Lec3_Security_class.pptx
- Количество слайдов: 26
 Week 3 SYMMETRIC KEY CRYPTO Altayeva Aigerim aigerim. muit@gmail. com
Week 3 SYMMETRIC KEY CRYPTO Altayeva Aigerim aigerim. muit@gmail. com
 Content 1. Polyalphabetic Ciphers Vigenère cipher 2. One-Time Pad - One-Time Pad Encryption - Drawback of the OTP - Why is it that the one-time pad can only be used once? 3. Stream ciphers - Stream cipher A 5/1 - Algebraic Description -
Content 1. Polyalphabetic Ciphers Vigenère cipher 2. One-Time Pad - One-Time Pad Encryption - Drawback of the OTP - Why is it that the one-time pad can only be used once? 3. Stream ciphers - Stream cipher A 5/1 - Algebraic Description -
 Polyalphabetic Ciphers To improve on the simple monoalphabetic technique is to use different monoalphabetic substitutions as one proceeds through the plaintext message. ● The general name for this approach is polyalphabetic substitution cipher. ● All these techniques have the following features in common: ● - A set of related monoalphabetic substitution rules is used A key determines which particular rule is chosen for a given transformation -
Polyalphabetic Ciphers To improve on the simple monoalphabetic technique is to use different monoalphabetic substitutions as one proceeds through the plaintext message. ● The general name for this approach is polyalphabetic substitution cipher. ● All these techniques have the following features in common: ● - A set of related monoalphabetic substitution rules is used A key determines which particular rule is chosen for a given transformation -
 Vigenère cipher The set of related monoalphabetic substitution rules consists of the 26 Caesar ciphers, with shifts of 0 through 25. ● Each cipher is denoted by a key letter, which is the ciphertext letter that substitutes for the plaintext letter a. ● Thus, a Caesar cipher with a shift of 3 is denoted by the key value d. ●
Vigenère cipher The set of related monoalphabetic substitution rules consists of the 26 Caesar ciphers, with shifts of 0 through 25. ● Each cipher is denoted by a key letter, which is the ciphertext letter that substitutes for the plaintext letter a. ● Thus, a Caesar cipher with a shift of 3 is denoted by the key value d. ●
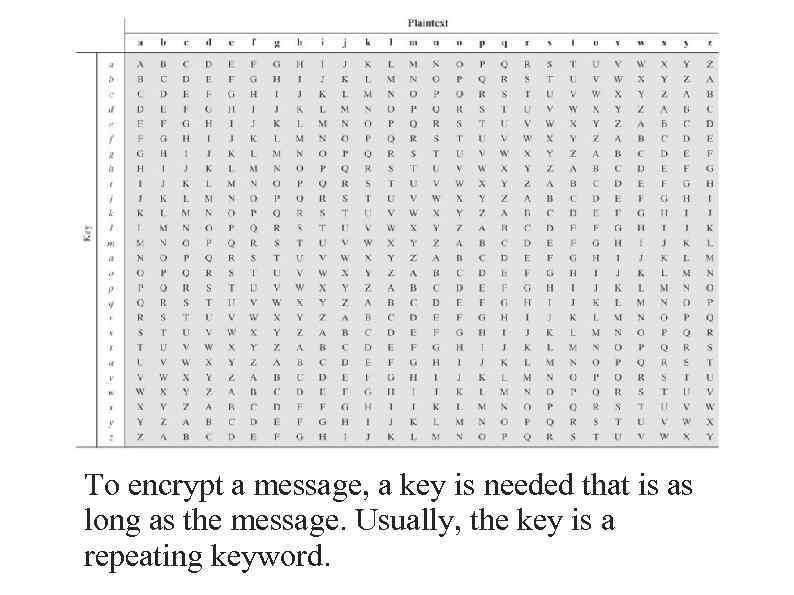 To encrypt a message, a key is needed that is as long as the message. Usually, the key is a repeating keyword.
To encrypt a message, a key is needed that is as long as the message. Usually, the key is a repeating keyword.
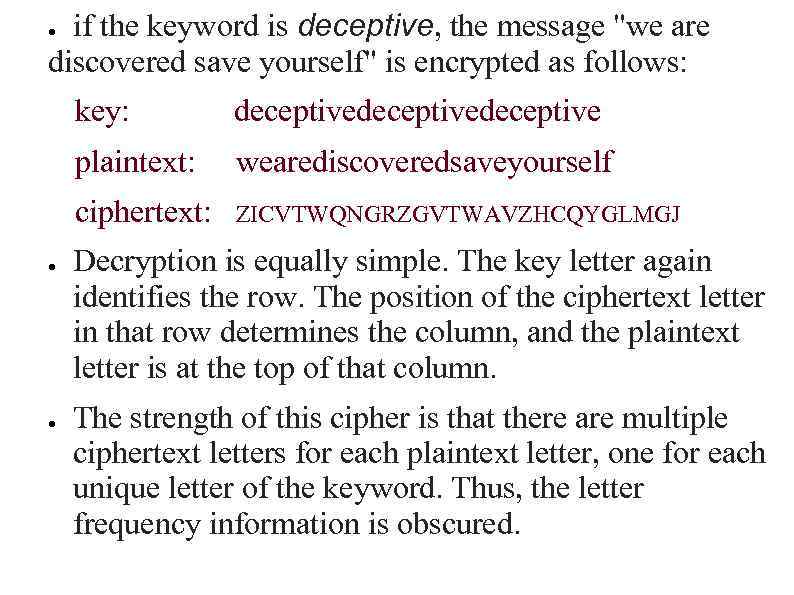 if the keyword is deceptive, the message "we are discovered save yourself" is encrypted as follows: ● key: plaintext: ● wearediscoveredsaveyourself ciphertext: ● deceptivedeceptive ZICVTWQNGRZGVTWAVZHCQYGLMGJ Decryption is equally simple. The key letter again identifies the row. The position of the ciphertext letter in that row determines the column, and the plaintext letter is at the top of that column. The strength of this cipher is that there are multiple ciphertext letters for each plaintext letter, one for each unique letter of the keyword. Thus, the letter frequency information is obscured.
if the keyword is deceptive, the message "we are discovered save yourself" is encrypted as follows: ● key: plaintext: ● wearediscoveredsaveyourself ciphertext: ● deceptivedeceptive ZICVTWQNGRZGVTWAVZHCQYGLMGJ Decryption is equally simple. The key letter again identifies the row. The position of the ciphertext letter in that row determines the column, and the plaintext letter is at the top of that column. The strength of this cipher is that there are multiple ciphertext letters for each plaintext letter, one for each unique letter of the keyword. Thus, the letter frequency information is obscured.
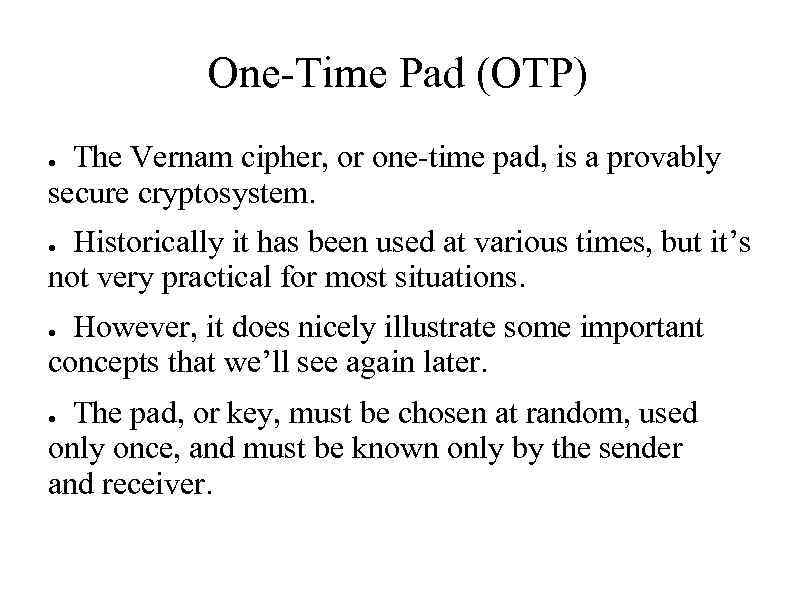 One-Time Pad (OTP) The Vernam cipher, or one-time pad, is a provably secure cryptosystem. ● Historically it has been used at various times, but it’s not very practical for most situations. ● However, it does nicely illustrate some important concepts that we’ll see again later. ● The pad, or key, must be chosen at random, used only once, and must be known only by the sender and receiver. ●
One-Time Pad (OTP) The Vernam cipher, or one-time pad, is a provably secure cryptosystem. ● Historically it has been used at various times, but it’s not very practical for most situations. ● However, it does nicely illustrate some important concepts that we’ll see again later. ● The pad, or key, must be chosen at random, used only once, and must be known only by the sender and receiver. ●
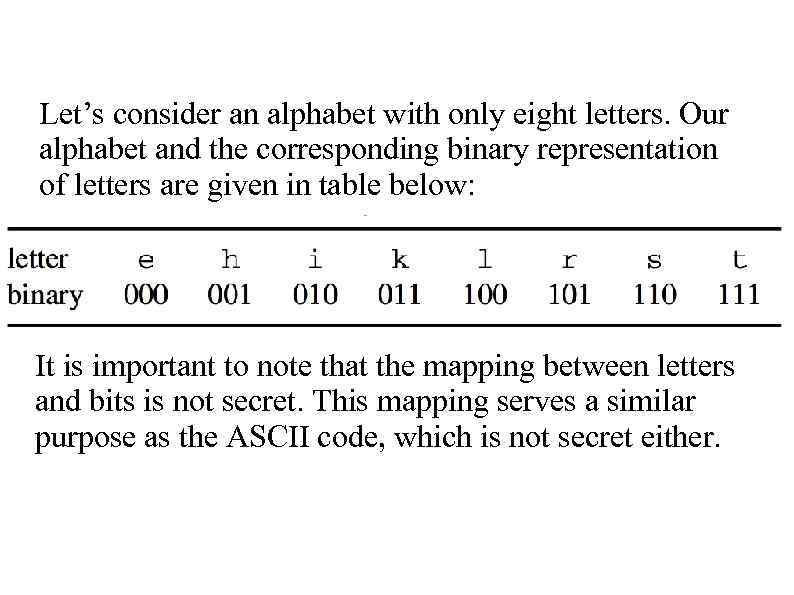 Let’s consider an alphabet with only eight letters. Our alphabet and the corresponding binary representation of letters are given in table below: It is important to note that the mapping between letters and bits is not secret. This mapping serves a similar purpose as the ASCII code, which is not secret either.
Let’s consider an alphabet with only eight letters. Our alphabet and the corresponding binary representation of letters are given in table below: It is important to note that the mapping between letters and bits is not secret. This mapping serves a similar purpose as the ASCII code, which is not secret either.
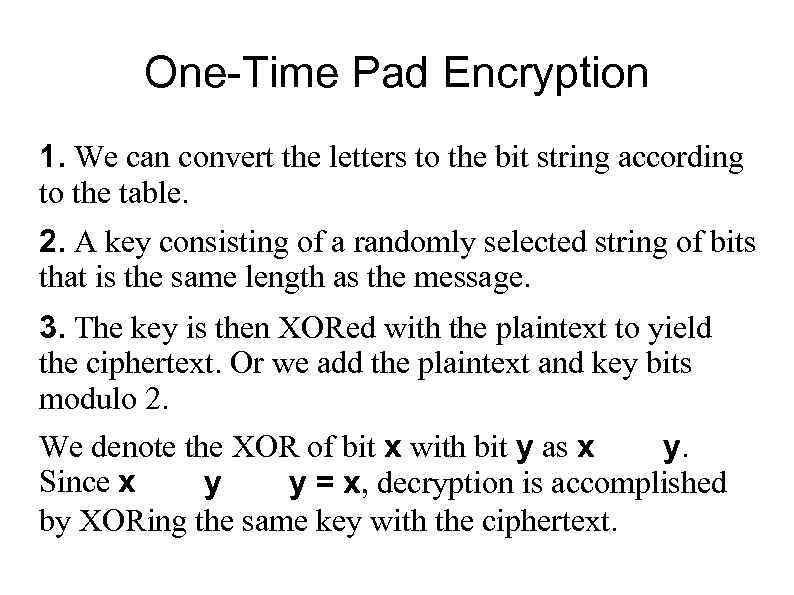 One-Time Pad Encryption 1. We can convert the letters to the bit string according to the table. 2. A key consisting of a randomly selected string of bits that is the same length as the message. 3. The key is then XORed with the plaintext to yield the ciphertext. Or we add the plaintext and key bits modulo 2. We denote the XOR of bit x with bit y as x y. Since x y = x, decryption is accomplished y by XORing the same key with the ciphertext.
One-Time Pad Encryption 1. We can convert the letters to the bit string according to the table. 2. A key consisting of a randomly selected string of bits that is the same length as the message. 3. The key is then XORed with the plaintext to yield the ciphertext. Or we add the plaintext and key bits modulo 2. We denote the XOR of bit x with bit y as x y. Since x y = x, decryption is accomplished y by XORing the same key with the ciphertext.
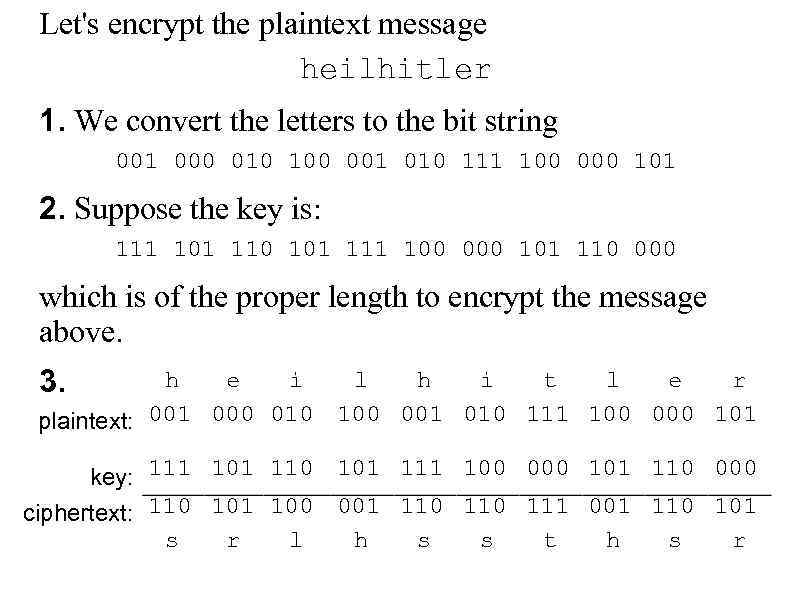 Let's encrypt the plaintext message heilhitler 1. We convert the letters to the bit string 001 000 010 100 001 010 111 100 000 101 2. Suppose the key is: 111 101 110 101 111 100 000 101 110 000 which is of the proper length to encrypt the message above. 3. h e i l h i t l e r plaintext: 001 000 010 100 001 010 111 100 000 101 key: 111 101 110 101 111 100 000 101 110 000 ciphertext: 110 101 100 001 110 111 001 110 101 s r l h s s t h s r
Let's encrypt the plaintext message heilhitler 1. We convert the letters to the bit string 001 000 010 100 001 010 111 100 000 101 2. Suppose the key is: 111 101 110 101 111 100 000 101 110 000 which is of the proper length to encrypt the message above. 3. h e i l h i t l e r plaintext: 001 000 010 100 001 010 111 100 000 101 key: 111 101 110 101 111 100 000 101 110 000 ciphertext: 110 101 100 001 110 111 001 110 101 s r l h s s t h s r
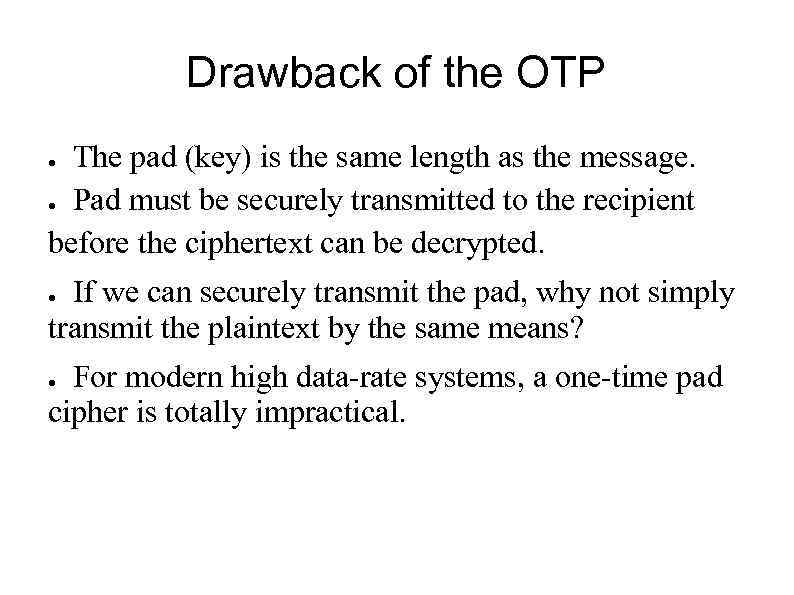 Drawback of the OTP The pad (key) is the same length as the message. ● Pad must be securely transmitted to the recipient before the ciphertext can be decrypted. ● If we can securely transmit the pad, why not simply transmit the plaintext by the same means? ● For modern high data-rate systems, a one-time pad cipher is totally impractical. ●
Drawback of the OTP The pad (key) is the same length as the message. ● Pad must be securely transmitted to the recipient before the ciphertext can be decrypted. ● If we can securely transmit the pad, why not simply transmit the plaintext by the same means? ● For modern high data-rate systems, a one-time pad cipher is totally impractical. ●
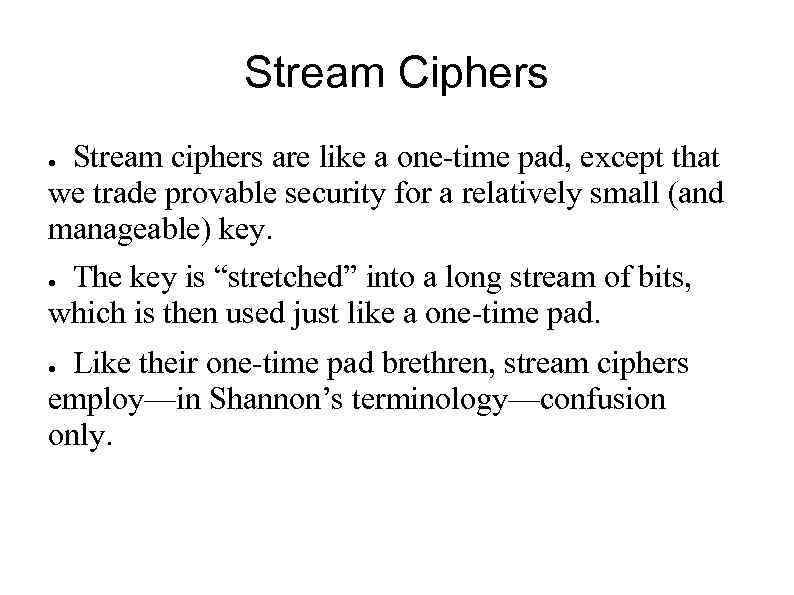 Stream Ciphers Stream ciphers are like a one-time pad, except that we trade provable security for a relatively small (and manageable) key. ● The key is “stretched” into a long stream of bits, which is then used just like a one-time pad. ● Like their one-time pad brethren, stream ciphers employ—in Shannon’s terminology—confusion only. ●
Stream Ciphers Stream ciphers are like a one-time pad, except that we trade provable security for a relatively small (and manageable) key. ● The key is “stretched” into a long stream of bits, which is then used just like a one-time pad. ● Like their one-time pad brethren, stream ciphers employ—in Shannon’s terminology—confusion only. ●
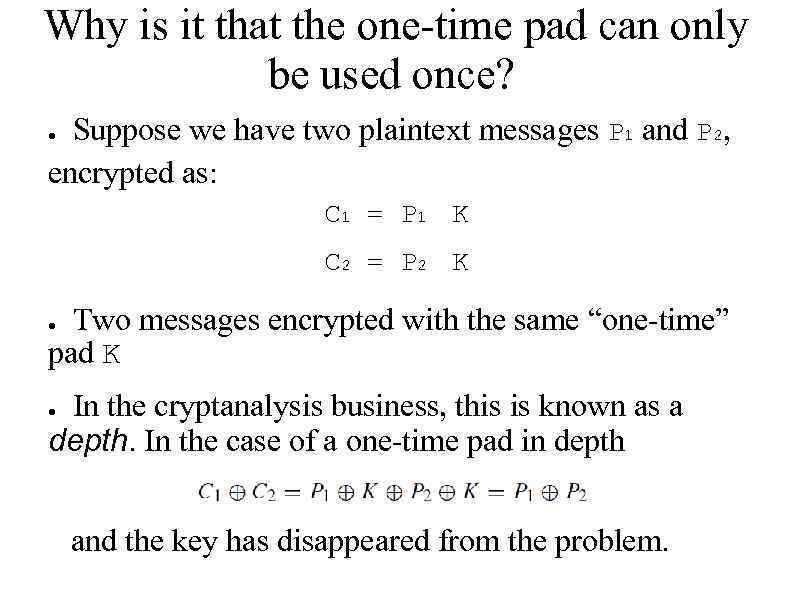 Why is it that the one-time pad can only be used once? Suppose we have two plaintext messages P 1 and P 2, encrypted as: ● C 1 = P 1 K C 2 = P 2 K Two messages encrypted with the same “one-time” pad K ● In the cryptanalysis business, this is known as a depth. In the case of a one-time pad in depth ● and the key has disappeared from the problem.
Why is it that the one-time pad can only be used once? Suppose we have two plaintext messages P 1 and P 2, encrypted as: ● C 1 = P 1 K C 2 = P 2 K Two messages encrypted with the same “one-time” pad K ● In the cryptanalysis business, this is known as a depth. In the case of a one-time pad in depth ● and the key has disappeared from the problem.
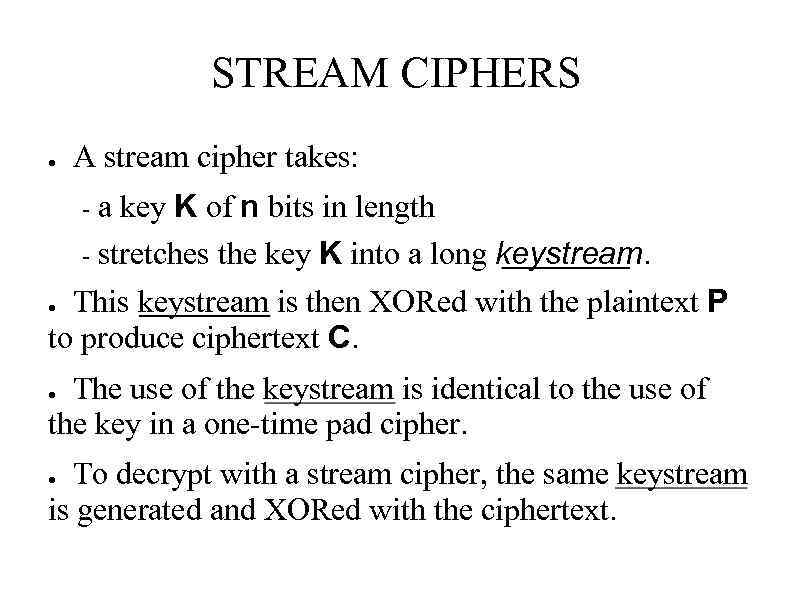 STREAM CIPHERS ● A stream cipher takes: a key K of n bits in length - stretches the key K into a long keystream. - This keystream is then XORed with the plaintext P to produce ciphertext C. ● The use of the keystream is identical to the use of the key in a one-time pad cipher. ● To decrypt with a stream cipher, the same keystream is generated and XORed with the ciphertext. ●
STREAM CIPHERS ● A stream cipher takes: a key K of n bits in length - stretches the key K into a long keystream. - This keystream is then XORed with the plaintext P to produce ciphertext C. ● The use of the keystream is identical to the use of the key in a one-time pad cipher. ● To decrypt with a stream cipher, the same keystream is generated and XORed with the ciphertext. ●
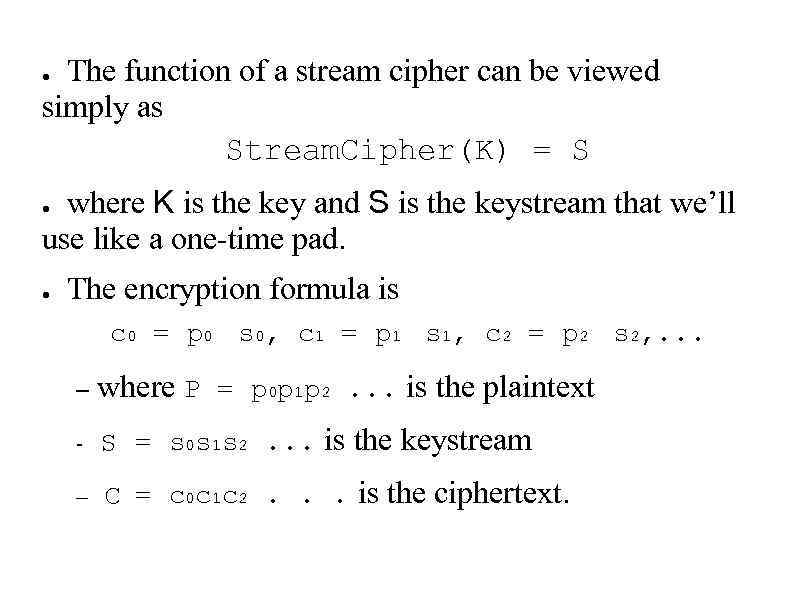 The function of a stream cipher can be viewed simply as Stream. Cipher(K) = S ● where K is the key and S is the keystream that we’ll use like a one-time pad. ● ● The encryption formula is c 0 = p 0 s 0, c 1 = p 1 s 1, c 2 = p 2 s 2, . . . – where P = p 0 p 1 p 2. . . is the plaintext - S = s 0 s 1 s 2. . . is the keystream – C = c 0 c 1 c 2. . . is the ciphertext.
The function of a stream cipher can be viewed simply as Stream. Cipher(K) = S ● where K is the key and S is the keystream that we’ll use like a one-time pad. ● ● The encryption formula is c 0 = p 0 s 0, c 1 = p 1 s 1, c 2 = p 2 s 2, . . . – where P = p 0 p 1 p 2. . . is the plaintext - S = s 0 s 1 s 2. . . is the keystream – C = c 0 c 1 c 2. . . is the ciphertext.
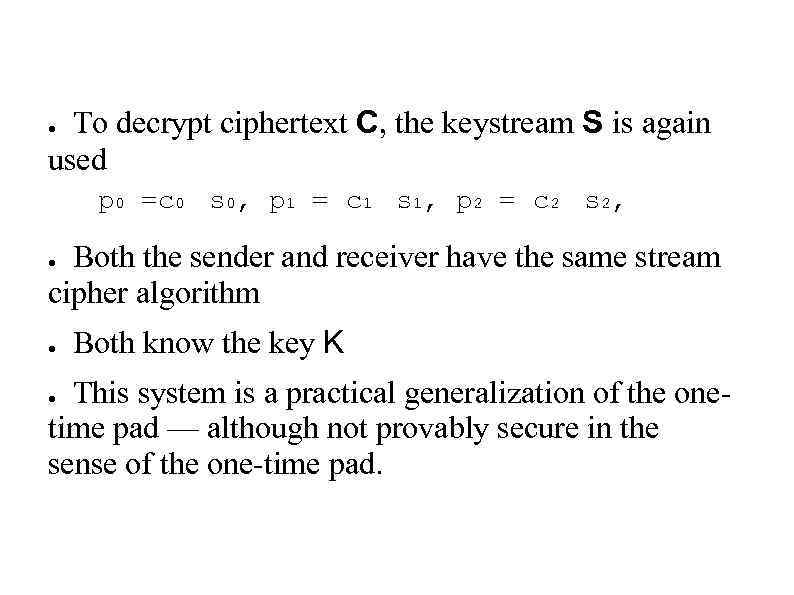 To decrypt ciphertext C, the keystream S is again used ● p 0 =c 0 s 0, p 1 = c 1 s 1, p 2 = c 2 s 2, Both the sender and receiver have the same stream cipher algorithm ● ● Both know the key K This system is a practical generalization of the onetime pad — although not provably secure in the sense of the one-time pad. ●
To decrypt ciphertext C, the keystream S is again used ● p 0 =c 0 s 0, p 1 = c 1 s 1, p 2 = c 2 s 2, Both the sender and receiver have the same stream cipher algorithm ● ● Both know the key K This system is a practical generalization of the onetime pad — although not provably secure in the sense of the one-time pad. ●
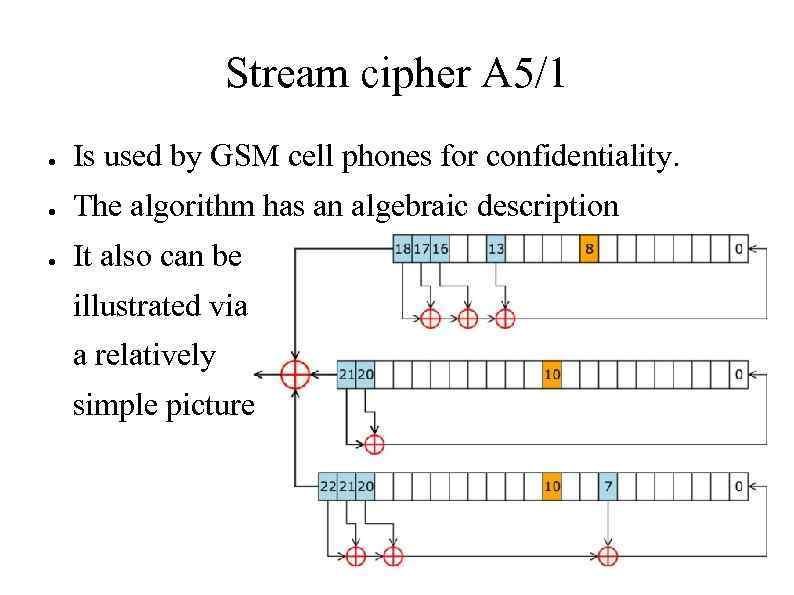 Stream cipher A 5/1 ● Is used by GSM cell phones for confidentiality. ● The algorithm has an algebraic description ● It also can be illustrated via a relatively simple picture
Stream cipher A 5/1 ● Is used by GSM cell phones for confidentiality. ● The algorithm has an algebraic description ● It also can be illustrated via a relatively simple picture
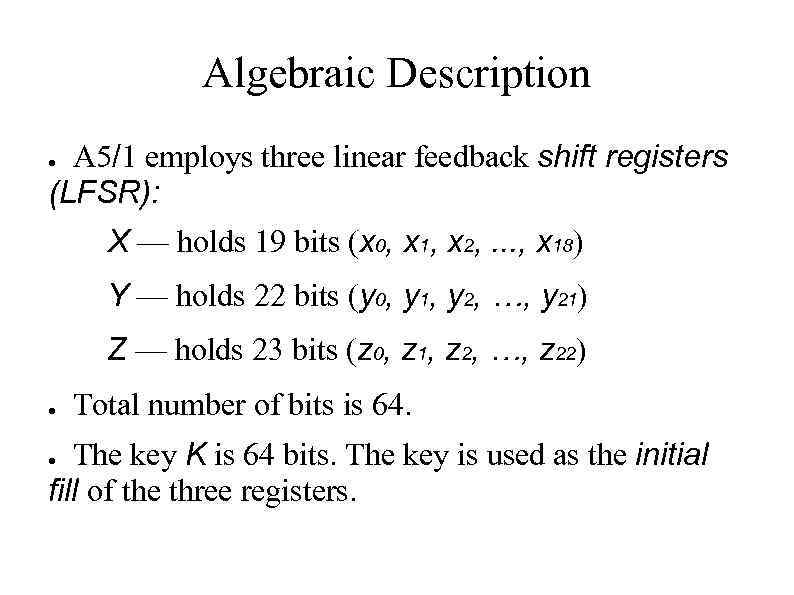 Algebraic Description A 5/1 employs three linear feedback shift registers (LFSR): ● X — holds 19 bits (x 0, x 1, x 2, . . . , x 18) Y — holds 22 bits (y 0, y 1, y 2, …, y 21) Z — holds 23 bits (z 0, z 1, z 2, …, z 22) ● Total number of bits is 64. The key K is 64 bits. The key is used as the initial fill of the three registers. ●
Algebraic Description A 5/1 employs three linear feedback shift registers (LFSR): ● X — holds 19 bits (x 0, x 1, x 2, . . . , x 18) Y — holds 22 bits (y 0, y 1, y 2, …, y 21) Z — holds 23 bits (z 0, z 1, z 2, …, z 22) ● Total number of bits is 64. The key K is 64 bits. The key is used as the initial fill of the three registers. ●
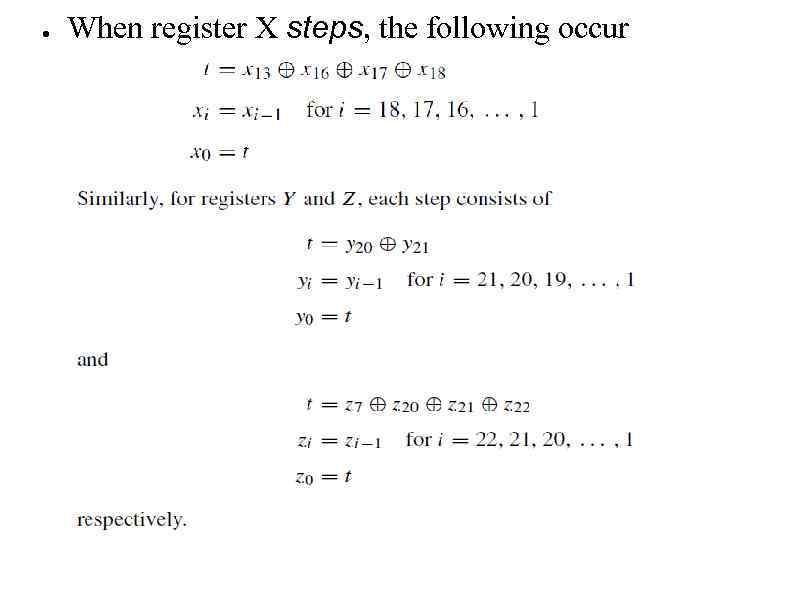 ● When register X steps, the following occur
● When register X steps, the following occur
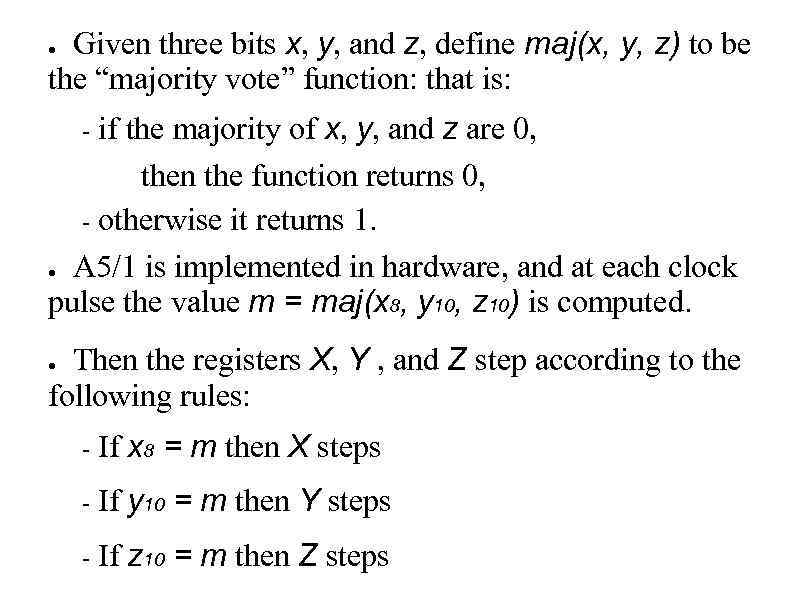 Given three bits x, y, and z, define maj(x, y, z) to be the “majority vote” function: that is: ● if the majority of x, y, and z are 0, then the function returns 0, - otherwise it returns 1. ● A 5/1 is implemented in hardware, and at each clock pulse the value m = maj(x 8, y 10, z 10) is computed. - Then the registers X, Y , and Z step according to the following rules: ● - If x 8 = m then X steps - If y 10 = m then Y steps - If z 10 = m then Z steps
Given three bits x, y, and z, define maj(x, y, z) to be the “majority vote” function: that is: ● if the majority of x, y, and z are 0, then the function returns 0, - otherwise it returns 1. ● A 5/1 is implemented in hardware, and at each clock pulse the value m = maj(x 8, y 10, z 10) is computed. - Then the registers X, Y , and Z step according to the following rules: ● - If x 8 = m then X steps - If y 10 = m then Y steps - If z 10 = m then Z steps
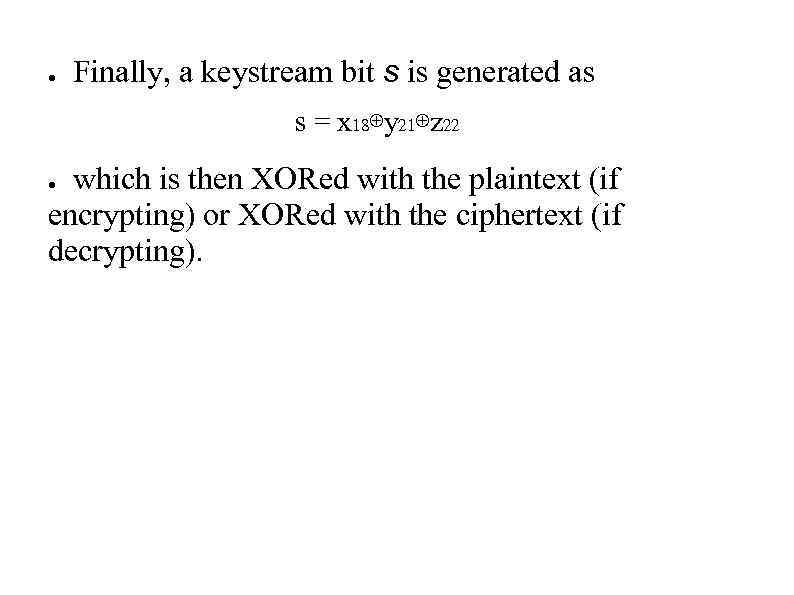 ● Finally, a keystream bit s is generated as s = x 18⊕y 21⊕z 22 which is then XORed with the plaintext (if encrypting) or XORed with the ciphertext (if decrypting). ●
● Finally, a keystream bit s is generated as s = x 18⊕y 21⊕z 22 which is then XORed with the plaintext (if encrypting) or XORed with the ciphertext (if decrypting). ●
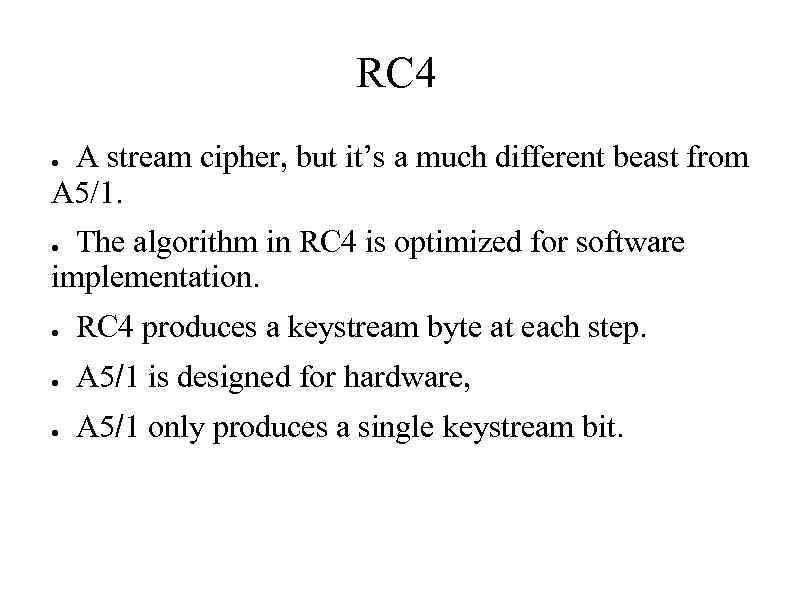 RC 4 A stream cipher, but it’s a much different beast from A 5/1. ● The algorithm in RC 4 is optimized for software implementation. ● ● RC 4 produces a keystream byte at each step. ● A 5/1 is designed for hardware, ● A 5/1 only produces a single keystream bit.
RC 4 A stream cipher, but it’s a much different beast from A 5/1. ● The algorithm in RC 4 is optimized for software implementation. ● ● RC 4 produces a keystream byte at each step. ● A 5/1 is designed for hardware, ● A 5/1 only produces a single keystream bit.
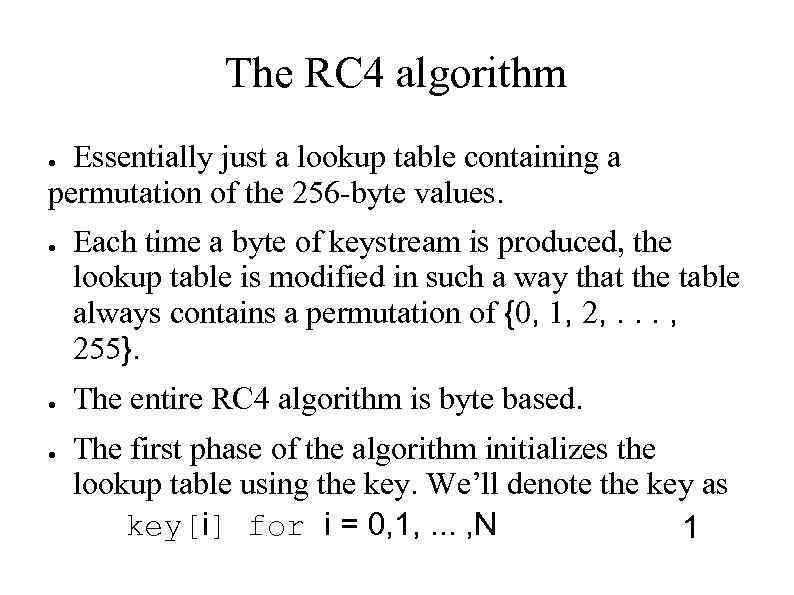 The RC 4 algorithm Essentially just a lookup table containing a permutation of the 256 -byte values. ● ● Each time a byte of keystream is produced, the lookup table is modified in such a way that the table always contains a permutation of {0, 1, 2, . . . , 255}. The entire RC 4 algorithm is byte based. The first phase of the algorithm initializes the lookup table using the key. We’ll denote the key as key[i] for i = 0, 1, . . . , N 1
The RC 4 algorithm Essentially just a lookup table containing a permutation of the 256 -byte values. ● ● Each time a byte of keystream is produced, the lookup table is modified in such a way that the table always contains a permutation of {0, 1, 2, . . . , 255}. The entire RC 4 algorithm is byte based. The first phase of the algorithm initializes the lookup table using the key. We’ll denote the key as key[i] for i = 0, 1, . . . , N 1
![RC 4 initialization for i = 0 to 255 S[i] = i K[i]=key[i mod. RC 4 initialization for i = 0 to 255 S[i] = i K[i]=key[i mod.](https://present5.com/presentation/14418837_392560903/image-24.jpg) RC 4 initialization for i = 0 to 255 S[i] = i K[i]=key[i mod. N] next i j=0 for i = 0 to 255 j=(j+S[i]+K[i]) mod 256 swap(S[i], S[j]) next i i=j=0 where each key[i] is a byte, and the lookup table as S[i], where each S[i] is also a byte. ● the key can be of any length from 0 to 256 bytes. ● The key is only used to initialize the permutation S ●
RC 4 initialization for i = 0 to 255 S[i] = i K[i]=key[i mod. N] next i j=0 for i = 0 to 255 j=(j+S[i]+K[i]) mod 256 swap(S[i], S[j]) next i i=j=0 where each key[i] is a byte, and the lookup table as S[i], where each S[i] is also a byte. ● the key can be of any length from 0 to 256 bytes. ● The key is only used to initialize the permutation S ●
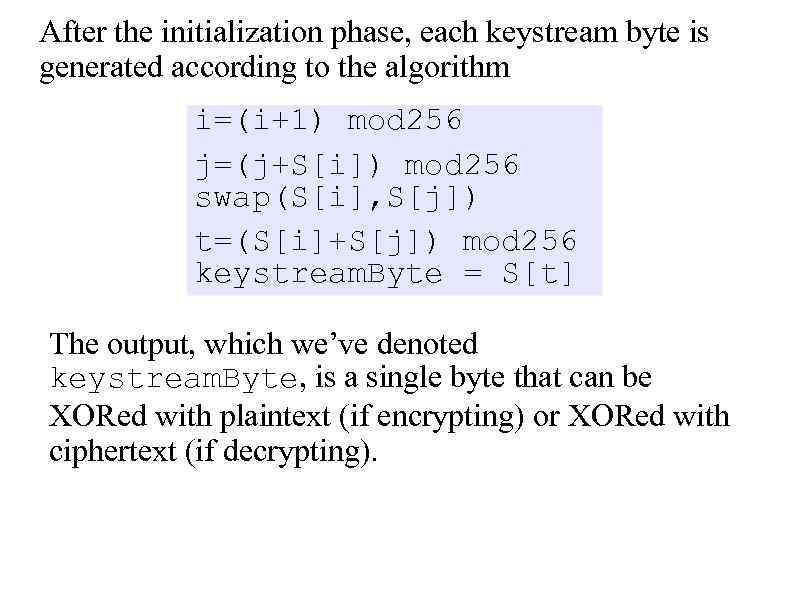 After the initialization phase, each keystream byte is generated according to the algorithm i=(i+1) mod 256 j=(j+S[i]) mod 256 swap(S[i], S[j]) t=(S[i]+S[j]) mod 256 keystream. Byte = S[t] The output, which we’ve denoted keystream. Byte, is a single byte that can be XORed with plaintext (if encrypting) or XORed with ciphertext (if decrypting).
After the initialization phase, each keystream byte is generated according to the algorithm i=(i+1) mod 256 j=(j+S[i]) mod 256 swap(S[i], S[j]) t=(S[i]+S[j]) mod 256 keystream. Byte = S[t] The output, which we’ve denoted keystream. Byte, is a single byte that can be XORed with plaintext (if encrypting) or XORed with ciphertext (if decrypting).
 References ● http: //en. wikipedia. org/wiki/A 5/1 Information Security Principles and Practice, Mark Stamp ● Chapter 3, SYMMETRIC KEY CRYPTO ● Cryptography and Network Security Principles and Practices, Fourth Edition, William Stallings - - Chapter 2. Classical Encryption Techniques ● 2. 1. Symmetric Cipher Model
References ● http: //en. wikipedia. org/wiki/A 5/1 Information Security Principles and Practice, Mark Stamp ● Chapter 3, SYMMETRIC KEY CRYPTO ● Cryptography and Network Security Principles and Practices, Fourth Edition, William Stallings - - Chapter 2. Classical Encryption Techniques ● 2. 1. Symmetric Cipher Model


