953409d46b2435fc397ce6306dfeba4d.ppt
- Количество слайдов: 32
Varna Free University E-BUSINESS Internet payment systems 27 Sept. 99 Prof. Teodora Bakardjieva
Outline • • Introduction Issues related Security Outstanding protocols Mechanisms Advantages and disadvantages Conclusion 27 Sept. 99 2
Introduction • In the past year, the number of users reachable through Internet has increased dramatically • Potential to establish a new kind of open marketplace for goods and services 27 Sept. 99 3
Introduction (cont) • Online shops in Internet – Bookshop (Amazon. com) – Flight Resevation and Hotel Reservation shopping place, etc. • An effective payment mechanism is needed 27 Sept. 99 4
Issues related • • • Security Performance Reliability Efficiency Bandwidth Anonymity (mainly in electronic coins) 27 Sept. 99 5
Security • Internet is not a secure place • There attacks from: – eavesdropping – masquerading – message tampering – replay 27 Sept. 99 6
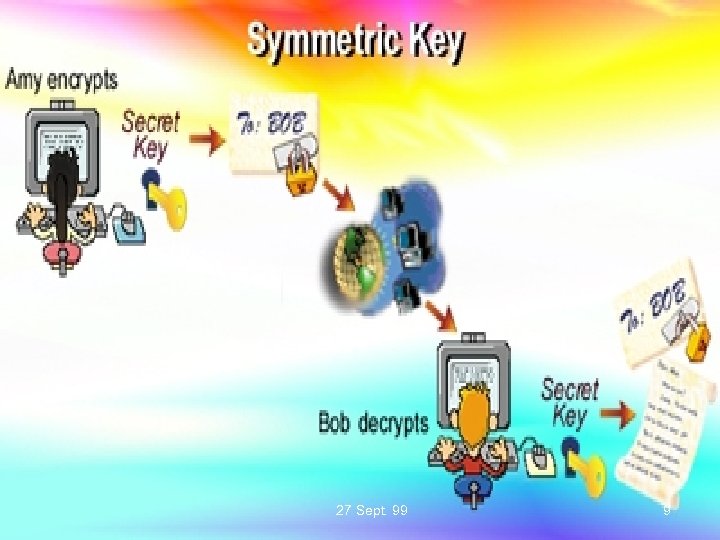
How to solve? • RSA public key cryptography is widely used for authentication and encryption in the computer industry • Using public/private (asymmetric) key pair or symmetric session key to prevent eavesdropping 27 Sept. 99 7
How to solve? (cont) • Using message digest to prevent message tampering • Using nonce to prevent replay • Using digital certificate to prevent masquerading 27 Sept. 99 8
27 Sept. 99 9

27 Sept. 99 10

27 Sept. 99 11
Outstanding protocols • Credit card based – Secure Electronic Transaction (SET) – Secure Socket Layer (SSL) • Electronic coins – Digi. Cash – Net. Cash 27 Sept. 99 12
Credit-card based systems • Parties involved: cardholder, merchant, issuer, acquirer and payment gateway • Transfer user's credit-card number to merchant via insecure network • A trusted third party to authenticate the public key 27 Sept. 99 13
Secure Electronic Transaction (SET) • Developed by VISA and Master. Card • To facilitate secure payment card transactions over the Internet • Digital Certificates create a trust chain throughout the transaction, verifying cardholder and merchant validity • It is the most secure payment protocol 27 Sept. 99 14
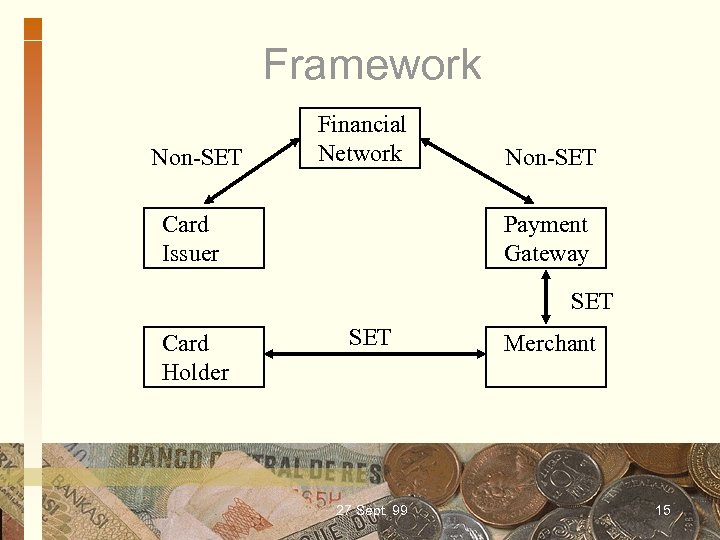
Framework Non-SET Financial Network Card Issuer Non-SET Payment Gateway SET Card Holder SET 27 Sept. 99 Merchant 15
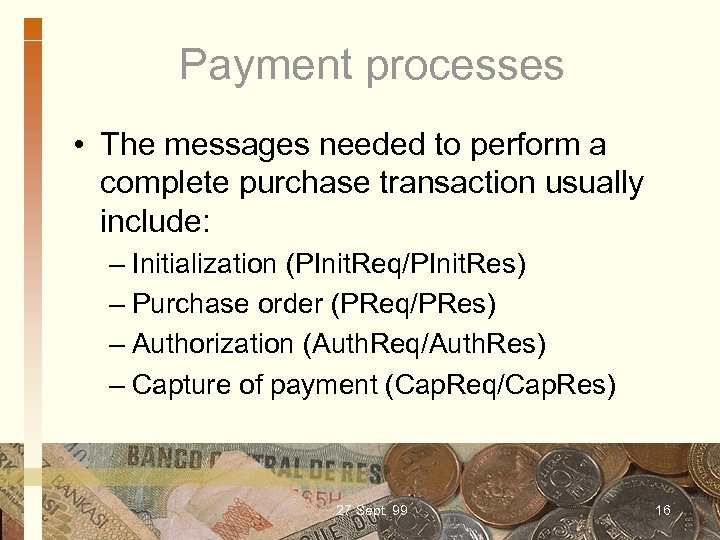
Payment processes • The messages needed to perform a complete purchase transaction usually include: – Initialization (PInit. Req/PInit. Res) – Purchase order (PReq/PRes) – Authorization (Auth. Req/Auth. Res) – Capture of payment (Cap. Req/Cap. Res) 27 Sept. 99 16
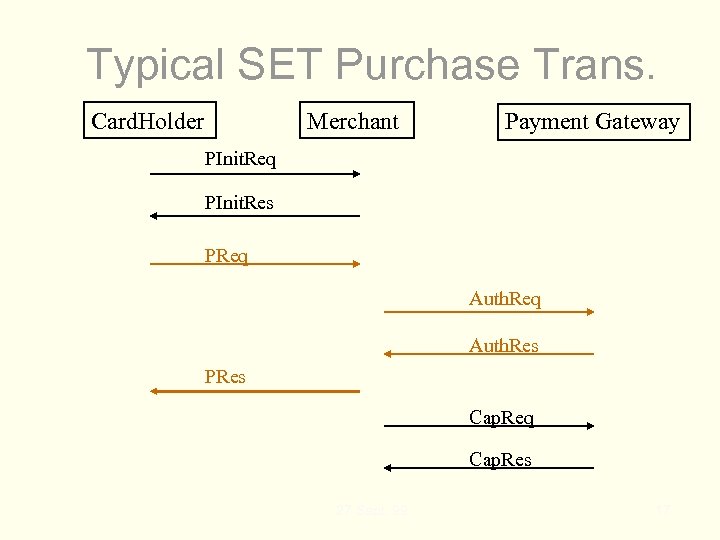
Typical SET Purchase Trans. Card. Holder Merchant Payment Gateway PInit. Req PInit. Res PReq Auth. Res PRes Cap. Req Cap. Res 27 Sept. 99 17
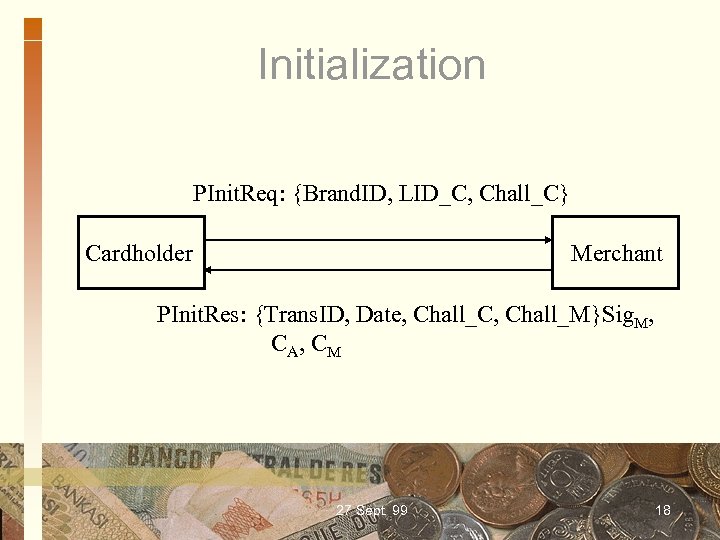
Initialization PInit. Req: {Brand. ID, LID_C, Chall_C} Cardholder Merchant PInit. Res: {Trans. ID, Date, Chall_C, Chall_M}Sig. M, C A, C M 27 Sept. 99 18
![Purchase order PReq: {OI, PI} Cardholder Merchant Pres: {Trans. ID, [Results], Chall_C}Sig. M 27 Purchase order PReq: {OI, PI} Cardholder Merchant Pres: {Trans. ID, [Results], Chall_C}Sig. M 27](https://present5.com/presentation/953409d46b2435fc397ce6306dfeba4d/image-19.jpg)
Purchase order PReq: {OI, PI} Cardholder Merchant Pres: {Trans. ID, [Results], Chall_C}Sig. M 27 Sept. 99 19
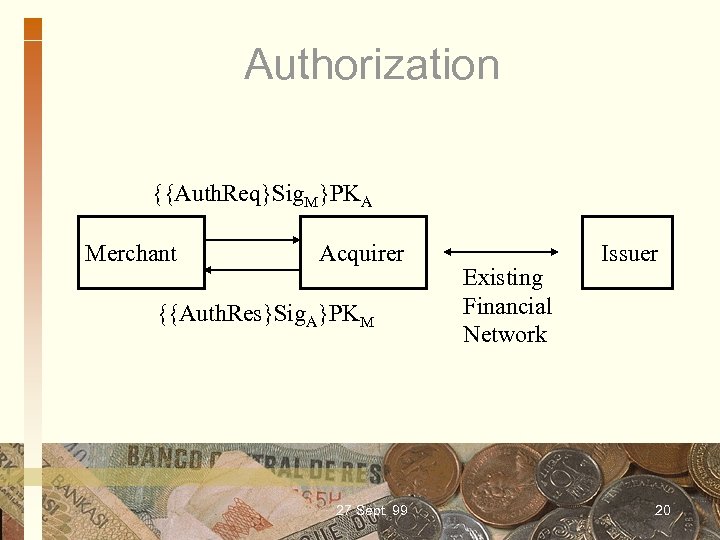
Authorization {{Auth. Req}Sig. M}PKA Merchant Acquirer {{Auth. Res}Sig. A}PKM 27 Sept. 99 Existing Financial Network Issuer 20
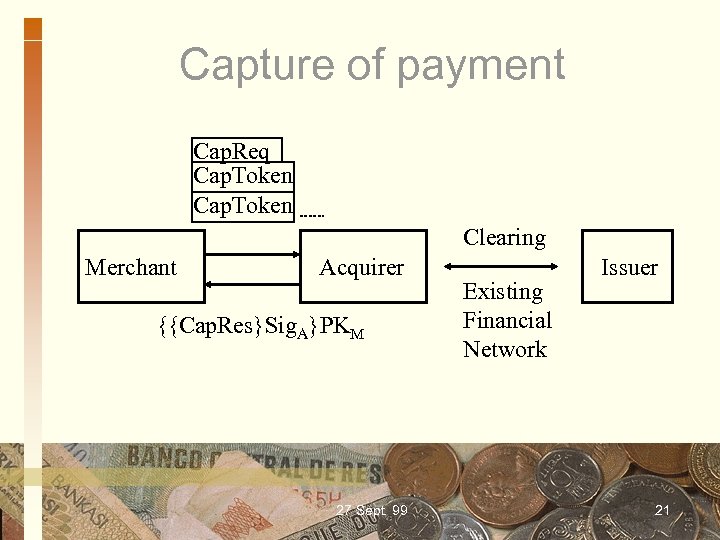
Capture of payment Cap. Req Cap. Token Clearing Merchant Acquirer {{Cap. Res}Sig. A}PKM 27 Sept. 99 Existing Financial Network Issuer 21
Advantages • It is secure enough to protect user's credit-card numbers and personal information from attacks • hardware independent • world-wide usage 27 Sept. 99 22
Disadvantages • User must have credit card • No transfer of funds between users • It is not cost-effective when the payment is small • None of anonymity and it is traceable 27 Sept. 99 23
Electronic cash/coins • Parties involved: client, merchant and bank • Client must have an account in the bank • Less security and encryption • Suitable for small payment, but not for large payment 27 Sept. 99 24
Digi. Cash (E-cash) • A fully anonymous electronic cash system • Using blind signature technique • Parties involved: bank, buyer and merchant • Using RSA public-key cryptography • Special client and merchant software needed 27 Sept. 99 25
Withdrawing Ecash coins • User's cyberwallet software calculates how many digital coins are needed to withdraw the requested amount • software then generates random serial numbers for those coins • the serial numbers are blinded by multiplying it by a random factor 27 Sept. 99 26
Withdrawing Ecash coins (cont) • Blinded coins are packaged into a message, digitally signed with user's private key, encrypted with the bank's public key, then sent to the bank • When the bank receives the message, it checks the signature • After signing the blind coins, the bank returns them to the user 27 Sept. 99 27
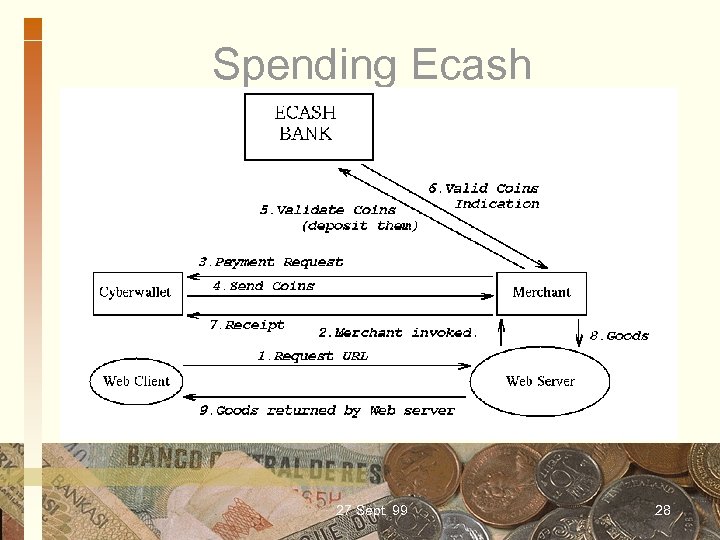
Spending Ecash 27 Sept. 99 28
Advantages • Cost-effective for small payment • User can transfer his electronic coins to other user • No need to apply credit card • Anonymous feature • Hardware independent 27 Sept. 99 29
Disadvantages • It is not suitable for large payment because of lower security • Client must use wallet software in order to store the withdrawn coins from the bank • A large database to store used serial numbers to prevent double spending 27 Sept. 99 30
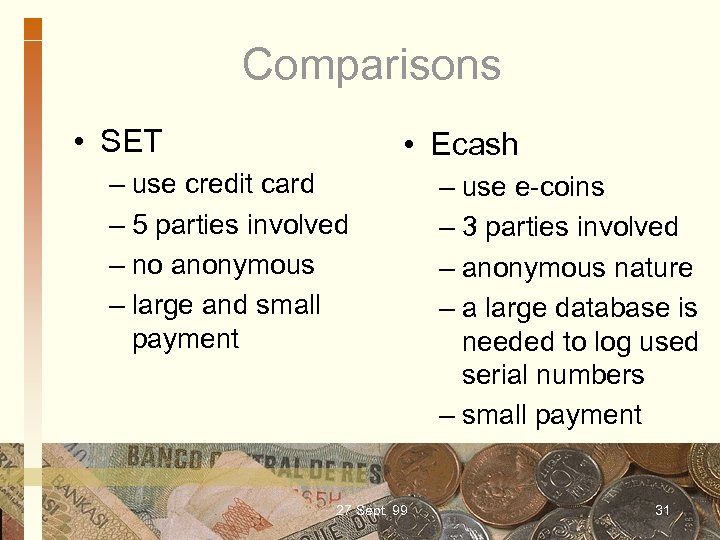
Comparisons • SET • Ecash – use credit card – 5 parties involved – no anonymous – large and small payment 27 Sept. 99 – use e-coins – 3 parties involved – anonymous nature – a large database is needed to log used serial numbers – small payment 31
Conclusions • An effective, secure and reliable Internet payment system is needed • Depending on the payment amount, different level of security is used • SET protocol is an outstanding payment protocol for secure electronic commerce 27 Sept. 99 32
953409d46b2435fc397ce6306dfeba4d.ppt