806e849d4411433d5d39865e8131b94e.ppt
- Количество слайдов: 53
Wireless Security (Based on slides by Dr. Frank Adelstein of ATC-NY/Odyssey Research Associates) Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 1
Protect what? • Integrity – System: performs its intended function in an unimpaired manner, free from deliberate or inadvertent unauthorized manipulation of the system. – Data: Should be possible for receiver to verify that data has not been modified; intruder should not be able to substitute fake data • Confidentiality – Only intended recipient(s) should be able to read data • Non-repudiation – Sender should not be able to falsely deny sending data. • Availability (Denial of Service, Distributed Do. S) – A third party with no access should not be able to block legitimate parties from using a resource. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 2
Security: Before/During/After • Prevention (before) – Authentication, authorization, accounting • Detection (during) – Intrusion Detection • Host/network • Signature/behavior • Reaction (after) – Digital Forensics • Evidence preservation • Who? What? When? From where? • Sources (files, logs, timestamp info, ISP records, …) – Attack Assessment, Damage Assessment, Data Recovery Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 3
Before • Prevention – Authentication: “Are they who they claim to be? ” “The act of verifying a claimed identity, in the form of a pre-existing label from a mutually known name space, as the originator of a message (message authentication) or as the end-point of a channel (entity authentication). ” – Authorization: “Do they have permission to do it? ” “The act of determining if a particular right, such as access to some resource, can be granted to the presenter of a particular credential. ” – Accounting: a log or history of what happened “The collection of resource consumption data for the purposes of capacity and trend analysis, cost allocation, auditing, and billing. Accounting management requires that resource consumption be measured, rated, assigned, and communicated between appropriate parties. ” Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 4
Security Tradeoffs Security vs. : • Convenience – long vs. short passwords – Multi-factor authentication – callback, smart cards, etc. • Availability – – locked out after 3 bad passwords ATM eats bank card Don’t allow remote access? what happens when log files fill up? Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 5
Wireless Risks • Wireless – all of the above concerns plus an increased risk of eavesdropping (and transmitting). – No need to tap or plug into the network. Only need to be “nearby. ” – Depending on the wireless technology, nearby can be line-of-sight, same room, outside a building, within a few miles (e. g. , Bluetooth sniper rifle) • Greatly increases threats to: confidentiality, integrity, non-repudiation Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 6
Risks (2) These risks can allow adversaries to: • Perform data snooping – Medical data becoming more available • Hijack sessions • Commit Fraud and identity theft Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 7
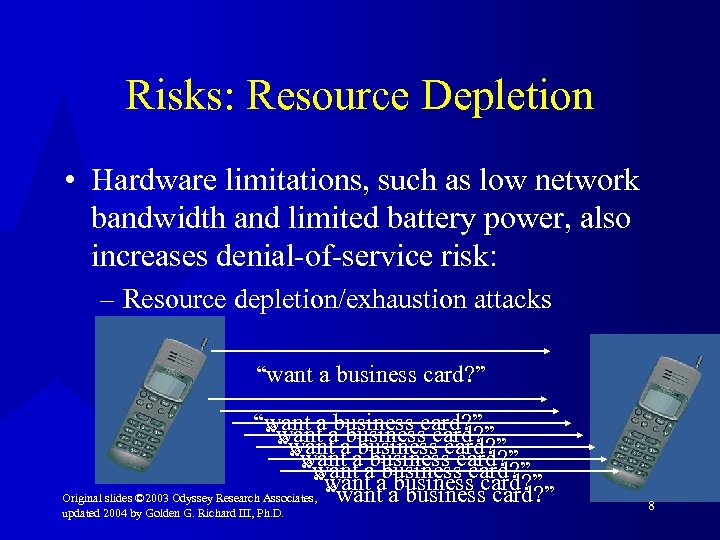
Risks: Resource Depletion • Hardware limitations, such as low network bandwidth and limited battery power, also increases denial-of-service risk: – Resource depletion/exhaustion attacks “want a business card? ” “want a a business card? ” “want business card? ” Original slides © 2003 Odyssey Research Associates, “want a business card? ” updated 2004 by Golden G. Richard III, Ph. D. 8
Protections • Make it harder to intercept transmissions at the intruder’s physical layer – Use low power, limit reception/interception range. – Use a technique like frequency hopping • But, generally want anyone to be able to join in and use the network. • Actually used to increase number of users, not for protection. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 9
Protections • Encryption: “they” can’t decode data, so they can’t use what they do steal • Digital signatures: prevent forging or modifying data Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 10
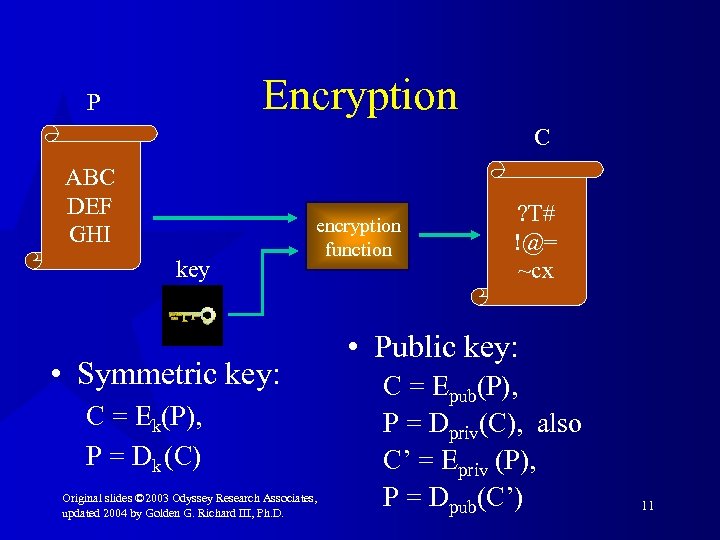
Encryption P C ABC DEF GHI key encryption function • Symmetric key: C = Ek(P), P = Dk (C) Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. ? T# !@= ~cx • Public key: C = Epub(P), P = Dpriv(C), also C’ = Epriv (P), P = Dpub(C’) 11
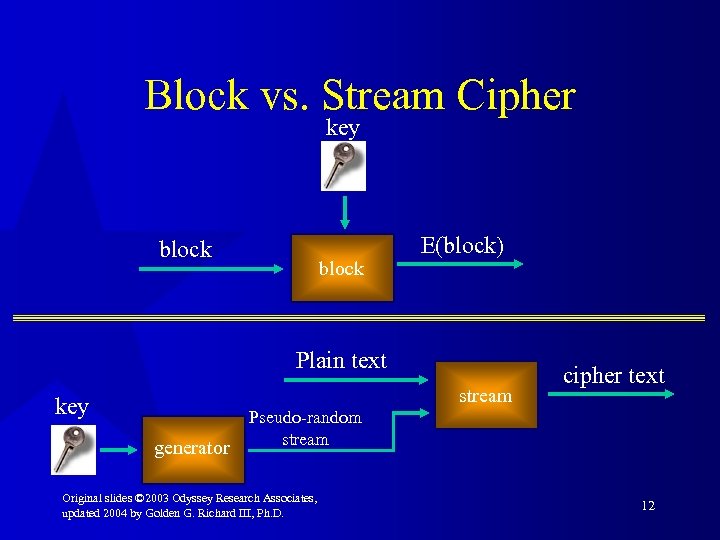
Block vs. Stream Cipher key block E(block) Plain text stream key generator cipher text Pseudo-random stream Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 12
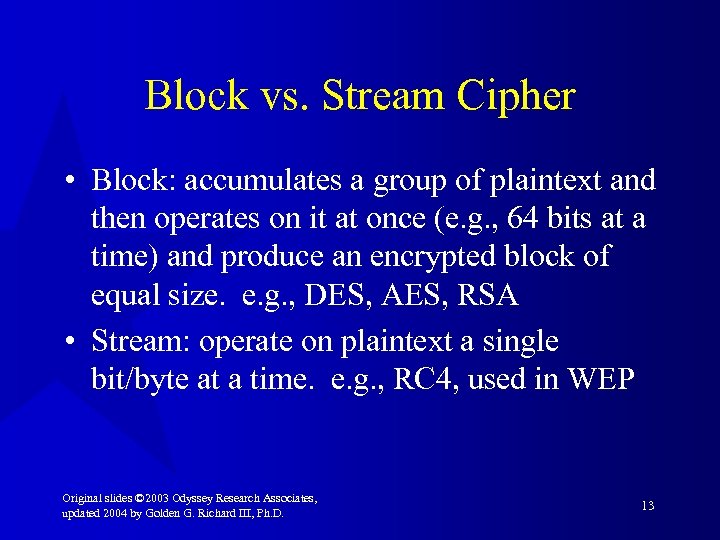
Block vs. Stream Cipher • Block: accumulates a group of plaintext and then operates on it at once (e. g. , 64 bits at a time) and produce an encrypted block of equal size. e. g. , DES, AES, RSA • Stream: operate on plaintext a single bit/byte at a time. e. g. , RC 4, used in WEP Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 13
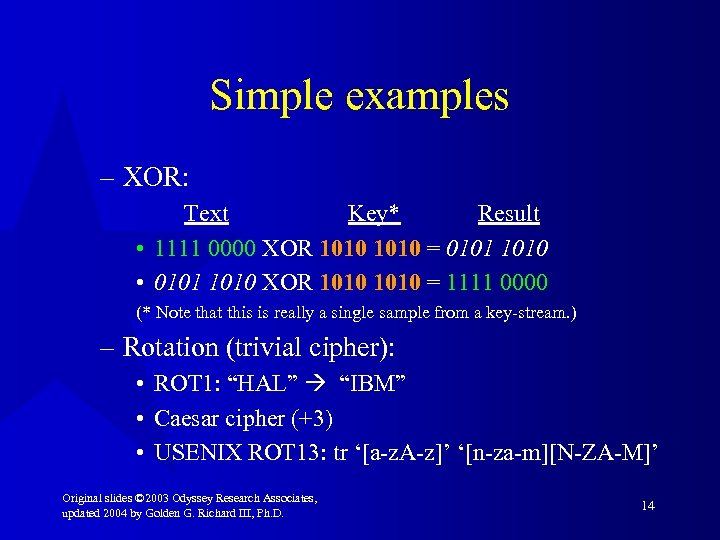
Simple examples – XOR: Text Key* Result • 1111 0000 XOR 1010 = 0101 1010 • 0101 1010 XOR 1010 = 1111 0000 (* Note that this is really a single sample from a key-stream. ) – Rotation (trivial cipher): • ROT 1: “HAL” “IBM” • Caesar cipher (+3) • USENIX ROT 13: tr ‘[a-z. A-z]’ ‘[n-za-m][N-ZA-M]’ Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 14
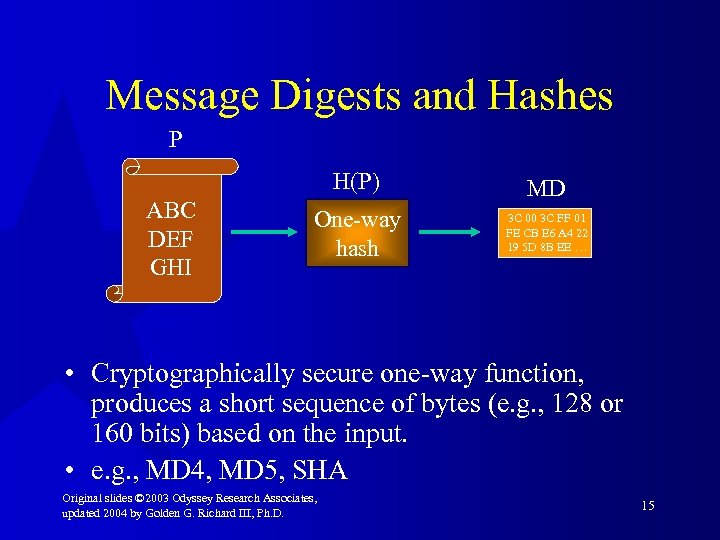
Message Digests and Hashes P H(P) ABC DEF GHI One-way hash MD 3 C 00 3 C FF 01 FE CB E 6 A 4 22 19 5 D 8 B EE … • Cryptographically secure one-way function, produces a short sequence of bytes (e. g. , 128 or 160 bits) based on the input. • e. g. , MD 4, MD 5, SHA Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 15
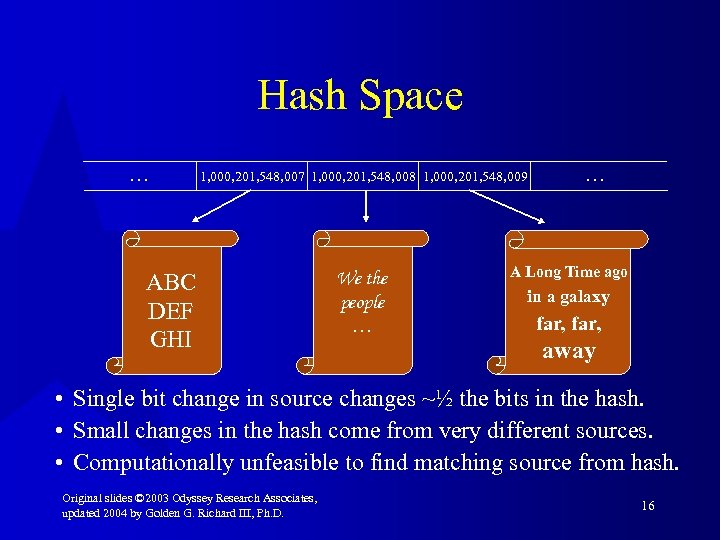
Hash Space. . . 1, 000, 201, 548, 007 1, 000, 201, 548, 008 1, 000, 201, 548, 009 ABC DEF GHI We the people … . . . A Long Time ago in a galaxy far, away • Single bit change in source changes ~½ the bits in the hash. • Small changes in the hash come from very different sources. • Computationally unfeasible to find matching source from hash. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 16
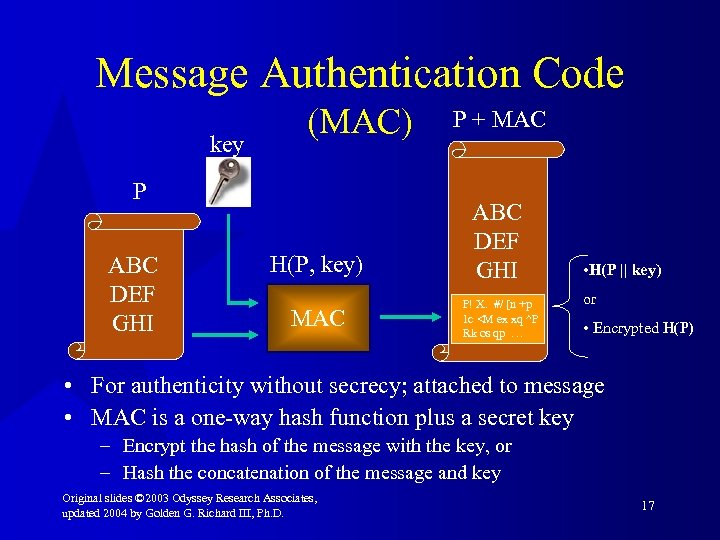
Message Authentication Code key (MAC) P ABC DEF GHI H(P, key) MAC P + MAC ABC DEF GHI P! X. #/ [n +p 1 c <M ex xq ^P Rk os qp … • H(P || key) or • Encrypted H(P) • For authenticity without secrecy; attached to message • MAC is a one-way hash function plus a secret key – Encrypt the hash of the message with the key, or – Hash the concatenation of the message and key Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 17
Costs of Protections • Encryption overhead! (more tradeoffs) – Poor performance – CPU load – Power consumption – Reduced battery life – Increased data size increased transmission time Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 18
Cost of Protections • Public Key Infrastructure (PKI) – Key management • Key setup • Key exchange – – – Certificates Trusted 3 rd party Shared secrets (and risks) vs. public key Individual vs. group keys (overhead) Certificate revocation or expiration Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 19
IP Security (IPsec) • IETF IPsec Working Group – Provide authentication. • Authentication Header (AH): RFC 2402 – Protect the data payload • Encapsulating Security Payload (ESP): RFC 2406 – Key management • Internet Security Association and Key Management Protocol (ISAKMP): RFC 2408 Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 20
Misc. Attacks Additional attack methods: • Man-in-the-middle attacks (e. g. , ARP cache poisoning, bogus services) –Use good authentication • Replay attacks – Use sequence numbers + one time data • Traffic analysis –Use encrypted communication Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 21
Misc. Security Physical security • “Stolen laptop” scenario • Defenses: – – CMOS password w/ hardware tamper protection Password protected accounts on computer Encrypted data Biometrics for authentication • None of these defenses result in return of the laptop, unfortunately Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 22
Misc. Non-Technical Attacks • “Social engineering” plus $$$ tend to be very effective – Look for resumes on the web, buy a drink, etc. – See Kevin Mitnick’s book for lots more • “Rubber-hose” cryptanalysis "Believe me, Baldric, an eternity in the company of Beelzebub and all his hellish minions will be as nothing compared to five minutes alone with me. . . and this pencil. ” – Blackadder. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 23
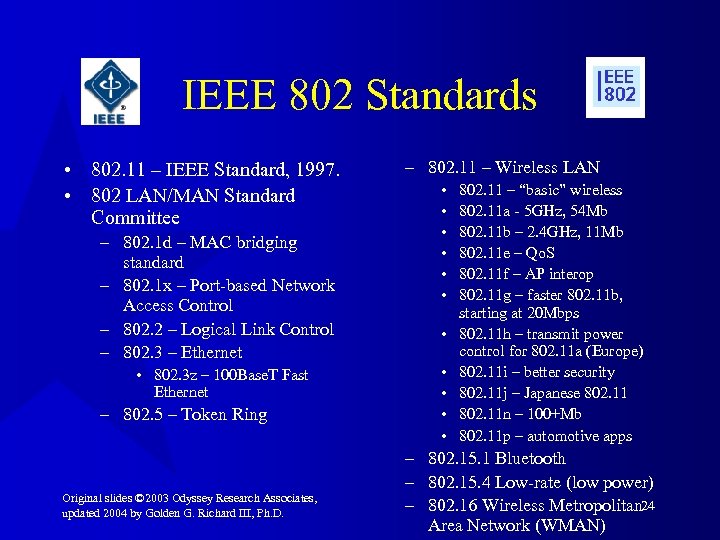
IEEE 802 Standards • 802. 11 – IEEE Standard, 1997. • 802 LAN/MAN Standard Committee – 802. 1 d – MAC bridging standard – 802. 1 x – Port-based Network Access Control – 802. 2 – Logical Link Control – 802. 3 – Ethernet • 802. 3 z – 100 Base. T Fast Ethernet – 802. 5 – Token Ring Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. – 802. 11 – Wireless LAN • • • 802. 11 – “basic” wireless 802. 11 a - 5 GHz, 54 Mb 802. 11 b – 2. 4 GHz, 11 Mb 802. 11 e – Qo. S 802. 11 f – AP interop 802. 11 g – faster 802. 11 b, starting at 20 Mbps 802. 11 h – transmit power control for 802. 11 a (Europe) 802. 11 i – better security 802. 11 j – Japanese 802. 11 n – 100+Mb 802. 11 p – automotive apps – 802. 15. 1 Bluetooth – 802. 15. 4 Low-rate (low power) – 802. 16 Wireless Metropolitan 24 Area Network (WMAN)
WEP – Protection for 802. 11 b • Wired Equivalent Privacy – “No worse than what you get with wire-based systems” • Criteria: – “Reasonably strong” – Self-synchronizing – stations often go in and out of coverage – Computationally efficient – in HW or SW since low MIPS CPUs might be used – Exportable – – Optional – not required to used it Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 25
WEP – How It Works • Secret key (40 bits or 104 bits) • Initialization vector (24 bits, by IEEE std. ) – Total of 64 or 128 bits “of protection. ” • RC 4 -based pseudo random number generator (PRNG) • Integrity Check Value (ICV): CRC 32 Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 26
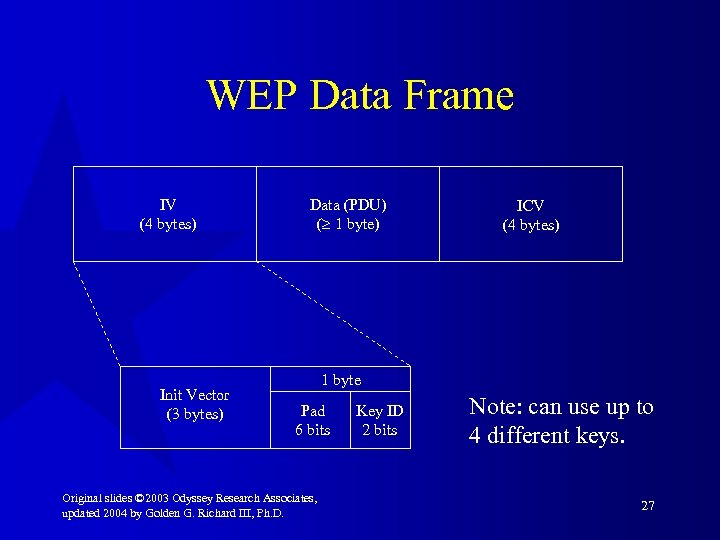
WEP Data Frame IV (4 bytes) Init Vector (3 bytes) Data (PDU) ( 1 byte) ICV (4 bytes) 1 byte Pad 6 bits Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. Key ID 2 bits Note: can use up to 4 different keys. 27
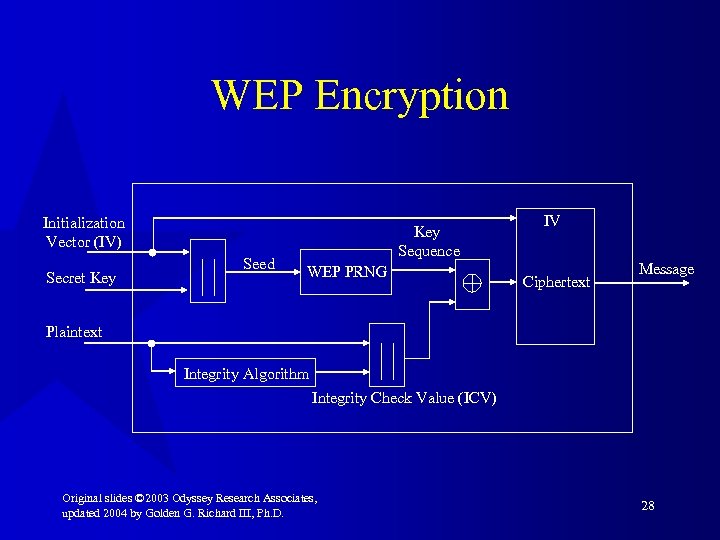
WEP Encryption Initialization Vector (IV) Secret Key Seed Key Sequence WEP PRNG IV Ciphertext Message Plaintext Integrity Algorithm Integrity Check Value (ICV) Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 28
WEP Encryption Process 1. Compute ICV using CRC-32 over plaintext msg. 2. Concatenate ICV to plaintext message. 3. Choose random IV and concat it to secret key and input it to RC 4 to produce pseudo random key sequence. 4. Encrypt plaintext + ICV by doing bitwise XOR with key sequence to produce ciphertext. 5. Put IV in front of cipertext. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 29
WEP Decryption Secret Key WEP PRNG IV Ciphertext Key Sequence Plaintext Seed Message Integrity Algorithm ICV’ - ICV Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 30
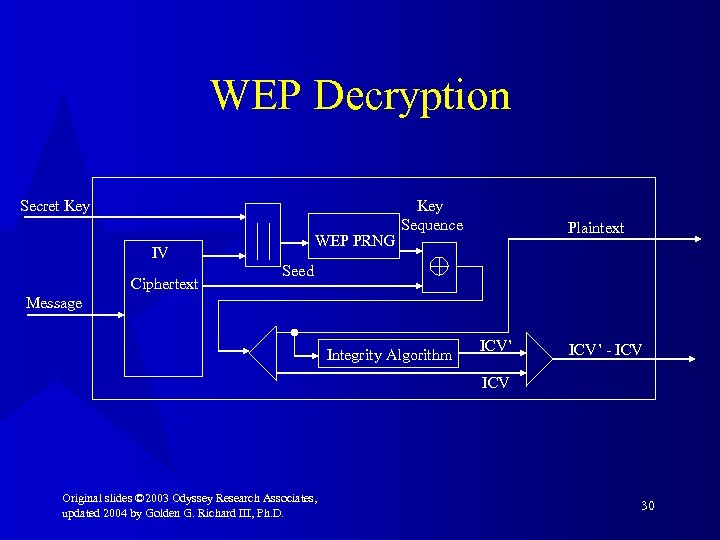
WEP Decryption Process 1. IV of message used to generate key sequence, k. 2. Ciphertext XOR k original plaintext + ICV. 3. Verify by computing integrity check on plaintext (ICV’) and comparing to recovered ICV. 4. If ICV’ then message is in error; send error to MAC management and back to sending station. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 31
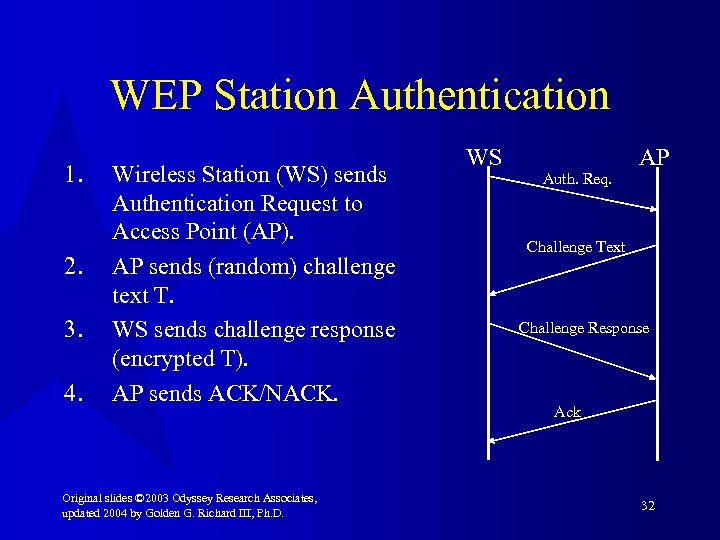
WEP Station Authentication 1. 2. 3. 4. Wireless Station (WS) sends Authentication Request to Access Point (AP). AP sends (random) challenge text T. WS sends challenge response (encrypted T). AP sends ACK/NACK. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. WS Auth. Req. AP Challenge Text Challenge Response Ack 32
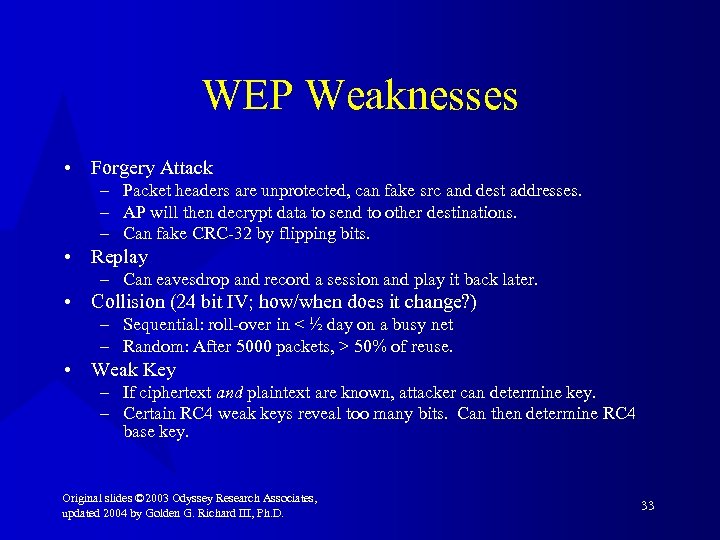
WEP Weaknesses • Forgery Attack – Packet headers are unprotected, can fake src and dest addresses. – AP will then decrypt data to send to other destinations. – Can fake CRC-32 by flipping bits. • Replay – Can eavesdrop and record a session and play it back later. • Collision (24 bit IV; how/when does it change? ) – Sequential: roll-over in < ½ day on a busy net – Random: After 5000 packets, > 50% of reuse. • Weak Key – If ciphertext and plaintext are known, attacker can determine key. – Certain RC 4 weak keys reveal too many bits. Can then determine RC 4 base key. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 33
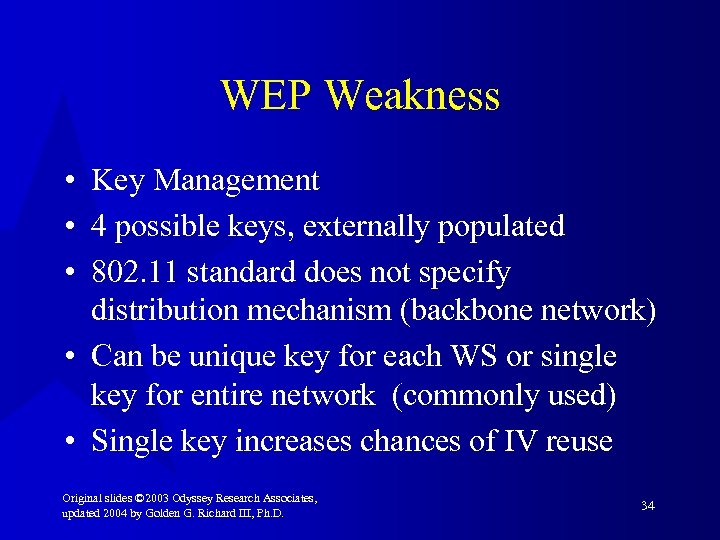
WEP Weakness • Key Management • 4 possible keys, externally populated • 802. 11 standard does not specify distribution mechanism (backbone network) • Can be unique key for each WS or single key for entire network (commonly used) • Single key increases chances of IV reuse Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 34
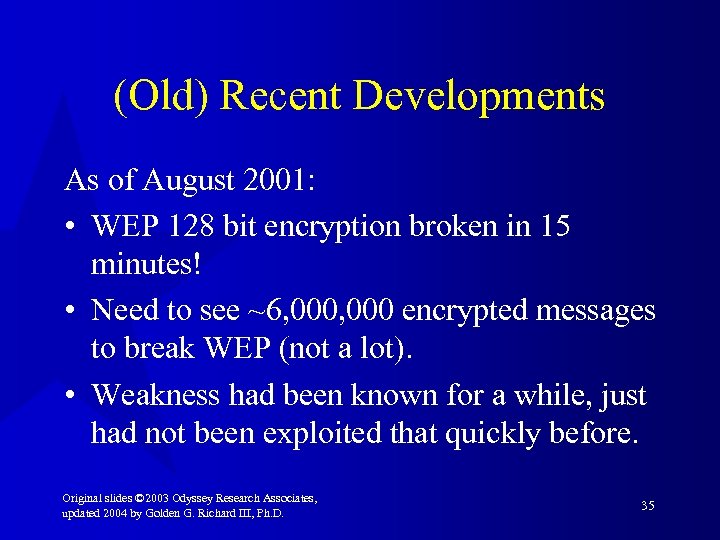
(Old) Recent Developments As of August 2001: • WEP 128 bit encryption broken in 15 minutes! • Need to see ~6, 000 encrypted messages to break WEP (not a lot). • Weakness had been known for a while, just had not been exploited that quickly before. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 35
Practical Results… Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 36
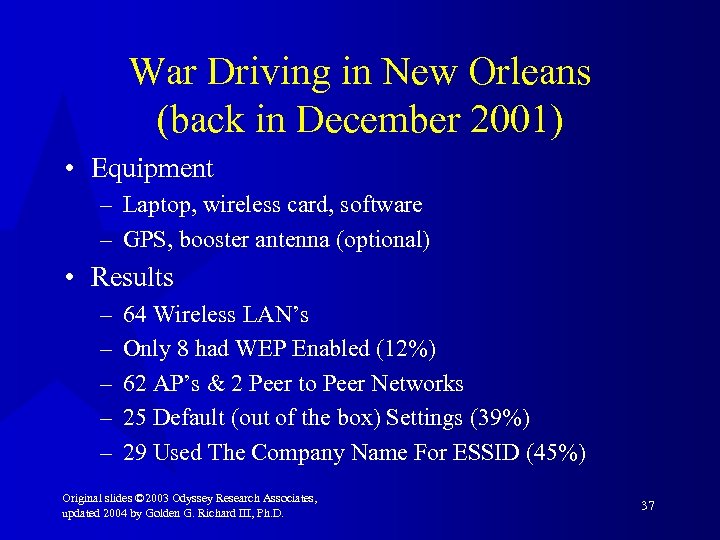
War Driving in New Orleans (back in December 2001) • Equipment – Laptop, wireless card, software – GPS, booster antenna (optional) • Results – – – 64 Wireless LAN’s Only 8 had WEP Enabled (12%) 62 AP’s & 2 Peer to Peer Networks 25 Default (out of the box) Settings (39%) 29 Used The Company Name For ESSID (45%) Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 37
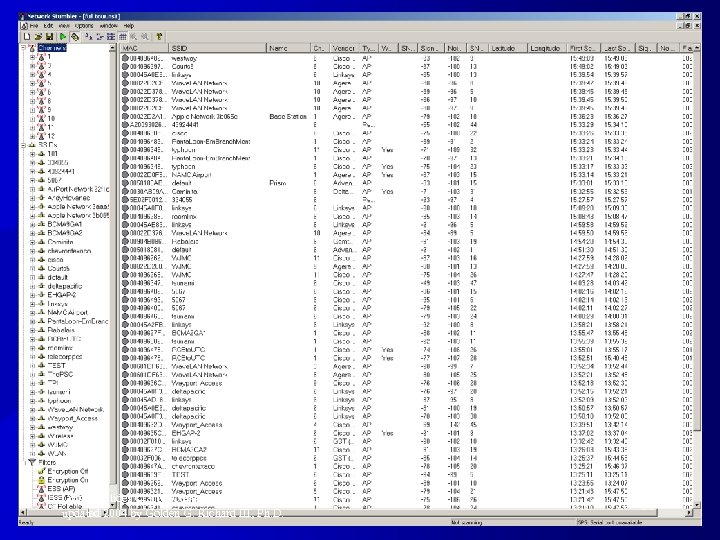
Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 38
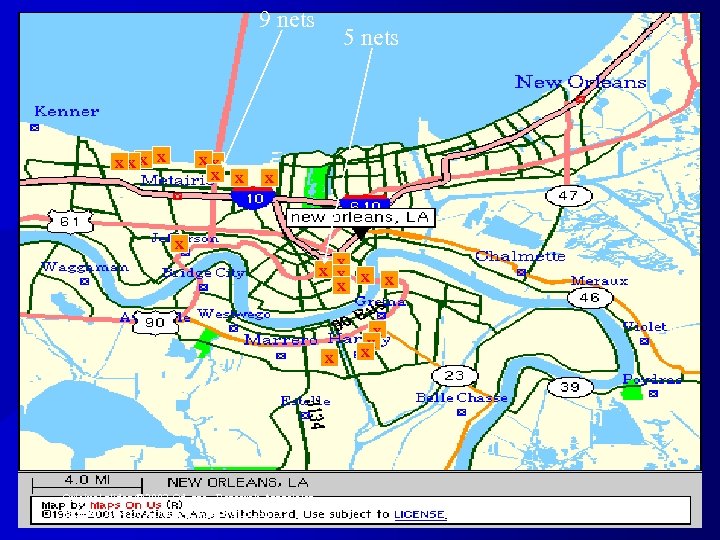
9 nets XXX X X 5 nets X X X X Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. X X X 39
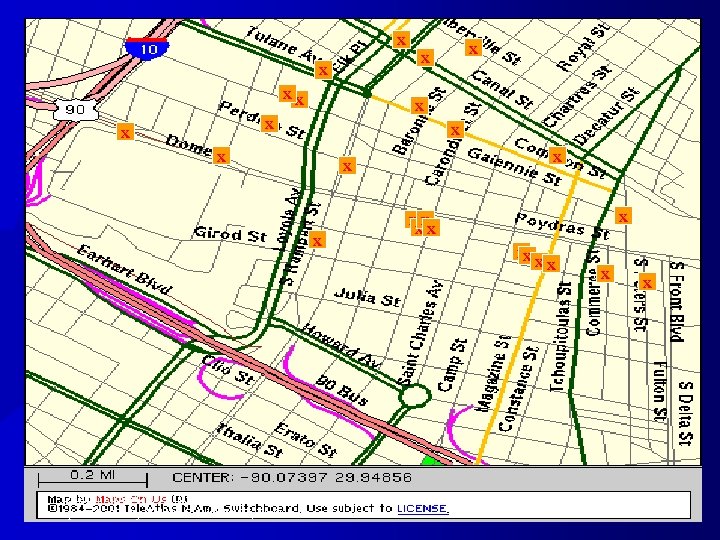
X X X X Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. X XX XX X X X 40
Ways to Improve Security with WEP • All encryption modes of operation should use (secure) MAC, rather than CRC • Use WEP(!) • Put wireless network outside of firewall • Use VPN to get inside • Limit connections based on MAC address – Easily defeated • Better key management: – Use individual keys – Change them early and often • Better: replace with something else Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 41
What’s next? • Wi. Fi Protected Access (WPA) available sooner – Approximation of what will be in 802. 11 i – Already cracked (11/2004) • 802. 11 i – Provides better security, key distribution, longer/better initialization vectors, etc. – Probably incompatible with most current hardware Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 42
802. 11 i – Improved encryption Algorithms • Temporal Key Integrity Protocol (TKIP) – for legacy hardware – Generates per-packet keys – 48 bit IV prevents replay attacks • Counter mode CBC-MAC Protocol (CCMP) – for new hardware – Not for legacy hardware—insufficient CPU power to run AES encryption – 802. 1 x – port based network access control • Authentication • Encryption key distribution Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 43
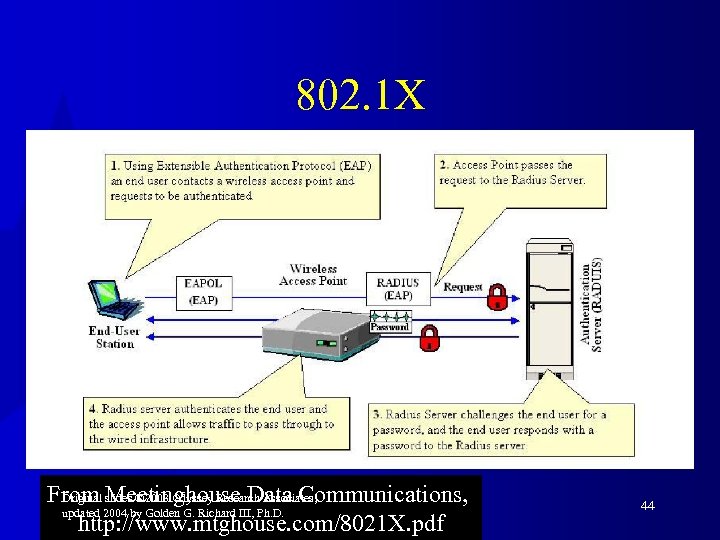
802. 1 X From slides © 2003 Odyssey Research Associates, Original Meetinghouse Data Communications, updated 2004 by Golden G. Richard III, Ph. D. http: //www. mtghouse. com/8021 X. pdf 44
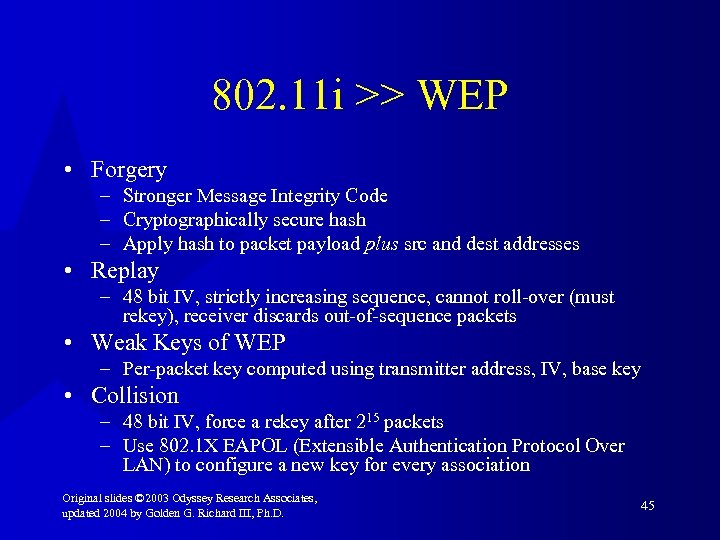
802. 11 i >> WEP • Forgery – Stronger Message Integrity Code – Cryptographically secure hash – Apply hash to packet payload plus src and dest addresses • Replay – 48 bit IV, strictly increasing sequence, cannot roll-over (must rekey), receiver discards out-of-sequence packets • Weak Keys of WEP – Per-packet key computed using transmitter address, IV, base key • Collision – 48 bit IV, force a rekey after 215 packets – Use 802. 1 X EAPOL (Extensible Authentication Protocol Over LAN) to configure a new key for every association Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 45
802. 11: Do. S a Major Concern • Denial of service attacks still a major problem • Physical-level Do. S • De-authentication attacks Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 46
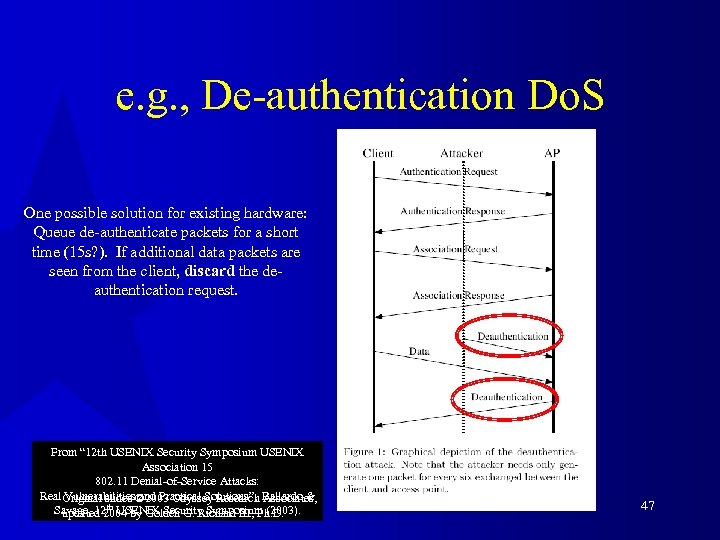
e. g. , De-authentication Do. S One possible solution for existing hardware: Queue de-authenticate packets for a short time (15 s? ). If additional data packets are seen from the client, discard the deauthentication request. From “ 12 th USENIX Security Symposium USENIX Association 15 802. 11 Denial-of-Service Attacks: Real Original slides © 2003 Odyssey Research Ballardo & Vulnerabilities and Practical Solutions”, Associates, Savage, 12 th USENIX Security Symposium (2003). updated 2004 by Golden G. Richard III, Ph. D. 47
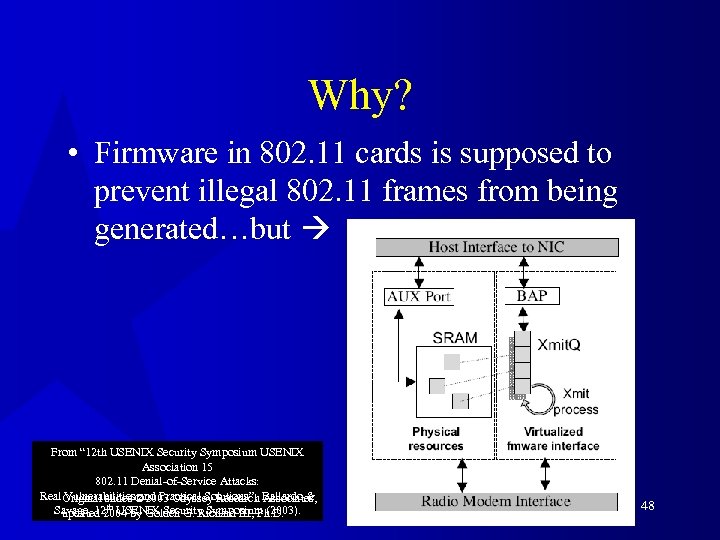
Why? • Firmware in 802. 11 cards is supposed to prevent illegal 802. 11 frames from being generated…but From “ 12 th USENIX Security Symposium USENIX Association 15 802. 11 Denial-of-Service Attacks: Real Original slides © 2003 Odyssey Research Ballardo & Vulnerabilities and Practical Solutions”, Associates, Savage, 12 th USENIX Security Symposium (2003). updated 2004 by Golden G. Richard III, Ph. D. 48
802. 11 • Jim Geier, “Spread Spectrum: Frequency Hopping vs. Direct Sequence, ” http: //www. wireless-nets. com/whitepaper_spread. htm. • 3 com, “What’s New in Wireless LANs: The IEEE 802. 11 b Standard, ” http: //www. 3 com. com/technology/tech_net/white_papers/503072 a. html. • Sultan Weatherspoon, “Overview of IEEE 802. 11 b Security, ” Intel Technology Journal, 2 nd Quarter 2000, http: //developer. intel. com/technology/itj/q 22000/pdf/art_5. pdf. • Jim Lansford, Adrian Stephens, and Ron Nevo, “Wi-Fi (802. 11 b) and Bluetooth: Enabling Coexistence, ” IEEE Network, Sept/Oct 2001. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 49
WEP • • • R. L. Rivest, “The RC 4 Encryption Algorithm, ” RSA Data Security, Inc. March 12, 1992 (proprietary). RFC 2401, Stephen Kent and Randall Atkinson, “Security Architecture for the Internet Protocol, ” Internet Engineering Task Force, Nov. 1998, http: //www. ietf. org/rfc 2401. txt. Nikita Borisov, Ian Goldberg, and David Wagner, “Intercepting Mobile Communications: The Insecurity of 802. 11 (-Draft-), ” Mac Crypto Workshop, Jan. 2001, http: //www. isaac. cs. berkeley. edu/isaac/wep-draft. pdf. Scott Fluhrer, Itsik Mantin, and Adi Shamir, “Weaknesses in the Key Scheduling Algorithm of RC 4, ” Proceedings of Selected Areas in Cryptography (SAC), Toronto, August 2001, http: //www. wisdom. weizmann. ac. il/~itsik/RC 4/Papers/Rc 4_ksa. ps. Adam Stubblefield, John Ioannidis, and Aviel D. Rubin, “Using the Fluhrer, Mantin, and Shamir Attack to Break WEP, ” AT&T Labs Technical Report TD -4 ZCPZZ, August 2001, http: //www. cs. rice. edu/~astubble/wep/. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 50
WEP • Nicki Hayes, “Wired Equivalent Privacy (WEP) – Gone in 15 Minutes!” http: //www. wirelessdevnet. com/channels/wireless/features/newsbyte 3 1. html. • “WEP Security Goes ‘Poof’, ” Information Security, 4(9), September 2001, p 30. • Craig Ellison, “Wireless LANs at Risk”, PC Magazine, April 9, 2002, pp. 66 – 68. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 51
Recent Additions • Fun stuff: Neal Stephenson, Cryptonomicon, Perennial, 1999. • “Evolving to Seamless All-IP Wireless/Mobile Networks, ” Special Issue of IEEE Communications Magazine, Dec. 2001, 39(12). • Air. Snort: http: //airsnort. sorceforge. net. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 52
802. 11 i and 802. 1 x • Jesse Walker, “ 802. 11 Security Considerations and Solutions, ” Intel Developer Forum, Spring 2002. • Merwyn Andrade, “Securing the WLAN with 802. 11 i, ” … • Dennis Eaton, “Diving into the 802. 11 i Spec: A Tutorial, ” Comms. Design, Nov 22, 2002, http: //www. commsdesign. com/printable. Article? doc_id=O EG 20021126 S 0003 • “Wireless Netowkr Security Bulletin V. 2. 1, ” White Paper, Proxim Corp, CP 6 -0103, 2003. • “IEEE Standard for Local and metropolitan area networks – Port Based Network Access Control, ” IEEE Std 802. 1 X 2001. Original slides © 2003 Odyssey Research Associates, updated 2004 by Golden G. Richard III, Ph. D. 53
806e849d4411433d5d39865e8131b94e.ppt