35ac234592aa4b18332118be9cac3294.ppt
- Количество слайдов: 23
 Using Honeynets for Internet Situational Awareness Vinod Yegneswaran, Paul Barford University of Wisconsin, Madison Hotnets 2005 Vern Paxson ICSI, LBNL
Using Honeynets for Internet Situational Awareness Vinod Yegneswaran, Paul Barford University of Wisconsin, Madison Hotnets 2005 Vern Paxson ICSI, LBNL
 Motivation o Currrent tasks for security analysts o Abuse monitoring o Audit and forensic analysis o NIDS/Firewall/ACL configuration o Vulnerability testing o Policy maintenance o Liaison activities o Network management o End host management 2
Motivation o Currrent tasks for security analysts o Abuse monitoring o Audit and forensic analysis o NIDS/Firewall/ACL configuration o Vulnerability testing o Policy maintenance o Liaison activities o Network management o End host management 2
 NIDS: State of the art o Pinpoint descriptions of low-level activities o Source A launched CVE-XXX against Dest B o Large volume of alerts o Too many false alarms o Vulnerable to flooding attacks / IP spoofing o Continual manual update of signatures o Lack of “longitudinal” baseline o Lack of breadth for root-cause inference 3
NIDS: State of the art o Pinpoint descriptions of low-level activities o Source A launched CVE-XXX against Dest B o Large volume of alerts o Too many false alarms o Vulnerable to flooding attacks / IP spoofing o Continual manual update of signatures o Lack of “longitudinal” baseline o Lack of breadth for root-cause inference 3
 Our vision o Network “Situational Awareness” (Net. SA) o “Degree of consistency between one’s perception of their situation and reality” -- US Navy o “an accurate set of information about one’s environment scaled to specific level of interest” -- NCOIC o Elevate quality and timeliness of alerts 4
Our vision o Network “Situational Awareness” (Net. SA) o “Degree of consistency between one’s perception of their situation and reality” -- US Navy o “an accurate set of information about one’s environment scaled to specific level of interest” -- NCOIC o Elevate quality and timeliness of alerts 4
 Our approach o Developing Net. SA “building blocks” toward o o Automated incident discovery Robust classification Real-time event notification Forensic analysis capabilities o Honeynet situational awareness o Rich source of information of large-scale malicious activity o Accurate attribution of events such as botnets, worms and misconfiguration 5
Our approach o Developing Net. SA “building blocks” toward o o Automated incident discovery Robust classification Real-time event notification Forensic analysis capabilities o Honeynet situational awareness o Rich source of information of large-scale malicious activity o Accurate attribution of events such as botnets, worms and misconfiguration 5
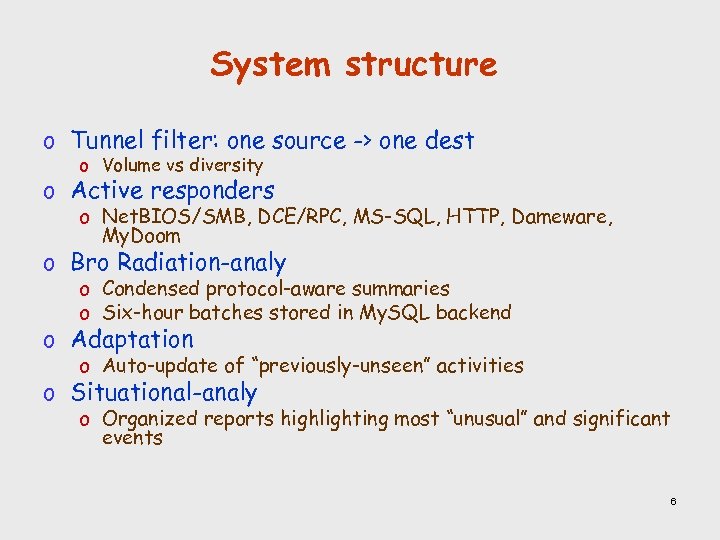 System structure o Tunnel filter: one source -> one dest o Volume vs diversity o Active responders o Net. BIOS/SMB, DCE/RPC, MS-SQL, HTTP, Dameware, My. Doom o Bro Radiation-analy o Condensed protocol-aware summaries o Six-hour batches stored in My. SQL backend o Adaptation o Auto-update of “previously-unseen” activities o Situational-analy o Organized reports highlighting most “unusual” and significant events 6
System structure o Tunnel filter: one source -> one dest o Volume vs diversity o Active responders o Net. BIOS/SMB, DCE/RPC, MS-SQL, HTTP, Dameware, My. Doom o Bro Radiation-analy o Condensed protocol-aware summaries o Six-hour batches stored in My. SQL backend o Adaptation o Auto-update of “previously-unseen” activities o Situational-analy o Organized reports highlighting most “unusual” and significant events 6
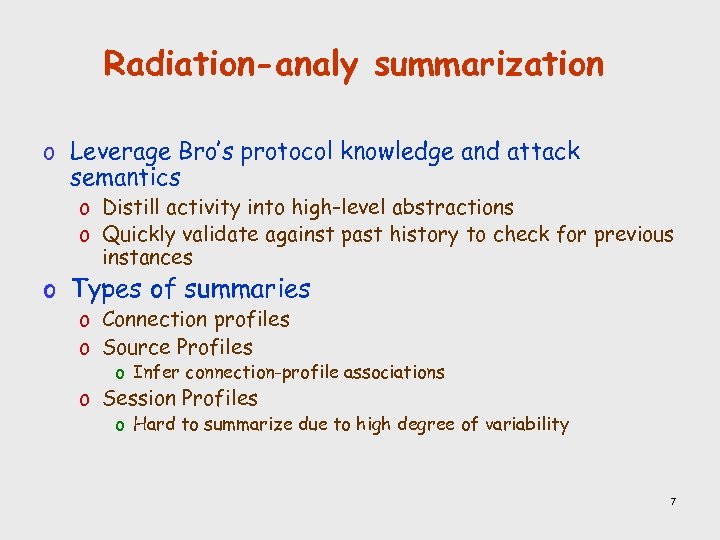 Radiation-analy summarization o Leverage Bro’s protocol knowledge and attack semantics o Distill activity into high-level abstractions o Quickly validate against past history to check for previous instances o Types of summaries o Connection profiles o Source Profiles o Infer connection-profile associations o Session Profiles o Hard to summarize due to high degree of variability 7
Radiation-analy summarization o Leverage Bro’s protocol knowledge and attack semantics o Distill activity into high-level abstractions o Quickly validate against past history to check for previous instances o Types of summaries o Connection profiles o Source Profiles o Infer connection-profile associations o Session Profiles o Hard to summarize due to high degree of variability 7
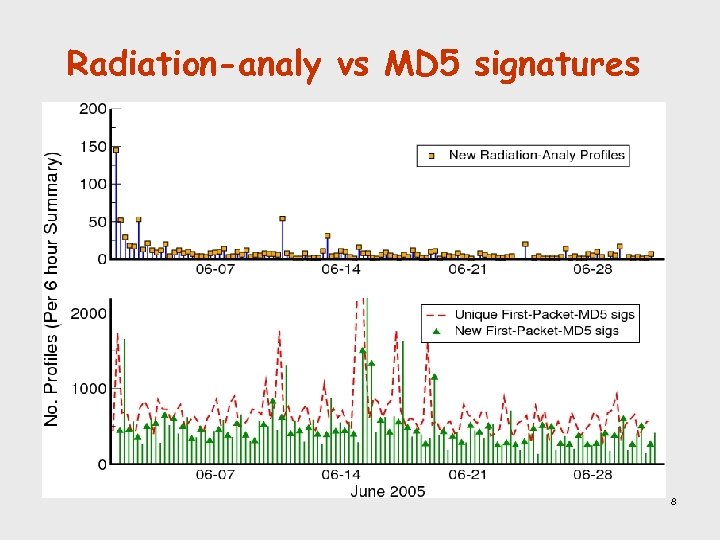 Radiation-analy vs MD 5 signatures 8
Radiation-analy vs MD 5 signatures 8
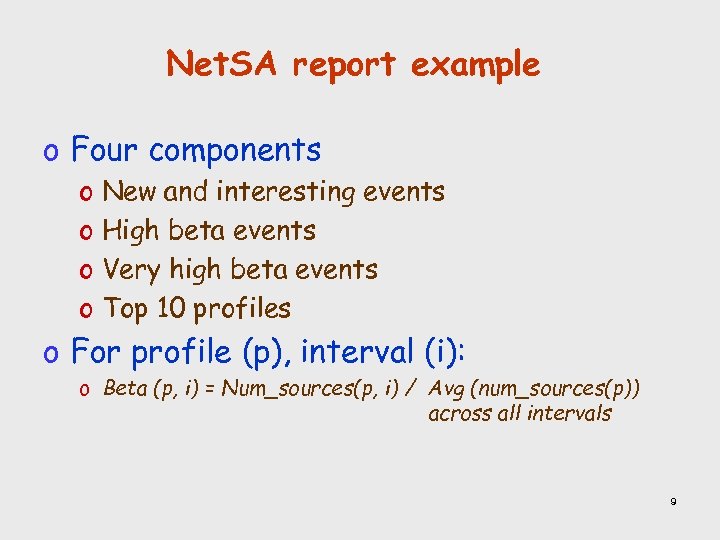 Net. SA report example o Four components o New and interesting events o High beta events o Very high beta events o Top 10 profiles o For profile (p), interval (i): o Beta (p, i) = Num_sources(p, i) / Avg (num_sources(p)) across all intervals 9
Net. SA report example o Four components o New and interesting events o High beta events o Very high beta events o Top 10 profiles o For profile (p), interval (i): o Beta (p, i) = Num_sources(p, i) / Avg (num_sources(p)) across all intervals 9
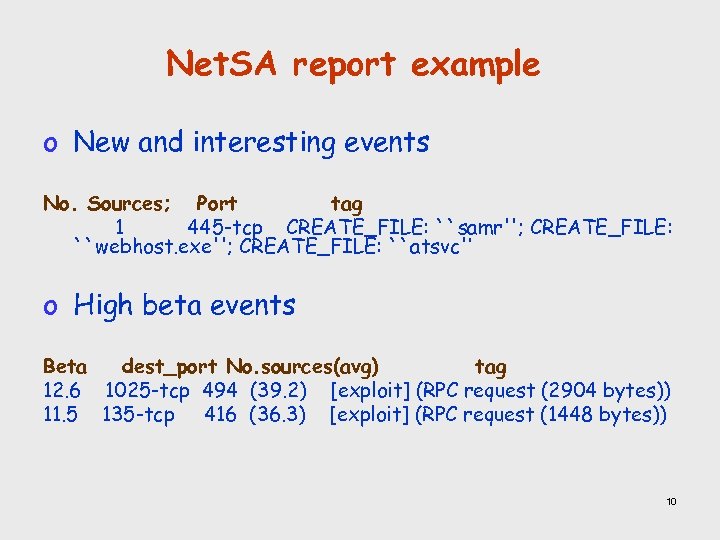 Net. SA report example o New and interesting events No. Sources; Port tag 1 445 -tcp CREATE_FILE: ``samr''; CREATE_FILE: ``webhost. exe''; CREATE_FILE: ``atsvc'‘ o High beta events Beta dest_port No. sources(avg) tag 12. 6 1025 -tcp 494 (39. 2) [exploit] (RPC request (2904 bytes)) 11. 5 135 -tcp 416 (36. 3) [exploit] (RPC request (1448 bytes)) 10
Net. SA report example o New and interesting events No. Sources; Port tag 1 445 -tcp CREATE_FILE: ``samr''; CREATE_FILE: ``webhost. exe''; CREATE_FILE: ``atsvc'‘ o High beta events Beta dest_port No. sources(avg) tag 12. 6 1025 -tcp 494 (39. 2) [exploit] (RPC request (2904 bytes)) 11. 5 135 -tcp 416 (36. 3) [exploit] (RPC request (1448 bytes)) 10
![Net. SA report example o Very high beta events (beta > 10) TAG: 1025/tcp/[exploit] Net. SA report example o Very high beta events (beta > 10) TAG: 1025/tcp/[exploit]](https://present5.com/presentation/35ac234592aa4b18332118be9cac3294/image-11.jpg) Net. SA report example o Very high beta events (beta > 10) TAG: 1025/tcp/[exploit] (RPC request (2904 bytes)) Hour 0. . 5 srcs: 97, 93, 79, 74, 68, 94, src-overlaps: 0, 8, 13, 10, 8, 10, /8 s: 25, 26, 19, 21, 16, 19, dsts: 103, 97, 80, 71, 76, 96, dst-overlaps: 0, 14, 12, 8, 8, 8, o Top 10 profiles Port 135 -tcp 1025 -tcp 135 -tcp … No. Sources Tag 591 RPC bind: afa 8 bd 80 -7 d 8 a-11 c 9 -bef 4 -08002 b 10298 len=72; RPC request (24 bytes) 494 [exploit] (RPC request (2904 bytes)) 416 [exploit] (RPC request (1448 bytes)) 11
Net. SA report example o Very high beta events (beta > 10) TAG: 1025/tcp/[exploit] (RPC request (2904 bytes)) Hour 0. . 5 srcs: 97, 93, 79, 74, 68, 94, src-overlaps: 0, 8, 13, 10, 8, 10, /8 s: 25, 26, 19, 21, 16, 19, dsts: 103, 97, 80, 71, 76, 96, dst-overlaps: 0, 14, 12, 8, 8, 8, o Top 10 profiles Port 135 -tcp 1025 -tcp 135 -tcp … No. Sources Tag 591 RPC bind: afa 8 bd 80 -7 d 8 a-11 c 9 -bef 4 -08002 b 10298 len=72; RPC request (24 bytes) 494 [exploit] (RPC request (2904 bytes)) 416 [exploit] (RPC request (1448 bytes)) 11
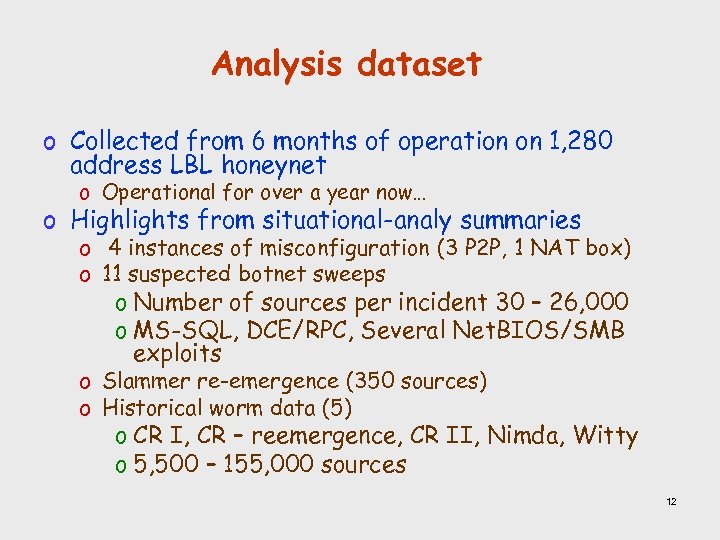 Analysis dataset o Collected from 6 months of operation on 1, 280 address LBL honeynet o Operational for over a year now… o Highlights from situational-analy summaries o 4 instances of misconfiguration (3 P 2 P, 1 NAT box) o 11 suspected botnet sweeps o Number of sources per incident 30 – 26, 000 o MS-SQL, DCE/RPC, Several Net. BIOS/SMB exploits o Slammer re-emergence (350 sources) o Historical worm data (5) o CR I, CR – reemergence, CR II, Nimda, Witty o 5, 500 – 155, 000 sources 12
Analysis dataset o Collected from 6 months of operation on 1, 280 address LBL honeynet o Operational for over a year now… o Highlights from situational-analy summaries o 4 instances of misconfiguration (3 P 2 P, 1 NAT box) o 11 suspected botnet sweeps o Number of sources per incident 30 – 26, 000 o MS-SQL, DCE/RPC, Several Net. BIOS/SMB exploits o Slammer re-emergence (350 sources) o Historical worm data (5) o CR I, CR – reemergence, CR II, Nimda, Witty o 5, 500 – 155, 000 sources 12
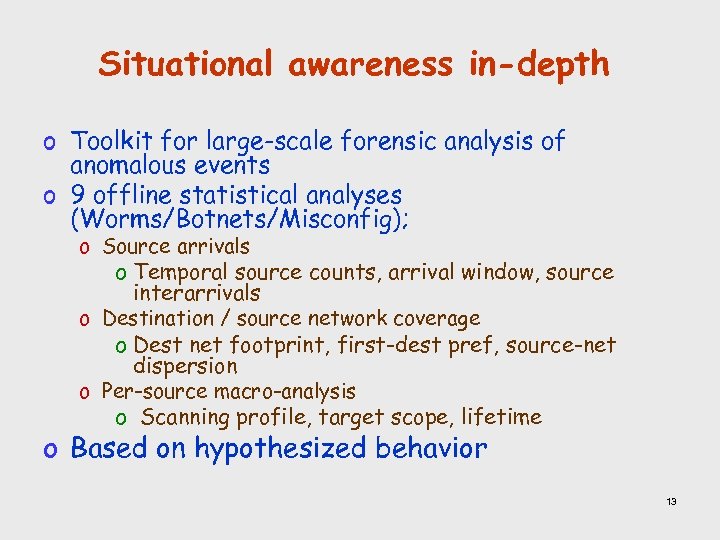 Situational awareness in-depth o Toolkit for large-scale forensic analysis of anomalous events o 9 offline statistical analyses (Worms/Botnets/Misconfig); o Source arrivals o Temporal source counts, arrival window, source interarrivals o Destination / source network coverage o Dest net footprint, first-dest pref, source-net dispersion o Per-source macro-analysis o Scanning profile, target scope, lifetime o Based on hypothesized behavior 13
Situational awareness in-depth o Toolkit for large-scale forensic analysis of anomalous events o 9 offline statistical analyses (Worms/Botnets/Misconfig); o Source arrivals o Temporal source counts, arrival window, source interarrivals o Destination / source network coverage o Dest net footprint, first-dest pref, source-net dispersion o Per-source macro-analysis o Scanning profile, target scope, lifetime o Based on hypothesized behavior 13
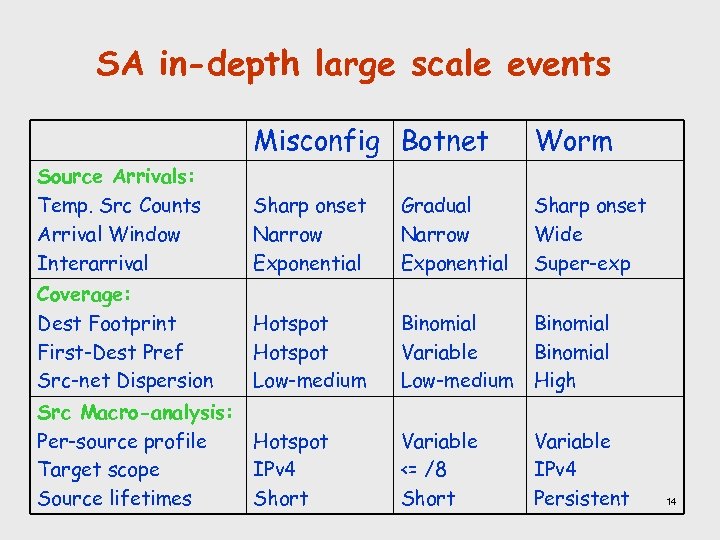 SA in-depth large scale events Misconfig Botnet Worm Source Arrivals: Temp. Src Counts Arrival Window Interarrival Sharp onset Narrow Exponential Gradual Narrow Exponential Sharp onset Wide Super-exp Coverage: Dest Footprint First-Dest Pref Src-net Dispersion Hotspot Low-medium Binomial Variable Binomial Low-medium High Src Macro-analysis: Per-source profile Hotspot Target scope IPv 4 Source lifetimes Short Variable <= /8 Short Variable IPv 4 Persistent 14
SA in-depth large scale events Misconfig Botnet Worm Source Arrivals: Temp. Src Counts Arrival Window Interarrival Sharp onset Narrow Exponential Gradual Narrow Exponential Sharp onset Wide Super-exp Coverage: Dest Footprint First-Dest Pref Src-net Dispersion Hotspot Low-medium Binomial Variable Binomial Low-medium High Src Macro-analysis: Per-source profile Hotspot Target scope IPv 4 Source lifetimes Short Variable <= /8 Short Variable IPv 4 Persistent 14
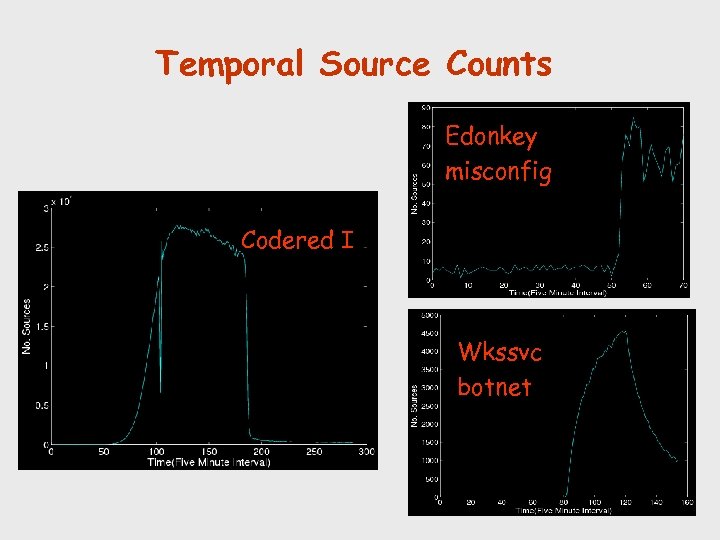 Temporal Source Counts Edonkey misconfig Codered I Wkssvc botnet 15
Temporal Source Counts Edonkey misconfig Codered I Wkssvc botnet 15
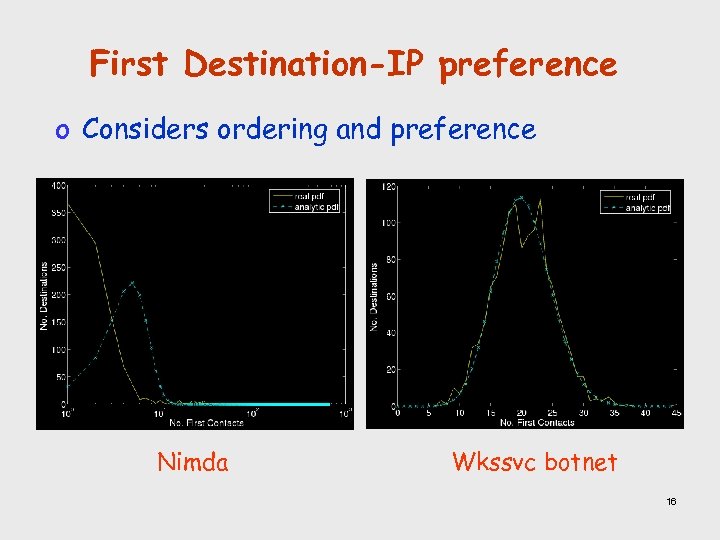 First Destination-IP preference o Considers ordering and preference Nimda Wkssvc botnet 16
First Destination-IP preference o Considers ordering and preference Nimda Wkssvc botnet 16
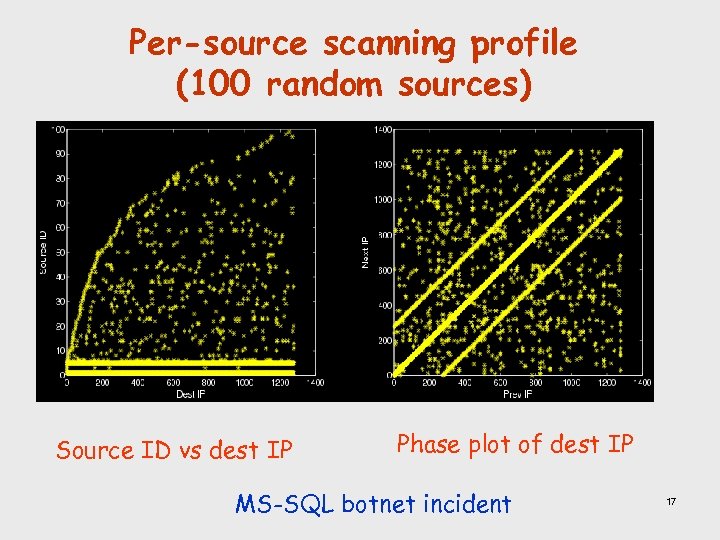 Per-source scanning profile (100 random sources) Source ID vs dest IP Phase plot of dest IP MS-SQL botnet incident 17
Per-source scanning profile (100 random sources) Source ID vs dest IP Phase plot of dest IP MS-SQL botnet incident 17
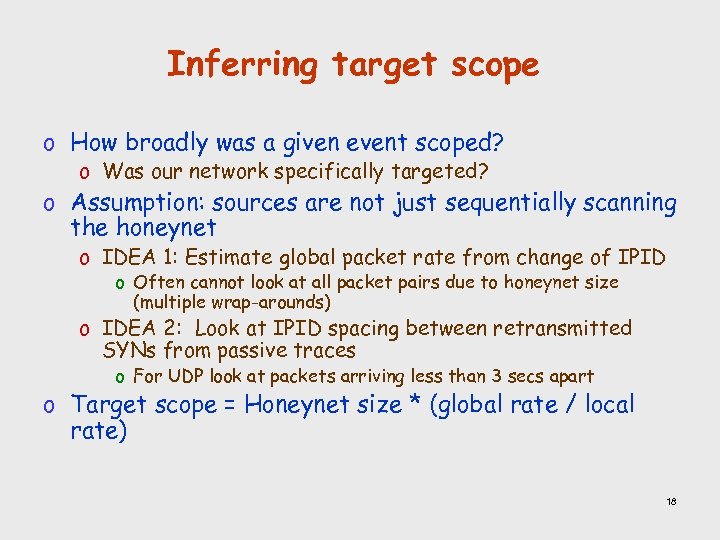 Inferring target scope o How broadly was a given event scoped? o Was our network specifically targeted? o Assumption: sources are not just sequentially scanning the honeynet o IDEA 1: Estimate global packet rate from change of IPID o Often cannot look at all packet pairs due to honeynet size (multiple wrap-arounds) o IDEA 2: Look at IPID spacing between retransmitted SYNs from passive traces o For UDP look at packets arriving less than 3 secs apart o Target scope = Honeynet size * (global rate / local rate) 18
Inferring target scope o How broadly was a given event scoped? o Was our network specifically targeted? o Assumption: sources are not just sequentially scanning the honeynet o IDEA 1: Estimate global packet rate from change of IPID o Often cannot look at all packet pairs due to honeynet size (multiple wrap-arounds) o IDEA 2: Look at IPID spacing between retransmitted SYNs from passive traces o For UDP look at packets arriving less than 3 secs apart o Target scope = Honeynet size * (global rate / local rate) 18
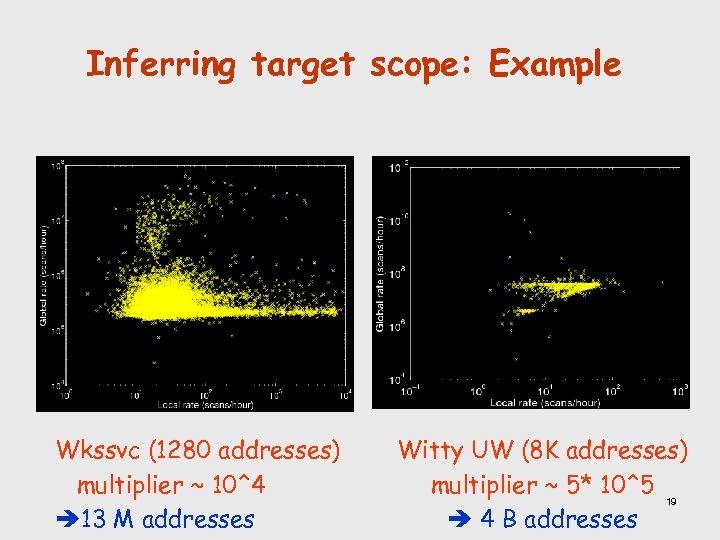 Inferring target scope: Example Wkssvc (1280 addresses) multiplier ~ 10^4 13 M addresses Witty UW (8 K addresses) multiplier ~ 5* 10^5 19 4 B addresses
Inferring target scope: Example Wkssvc (1280 addresses) multiplier ~ 10^4 13 M addresses Witty UW (8 K addresses) multiplier ~ 5* 10^5 19 4 B addresses
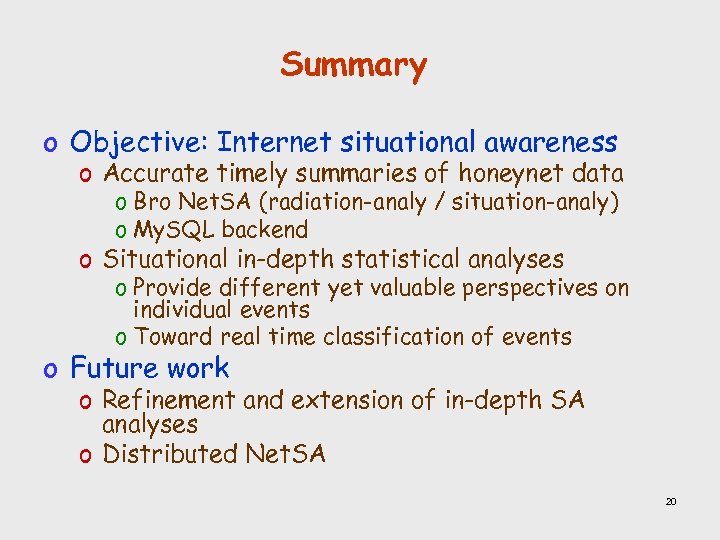 Summary o Objective: Internet situational awareness o Accurate timely summaries of honeynet data o Bro Net. SA (radiation-analy / situation-analy) o My. SQL backend o Situational in-depth statistical analyses o Provide different yet valuable perspectives on individual events o Toward real time classification of events o Future work o Refinement and extension of in-depth SA analyses o Distributed Net. SA 20
Summary o Objective: Internet situational awareness o Accurate timely summaries of honeynet data o Bro Net. SA (radiation-analy / situation-analy) o My. SQL backend o Situational in-depth statistical analyses o Provide different yet valuable perspectives on individual events o Toward real time classification of events o Future work o Refinement and extension of in-depth SA analyses o Distributed Net. SA 20
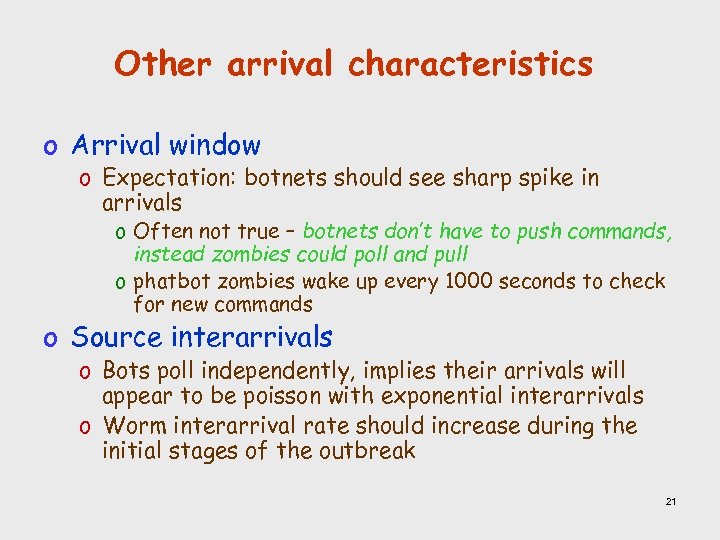 Other arrival characteristics o Arrival window o Expectation: botnets should see sharp spike in arrivals o Often not true – botnets don’t have to push commands, instead zombies could poll and pull o phatbot zombies wake up every 1000 seconds to check for new commands o Source interarrivals o Bots poll independently, implies their arrivals will appear to be poisson with exponential interarrivals o Worm interarrival rate should increase during the initial stages of the outbreak 21
Other arrival characteristics o Arrival window o Expectation: botnets should see sharp spike in arrivals o Often not true – botnets don’t have to push commands, instead zombies could poll and pull o phatbot zombies wake up every 1000 seconds to check for new commands o Source interarrivals o Bots poll independently, implies their arrivals will appear to be poisson with exponential interarrivals o Worm interarrival rate should increase during the initial stages of the outbreak 21
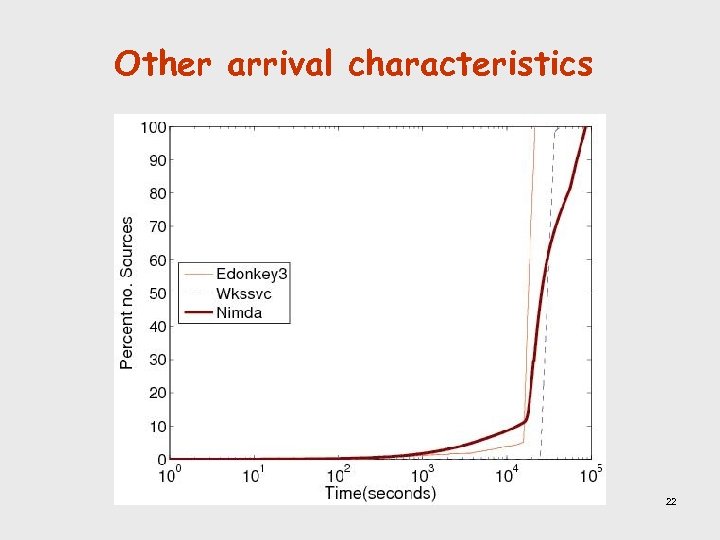 Other arrival characteristics 22
Other arrival characteristics 22
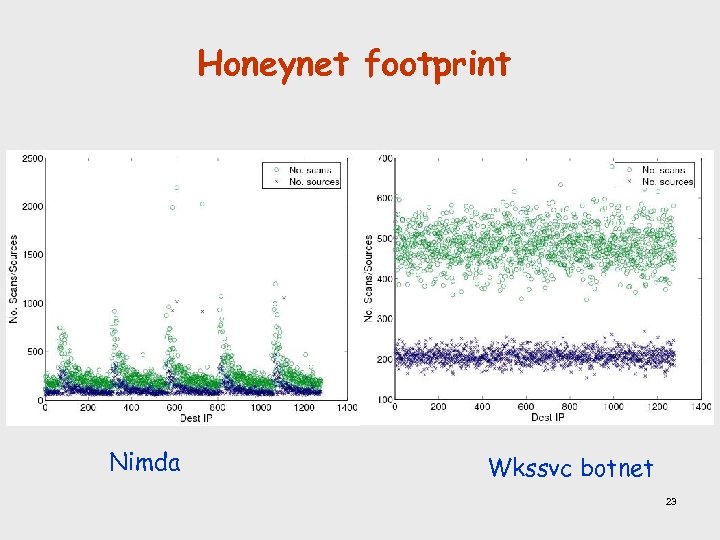 Honeynet footprint Nimda Wkssvc botnet 23
Honeynet footprint Nimda Wkssvc botnet 23


