3801b4c0c4973ceae777b1ea3a172fe9.ppt
- Количество слайдов: 38

Web site security Part 2 : Defending Against SQL Injection Reporter : James Chen 1
Outline n What is SQL Injection? n SQL Injection Testing Methodology SQL Injection Defense n SQL injection detection method and tools n My Automatic Anti-SQL Injection Method features n Summary n 2
What is SQL Injection? n The ability to inject SQL commands into the database engine through an existing application 3
How common is it? n n n It is probably the most common Website vulnerability today! It is a flaw in "web application" development, it is not a DB or web server problem ¨ Most programmers are still not aware of this problem ¨ A lot of the tutorials & demo “templates” are vulnerable ¨ Even worse, a lot of solutions posted on the Internet are not good enough In our pen tests over 60% of our clients turn out to be vulnerable to SQL Injection 4
Vulnerable Applications n n Almost all SQL databases and programming languages are potentially vulnerable ¨ MS SQL Server, Oracle, My. SQL, Postgres, DB 2, MS Access, Sybase, Informix, etc Accessed through applications developed using: ¨ Perl and CGI scripts that access databases ¨ ASP, JSP, PHP ¨ XML, XSL and XSQL ¨ Javascript ¨ VB, MFC, and other ODBC-based tools and APIs ¨ DB specific Web-based applications and API’s ¨ Reports and DB Applications ¨ 3 and 4 GL-based languages (C, OCI, Pro*C, and COBOL) ¨ many more 5
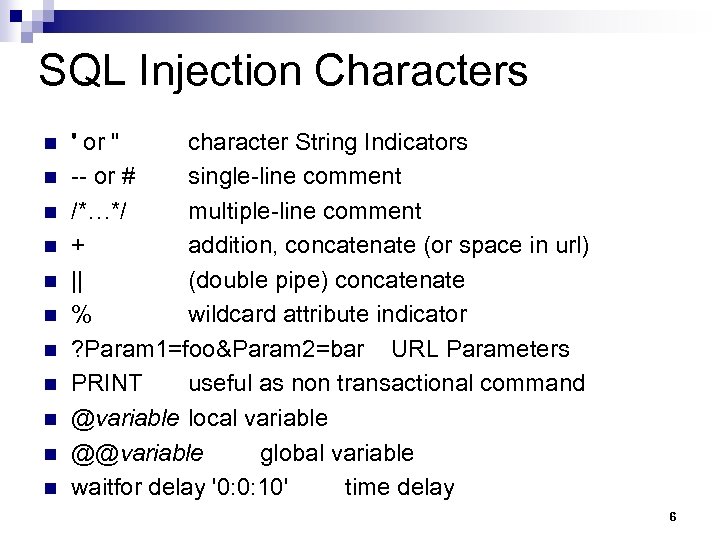
SQL Injection Characters n n n ' or " character String Indicators -- or # single-line comment /*…*/ multiple-line comment + addition, concatenate (or space in url) || (double pipe) concatenate % wildcard attribute indicator ? Param 1=foo&Param 2=bar URL Parameters PRINT useful as non transactional command @variable local variable @@variable global variable waitfor delay '0: 0: 10' time delay 6
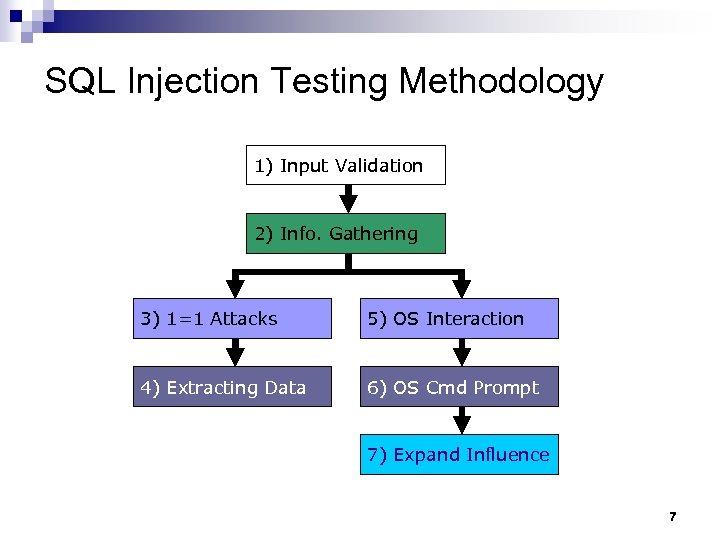
SQL Injection Testing Methodology 1) Input Validation 2) Info. Gathering 3) 1=1 Attacks 5) OS Interaction 4) Extracting Data 6) OS Cmd Prompt 7) Expand Influence 7
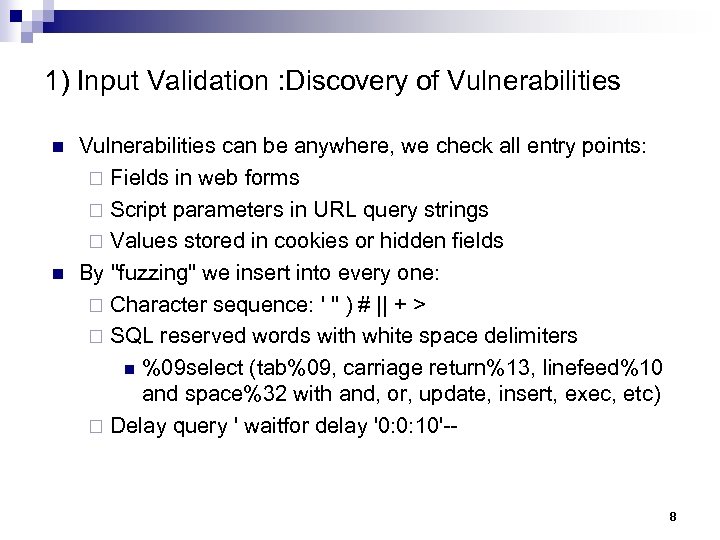
1) Input Validation : Discovery of Vulnerabilities n n Vulnerabilities can be anywhere, we check all entry points: ¨ Fields in web forms ¨ Script parameters in URL query strings ¨ Values stored in cookies or hidden fields By "fuzzing" we insert into every one: ¨ Character sequence: ' " ) # || + > ¨ SQL reserved words with white space delimiters n %09 select (tab%09, carriage return%13, linefeed%10 and space%32 with and, or, update, insert, exec, etc) ¨ Delay query ' waitfor delay '0: 0: 10'-- 8
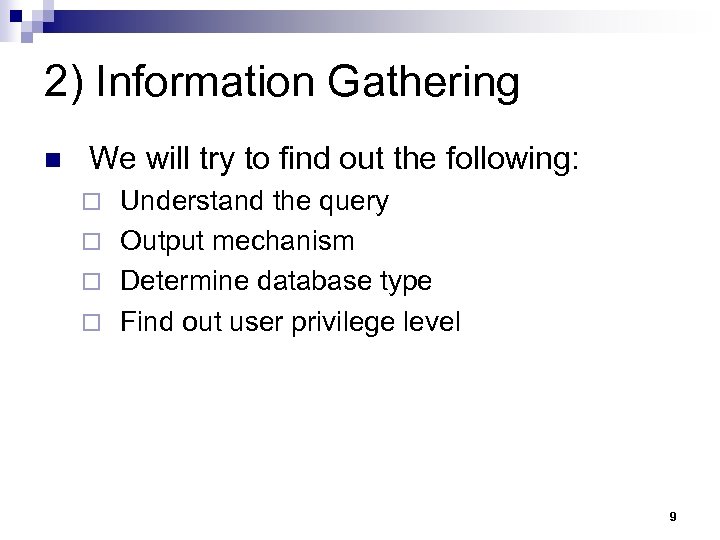
2) Information Gathering n We will try to find out the following: Understand the query ¨ Output mechanism ¨ Determine database type ¨ Find out user privilege level ¨ 9
3) 1=1 Attacks Discover DB structure n Enumerating table columns in different DBs n Database Enumeration n 10
4) Extracting Data Password grabbing n Create DB Accounts n Grabbing MS SQL Server Hashes n Brute forcing Passwords n Transfer DB structure and data n Create Identical DB Structure n Transfer DB n 11
5) OS Interaction Interacting with the OS n Assessing Network Connectivity n Gathering IP information through reverse lookups n Network Reconnaissance n 12
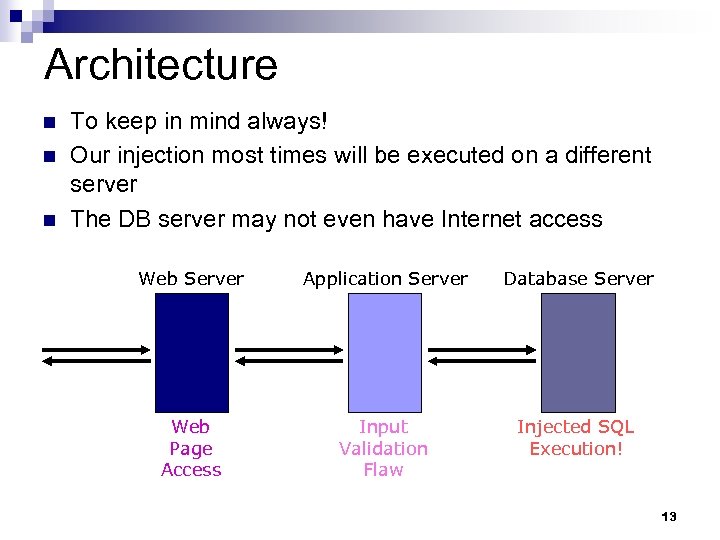
Architecture n n n To keep in mind always! Our injection most times will be executed on a different server The DB server may not even have Internet access Web Server Application Server Database Server Web Page Access Input Validation Flaw Injected SQL Execution! 13
6) OS Cmd Prompt Jumping to the OS n Using Active. X Automation Scripts n Retrieving VNC Password from Registry n 14
7) Expand Influence Hopping into other DB Servers n Linked Servers n Executing through stored procedures remotely n Uploading files through reverse connection n Uploading files through SQL Injection n 15
Evasion Techniques n Input validation or IDS Signature Evasion ¨ Evading ' OR 1=1 signature n ' OR 'something' like 'some%‘ ¨ use PHP addslashes() function to escape characters n This can be easily evaded by using replacements for any of characters in a numeric field n To be circumvented by encoding or using Char() n Using white spaces, comments, string concatenation, variables, hex value 16
SQL Injection Defense It is quite simple: input validation n The real challenge is making best practices consistent through all your code n ¨ Enforce "strong design" in new applications ¨ You should audit your existing websites and source code n Even if you have an air tight design, harden your servers 17
Strong Design n Define an easy "secure" path to querying data ¨ Use stored procedures for interacting with database ¨ Call stored procedures through a parameterized API ¨ Validate all input through generic routines ¨ Use the principle of "least privilege" n Define several roles, one for each kind of query 18
Input Validation n Define data types for each field ¨ Implement n stringent "allow only good" filters If the input is supposed to be numeric, use a numeric variable in your script to store it ¨ Reject bad input rather than attempting to escape or modify it ¨ Implement stringent "known bad" filters n For example: reject "select", "insert", "update", "shutdown", "delete", "drop", "--", "'" 19
Harden the Server n n n n Run DB as a low-privilege user account Remove unused stored procedures and functionality or restrict access to administrators Change permissions and remove "public" access to system objects Audit password strength for all user accounts Remove pre-authenticated linked servers Remove unused network protocols Firewall the server so that only trusted clients can connect to it (typically only: administrative network, web server and backup server) 20
Detection and Dissuasion n n You may want to react to SQL injection attempts by: ¨ Logging the attempts ¨ Sending email alerts ¨ Blocking the offending IP ¨ Sending back intimidating error messages: n "WARNING: Improper use of this application has been detected. A possible attack was identified. Legal actions will be taken. " n Check with your lawyers for proper wording This should be coded into your validation scripts 21
SQL injection detection method has introduced n. Typical validation procedure n. Anti-SQL-Injection. php n. To take the popular open-source IDS Snort n. WAVES—Black-box approach 22
WAVES—Black-box approach n Huang, Y. W. , Huang, S. K. , Lin, T. P. , Tsai, C. H. “Web Application Security Assessment by Fault Injection and Behavior Monitoring. ” In Proc. 12 th Int’l World Wide Web Conference, p. 148 -159, Budapest, Hungary, 2003. n Using crawler to discover all pages in a Web site that contain HTML forms are parsed and stored in XML format. To inject malicious SQL patterns into the serverside program that processes the form’s input. If the filtering mechanism is provided on a global scale, then injection will fail. n n n 23
Automatic black-box method features Complete crawling n Bypass the validation procedure n Test set and injection patterns Automatic generation (self-learning) n Output analysis according output error messages n 24
Other sql injection tools introduction Absinthe n Web. Scarab n Web. Goat n 25
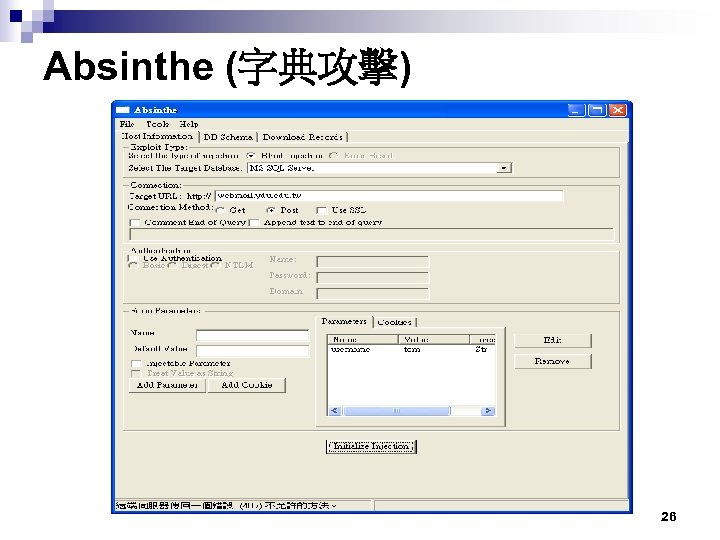
Absinthe (字典攻擊) 26
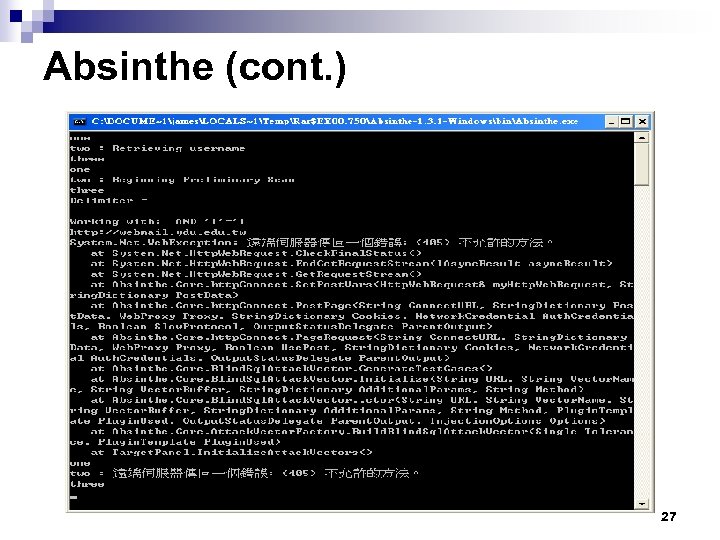
Absinthe (cont. ) 27
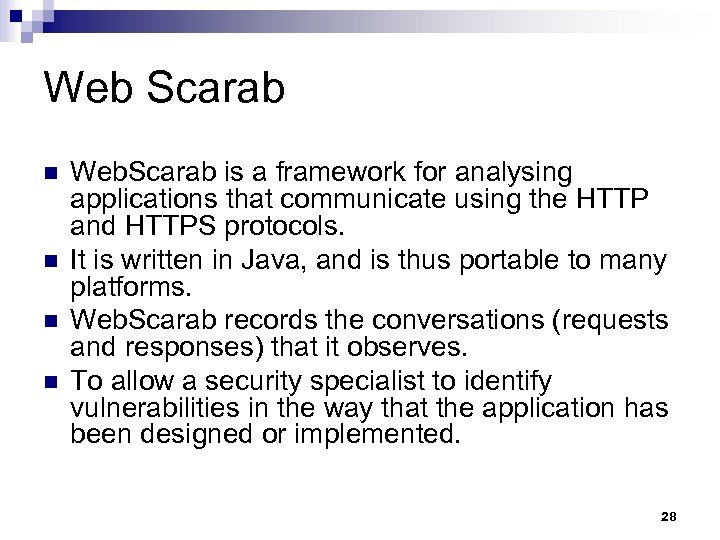
Web Scarab n n Web. Scarab is a framework for analysing applications that communicate using the HTTP and HTTPS protocols. It is written in Java, and is thus portable to many platforms. Web. Scarab records the conversations (requests and responses) that it observes. To allow a security specialist to identify vulnerabilities in the way that the application has been designed or implemented. 28
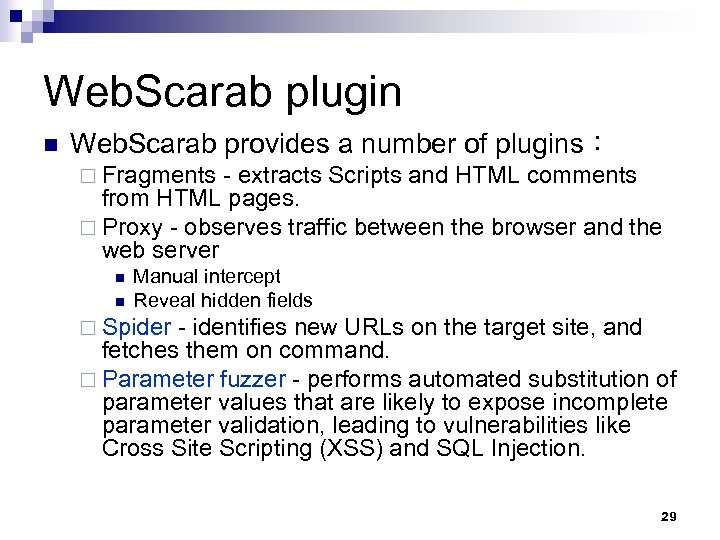
Web. Scarab plugin n Web. Scarab provides a number of plugins: ¨ Fragments - extracts Scripts and HTML comments from HTML pages. ¨ Proxy - observes traffic between the browser and the web server n n Manual intercept Reveal hidden fields ¨ Spider - identifies new URLs on the target site, and fetches them on command. ¨ Parameter fuzzer - performs automated substitution of parameter values that are likely to expose incomplete parameter validation, leading to vulnerabilities like Cross Site Scripting (XSS) and SQL Injection. 29
Web. Scarab Feature Web. Scarab is extensible. n Each feature above is implemented as a plugin, and can be removed or replaced. n New features can be easily implemented as well. n Web. Scarab is intended to become the tool of choice for serious Web debugging. n 30
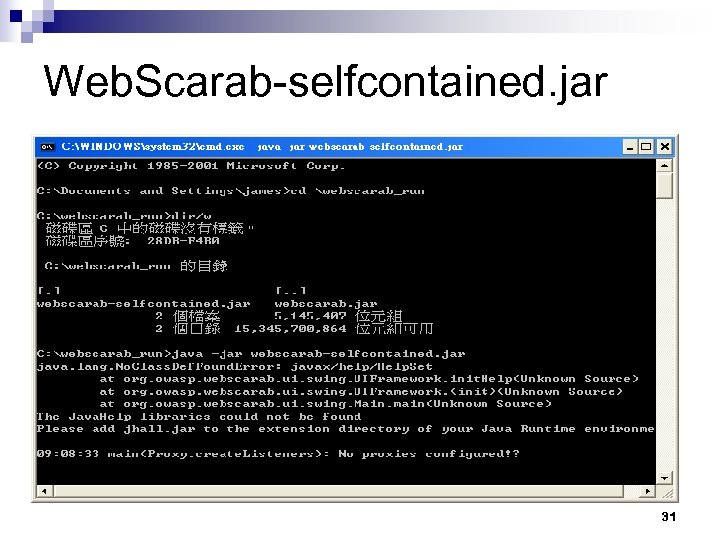
Web. Scarab-selfcontained. jar 31
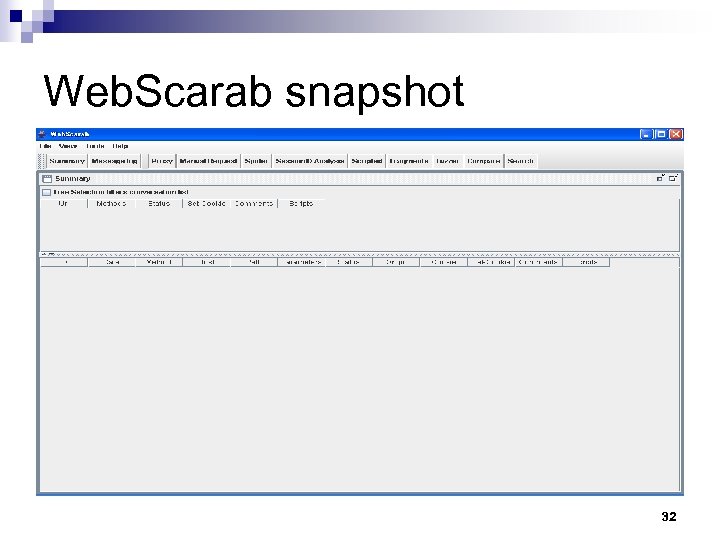
Web. Scarab snapshot 32
Web. Goat Web application security is difficult to learn and practice. n Web. Goat is a full J 2 EE web application designed to teach web application security lessons. n 33
My Automatic Anti-SQL Injection Method features 不需要重新改寫網頁 n 不需調整資料庫安全權限 n 不需透過IDS或其他網路防禦設備 n 不針對字典攻擊做防禦 n 自動加入 input vlidation or filter function於 網頁中 n 34
How to insert validation function n n Using crawler to discover all pages in a Web site that contain HTML forms are parsed and stored in XML format. To inject validation function into the server-side program that processes the form’s input. If SQL injection fail, my solutioin is success. 35
How to implement my solution n n Using Web Scarab as platform. Using Web Scarab’s Spider to identifies new URLs on the target site, and fetches them on command. To inject validation function into the server-side program that processes the form’s input. Testing: using Web Scarab’s Parameter fuzzer to expose incomplete parameter validation, leading to vulnerabilities like Cross Site Scripting (XSS) and SQL Injection. 36
Summary n n SQL Injection is a dangerous vulnerability All programming languages and all SQL databases are potentially vulnerable Protecting against it requires Input validation, IDS detection AND strong database and OS hardening must be used together. We try to implement a anti-SQL Injection system to insert correct input validation function automatically. 37
Reference n Advanced SQL Injection, Victor Chapela , http: //www. owasp. org/docroot/owasp/misc/Advanced_SQL_Injection. ppt 38
3801b4c0c4973ceae777b1ea3a172fe9.ppt