b1b1217b5b209d4ded10bf9464acb86f.ppt
- Количество слайдов: 22
 Trust calculus for PKI Roman Novotný, Milan Vereščák
Trust calculus for PKI Roman Novotný, Milan Vereščák
 Outline l l l PKI Maurer deterministic model Maurer probabilistic model Maurer PKI on P 2 P Roman continues with modeling in real world
Outline l l l PKI Maurer deterministic model Maurer probabilistic model Maurer PKI on P 2 P Roman continues with modeling in real world
 Public key infrastructure (PKI) l l l PKI – complex distributed systems of the end entities, CA, certificates, RA Public key cryptography Certificate issuance Certificate validation Certificate revocation CA – trusted third party
Public key infrastructure (PKI) l l l PKI – complex distributed systems of the end entities, CA, certificates, RA Public key cryptography Certificate issuance Certificate validation Certificate revocation CA – trusted third party
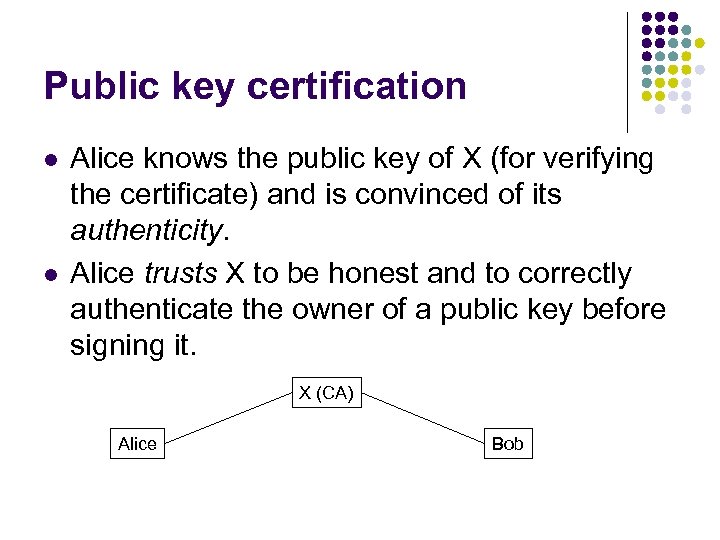 Public key certification l l Alice knows the public key of X (for verifying the certificate) and is convinced of its authenticity. Alice trusts X to be honest and to correctly authenticate the owner of a public key before signing it. X (CA) Alice Bob
Public key certification l l Alice knows the public key of X (for verifying the certificate) and is convinced of its authenticity. Alice trusts X to be honest and to correctly authenticate the owner of a public key before signing it. X (CA) Alice Bob
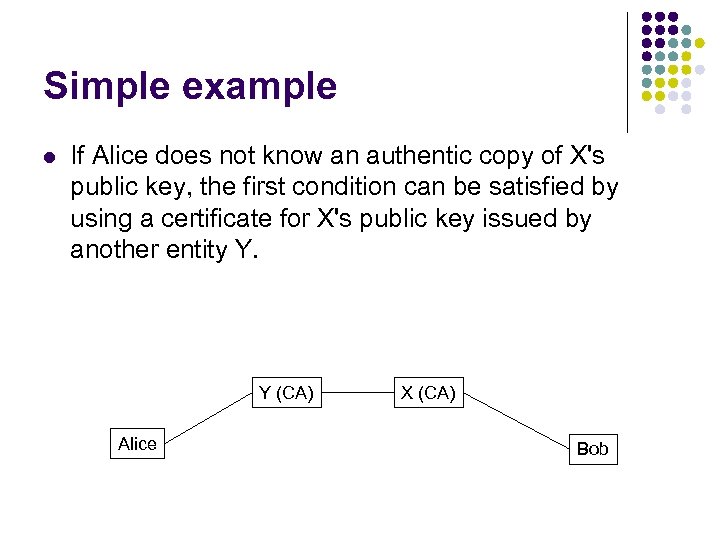 Simple example l If Alice does not know an authentic copy of X's public key, the first condition can be satisfied by using a certificate for X's public key issued by another entity Y. Y (CA) Alice X (CA) Bob
Simple example l If Alice does not know an authentic copy of X's public key, the first condition can be satisfied by using a certificate for X's public key issued by another entity Y. Y (CA) Alice X (CA) Bob
 Maurer PKI deterministic model Requirements: l Generality and expressive power. l Precise Semantics. l Evaluation order independence. l Efficient implementation. l Scalability. l Easy usability.
Maurer PKI deterministic model Requirements: l Generality and expressive power. l Precise Semantics. l Evaluation order independence. l Efficient implementation. l Scalability. l Easy usability.
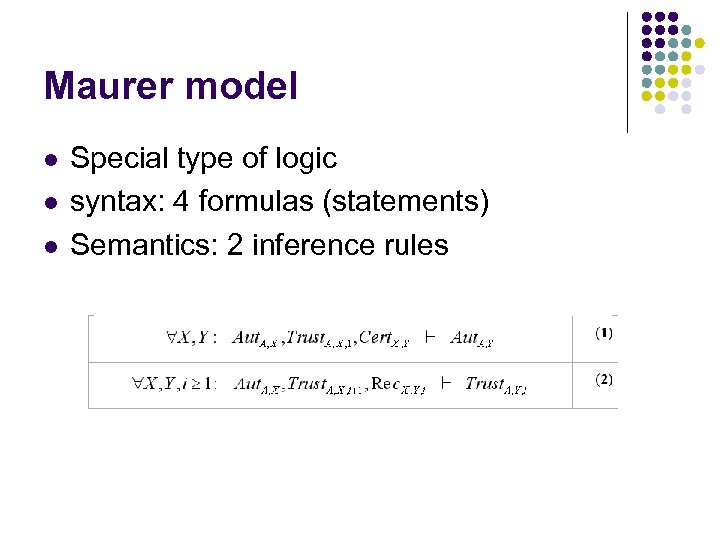 Maurer model l Special type of logic syntax: 4 formulas (statements) Semantics: 2 inference rules
Maurer model l Special type of logic syntax: 4 formulas (statements) Semantics: 2 inference rules
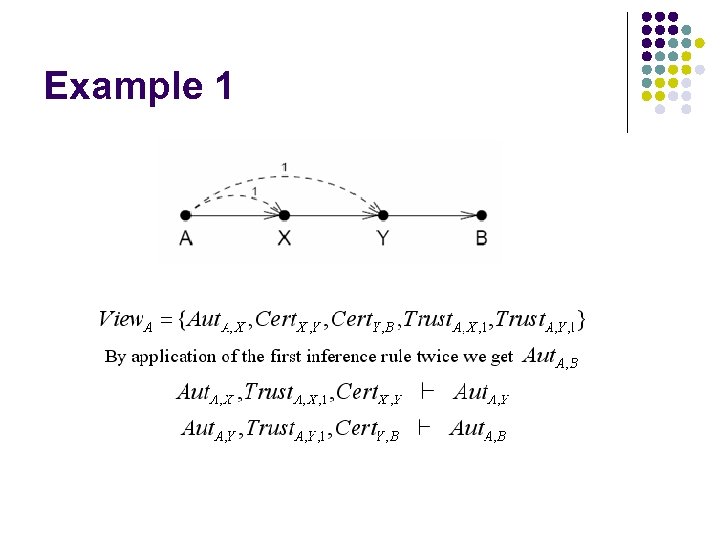 Example 1
Example 1
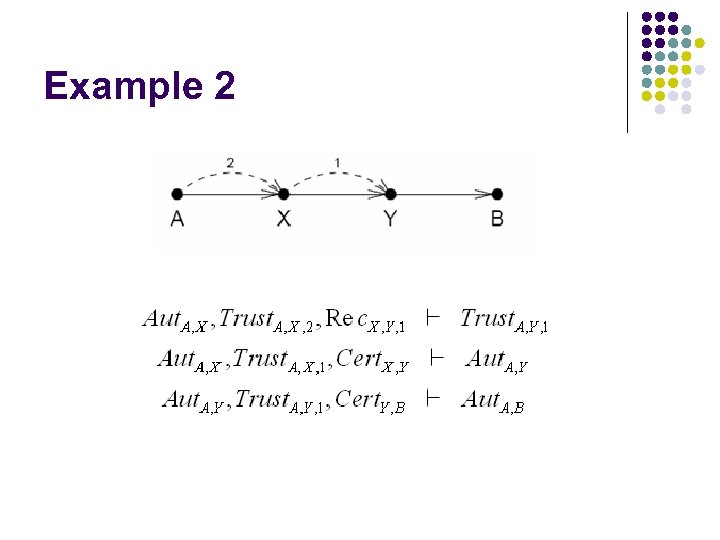 Example 2
Example 2
 Probablistic Maurer model l True/false (trust/distrust) This model measures validity on continuos scale from 0 to 1 Every statement has assigned confidence parameter
Probablistic Maurer model l True/false (trust/distrust) This model measures validity on continuos scale from 0 to 1 Every statement has assigned confidence parameter
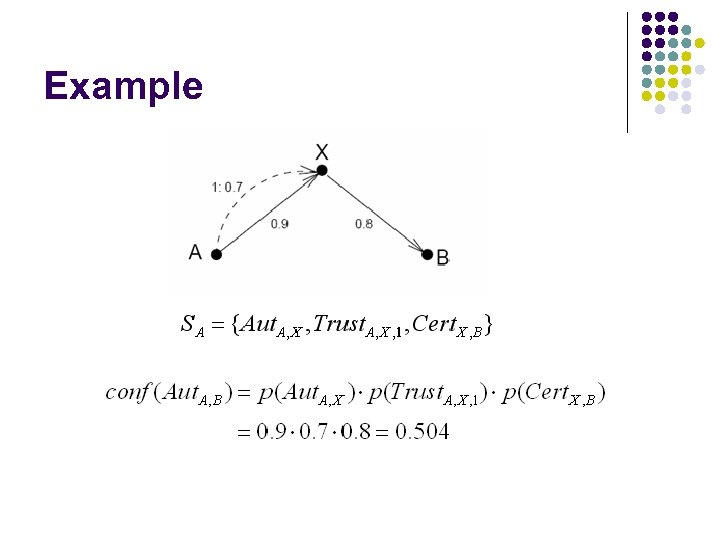 Example
Example
 PKI based on P 2 P network l l l Based on Chord: scalable p 2 p lookup protocol Chord p 2 p network consists of nodes maps given key onto a node Node identifier (e. g. IP address of node) Key (e. g. filename) Hash function maps both the key and the node identifier into m-bit identifier
PKI based on P 2 P network l l l Based on Chord: scalable p 2 p lookup protocol Chord p 2 p network consists of nodes maps given key onto a node Node identifier (e. g. IP address of node) Key (e. g. filename) Hash function maps both the key and the node identifier into m-bit identifier
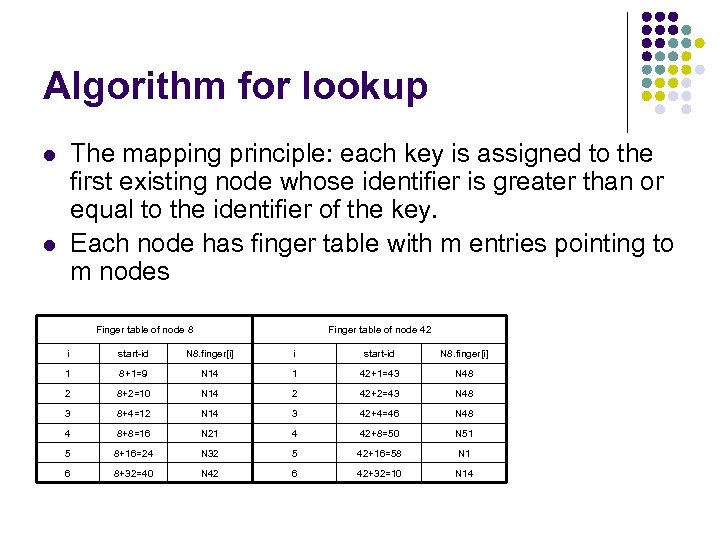 Algorithm for lookup The mapping principle: each key is assigned to the first existing node whose identifier is greater than or equal to the identifier of the key. Each node has finger table with m entries pointing to m nodes l l Finger table of node 8 Finger table of node 42 i start-id N 8. finger[i] 1 8+1=9 N 14 1 42+1=43 N 48 2 8+2=10 N 14 2 42+2=43 N 48 3 8+4=12 N 14 3 42+4=46 N 48 4 8+8=16 N 21 4 42+8=50 N 51 5 8+16=24 N 32 5 42+16=58 N 1 6 8+32=40 N 42 6 42+32=10 N 14
Algorithm for lookup The mapping principle: each key is assigned to the first existing node whose identifier is greater than or equal to the identifier of the key. Each node has finger table with m entries pointing to m nodes l l Finger table of node 8 Finger table of node 42 i start-id N 8. finger[i] 1 8+1=9 N 14 1 42+1=43 N 48 2 8+2=10 N 14 2 42+2=43 N 48 3 8+4=12 N 14 3 42+4=46 N 48 4 8+8=16 N 21 4 42+8=50 N 51 5 8+16=24 N 32 5 42+16=58 N 1 6 8+32=40 N 42 6 42+32=10 N 14
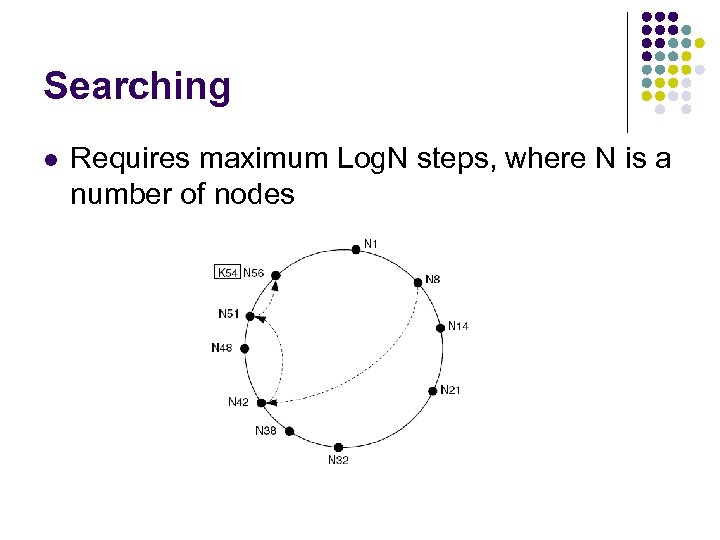 Searching l Requires maximum Log. N steps, where N is a number of nodes
Searching l Requires maximum Log. N steps, where N is a number of nodes
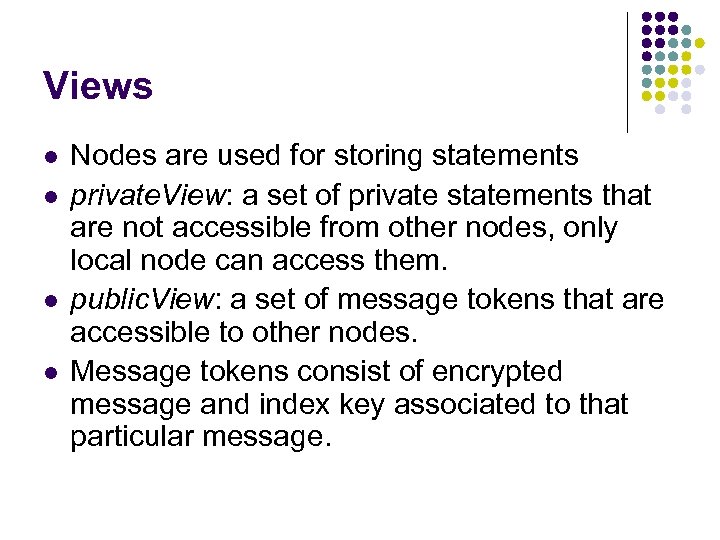 Views l l Nodes are used for storing statements private. View: a set of private statements that are not accessible from other nodes, only local node can access them. public. View: a set of message tokens that are accessible to other nodes. Message tokens consist of encrypted message and index key associated to that particular message.
Views l l Nodes are used for storing statements private. View: a set of private statements that are not accessible from other nodes, only local node can access them. public. View: a set of message tokens that are accessible to other nodes. Message tokens consist of encrypted message and index key associated to that particular message.
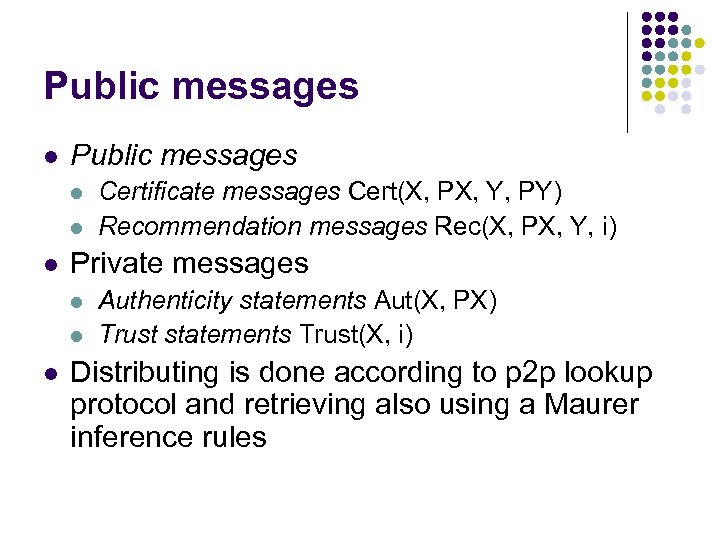 Public messages l l l Private messages l l l Certificate messages Cert(X, PX, Y, PY) Recommendation messages Rec(X, PX, Y, i) Authenticity statements Aut(X, PX) Trust statements Trust(X, i) Distributing is done according to p 2 p lookup protocol and retrieving also using a Maurer inference rules
Public messages l l l Private messages l l l Certificate messages Cert(X, PX, Y, PY) Recommendation messages Rec(X, PX, Y, i) Authenticity statements Aut(X, PX) Trust statements Trust(X, i) Distributing is done according to p 2 p lookup protocol and retrieving also using a Maurer inference rules
 Advantages of P 2 P model l load distribution: Hash function distributes message tokens (public messages) uniformly among the nodes. scalability: We need Log(N) steps to retrieve or publicate a message token of the total number of N nodes. fault resistance: This is because of decentralized character of this model.
Advantages of P 2 P model l load distribution: Hash function distributes message tokens (public messages) uniformly among the nodes. scalability: We need Log(N) steps to retrieve or publicate a message token of the total number of N nodes. fault resistance: This is because of decentralized character of this model.
 Improvement of model l Binding between public keys and certification informations Time – aware model Validity template
Improvement of model l Binding between public keys and certification informations Time – aware model Validity template
 Statements l l l Authenticity of binding - Aut(A, X, P, I) Trust – Trust(A, X, D, I) Certificates – Cert(X, Y, P, I) Trust Transfers – Tran(X, Y, P, I) Certification Validity Templates – Val(A, C, t) Transfer Validity Templates – Val(A, T, t)
Statements l l l Authenticity of binding - Aut(A, X, P, I) Trust – Trust(A, X, D, I) Certificates – Cert(X, Y, P, I) Trust Transfers – Tran(X, Y, P, I) Certification Validity Templates – Val(A, C, t) Transfer Validity Templates – Val(A, T, t)
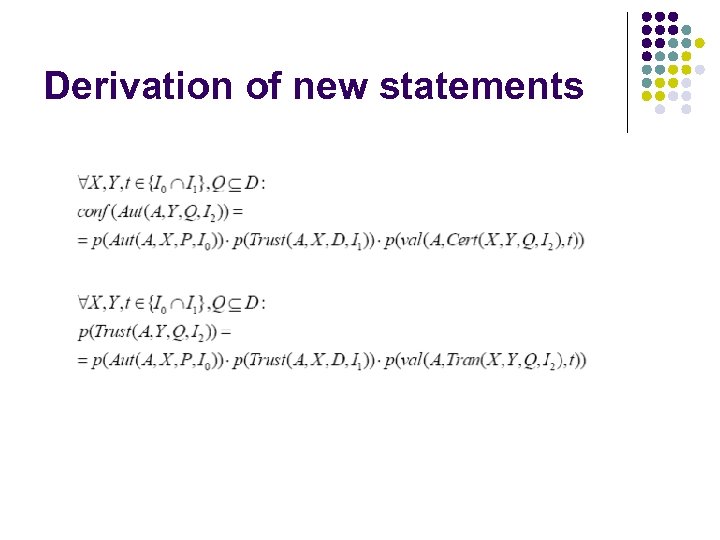 Derivation of new statements
Derivation of new statements
 X. 509 and model l Set of property – subject’s name, issuer, signature algorithm Time interval – validity – not before, not after Certification revocation list – Cert(X, 0, L, I), where 0 – empty set
X. 509 and model l Set of property – subject’s name, issuer, signature algorithm Time interval – validity – not before, not after Certification revocation list – Cert(X, 0, L, I), where 0 – empty set
 Thanks for your attention
Thanks for your attention


