9b0867a96ccfe18ddb478c23cd4bb387.ppt
- Количество слайдов: 33
 Wireless RADIUS Access Susan Mulholland Joseph Paulowskey Joseph Woulfe
Wireless RADIUS Access Susan Mulholland Joseph Paulowskey Joseph Woulfe
 What is a Wi-Fi? § § Stands for Wireless Fidelity The wireless networking and networking is called 802. 11 Can connect PC’s, notebooks, and PDAs to enable them to share internet connections, printers and documents Can be up to 300 feet
What is a Wi-Fi? § § Stands for Wireless Fidelity The wireless networking and networking is called 802. 11 Can connect PC’s, notebooks, and PDAs to enable them to share internet connections, printers and documents Can be up to 300 feet
 Three kinds of 802. 11 § 802. 11 b § 802. 11 a § 802. 11 g § The first version of 802. 11 b § Slowest § Least expensive § The second version § Can handle up to 54 mega bits per second § Operates at 5 GHz § The third version § Operates at 2. 4 GHz § Has advantage of higher speeds
Three kinds of 802. 11 § 802. 11 b § 802. 11 a § 802. 11 g § The first version of 802. 11 b § Slowest § Least expensive § The second version § Can handle up to 54 mega bits per second § Operates at 5 GHz § The third version § Operates at 2. 4 GHz § Has advantage of higher speeds
 Advantages of Wi-Fi § § § Allows LANs to be deployed without cabling Reduce the costs of network deployment and expansion. Can host wireless LANs. Networks support roaming Wi-Fi client works in all different countries A global set of standards
Advantages of Wi-Fi § § § Allows LANs to be deployed without cabling Reduce the costs of network deployment and expansion. Can host wireless LANs. Networks support roaming Wi-Fi client works in all different countries A global set of standards
 Disadvantages of Wi-Fi § § § Power consumption is high Concerns about battery life and heat Has limited range. Access points could be used to steal personal information transmitted from Wi-Fi users. Wired Equivalent Privacy or WEP is easy to be breakable even when correctly configured. WPA 2 Wired Protected Access is improved and better than WEP.
Disadvantages of Wi-Fi § § § Power consumption is high Concerns about battery life and heat Has limited range. Access points could be used to steal personal information transmitted from Wi-Fi users. Wired Equivalent Privacy or WEP is easy to be breakable even when correctly configured. WPA 2 Wired Protected Access is improved and better than WEP.
 Wi-Fi Security § § If a hotspot is open, then anyone with a Wi-Fi card can access the hotspot. The original standard was 64 -bit encryption that was easily broken. If it is secure using 128 -bit encryption, then the user needs to know a WEP key to connect. Using a hotspot at your house, you need a WEP 128 -bit encryption preventing intruders into your network.
Wi-Fi Security § § If a hotspot is open, then anyone with a Wi-Fi card can access the hotspot. The original standard was 64 -bit encryption that was easily broken. If it is secure using 128 -bit encryption, then the user needs to know a WEP key to connect. Using a hotspot at your house, you need a WEP 128 -bit encryption preventing intruders into your network.
 Wi-Fi network in your home § 802. 11 b § Is slightly less expensive and the slowest of the three 802. 11. For home use, 802. 11 g costs just a little more, but is up to 5 times faster. If you will be doing a lot of file transfers between computers in your home, 802. 11 g is definitely the way to go. § 802. 11 g § Costs just a little more, § Up to 5 times faster. If you do a lot of file transfers between computers in your home, then 802. 11 g is the best the way to go.
Wi-Fi network in your home § 802. 11 b § Is slightly less expensive and the slowest of the three 802. 11. For home use, 802. 11 g costs just a little more, but is up to 5 times faster. If you will be doing a lot of file transfers between computers in your home, 802. 11 g is definitely the way to go. § 802. 11 g § Costs just a little more, § Up to 5 times faster. If you do a lot of file transfers between computers in your home, then 802. 11 g is the best the way to go.
 Two kinds of Wi-Fi § Commerical Wi-Fi § Services are available such as Internet cafes, Borders bookstore, and more. T-Mobile has many hotspots in all Borders and Starbucks. § Free Wi-Fi § Many members of local governments have joined with local community groups to help expand free Wi-Fi networks. Some community groups built their Wi-Fi networks based on volunteer efforts and donations.
Two kinds of Wi-Fi § Commerical Wi-Fi § Services are available such as Internet cafes, Borders bookstore, and more. T-Mobile has many hotspots in all Borders and Starbucks. § Free Wi-Fi § Many members of local governments have joined with local community groups to help expand free Wi-Fi networks. Some community groups built their Wi-Fi networks based on volunteer efforts and donations.
 About Wi-Fi revolution § § § Consultants from Pyramid Research predicted that more Americans would use Wi-Fi than cellular networks by 2007. Last year, approximately 30. 2 million Americans used Wi-Fi, according to Pyramid comparing with 213 million mobile-phone customers. Demand for Wi-Fi is increasing. However, the pace shows signs of slowdown.
About Wi-Fi revolution § § § Consultants from Pyramid Research predicted that more Americans would use Wi-Fi than cellular networks by 2007. Last year, approximately 30. 2 million Americans used Wi-Fi, according to Pyramid comparing with 213 million mobile-phone customers. Demand for Wi-Fi is increasing. However, the pace shows signs of slowdown.
 RADIUS l l Stands for: Remote Dial In User Service The Certificates are used to authenticate the user’s computer and to authenticate the RADIUS server.
RADIUS l l Stands for: Remote Dial In User Service The Certificates are used to authenticate the user’s computer and to authenticate the RADIUS server.
 Deployment Diagram l This diagram shows how the user’s wireless device will connect through the wireless access point. The credentials will then be sent from the access point to the radius server which will verify the user information using the Network Information Service (NIS) server. Upon verification in the NIS server the user acceptance will be passed back up to the RADIUS server then back up to the access point which will put the user back on the network. The user will then be allowed to do a DHCP request for an IP address and the DHCP server will respond.
Deployment Diagram l This diagram shows how the user’s wireless device will connect through the wireless access point. The credentials will then be sent from the access point to the radius server which will verify the user information using the Network Information Service (NIS) server. Upon verification in the NIS server the user acceptance will be passed back up to the RADIUS server then back up to the access point which will put the user back on the network. The user will then be allowed to do a DHCP request for an IP address and the DHCP server will respond.
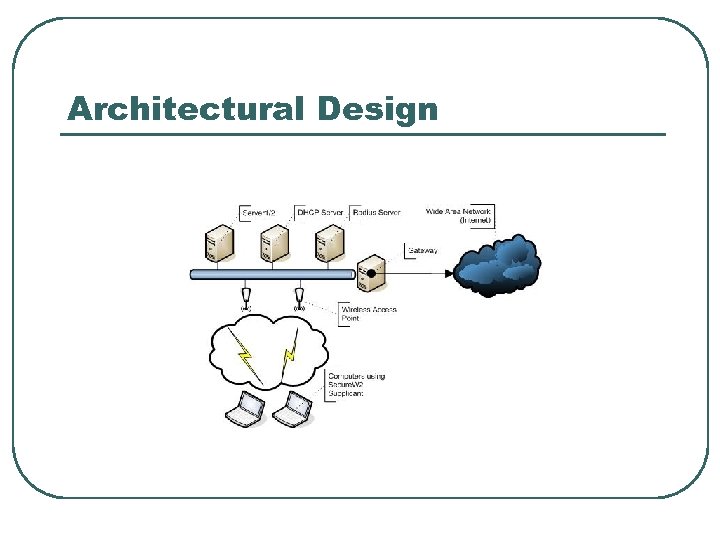 Architectural Design
Architectural Design
 Radiusd. conf l l The radiusd. conf file is the main configuration file for the Free. Radius Server radiusd. conf file. • Port =1812 #sets the port to listen on to 1812 • Log_auth = yes #sets the server to log authentication requests
Radiusd. conf l l The radiusd. conf file is the main configuration file for the Free. Radius Server radiusd. conf file. • Port =1812 #sets the port to listen on to 1812 • Log_auth = yes #sets the server to log authentication requests
 Clients. conf l The clients. conf file is a configuration file for the Free. Radius server that establishes what clients can connect to the radius server. l The following are the lines that were modified in the client. conf file to allow for the single test access point to be a client as well as the local host to be a client for testing. • • client [134. 198. 161. 212]{ secret = cmps 354 shortname = WAP 354 } client localhost{ secret = cmps 354 shortname = lh }
Clients. conf l The clients. conf file is a configuration file for the Free. Radius server that establishes what clients can connect to the radius server. l The following are the lines that were modified in the client. conf file to allow for the single test access point to be a client as well as the local host to be a client for testing. • • client [134. 198. 161. 212]{ secret = cmps 354 shortname = WAP 354 } client localhost{ secret = cmps 354 shortname = lh }
 Eap. conf l l The eap. conf file is a file that handles the configuration for the EAP protocols in Free. Radius. The following lines have to be adjusted. • • • default_eap_type = tls #tls is the authentication form that is being used #The following is from the tls module private_key_password = private_key_file = ${raddbdir}/certs/serverkey_cert. pem certificate_file = ${raddbdir}/certs/serverkey_cert. pem CA_file = /usr/local/openssl/cmps. CA/cacert. pem dhfile = /dev/null #link to a built in null location random_file = /dev/urandom #link to a built in random number generator #The following is from the ttls module #default_eap_type = copy_request_to_tunnel = yes use_tunnled_reply = yes
Eap. conf l l The eap. conf file is a file that handles the configuration for the EAP protocols in Free. Radius. The following lines have to be adjusted. • • • default_eap_type = tls #tls is the authentication form that is being used #The following is from the tls module private_key_password = private_key_file = ${raddbdir}/certs/serverkey_cert. pem certificate_file = ${raddbdir}/certs/serverkey_cert. pem CA_file = /usr/local/openssl/cmps. CA/cacert. pem dhfile = /dev/null #link to a built in null location random_file = /dev/urandom #link to a built in random number generator #The following is from the ttls module #default_eap_type = copy_request_to_tunnel = yes use_tunnled_reply = yes
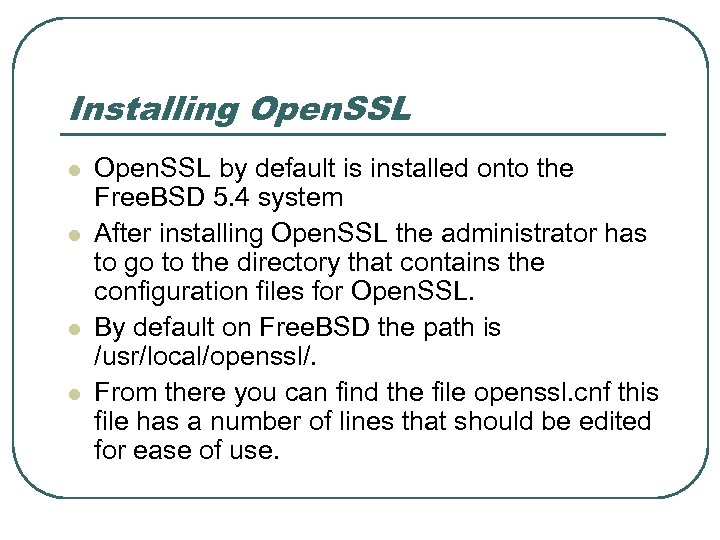 Installing Open. SSL l l Open. SSL by default is installed onto the Free. BSD 5. 4 system After installing Open. SSL the administrator has to go to the directory that contains the configuration files for Open. SSL. By default on Free. BSD the path is /usr/local/openssl/. From there you can find the file openssl. cnf this file has a number of lines that should be edited for ease of use.
Installing Open. SSL l l Open. SSL by default is installed onto the Free. BSD 5. 4 system After installing Open. SSL the administrator has to go to the directory that contains the configuration files for Open. SSL. By default on Free. BSD the path is /usr/local/openssl/. From there you can find the file openssl. cnf this file has a number of lines that should be edited for ease of use.
 openssl. cnf l l lines that should be edited for ease of use. # These are some of the lines that should be modified • [ CA_default ] dir =. /cmps. CA # Where the CA is kept#further downcountry. Name_default = US state. Or. Province. Name_default =Pennsylvania 0. organization. Name_default = Computing Science Department
openssl. cnf l l lines that should be edited for ease of use. # These are some of the lines that should be modified • [ CA_default ] dir =. /cmps. CA # Where the CA is kept#further downcountry. Name_default = US state. Or. Province. Name_default =Pennsylvania 0. organization. Name_default = Computing Science Department
 xpextensions l l After editing the defaults of the openssl. cnf file another file must be created because these certificates are going to be used on Microsoft Windows XP computers. The file should be created and named xpextensions.
xpextensions l l After editing the defaults of the openssl. cnf file another file must be created because these certificates are going to be used on Microsoft Windows XP computers. The file should be created and named xpextensions.
![xpextensions l The following lines should be added to xpextensions: • [ xpclient_ext]extended. Key. xpextensions l The following lines should be added to xpextensions: • [ xpclient_ext]extended. Key.](https://present5.com/presentation/9b0867a96ccfe18ddb478c23cd4bb387/image-19.jpg) xpextensions l The following lines should be added to xpextensions: • [ xpclient_ext]extended. Key. Usage = • 1. 3. 6. 1. 5. 5. 7. 3. 2 [ xpserver_ext ]extended. Key. Usage = 1. 3. 6. 1. 5. 5. 7. 3. 1
xpextensions l The following lines should be added to xpextensions: • [ xpclient_ext]extended. Key. Usage = • 1. 3. 6. 1. 5. 5. 7. 3. 2 [ xpserver_ext ]extended. Key. Usage = 1. 3. 6. 1. 5. 5. 7. 3. 1
 Creating a Certificate Authority l To create a certificate authority you must edit the CA. sh file in the openssl/misc directory • CATOP=. /cmps. CA #this path should match the dir specified in #openssl. cnf
Creating a Certificate Authority l To create a certificate authority you must edit the CA. sh file in the openssl/misc directory • CATOP=. /cmps. CA #this path should match the dir specified in #openssl. cnf
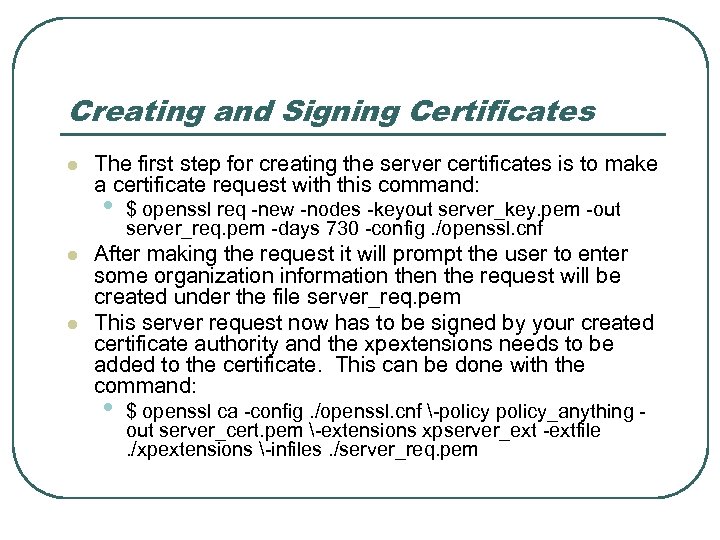 Creating and Signing Certificates l The first step for creating the server certificates is to make a certificate request with this command: • l l $ openssl req -new -nodes -keyout server_key. pem -out server_req. pem -days 730 -config. /openssl. cnf After making the request it will prompt the user to enter some organization information the request will be created under the file server_req. pem This server request now has to be signed by your created certificate authority and the xpextensions needs to be added to the certificate. This can be done with the command: • $ openssl ca -config. /openssl. cnf -policy_anything out server_cert. pem -extensions xpserver_ext -extfile. /xpextensions -infiles. /server_req. pem
Creating and Signing Certificates l The first step for creating the server certificates is to make a certificate request with this command: • l l $ openssl req -new -nodes -keyout server_key. pem -out server_req. pem -days 730 -config. /openssl. cnf After making the request it will prompt the user to enter some organization information the request will be created under the file server_req. pem This server request now has to be signed by your created certificate authority and the xpextensions needs to be added to the certificate. This can be done with the command: • $ openssl ca -config. /openssl. cnf -policy_anything out server_cert. pem -extensions xpserver_ext -extfile. /xpextensions -infiles. /server_req. pem
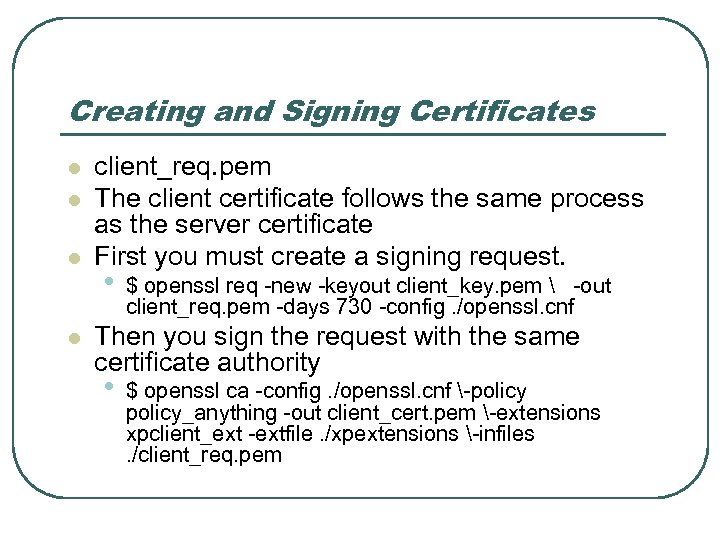 Creating and Signing Certificates l l client_req. pem The client certificate follows the same process as the server certificate First you must create a signing request. • $ openssl req -new -keyout client_key. pem -out client_req. pem -days 730 -config. /openssl. cnf Then you sign the request with the same certificate authority • $ openssl ca -config. /openssl. cnf -policy_anything -out client_cert. pem -extensions xpclient_ext -extfile. /xpextensions -infiles. /client_req. pem
Creating and Signing Certificates l l client_req. pem The client certificate follows the same process as the server certificate First you must create a signing request. • $ openssl req -new -keyout client_key. pem -out client_req. pem -days 730 -config. /openssl. cnf Then you sign the request with the same certificate authority • $ openssl ca -config. /openssl. cnf -policy_anything -out client_cert. pem -extensions xpclient_ext -extfile. /xpextensions -infiles. /client_req. pem
 Creating and Signing Certificates l l Finally after you have created your signed certificate in the client_cert. pem you have to convert it to a. p 12 file for windows machines. You can do that with this command openssl pkcs 12 -export -in client_cert. pem -inkey client_key. pem out client_cert. p 12 -clcerts
Creating and Signing Certificates l l Finally after you have created your signed certificate in the client_cert. pem you have to convert it to a. p 12 file for windows machines. You can do that with this command openssl pkcs 12 -export -in client_cert. pem -inkey client_key. pem out client_cert. p 12 -clcerts
 Wireless Access Points l l The Wireless Access points need to be configured for the network Set static IP IP address should be reflected in the clients. conf file of the radius directory The SSID needs to be modified to “CMPS”
Wireless Access Points l l The Wireless Access points need to be configured for the network Set static IP IP address should be reflected in the clients. conf file of the radius directory The SSID needs to be modified to “CMPS”
 Wireless Access Points
Wireless Access Points
 User Interface Design l l l Secure. W 2 Supplicant The Secure. W 2 client is a WPA supplicant that installs onto the users Windows XP computer. This is used to authenticate the user through the RADIUS server using the TTLS protocol.
User Interface Design l l l Secure. W 2 Supplicant The Secure. W 2 client is a WPA supplicant that installs onto the users Windows XP computer. This is used to authenticate the user through the RADIUS server using the TTLS protocol.
 Secure. W 2 Installation l l The Secure. W 2 client can be downloaded from http: //www. securew 2. com/uk/download/i ndex. htm
Secure. W 2 Installation l l The Secure. W 2 client can be downloaded from http: //www. securew 2. com/uk/download/i ndex. htm
 Secure. W 2 Installation
Secure. W 2 Installation
 Secure. W 2 Installation
Secure. W 2 Installation
 Configuration l l Secure. W 2 allows for PAP authentication Secure. W 2 also allows you to input a user id and password combination for quick reconnecting to the network This can be used on a personal computer The configuration of the Secure. W 2 Client is shown below
Configuration l l Secure. W 2 allows for PAP authentication Secure. W 2 also allows you to input a user id and password combination for quick reconnecting to the network This can be used on a personal computer The configuration of the Secure. W 2 Client is shown below


 Resources § § § http: //en. wikipedia. org/wiki/Wi. Fi http: //www. wi-fihotspotlist. com/ http: //www. wififreespot. com/pa. html http: //www. wifimaps. com/ http: //www. cs. scranton. edu/%7 Etjm 2 f/sc hool/cmps 490/System. Documentation. do c#_Toc 121278389
Resources § § § http: //en. wikipedia. org/wiki/Wi. Fi http: //www. wi-fihotspotlist. com/ http: //www. wififreespot. com/pa. html http: //www. wifimaps. com/ http: //www. cs. scranton. edu/%7 Etjm 2 f/sc hool/cmps 490/System. Documentation. do c#_Toc 121278389


