-pc: netbios-ssn ches-pc: 3001 ches-pc: 3002 ches-pc: 3003 ches-pc: 5180 ches-pc: microsoft-ds ches-pc: isakmp ches-pc: 1027 ches-pc: 3008 ches-pc: 3473 ches-pc: 6514 ches-pc: 6515 ches-pc: netbios-ns ches-pc: netbios-dgm ches-pc: 1900 ches-pc: ntp ches-pc: 1900 ches-pc: 3471 Foreign Address ches-pc: 0 ches-pc: 0 ches-pc: 0 ches-pc: 0 *: * *: * *: * *: * State LISTENING LISTENING LISTENING LISTENING
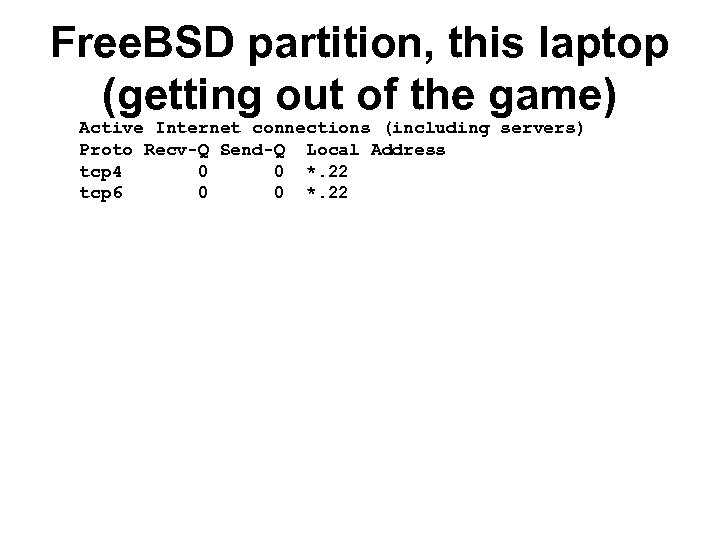
Free. BSD partition, this laptop (getting out of the game) Active Internet connections (including servers) Proto Recv-Q Send-Q Local Address tcp 4 0 0 *. 22 tcp 6 0 0 *. 22
It is easy to dump on Microsoft, but many others have made the same mistakes before
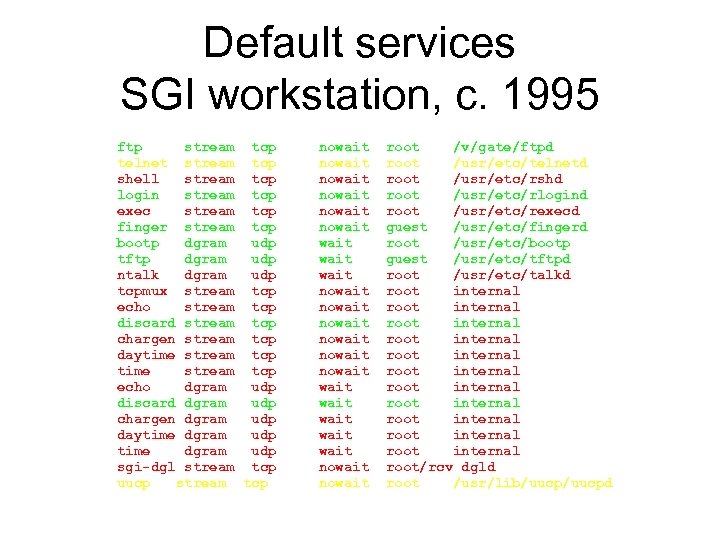
Default services SGI workstation, c. 1995 ftp stream tcp telnet stream tcp shell stream tcp login stream tcp exec stream tcp finger stream tcp bootp dgram udp tftp dgram udp ntalk dgram udp tcpmux stream tcp echo stream tcp discard stream tcp chargen stream tcp daytime stream tcp echo dgram udp discard dgram udp chargen dgram udp daytime dgram udp sgi-dgl stream tcp uucp stream tcp nowait nowait nowait wait wait nowait root /v/gate/ftpd root /usr/etc/telnetd root /usr/etc/rshd root /usr/etc/rlogind root /usr/etc/rexecd guest /usr/etc/fingerd root /usr/etc/bootp guest /usr/etc/tftpd root /usr/etc/talkd root internal root internal root internal root/rcv dgld root /usr/lib/uucpd

More default services (cont. ) mountd/1 stream rpc/tcp wait/lc mountd/1 dgram rpc/udp wait/lc sgi_mountd/1 stream rpc/tcp wait/lc sgi_mountd/1 dgram rpc/udp wait/lc rstatd/1 -3 dgram rpc/udp wait walld/1 dgram rpc/udp wait rusersd/1 dgram rpc/udp wait rquotad/1 dgram rpc/udp wait sprayd/1 dgram rpc/udp wait bootparam/1 dgram rpc/udp wait sgi_videod/1 stream rpc/tcp wait sgi_fam/1 stream rpc/tcp wait sgi_snoopd/1 stream rpc/tcp wait sgi_pcsd/1 dgram rpc/udp wait sgi_pod/1 stream rpc/tcp wait tcpmux/sgi_scanner stream tcp nowait tcpmux/sgi_printer stream tcp nowait 9 fs stream tcp nowait webproxy stream tcp nowait root root root root root rpc. mountd rpc. rstatd rpc. rwalld rpc. rusersd rpc. rquotad rpc. sprayd rpc. bootparamd ? videod ? fam ? rpc. snoopd ? cvpcsd ? podd ? scan/net/scannerd ? print/printerd /v/bin/u 9 fs /usr/local/etc/webserv

Types of malware • • • Worms Viruses Trojans Cookies Adware Keystroke loggers

worms • Stand-alone programs that propagate themselves through computers • Usually enter via network ports
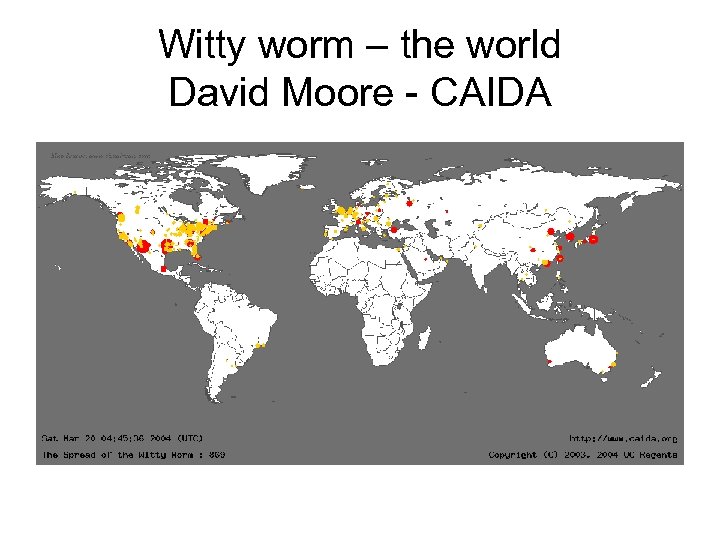
Witty worm – the world David Moore - CAIDA

The witty worm…USA David Moore - CAIDA

viruses • Programs that propagate by infecting other programs • Spread by infecting other programs on a computer, and moving infected programs to other machines, e. g. through mail attachments

trojans • Programs that appear useful, but may have evil side effects. – Imagine a tax preparation program that erases your disk on April 14
cookies • Data stored on your computer by a web server, and returned to that server on future connections • Used to track you and your activities • Not always a bad thing • Not an executable program

adware • Programs that reside in your computer for marketing purposes • May track your browsing, spending, or network activities

Keystroke loggers • Hardware or software that records your keystrokes • Great way to collect passwords, credit card numbers, etc.

Remedies Do you know enough to fix your own computer?




Homepage data • • • Default settings Amount of graphics OS forcing a default Adaware forcing a default Various broadband difficulties with graphics • So much CPU activity that homepage can’t load
You may need to back up yesterday • Pay attention to small differences in your computer’s behavior • Don’t wait for a month to go by before asking someone else • Write down error messages • Go somewhere else to check the errors – The Bernardsville Public Library
Don’t open a new program until you’ve read tomorrow’s paper Circuits, Thursday NYT Personal Journal, WSJ CNET





Help comes in many guises http: //blogs. msdn. com/ie/archive/2 005/01/11/350949. aspx
www. sans. org • Delivered-To: Lepac@cheswick. com From: The SANS Institute <Webcast@sans. org> Subject: Internet Storm Center Threat Update and What Works in Intrusion Prevention Webcasts Please sign into the SANS Portal for upcoming complimentary webcasts in January 2005. On Wednesday, January 12, 2005, the Internet Storm Center will present the latest "Threat Update. " On Thursday, January 20, 2005, SANS will host "What Works in Intrusion Prevention. " 01/19/05 Zombie-nets, Pop-ups, and Spam 45 of 45
http: //tired-ofspam. home. comcast. net/eblocs. h tml
01/19/05 Zombie-nets, Pop-ups, and Spam 47 of 45
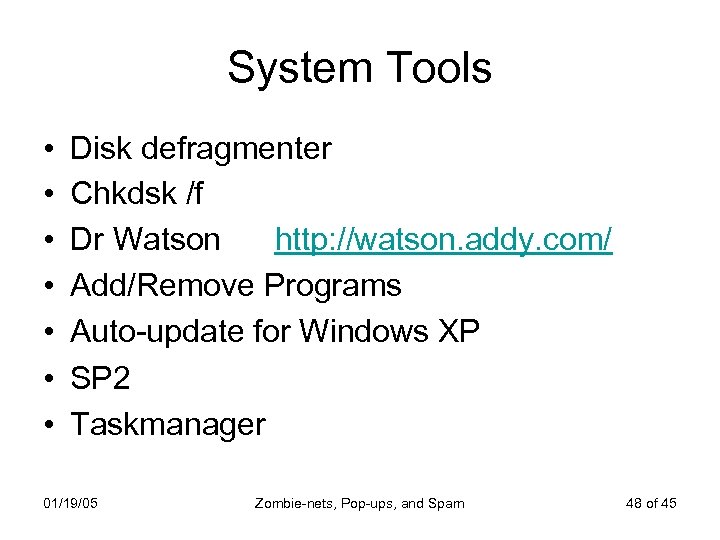
System Tools • • Disk defragmenter Chkdsk /f Dr Watson http: //watson. addy. com/ Add/Remove Programs Auto-update for Windows XP SP 2 Taskmanager 01/19/05 Zombie-nets, Pop-ups, and Spam 48 of 45
Programs that help • • • Up-to-date Anti-virus software Trojan Hunter Spybot Search and Destroy Adaware Avert Stinger Mc. Afee targeted trojan and virus removal programs • Firewalls 01/19/05 Zombie-nets, Pop-ups, and Spam 49 of 45

Websites • • • Download. com CNet. com Google. com Mc. Afee. com Symantec. com CERT. org 01/19/05 Zombie-nets, Pop-ups, and Spam 50 of 45

Backup • What you have to loose 01/19/05 Zombie-nets, Pop-ups, and Spam 51 of 45
Set System Restore points • Make sure you have Operating system source Disks • You may have to buy a new Operating system or upgrade your computer • Make sure you have product keys and authentication. • Caution requires a minimum of two locations 01/19/05 Zombie-nets, Pop-ups, and Spam 52 of 45

Hardware tools • • Key drives External HD External zip drives CD-R or equivalent 01/19/05 Zombie-nets, Pop-ups, and Spam 53 of 45
01/19/05 Zombie-nets, Pop-ups, and Spam 54 of 45
Hardware v Software • Software needs continual updates • Hardware can be neglected, or you can forget the passwords to the interface 01/19/05 Zombie-nets, Pop-ups, and Spam 55 of 45

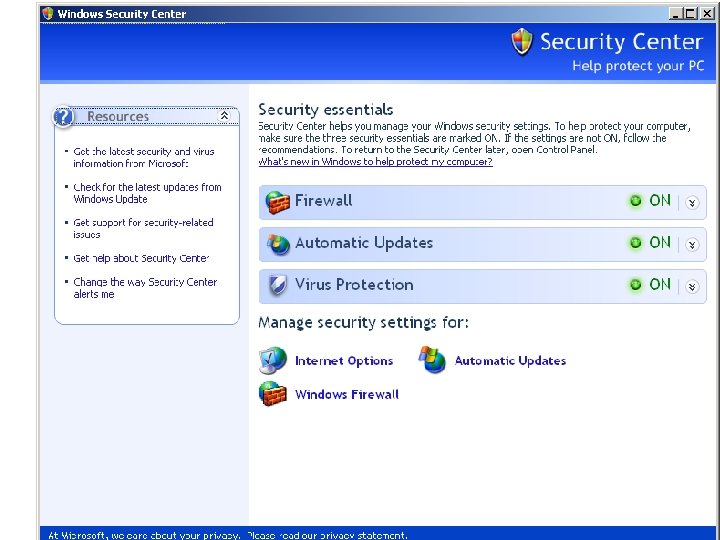
Updates • To auto update or not • Download but prompt to install • Manual install 01/19/05 Zombie-nets, Pop-ups, and Spam 56 of 45
Passwords • 8 or more digits, mixed letters and numbers • Sentence • Dictionary attack • Foreign words • equations 01/19/05 Zombie-nets, Pop-ups, and Spam 57 of 45
Encryption • • At what level Wireless network Router password Server Super user Computer US v the rest of the world- 128 bit encryption 01/19/05 Zombie-nets, Pop-ups, and Spam 58 of 45
Free software • Only owrks in emerging typse of program solutions • Then only until the programmers are in school or dating • Success can be overwhelming and eventually you have to buy coke. 01/19/05 Zombie-nets, Pop-ups, and Spam 59 of 45

System administration • Windows machines do not have automatio to make it easy. 01/19/05 Zombie-nets, Pop-ups, and Spam 60 of 45
Causes • Buffer overflow errors • Port use • TCP/IP coopting 01/19/05 Zombie-nets, Pop-ups, and Spam 61 of 45

Progression • Internet • Network • Your machine 01/19/05 Zombie-nets, Pop-ups, and Spam 62 of 45
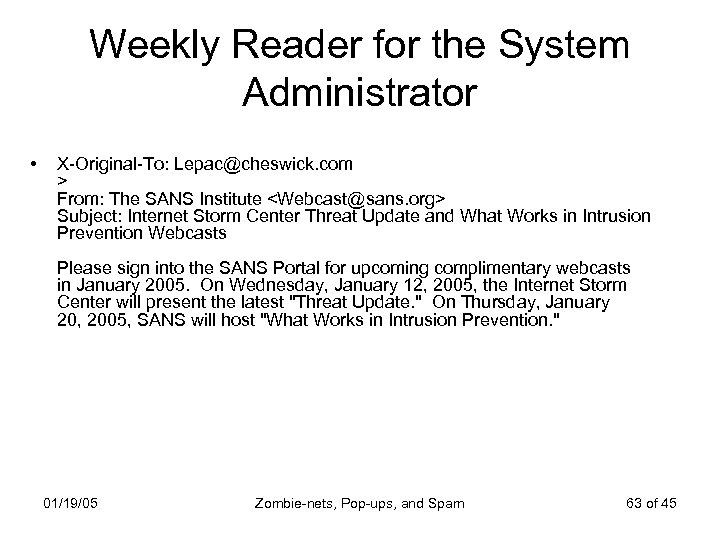
Weekly Reader for the System Administrator • X-Original-To: Lepac@cheswick. com > From: The SANS Institute <Webcast@sans. org> Subject: Internet Storm Center Threat Update and What Works in Intrusion Prevention Webcasts Please sign into the SANS Portal for upcoming complimentary webcasts in January 2005. On Wednesday, January 12, 2005, the Internet Storm Center will present the latest "Threat Update. " On Thursday, January 20, 2005, SANS will host "What Works in Intrusion Prevention. " 01/19/05 Zombie-nets, Pop-ups, and Spam 63 of 45
Help comes in many guises http: //blogs. msdn. com/ie/archive/2 005/01/11/350949. aspx
If its Tuesday it’s another Microsoft Security Bulletin http: //netsecurity. about. com/cs/wi ndowsxp/a/aa 041404. htm
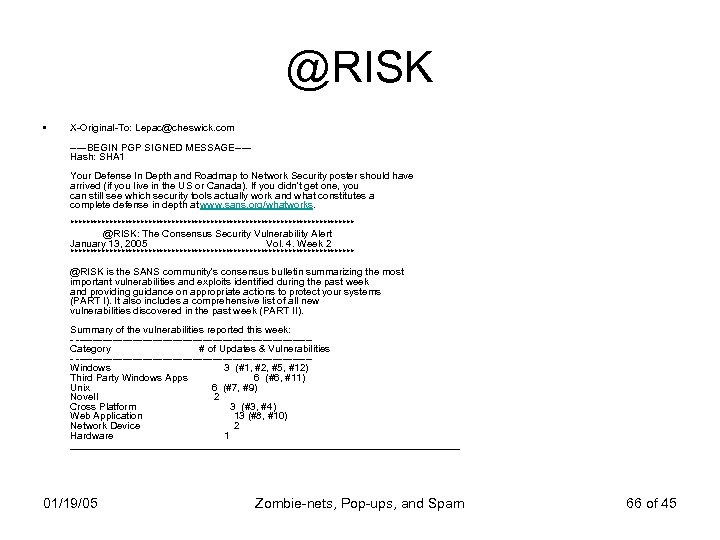
@RISK • X-Original-To: Lepac@cheswick. com -----BEGIN PGP SIGNED MESSAGE----Hash: SHA 1 Your Defense In Depth and Roadmap to Network Security poster should have arrived (if you live in the US or Canada). If you didn't get one, you can still see which security tools actually work and what constitutes a complete defense in depth at www. sans. org/whatworks. ************************************* @RISK: The Consensus Security Vulnerability Alert January 13, 2005 Vol. 4. Week 2 ************************************* @RISK is the SANS community's consensus bulletin summarizing the most important vulnerabilities and exploits identified during the past week and providing guidance on appropriate actions to protect your systems (PART I). It also includes a comprehensive list of all new vulnerabilities discovered in the past week (PART II). Summary of the vulnerabilities reported this week: - -----------------------------------Category # of Updates & Vulnerabilities - -----------------------------------Windows 3 (#1, #2, #5, #12) Third Party Windows Apps 6 (#6, #11) Unix 6 (#7, #9) Novell 2 Cross Platform 3 (#3, #4) Web Application 13 (#8, #10) Network Device 2 Hardware 1 ___________________________________ 01/19/05 Zombie-nets, Pop-ups, and Spam 66 of 45

CERT • Community Emergency Response Team http: //www. cert. org/ • http: //www. cert. org/ 01/19/05 Zombie-nets, Pop-ups, and Spam 67 of 45

Smart phone hacking exploits http: //www. techweb. com/article/printa ble. Article. jhtml; jsessionid=2 ZHIULZR Z 11 U 4 QSNDBCCKHSCJUMEKJVN? article. ID=56200144&site_section=70 0028
Security by Obscurity “Please do not Forward, CC, or BCC this E -mail outside of the XXXX-security-discuss community. Confidentiality is essential for effective Internet security countermeasures. ”

Legitimate Companies doing possibly illegitimate things • http: //www. wildtangent. com/ http: //www. weatherbug. com/ • http: //www. weatherbug. com/ • http: //www. apple. com/itunes/ • http: //www. aim. com/ 01/19/05 Zombie-nets, Pop-ups, and Spam 70 of 45
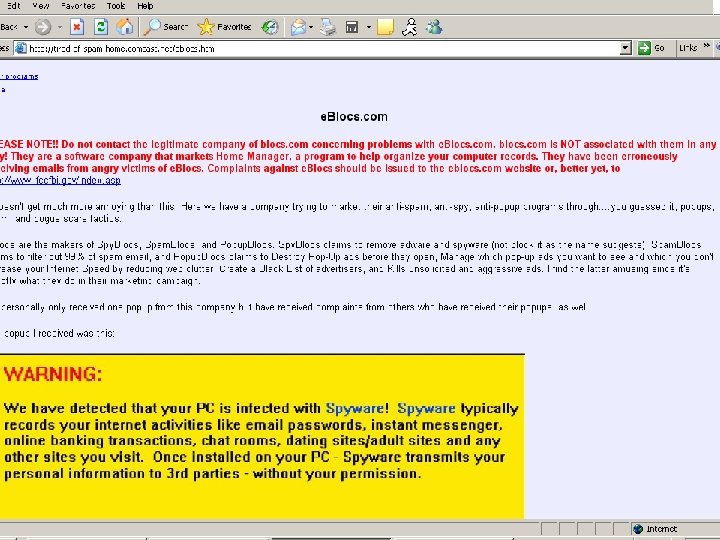
One Case Study • http: //www. eblocs. com/ • http: //tired-ofspam. home. comcast. net/eblocs. html • http: //www. nationaldonotemail. com/cart 11. html • http: //www. spywarewarrior. com/rogue_antispyware. htm 01/19/05 Zombie-nets, Pop-ups, and Spam 71 of 45
Windows XP • Could not open any programs • No processes in Task manager were obvious CPU hogs • Could not get a number of Pop-ups off the desktop, inc a “faulty” load of e. Blocs 01/19/05 Zombie-nets, Pop-ups, and Spam 72 of 45
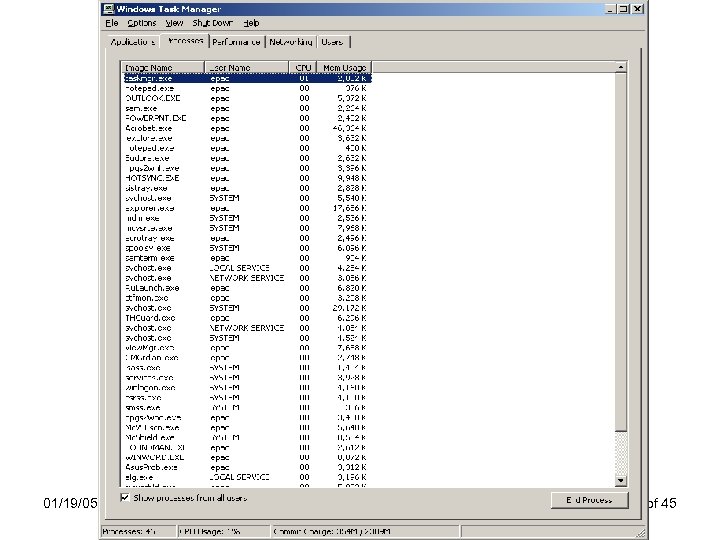
01/19/05 Zombie-nets, Pop-ups, and Spam 73 of 45

01/19/05 Zombie-nets, Pop-ups, and Spam 74 of 45
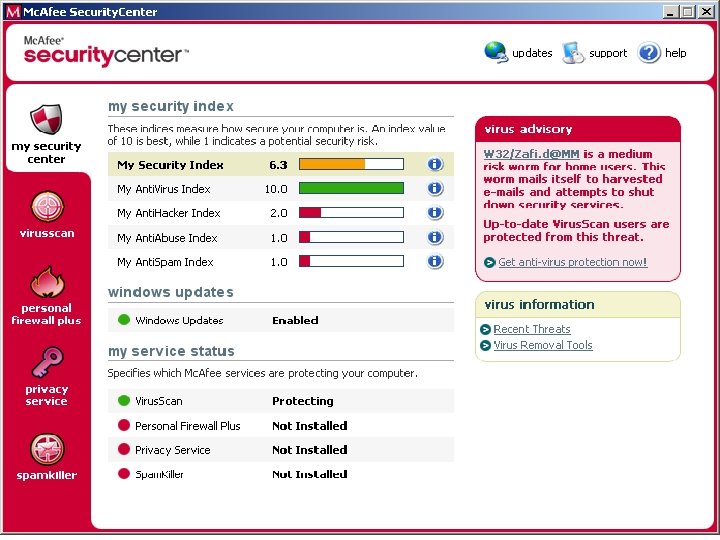
01/19/05 Zombie-nets, Pop-ups, and Spam 75 of 45
01/19/05 Zombie-nets, Pop-ups, and Spam 76 of 45
Programs • Different versions have different security features • Automatic updates can break security in one way or another • Not having automatic updates can kill a computer 01/19/05 Zombie-nets, Pop-ups, and Spam 77 of 45

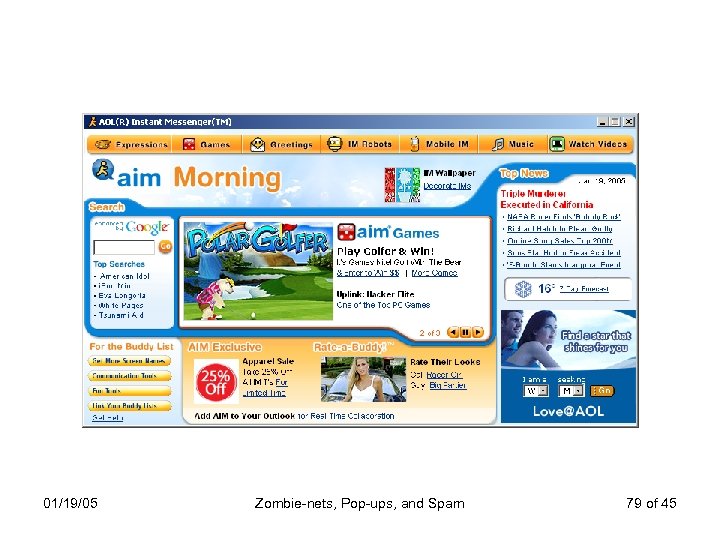
01/19/05 Zombie-nets, Pop-ups, and Spam 79 of 45
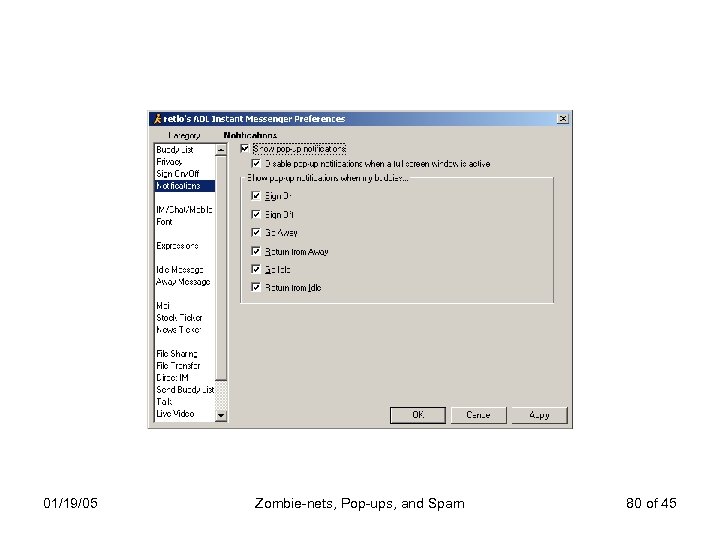
01/19/05 Zombie-nets, Pop-ups, and Spam 80 of 45
Default settings • Make sure important switches are turned off • Read anything marked Security in a program you want to use • Manual v Automatic Updates • Reminders 01/19/05 Zombie-nets, Pop-ups, and Spam 81 of 45
Plan B: Get out of the Game
Plan B: non-Microsoft operating systems • For a business, this can be hard – Are the applications you want to run available and viable on your Plan B system – Will you have trouble exchanging information with your customers? – What kind of support requirements does the system have, and can you find support people? 01/19/05 Zombie-nets, Pop-ups, and Spam 83 of 45

Some Plan B choices • • Apple Macintosh Linux (many flavors) Unix (several flavours) Open source software 01/19/05 Zombie-nets, Pop-ups, and Spam 84 of 45
Apple Macintosh • A long-time favorite of artists – Handles things like photos and movies better than common Windows applications • More stable than Windows • Requires much less maintenance than Windows • Much less malware directed at it • Hardware and software is more expensive 01/19/05 Zombie-nets, Pop-ups, and Spam 85 of 45

Linux • Most versions of Linux are free – May be downloaded and installed on the net • Gnoppix – linux without bothering your hard drive: http: //www. gnoppix. org 01/19/05 Zombie-nets, Pop-ups, and Spam 86 of 45
Unix • Software workbench for much of the world • Free. BSD, Open. BSD, Net. BSD are the common ones – Also commercial versions for HP, Sun, etc. • • Non-commercial versions are free Very high quality software Very robust May lack the application or drivers you need

Open source software • • Free software that you can build yourself Many improve it Wikipedia is an open source encyclopedia Open source – Mozilla firefox (web browser) – Gaim (instant messager) – Mythtv (PVR, like Ti. Vo)
Zombie-nets, Pop-ups, and Spam By Bill and Lorette Cheswick ches@cheswick. com lepac@cheswick. com http: //www. cheswick. com
4fa2a04209e785dff3dc6a4aa9d55992.ppt