291fe2c0f814873dffa39e5ec306684b.ppt
- Количество слайдов: 70
 United States Department of the Interior Social Engineering & Internal/External Threats March 22, 2006 Leland C. Dudek Leland_dudek@ios. doi. gov
United States Department of the Interior Social Engineering & Internal/External Threats March 22, 2006 Leland C. Dudek Leland_dudek@ios. doi. gov
 Agenda u What’s u DOI at stake? FY 2005 Threat/Incident Statistics u Survey of Government Departments - Alarming Statistics u Social Engineering – Often the first vector of attack u Internal and External Threats
Agenda u What’s u DOI at stake? FY 2005 Threat/Incident Statistics u Survey of Government Departments - Alarming Statistics u Social Engineering – Often the first vector of attack u Internal and External Threats
 Train 2 Secure What’s at Stake u Information u Provision u Data Privacy - Confidentiality of Services - Availability Manipulation - Integrity u Critical Roles and Missions u Critical Infrastructure u Agency Reputation
Train 2 Secure What’s at Stake u Information u Provision u Data Privacy - Confidentiality of Services - Availability Manipulation - Integrity u Critical Roles and Missions u Critical Infrastructure u Agency Reputation
 DOI FY 2005 Threat/Incident Statistics u Over 650 million suspicious probes/attacks blocked u Over 3. 4 million viruses, trojans, worms detected, deleted, cleaned
DOI FY 2005 Threat/Incident Statistics u Over 650 million suspicious probes/attacks blocked u Over 3. 4 million viruses, trojans, worms detected, deleted, cleaned
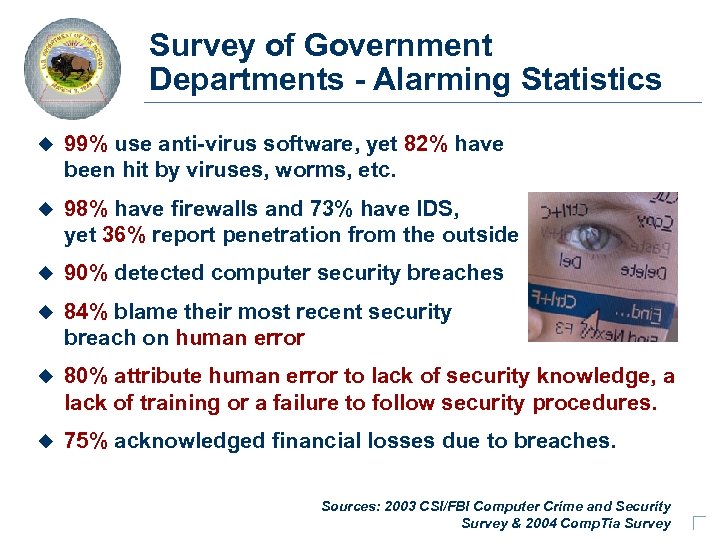 Train 2 Secure Survey of Government Departments - Alarming Statistics u 99% use anti-virus software, yet 82% have been hit by viruses, worms, etc. u 98% have firewalls and 73% have IDS, yet 36% report penetration from the outside u 90% detected computer security breaches u 84% blame their most recent security breach on human error u 80% attribute human error to lack of security knowledge, a lack of training or a failure to follow security procedures. u 75% acknowledged financial losses due to breaches. Sources: 2003 CSI/FBI Computer Crime and Security Survey & 2004 Comp. Tia Survey
Train 2 Secure Survey of Government Departments - Alarming Statistics u 99% use anti-virus software, yet 82% have been hit by viruses, worms, etc. u 98% have firewalls and 73% have IDS, yet 36% report penetration from the outside u 90% detected computer security breaches u 84% blame their most recent security breach on human error u 80% attribute human error to lack of security knowledge, a lack of training or a failure to follow security procedures. u 75% acknowledged financial losses due to breaches. Sources: 2003 CSI/FBI Computer Crime and Security Survey & 2004 Comp. Tia Survey
 Social Engineering Hey! I need to reset your password… can you tell me your old one? Help Desk or Social Engineering? Can be either an internal or external threat…
Social Engineering Hey! I need to reset your password… can you tell me your old one? Help Desk or Social Engineering? Can be either an internal or external threat…
 What is Social Engineering u Social Engineering is the unauthorized acquisition of sensitive information or inappropriate access privileges by a potential threat source, based upon the building of an inappropriate trust relationship with a legitimate user of an information technology system. u The goal of social engineering is to trick someone – into providing valuable information or access to that information.
What is Social Engineering u Social Engineering is the unauthorized acquisition of sensitive information or inappropriate access privileges by a potential threat source, based upon the building of an inappropriate trust relationship with a legitimate user of an information technology system. u The goal of social engineering is to trick someone – into providing valuable information or access to that information.
 Social Engineering… a Wikipedia definition u In the field of computer security, social engineering is the practice of obtaining confidential information by manipulation of legitimate users. A social engineer will commonly use the telephone or Internet to trick people into revealing sensitive information or getting them to do something that is against typical policies. Perhaps the simplest, but still effective attack is tricking a user into thinking one is an administrator and requesting a password for various purposes. Users of Internet systems frequently receive messages that request password or credit card information in order to "set up their account" or "reactivate settings" or some other benign operation in what are called phishing attacks. Users must be warned early and frequently not to divulge passwords or any other sensitive information to anyone for any purpose, even to legitimate system administrators. In reality, administrators of computer systems rarely, if ever, need to know the user's password to perform administrative tasks. u Social engineering also applies to the act of face-to-face manipulation to gain physical access to computer systems. u In an IT security survey, 90% of office workers gave away their password in exchange for a cheap pen.
Social Engineering… a Wikipedia definition u In the field of computer security, social engineering is the practice of obtaining confidential information by manipulation of legitimate users. A social engineer will commonly use the telephone or Internet to trick people into revealing sensitive information or getting them to do something that is against typical policies. Perhaps the simplest, but still effective attack is tricking a user into thinking one is an administrator and requesting a password for various purposes. Users of Internet systems frequently receive messages that request password or credit card information in order to "set up their account" or "reactivate settings" or some other benign operation in what are called phishing attacks. Users must be warned early and frequently not to divulge passwords or any other sensitive information to anyone for any purpose, even to legitimate system administrators. In reality, administrators of computer systems rarely, if ever, need to know the user's password to perform administrative tasks. u Social engineering also applies to the act of face-to-face manipulation to gain physical access to computer systems. u In an IT security survey, 90% of office workers gave away their password in exchange for a cheap pen.
 The Weakest Link in the IT Security Chain u People are usually the weakest link in the security chain. u Social engineering is still the most effective method used to get around security obstacles. u A skilled social engineer will often try to exploit this weakness before spending time and effort on other methods to crack passwords.
The Weakest Link in the IT Security Chain u People are usually the weakest link in the security chain. u Social engineering is still the most effective method used to get around security obstacles. u A skilled social engineer will often try to exploit this weakness before spending time and effort on other methods to crack passwords.
 The Weakest Link in the IT Security Chain u Why try to hack through someone’s security system when you can get a user to open the door for you? u Social engineering is the hardest form of attack to defend against because it cannot be defended with hardware or software alone. u A successful defense depends on having good policies in place ensuring that all employees are trained to follow them.
The Weakest Link in the IT Security Chain u Why try to hack through someone’s security system when you can get a user to open the door for you? u Social engineering is the hardest form of attack to defend against because it cannot be defended with hardware or software alone. u A successful defense depends on having good policies in place ensuring that all employees are trained to follow them.
 Different Avenues of Persuasion In attempting to persuade someone to do something, there are two methods a persuader can employ: u The Direct Route u – – – u the social engineer simply asks for the information or access with no set up often challenged and refused seldom used due to low probability of success The Peripheral Route – Contrived situation - The more factors the target must consider in addition to the basic request, the more likely the target is to be persuaded. v Forgot a password v Manager on vacation v Looming deadlines – Personal Persuasion - Many social engineers are adept at using personal persuasion to overcome initial resistance. v The goal is not to force compliance but to get voluntary action v Target believes they are making the decision
Different Avenues of Persuasion In attempting to persuade someone to do something, there are two methods a persuader can employ: u The Direct Route u – – – u the social engineer simply asks for the information or access with no set up often challenged and refused seldom used due to low probability of success The Peripheral Route – Contrived situation - The more factors the target must consider in addition to the basic request, the more likely the target is to be persuaded. v Forgot a password v Manager on vacation v Looming deadlines – Personal Persuasion - Many social engineers are adept at using personal persuasion to overcome initial resistance. v The goal is not to force compliance but to get voluntary action v Target believes they are making the decision
 Different Avenues of Persuasion A Direct Route uses: – Systematic – logical arguments To: – stimulate a favorable response – prompting the recipient to action
Different Avenues of Persuasion A Direct Route uses: – Systematic – logical arguments To: – stimulate a favorable response – prompting the recipient to action
 Different Avenues of Persuasion A Peripheral Route uses: – peripheral cues – mental shortcuts – misrepresent their objectives To: – trigger acceptance without thinking
Different Avenues of Persuasion A Peripheral Route uses: – peripheral cues – mental shortcuts – misrepresent their objectives To: – trigger acceptance without thinking
 Different Avenues of Persuasion u One way in which the social engineer can make prospective victims more susceptible to Peripheral routes to persuasion is by making some statement at the outset that triggers a strong emotion such as: – Excitement “The Chief of Staff is writing up an award nomination for you and needs some additional information!” – Fear “The Chief Information Officer is waiting for this!”
Different Avenues of Persuasion u One way in which the social engineer can make prospective victims more susceptible to Peripheral routes to persuasion is by making some statement at the outset that triggers a strong emotion such as: – Excitement “The Chief of Staff is writing up an award nomination for you and needs some additional information!” – Fear “The Chief Information Officer is waiting for this!”
 Perception u In a typical transaction our perception about the request for service begins with a basic belief that each party is who they say they are. u Some social engineering victims may tend to rely primarily on their belief that the person with whom they dealt was honest, and to give little thought to the activities.
Perception u In a typical transaction our perception about the request for service begins with a basic belief that each party is who they say they are. u Some social engineering victims may tend to rely primarily on their belief that the person with whom they dealt was honest, and to give little thought to the activities.
 Common Types of Social Engineering Exploit Methods u Social engineering can be broken into : – Human based: person-to-person interactions to retrieve the desired information – Computer based: computer software that attempts to retrieve the desired information.
Common Types of Social Engineering Exploit Methods u Social engineering can be broken into : – Human based: person-to-person interactions to retrieve the desired information – Computer based: computer software that attempts to retrieve the desired information.
 Human-based u Impersonation - Case studies indicate that help desks are the most frequent targets of social engineering attacks. – A Social Engineer calls the help desk – Help desk is helpful – Social engineer will often know names of employees u Important User - A common ploy is to pretend to be a senior executive. – Help desk is less likely to turn down a request coming from a highlevel official – Social engineer may threaten to report the employee to their supervisor.
Human-based u Impersonation - Case studies indicate that help desks are the most frequent targets of social engineering attacks. – A Social Engineer calls the help desk – Help desk is helpful – Social engineer will often know names of employees u Important User - A common ploy is to pretend to be a senior executive. – Help desk is less likely to turn down a request coming from a highlevel official – Social engineer may threaten to report the employee to their supervisor.
 Human-based u Third-party Authorization - The social engineer may have obtained the name of someone in the organization who has the authority to grant access to information. – Mr. Martinez says its OK. – “Before he went on vacation, Mr. Martinez said I should call you to get this information. u Tech Support - Social engineer pretends to be someone from the infrastructure-support groups. – System is having a problem – Needs them to log on to test the connection
Human-based u Third-party Authorization - The social engineer may have obtained the name of someone in the organization who has the authority to grant access to information. – Mr. Martinez says its OK. – “Before he went on vacation, Mr. Martinez said I should call you to get this information. u Tech Support - Social engineer pretends to be someone from the infrastructure-support groups. – System is having a problem – Needs them to log on to test the connection
 Human-based u In Person - The social engineer may enter the building and pretend to be an employee, guest or service personnel. – May be dressed in a uniform – Allowed to roam – Becomes part of the cleaning crew u Dumpster diving - Going through the trash u Shoulder Surfing - Looking over a shoulder to see what someone is typing. – Passwords – Phone-card numbers
Human-based u In Person - The social engineer may enter the building and pretend to be an employee, guest or service personnel. – May be dressed in a uniform – Allowed to roam – Becomes part of the cleaning crew u Dumpster diving - Going through the trash u Shoulder Surfing - Looking over a shoulder to see what someone is typing. – Passwords – Phone-card numbers
 Computer-based u Popup Windows - A window will appear on the screen telling the user they have lost their network connection and needs to reenter their user name and password. – A program will then e-mail the intruder the information. u Mail attachments - Programs can and are frequently hidden in e-mail attachments. – Viruses – Worms – Trojans
Computer-based u Popup Windows - A window will appear on the screen telling the user they have lost their network connection and needs to reenter their user name and password. – A program will then e-mail the intruder the information. u Mail attachments - Programs can and are frequently hidden in e-mail attachments. – Viruses – Worms – Trojans
 Computer-based u Spam, Chain Letters and Hoaxes - These all rely on social engineering to be spread. – While they do not usually cause damage, they do cause a loss of productivity. – Frequently used by entrepreneurs in African countries (e. g. , Nigerian scams) – They use valuable network resources. u Websites - A common ploy is to offer something – free or a chance to win a sweepstakes on a Website. To register requires an e-mail address and password.
Computer-based u Spam, Chain Letters and Hoaxes - These all rely on social engineering to be spread. – While they do not usually cause damage, they do cause a loss of productivity. – Frequently used by entrepreneurs in African countries (e. g. , Nigerian scams) – They use valuable network resources. u Websites - A common ploy is to offer something – free or a chance to win a sweepstakes on a Website. To register requires an e-mail address and password.
 Computer-based Hacking Made Easy (http: //www. washingtonpost. com/wp-dyn/content/article/2006/03/16/AR 2006031600916_pf. html ) u When Graeme Frost received an e-mail notice that an expensive digital camera had been charged to his credit card account, he immediately clicked on the Internet link included in the message that said it would allow him to dispute the charge. As the 29 -year-old resident of southwestern England scoured the resulting Web page for the merchant's phone number, the site silently installed a password-stealing program that transmitted all of his personal and financial information. u Frost is just one of thousands of victims whose personal data has been stolen by what security experts are calling one of the more brazen and sophisticated Internet fraud rings ever uncovered. The Web-based software employed by ring members to manage large numbers of illegally commandeered computers is just as easy to use as basic commercial office programs. No knowledge of computer programming or hacking techniques is required to operate the software, which allows the user to infiltrate and steal financial information from thousands of PCs simultaneously. u The quality of the software tools cyber criminals are using to sort through the mountains of information they've stolen is a clear sign that they are seeking more efficient ways to monetize that data, experts say.
Computer-based Hacking Made Easy (http: //www. washingtonpost. com/wp-dyn/content/article/2006/03/16/AR 2006031600916_pf. html ) u When Graeme Frost received an e-mail notice that an expensive digital camera had been charged to his credit card account, he immediately clicked on the Internet link included in the message that said it would allow him to dispute the charge. As the 29 -year-old resident of southwestern England scoured the resulting Web page for the merchant's phone number, the site silently installed a password-stealing program that transmitted all of his personal and financial information. u Frost is just one of thousands of victims whose personal data has been stolen by what security experts are calling one of the more brazen and sophisticated Internet fraud rings ever uncovered. The Web-based software employed by ring members to manage large numbers of illegally commandeered computers is just as easy to use as basic commercial office programs. No knowledge of computer programming or hacking techniques is required to operate the software, which allows the user to infiltrate and steal financial information from thousands of PCs simultaneously. u The quality of the software tools cyber criminals are using to sort through the mountains of information they've stolen is a clear sign that they are seeking more efficient ways to monetize that data, experts say.
 Computer-based Hacking Made Easy u Frost's data, along with information stolen from thousands of other victims, made its way to a Web site hosted by a Russian Internet service provider. The site is currently the home base of a network of sites designed to break into computers through a security hole in Microsoft's Internet Explorer Web browser. The data thieves use the IE flaw to install programs known as "keyloggers" on computers that visit the specially coded Web pages. The keyloggers then copy the victims' stored passwords and computer keystrokes and upload that information to the database. u The hacking software also features automated tools that allow the fraudsters to make minute adjustments or sweeping changes to their networks of hacked PCs. With the click of a mouse or a drag on a pull-down menu, users can add or delete files on infected computers. u They can even update their spyware installations with new versions tailored to defeat the most recent anti-virus updates. With one click on the Web site's "Add New Exploit" button, users can simultaneously modify all of the keylogger programs already installed on their networks. u Symantec and other security experts also have spotted earlier versions of the software installed on at least two other Web sites, one of which is still active and has harvested password information from nearly 30, 000 victims, the bulk of whom reside in the United States and Brazil.
Computer-based Hacking Made Easy u Frost's data, along with information stolen from thousands of other victims, made its way to a Web site hosted by a Russian Internet service provider. The site is currently the home base of a network of sites designed to break into computers through a security hole in Microsoft's Internet Explorer Web browser. The data thieves use the IE flaw to install programs known as "keyloggers" on computers that visit the specially coded Web pages. The keyloggers then copy the victims' stored passwords and computer keystrokes and upload that information to the database. u The hacking software also features automated tools that allow the fraudsters to make minute adjustments or sweeping changes to their networks of hacked PCs. With the click of a mouse or a drag on a pull-down menu, users can add or delete files on infected computers. u They can even update their spyware installations with new versions tailored to defeat the most recent anti-virus updates. With one click on the Web site's "Add New Exploit" button, users can simultaneously modify all of the keylogger programs already installed on their networks. u Symantec and other security experts also have spotted earlier versions of the software installed on at least two other Web sites, one of which is still active and has harvested password information from nearly 30, 000 victims, the bulk of whom reside in the United States and Brazil.
 Computer-based Hacking Made Easy (http: //www. washingtonpost. com/wp-dyn/content/article/2006/03/16/AR 2006031600916_pf. html ) Keyloggers – Watching while you type… u u u Fast becoming among the most prevalent and insidious online threats: More than half of the viruses, worms and other malicious computer code that Symantec now tracks are designed not to harm host machines but to surreptitiously gather data from them. These keylogger-control Web sites follow a trend toward automation in other realms of online fraud, such as virus-creation programs, spamming software and pre-packaged toolkits to help fraudsters set up "phishing" sites -- Web pages designed to trick people into giving away their personal and financial data at what looks like a legitimate e-commerce or banking site. "This type of plug-and-play, click-and-hack software simply represents the commercialization of criminal activity, and in many respects lowers the technical knowledge barrier of entry to this type of crime. " Online criminals hack into thousands of small-merchant Web sites and embed code that silently install keyloggers when users browse the sites with Internet Explorer. A recent analysis for SANS estimated that nearly 10 million U. S. households own a computer that is infected with some type of keystroke logging program. Although not every PC user whose keystrokes are being logged has experienced financial losses the analysis estimates that organized-crime groups have access to roughly $24 billion in bank assets from accounts associated with the owners of infected machines.
Computer-based Hacking Made Easy (http: //www. washingtonpost. com/wp-dyn/content/article/2006/03/16/AR 2006031600916_pf. html ) Keyloggers – Watching while you type… u u u Fast becoming among the most prevalent and insidious online threats: More than half of the viruses, worms and other malicious computer code that Symantec now tracks are designed not to harm host machines but to surreptitiously gather data from them. These keylogger-control Web sites follow a trend toward automation in other realms of online fraud, such as virus-creation programs, spamming software and pre-packaged toolkits to help fraudsters set up "phishing" sites -- Web pages designed to trick people into giving away their personal and financial data at what looks like a legitimate e-commerce or banking site. "This type of plug-and-play, click-and-hack software simply represents the commercialization of criminal activity, and in many respects lowers the technical knowledge barrier of entry to this type of crime. " Online criminals hack into thousands of small-merchant Web sites and embed code that silently install keyloggers when users browse the sites with Internet Explorer. A recent analysis for SANS estimated that nearly 10 million U. S. households own a computer that is infected with some type of keystroke logging program. Although not every PC user whose keystrokes are being logged has experienced financial losses the analysis estimates that organized-crime groups have access to roughly $24 billion in bank assets from accounts associated with the owners of infected machines.
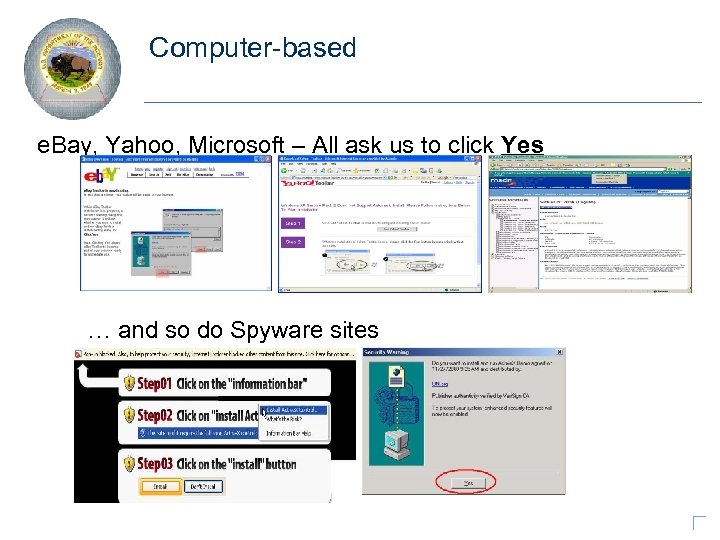 Computer-based e. Bay, Yahoo, Microsoft – All ask us to click Yes … and so do Spyware sites
Computer-based e. Bay, Yahoo, Microsoft – All ask us to click Yes … and so do Spyware sites
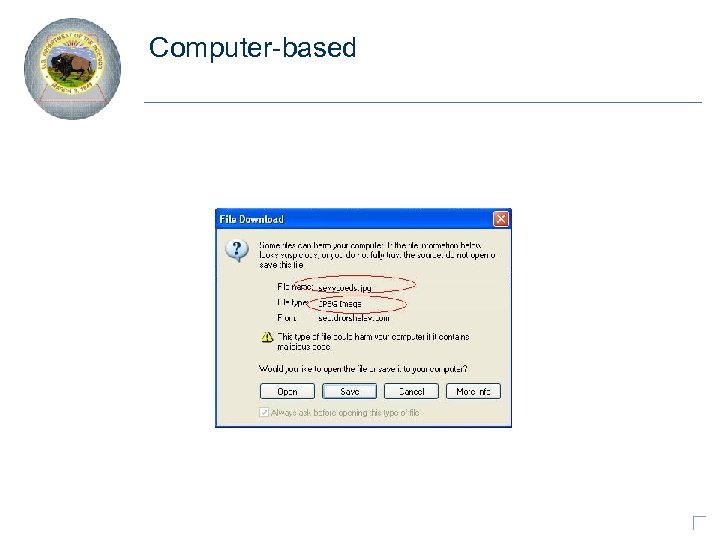 Computer-based
Computer-based
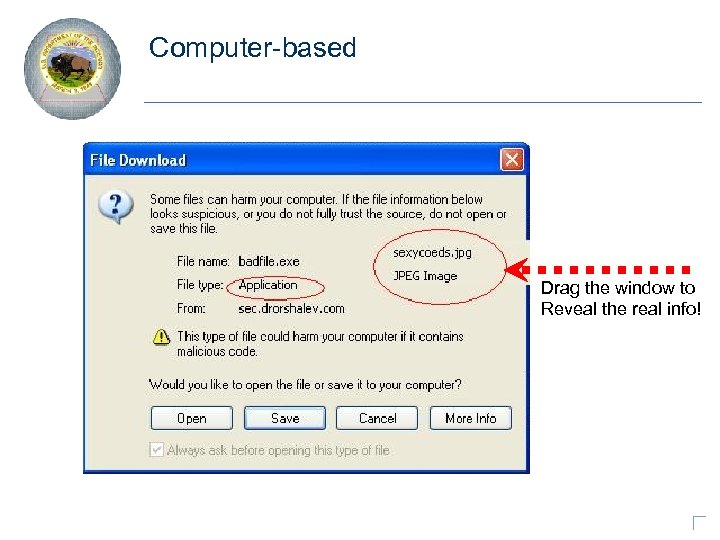 Computer-based Drag the window to Reveal the real info!
Computer-based Drag the window to Reveal the real info!
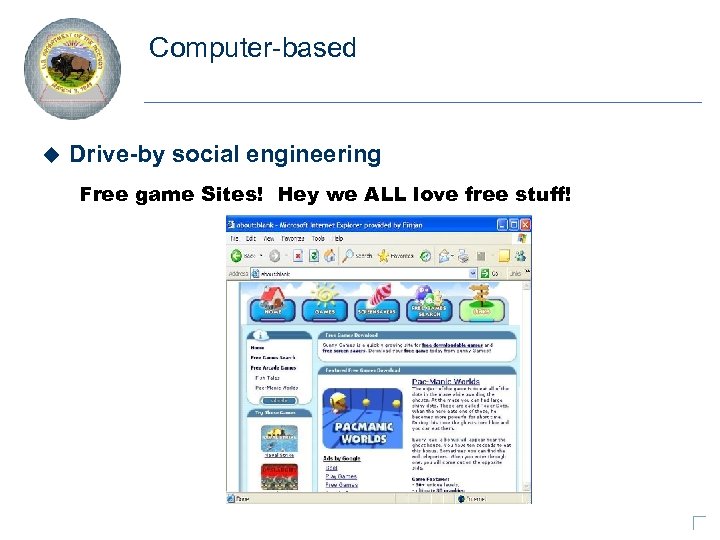 Computer-based u Drive-by social engineering Free game Sites! Hey we ALL love free stuff!
Computer-based u Drive-by social engineering Free game Sites! Hey we ALL love free stuff!
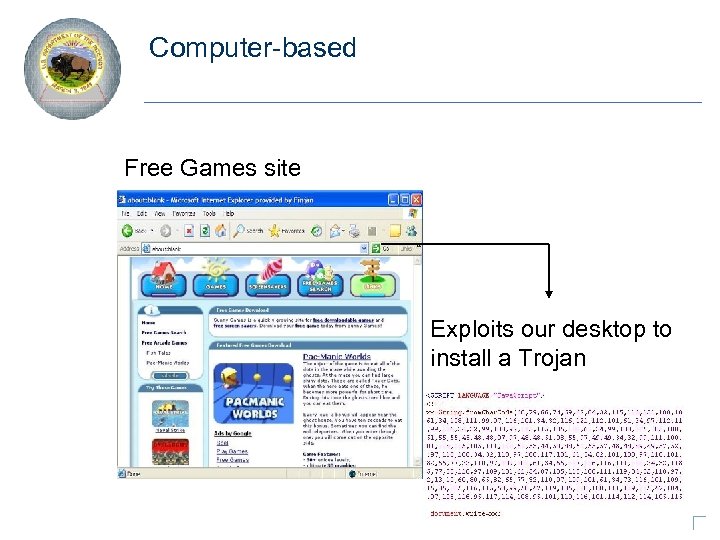 Computer-based Free Games site Exploits our desktop to install a Trojan
Computer-based Free Games site Exploits our desktop to install a Trojan
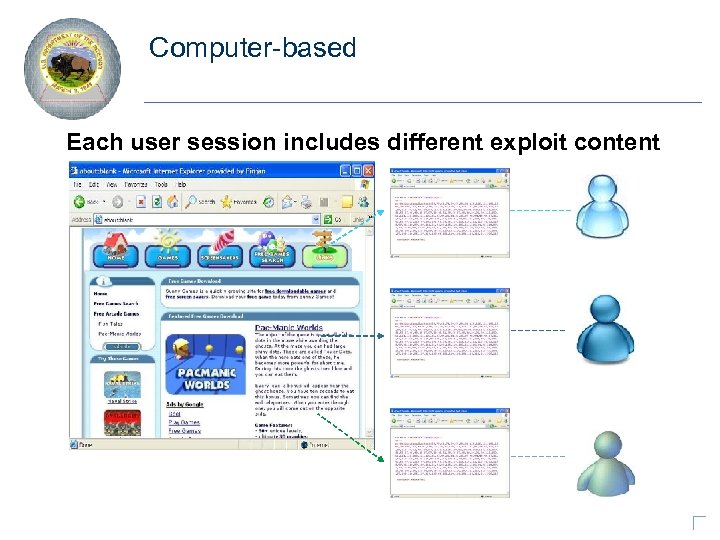 Computer-based Each user session includes different exploit content
Computer-based Each user session includes different exploit content
 Common Types of Social Engineering Exploit Methods v Most dire request (e. g. , recent Pay. Pal e-mail phishing scams) v Contrived situation (e. g. , Nigerian e-mail scams)
Common Types of Social Engineering Exploit Methods v Most dire request (e. g. , recent Pay. Pal e-mail phishing scams) v Contrived situation (e. g. , Nigerian e-mail scams)
 Exploiting Human Nature and Personality Traits Social engineers prey on qualities of human nature and personality traits: Ø the desire to be helpful, cooperative, or a team player Ø the tendency to trust people Ø the fear of getting into trouble, moral obligation or duty, guilt The most skilled social engineer is able to obtain information without raising any suspicion as to what they are doing.
Exploiting Human Nature and Personality Traits Social engineers prey on qualities of human nature and personality traits: Ø the desire to be helpful, cooperative, or a team player Ø the tendency to trust people Ø the fear of getting into trouble, moral obligation or duty, guilt The most skilled social engineer is able to obtain information without raising any suspicion as to what they are doing.
 Personality Traits u In the following discussion we will examine how various social engineering personality traits enhance the possibility of successful social engineering. u When present, these traits increase the likelihood of compliance.
Personality Traits u In the following discussion we will examine how various social engineering personality traits enhance the possibility of successful social engineering. u When present, these traits increase the likelihood of compliance.
 Personality Traits u Diffusion of responsibility - The target is made to believe that they are not solely responsible for their actions. – The social engineer creates situations with many factors that dilute personal responsibility for decision making. – The social engineer may drop names. – May claim someone higher up has made the decision. u Chance for ingratiation - The target is lead to believe that compliance with the request will enhance their chances of receiving some sort of benefit. – Gaining advantage over a competitor. – Getting in good with the boss.
Personality Traits u Diffusion of responsibility - The target is made to believe that they are not solely responsible for their actions. – The social engineer creates situations with many factors that dilute personal responsibility for decision making. – The social engineer may drop names. – May claim someone higher up has made the decision. u Chance for ingratiation - The target is lead to believe that compliance with the request will enhance their chances of receiving some sort of benefit. – Gaining advantage over a competitor. – Getting in good with the boss.
 Personality Traits u Trust Relationships - The social engineer expends time developing a trust relationship with the intended victim. – Usually following a series of small interactions. u Moral duty - Encouraging the target to act out of a sense of moral duty or moral outrage. – Requires the social engineer to gather information on the target and the organization. – Tries to get the target to believe that compliance will mitigate some sort of wrong that has been done.
Personality Traits u Trust Relationships - The social engineer expends time developing a trust relationship with the intended victim. – Usually following a series of small interactions. u Moral duty - Encouraging the target to act out of a sense of moral duty or moral outrage. – Requires the social engineer to gather information on the target and the organization. – Tries to get the target to believe that compliance will mitigate some sort of wrong that has been done.
 Personality Traits u Guilt-Most individuals attempt to avoid guilt feelings if possible. – Social engineers create situations designed to: – tug at the heartstrings – manipulate empathy – create sympathy – If granting a request will lead to avoidance of guilt, target is more likely to comply. – Believing that not granting the request will lead to significant problems to the requestor is often enough to weigh the balance in favor of compliance with the request.
Personality Traits u Guilt-Most individuals attempt to avoid guilt feelings if possible. – Social engineers create situations designed to: – tug at the heartstrings – manipulate empathy – create sympathy – If granting a request will lead to avoidance of guilt, target is more likely to comply. – Believing that not granting the request will lead to significant problems to the requestor is often enough to weigh the balance in favor of compliance with the request.
 Personality Traits u Identification - Trying to get the target to identify with the social engineer. – The social engineer tries to build a connection with the target based on information gathered. – Informality is another trait social engineers excel at. u Desire to help - Social engineers rely on people’s desire to be helpful. – Holding the door. – Logging on to an account. – Lack of assertiveness or refusal skills.
Personality Traits u Identification - Trying to get the target to identify with the social engineer. – The social engineer tries to build a connection with the target based on information gathered. – Informality is another trait social engineers excel at. u Desire to help - Social engineers rely on people’s desire to be helpful. – Holding the door. – Logging on to an account. – Lack of assertiveness or refusal skills.
 Personality Traits u Cooperation - The less conflict with the target the better. – Voice of reason – logic – patience
Personality Traits u Cooperation - The less conflict with the target the better. – Voice of reason – logic – patience
 Social Engineering Example Mr. Smith: Hello? Caller: Hello, Mr. Smith. This is Fred Jones in tech support. Due to some disk space constraints, we’re going to be moving some user’s home directories to another disk at 8: 00 this evening. Your account will be part of this move, and will be unavailable temporarily. Mr. Smith: Uh, okay. I’ll be home by then, anyway. Caller: Good. Be sure to log off before you leave. I just need to check a couple of things. What was your username again, smith? Mr. Smith: Yes. It’s smith. None of my files will be lost in the move, will they? Caller: No sir. But I’ll check your account just to make sure. What was the password on that account, so I can get in to check your files? Mr. Smith: My password is Tuesday, in lower case letters. Caller: Okay, Mr. Smith, thank you for your help. I’ll make sure to check you account and verify all the files are there. Mr. Smith: Thank you. Bye.
Social Engineering Example Mr. Smith: Hello? Caller: Hello, Mr. Smith. This is Fred Jones in tech support. Due to some disk space constraints, we’re going to be moving some user’s home directories to another disk at 8: 00 this evening. Your account will be part of this move, and will be unavailable temporarily. Mr. Smith: Uh, okay. I’ll be home by then, anyway. Caller: Good. Be sure to log off before you leave. I just need to check a couple of things. What was your username again, smith? Mr. Smith: Yes. It’s smith. None of my files will be lost in the move, will they? Caller: No sir. But I’ll check your account just to make sure. What was the password on that account, so I can get in to check your files? Mr. Smith: My password is Tuesday, in lower case letters. Caller: Okay, Mr. Smith, thank you for your help. I’ll make sure to check you account and verify all the files are there. Mr. Smith: Thank you. Bye.
 Potential Security Breaches u Help Desks - They try too hard to be helpful. u Websites - As we discussed before, setting up a bogus website to trap information (e. g. , clone any well-known web site and cause people to click on a bogus link in an e -mail to enter their logon credentials – phishing). u A social engineer may simply walk in and behave like one of the employees. – We tend NOT to challenge unfamiliar personnel often enough
Potential Security Breaches u Help Desks - They try too hard to be helpful. u Websites - As we discussed before, setting up a bogus website to trap information (e. g. , clone any well-known web site and cause people to click on a bogus link in an e -mail to enter their logon credentials – phishing). u A social engineer may simply walk in and behave like one of the employees. – We tend NOT to challenge unfamiliar personnel often enough
 Common Defenses u Everyone that enters the building (contractors, business partners, vendors, employees) must show identification. u Passwords should never be spoken over the phone. u Passwords are not to be left lying around – they must be stored in a secure location only accessible to the individual they were issued to. u Caller ID technology can be used to help verify who you are speaking to. u Properly destroy passwords and all sensitive but unclassified (SBU) information - invest in and properly use shredders and degaussers.
Common Defenses u Everyone that enters the building (contractors, business partners, vendors, employees) must show identification. u Passwords should never be spoken over the phone. u Passwords are not to be left lying around – they must be stored in a secure location only accessible to the individual they were issued to. u Caller ID technology can be used to help verify who you are speaking to. u Properly destroy passwords and all sensitive but unclassified (SBU) information - invest in and properly use shredders and degaussers.
 Recognize the Signs u Recognize key signs that indicate you may be the target of a social engineering attack: – Refusal to give contact information – “I cannot be contacted” – “I’m on my cell phone and the battery is about to die” – The number they give you is a “call out only” number – Rushing – Name-dropping – Intimidation – Small mistakes – Requesting sensitive information
Recognize the Signs u Recognize key signs that indicate you may be the target of a social engineering attack: – Refusal to give contact information – “I cannot be contacted” – “I’m on my cell phone and the battery is about to die” – The number they give you is a “call out only” number – Rushing – Name-dropping – Intimidation – Small mistakes – Requesting sensitive information
 Defense… the 2 step… (actually 4 step) Step 1 u If you cannot personally identify a caller who asks for Personal information about you or anyone else (including badge number or employee number), for information about your computer system, or for any other sensitive information, do not provide the information. u Insist on verifying the caller’s identity by calling them back at their proper telephone number as listed in organization’s telephone directory. This procedure creates minimal inconvenience to legitimate activity when compared with the scope of potential losses.
Defense… the 2 step… (actually 4 step) Step 1 u If you cannot personally identify a caller who asks for Personal information about you or anyone else (including badge number or employee number), for information about your computer system, or for any other sensitive information, do not provide the information. u Insist on verifying the caller’s identity by calling them back at their proper telephone number as listed in organization’s telephone directory. This procedure creates minimal inconvenience to legitimate activity when compared with the scope of potential losses.
 Defense… the 2 step… (actually 4 step) Step 2 u Remember that passwords are sensitive. A password for your personal account should be known ONLY to you. Systems administrators or maintenance technicians who need to do something to your account will not require your password. They have their own password with system privileges that will allow them to work on your account without the need for you to reveal you password. If a system administrator or maintenance technician asks you for your password, be suspicious, very suspicious.
Defense… the 2 step… (actually 4 step) Step 2 u Remember that passwords are sensitive. A password for your personal account should be known ONLY to you. Systems administrators or maintenance technicians who need to do something to your account will not require your password. They have their own password with system privileges that will allow them to work on your account without the need for you to reveal you password. If a system administrator or maintenance technician asks you for your password, be suspicious, very suspicious.
 Defense… the 2 step… (actually 4 step) Step 3 u Systems maintenance technicians from outside vendors who come on site should be accompanied by the local site administrator (who should be known to you). If the site administrator is not familiar to you, or if the technician comes alone, it is wise to give a call to your known site administrator to check if the technician should be there. Unfortunately, many people are reluctant to do this because it makes them look paranoid, and it is embarrassing to show that they do not trust a visitor.
Defense… the 2 step… (actually 4 step) Step 3 u Systems maintenance technicians from outside vendors who come on site should be accompanied by the local site administrator (who should be known to you). If the site administrator is not familiar to you, or if the technician comes alone, it is wise to give a call to your known site administrator to check if the technician should be there. Unfortunately, many people are reluctant to do this because it makes them look paranoid, and it is embarrassing to show that they do not trust a visitor.
 Defense… the 2 step… (actually 4 step) Step 4 u If you feel you have thwarted or perhaps been victimized by an attempt at social engineering, report the incident to your manager and to security personnel immediately!
Defense… the 2 step… (actually 4 step) Step 4 u If you feel you have thwarted or perhaps been victimized by an attempt at social engineering, report the incident to your manager and to security personnel immediately!
 Final Thoughts u A social engineer with enough time, patience and tenacity will eventually exploit some weakness in the security of an enterprise. u The best defense against social engineering attacks combines raising the bar of awareness among employees, volunteers and contractors, a sense of personal responsibility to protect DOI’s mission and IT assets, an understanding of the signs of social engineering attacks, and reporting any suspected incidents.
Final Thoughts u A social engineer with enough time, patience and tenacity will eventually exploit some weakness in the security of an enterprise. u The best defense against social engineering attacks combines raising the bar of awareness among employees, volunteers and contractors, a sense of personal responsibility to protect DOI’s mission and IT assets, an understanding of the signs of social engineering attacks, and reporting any suspected incidents.
 Credits (or who I stole this presentation from…) u Plagiarism is the greatest form of flattery u With Permission from Stan Lowe (DOI BLM) – Melissa Guenther – Wikipedia – Foundstone
Credits (or who I stole this presentation from…) u Plagiarism is the greatest form of flattery u With Permission from Stan Lowe (DOI BLM) – Melissa Guenther – Wikipedia – Foundstone
 Ready for a break? Questions?
Ready for a break? Questions?
 United States Department of the Interior Social Engineering & Internal/External Threats March 22, 2006 Lawrence K. Ruffin Lawrence_Ruffin@ios. doi. gov
United States Department of the Interior Social Engineering & Internal/External Threats March 22, 2006 Lawrence K. Ruffin Lawrence_Ruffin@ios. doi. gov
 Internal and External Threats The greatest security risks to an agency frequently come from the action, inaction, or inadvertent mistakes of people. Ø Motivated internal threat agents pose the greatest risk due to their access to sensitive information and privileges Ø External threats pose a risk to vulnerable systems and gaps in network security coverage. It is estimated that 99% of all reported intrusions result through exploitation of known vulnerabilities or configuration errors, for which safeguards and countermeasures were available.
Internal and External Threats The greatest security risks to an agency frequently come from the action, inaction, or inadvertent mistakes of people. Ø Motivated internal threat agents pose the greatest risk due to their access to sensitive information and privileges Ø External threats pose a risk to vulnerable systems and gaps in network security coverage. It is estimated that 99% of all reported intrusions result through exploitation of known vulnerabilities or configuration errors, for which safeguards and countermeasures were available.
 Internal and External Threats Insider Threat Greatest at Financial Institutions By Allen Bernard @ CIOUpdate. com u Internal attacks on information technology systems are surpassing external attacks at the world's largest financial institutions, according to the 2005 Global Security Survey by Deloitte Touche Tohmatsu (DTT). u Thirty-five percent of respondents confirmed encountering attacks from inside their organization in 2005 (up from 14% in 2004) compared to 26% from external sources (up from 23% in 2004).
Internal and External Threats Insider Threat Greatest at Financial Institutions By Allen Bernard @ CIOUpdate. com u Internal attacks on information technology systems are surpassing external attacks at the world's largest financial institutions, according to the 2005 Global Security Survey by Deloitte Touche Tohmatsu (DTT). u Thirty-five percent of respondents confirmed encountering attacks from inside their organization in 2005 (up from 14% in 2004) compared to 26% from external sources (up from 23% in 2004).
 Internal and External Threats Before We Do Anything… u Accept the FACT that vulnerabilities open doors to the unexpected. u Accept that there is NO separation between the cyber world and the physical world. u We’ve become distracted – insider threat is real & growing. u Terrorism is multifaceted. Traditional definitions must be adapted to the new realities. u Change the way you THINK about future threats…don’t be a security APPEASER.
Internal and External Threats Before We Do Anything… u Accept the FACT that vulnerabilities open doors to the unexpected. u Accept that there is NO separation between the cyber world and the physical world. u We’ve become distracted – insider threat is real & growing. u Terrorism is multifaceted. Traditional definitions must be adapted to the new realities. u Change the way you THINK about future threats…don’t be a security APPEASER.
 Appeaser u According to Webster’s Dictionary: u Ap*peas"er, n. One who appeases; a pacifier. u According to Verton’s Dictionary: u Ap*peas"er, n. “One who feeds a crocodile hoping it will eat him last. ” – Sir Winston Churchill
Appeaser u According to Webster’s Dictionary: u Ap*peas"er, n. One who appeases; a pacifier. u According to Verton’s Dictionary: u Ap*peas"er, n. “One who feeds a crocodile hoping it will eat him last. ” – Sir Winston Churchill
 What Do I Really Mean By “Appeasement? ” u Maybe we are growing dangerously complacent? u Maybe we do underestimate our enemies? u Maybe we really do think this is as bad as it can get? u Maybe threat-independent model is not how we should be approaching these issues?
What Do I Really Mean By “Appeasement? ” u Maybe we are growing dangerously complacent? u Maybe we do underestimate our enemies? u Maybe we really do think this is as bad as it can get? u Maybe threat-independent model is not how we should be approaching these issues?
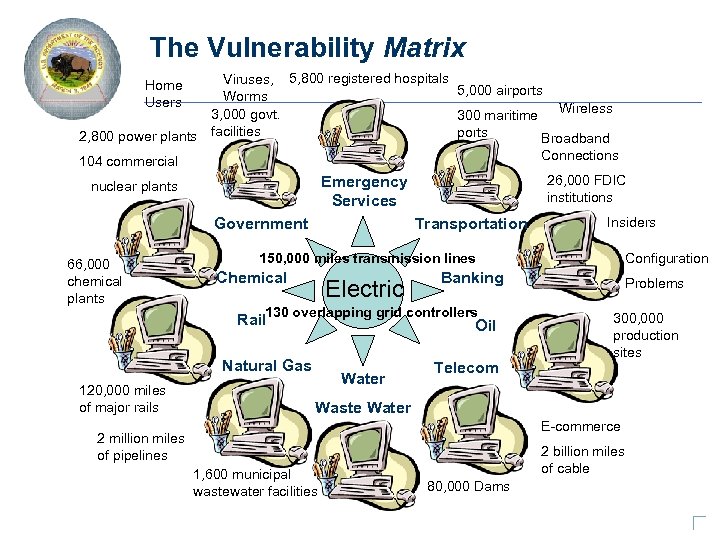 The Vulnerability Matrix Viruses, 5, 800 registered hospitals 5, 000 airports Worms Wireless 3, 000 govt. 300 maritime ports 2, 800 power plants facilities Broadband Connections 104 commercial Home Users Government 66, 000 chemical plants Transportation Insiders 150, 000 miles transmission lines Chemical Electric 120, 000 miles of major rails Water Configuration Banking Rail 130 overlapping grid controllers. Oil Natural Gas 2 million miles of pipelines 26, 000 FDIC institutions Emergency Services nuclear plants Telecom Problems 300, 000 production sites Waste Water E-commerce Natural Gas 1, 600 municipal wastewater facilities 2 billion miles of cable 80, 000 Dams
The Vulnerability Matrix Viruses, 5, 800 registered hospitals 5, 000 airports Worms Wireless 3, 000 govt. 300 maritime ports 2, 800 power plants facilities Broadband Connections 104 commercial Home Users Government 66, 000 chemical plants Transportation Insiders 150, 000 miles transmission lines Chemical Electric 120, 000 miles of major rails Water Configuration Banking Rail 130 overlapping grid controllers. Oil Natural Gas 2 million miles of pipelines 26, 000 FDIC institutions Emergency Services nuclear plants Telecom Problems 300, 000 production sites Waste Water E-commerce Natural Gas 1, 600 municipal wastewater facilities 2 billion miles of cable 80, 000 Dams
 IT Security - How Important Is It Really? u Not only about $… It’s about public safety too! – Railroads. – Water & Wastewater Treatment. – Uranium Mining. – Oil Wells, Water Flood Operations. – Airline Baggage Checking. – Aug. 14 Power Failure. – Online Information Control.
IT Security - How Important Is It Really? u Not only about $… It’s about public safety too! – Railroads. – Water & Wastewater Treatment. – Uranium Mining. – Oil Wells, Water Flood Operations. – Airline Baggage Checking. – Aug. 14 Power Failure. – Online Information Control.
 Risk Management u Risk = Threat * Probability * Impact Ø Threat = an entity likely to have intent and capability to exploit a vulnerability in a system – Disgruntled Insiders (e. g. , employees or contractors) – Hackers for Hire (e. g. , State- or non-State sponsored) – Organized Crime – Terrorists Ø Probability = Likelihood of someone having intent, motivation and capability to exploit a known weakness in a system Ø Impact = Potential magnitude of harm to information or an information system resulting from someone actually exploiting a known weakness
Risk Management u Risk = Threat * Probability * Impact Ø Threat = an entity likely to have intent and capability to exploit a vulnerability in a system – Disgruntled Insiders (e. g. , employees or contractors) – Hackers for Hire (e. g. , State- or non-State sponsored) – Organized Crime – Terrorists Ø Probability = Likelihood of someone having intent, motivation and capability to exploit a known weakness in a system Ø Impact = Potential magnitude of harm to information or an information system resulting from someone actually exploiting a known weakness
 Cyber-Terrorism: Controversial Topic u u Richard Clarke Testifying at 9/11 Commission Hearing, 3/24/04 “The problem is that when you make a recommendation before [an attack] happens, people tend to think you're nuts. ” “That's the kind of mind set that made it difficult for us…the institutional bureaucracy…couldn't see threat because it hadn't happened. ”
Cyber-Terrorism: Controversial Topic u u Richard Clarke Testifying at 9/11 Commission Hearing, 3/24/04 “The problem is that when you make a recommendation before [an attack] happens, people tend to think you're nuts. ” “That's the kind of mind set that made it difficult for us…the institutional bureaucracy…couldn't see threat because it hadn't happened. ”
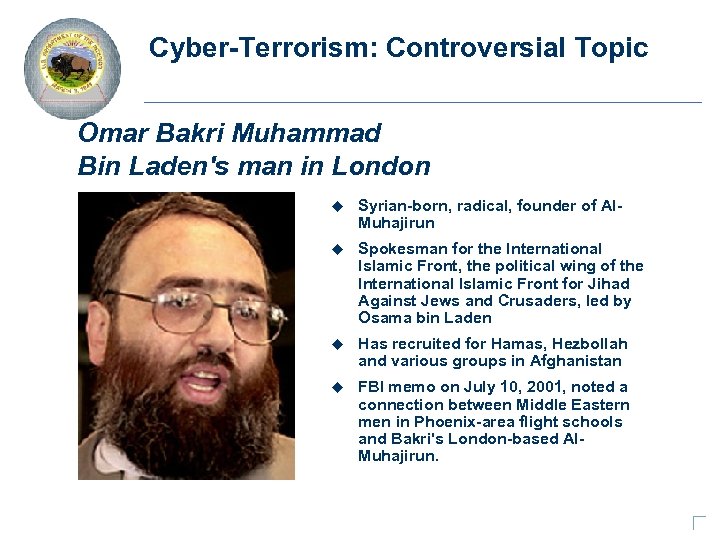 Cyber-Terrorism: Controversial Topic Omar Bakri Muhammad Bin Laden's man in London u Syrian-born, radical, founder of Al. Muhajirun u Spokesman for the International Islamic Front, the political wing of the International Islamic Front for Jihad Against Jews and Crusaders, led by Osama bin Laden u Has recruited for Hamas, Hezbollah and various groups in Afghanistan u FBI memo on July 10, 2001, noted a connection between Middle Eastern men in Phoenix-area flight schools and Bakri's London-based Al. Muhajirun.
Cyber-Terrorism: Controversial Topic Omar Bakri Muhammad Bin Laden's man in London u Syrian-born, radical, founder of Al. Muhajirun u Spokesman for the International Islamic Front, the political wing of the International Islamic Front for Jihad Against Jews and Crusaders, led by Osama bin Laden u Has recruited for Hamas, Hezbollah and various groups in Afghanistan u FBI memo on July 10, 2001, noted a connection between Middle Eastern men in Phoenix-area flight schools and Bakri's London-based Al. Muhajirun.
 Cyber-Terrorism: Controversial Topic Bakri On Cyber Attacks u "In a matter of time, you will see attacks on the stock market. " u “I would not be surprised if tomorrow I hear of a big economic collapse because of somebody attacking the main technical systems in big companies. " u "The third letter from Osama bin Laden…was clearly addressing using the technology in order to destroy the economy of the capitalist states. This is a matter that is very clear. "
Cyber-Terrorism: Controversial Topic Bakri On Cyber Attacks u "In a matter of time, you will see attacks on the stock market. " u “I would not be surprised if tomorrow I hear of a big economic collapse because of somebody attacking the main technical systems in big companies. " u "The third letter from Osama bin Laden…was clearly addressing using the technology in order to destroy the economy of the capitalist states. This is a matter that is very clear. "
 Insider Threats • Why spend R&D money when you can steal it? • Economic Espionage: $ hundreds of billions • Four forms of insider: Ø Internal (current/former employees, executives) Ø External (contractor, maintenance, business partner) Ø Collaborator (external working with internal) Ø Rogue Ideologue (seeks hire for purpose of doing harm) • Technology Complicates Internal Defenses Ø The Perimeter is gone! Ø USB devices, cell phone cameras, common configuration errors, lack of access controls, contractors, outsourcing
Insider Threats • Why spend R&D money when you can steal it? • Economic Espionage: $ hundreds of billions • Four forms of insider: Ø Internal (current/former employees, executives) Ø External (contractor, maintenance, business partner) Ø Collaborator (external working with internal) Ø Rogue Ideologue (seeks hire for purpose of doing harm) • Technology Complicates Internal Defenses Ø The Perimeter is gone! Ø USB devices, cell phone cameras, common configuration errors, lack of access controls, contractors, outsourcing
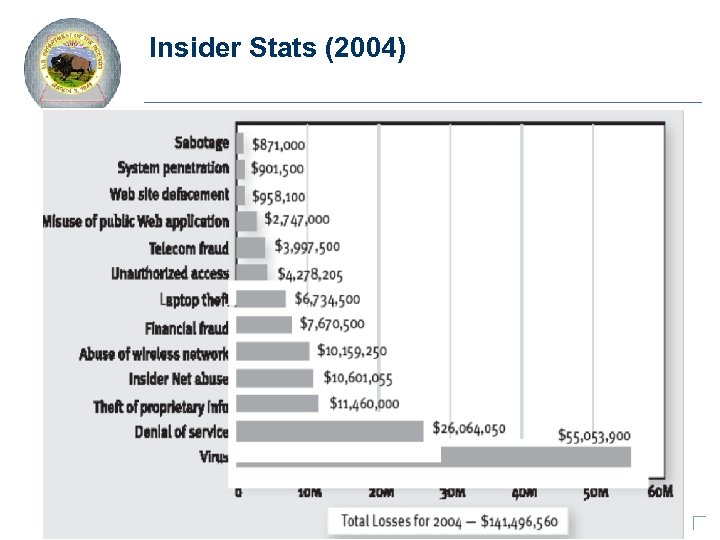 Insider Stats (2004)
Insider Stats (2004)
 Types of Data Being Stolen • • Computer source code Business plans and design specifications Customer and order information databases Motorola 2 -way radio specifications Newest Intel chip specifications (twice) Sales and pricing data Oil and gas well logs and software used in the analysis of the information • Engineering drawings for next generation of Gillette razor systems • Eng. Drawings Next Generation Space Shuttle (inside or outside? ? )
Types of Data Being Stolen • • Computer source code Business plans and design specifications Customer and order information databases Motorola 2 -way radio specifications Newest Intel chip specifications (twice) Sales and pricing data Oil and gas well logs and software used in the analysis of the information • Engineering drawings for next generation of Gillette razor systems • Eng. Drawings Next Generation Space Shuttle (inside or outside? ? )
 Case: Ramon • An intellectual of sorts, highly educated, conservative in his politics, painfully introverted, somewhat arrogant and kind of a geek. • Expert programmer who preferred communicating with associates through e-mail rather than in person. • Hacked his employer's computer system without permission to show management that there were serious security gaps that needed to be fixed. Ø Robert Hanssen – The worst insider spy case in FBI history.
Case: Ramon • An intellectual of sorts, highly educated, conservative in his politics, painfully introverted, somewhat arrogant and kind of a geek. • Expert programmer who preferred communicating with associates through e-mail rather than in person. • Hacked his employer's computer system without permission to show management that there were serious security gaps that needed to be fixed. Ø Robert Hanssen – The worst insider spy case in FBI history.
 Insider Psychological Profile Introverted: A common characteristic of IT specialists, which can pose a significant management challenge. Frustrated: Family or social problems may be compounded by negative attitudes toward authority. Computer-dependent: Such individuals often prefer online activity to direct social interaction. Ethical flexibility: Dangerous insiders view malicious actions as justified, given their circumstances. Entitlement: Feelings of being “special” employees—for example, the only ones with the necessary training. Being overworked with no rewards can lead to a desire for revenge. Reduced loyalty: Some insiders identify with the IT/programming profession and not with the organization that employs them. Lack of empathy: The impersonal nature of cyberspace leads to a lack of regard for the impact of the perpetrators’ actions on others.
Insider Psychological Profile Introverted: A common characteristic of IT specialists, which can pose a significant management challenge. Frustrated: Family or social problems may be compounded by negative attitudes toward authority. Computer-dependent: Such individuals often prefer online activity to direct social interaction. Ethical flexibility: Dangerous insiders view malicious actions as justified, given their circumstances. Entitlement: Feelings of being “special” employees—for example, the only ones with the necessary training. Being overworked with no rewards can lead to a desire for revenge. Reduced loyalty: Some insiders identify with the IT/programming profession and not with the organization that employs them. Lack of empathy: The impersonal nature of cyberspace leads to a lack of regard for the impact of the perpetrators’ actions on others.
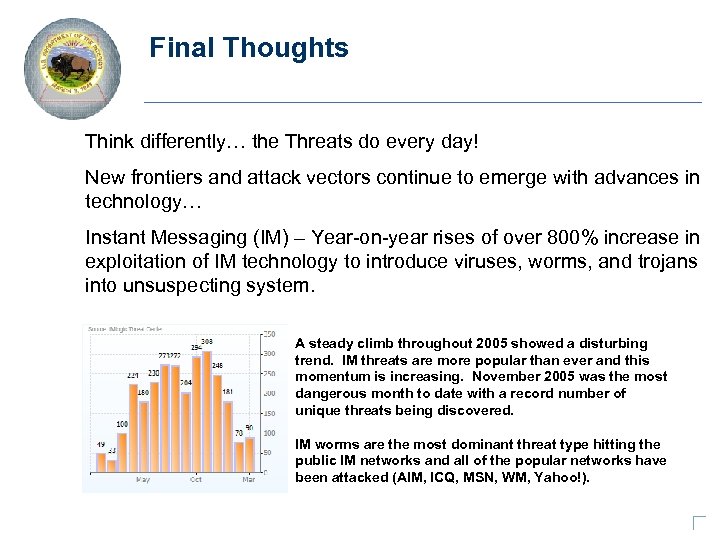 Final Thoughts Think differently… the Threats do every day! New frontiers and attack vectors continue to emerge with advances in technology… Instant Messaging (IM) – Year-on-year rises of over 800% increase in exploitation of IM technology to introduce viruses, worms, and trojans into unsuspecting system. A steady climb throughout 2005 showed a disturbing trend. IM threats are more popular than ever and this momentum is increasing. November 2005 was the most dangerous month to date with a record number of unique threats being discovered. IM worms are the most dominant threat type hitting the public IM networks and all of the popular networks have been attacked (AIM, ICQ, MSN, WM, Yahoo!).
Final Thoughts Think differently… the Threats do every day! New frontiers and attack vectors continue to emerge with advances in technology… Instant Messaging (IM) – Year-on-year rises of over 800% increase in exploitation of IM technology to introduce viruses, worms, and trojans into unsuspecting system. A steady climb throughout 2005 showed a disturbing trend. IM threats are more popular than ever and this momentum is increasing. November 2005 was the most dangerous month to date with a record number of unique threats being discovered. IM worms are the most dominant threat type hitting the public IM networks and all of the popular networks have been attacked (AIM, ICQ, MSN, WM, Yahoo!).
 Final Thoughts Think differently… the Threats do every day! New frontiers and attack vectors continue to emerge with advances in technology… Wireless technology and devices potentially open back-doors into networks and bridges agency trusted networks with un-trusted networks and the public infrastructure (the Internet). Highly portable media with enormous storage capacity on extremely small footprints can be used to steal information.
Final Thoughts Think differently… the Threats do every day! New frontiers and attack vectors continue to emerge with advances in technology… Wireless technology and devices potentially open back-doors into networks and bridges agency trusted networks with un-trusted networks and the public infrastructure (the Internet). Highly portable media with enormous storage capacity on extremely small footprints can be used to steal information.
 Credits u Dan Verton - Vice President & Executive Editor, IT Security Magazine, FISSEA March 2005 presentation on Cyber-Terrorism and Security
Credits u Dan Verton - Vice President & Executive Editor, IT Security Magazine, FISSEA March 2005 presentation on Cyber-Terrorism and Security
 Thank You Questions?
Thank You Questions?


