a53fff8b9912f37825ba9612415f81b3.ppt
- Количество слайдов: 48
UNIVERSITE LIBRE DE BRUXELLES Solvay Business School SEMINAIRE DE TECHNOLOGIES DE L’INFORMATION ET DE LA COMMUNICATION GEST 116 e. Business – Payments & Security Pascale Vande Velde
Content of e. Business course Technologies de l’information et de La communication Introduction – Part II Payments & Security Supply chain management V. 1. 1 Solvay Business School 2
Technologies de l’information et de La communication Introduction to epayments Network security principles and concepts B 2 C e. Payments solutions B 2 B e. Payments solutions V. 1. 1 Solvay Business School 3
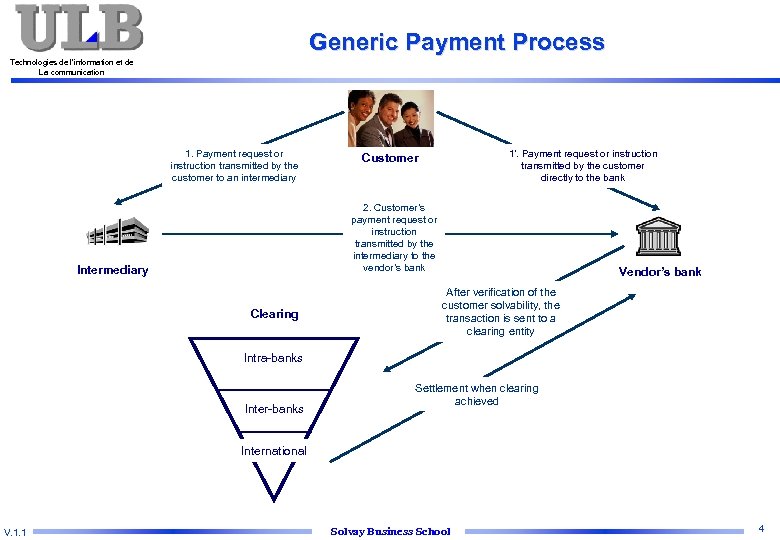
Generic Payment Process Technologies de l’information et de La communication 1. Payment request or instruction transmitted by the customer to an intermediary 1’. Payment request or instruction transmitted by the customer directly to the bank Customer 2. Customer’s payment request or instruction transmitted by the intermediary to the vendor’s bank Intermediary Clearing Vendor’s bank After verification of the customer solvability, the transaction is sent to a clearing entity Intra-banks Inter-banks Settlement when clearing achieved International V. 1. 1 Solvay Business School 4
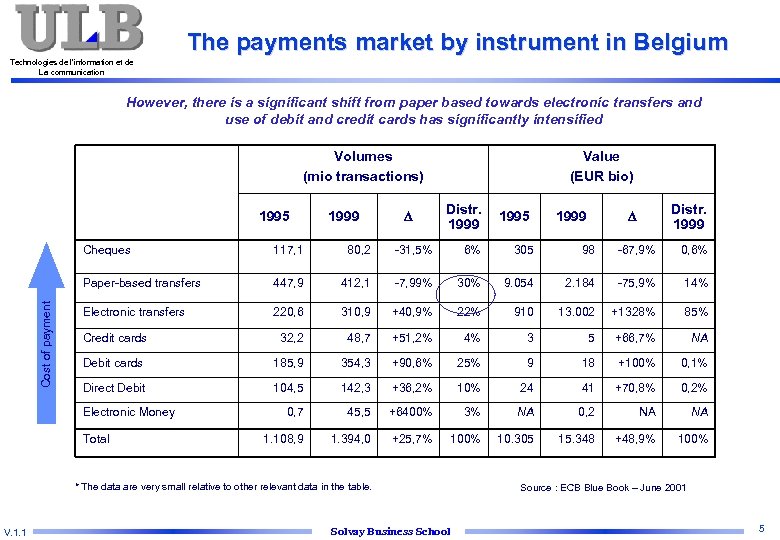
The payments market by instrument in Belgium Technologies de l’information et de La communication However, there is a significant shift from paper based towards electronic transfers and use of debit and credit cards has significantly intensified Volumes (mio transactions) 1995 1999 Value (EUR bio) Distr. 1999 1995 Distr. 1999 117, 1 80, 2 -31, 5% 6% 305 98 -67, 9% 0, 6% Paper-based transfers Cost of payment Cheques 447, 9 412, 1 -7, 99% 30% 9. 054 2. 184 -75, 9% 14% Electronic transfers 220, 6 310, 9 +40, 9% 22% 910 13. 002 +1328% 85% Credit cards 32, 2 48, 7 +51, 2% 4% 3 5 +66, 7% NA Debit cards 185, 9 354, 3 +90, 6% 25% 9 18 +100% 0, 1% Direct Debit 104, 5 142, 3 +36, 2% 10% 24 41 +70, 8% 0, 2% 0, 7 45, 5 +6400% 3% NA 0, 2 NA NA 1. 108, 9 1. 394, 0 +25, 7% 100% 10. 305 15. 348 +48, 9% 100% Electronic Money Total * The data are very small relative to other relevant data in the table. V. 1. 1 Solvay Business School Source : ECB Blue Book – June 2001 5
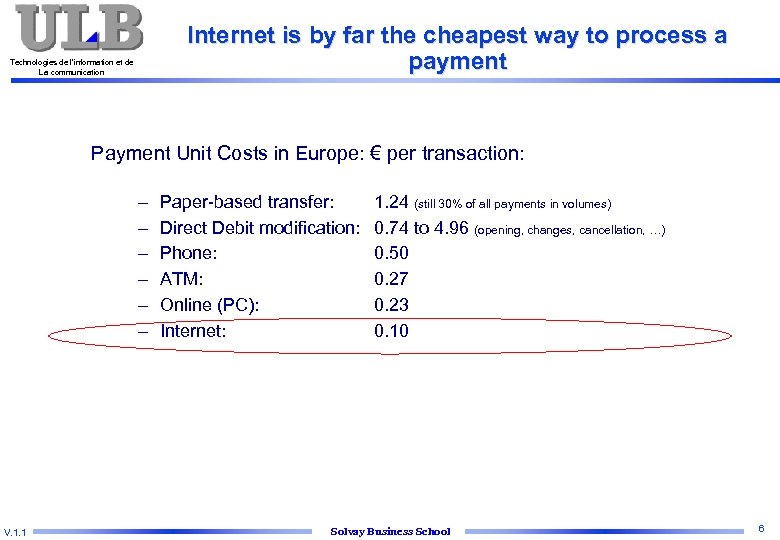
Internet is by far the cheapest way to process a payment Technologies de l’information et de La communication Payment Unit Costs in Europe: € per transaction: – – – V. 1. 1 Paper-based transfer: Direct Debit modification: Phone: ATM: Online (PC): Internet: 1. 24 (still 30% of all payments in volumes) 0. 74 to 4. 96 (opening, changes, cancellation, …) 0. 50 0. 27 0. 23 0. 10 Solvay Business School 6
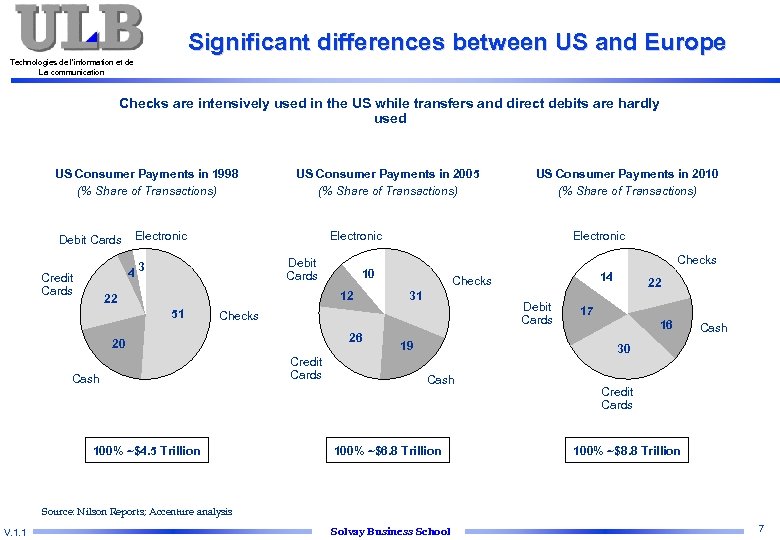
Significant differences between US and Europe Technologies de l’information et de La communication Checks are intensively used in the US while transfers and direct debits are hardly used US Consumer Payments in 1998 (% Share of Transactions) Debit Cards Electronic 10 12 22 Electronic Checks Debit Cards 51 US Consumer Payments in 2010 (% Share of Transactions) Electronic 43 Credit Cards US Consumer Payments in 2005 (% Share of Transactions) 31 Debit Cards Checks 26 20 Cash 100% ~$4. 5 Trillion Credit Cards 14 Checks 19 22 17 16 Cash 30 Cash 100% ~$6. 8 Trillion Credit Cards 100% ~$8. 8 Trillion Source: Nilson Reports; Accenture analysis V. 1. 1 Solvay Business School 7
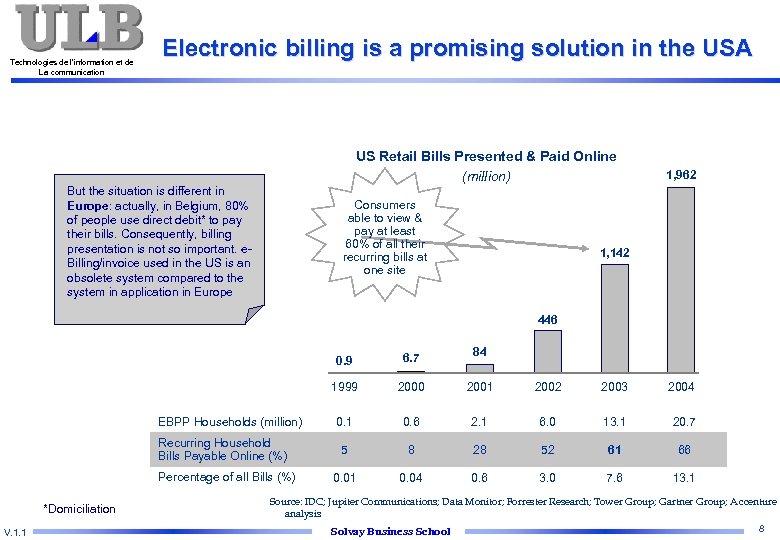
Technologies de l’information et de La communication Electronic billing is a promising solution in the USA US Retail Bills Presented & Paid Online (million) But the situation is different in Europe: actually, in Belgium, 80% of people use direct debit* to pay their bills. Consequently, billing presentation is not so important. e. Billing/invoice used in the US is an obsolete system compared to the system in application in Europe Consumers able to view & pay at least 60% of all their recurring bills at one site 1, 962 1, 142 446 0. 9 Recurring Household Bills Payable Online (%) Percentage of all Bills (%) *Domiciliation V. 1. 1 84 1999 EBPP Households (million) 6. 7 2000 2001 2002 2003 2004 0. 1 0. 6 2. 1 6. 0 13. 1 20. 7 5 8 28 52 61 66 0. 01 0. 04 0. 6 3. 0 7. 6 13. 1 Source: IDC; Jupiter Communications; Data Monitor; Forrester Research; Tower Group; Gartner Group; A ccenture analysis Solvay Business School 8
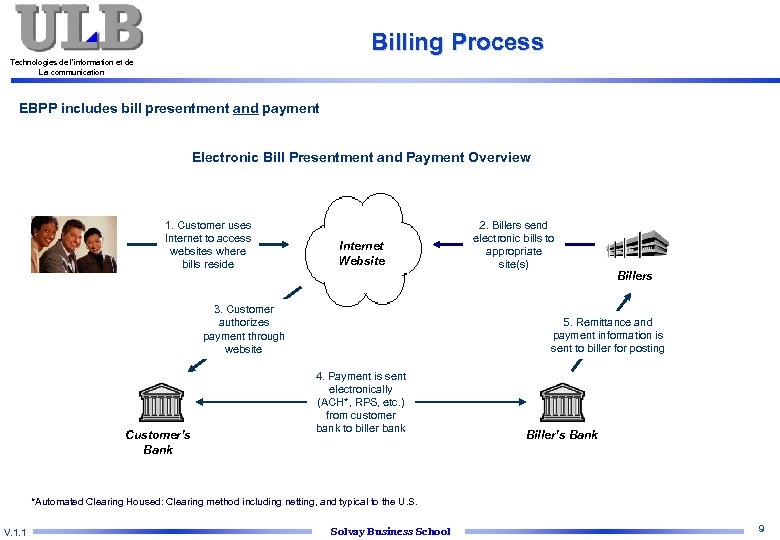
Billing Process Technologies de l’information et de La communication EBPP includes bill presentment and payment Electronic Bill Presentment and Payment Overview 1. Customer uses Internet to access websites where bills reside Internet Website 3. Customer authorizes payment through website Customer’s Bank 2. Billers send electronic bills to appropriate site(s) Billers 5. Remittance and payment information is sent to biller for posting 4. Payment is sent electronically (ACH*, RPS, etc. ) from customer bank to biller bank Biller’s Bank *Automated Clearing Housed: Clearing method including netting, and typical to the U. S. V. 1. 1 Solvay Business School 9
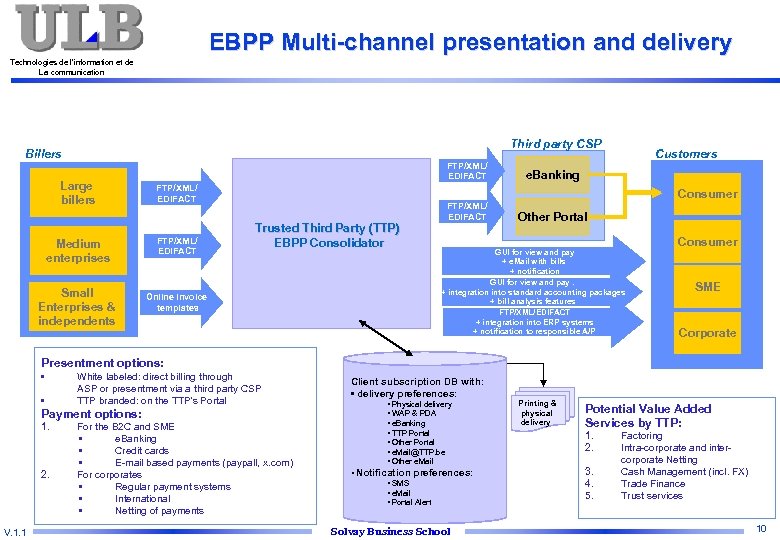
EBPP Multi-channel presentation and delivery Technologies de l’information et de La communication Third party CSP Billers Large billers Medium enterprises Small Enterprises & independents FTP/XML/ EDIFACT Customers e. Banking Consumer Trusted Third Party (TTP) EBPP Consolidator Online invoice templates FTP/XML/ EDIFACT Other Portal GUI for view and pay + e. Mail with bills + notification GUI for view and pay. + integration into standard accounting packages + bill analysis features FTP/XML/EDIFACT + integration into ERP systems + notification to responsible A/P Consumer SME Corporate Presentment options: • • White labeled: direct billing through ASP or presentment via a third party CSP TTP branded: on the TTP’s Portal Payment options: 1. 2. V. 1. 1 For the B 2 C and SME • e. Banking • Credit cards • E-mail based payments (paypall, x. com) For corporates • Regular payment systems • International • Netting of payments Client subscription DB with: • delivery preferences: • Physical delivery • WAP & PDA • e. Banking • TTP Portal • Other Portal • e. Mail@TTP. be • Other e. Mail • Notification preferences: • SMS • e. Mail • Portal Alert Solvay Business School Printing & physical delivery Potential Value Added Services by TTP: 1. 2. 3. 4. 5. Factoring Intra-corporate and intercorporate Netting Cash Management (incl. FX) Trade Finance Trust services 10
Technologies de l’information et de La communication Introduction to epayments Network security principles and concepts B 2 C e. Payments solutions B 2 B e. Payments solutions V. 1. 1 Solvay Business School 11
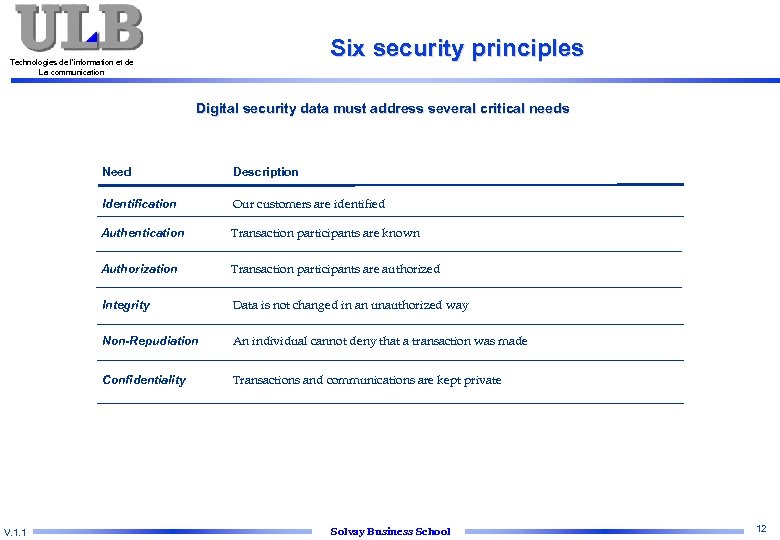
Six security principles Technologies de l’information et de La communication Digital security data must address several critical needs Need Identification Our customers are identified Authentication Transaction participants are known Authorization Transaction participants are authorized Integrity Data is not changed in an unauthorized way Non-Repudiation An individual cannot deny that a transaction was made Confidentiality V. 1. 1 Description Transactions and communications are kept private Solvay Business School 12
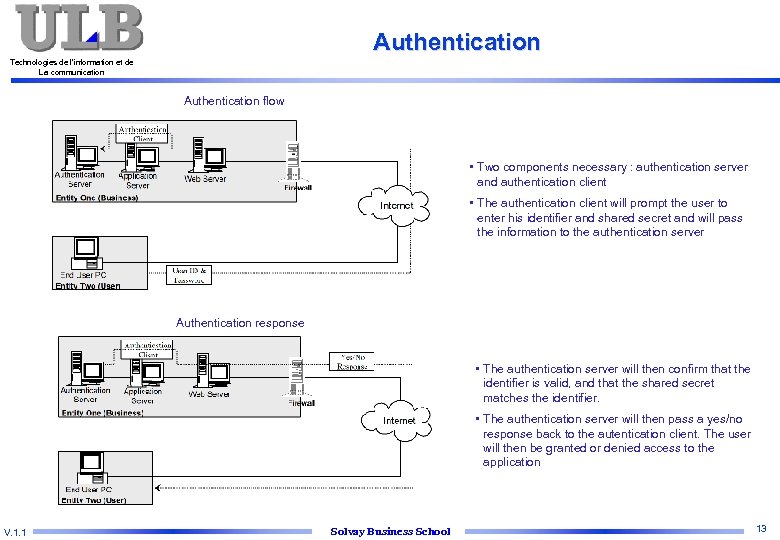
Authentication Technologies de l’information et de La communication Authentication flow • Two components necessary : authentication server and authentication client • The authentication client will prompt the user to enter his identifier and shared secret and will pass the information to the authentication server Authentication response • The authentication server will then confirm that the identifier is valid, and that the shared secret matches the identifier. • The authentication server will then pass a yes/no response back to the autentication client. The user will then be granted or denied access to the application V. 1. 1 Solvay Business School 13
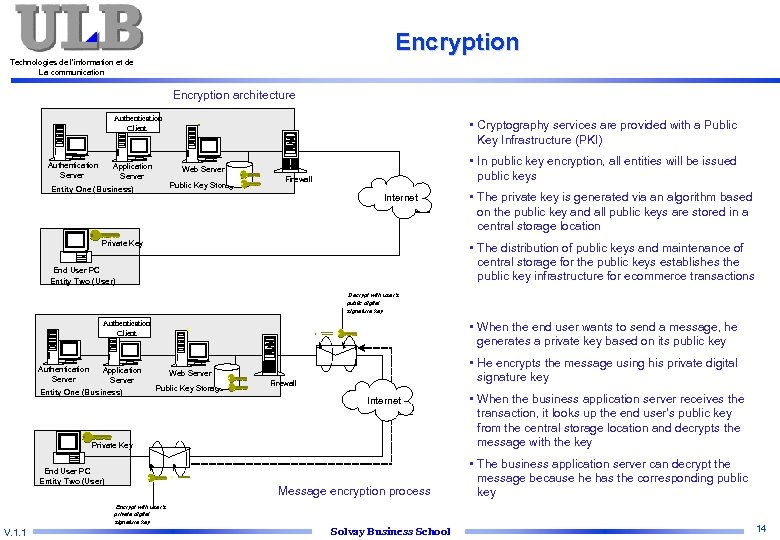
Encryption Technologies de l’information et de La communication Encryption architecture Authentication Client Authentication Server Application Server • Cryptography services are provided with a Public Key Infrastructure (PKI) • In public key encryption, all entities will be issued public keys Web Server Public Key Storage Entity One (Business) Firewall Internet Private Key • The private key is generated via an algorithm based on the public key and all public keys are stored in a central storage location • The distribution of public keys and maintenance of central storage for the public keys establishes the public key infrastructure for ecommerce transactions End User PC Entity Two (User) Decrypt with user’s public digital signature key Authentication Client Authentication Server Application Server Entity One (Business) • When the end user wants to send a message, he generates a private key based on its public key • He encrypts the message using his private digital signature key Web Server Public Key Storage Firewall Internet Private Key End User PC Entity Two (User) Message encryption process Encrypt with user’s private digital signature key V. 1. 1 Solvay Business School • When the business application server receives the transaction, it looks up the end user’s public key from the central storage location and decrypts the message with the key • The business application server can decrypt the message because he has the corresponding public key 14
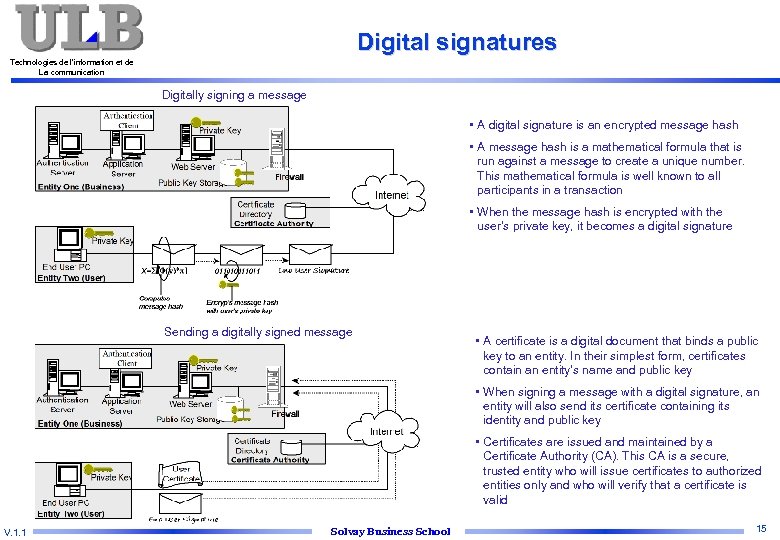
Digital signatures Technologies de l’information et de La communication Digitally signing a message • A digital signature is an encrypted message hash • A message hash is a mathematical formula that is run against a message to create a unique number. This mathematical formula is well known to all participants in a transaction • When the message hash is encrypted with the user’s private key, it becomes a digital signature Sending a digitally signed message • A certificate is a digital document that binds a public key to an entity. In their simplest form, certificates contain an entity’s name and public key • When signing a message with a digital signature, an entity will also send its certificate containing its identity and public key • Certificates are issued and maintained by a Certificate Authority (CA). This CA is a secure, trusted entity who will issue certificates to authorized entities only and who will verify that a certificate is valid V. 1. 1 Solvay Business School 15
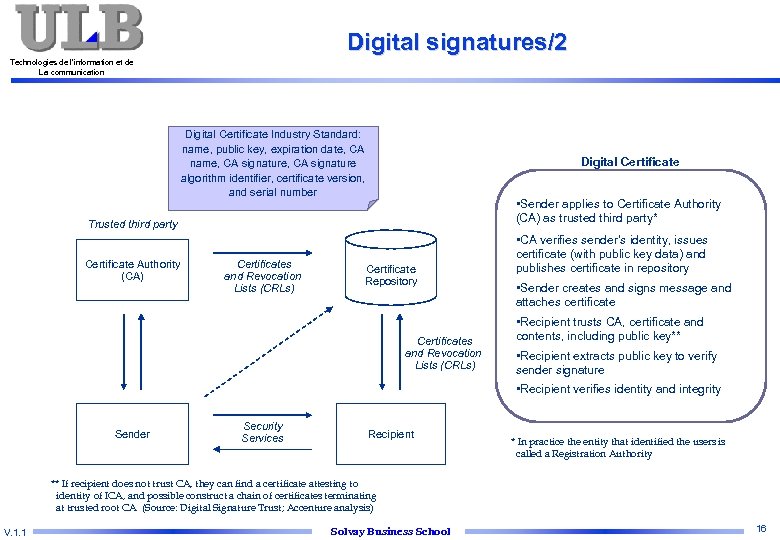
Digital signatures/2 Technologies de l’information et de La communication Digital Certificate Industry Standard: name, public key, expiration date, CA name, CA signature algorithm identifier, certificate version, and serial number Digital Certificate • Sender applies to Certificate Authority (CA) as trusted third party* Trusted third party Certificate Authority (CA) Certificates and Revocation Lists (CRLs) Certificate Repository Certificates and Revocation Lists (CRLs) • CA verifies sender’s identity, issues certificate (with public key data) and publishes certificate in repository • Sender creates and signs message and attaches certificate • Recipient trusts CA, certificate and contents, including public key** • Recipient extracts public key to verify sender signature • Recipient verifies identity and integrity Sender Security Services Recipient * In practice the entity that identified the users is called a Registration Authority ** If recipient does not trust CA, they can find a certificate attesting to identity of ICA, and possible construct a chain of certificates terminating at trusted root CA (Source: Digital Signature Trust; Accenture analysis) V. 1. 1 Solvay Business School 16
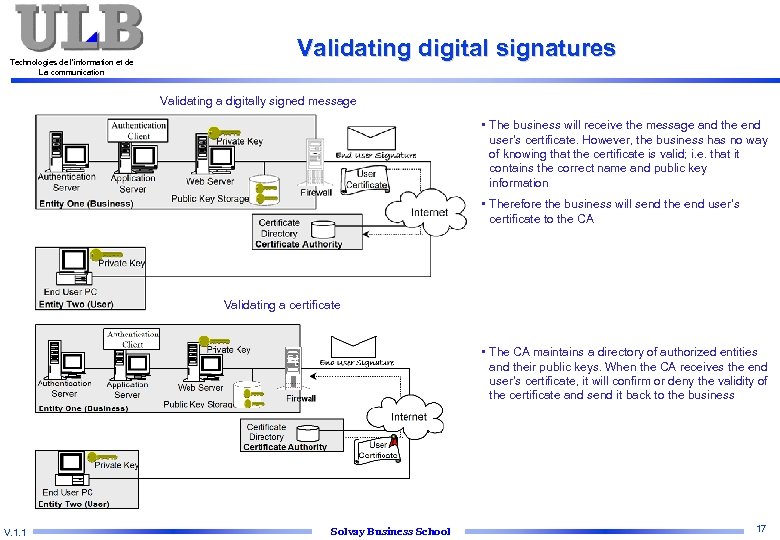
Technologies de l’information et de La communication Validating digital signatures Validating a digitally signed message • The business will receive the message and the end user’s certificate. However, the business has no way of knowing that the certificate is valid; i. e. that it contains the correct name and public key information • Therefore the business will send the end user’s certificate to the CA Validating a certificate • The CA maintains a directory of authorized entities and their public keys. When the CA receives the end user’s certificate, it will confirm or deny the validity of the certificate and send it back to the business V. 1. 1 Solvay Business School 17
Digital signature – Recent legislation Technologies de l’information et de La communication n n European directive (December 13, 1999) on digital signatures Belgian law (October 20, 2000 and July 9, 2001) – A signature can consist of a set of electronic data which can be associated to a well defined person and which certifies the integrity of the content – Legally binding of a digitally signed document n n The law targets mainly the digital signatures based on assymmetric cryptography and combined with a digital certificate (PKI) Legislation defines role and responsibilities of the Certification Authority – Approval – Control n n CA role consists of certifying the link between a person and its public key CA liability : a CA which delivers a qualified certificate is liable for any damages caused to anyone who has trusted the certificate – In practice, purpose is to limit carelessness (not timely revocation of a certificate…) V. 1. 1 Solvay Business School 18
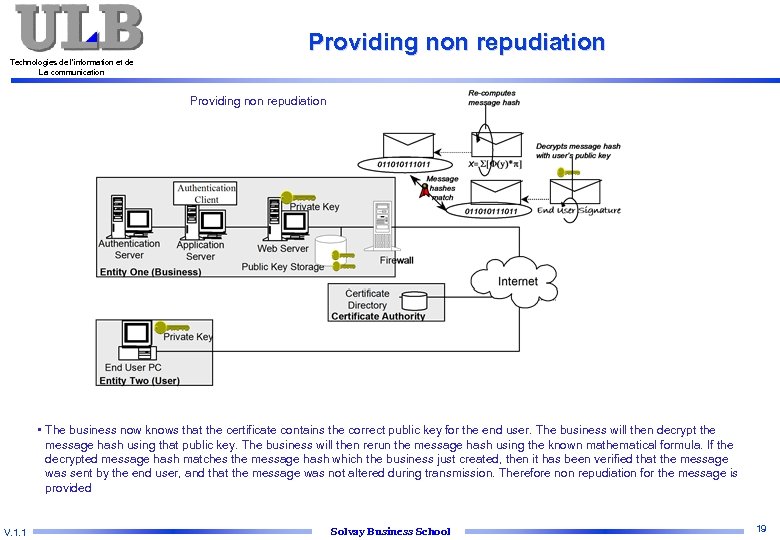
Providing non repudiation Technologies de l’information et de La communication Providing non repudiation • The business now knows that the certificate contains the correct public key for the end user. The business will then decrypt the message hash using that public key. The business will then rerun the message hash using the known mathematical formula. If the decrypted message hash matches the message hash which the business just created, then it has been verified that the message was sent by the end user, and that the message was not altered during transmission. Therefore non repudiation for the message is provided V. 1. 1 Solvay Business School 19
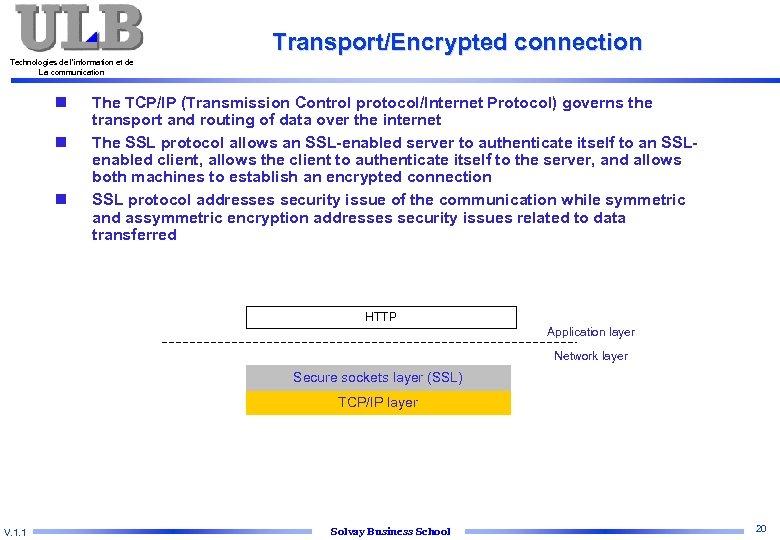
Transport/Encrypted connection Technologies de l’information et de La communication n The TCP/IP (Transmission Control protocol/Internet Protocol) governs the transport and routing of data over the internet The SSL protocol allows an SSL-enabled server to authenticate itself to an SSLenabled client, allows the client to authenticate itself to the server, and allows both machines to establish an encrypted connection SSL protocol addresses security issue of the communication while symmetric and assymmetric encryption addresses security issues related to data transferred HTTP Application layer Network layer Secure sockets layer (SSL) TCP/IP layer V. 1. 1 Solvay Business School 20
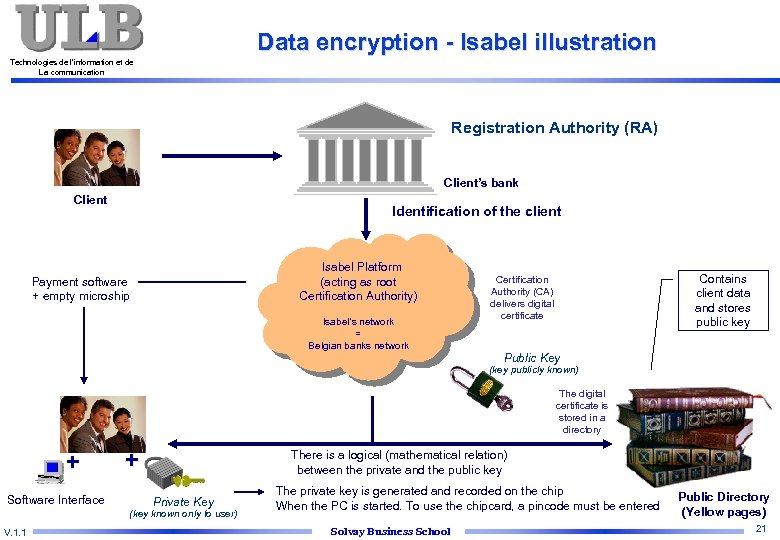
Data encryption - Isabel illustration Technologies de l’information et de La communication Registration Authority (RA) Client’s bank Client Identification of the client Isabel Platform (acting as root Certification Authority) Payment software + empty microship Isabel’s network = Belgian banks network Contains client data and stores public key Certification Authority (CA) delivers digital certificate Public Key (key publicly known) The digital certificate is stored in a directory + Software Interface + There is a logical (mathematical relation) between the private and the public key Private Key (key known only to user) V. 1. 1 The private key is generated and recorded on the chip When the PC is started. To use the chipcard, a pincode must be entered Solvay Business School Public Directory (Yellow pages) 21
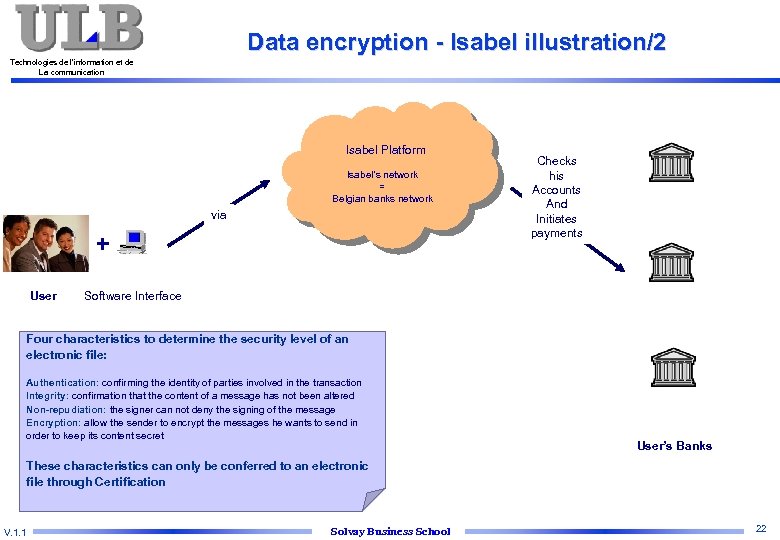
Data encryption - Isabel illustration/2 Technologies de l’information et de La communication Isabel Platform Isabel’s network = Belgian banks network via + User Checks his Accounts And Initiates payments Software Interface Four characteristics to determine the security level of an electronic file: Authentication: confirming the identity of parties involved in the transaction Integrity: confirmation that the content of a message has not been altered Non-repudiation: the signer can not deny the signing of the message Encryption: allow the sender to encrypt the messages he wants to send in order to keep its content secret User’s Banks These characteristics can only be conferred to an electronic file through Certification V. 1. 1 Solvay Business School 22
Technologies de l’information et de La communication Introduction to epayments Network security principles and concepts B 2 C e. Payments solutions B 2 B e. Payments solutions V. 1. 1 Solvay Business School 23
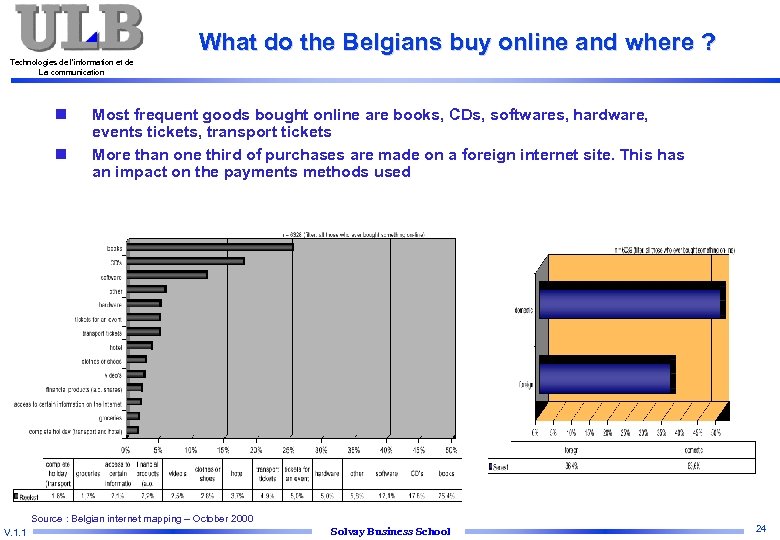
What do the Belgians buy online and where ? Technologies de l’information et de La communication n n Most frequent goods bought online are books, CDs, softwares, hardware, events tickets, transport tickets More than one third of purchases are made on a foreign internet site. This has an impact on the payments methods used Source : Belgian internet mapping – October 2000 V. 1. 1 Solvay Business School 24
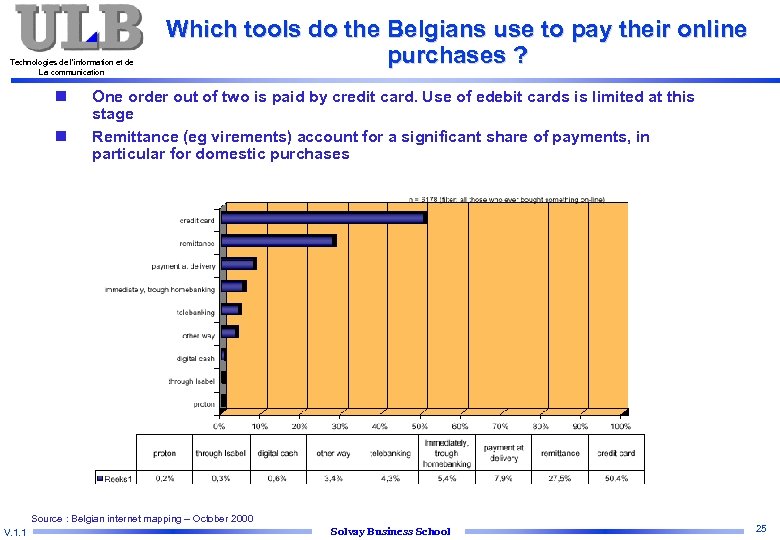
Technologies de l’information et de La communication n n Which tools do the Belgians use to pay their online purchases ? One order out of two is paid by credit card. Use of edebit cards is limited at this stage Remittance (eg virements) account for a significant share of payments, in particular for domestic purchases Source : Belgian internet mapping – October 2000 V. 1. 1 Solvay Business School 25
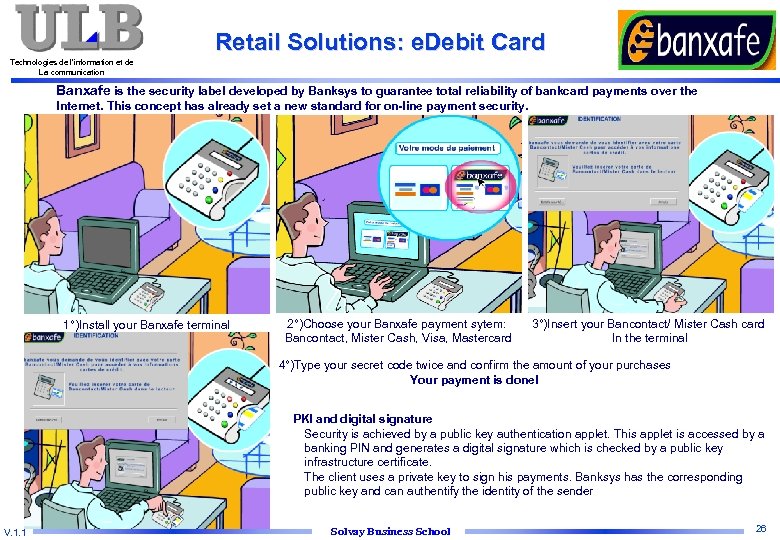
Retail Solutions: e. Debit Card Technologies de l’information et de La communication Banxafe is the security label developed by Banksys to guarantee total reliability of bankcard payments over the Internet. This concept has already set a new standard for on-line payment security. 1°)Install your Banxafe terminal 2°)Choose your Banxafe payment sytem: Bancontact, Mister Cash, Visa, Mastercard 3°)Insert your Bancontact/ Mister Cash card In the terminal 4°)Type your secret code twice and confirm the amount of your purchases Your payment is done! PKI and digital signature Security is achieved by a public key authentication applet. This applet is accessed by a banking PIN and generates a digital signature which is checked by a public key infrastructure certificate. The client uses a private key to sign his payments. Banksys has the corresponding public key and can authentify the identity of the sender V. 1. 1 Solvay Business School 26
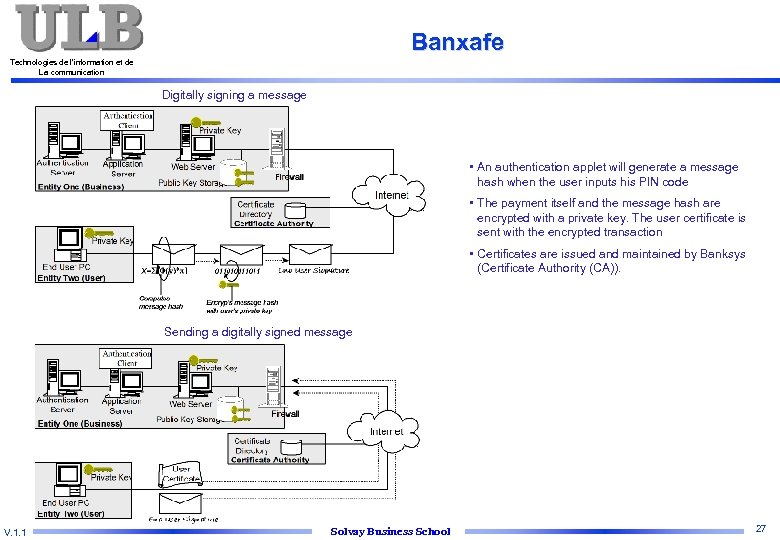
Banxafe Technologies de l’information et de La communication Digitally signing a message • An authentication applet will generate a message hash when the user inputs his PIN code • The payment itself and the message hash are encrypted with a private key. The user certificate is sent with the encrypted transaction • Certificates are issued and maintained by Banksys (Certificate Authority (CA)). Sending a digitally signed message V. 1. 1 Solvay Business School 27
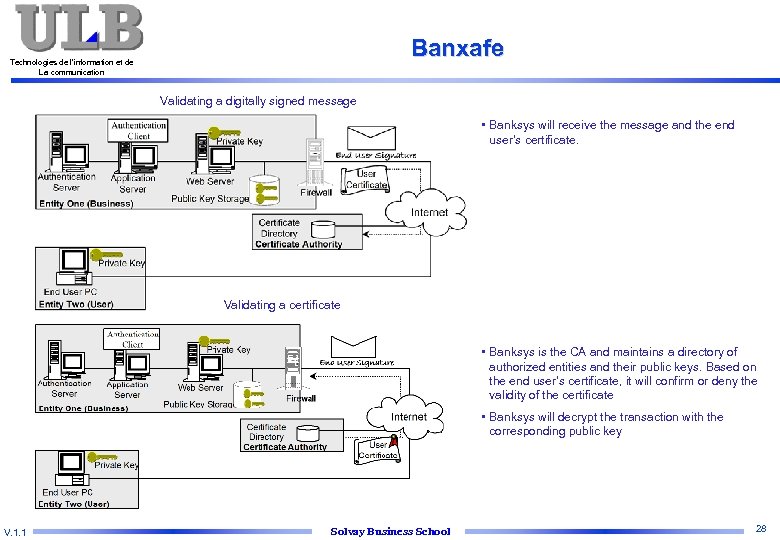
Banxafe Technologies de l’information et de La communication Validating a digitally signed message • Banksys will receive the message and the end user’s certificate. Validating a certificate • Banksys is the CA and maintains a directory of authorized entities and their public keys. Based on the end user’s certificate, it will confirm or deny the validity of the certificate • Banksys will decrypt the transaction with the corresponding public key V. 1. 1 Solvay Business School 28
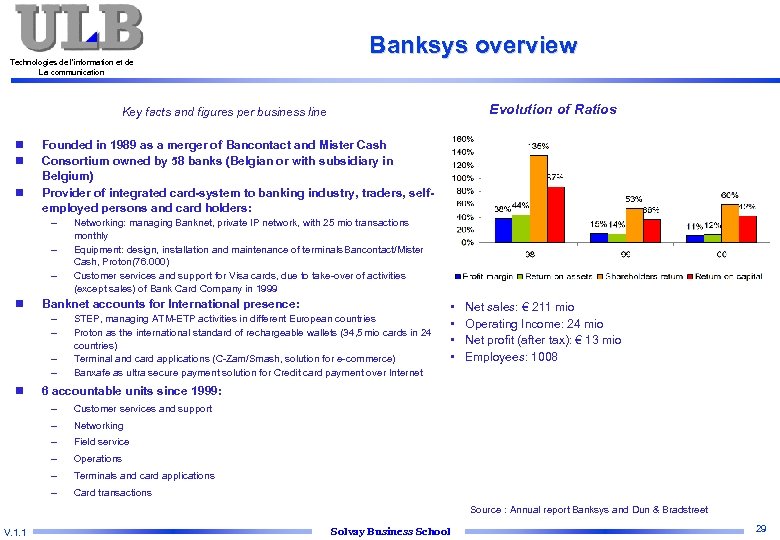
Technologies de l’information et de La communication Banksys overview Evolution of Ratios Key facts and figures per business line n n n Founded in 1989 as a merger of Bancontact and Mister Cash Consortium owned by 58 banks (Belgian or with subsidiary in Belgium) Provider of integrated card-system to banking industry, traders, selfemployed persons and card holders: – – – n Banknet accounts for International presence: – – n Networking: managing Banknet, private IP network, with 25 mio transactions monthly Equipment: design, installation and maintenance of terminals Bancontact/Mister Cash, Proton(76. 000) Customer services and support for Visa cards, due to take-over of activities (except sales) of Bank Card Company in 1999 STEP, managing ATM-ETP activities in different European countries Proton as the international standard of rechargeable wallets (34, 5 mio cards in 24 countries) Terminal and card applications (C-Zam/Smash, solution for e-commerce) Banxafe as ultra secure payment solution for Credit card payment over Internet • • Net sales: € 211 mio Operating Income: 24 mio Net profit (after tax): € 13 mio Employees: 1008 6 accountable units since 1999: – Customer services and support – Networking – Field service – Operations – Terminals and card applications – Card transactions Source : Annual report Banksys and Dun & Bradstreet V. 1. 1 Solvay Business School 29
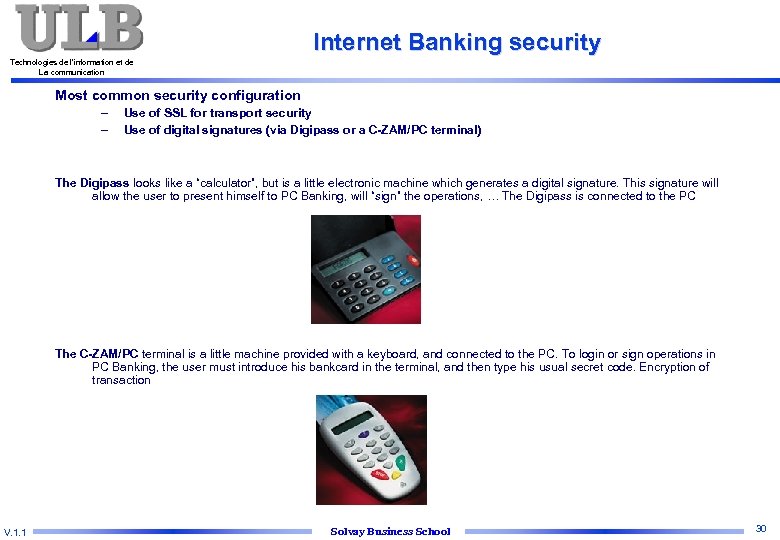
Internet Banking security Technologies de l’information et de La communication Most common security configuration – – Use of SSL for transport security Use of digital signatures (via Digipass or a C-ZAM/PC terminal) The Digipass looks like a “calculator”, but is a little electronic machine which generates a digital signature. This signature will allow the user to present himself to PC Banking, will “sign” the operations, … The Digipass is connected to the PC The C-ZAM/PC terminal is a little machine provided with a keyboard, and connected to the PC. To login or sign operations in PC Banking, the user must introduce his bankcard in the terminal, and then type his usual secret code. Encryption of transaction V. 1. 1 Solvay Business School 30
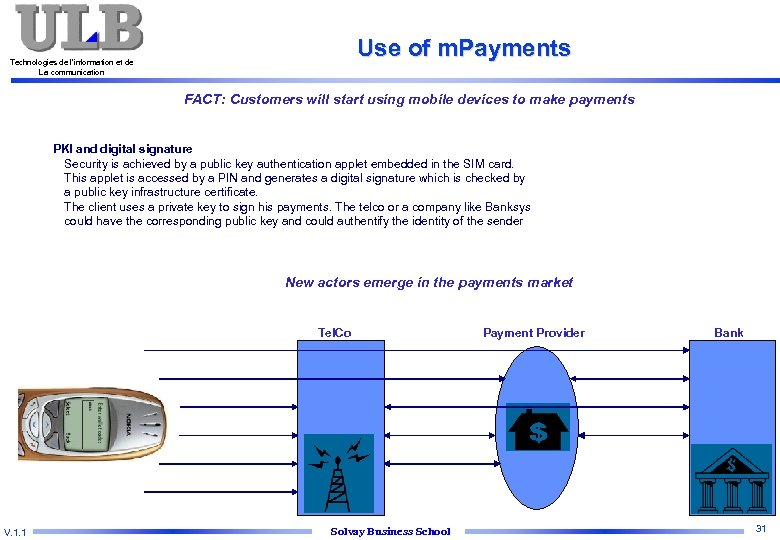
Use of m. Payments Technologies de l’information et de La communication FACT: Customers will start using mobile devices to make payments PKI and digital signature Security is achieved by a public key authentication applet embedded in the SIM card. This applet is accessed by a PIN and generates a digital signature which is checked by a public key infrastructure certificate. The client uses a private key to sign his payments. The telco or a company like Banksys could have the corresponding public key and could authentify the identity of the sender New actors emerge in the payments market Tel. Co V. 1. 1 Solvay Business School Payment Provider Bank 31
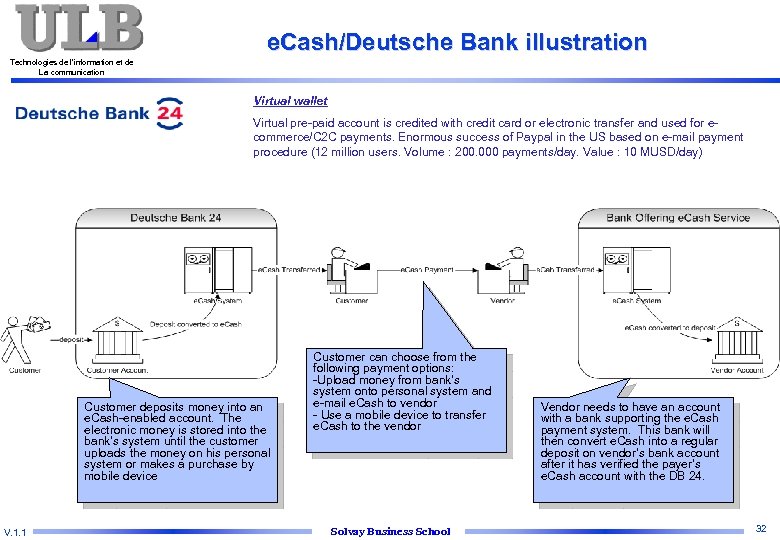
e. Cash/Deutsche Bank illustration Technologies de l’information et de La communication Virtual wallet Virtual pre-paid account is credited with credit card or electronic transfer and used for ecommerce/C 2 C payments. Enormous success of Paypal in the US based on e-mail payment procedure (12 million users. Volume : 200. 000 payments/day. Value : 10 MUSD/day) Customer deposits money into an e. Cash-enabled account. The electronic money is stored into the bank’s system until the customer uploads the money on his personal system or makes a purchase by mobile device V. 1. 1 Customer can choose from the following payment options: -Upload money from bank’s system onto personal system and e-mail e. Cash to vendor - Use a mobile device to transfer e. Cash to the vendor Solvay Business School Vendor needs to have an account with a bank supporting the e. Cash payment system. This bank will then convert e. Cash into a regular deposit on vendor’s bank account after it has verified the payer’s e. Cash account with the DB 24. 32
Technologies de l’information et de La communication Introduction to epayments Network security principles and concepts B 2 C e. Payments solutions B 2 B e. Payments solutions V. 1. 1 Solvay Business School 33
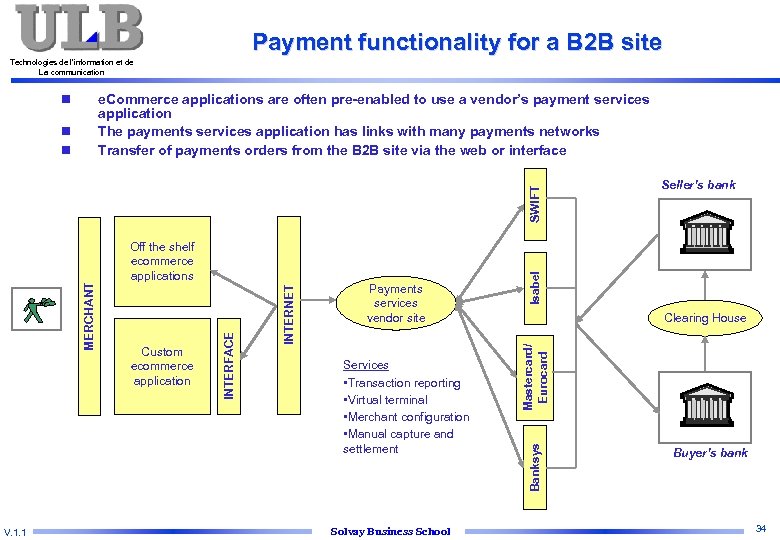
Payment functionality for a B 2 B site Technologies de l’information et de La communication n e. Commerce applications are often pre-enabled to use a vendor’s payment services application The payments services application has links with many payments networks Transfer of payments orders from the B 2 B site via the web or interface V. 1. 1 Services • Transaction reporting • Virtual terminal • Merchant configuration • Manual capture and settlement Solvay Business School Isabel Seller’s bank Clearing House Mastercard/ Eurocard Payments services vendor site Banksys Custom ecommerce application INTERNET Off the shelf ecommerce applications INTERFACE $ $$ MERCHANT SWIFT n n Buyer’s bank 34
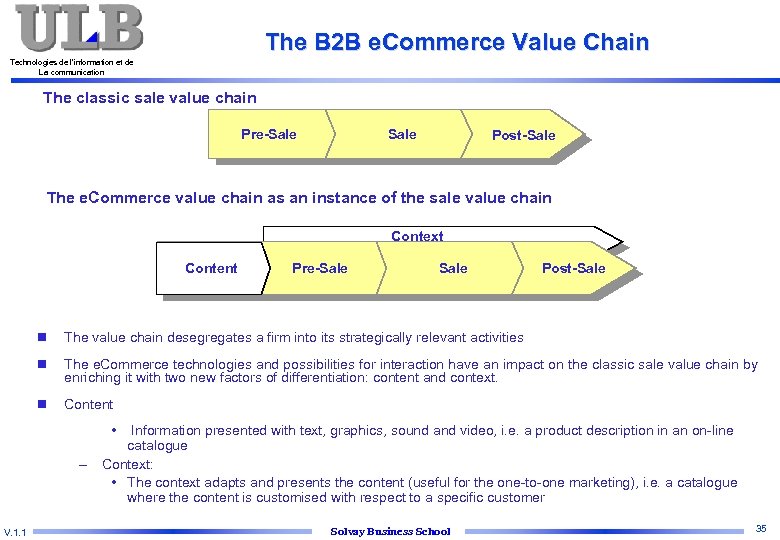
The B 2 B e. Commerce Value Chain Technologies de l’information et de La communication The classic sale value chain Pre-Sale Post-Sale The e. Commerce value chain as an instance of the sale value chain Context Content Pre-Sale Post-Sale n The value chain desegregates a firm into its strategically relevant activities n The e. Commerce technologies and possibilities for interaction have an impact on the classic sale value chain by enriching it with two new factors of differentiation: content and context. n Content • – V. 1. 1 Information presented with text, graphics, sound and video, i. e. a product description in an on-line catalogue Context: • The context adapts and presents the content (useful for the one-to-one marketing), i. e. a catalogue where the content is customised with respect to a specific customer Solvay Business School 35

e. Commerce value chain Technologies de l’information et de La communication n V. 1. 1 These processes illustrate the typical interactions between buyers and sellers in trading relationships The processes of the actors interact mutually through the services provided by intermediaries e. Commerce intermediaries: actors enabling various e. Commerce related activities Buyers: Sellers: - Investigate offerings - Prepare market presence - Publish need - Publish offerings - Evaluate and select offers - Bid in expressed demand - Place order - Respond to standard inquiries - Cancel order - Process orders - Receive goods or services - Confirm order - Accept/non-accept goods - Acknowledge cancellation - Receive invoice - Distribute goods - Dispute (protest invoice, …) - Issue invoice - Submit payment - Request support - Receive payment - Provide support Solvay Business School 36
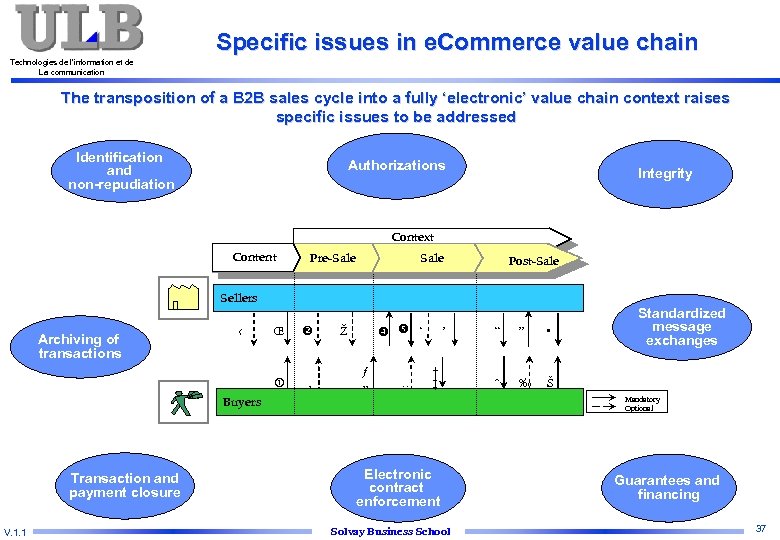
Specific issues in e. Commerce value chain Technologies de l’information et de La communication The transposition of a B 2 B sales cycle into a fully ‘electronic’ value chain context raises specific issues to be addressed Identification and non-repudiation Authorizations Integrity Context Content Pre-Sale Post-Sale Sellers $ $$ Transaction and payment closure V. 1. 1 Œ ‹ Archiving of transactions ‚ ‘ Ž ƒ „ … ’ † ‡ Buyers “ ” • ˆ ‰ Standardized message exchanges Š Mandatory Optional Electronic contract enforcement Solvay Business School Guarantees and financing 37
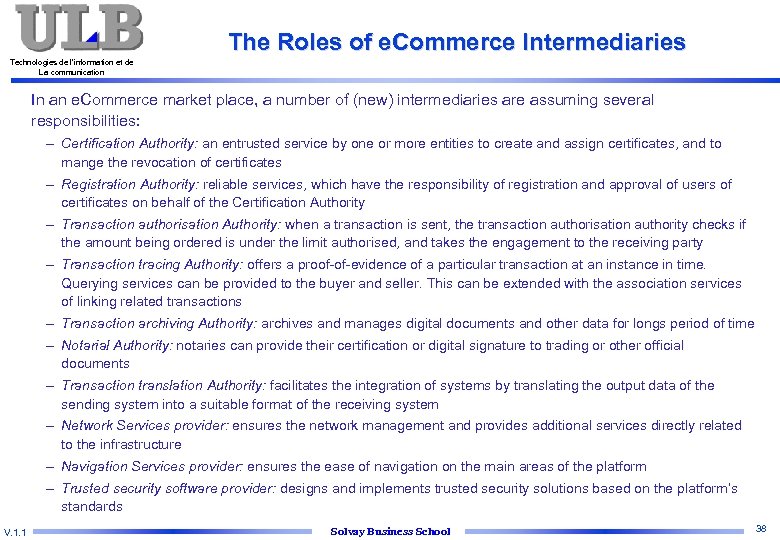
The Roles of e. Commerce Intermediaries Technologies de l’information et de La communication In an e. Commerce market place, a number of (new) intermediaries are assuming several responsibilities: – Certification Authority: an entrusted service by one or more entities to create and assign certificates, and to mange the revocation of certificates – Registration Authority: reliable services, which have the responsibility of registration and approval of users of certificates on behalf of the Certification Authority – Transaction authorisation Authority: when a transaction is sent, the transaction authorisation authority checks if the amount being ordered is under the limit authorised, and takes the engagement to the receiving party – Transaction tracing Authority: offers a proof-of-evidence of a particular transaction at an instance in time. Querying services can be provided to the buyer and seller. This can be extended with the association services of linking related transactions – Transaction archiving Authority: archives and manages digital documents and other data for longs period of time – Notarial Authority: notaries can provide their certification or digital signature to trading or other official documents – Transaction translation Authority: facilitates the integration of systems by translating the output data of the sending system into a suitable format of the receiving system – Network Services provider: ensures the network management and provides additional services directly related to the infrastructure – Navigation Services provider: ensures the ease of navigation on the main areas of the platform – Trusted security software provider: designs and implements trusted security solutions based on the platform’s standards V. 1. 1 Solvay Business School 38
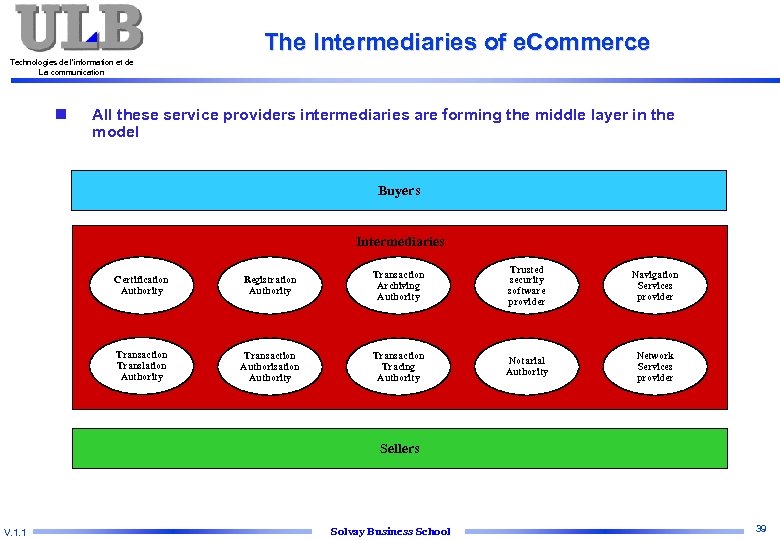
The Intermediaries of e. Commerce Technologies de l’information et de La communication n All these service providers intermediaries are forming the middle layer in the model Buyers Intermediaries Certification Authority Registration Authority Transaction Archiving Authority Trusted security software provider Navigation Services provider Transaction Translation Authority Transaction Authorisation Authority Transaction Tracing Authority Notarial Authority Network Services provider Sellers V. 1. 1 Solvay Business School 39
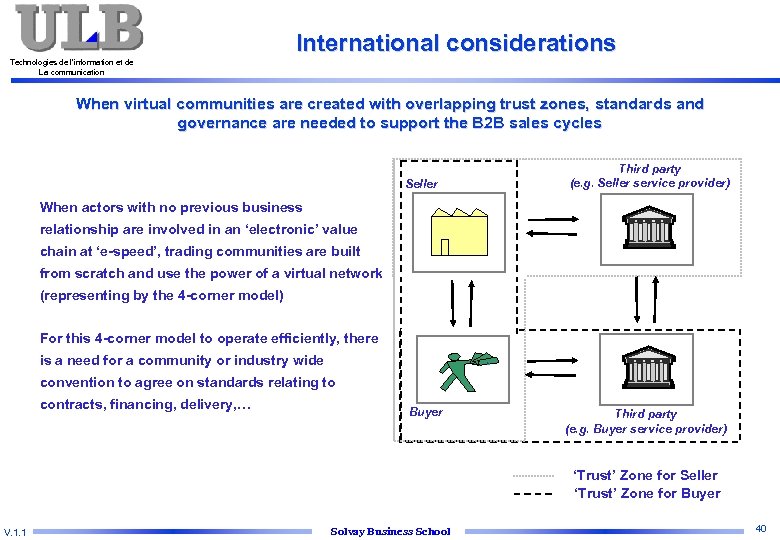
International considerations Technologies de l’information et de La communication When virtual communities are created with overlapping trust zones, standards and governance are needed to support the B 2 B sales cycles Third party (e. g. Seller service provider) Seller When actors with no previous business relationship are involved in an ‘electronic’ value chain at ‘e-speed’, trading communities are built from scratch and use the power of a virtual network (representing by the 4 -corner model) For this 4 -corner model to operate efficiently, there is a need for a community or industry wide $ $ $ convention to agree on standards relating to contracts, financing, delivery, … Buyer Third party (e. g. Buyer service provider) ‘Trust’ Zone for Seller ‘Trust’ Zone for Buyer V. 1. 1 Solvay Business School 40
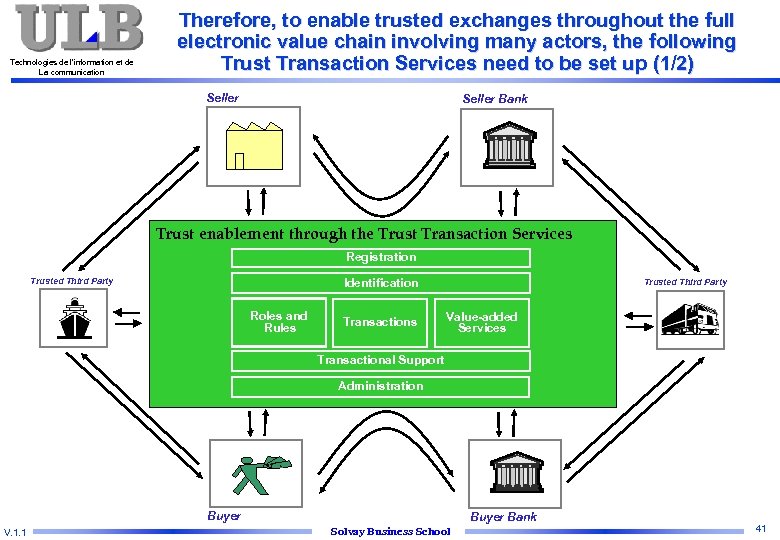
Technologies de l’information et de La communication Therefore, to enable trusted exchanges throughout the full electronic value chain involving many actors, the following Trust Transaction Services need to be set up (1/2) Seller Bank Trust enablement through the Trust Transaction Services Registration Identification Trusted Third Party Roles and Rules Transactions Trusted Third Party Value-added Services Transactional Support Administration $ $ $ Buyer V. 1. 1 Buyer Bank Solvay Business School 41
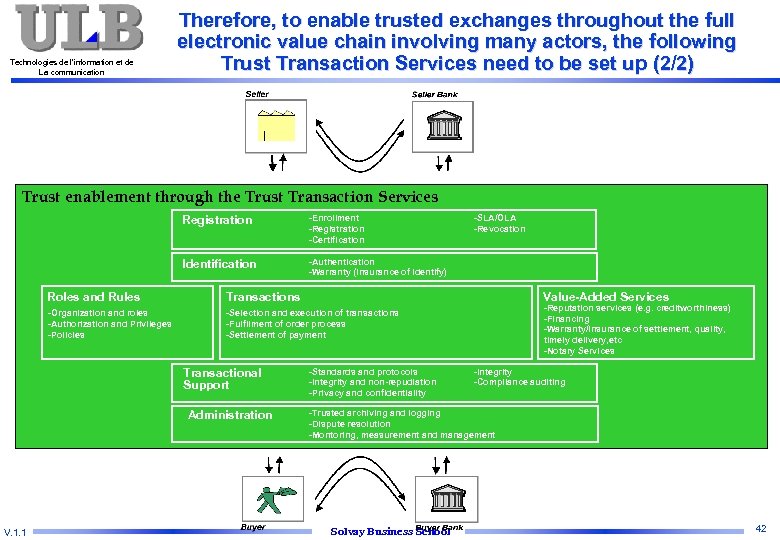
Technologies de l’information et de La communication Therefore, to enable trusted exchanges throughout the full electronic value chain involving many actors, the following Trust Transaction Services need to be set up (2/2) Trust enablement through the Trust Transaction Services Registration -Enrollment -Registration -Certification Identification -Authentication -Warranty (Insurance of identify) Value-Added Services Roles and Rules Transactions -Organization and roles -Authorization and Privileges -Policies -Selection and execution of transactions -Fulfilment of order process -Settlement of payment Transactional Support Administration V. 1. 1 -SLA/OLA -Revocation -Standards and protocols -Integrity and non-repudiation -Privacy and confidentiality -Reputation services (e. g. creditworthiness) -Financing -Warranty/insurance of settlement, quality, timely delivery, etc -Notary Services -Integrity -Compliance auditing -Trusted archiving and logging -Dispute resolution -Montoring, measurement and management Solvay Business School 42
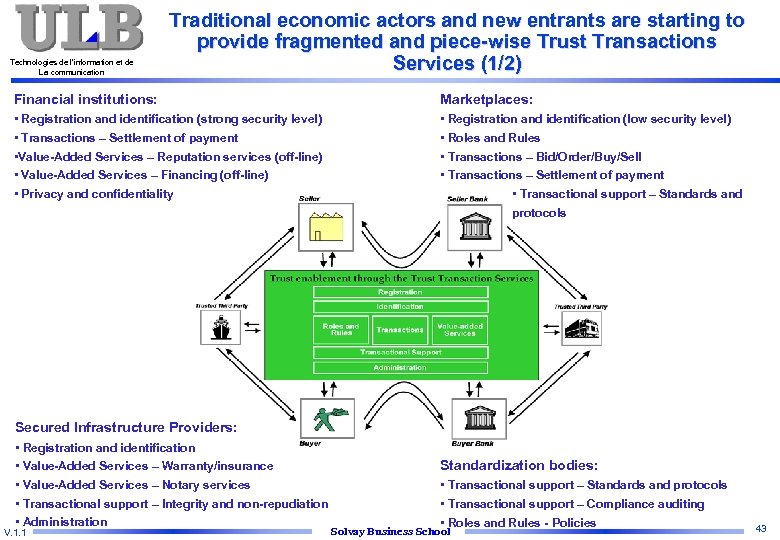
Technologies de l’information et de La communication Traditional economic actors and new entrants are starting to provide fragmented and piece-wise Trust Transactions Services (1/2) Financial institutions: Marketplaces: • Registration and identification (strong security level) • Transactions – Settlement of payment • Value-Added Services – Reputation services (off-line) • Value-Added Services – Financing (off-line) • Privacy and confidentiality • Registration and identification (low security level) • Roles and Rules • Transactions – Bid/Order/Buy/Sell • Transactions – Settlement of payment • Transactional support – Standards and protocols Secured Infrastructure Providers: • Registration and identification • Value-Added Services – Warranty/insurance • Value-Added Services – Notary services • Transactional support – Integrity and non-repudiation • Administration V. 1. 1 Standardization bodies: • Transactional support – Standards and protocols • Transactional support – Compliance auditing • Roles and Rules - Policies Solvay Business School 43

Technologies de l’information et de La communication Traditional economic actors and new entrants are starting to provide fragmented and piece-wise Trust Transactions Services (2/2) Financial institutions: Secured Infrastructure Providers: • Registration and identification – Corporate customers of Belgian banks with Isabel – ABN-AMRO, Deutsche Bank and Allianz (via Hypo. Vereinsbank) started using Identrus-based certificates to secure new applications • Transactions – Barclays B 2 B. com UK first purchase-to-payment portal to cover entire B 2 B trading chain – Dresdner Bank Europe’s first transactional financial portal to offer corporates online banking, risk management and transaction services • S. W. I. F. T. with Trust. Act is a secured Internet-based messaging service with non-repudiation and identification based on Identrus certificates • Isabel provides proprietary certificates and a secured messaging service to all corporate customers of the Belgian banks (more than 45, 000 companies) • Government sponsored bodies such as the Spanish Mint provide all citizens with a digital certificate and signature Marketplaces: • ‘Industry-centered’ (industry consortia or independent) or ‘company-centered’ • Focus on seamless procurement and supply chain integration V. 1. 1 Standardization bodies: • S. W. I. F. T. with Bolero have released 65 XML document definitions as used in international trade (e. g. commercial, documentary credit, customs) to be transported through the secured S. W. I. F. T. /Trust. Act infrastructure • Identrus has defined a industry standard for digital certificates, a payment initiation application and a contractual framework that regulates their usage • E. U. passed a directive on 19 January 2000 making digital signatures equivalent to paper based signatures Solvay Business School 44
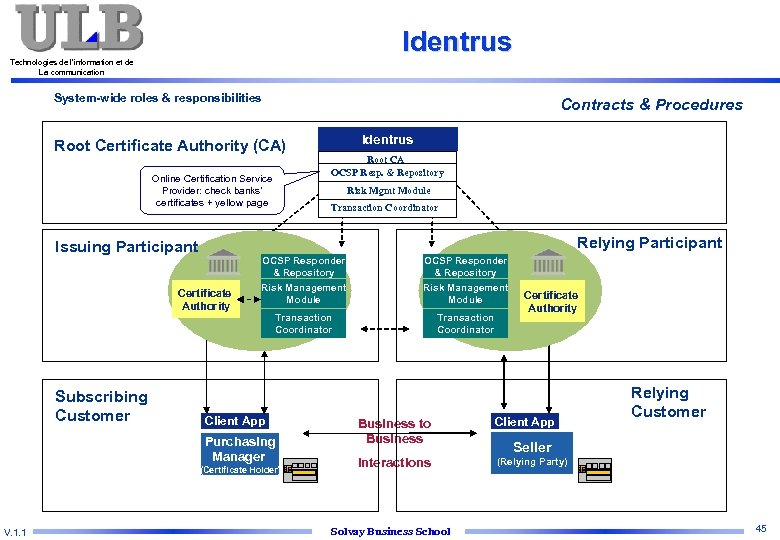
Identrus Technologies de l’information et de La communication System-wide roles & responsibilities Contracts & Procedures Root Certificate Authority (CA) Online Certification Service Provider: check banks’ certificates + yellow page Risk Mgmt Module Transaction Coordinator OCSP Responder & Repository Certificate Authority OCSP Responder & Repository Risk Management Module Transaction Coordinator Client App Purchasing Manager (Certificate Holder) V. 1. 1 Root CA OCSP Resp. & Repository Relying Participant Issuing Participant Subscribing Customer Identrus Certificate Authority Business to Business Client App Interactions Relying Customer (Relying Party) Solvay Business School Seller 45
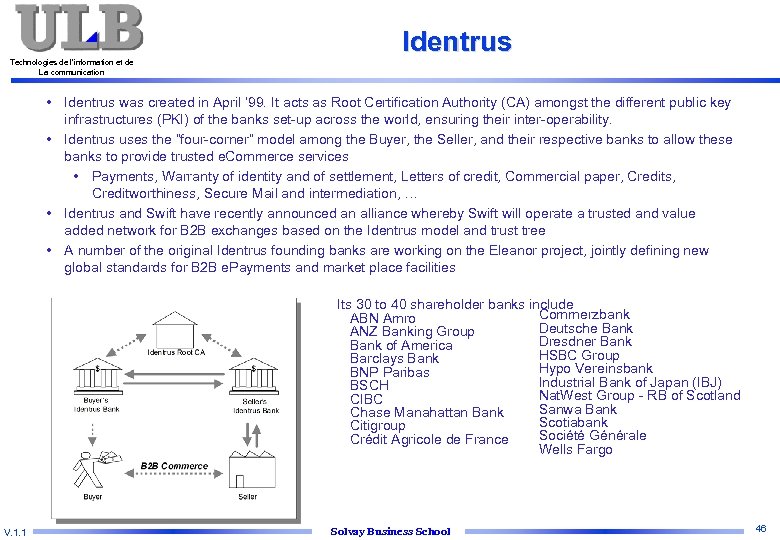
Identrus Technologies de l’information et de La communication • Identrus was created in April ’ 99. It acts as Root Certification Authority (CA) amongst the different public key infrastructures (PKI) of the banks set-up across the world, ensuring their inter-operability. • Identrus uses the “four-corner” model among the Buyer, the Seller, and their respective banks to allow these banks to provide trusted e. Commerce services • Payments, Warranty of identity and of settlement, Letters of credit, Commercial paper, Credits, Creditworthiness, Secure Mail and intermediation, … • Identrus and Swift have recently announced an alliance whereby Swift will operate a trusted and value added network for B 2 B exchanges based on the Identrus model and trust tree • A number of the original Identrus founding banks are working on the Eleanor project, jointly defining new global standards for B 2 B e. Payments and market place facilities Its 30 to 40 shareholder banks include Commerzbank ABN Amro Deutsche Bank ANZ Banking Group Dresdner Bank of America HSBC Group Barclays Bank Hypo Vereinsbank BNP Paribas Industrial Bank of Japan (IBJ) BSCH Nat. West Group - RB of Scotland CIBC Sanwa Bank Chase Manahattan Bank Scotiabank Citigroup Société Générale Crédit Agricole de France Wells Fargo V. 1. 1 Solvay Business School 46
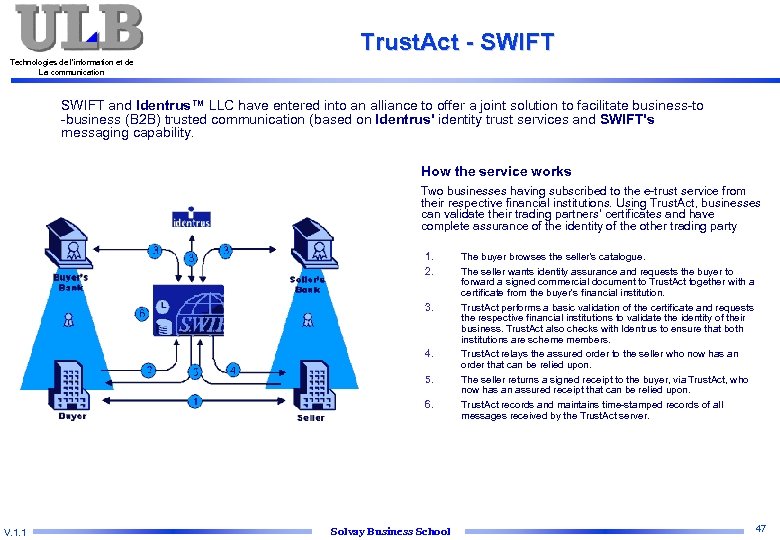
Trust. Act - SWIFT Technologies de l’information et de La communication SWIFT and Identrus™ LLC have entered into an alliance to offer a joint solution to facilitate business-to -business (B 2 B) trusted communication (based on Identrus' identity trust services and SWIFT's messaging capability. How the service works Two businesses having subscribed to the e-trust service from their respective financial institutions. Using Trust. Act, businesses can validate their trading partners' certificates and have complete assurance of the identity of the other trading party 1. 2. 3. 4. 5. 6. V. 1. 1 Solvay Business School The buyer browses the seller's catalogue. The seller wants identity assurance and requests the buyer to forward a signed commercial document to Trust. Act together with a certificate from the buyer's financial institution. Trust. Act performs a basic validation of the certificate and requests the respective financial institutions to validate the identity of their business. Trust. Act also checks with Identrus to ensure that both institutions are scheme members. Trust. Act relays the assured order to the seller who now has an order that can be relied upon. The seller returns a signed receipt to the buyer, via Trust. Act, who now has an assured receipt that can be relied upon. Trust. Act records and maintains time-stamped records of all messages received by the Trust. Act server. 47
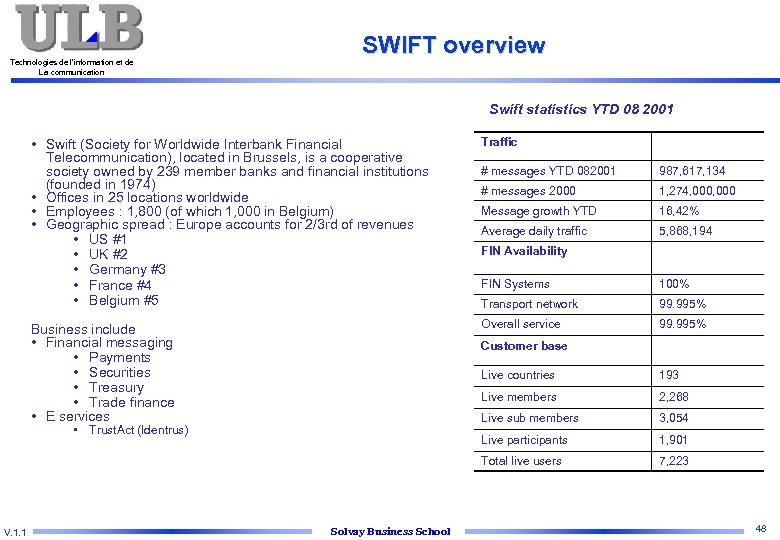
Technologies de l’information et de La communication SWIFT overview Swift statistics YTD 08 2001 • Swift (Society for Worldwide Interbank Financial Telecommunication), located in Brussels, is a cooperative society owned by 239 member banks and financial institutions (founded in 1974) • Offices in 25 locations worldwide • Employees : 1, 800 (of which 1, 000 in Belgium) • Geographic spread : Europe accounts for 2/3 rd of revenues • US #1 • UK #2 • Germany #3 • France #4 • Belgium #5 Traffic Business include • Financial messaging • Payments • Securities • Treasury • Trade finance • E services # messages YTD 082001 987, 617, 134 # messages 2000 1, 274, 000 Message growth YTD 16, 42% Average daily traffic 5, 868, 194 FIN Availability FIN Systems 100% Transport network 99. 995% Overall service 99. 995% Customer base Live countries Live members Live participants Solvay Business School 3, 054 1, 901 Total live users V. 1. 1 2, 268 Live sub members • Trust. Act (Identrus) 193 7, 223 48
a53fff8b9912f37825ba9612415f81b3.ppt