0796dbf04565f728daf0e780f0d9c918.ppt
- Количество слайдов: 34
Trust-Level Based Authentication Services in Mobile Ad Hoc Networks MPhil Term 2 Presentation (Spring 2003) by Edith Ngai Advisor: Prof. Michael R. Lyu
Outline Background Related Work Trust-Level Based Authentication Services Self-Initialization Certificate Renewal Future Work Discussion. Science and Engineering, The Chinese University of Hong & Conclusion Department of Computer Kong 2
Background Mobile Ad Hoc Network An ad hoc network is a collection of nodes that do not need to rely on predefined infrastructure to keep the network connected. Nodes of ad hoc networks are often mobile, apply wireless communication (MANET) Applications – – Personal area networks Military communications Sensor networks Disaster area networks Department of Computer Science and Engineering, The Chinese University of Hong Kong 3
Background Characteristics Dynamic network topology Limited physical security Limited bandwidth Energy constrained nodes Natures of ad hoc networks make them vulnerable to security attacks Passive eavesdropping Denial of service attacks by malicious nodes Attacks from compromised entities or stolen devices Department of Computer Science and Engineering, The Chinese University of Hong Kong 4
Background Vulnerabilities – Traditional network vs Ad hoc network Wired network – Adversary must gain physical access to wired link – Adversary has to sneak through security holes at firewalls or routers Ad hoc network – Wireless links give poor physical protection – Mobile nodes are capable of roaming independently – Decentralized management Department of Computer Science and Engineering, The Chinese University of Hong 5 Kong
Background Key Management Security in networks widely rely on key management mechanisms Trust third party (TTP) is an entity trusted by all users and is often used to provide key management services Certificate authorities (CA) is a public key management system responsible for issuing and revoking certificates A certificate binds the identity of an entity to its public key Department of Computer Science and Engineering, The Chinese University of Hong Kong 6
Background Public Key Encryption We use public key encryption to secure the network It can obtain non-repudiation, confidentiality, integrity and authentication Adversary can defeat the system by impersonation when entities are exchanging public keys, or alter the public file containing public keys Public key cryptography requires the authenticity of public keys Department of Computer Science and Engineering, The Chinese University of Hong Kong 7
Related Work Traditional network authentication solutions rely on TTP or CA Popular network authentication architectures include X. 509 and Kerberos. Some model on hierarchical CAs Ad hoc network is infrastructureless No centralized server for key Department of Computer Science and Engineering, The Chinese University of Hong management Kong 8
Related Work Pretty Good Privacy (PGP) is proposed following a web of trust authentication model. A node rely on trusted PGP users to introduce others Threshold secret sharing can distribute the functionality of centralized CA server among a fixed group of servers Proactive secret sharing can improve robustness by updating secret keys Department of Computer Science and Engineering, The Chinese University of Hong 9 periodically Kong
Related Work Partially distributed certificate authority – makes use of a (k, n) threshold scheme to distribute the services of CA to a set of specialized server nodes – requires rich network connectivity among group of servers Fully distributed certificate authority – extends certificate services to every nodes and a threshold number of neighboring nodes can collaboratively act as a authentication server – requires enough neighboring nodes Department of Computer Science and Engineering, The Chinese University of Hong 10 Kong
Related Work Self-issued certificates – Issues certificates by users themselves without the involvement of any certificate authority – Any pair of users can find certificate chains to each other using their certificate repositories – Problem exists if certificates issued did not reach certain amont Department of Computer Science and Engineering, The Chinese University of Hong Kong 11
Trust-Level Based Authentication Services Primitives Adopt fully distributed certificate authorities approach Combine the authentication services with trust level concept Apply weighted threshold secret sharing instead of general threshold secret sharing scheme Extend certificate services not limited to neighboring nodes using trust chains Department of Computer Science and Engineering, The Chinese University of Hong Kong 12
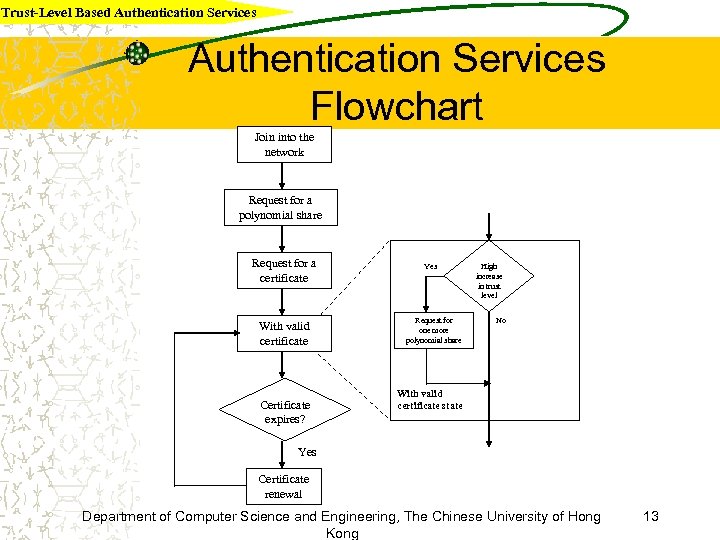
Trust-Level Based Authentication Services Flowchart Join into the network Request for a polynomial share Request for a certificate With valid certificate Certificate expires? Yes Request for one more polynomial share High increase in trust level No With valid certificate state Yes Certificate renewal Department of Computer Science and Engineering, The Chinese University of Hong Kong 13
Trust-Level Based Authentication Services Trust Model A trust model defines how the nodes in the network trust each other Past work on authentication services just define trust model to be - a node with valid certificate can be trusted in the network We add in the concept of trust level We define that each node keeps a trust value to each of its neighboring nodes Department of Computer Science and Engineering, The Chinese University of Hong Kong 14
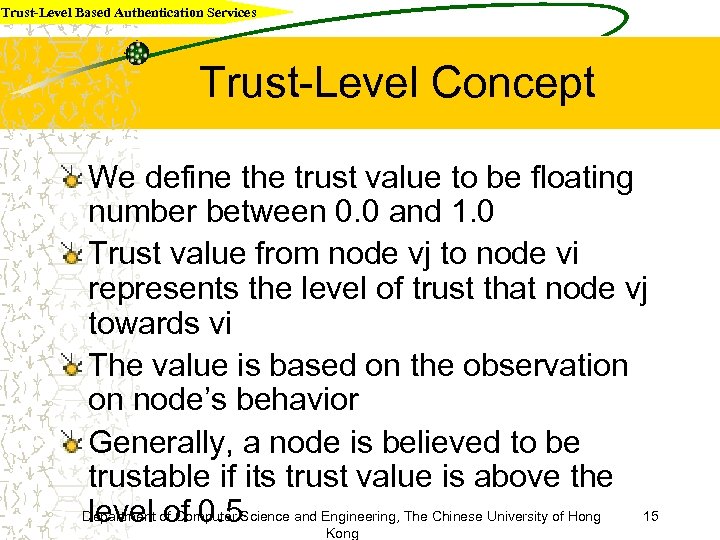
Trust-Level Based Authentication Services Trust-Level Concept We define the trust value to be floating number between 0. 0 and 1. 0 Trust value from node vj to node vi represents the level of trust that node vj towards vi The value is based on the observation on node’s behavior Generally, a node is believed to be trustable if its trust value is above the Department of Computer Science and Engineering, The Chinese University of Hong 15 level of 0. 5 Kong
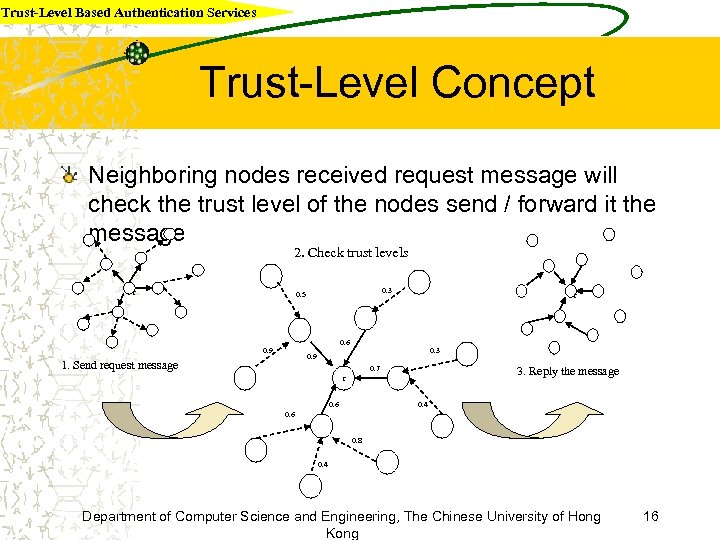
Trust-Level Based Authentication Services Trust-Level Concept Neighboring nodes received request message will check the trust level of the nodes send / forward it the message 2. Check trust levels r 0. 3 0. 5 r 0. 6 0. 9 0. 3 0. 9 1. Send request message 0. 7 3. Reply the message r 0. 6 0. 4 0. 6 0. 8 0. 4 Department of Computer Science and Engineering, The Chinese University of Hong Kong 16
Trust-Level Based Authentication Services Assumptions Each node has a unique ID Each node can discover its one-hop neighbours Communication link within one-hop neighbours is reliable. The mobility is characterized by maximum node moving speed Each node maintains a trust value to each neighbors A node holds a limited number of polynomial shares Trust values on a path can form a trust chain. Department of Computer Science and Engineering, The Chinese University of Hong Kong 17
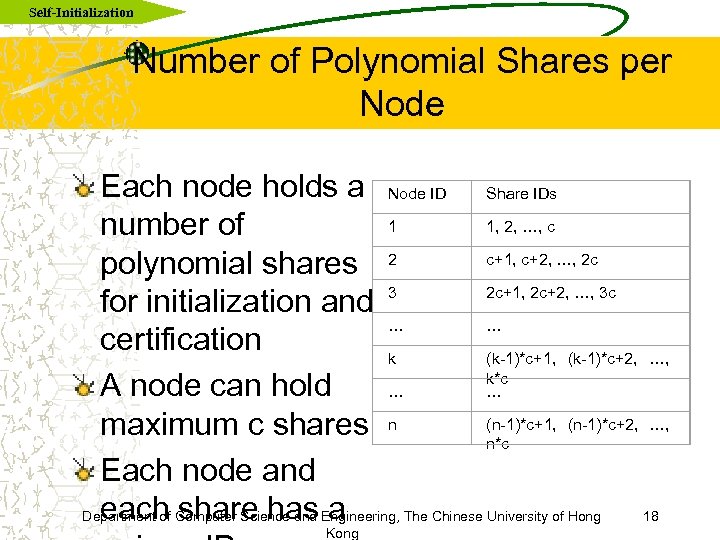
Self-Initialization Number of Polynomial Shares per Node Each node holds a Node ID Share IDs 1 1, 2, …, c number of c+1, c+2, …, 2 c polynomial shares 2 2 c+1, 2 c+2, …, 3 c for initialization and 3 … … certification k (k-1)*c+1, (k-1)*c+2, …, k*c A node can hold … … (n-1)*c+1, (n-1)*c+2, …, maximum c shares n n*c Each node and each share has a Department of Computer Science and Engineering, The Chinese University of Hong 18 Kong
Self-Initialization Request for More Polynomial Share A node gets 1 polynomial share when it joins the network It can request for more polynomial share if its trust level is high enough some time later A field “trust level increased” can be added in the reply message in certification A node can make more contribution to certification and initialization if it holds Department of Computer Science and Engineering, The Chinese University of Hong 19 more shares Kong
Self-Initialization Algorithm Apply the localized self-initialization algorithm A node vi broadcasts its request for a polynomial share Nodes reply to vi with their partial shares Let a 1, a 2, … ak be the polynomial share IDs received by vi, the corresponding polynomial share Pa 1, Pa 2, … Pak 20 Department of Computer Science and Engineering, The Chinese University of Hong Kong
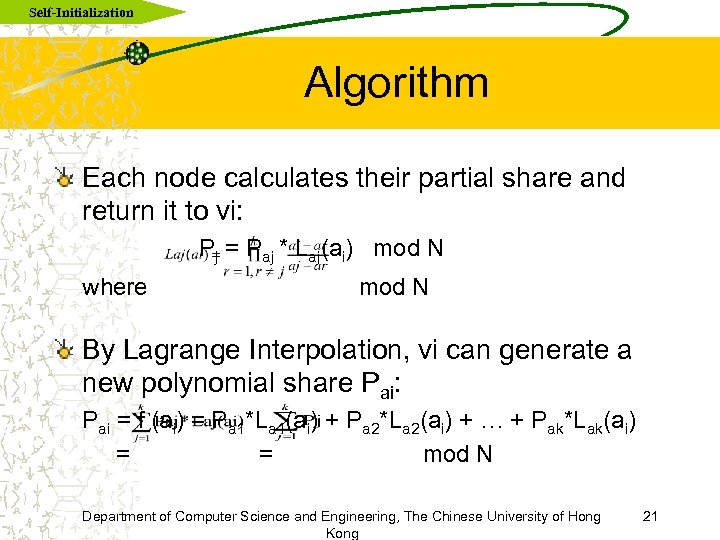
Self-Initialization Algorithm Each node calculates their partial share and return it to vi: Pj = Paj * Laj(ai) mod N where mod N By Lagrange Interpolation, vi can generate a new polynomial share Pai: Pai = f (ai) = Pa 1*La 1(ai) + Pa 2*La 2(ai) + … + Pak*Lak(ai) = = mod N Department of Computer Science and Engineering, The Chinese University of Hong Kong 21
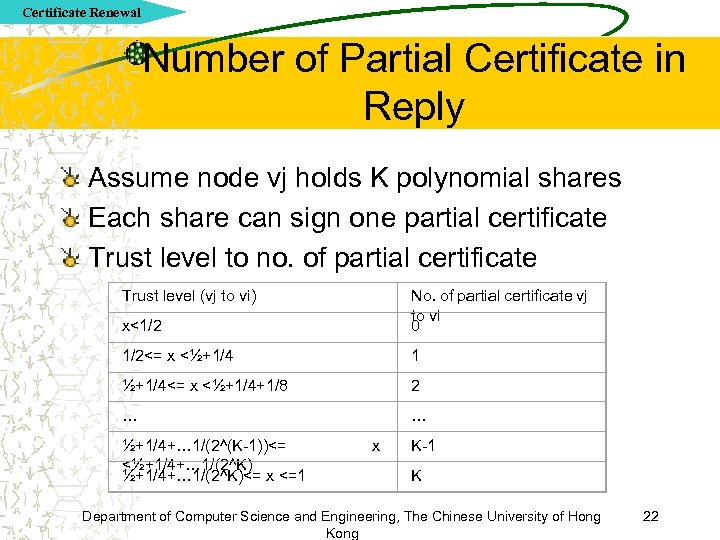
Certificate Renewal Number of Partial Certificate in Reply Assume node vj holds K polynomial shares Each share can sign one partial certificate Trust level to no. of partial certificate Trust level (vj to vi) x<1/2 No. of partial certificate vj to vi 0 1/2<= x <½+1/4 1 ½+1/4<= x <½+1/4+1/8 2 … … ½+1/4+… 1/(2^(K-1))<= <½+1/4+… 1/(2^K)<= x <=1 x K-1 K Department of Computer Science and Engineering, The Chinese University of Hong Kong 22
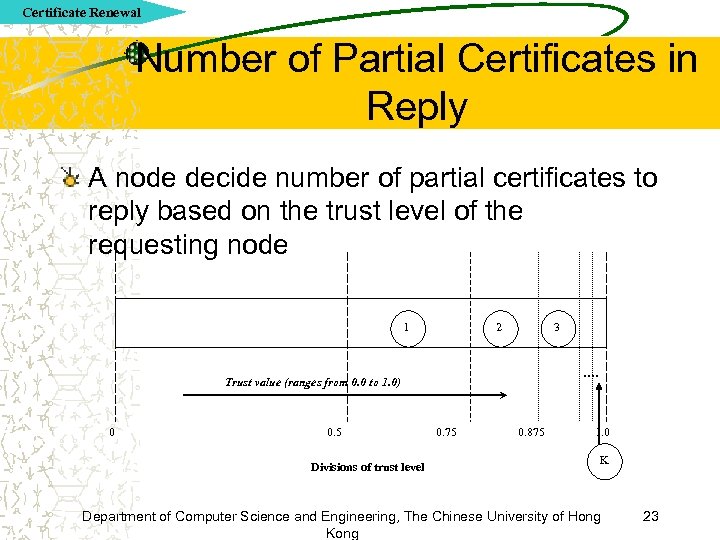
Certificate Renewal Number of Partial Certificates in Reply A node decide number of partial certificates to reply based on the trust level of the requesting node 1 2 3 …. Trust value (ranges from 0. 0 to 1. 0) 0 0. 5 Divisions of trust level 0. 75 0. 875 1. 0 K Department of Computer Science and Engineering, The Chinese University of Hong Kong 23
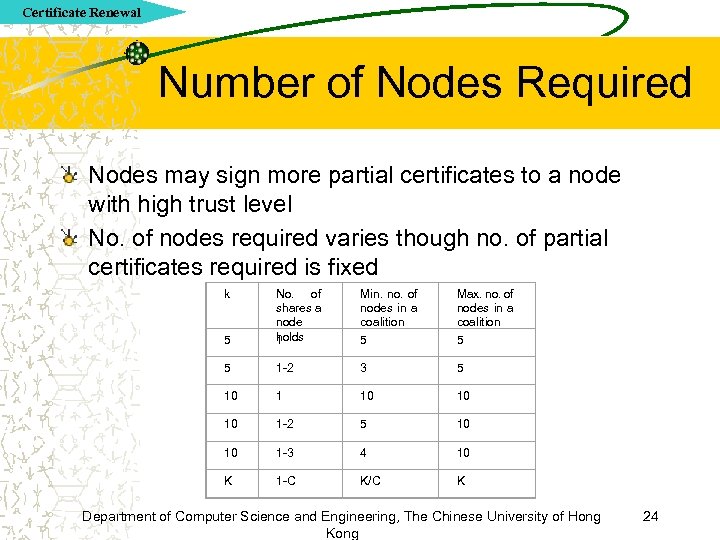
Certificate Renewal Number of Nodes Required Nodes may sign more partial certificates to a node with high trust level No. of nodes required varies though no. of partial certificates required is fixed k 5 No. of shares a node holds 1 Min. no. of nodes in a coalition 5 Max. no. of nodes in a coalition 5 5 1 -2 3 5 10 10 10 1 -2 5 10 10 1 -3 4 10 K 1 -C K/C K Department of Computer Science and Engineering, The Chinese University of Hong Kong 24
Certificate Renewal Trust Relationship of Nodes Certification is not limited to neighboring nodes with our trust level model Nodes have never met can determine each other trustable or not by a trust chain vi V 2 v 2 V 1 v 1 Trust values can be calculated to a single value with formula Department of Computer Science and Engineering, The Chinese University of Hong Kong 25
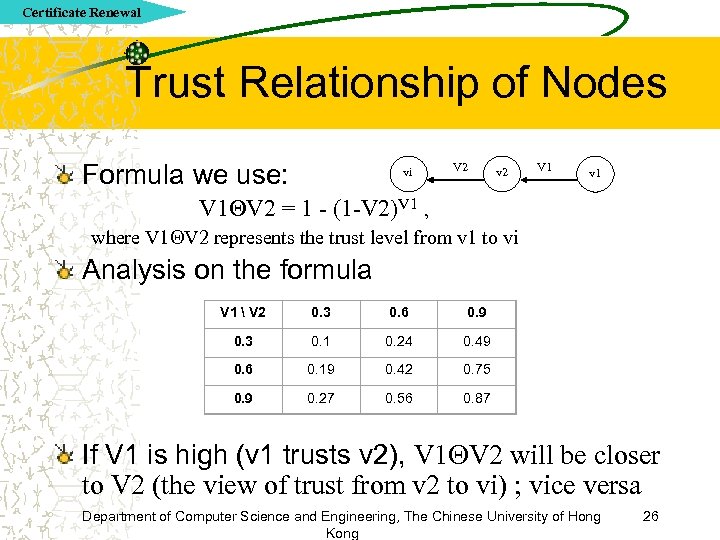
Certificate Renewal Trust Relationship of Nodes Formula we use: vi V 2 v 2 V 1 v 1 V 2 = 1 - (1 -V 2)V 1 , where V 1 V 2 represents the trust level from v 1 to vi Analysis on the formula V 1 V 2 0. 3 0. 6 0. 9 0. 3 0. 1 0. 24 0. 49 0. 6 0. 19 0. 42 0. 75 0. 9 0. 27 0. 56 0. 87 If V 1 is high (v 1 trusts v 2), V 1 V 2 will be closer to V 2 (the view of trust from v 2 to vi) ; vice versa Department of Computer Science and Engineering, The Chinese University of Hong Kong 26
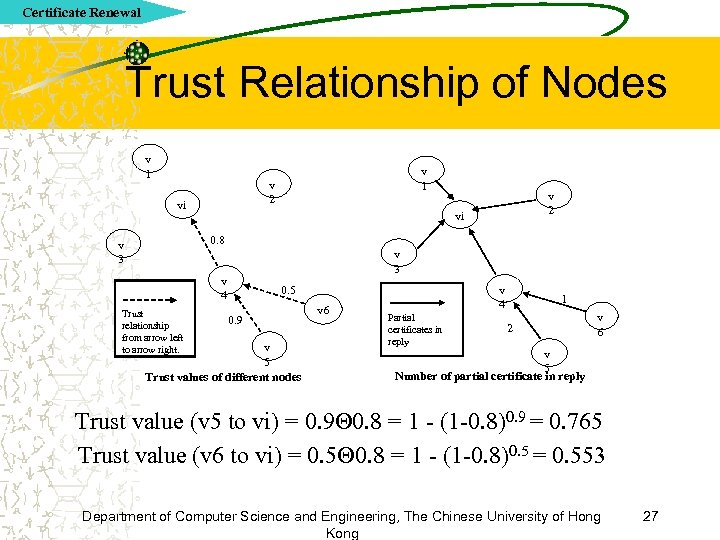
Certificate Renewal Trust Relationship of Nodes v 1 v 2 vi 0. 8 v 3 v 4 Trust relationship from arrow left to arrow right. v 4 0. 5 0. 9 v 5 Trust values of different nodes v 6 Partial certificates in reply 1 2 v 6 v 5 Number of partial certificate in reply Trust value (v 5 to vi) = 0. 9 0. 8 = 1 - (1 -0. 8)0. 9 = 0. 765 Trust value (v 6 to vi) = 0. 5 0. 8 = 1 - (1 -0. 8)0. 5 = 0. 553 Department of Computer Science and Engineering, The Chinese University of Hong Kong 27
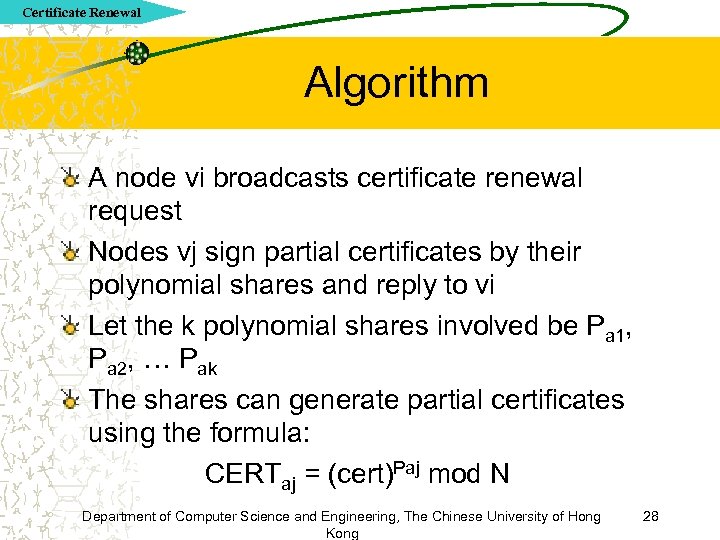
Certificate Renewal Algorithm A node vi broadcasts certificate renewal request Nodes vj sign partial certificates by their polynomial shares and reply to vi Let the k polynomial shares involved be Pa 1, Pa 2, … Pak The shares can generate partial certificates using the formula: CERTaj = (cert)Paj mod N Department of Computer Science and Engineering, The Chinese University of Hong Kong 28
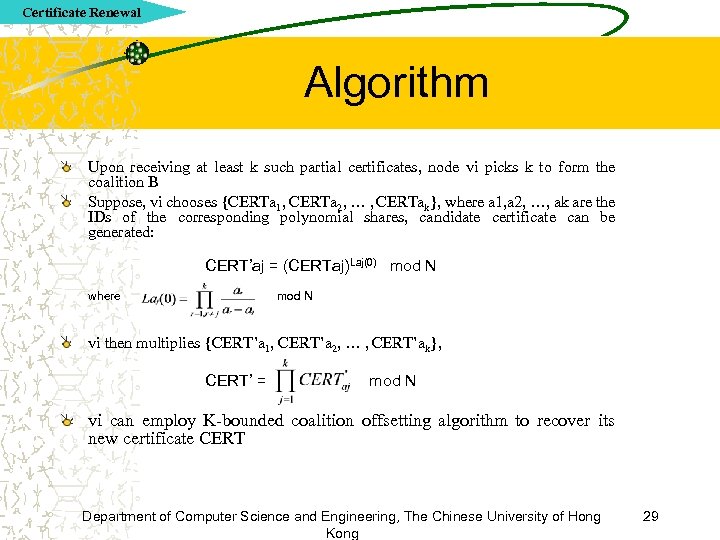
Certificate Renewal Algorithm Upon receiving at least k such partial certificates, node vi picks k to form the coalition B Suppose, vi chooses {CERTa 1, CERTa 2, … , CERTak}, where a 1, a 2, …, ak are the IDs of the corresponding polynomial shares, candidate certificate can be generated: CERT’aj = (CERTaj)Laj(0) mod N where mod N vi then multiplies {CERT’a 1, CERT’a 2, … , CERT’ak}, CERT’ = mod N vi can employ K-bounded coalition offsetting algorithm to recover its new certificate CERT Department of Computer Science and Engineering, The Chinese University of Hong Kong 29
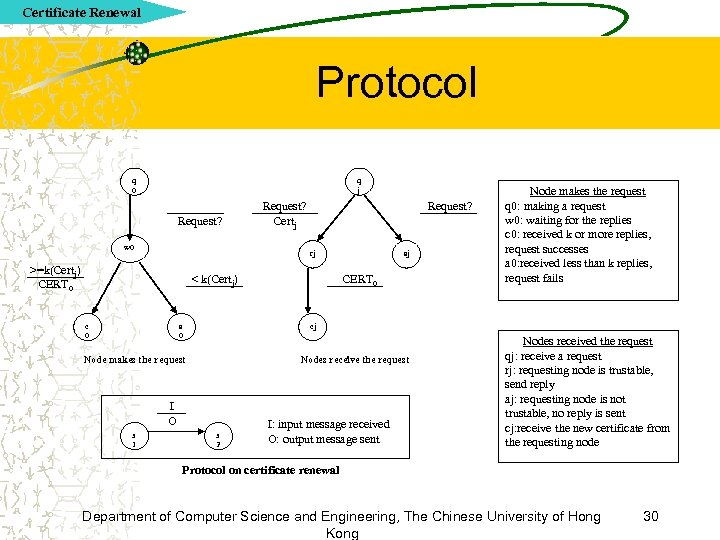
Certificate Renewal Protocol q 0 q j Request? w 0 Request? Certj Request? rj >=k(Certj) CERT 0 < k(Certj) c 0 a 0 CERT 0 cj Node makes the request Nodes receive the request I O s 1 aj Node makes the request q 0: making a request w 0: waiting for the replies c 0: received k or more replies, request successes a 0: received less than k replies, request fails s 2 I: input message received O: output message sent Nodes received the request qj: receive a request rj: requesting node is trustable, send reply aj: requesting node is not trustable, no reply is sent cj: receive the new certificate from the requesting node Protocol on certificate renewal Department of Computer Science and Engineering, The Chinese University of Hong Kong 30
Future Work Simulation will be carried out To evaluate the performance of our authentication services Possible simulators can simulate ad hoc networks are Ns-2, glomosim, etc Main difficulty is how to modify the C++ and Otcl codes in Ns-2 for simulation Department of Computer Science and Engineering, The Chinese University of Hong Kong 31
Discussion Trust-level concept – Formalizes the authentication services in network – Classifies the trust of nodes by levels – Allows weighted threshold secret sharing and trust chain be applied Weighted threshold secret sharing – Speeds up collection of enough shares in certification and initialization – Nodes can make more contribution with high trust level – Coalition size decreases dynamically according to trust level of nodes Trust chain – Allows nodes never met to determine the trust of each other – Reduces the Science and Engineering, The Chinese University nodes Department of Computer problem of not enough neighboring of Hong in 32 Kong
Conclusion We studied the characteristics, vulnerabilities and key management techniques of mobile ad hoc networks We proposed a scalable distributed authentication services to secure mobile ad hoc networks We combined trust level concept and fully distributed CA approach to provide authentication services We applied weighted threshold secret sharing scheme Department of Computer Science and Engineering, The Chinese University of Hong Kong 33
Q&A Department of Computer Science and Engineering, The Chinese University of Hong Kong 34
0796dbf04565f728daf0e780f0d9c918.ppt