172fdb2e5baae1d339f582fd483c11f6.ppt
- Количество слайдов: 9
VOMS Architecture WP 4 (EDT) Meeting Bologna, October 8 2002 Bologna, 8/10/2002 WP 4 (EDT) Meeting
VOMS components • Client – contacts the server presenting user certificate and obtains a list of groups, roles and capabilities of the user • voms-proxy-init command • Server – receives requests from clients and returns information about the user – Secure communications client-server – Current implementation in C, My. SQL • Administration interface – Permits creation and management of users, groups, roles, capabilities • implementation in Java (Tomcat) soon! • vailable implementation in php (https) a Bologna, 8/10/2002 WP 4 (EDT) Meeting 2
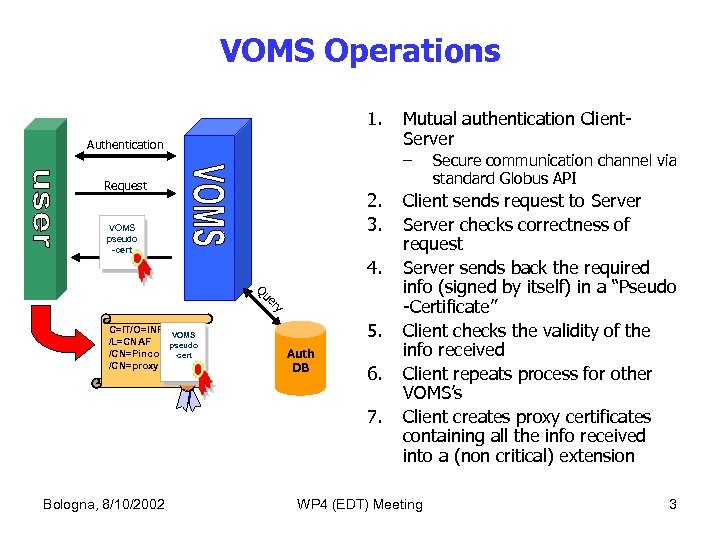
VOMS Operations 1. Authentication – Request 2. 3. VOMS pseudo -cert 4. y er Qu C=IT/O=INFN VOMS /L=CNAF pseudo /CN=Pinco Palla -cert /CN=proxy 5. Auth DB 6. 7. Bologna, 8/10/2002 Mutual authentication Client. Server Secure communication channel via standard Globus API Client sends request to Server checks correctness of request Server sends back the required info (signed by itself) in a “Pseudo -Certificate” Client checks the validity of the info received Client repeats process for other VOMS’s Client creates proxy certificates containing all the info received into a (non critical) extension WP 4 (EDT) Meeting 3
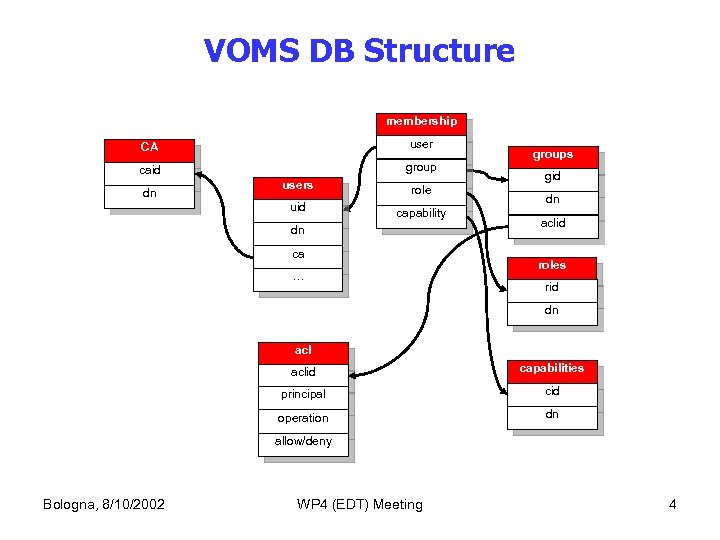
VOMS DB Structure membership CA user caid group dn users uid role capability dn ca … groups gid dn aclid roles rid dn aclid capabilities principal cid operation dn allow/deny Bologna, 8/10/2002 WP 4 (EDT) Meeting 4
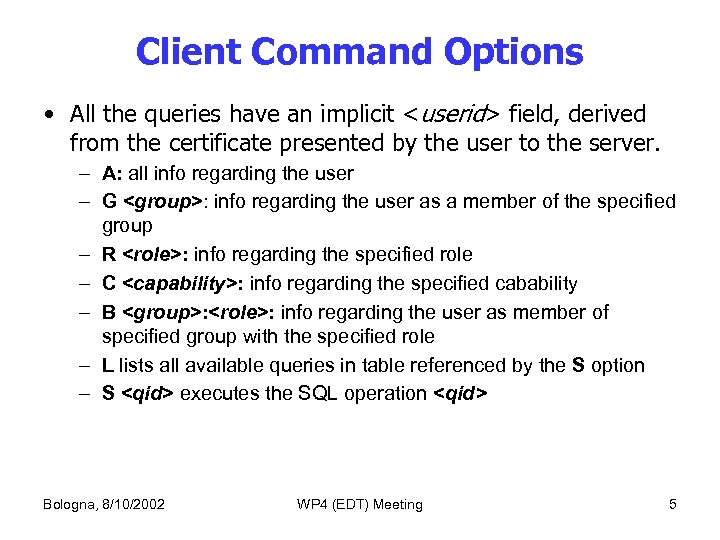
Client Command Options • All the queries have an implicit <userid> field, derived from the certificate presented by the user to the server. – A: all info regarding the user – G <group>: info regarding the user as a member of the specified group – R <role>: info regarding the specified role – C <capability>: info regarding the specified cabability – B <group>: <role>: info regarding the user as member of specified group with the specified role – L lists all available queries in table referenced by the S option – S <qid> executes the SQL operation <qid> Bologna, 8/10/2002 WP 4 (EDT) Meeting 5
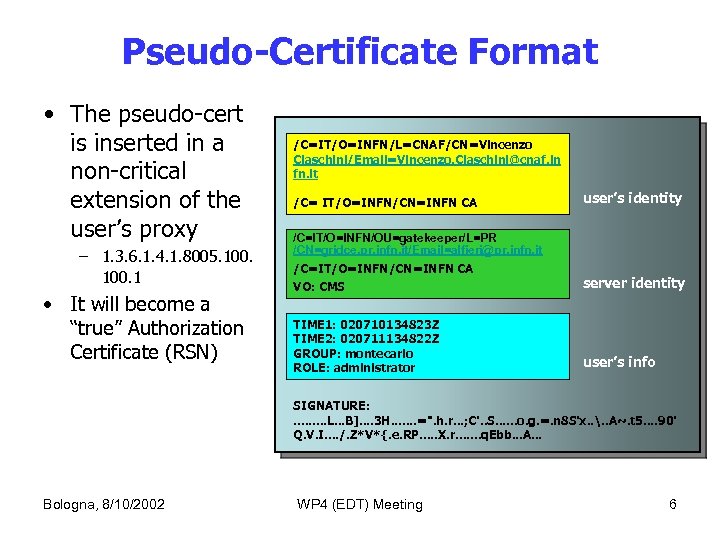
Pseudo-Certificate Format • The pseudo-cert is inserted in a non-critical extension of the user’s proxy – 1. 3. 6. 1. 4. 1. 8005. 100. 1 • It will become a “true” Authorization Certificate (RSN) /C=IT/O=INFN/L=CNAF/CN=Vincenzo Ciaschini/Email=Vincenzo. Ciaschini@cnaf. in fn. it /C= IT/O=INFN/CN=INFN CA user’s identity /C=IT/O=INFN/OU=gatekeeper/L=PR /CN=gridce. pr. infn. it/Email=alfieri@pr. infn. it /C=IT/O=INFN/CN=INFN CA VO: CMS server identity TIME 1: 020710134823 Z TIME 2: 020711134822 Z GROUP: montecarlo ROLE: administrator user’s info SIGNATURE: . . L. . . B]. . 3 H. . . . =". h. r. . . ; C'. . S. . . o. g. =. n 8 S'x. . . . A~. t 5. . 90' Q. V. I. . /. Z*V*{. e. RP. . . X. r. . . . q. Ebb. . . A. . . Bologna, 8/10/2002 WP 4 (EDT) Meeting 6
Intermezzo: mkgridmap++ • Coexistence of VOMS and VO LDAP servers • mkgridmap++ – produces grid-mapfiles from both LDAP and VOMS servers; – new config file directive • voms: // – authenticated access to VOMS (not LDAP) servers • temporary change to VOMS authentication mechanism (? ) Bologna, 8/10/2002 WP 4 (EDT) Meeting 7
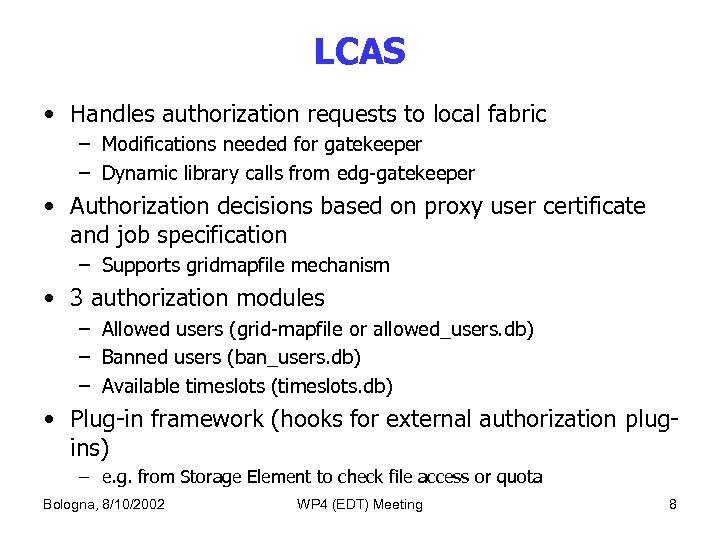
LCAS • Handles authorization requests to local fabric – Modifications needed for gatekeeper – Dynamic library calls from edg-gatekeeper • Authorization decisions based on proxy user certificate and job specification – Supports gridmapfile mechanism • 3 authorization modules – Allowed users (grid-mapfile or allowed_users. db) – Banned users (ban_users. db) – Available timeslots (timeslots. db) • Plug-in framework (hooks for external authorization plugins) – e. g. from Storage Element to check file access or quota Bologna, 8/10/2002 WP 4 (EDT) Meeting 8
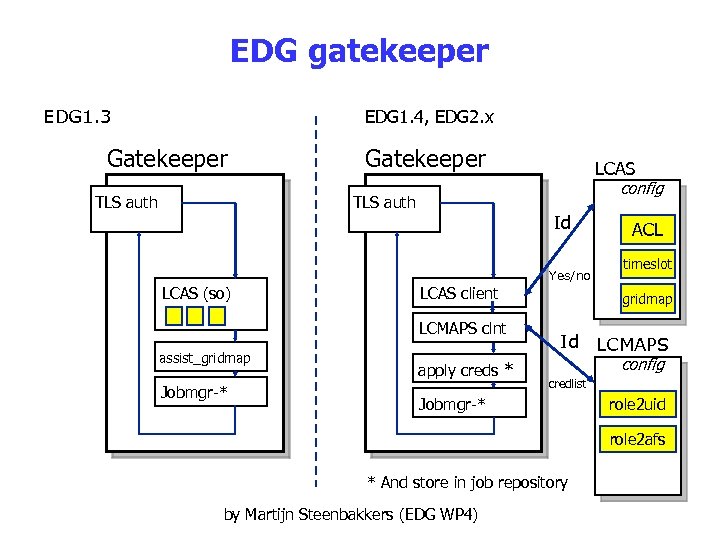
EDG gatekeeper EDG 1. 3 EDG 1. 4, EDG 2. x Gatekeeper TLS auth Gatekeeper LCAS config TLS auth Id Yes/no LCAS (so) LCAS client LCMAPS clnt assist_gridmap Jobmgr-* apply creds * ACL timeslot gridmap Id LCMAPS config credlist Jobmgr-* role 2 uid role 2 afs * And store in job repository by Martijn Steenbakkers (EDG WP 4)
172fdb2e5baae1d339f582fd483c11f6.ppt