7664f9ee276a56e16a4a60370cc7b85b.ppt
- Количество слайдов: 20
 Welcome to Rutgers! 1 st Rutgers-Helsinki Ph. D. Student Workshop on Spontaneous Networking Liviu Iftode Department of Computer Science Rutgers University
Welcome to Rutgers! 1 st Rutgers-Helsinki Ph. D. Student Workshop on Spontaneous Networking Liviu Iftode Department of Computer Science Rutgers University
 My talk… u Proto-History u Workshop Overview u Disco Lab
My talk… u Proto-History u Workshop Overview u Disco Lab
 The time before the workshop u Jan 2004, ANWIRE Winter School on Middleware in Cyprus (organized by M. Dikaiakos): meeting Oriana u Summer 2004: Oriana intern in Disco Lab u October 2004: NSF supplemental award for international collaboration u August 2005: visit to University of Helsinki u November 2005: Kimmo at Rutgers
The time before the workshop u Jan 2004, ANWIRE Winter School on Middleware in Cyprus (organized by M. Dikaiakos): meeting Oriana u Summer 2004: Oriana intern in Disco Lab u October 2004: NSF supplemental award for international collaboration u August 2005: visit to University of Helsinki u November 2005: Kimmo at Rutgers
 Spontaneous Networking u Services over ad-hoc networks u An application-oriented approach to ad-hoc networking u Location-awareness u Loosely defined boundaries u Unplanned networks, unexpected users u Examples n Ad-hoc networks of smart phones n Vehicular networks
Spontaneous Networking u Services over ad-hoc networks u An application-oriented approach to ad-hoc networking u Location-awareness u Loosely defined boundaries u Unplanned networks, unexpected users u Examples n Ad-hoc networks of smart phones n Vehicular networks
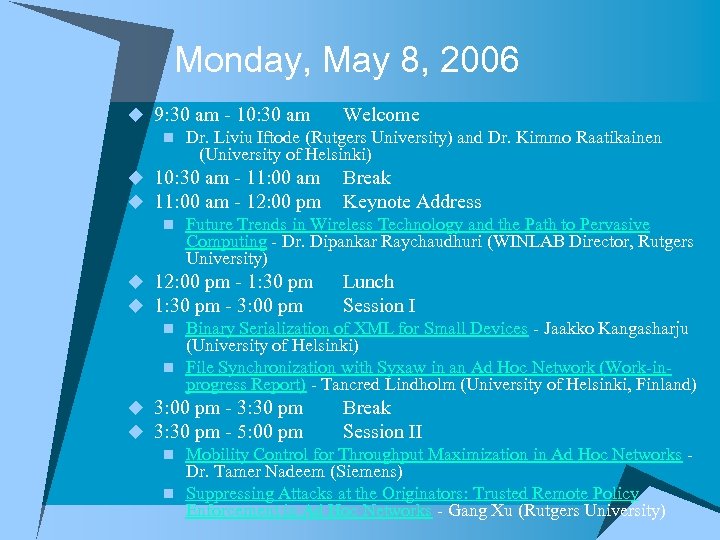 Monday, May 8, 2006 u 9: 30 am - 10: 30 am Welcome n Dr. Liviu Iftode (Rutgers University) and Dr. Kimmo Raatikainen (University of Helsinki) u 10: 30 am - 11: 00 am Break u 11: 00 am - 12: 00 pm Keynote Address n Future Trends in Wireless Technology and the Path to Pervasive Computing - Dr. Dipankar Raychaudhuri (WINLAB Director, Rutgers University) u 12: 00 pm - 1: 30 pm Lunch u 1: 30 pm - 3: 00 pm Session I n Binary Serialization of XML for Small Devices - Jaakko Kangasharju (University of Helsinki) n File Synchronization with Syxaw in an Ad Hoc Network (Work-inprogress Report) - Tancred Lindholm (University of Helsinki, Finland) u 3: 00 pm - 3: 30 pm Break u 3: 30 pm - 5: 00 pm Session II n Mobility Control for Throughput Maximization in Ad Hoc Networks - Dr. Tamer Nadeem (Siemens) n Suppressing Attacks at the Originators: Trusted Remote Policy Enforcement in Ad Hoc Networks - Gang Xu (Rutgers University)
Monday, May 8, 2006 u 9: 30 am - 10: 30 am Welcome n Dr. Liviu Iftode (Rutgers University) and Dr. Kimmo Raatikainen (University of Helsinki) u 10: 30 am - 11: 00 am Break u 11: 00 am - 12: 00 pm Keynote Address n Future Trends in Wireless Technology and the Path to Pervasive Computing - Dr. Dipankar Raychaudhuri (WINLAB Director, Rutgers University) u 12: 00 pm - 1: 30 pm Lunch u 1: 30 pm - 3: 00 pm Session I n Binary Serialization of XML for Small Devices - Jaakko Kangasharju (University of Helsinki) n File Synchronization with Syxaw in an Ad Hoc Network (Work-inprogress Report) - Tancred Lindholm (University of Helsinki, Finland) u 3: 00 pm - 3: 30 pm Break u 3: 30 pm - 5: 00 pm Session II n Mobility Control for Throughput Maximization in Ad Hoc Networks - Dr. Tamer Nadeem (Siemens) n Suppressing Attacks at the Originators: Trusted Remote Policy Enforcement in Ad Hoc Networks - Gang Xu (Rutgers University)
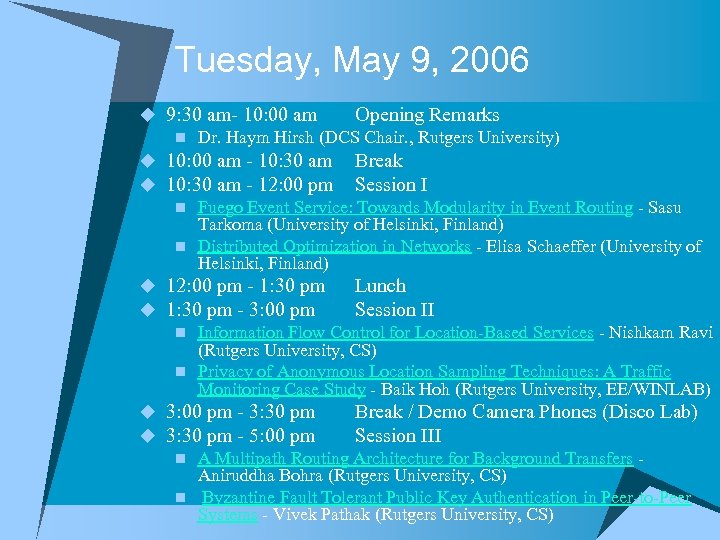 Tuesday, May 9, 2006 u 9: 30 am- 10: 00 am Opening Remarks n Dr. Haym Hirsh (DCS Chair. , Rutgers University) u 10: 00 am - 10: 30 am Break u 10: 30 am - 12: 00 pm Session I n Fuego Event Service: Towards Modularity in Event Routing - Sasu Tarkoma (University of Helsinki, Finland) n Distributed Optimization in Networks - Elisa Schaeffer (University of Helsinki, Finland) u 12: 00 pm - 1: 30 pm Lunch u 1: 30 pm - 3: 00 pm Session II n Information Flow Control for Location-Based Services - Nishkam Ravi (Rutgers University, CS) n Privacy of Anonymous Location Sampling Techniques: A Traffic Monitoring Case Study - Baik Hoh (Rutgers University, EE/WINLAB) u 3: 00 pm - 3: 30 pm Break / Demo Camera Phones (Disco Lab) u 3: 30 pm - 5: 00 pm Session III n A Multipath Routing Architecture for Background Transfers - Aniruddha Bohra (Rutgers University, CS) n Byzantine Fault Tolerant Public Key Authentication in Peer-to-Peer Systems - Vivek Pathak (Rutgers University, CS)
Tuesday, May 9, 2006 u 9: 30 am- 10: 00 am Opening Remarks n Dr. Haym Hirsh (DCS Chair. , Rutgers University) u 10: 00 am - 10: 30 am Break u 10: 30 am - 12: 00 pm Session I n Fuego Event Service: Towards Modularity in Event Routing - Sasu Tarkoma (University of Helsinki, Finland) n Distributed Optimization in Networks - Elisa Schaeffer (University of Helsinki, Finland) u 12: 00 pm - 1: 30 pm Lunch u 1: 30 pm - 3: 00 pm Session II n Information Flow Control for Location-Based Services - Nishkam Ravi (Rutgers University, CS) n Privacy of Anonymous Location Sampling Techniques: A Traffic Monitoring Case Study - Baik Hoh (Rutgers University, EE/WINLAB) u 3: 00 pm - 3: 30 pm Break / Demo Camera Phones (Disco Lab) u 3: 30 pm - 5: 00 pm Session III n A Multipath Routing Architecture for Background Transfers - Aniruddha Bohra (Rutgers University, CS) n Byzantine Fault Tolerant Public Key Authentication in Peer-to-Peer Systems - Vivek Pathak (Rutgers University, CS)
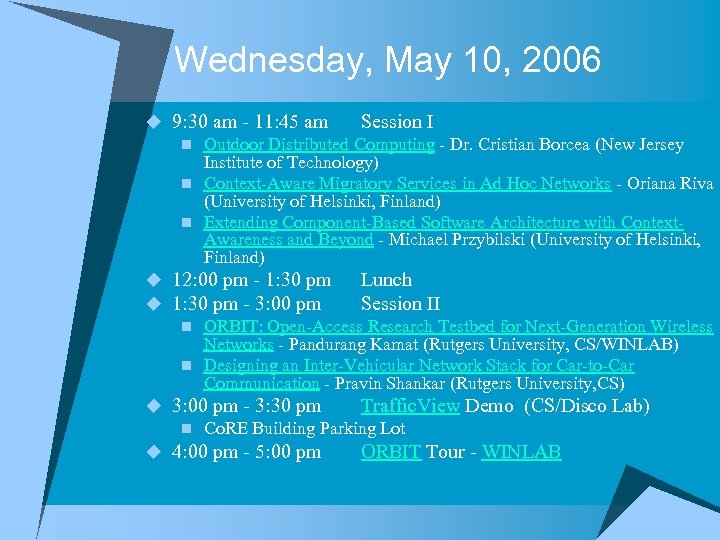 Wednesday, May 10, 2006 u 9: 30 am - 11: 45 am Session I n Outdoor Distributed Computing - Dr. Cristian Borcea (New Jersey Institute of Technology) n Context-Aware Migratory Services in Ad Hoc Networks - Oriana Riva (University of Helsinki, Finland) n Extending Component-Based Software Architecture with Context. Awareness and Beyond - Michael Przybilski (University of Helsinki, Finland) u 12: 00 pm - 1: 30 pm Lunch u 1: 30 pm - 3: 00 pm Session II n ORBIT: Open-Access Research Testbed for Next-Generation Wireless Networks - Pandurang Kamat (Rutgers University, CS/WINLAB) n Designing an Inter-Vehicular Network Stack for Car-to-Car Communication - Pravin Shankar (Rutgers University, CS) u 3: 00 pm - 3: 30 pm Traffic. View Demo (CS/Disco Lab) n Co. RE Building Parking Lot u 4: 00 pm - 5: 00 pm ORBIT Tour - WINLAB
Wednesday, May 10, 2006 u 9: 30 am - 11: 45 am Session I n Outdoor Distributed Computing - Dr. Cristian Borcea (New Jersey Institute of Technology) n Context-Aware Migratory Services in Ad Hoc Networks - Oriana Riva (University of Helsinki, Finland) n Extending Component-Based Software Architecture with Context. Awareness and Beyond - Michael Przybilski (University of Helsinki, Finland) u 12: 00 pm - 1: 30 pm Lunch u 1: 30 pm - 3: 00 pm Session II n ORBIT: Open-Access Research Testbed for Next-Generation Wireless Networks - Pandurang Kamat (Rutgers University, CS/WINLAB) n Designing an Inter-Vehicular Network Stack for Car-to-Car Communication - Pravin Shankar (Rutgers University, CS) u 3: 00 pm - 3: 30 pm Traffic. View Demo (CS/Disco Lab) n Co. RE Building Parking Lot u 4: 00 pm - 5: 00 pm ORBIT Tour - WINLAB
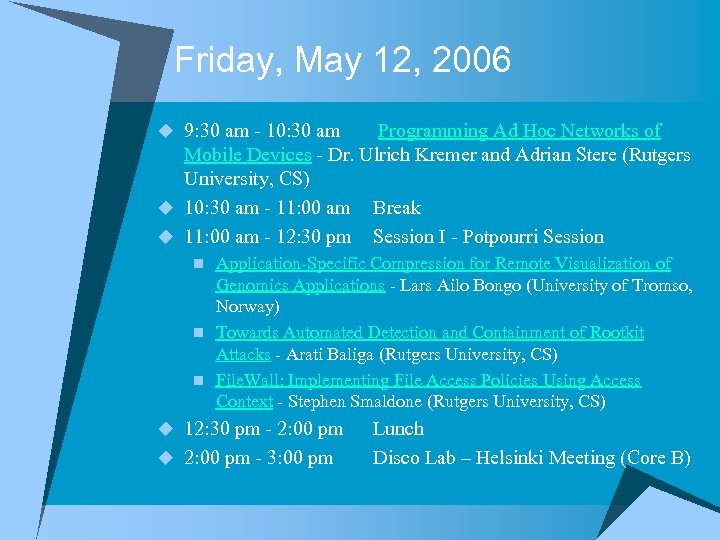 Friday, May 12, 2006 u 9: 30 am - 10: 30 am Programming Ad Hoc Networks of Mobile Devices - Dr. Ulrich Kremer and Adrian Stere (Rutgers University, CS) u 10: 30 am - 11: 00 am Break u 11: 00 am - 12: 30 pm Session I - Potpourri Session n Application-Specific Compression for Remote Visualization of Genomics Applications - Lars Ailo Bongo (University of Tromso, Norway) n Towards Automated Detection and Containment of Rootkit Attacks - Arati Baliga (Rutgers University, CS) n File. Wall: Implementing File Access Policies Using Access Context - Stephen Smaldone (Rutgers University, CS) u 12: 30 pm - 2: 00 pm u 2: 00 pm - 3: 00 pm Lunch Disco Lab – Helsinki Meeting (Core B)
Friday, May 12, 2006 u 9: 30 am - 10: 30 am Programming Ad Hoc Networks of Mobile Devices - Dr. Ulrich Kremer and Adrian Stere (Rutgers University, CS) u 10: 30 am - 11: 00 am Break u 11: 00 am - 12: 30 pm Session I - Potpourri Session n Application-Specific Compression for Remote Visualization of Genomics Applications - Lars Ailo Bongo (University of Tromso, Norway) n Towards Automated Detection and Containment of Rootkit Attacks - Arati Baliga (Rutgers University, CS) n File. Wall: Implementing File Access Policies Using Access Context - Stephen Smaldone (Rutgers University, CS) u 12: 30 pm - 2: 00 pm u 2: 00 pm - 3: 00 pm Lunch Disco Lab – Helsinki Meeting (Core B)
 Workshop Speakers u Rutgers, Computer Science n Disco Lab n Power and Energy Management Lab (EEL) u University of Helsinki, Computer Science u Rutgers. , WINLAB/ Electrical and Computer Engineering u New Jersey Institute of Technology u Siemens Corporate Research, Inc. u University of Tromso, Norway
Workshop Speakers u Rutgers, Computer Science n Disco Lab n Power and Energy Management Lab (EEL) u University of Helsinki, Computer Science u Rutgers. , WINLAB/ Electrical and Computer Engineering u New Jersey Institute of Technology u Siemens Corporate Research, Inc. u University of Tromso, Norway
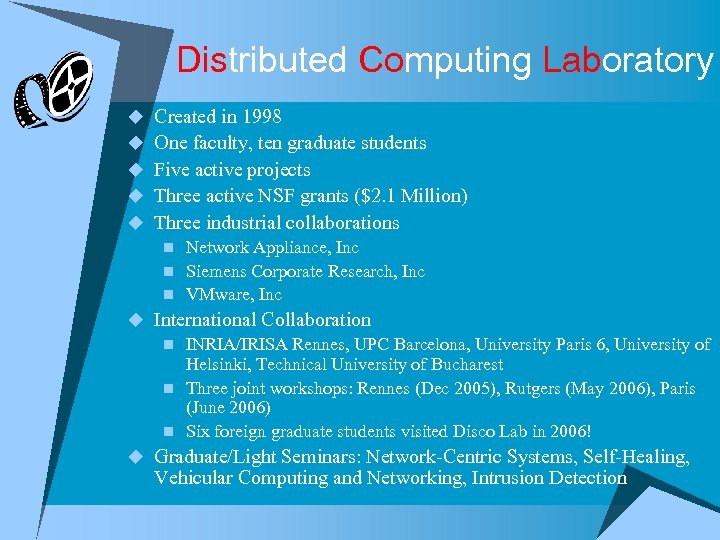 Distributed Computing Laboratory u Created in 1998 u One faculty, ten graduate students u Five active projects u Three active NSF grants ($2. 1 Million) u Three industrial collaborations n Network Appliance, Inc n Siemens Corporate Research, Inc n VMware, Inc u International Collaboration n INRIA/IRISA Rennes, UPC Barcelona, University Paris 6, University of Helsinki, Technical University of Bucharest n Three joint workshops: Rennes (Dec 2005), Rutgers (May 2006), Paris (June 2006) n Six foreign graduate students visited Disco Lab in 2006! u Graduate/Light Seminars: Network-Centric Systems, Self-Healing, Vehicular Computing and Networking, Intrusion Detection
Distributed Computing Laboratory u Created in 1998 u One faculty, ten graduate students u Five active projects u Three active NSF grants ($2. 1 Million) u Three industrial collaborations n Network Appliance, Inc n Siemens Corporate Research, Inc n VMware, Inc u International Collaboration n INRIA/IRISA Rennes, UPC Barcelona, University Paris 6, University of Helsinki, Technical University of Bucharest n Three joint workshops: Rennes (Dec 2005), Rutgers (May 2006), Paris (June 2006) n Six foreign graduate students visited Disco Lab in 2006! u Graduate/Light Seminars: Network-Centric Systems, Self-Healing, Vehicular Computing and Networking, Intrusion Detection
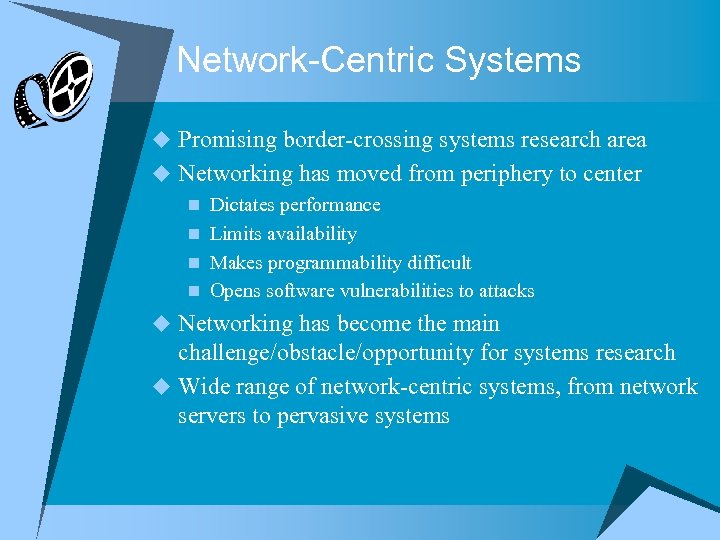 Network-Centric Systems u Promising border-crossing systems research area u Networking has moved from periphery to center n Dictates performance n Limits availability n Makes programmability difficult n Opens software vulnerabilities to attacks u Networking has become the main challenge/obstacle/opportunity for systems research u Wide range of network-centric systems, from network servers to pervasive systems
Network-Centric Systems u Promising border-crossing systems research area u Networking has moved from periphery to center n Dictates performance n Limits availability n Makes programmability difficult n Opens software vulnerabilities to attacks u Networking has become the main challenge/obstacle/opportunity for systems research u Wide range of network-centric systems, from network servers to pervasive systems
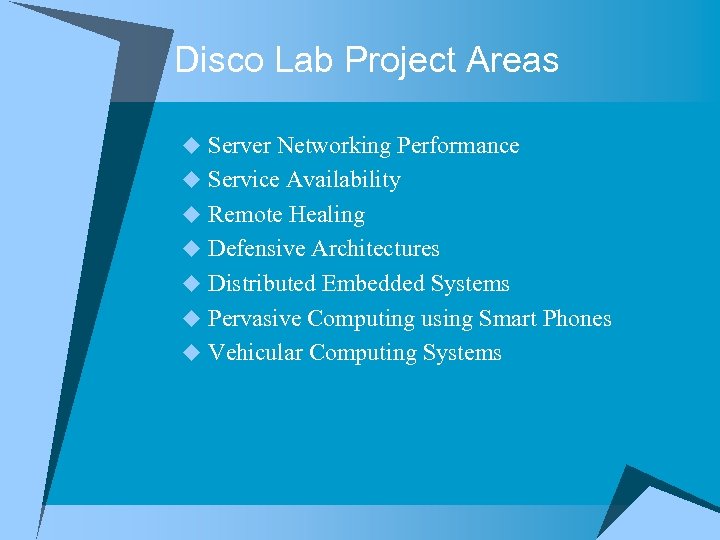 Disco Lab Project Areas u Server Networking Performance u Service Availability u Remote Healing u Defensive Architectures u Distributed Embedded Systems u Pervasive Computing using Smart Phones u Vehicular Computing Systems
Disco Lab Project Areas u Server Networking Performance u Service Availability u Remote Healing u Defensive Architectures u Distributed Embedded Systems u Pervasive Computing using Smart Phones u Vehicular Computing Systems
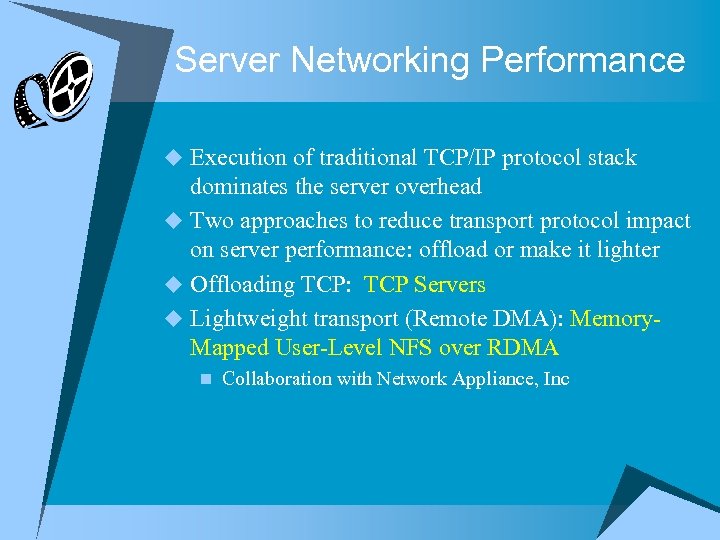 Server Networking Performance u Execution of traditional TCP/IP protocol stack dominates the server overhead u Two approaches to reduce transport protocol impact on server performance: offload or make it lighter u Offloading TCP: TCP Servers u Lightweight transport (Remote DMA): Memory. Mapped User-Level NFS over RDMA n Collaboration with Network Appliance, Inc
Server Networking Performance u Execution of traditional TCP/IP protocol stack dominates the server overhead u Two approaches to reduce transport protocol impact on server performance: offload or make it lighter u Offloading TCP: TCP Servers u Lightweight transport (Remote DMA): Memory. Mapped User-Level NFS over RDMA n Collaboration with Network Appliance, Inc
 Service Availability u For the client, server availability is not enough u How to provide end-to-end service availability? u Migratory TCP n Migrate server end-point of live connection u Service Continuations n Migrate service sessions between cooperative servers running the same service
Service Availability u For the client, server availability is not enough u How to provide end-to-end service availability? u Migratory TCP n Migrate server end-point of live connection u Service Continuations n Migrate service sessions between cooperative servers running the same service
 Remote Healing u Traditionally, recovery from OS failures means reboot u How to access memory when OS is unavailable? u Backdoor n Trusted I/O device that can execute remote memory operations without involving local OS/CPU n I-NIC (e. g. Myrinet) supporting R-DMA operations u Remote Monitoring n Sensor Box u Remote Repairing n Repare remote OS state u Remote Recovery n Recover service sessions from a failed OS
Remote Healing u Traditionally, recovery from OS failures means reboot u How to access memory when OS is unavailable? u Backdoor n Trusted I/O device that can execute remote memory operations without involving local OS/CPU n I-NIC (e. g. Myrinet) supporting R-DMA operations u Remote Monitoring n Sensor Box u Remote Repairing n Repare remote OS state u Remote Recovery n Recover service sessions from a failed OS
 Defensive Architectures u From OS failures to compromised OS n Once OS is compromised, the attack is hard to detect and even harder to contain n How to do intrusion detection+containment automatically? u Defensive Architectures use trusted entities to monitor system integrity and/or enforce access policies n A priviledged VM: Paladine n A TPM-based service code monitor: Satem n Interposed between client and file server: File. Wall u Continuous Monitoring n Discrete detection remains vulnerable n Continuous invariant checking u Cooperative Monitoring n Cooperative detection u Cooperative Continuous Monitoring n Continuous checking of distributed invariants
Defensive Architectures u From OS failures to compromised OS n Once OS is compromised, the attack is hard to detect and even harder to contain n How to do intrusion detection+containment automatically? u Defensive Architectures use trusted entities to monitor system integrity and/or enforce access policies n A priviledged VM: Paladine n A TPM-based service code monitor: Satem n Interposed between client and file server: File. Wall u Continuous Monitoring n Discrete detection remains vulnerable n Continuous invariant checking u Cooperative Monitoring n Cooperative detection u Cooperative Continuous Monitoring n Continuous checking of distributed invariants
 Distributed Embedded Systems u We know how to program distributed systems with stable configuration and reliable networking u We do not know how to program large and dynamic networks of embedded systems u Execution migration and self-routing n Smart Messages u High-level distributed models for programming embedded systems in the physical space n Spatial Programming n Spatial Views (EEL in collaboration with Disco Lab)
Distributed Embedded Systems u We know how to program distributed systems with stable configuration and reliable networking u We do not know how to program large and dynamic networks of embedded systems u Execution migration and self-routing n Smart Messages u High-level distributed models for programming embedded systems in the physical space n Spatial Programming n Spatial Views (EEL in collaboration with Disco Lab)
 Pervasive Computing using Smart Phones u Smart phone n the first device that enables pervasive computing and makes undergraduate students happy u Smiles project n Exploit dual connectivity for service provisioning n Indoor localization using camera phones (Demo!) n Privacy guarantees in location-based services u Next generation: Smart phone + i. Pod n Low-bandwidth continuous connectivity is a form of weak connectivity n Coda on smart phones?
Pervasive Computing using Smart Phones u Smart phone n the first device that enables pervasive computing and makes undergraduate students happy u Smiles project n Exploit dual connectivity for service provisioning n Indoor localization using camera phones (Demo!) n Privacy guarantees in location-based services u Next generation: Smart phone + i. Pod n Low-bandwidth continuous connectivity is a form of weak connectivity n Coda on smart phones?
 Vehicular Computing Systems u Make mobile ad-hoc networks real and real-time! u Dedicated Short Range Communications (DSRC) for V 2 V communication u What are the killer applications? n Near view for active accident avoidance: Traffic. View n Far-view for automobile congestion detection/avoidance and route planning u Traffic. View: one of the first outdoor experiments with a real vehicular computing system (Demo!) u Security concerns: Trust and Privacy n Probabilistic validation of aggregated traffic data u Content-distribution over vehicular networks u Dual connectivity: cellular/short range
Vehicular Computing Systems u Make mobile ad-hoc networks real and real-time! u Dedicated Short Range Communications (DSRC) for V 2 V communication u What are the killer applications? n Near view for active accident avoidance: Traffic. View n Far-view for automobile congestion detection/avoidance and route planning u Traffic. View: one of the first outdoor experiments with a real vehicular computing system (Demo!) u Security concerns: Trust and Privacy n Probabilistic validation of aggregated traffic data u Content-distribution over vehicular networks u Dual connectivity: cellular/short range
 Some Lessons u Novel hardware inspires systems research n RDMA, TPM, Smart Phones, DSRC u Offloading as principle of systems design n Functionality, monitoring, policy enforcement, validation u Pervasive computing and vehicular computing are coming n Outdoors is not like indoors! n Outdoor systems are hard to build, test and evaluate u International collaboration is a professional and social exercise absolutely necessary for students
Some Lessons u Novel hardware inspires systems research n RDMA, TPM, Smart Phones, DSRC u Offloading as principle of systems design n Functionality, monitoring, policy enforcement, validation u Pervasive computing and vehicular computing are coming n Outdoors is not like indoors! n Outdoor systems are hard to build, test and evaluate u International collaboration is a professional and social exercise absolutely necessary for students


