c4702676a3db53a6494d191eb098b0d9.ppt
- Количество слайдов: 24
Web Spoofing John D. Cook Andrew Linn
Web huh? Spoof: A hoax, trick, or deception n Discussed among academics in the 1980’s as the concept of IP spoofing n IP Spoofing was used in a few early and well known attacks n IP Spoofing fell out of popularity (TCP) n Still done today in different forms. n Not all web spoofs are malicious n
Phishing n n n Pronounced fishing, just much less fun Broad term to describe attempted acquisition of private or sensitive information Passive or aggressive attack. Not all phishing attacks are web spoofs Nature of web spoofs make them a good choice however. An example of the many uses of web spoofs
Phishing Spoof Attacks n n n Fairly common; They are easy and WORK!! “Man in the middle” attack Rewrites the URLs of a page http: //www. cnn. com http: //www. IAm. Attacker. com/http: //www. cnn. com Users can get trapped in the attackers system
Email Hoaxes Often a phishing attack as well as a type of spoof n Rely on carelessness or ignorance of the user n Appear to be from legitimate service n Login IDs, Passwords, Credit Card Numbers, and SS numbers are the “booty” n
Email Hoaxes Cont. Some serve as a way to implement a web page spoof that in itself is a phishing attack. n FSU Phishing Email Hoax n Wo. W Email Hoax n I love Fire. Fox n The purpose of the hoax n

Spoofs Today Because everything else was totally last month. n Video games are in. So is stealing them. n The downside of all info stored “server-side”. n Online shopping = stolen credit cards. Yes, because us Americans just don’t go to the store anymore. n
Recognizing Spoofs Look for the lock at the bottom of your browser. Though this isn’t always indicative of a safe website n Use a *good* browser. My ambiguity in that statement allows me to not be biased. n Check certificates of the page n Or just pay attention. n

The “Shadow Web” Known as Web spoofing n First examined by Princeton researchers in 1996 n Tested in 2002 by researchers at Dartmouth n Traps the user in attacker’s web n Uses Java. Script to rewrite browser n Effectively spoofs the entire Web n

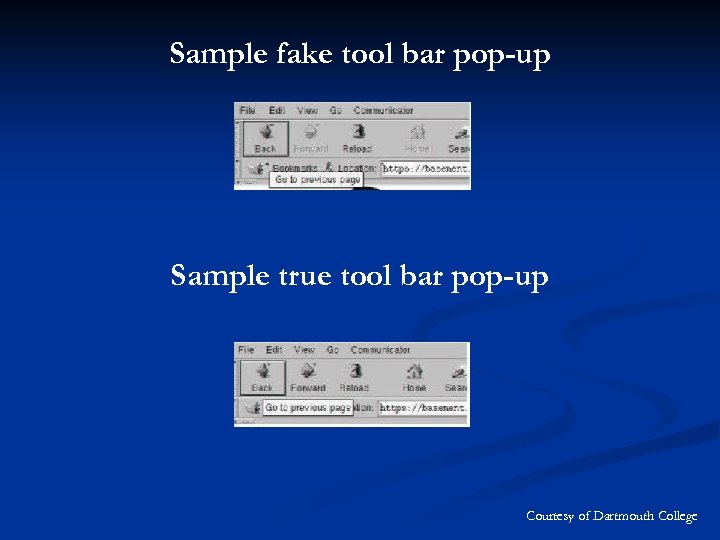
Sample fake tool bar pop-up Sample true tool bar pop-up Courtesy of Dartmouth College
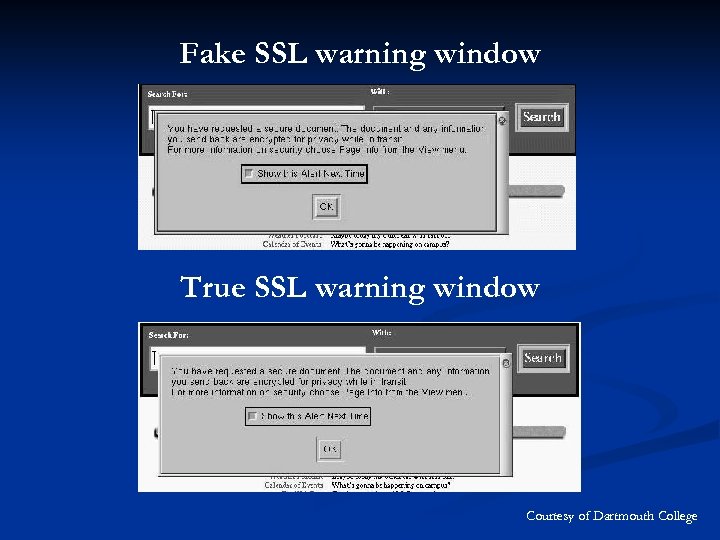
Fake SSL warning window True SSL warning window Courtesy of Dartmouth College

The “Shadow Web” While plausible, it is unlikely n High yield = Huge effort n Various browsers, customization, and security software options prevent it from being a viable attack n Acts as a Man-in-the-Middle attack n
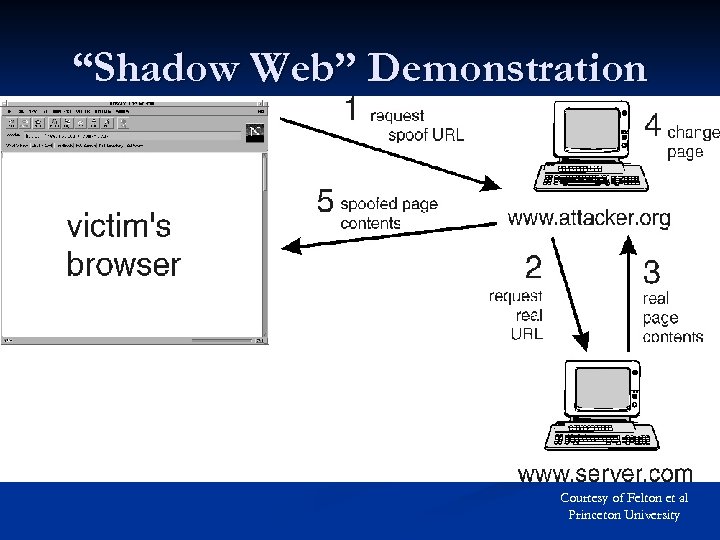
“Shadow Web” Demonstration Courtesy of Felton et al Princeton University

The “Shadow Web” Attacks Simple surveillance -> Phishing attacks n Data manipulation -> Man-in-the-Middle n

The “Shadow Web” Detection Disable Java. Script n Customize n Pop-up and spam blockers n Firewalls and other security software n
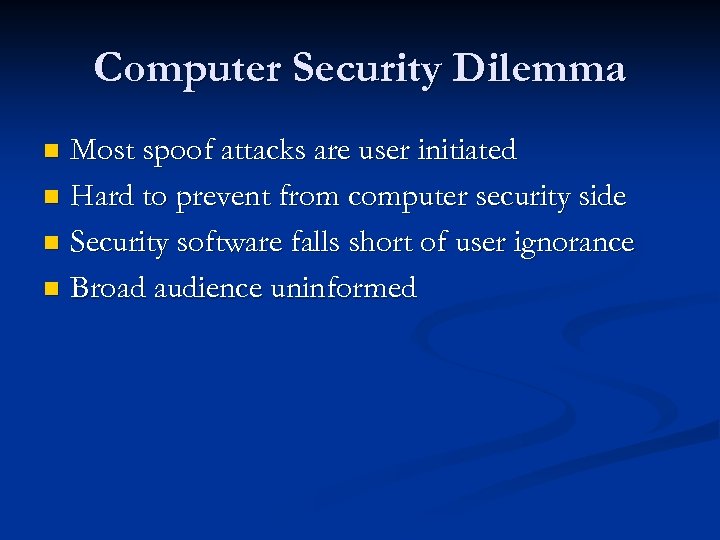
Computer Security Dilemma Most spoof attacks are user initiated n Hard to prevent from computer security side n Security software falls short of user ignorance n Broad audience uninformed n
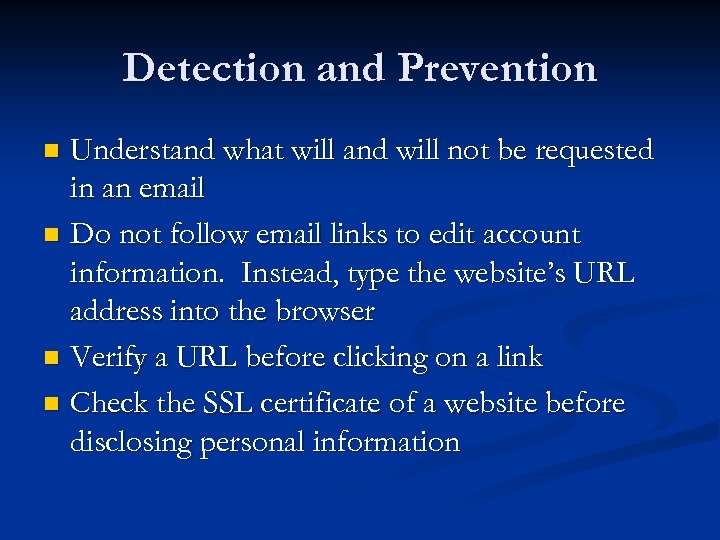
Detection and Prevention Understand what will and will not be requested in an email n Do not follow email links to edit account information. Instead, type the website’s URL address into the browser n Verify a URL before clicking on a link n Check the SSL certificate of a website before disclosing personal information n
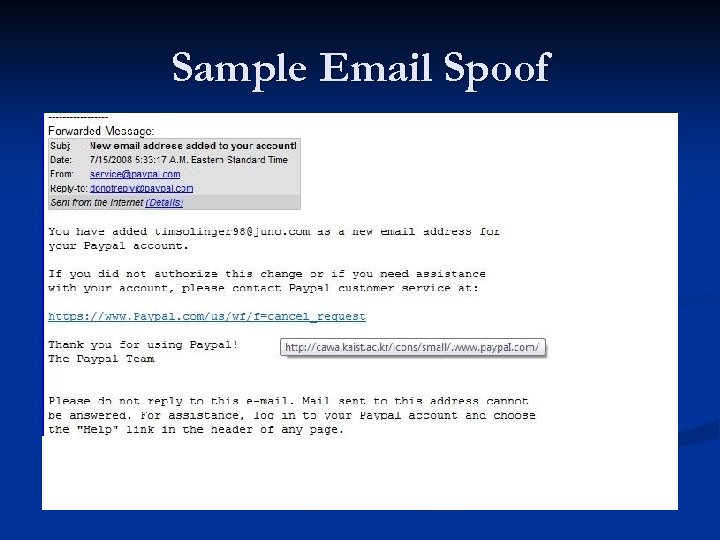
Sample Email Spoof
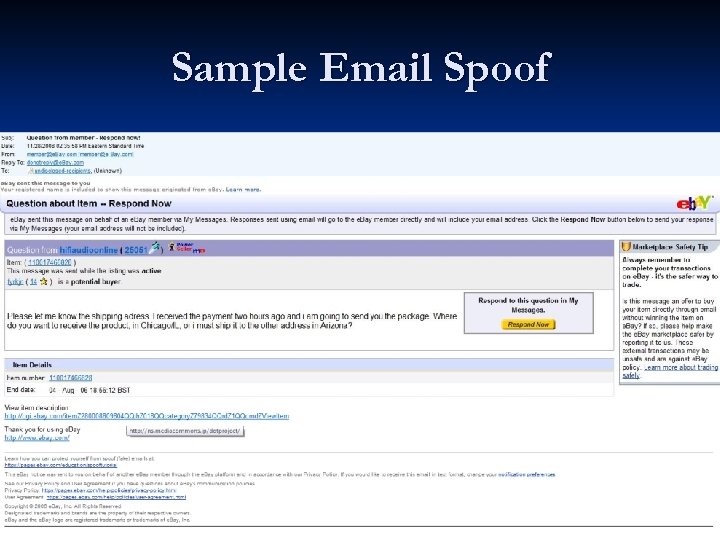
Sample Email Spoof
Motivations Most spoof attacks are phishing attacks n Some serve to smear a company’s reputation or hurt their finances with false reports n Others for fun or political goals n All spoofs, even those that are jokes, have the potential for harm n
Brick and Mortar Virtual world vs. physical n Harder to verify Amazon. com than brick and mortar store n Security software helps, but educated user base best defense against spoof attack n
Criminal Act Identity theft is a growing concern n Spoofing is used in many phishing scams to facilitate identity theft n Most attackers use stolen or hacked machines n When caught, attackers must be punished appropriately n
Questions?
c4702676a3db53a6494d191eb098b0d9.ppt