7bd1a5fb147bdfb7b33a58263379b226.ppt
- Количество слайдов: 39
 Toward Automated Authorization Policy Enforcement Vinod Ganapathy Trent Jaeger Somesh Jha vg@cs. wisc. edu tjaeger@cse. psu. edu jha@cs. wisc. edu March 1 st, 2006 Second Annual Security-enhanced Linux Symposium Baltimore, Maryland SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement
Toward Automated Authorization Policy Enforcement Vinod Ganapathy Trent Jaeger Somesh Jha vg@cs. wisc. edu tjaeger@cse. psu. edu jha@cs. wisc. edu March 1 st, 2006 Second Annual Security-enhanced Linux Symposium Baltimore, Maryland SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement
 Introduction • SELinux helps meet information-flow goals Request User App Yes/No Allowed? Yes/No • Expressive access-control policy language • Security-enhanced operating system SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 2
Introduction • SELinux helps meet information-flow goals Request User App Yes/No Allowed? Yes/No • Expressive access-control policy language • Security-enhanced operating system SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 2
 Security-aware Applications • Need for security-aware applications Request User App Yes/No Allowed? Yes/No • Can we build applications that can enforce mandatory access control policies? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 3
Security-aware Applications • Need for security-aware applications Request User App Yes/No Allowed? Yes/No • Can we build applications that can enforce mandatory access control policies? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 3
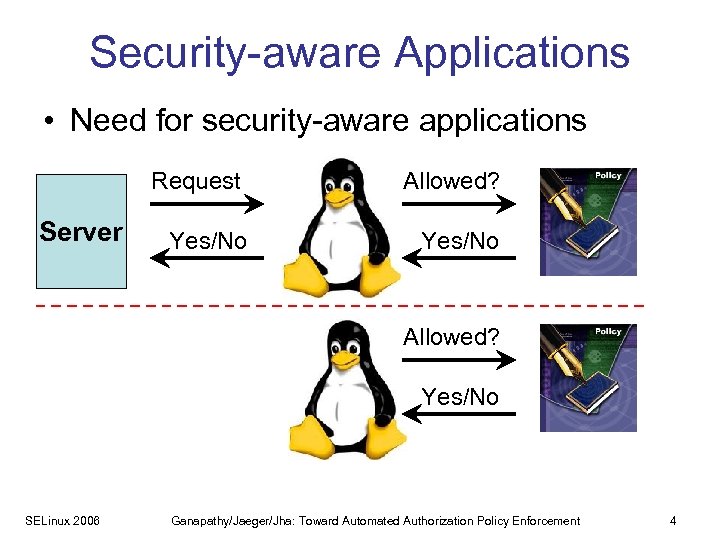 Security-aware Applications • Need for security-aware applications Request Server Client Yes/No Allowed? Yes/No SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 4
Security-aware Applications • Need for security-aware applications Request Server Client Yes/No Allowed? Yes/No SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 4
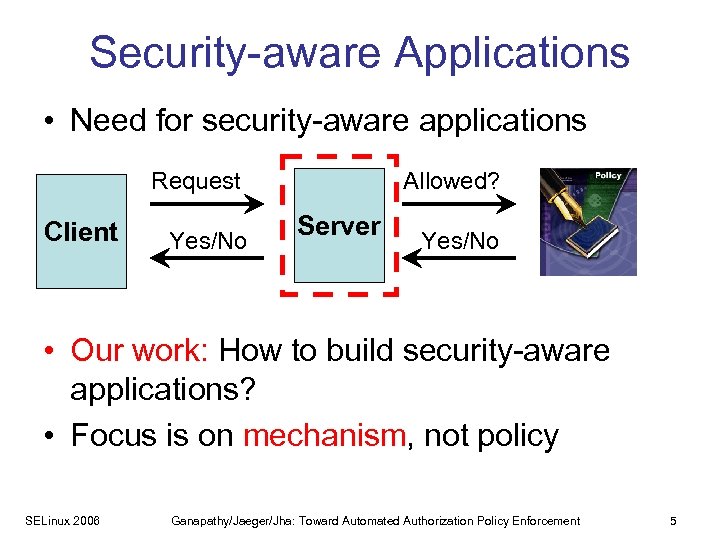 Security-aware Applications • Need for security-aware applications Request Client Yes/No Allowed? Server Yes/No • Our work: How to build security-aware applications? • Focus is on mechanism, not policy SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 5
Security-aware Applications • Need for security-aware applications Request Client Yes/No Allowed? Server Yes/No • Our work: How to build security-aware applications? • Focus is on mechanism, not policy SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 5
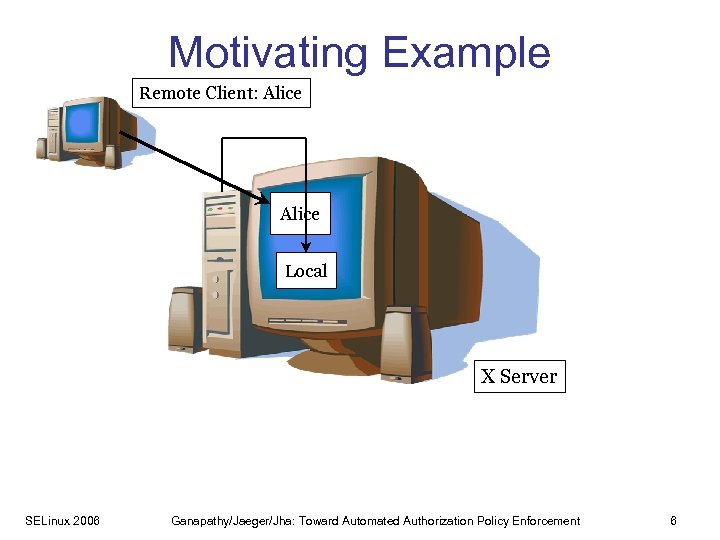 Motivating Example Remote Client: Alice Local X Server SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 6
Motivating Example Remote Client: Alice Local X Server SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 6
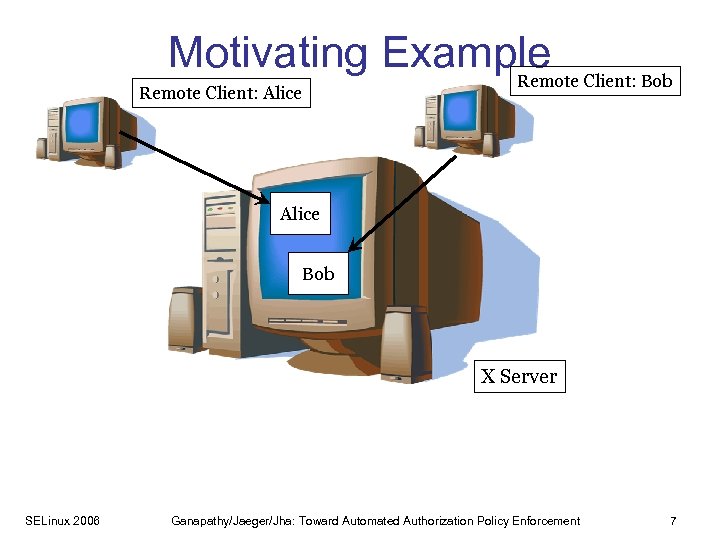 Motivating Example Client: Bob Remote Client: Alice Bob X Server SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 7
Motivating Example Client: Bob Remote Client: Alice Bob X Server SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 7
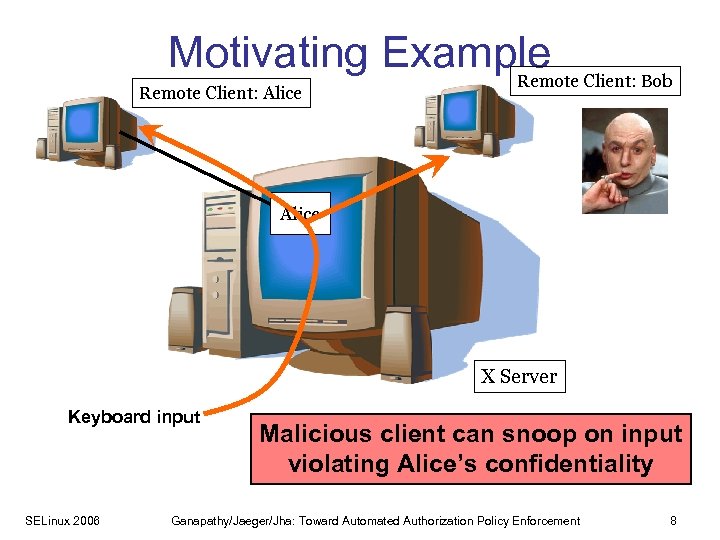 Motivating Example Client: Bob Remote Client: Alice X Server Keyboard input SELinux 2006 Malicious client can snoop on input violating Alice’s confidentiality Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 8
Motivating Example Client: Bob Remote Client: Alice X Server Keyboard input SELinux 2006 Malicious client can snoop on input violating Alice’s confidentiality Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 8
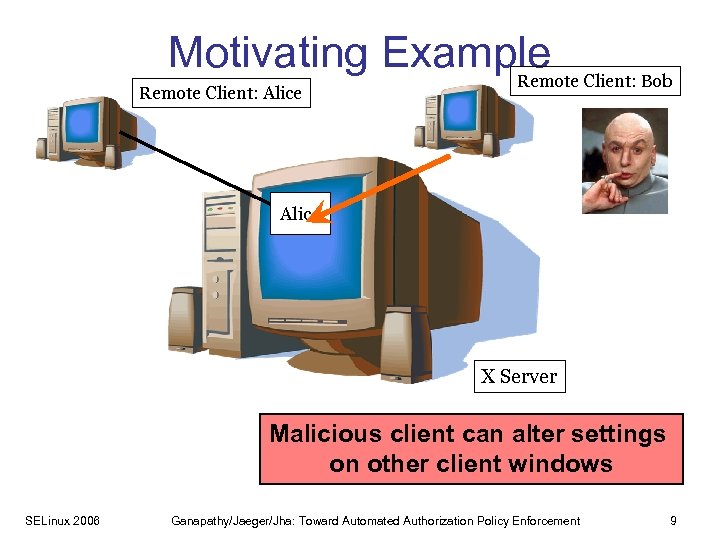 Motivating Example Client: Bob Remote Client: Alice X Server Malicious client can alter settings on other client windows SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 9
Motivating Example Client: Bob Remote Client: Alice X Server Malicious client can alter settings on other client windows SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 9
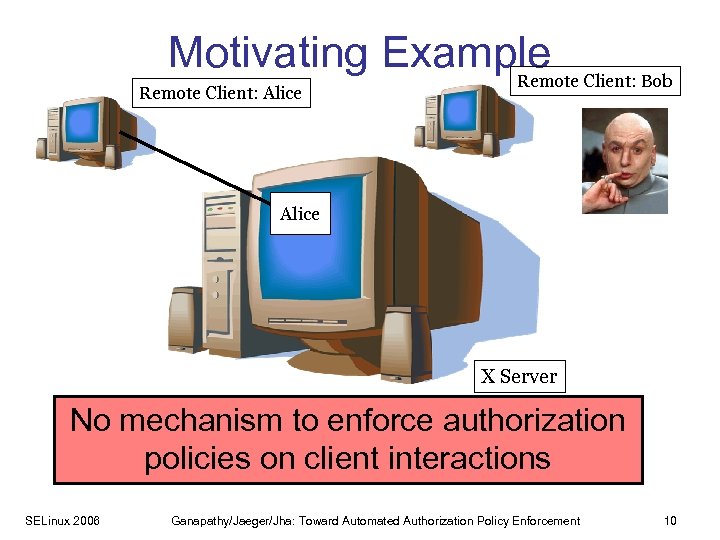 Motivating Example Client: Bob Remote Client: Alice X Server No mechanism to enforce authorization policies on client interactions SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 10
Motivating Example Client: Bob Remote Client: Alice X Server No mechanism to enforce authorization policies on client interactions SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 10
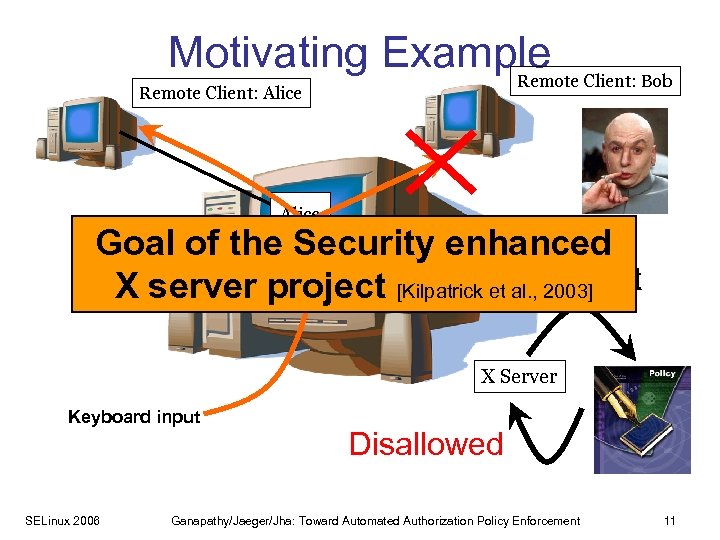 Motivating Example Client: Bob Remote Client: Alice Input Goal of the Security enhanced Request X server project [Kilpatrick et al. , 2003] X Server Keyboard input SELinux 2006 Disallowed Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 11
Motivating Example Client: Bob Remote Client: Alice Input Goal of the Security enhanced Request X server project [Kilpatrick et al. , 2003] X Server Keyboard input SELinux 2006 Disallowed Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 11
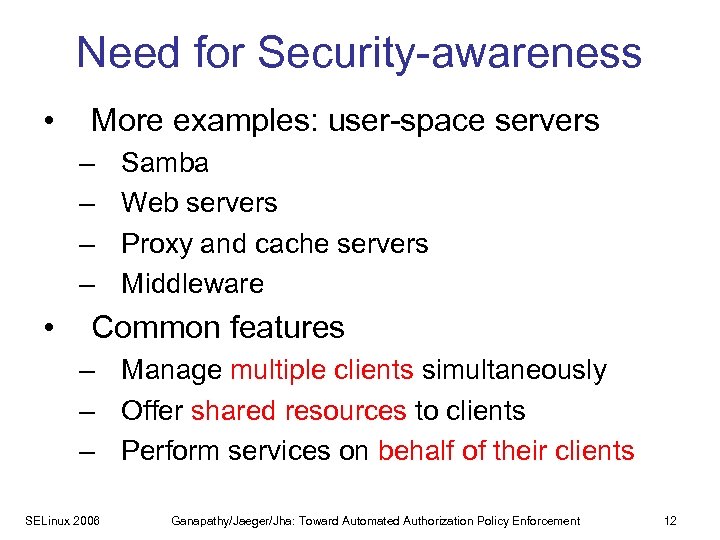 Need for Security-awareness • More examples: user-space servers – – • Samba Web servers Proxy and cache servers Middleware Common features – Manage multiple clients simultaneously – Offer shared resources to clients – Perform services on behalf of their clients SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 12
Need for Security-awareness • More examples: user-space servers – – • Samba Web servers Proxy and cache servers Middleware Common features – Manage multiple clients simultaneously – Offer shared resources to clients – Perform services on behalf of their clients SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 12
 Main Claim To effectively meet security-goals, all applications managing shared resources must be made security-aware SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 13
Main Claim To effectively meet security-goals, all applications managing shared resources must be made security-aware SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 13
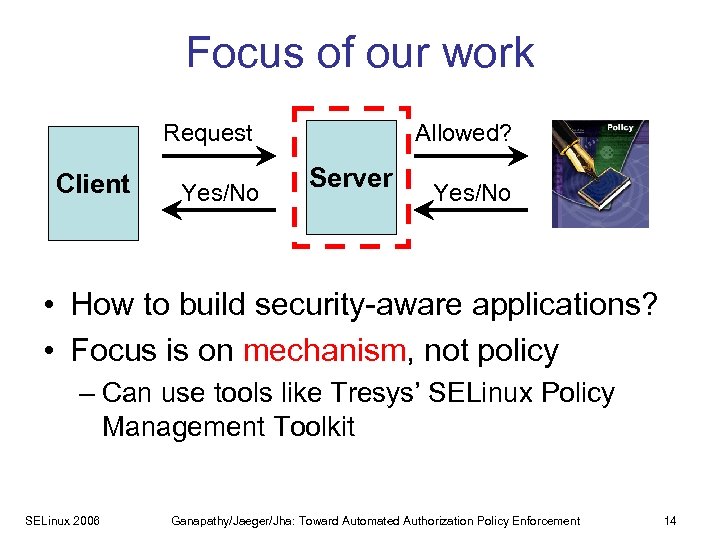 Focus of our work Request Client Yes/No Allowed? Server Yes/No • How to build security-aware applications? • Focus is on mechanism, not policy – Can use tools like Tresys’ SELinux Policy Management Toolkit SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 14
Focus of our work Request Client Yes/No Allowed? Server Yes/No • How to build security-aware applications? • Focus is on mechanism, not policy – Can use tools like Tresys’ SELinux Policy Management Toolkit SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 14
 Security-aware Applications Our work: • How to build security-aware applications? Tool support to retrofit legacy servers • Proactively design code for security for MULTICS project [Corbato et al. , 1965] – authorization policy enforcement – Postfix mail server [Venema] • Retrofit existing, legacy code – Linux Security Modules project [Wright et al. , 2002] – Security-enhanced X project [Kilpatrick et al. , 2003] – Privilege separated Open. SSH [Provos et al. , 2003] SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 15
Security-aware Applications Our work: • How to build security-aware applications? Tool support to retrofit legacy servers • Proactively design code for security for MULTICS project [Corbato et al. , 1965] – authorization policy enforcement – Postfix mail server [Venema] • Retrofit existing, legacy code – Linux Security Modules project [Wright et al. , 2002] – Security-enhanced X project [Kilpatrick et al. , 2003] – Privilege separated Open. SSH [Provos et al. , 2003] SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 15
 Our Work Legacy server Security-aware server • Tools to analyze and retrofit legacy code • Two case studies: – Retrofitting the X server – Retrofitting Linux SELinux 2006 [IEEE S&P 2006] [ACM CCS 2005] Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 16
Our Work Legacy server Security-aware server • Tools to analyze and retrofit legacy code • Two case studies: – Retrofitting the X server – Retrofitting Linux SELinux 2006 [IEEE S&P 2006] [ACM CCS 2005] Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 16
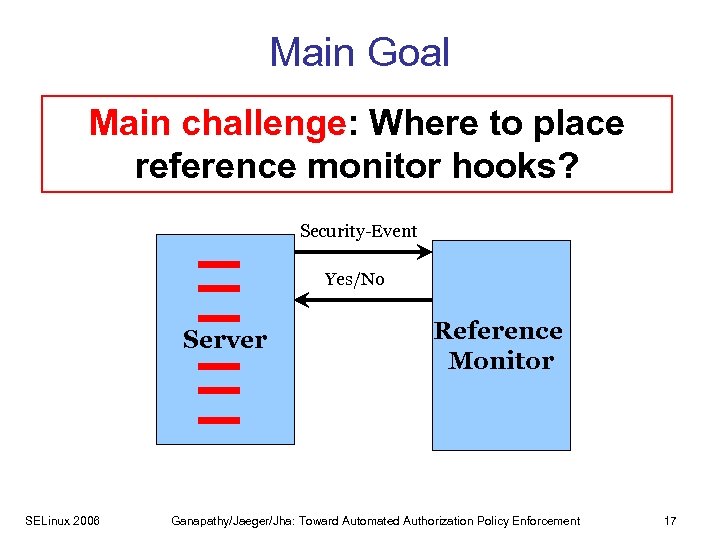 Main Goal • Tool support to add referenceto place Main challenge: Where monitoring to user-space servers reference monitor hooks? Security-Event Yes/No Server SELinux 2006 Reference Monitor Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 17
Main Goal • Tool support to add referenceto place Main challenge: Where monitoring to user-space servers reference monitor hooks? Security-Event Yes/No Server SELinux 2006 Reference Monitor Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 17
![Authorization Policies • Access-control matrix [Lampson’ 71] /etc/passwd root vg r/w /usr/vg/a. out /var/log Authorization Policies • Access-control matrix [Lampson’ 71] /etc/passwd root vg r/w /usr/vg/a. out /var/log](https://present5.com/presentation/7bd1a5fb147bdfb7b33a58263379b226/image-18.jpg) Authorization Policies • Access-control matrix [Lampson’ 71] /etc/passwd root vg r/w /usr/vg/a. out /var/log r/w/x r/w r • Three entities: ‹subject, operation› – Subject (user or process) – Object (resource, such as file or socket) – Security-sensitive operation (access vectors) SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 18
Authorization Policies • Access-control matrix [Lampson’ 71] /etc/passwd root vg r/w /usr/vg/a. out /var/log r/w/x r/w r • Three entities: ‹subject, operation› – Subject (user or process) – Object (resource, such as file or socket) – Security-sensitive operation (access vectors) SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 18
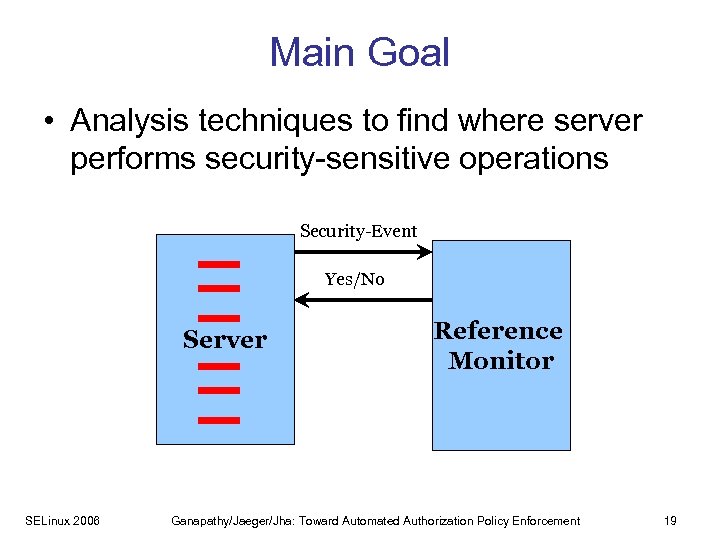 Main Goal • Analysis techniques to find where server performs security-sensitive operations Security-Event Yes/No Server SELinux 2006 Reference Monitor Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 19
Main Goal • Analysis techniques to find where server performs security-sensitive operations Security-Event Yes/No Server SELinux 2006 Reference Monitor Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 19
 Key Insight: Fingerprints • Each security-sensitive operation has a fingerprint • Intuition: Denotes key code-level steps to achieve the operation SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 20
Key Insight: Fingerprints • Each security-sensitive operation has a fingerprint • Intuition: Denotes key code-level steps to achieve the operation SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 20
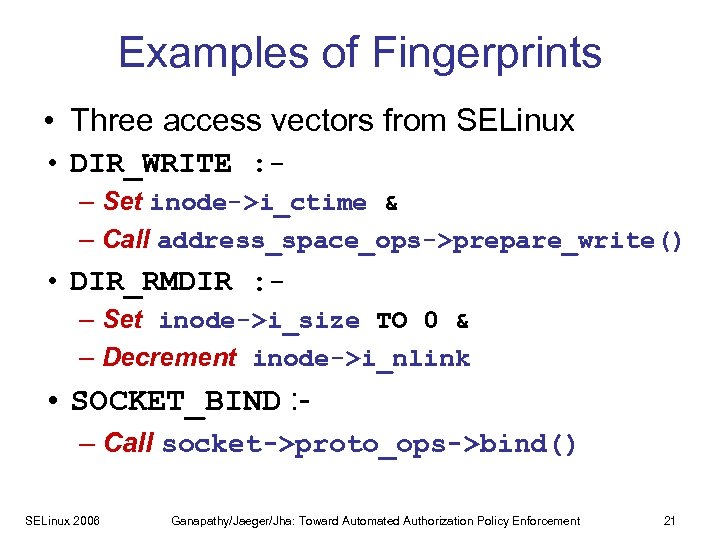 Examples of Fingerprints • Three access vectors from SELinux • DIR_WRITE : – Set inode->i_ctime & – Call address_space_ops->prepare_write() • DIR_RMDIR : – Set inode->i_size TO 0 & – Decrement inode->i_nlink • SOCKET_BIND : – Call socket->proto_ops->bind() SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 21
Examples of Fingerprints • Three access vectors from SELinux • DIR_WRITE : – Set inode->i_ctime & – Call address_space_ops->prepare_write() • DIR_RMDIR : – Set inode->i_size TO 0 & – Decrement inode->i_nlink • SOCKET_BIND : – Call socket->proto_ops->bind() SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 21
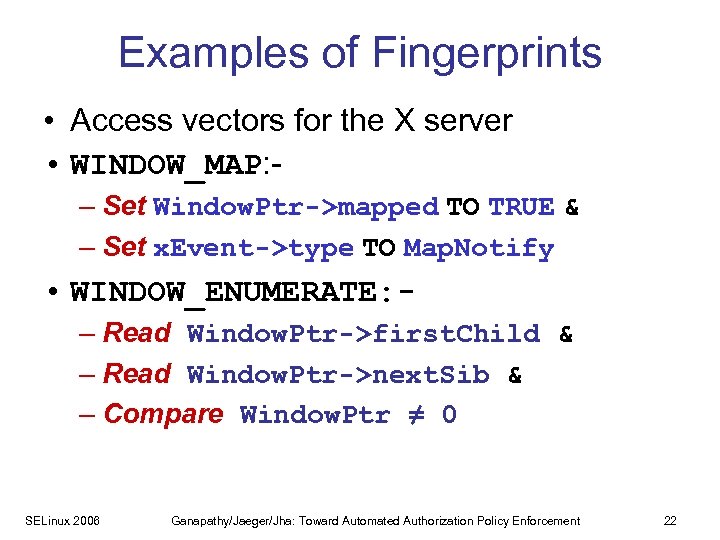 Examples of Fingerprints • Access vectors for the X server • WINDOW_MAP: – Set Window. Ptr->mapped TO TRUE & – Set x. Event->type TO Map. Notify • WINDOW_ENUMERATE: – Read Window. Ptr->first. Child & – Read Window. Ptr->next. Sib & – Compare Window. Ptr ≠ 0 SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 22
Examples of Fingerprints • Access vectors for the X server • WINDOW_MAP: – Set Window. Ptr->mapped TO TRUE & – Set x. Event->type TO Map. Notify • WINDOW_ENUMERATE: – Read Window. Ptr->first. Child & – Read Window. Ptr->next. Sib & – Compare Window. Ptr ≠ 0 SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 22
 Key Insight: Fingerprints • How to find fingerprints? • How to use fingerprints to place hooks? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 23
Key Insight: Fingerprints • How to find fingerprints? • How to use fingerprints to place hooks? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 23
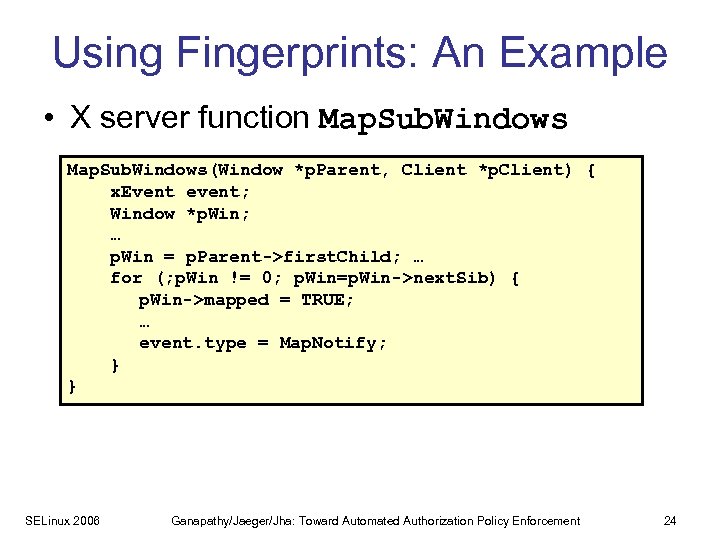 Using Fingerprints: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { x. Event event; Window *p. Win; … p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { p. Win->mapped = TRUE; … event. type = Map. Notify; } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 24
Using Fingerprints: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { x. Event event; Window *p. Win; … p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { p. Win->mapped = TRUE; … event. type = Map. Notify; } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 24
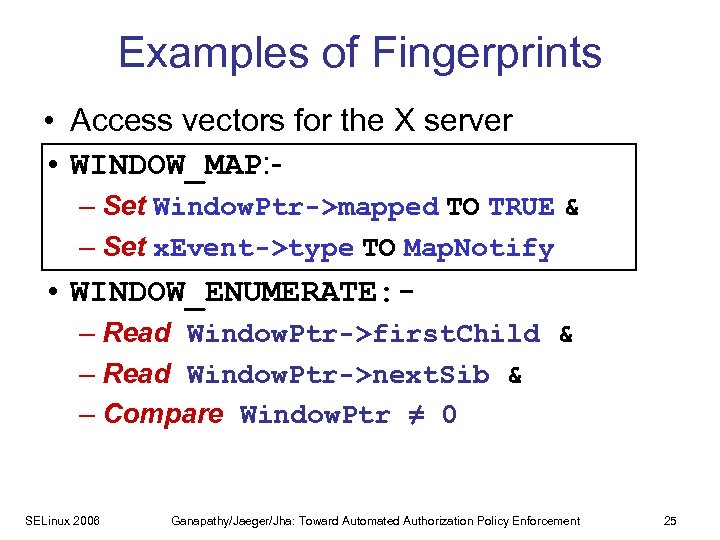 Examples of Fingerprints • Access vectors for the X server • WINDOW_MAP: – Set Window. Ptr->mapped TO TRUE & – Set x. Event->type TO Map. Notify • WINDOW_ENUMERATE: – Read Window. Ptr->first. Child & – Read Window. Ptr->next. Sib & – Compare Window. Ptr ≠ 0 SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 25
Examples of Fingerprints • Access vectors for the X server • WINDOW_MAP: – Set Window. Ptr->mapped TO TRUE & – Set x. Event->type TO Map. Notify • WINDOW_ENUMERATE: – Read Window. Ptr->first. Child & – Read Window. Ptr->next. Sib & – Compare Window. Ptr ≠ 0 SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 25
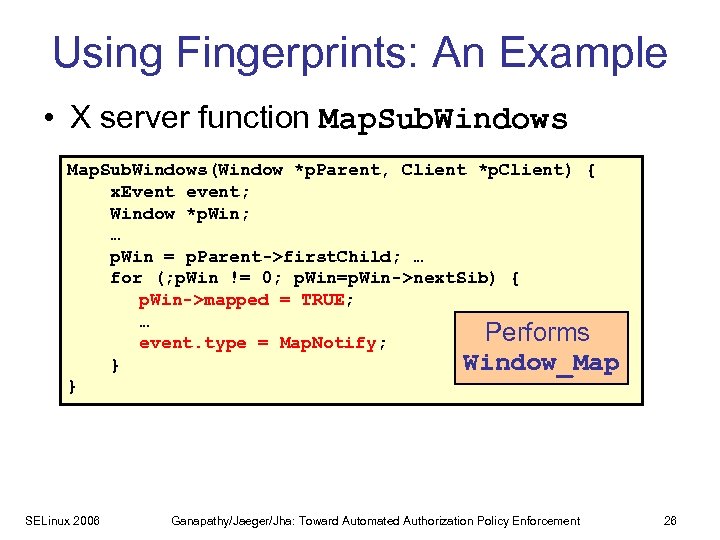 Using Fingerprints: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { x. Event event; Window *p. Win; … p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { p. Win->mapped = TRUE; … Performs event. type = Map. Notify; Window_Map } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 26
Using Fingerprints: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { x. Event event; Window *p. Win; … p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { p. Win->mapped = TRUE; … Performs event. type = Map. Notify; Window_Map } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 26
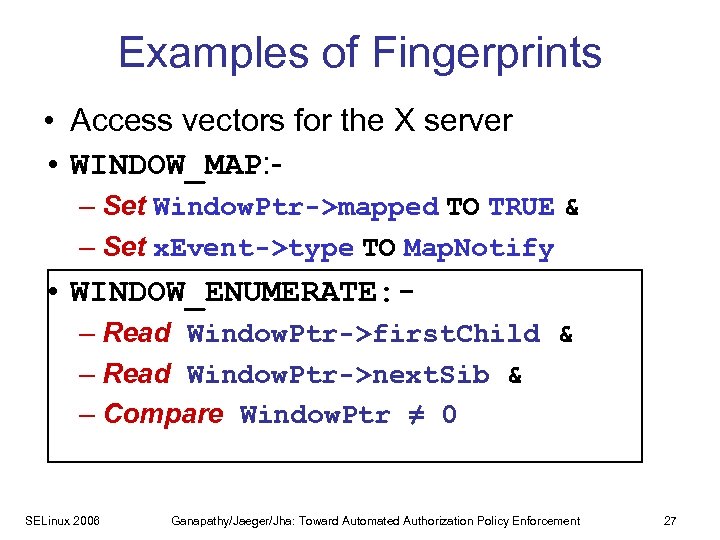 Examples of Fingerprints • Access vectors for the X server • WINDOW_MAP: – Set Window. Ptr->mapped TO TRUE & – Set x. Event->type TO Map. Notify • WINDOW_ENUMERATE: – Read Window. Ptr->first. Child & – Read Window. Ptr->next. Sib & – Compare Window. Ptr ≠ 0 SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 27
Examples of Fingerprints • Access vectors for the X server • WINDOW_MAP: – Set Window. Ptr->mapped TO TRUE & – Set x. Event->type TO Map. Notify • WINDOW_ENUMERATE: – Read Window. Ptr->first. Child & – Read Window. Ptr->next. Sib & – Compare Window. Ptr ≠ 0 SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 27
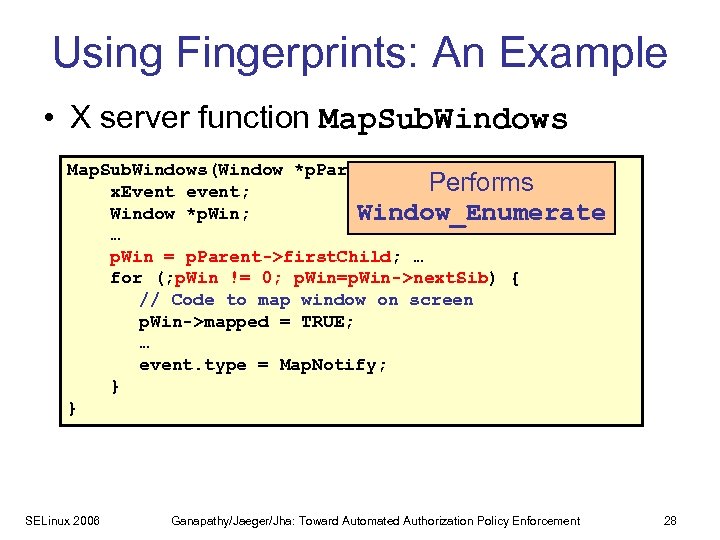 Using Fingerprints: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { Performs x. Event event; Window *p. Win; Window_Enumerate … p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { // Code to map window on screen p. Win->mapped = TRUE; … event. type = Map. Notify; } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 28
Using Fingerprints: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { Performs x. Event event; Window *p. Win; Window_Enumerate … p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { // Code to map window on screen p. Win->mapped = TRUE; … event. type = Map. Notify; } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 28
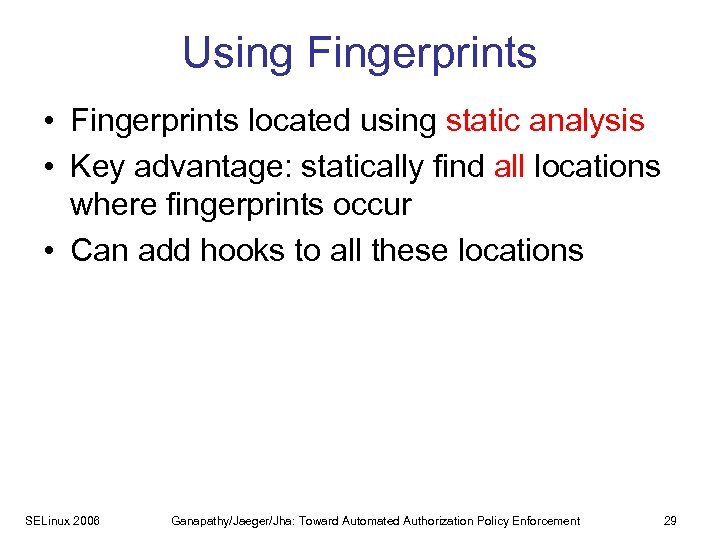 Using Fingerprints • Fingerprints located using static analysis • Key advantage: statically find all locations where fingerprints occur • Can add hooks to all these locations SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 29
Using Fingerprints • Fingerprints located using static analysis • Key advantage: statically find all locations where fingerprints occur • Can add hooks to all these locations SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 29
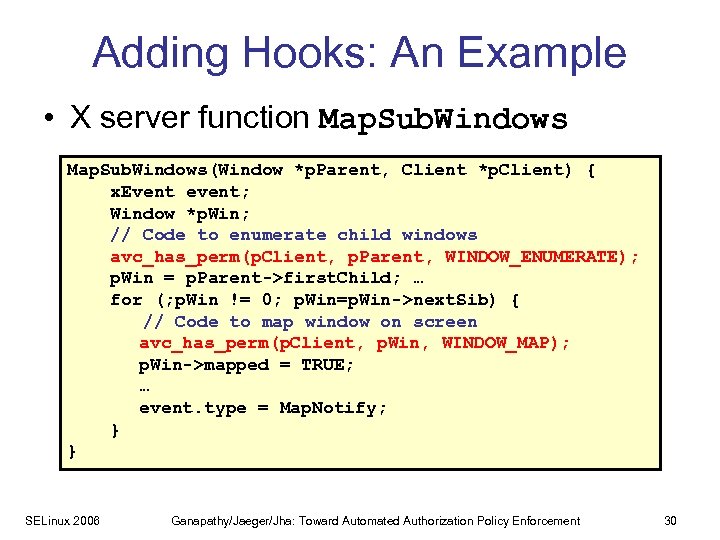 Adding Hooks: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { x. Event event; Window *p. Win; // Code to enumerate child windows avc_has_perm(p. Client, p. Parent, WINDOW_ENUMERATE); p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { // Code to map window on screen avc_has_perm(p. Client, p. Win, WINDOW_MAP); p. Win->mapped = TRUE; … event. type = Map. Notify; } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 30
Adding Hooks: An Example • X server function Map. Sub. Windows(Window *p. Parent, Client *p. Client) { x. Event event; Window *p. Win; // Code to enumerate child windows avc_has_perm(p. Client, p. Parent, WINDOW_ENUMERATE); p. Win = p. Parent->first. Child; … for (; p. Win != 0; p. Win=p. Win->next. Sib) { // Code to map window on screen avc_has_perm(p. Client, p. Win, WINDOW_MAP); p. Win->mapped = TRUE; … event. type = Map. Notify; } } SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 30
 Key Insight: Fingerprints • How to find fingerprints? • How to use fingerprints to place hooks? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 31
Key Insight: Fingerprints • How to find fingerprints? • How to use fingerprints to place hooks? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 31
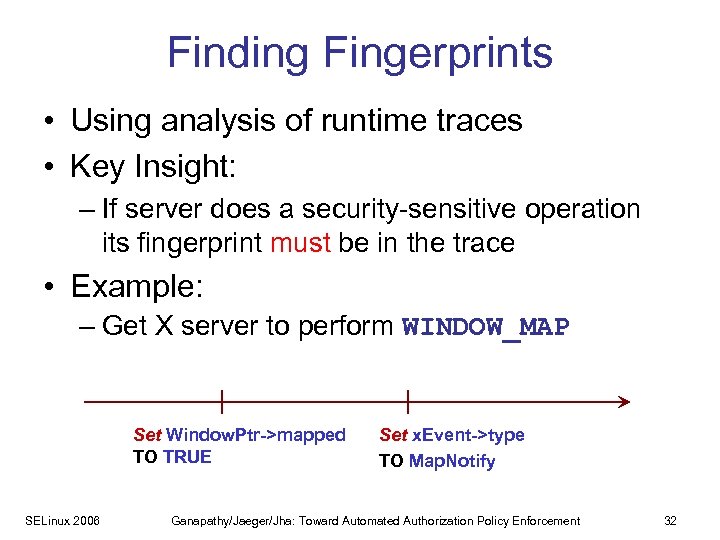 Finding Fingerprints • Using analysis of runtime traces • Key Insight: – If server does a security-sensitive operation its fingerprint must be in the trace • Example: – Get X server to perform WINDOW_MAP Set Window. Ptr->mapped TO TRUE SELinux 2006 Set x. Event->type TO Map. Notify Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 32
Finding Fingerprints • Using analysis of runtime traces • Key Insight: – If server does a security-sensitive operation its fingerprint must be in the trace • Example: – Get X server to perform WINDOW_MAP Set Window. Ptr->mapped TO TRUE SELinux 2006 Set x. Event->type TO Map. Notify Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 32
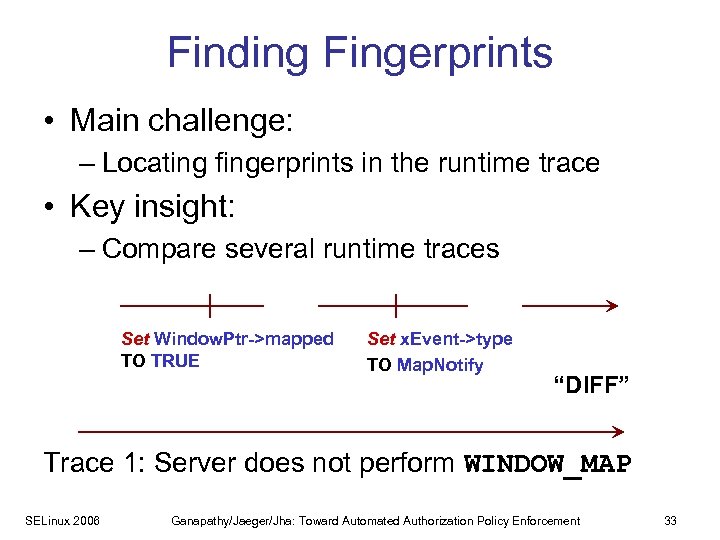 Finding Fingerprints • Main challenge: – Locating fingerprints in the runtime trace • Key insight: – Compare several runtime traces Set Window. Ptr->mapped TO TRUE Set x. Event->type TO Map. Notify “DIFF” Trace 1: Server does not perform WINDOW_MAP SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 33
Finding Fingerprints • Main challenge: – Locating fingerprints in the runtime trace • Key insight: – Compare several runtime traces Set Window. Ptr->mapped TO TRUE Set x. Event->type TO Map. Notify “DIFF” Trace 1: Server does not perform WINDOW_MAP SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 33
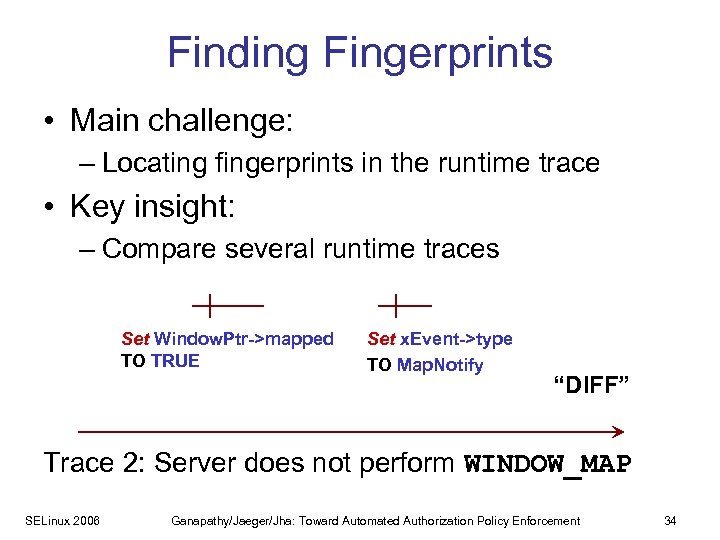 Finding Fingerprints • Main challenge: – Locating fingerprints in the runtime trace • Key insight: – Compare several runtime traces Set Window. Ptr->mapped TO TRUE Set x. Event->type TO Map. Notify “DIFF” Trace 2: Server does not perform WINDOW_MAP SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 34
Finding Fingerprints • Main challenge: – Locating fingerprints in the runtime trace • Key insight: – Compare several runtime traces Set Window. Ptr->mapped TO TRUE Set x. Event->type TO Map. Notify “DIFF” Trace 2: Server does not perform WINDOW_MAP SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 34
 Key Insight: Fingerprints • How to find fingerprints? • How to use fingerprints to place hooks? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 35
Key Insight: Fingerprints • How to find fingerprints? • How to use fingerprints to place hooks? SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 35
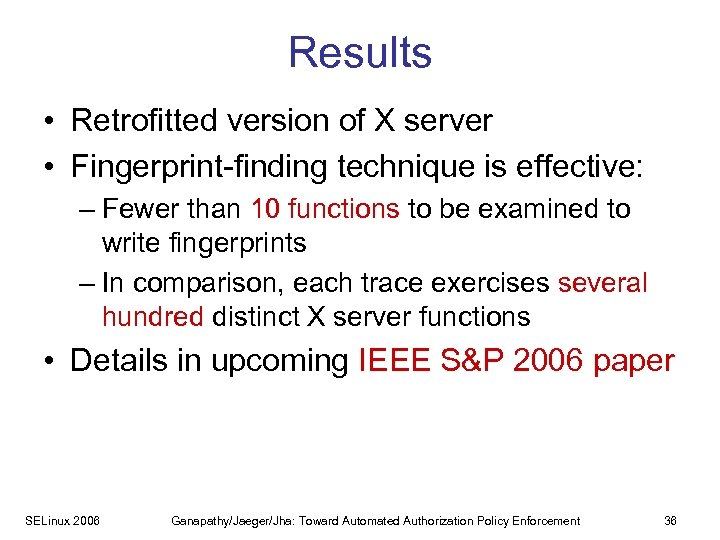 Results • Retrofitted version of X server • Fingerprint-finding technique is effective: – Fewer than 10 functions to be examined to write fingerprints – In comparison, each trace exercises several hundred distinct X server functions • Details in upcoming IEEE S&P 2006 paper SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 36
Results • Retrofitted version of X server • Fingerprint-finding technique is effective: – Fewer than 10 functions to be examined to write fingerprints – In comparison, each trace exercises several hundred distinct X server functions • Details in upcoming IEEE S&P 2006 paper SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 36
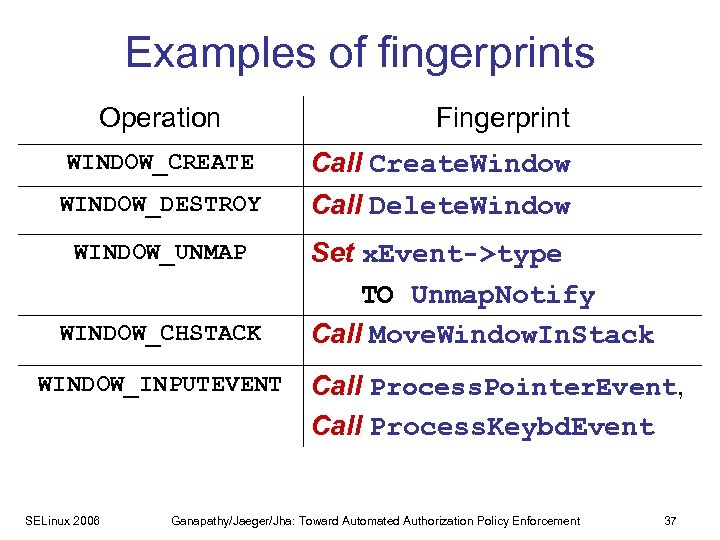 Examples of fingerprints Operation WINDOW_CREATE WINDOW_DESTROY WINDOW_UNMAP WINDOW_CHSTACK WINDOW_INPUTEVENT SELinux 2006 Fingerprint Call Create. Window Call Delete. Window Set x. Event->type TO Unmap. Notify Call Move. Window. In. Stack Call Process. Pointer. Event, Call Process. Keybd. Event Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 37
Examples of fingerprints Operation WINDOW_CREATE WINDOW_DESTROY WINDOW_UNMAP WINDOW_CHSTACK WINDOW_INPUTEVENT SELinux 2006 Fingerprint Call Create. Window Call Delete. Window Set x. Event->type TO Unmap. Notify Call Move. Window. In. Stack Call Process. Pointer. Event, Call Process. Keybd. Event Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 37
 Slide to take home • Goal: Placing authorization hooks in servers • Key insight: Security-sensitive operations have fingerprints • Finding fingerprints: Using “diff” of runtime traces • Placing hooks: By statically locating fingerprints SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 38
Slide to take home • Goal: Placing authorization hooks in servers • Key insight: Security-sensitive operations have fingerprints • Finding fingerprints: Using “diff” of runtime traces • Placing hooks: By statically locating fingerprints SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement 38
 Questions? Toward Automated Authorization Policy Enforcement Vinod Ganapathy Trent Jaeger Somesh Jha vg@cs. wisc. edu tjaeger@cse. psu. edu jha@cs. wisc. edu http: //www. cs. wisc. edu/~vg http: //www. cse. psu. edu/~tjaeger http: //www. cs. wisc. edu/~jha SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement
Questions? Toward Automated Authorization Policy Enforcement Vinod Ganapathy Trent Jaeger Somesh Jha vg@cs. wisc. edu tjaeger@cse. psu. edu jha@cs. wisc. edu http: //www. cs. wisc. edu/~vg http: //www. cse. psu. edu/~tjaeger http: //www. cs. wisc. edu/~jha SELinux 2006 Ganapathy/Jaeger/Jha: Toward Automated Authorization Policy Enforcement


