b2b4528f3f7277f5eb89b3b880387ec9.ppt
- Количество слайдов: 32
Wireless & Mobile Systems n IEEE 802. 11 WLAN Network Architecture and Design 1
The wireless revolution n n NO WIRES Goals n n One Wireless standard for at Home, in the Office, and on the Move. Interoperability with wired networks Security, QOS, Roaming users. Usage: n n n Entertainment (films, shows, gaming, music, . . ) Information (Internet, . . ) E-commerce (secure home shopping, . . ) Social contacts (email, voice, interest groups, . . ) PC (documents, data, printing, scanner, server, . . . ) Control (A/V devices, security, . . ) Network Architecture and Design 2
IEEE 802. 11 vs. 802. 3 n n n Similarity n Same LLC (Logical Link Control). There in no differences for upper layer protocol Differences n WLAN is not private (not protected) n WLAN is exposed to more distractions (environment problems) n Reflectors n Changes in strength on the Rx signal in small position change n Moving object can change the wave signal n Other infrared devices overlap the Tx path. n Etc… n Mobility n The WLAN user can move from one place to another – big advantage. But it cause internal complexity. Roaming between access points and between different IP networks (Mobile IP or DHCP). n Servers and services need to be changed (Printer, Proxy server, file server, etc…) n IEEE 802. 11 PHY has NO collision detection n IEEE 802. 3 use collision detection algorithm. n IEEE 802. 11 use collision avoidance algorithm. Translation of 802. 11 802. 3 is not on the scope of the IEEE 802. 11 spec’ Network Architecture and Design 3
Architecture Network Architecture and Design 4
WLAN 802. 11 requirements n n n Mobility Tolerant to faults Support: n n Small and transient (temporary) Networks Large [semi-]permanent Networks Power saving without losing network connectivity. Allow all network protocols to run over WLAN without any considerations. Network Architecture and Design 5
Wireless Network Overview n n APs (access points) and stations BSS (Basic service set) DS (Distribution system) and ESS (Extended Service Set) Ad-hoc networks Network Architecture and Design 6
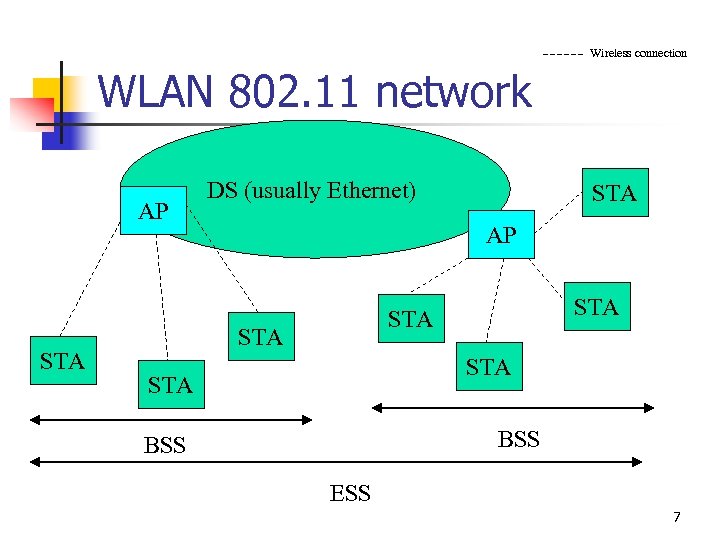
Wireless connection WLAN 802. 11 network AP STA DS (usually Ethernet) STA AP STA STA STA BSS ESS 7
APs & stations n n Each node in the IEEE 802. 11 network may be station (STA) or and access point In definition AP contains a station. Network Architecture and Design 8
BSS n n n Set of arbitrary stations, and one AP Station have to be associated with the AP in order to be part of the BSS Local relay function through the AP. n n Advantage : When station is in power saving mode the AP will buffer traffic for the (sleeping) mobile station. Disadvantage: Consume twice bandwidth Network Architecture and Design 9
DS Logical communication between the APs n The DS is the backbone of the WLAN and may be constructed over wired or wireless connection. n The communication between the APs over the DS, is in the scope of TGf (IAPP – inter access point protocol). n The connection of the several BSS networks forms Extended Service Set (ESS) n Network Architecture and Design 10
ESS n n Group more than one BSS networks The APs communicate among themselves to form relay between the BSS domains, through abstract distribution system (DS) Network Architecture and Design 11
Ad-hoc networks (IBSS) n n Temporary set of stations Forming as ad-hoc network – an independent BSS (IBSS), means that there is no connection to wired network n n n No AP No relay function (direct connection) Simple setup Network Architecture and Design 12
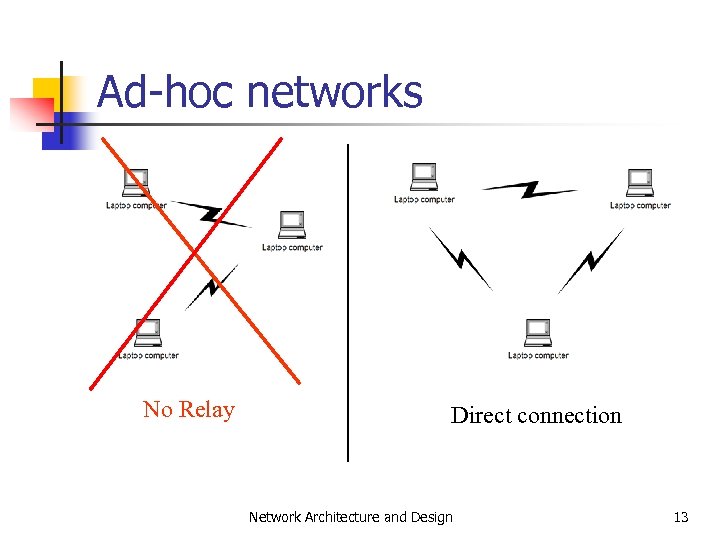
Ad-hoc networks No Relay Direct connection Network Architecture and Design 13
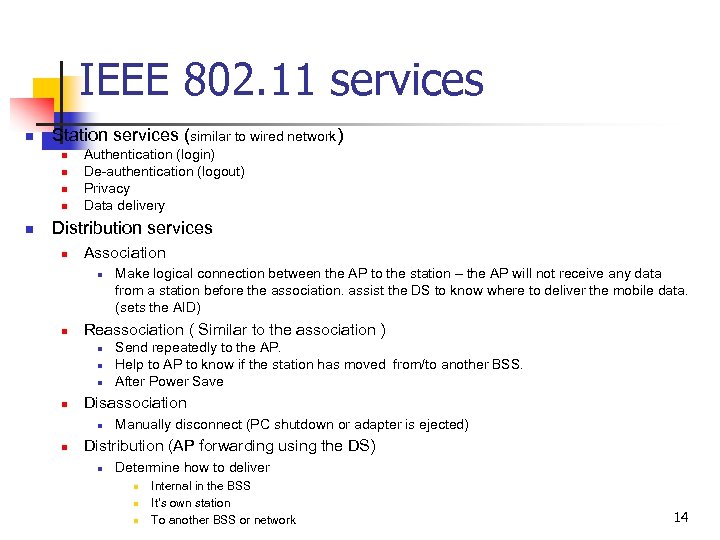
IEEE 802. 11 services n Station services (similar to wired network) n n n Authentication (login) De-authentication (logout) Privacy Data delivery Distribution services n Association n n Reassociation ( Similar to the association ) n n Send repeatedly to the AP. Help to AP to know if the station has moved from/to another BSS. After Power Save Disassociation n n Make logical connection between the AP to the station – the AP will not receive any data from a station before the association. assist the DS to know where to deliver the mobile data. (sets the AID) Manually disconnect (PC shutdown or adapter is ejected) Distribution (AP forwarding using the DS) n Determine how to deliver n n n Internal in the BSS It’s own station To another BSS or network 14
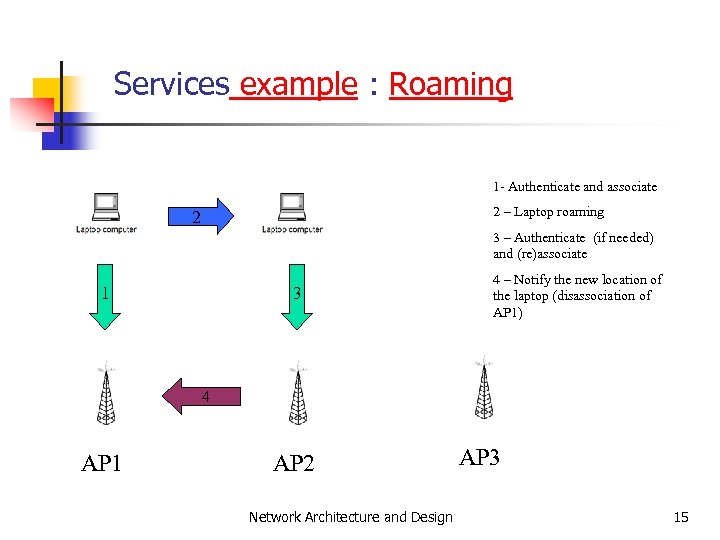
Services example : Roaming 1 - Authenticate and associate 2 – Laptop roaming 2 3 – Authenticate (if needed) and (re)associate 1 3 4 – Notify the new location of the laptop (disassociation of AP 1) 4 AP 1 AP 2 Network Architecture and Design AP 3 15
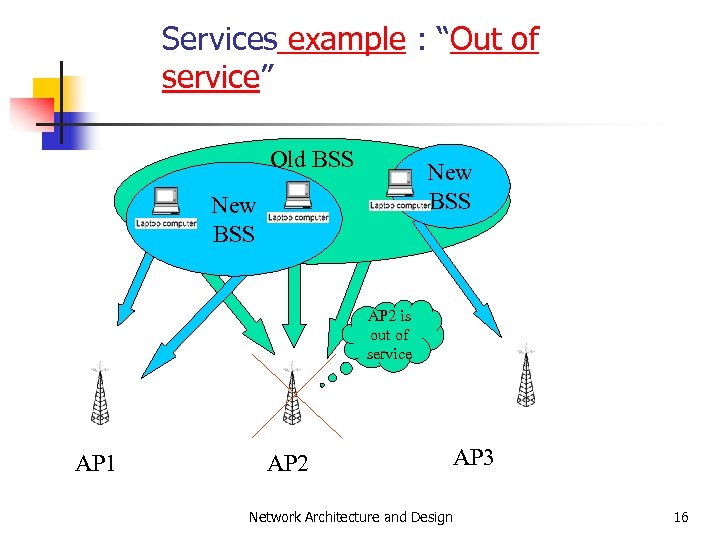
Services example : “Out of service” Old BSS New BSS AP 2 is out of service AP 1 AP 2 Network Architecture and Design AP 3 16
Medium Access Control (MAC) Layer Network Architecture and Design 17
MAC functionalities n n n Reliability of data delivery service Control of shared WL network Frame Types (informational section) Management Privacy service (Wired Equivalent Privacy WEP) Network Architecture and Design 18
Reliability of data delivery service n Problems to solve n n n The air is noisy and unreliable media The Hidden Node problem Solutions : Frame Exchange Protocol n n n Every frame is acknowledged (ACK) CTS & RTS frames Fragment long data frames Network Architecture and Design 19
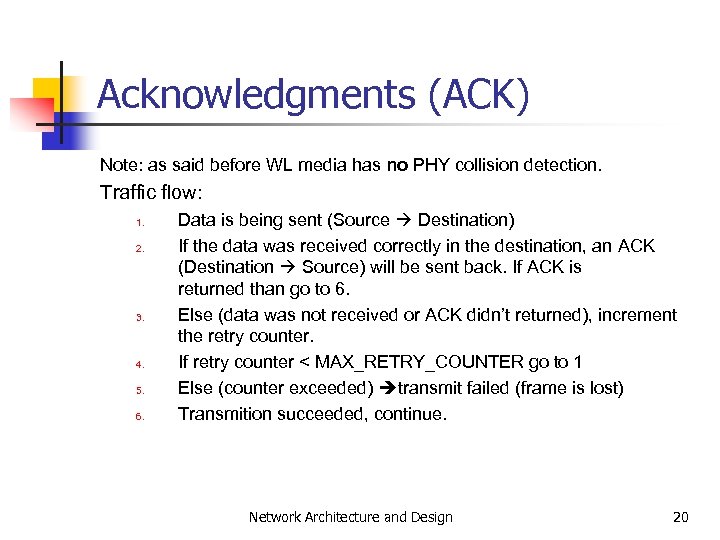
Acknowledgments (ACK) Note: as said before WL media has no PHY collision detection. Traffic flow: 1. 2. 3. 4. 5. 6. Data is being sent (Source Destination) If the data was received correctly in the destination, an ACK (Destination Source) will be sent back. If ACK is returned than go to 6. Else (data was not received or ACK didn’t returned), increment the retry counter. If retry counter < MAX_RETRY_COUNTER go to 1 Else (counter exceeded) transmit failed (frame is lost) Transmition succeeded, continue. Network Architecture and Design 20
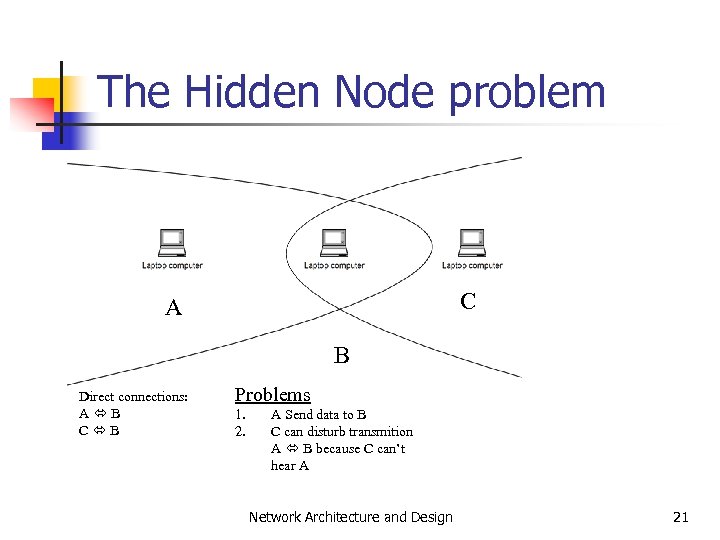
The Hidden Node problem C A B Direct connections: A B C B Problems 1. 2. A Send data to B C can disturb transmition A B because C can’t hear A Network Architecture and Design 21
Solving the Hidden Node problem n Request To Send (RTS): n n n Source announcing its transmition. Will cause its neighborhood stop transmitting Clear To Send (CTS): n n Destination received the RTS and announce the source to send the data. Will cause its (the destination) neighborhood stop transmitting. Network Architecture and Design 22
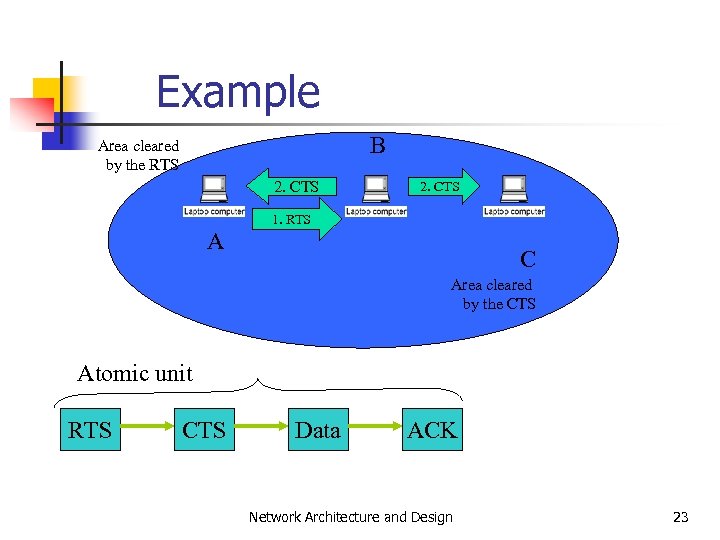
Example B Area cleared by the RTS 2. CTS 1. RTS A C Area cleared by the CTS Atomic unit RTS CTS Data ACK Network Architecture and Design 23
Control of shared WL network MAC access mechanism n Distributed Coordination Function n n Based on the IEEE 802. 3 Ethernet access mechanism. Point Coordination Function n n Token based mechanism (one Point Coordinator in the BSS at the AP, that gives the ‘token’ to speak) Not relevant to WLAN implementations. Network Architecture and Design 24
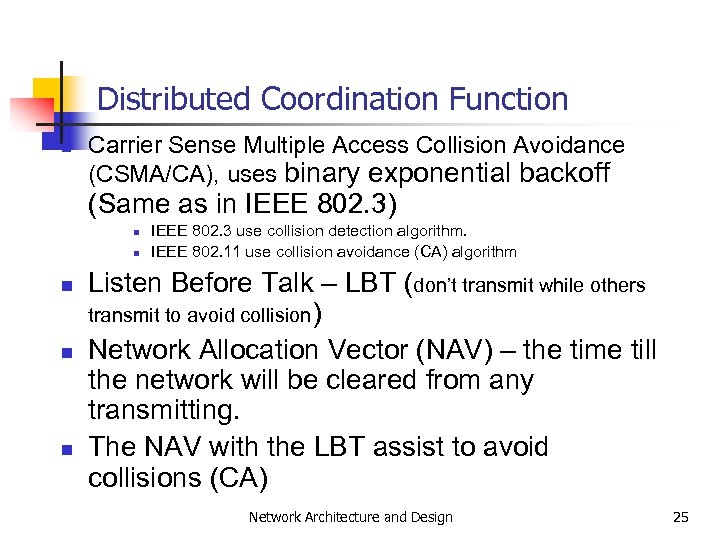
Distributed Coordination Function n Carrier Sense Multiple Access Collision Avoidance (CSMA/CA), uses binary exponential backoff (Same as in IEEE 802. 3) n n n IEEE 802. 3 use collision detection algorithm. IEEE 802. 11 use collision avoidance (CA) algorithm Listen Before Talk – LBT (don’t transmit while others transmit to avoid collision) Network Allocation Vector (NAV) – the time till the network will be cleared from any transmitting. The NAV with the LBT assist to avoid collisions (CA) Network Architecture and Design 25
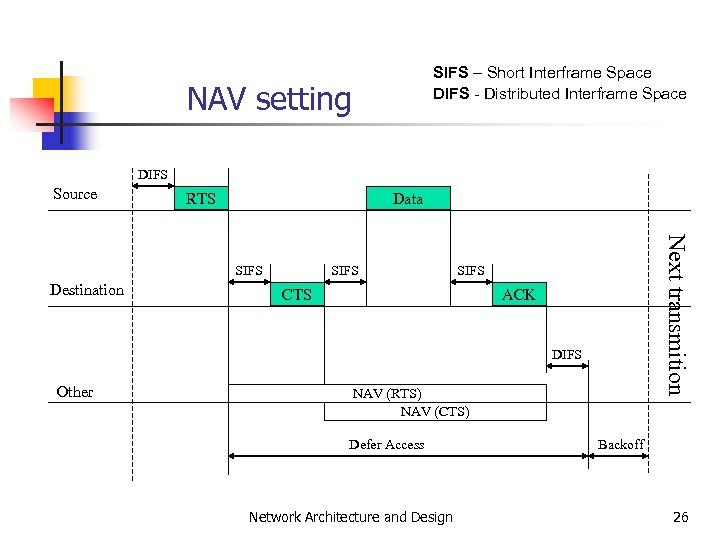
SIFS – Short Interframe Space DIFS - Distributed Interframe Space NAV setting DIFS Source RTS Data Destination SIFS Next transmition SIFS CTS ACK DIFS Other NAV (RTS) NAV (CTS) Defer Access Network Architecture and Design Backoff 26
Fragmentation n Needed to decrease the probability of the surrounding destruction (microwave ovens, etc…) by splitting frame to smaller parts It is possible to tune the size from which the frame will be fragmented by a MIB (management Information Base) parameter name dot 11 Fragmentation. Treshold By default no fragmentation is being done. Network Architecture and Design 27
Privacy 1. 2. 3. 4. Any one with antenna can here you Wired Equivalent Privacy (WEP) Only the data is encrypted (the MAC layer is not changed after the encryption). WEP doesn’t protect from traffic analysis. RC 4 – symmetric stream cipher algorithm with variable key length is used (same key and algorithm for encryption and decryption) Network Architecture and Design 28
WEP details Two methods: n Default keys (up to four) will be shared in the BSS or the whole ESS. n n n It is useful to learn some default keys once The keys can be revealed more easily. One-To-One key mapping. Network Architecture and Design 29
MAC Management We need management environment in order to solve those problems: 1. Noisy media n n 2. Every one can connect to the WLAN n 3. 4. Many users on air Destructions from other WLANs Security issues Mobility Power management Network Architecture and Design 30
Open Issues n n n Load balancing between APs IP roaming problems (In BSS & In IBSS) “Tower of Babel” n n ~40 802. 11 different vendors No argument on: n n QOS Roaming Etc… PAN (connect from public area to remote ISP with security) Network Architecture and Design 31
End of Seventh Lecture Network Architecture and Design 32
b2b4528f3f7277f5eb89b3b880387ec9.ppt