49ddac34d54ea30ff9cd463abbb01c86.ppt
- Количество слайдов: 24
Using Traffic Shaping to Combat Spam David Cawley, Senior Engineer December 12 th, 2007
Overview 1. Evolution of E-mail & Spam 2. Spamonomics 3. SMTP Multiplexing 4. Traffic Shaping 5. Asynchronous IO 6. Passive OS Fingerprinting
The Dawn of E-mail • 1965 MIT shared mainframe • 1971 The @ symbol • 1976 Queen of England sends an e-mail • 1982 IETF RFC 821/822 • 1989 Lotus Notes released (35 k copies sold) • 1996 Microsoft Internet Mail 1. 0 • 2001 IETF RFC 2821/2822
Attempts to secure. . . • SMTP is inherently insecure • SMTP-Auth/TLS • SPF • Sender-ID • Why it didn't stop spam
The Evolution of Spam • 1978 The first spam • 1988 Usenet cross-posting • 1993 “spam” coined as a name • 1997 Open Relays abused • 2000 Birth of Nigerian spam • 2001 Formail exploit • 2003 Sobig virus sends spam
The Evolution of Spam • 2003 CAN-SPAM act • 2004 Bill gates prediction & botnets • 2005 Image spam, Ascii art • 2006 Animated images, flash, pdf • 2007 mp 3, excel, p 2 p botnets
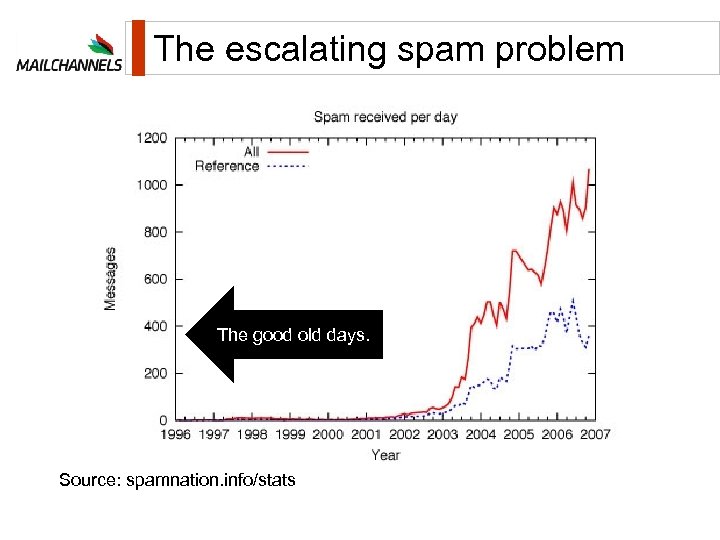
The escalating spam problem The good old days. Source: spamnation. info/stats
![Spammer Economics • 0. 02% people click and buy [source: NY Times] • Average Spammer Economics • 0. 02% people click and buy [source: NY Times] • Average](https://present5.com/presentation/49ddac34d54ea30ff9cd463abbb01c86/image-8.jpg)
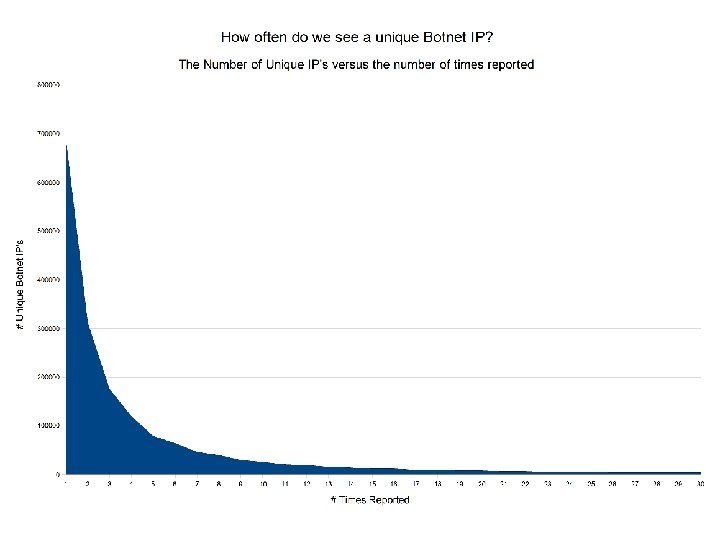
Spammer Economics • 0. 02% people click and buy [source: NY Times] • Average filter effectiveness is 90% – 1/10 of spam messages get through • Improve effectiveness to 95% – 1/20 of spam messages get through • Spammer Solution? – Double spam volume – Same profit
Traditional Filtering • MD 5's, Fuzzy Signatures, Bayesian • Header Regex, RBL's, URL Lists, Grey Listing • Problems – Obfuscation Techniques – Formats – html, image, pdf, doc, xls, ole, mp 3. . – Zombies, Botnets
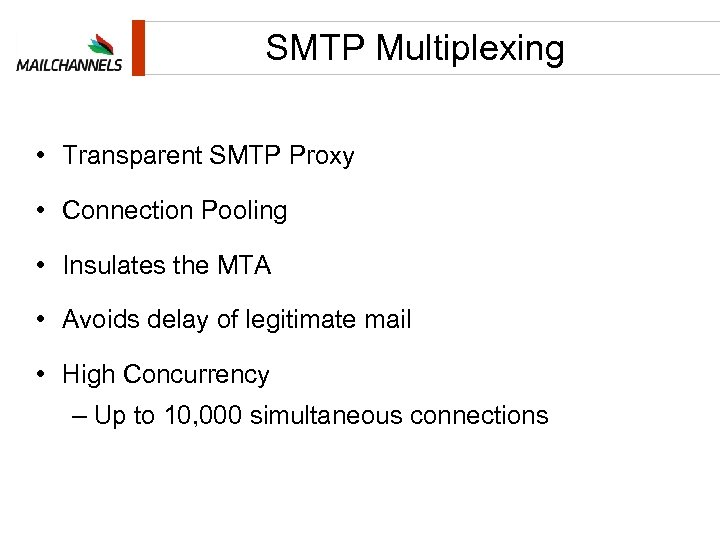
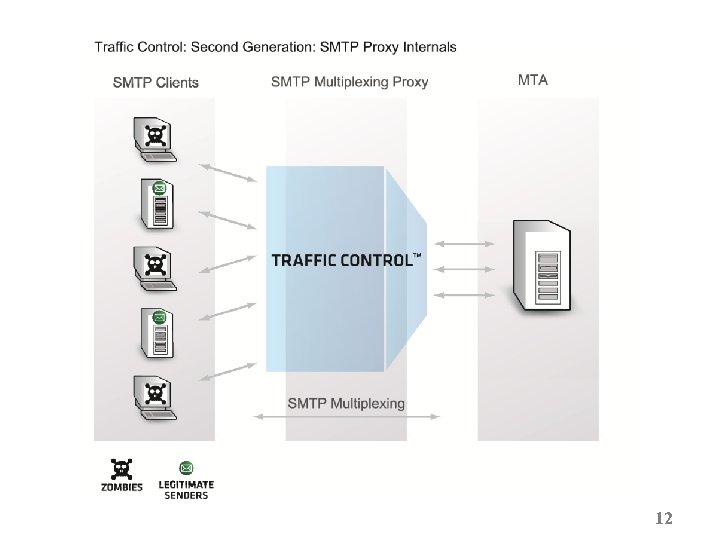
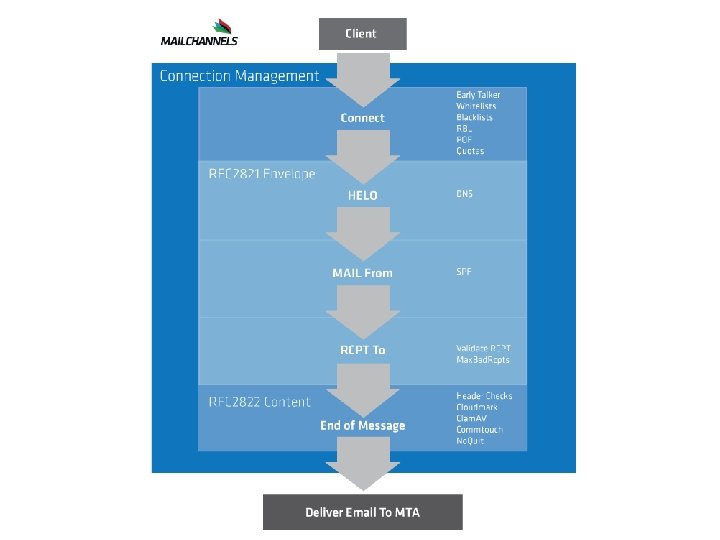
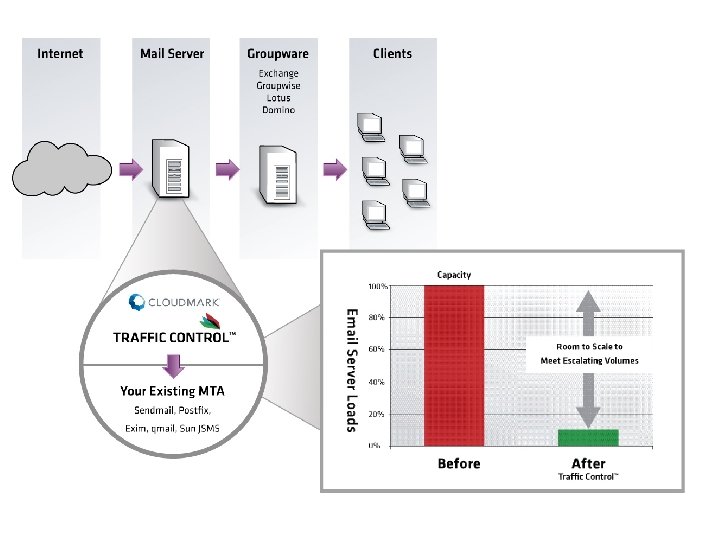
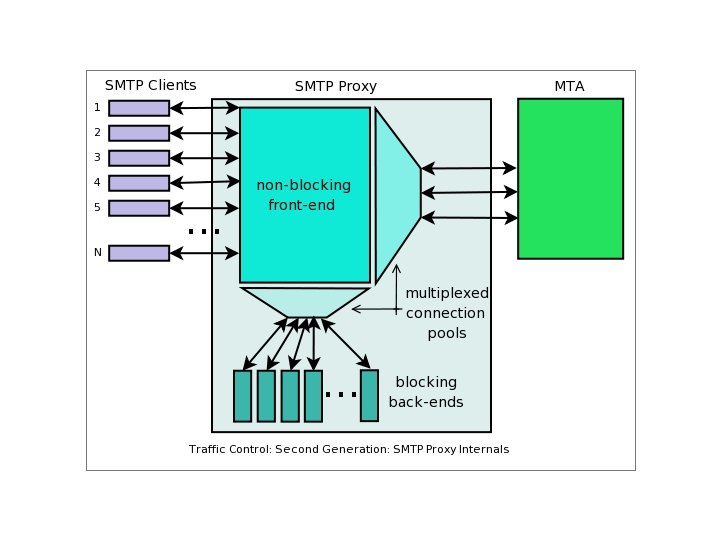
SMTP Multiplexing • Transparent SMTP Proxy • Connection Pooling • Insulates the MTA • Avoids delay of legitimate mail • High Concurrency – Up to 10, 000 simultaneous connections
12
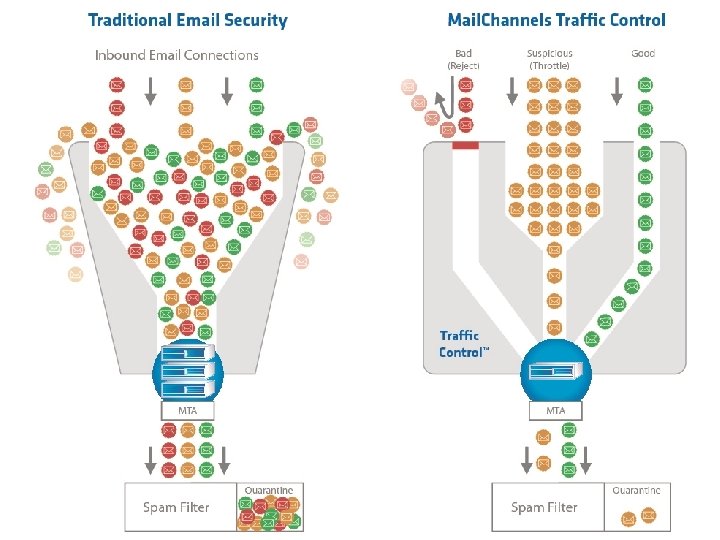
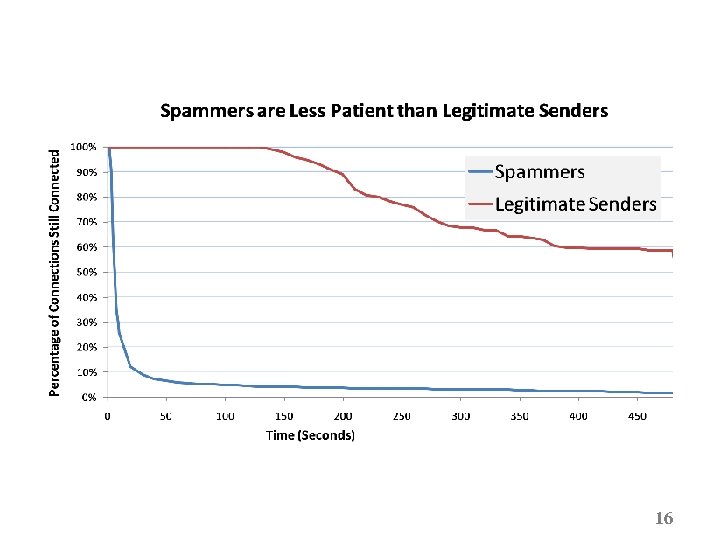
Traffic Shaping • What can we do? • Provide a Quality of Service • Reputation Network • Throttle unknown senders • Fast track legitimate senders
16
Does Sendmail Throttle? ratecontrol Connection. Rate. Throttle conncontrol
Asynchronous IO • Non-Blocking front end • Blocking Back-end • Event driven • Finite State Machine • Management of Resources
Passive OS Fingerprinting 1. Look at IP packet data 2. Determine the Operating System 3. Decision to Throttle
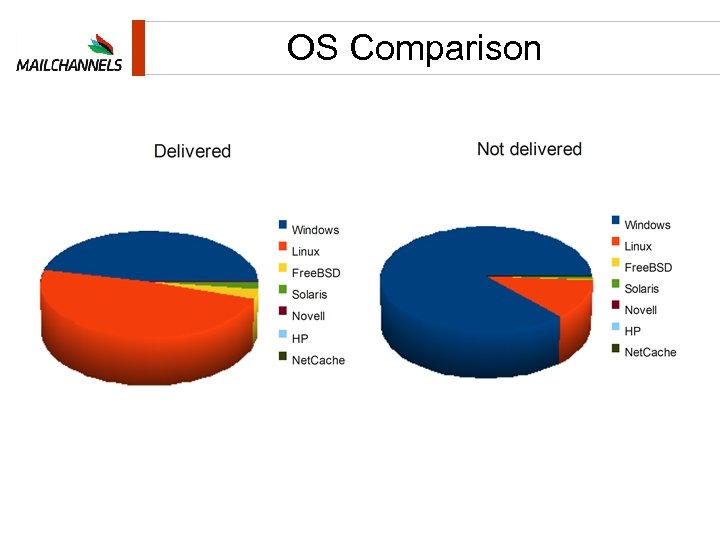
OS Comparison
Conclusions 1. Spamming is driven by economics 2. Botnet operators need to make money 3. Slowing down spam makes it go away

Nick Shelness, Former CTO, Lotus: “I am able to report that I have been running an instance of Traffic. Control in my own network for four months, and that it has reduced the volume of spam hitting my boundary MTAs on most days by approximately 95%. ” questions@mailchannels. com +1 -778 -785 -6143 www. mailchannels. com
49ddac34d54ea30ff9cd463abbb01c86.ppt