 Threat Monitoring Center (TMC) TMC Overview
Threat Monitoring Center (TMC) TMC Overview
 Presentation Outline • HBGary Overview o Products o Services • Threat Monitoring Center Overview
Presentation Outline • HBGary Overview o Products o Services • Threat Monitoring Center Overview
 HBGary • Company established in 2003, founded by Greg Hoglund • Recently formed HBGary Federal • Provide classified software and services, leveraging HBGary malware analysis product-line • HQs in Sacremento, CA offices in DC, establishing SCIF in Colorado • Aaron Barr o CEO • Ted Vera o President | COO
HBGary • Company established in 2003, founded by Greg Hoglund • Recently formed HBGary Federal • Provide classified software and services, leveraging HBGary malware analysis product-line • HQs in Sacremento, CA offices in DC, establishing SCIF in Colorado • Aaron Barr o CEO • Ted Vera o President | COO
 Evolving Risk Environment • • Valuable cyber targets Attackers are motivated and well-funded Malware is sophisticated and targeted Existing security isn’t stopping the attacks
Evolving Risk Environment • • Valuable cyber targets Attackers are motivated and well-funded Malware is sophisticated and targeted Existing security isn’t stopping the attacks
 Cybersecurity Challenges • Most CERT/SOCs do not have the tools or capabilities to enable them to move past analysis of infections to analysis of threats. • A set of capabilities need to be developed and integrated in the following areas to enable better situational awareness and incident response. o o o Malware and Threat analysis Workflow and knowledge management Communications and Collaboration Resource Characterization and Visualization Mission Impact and COAs
Cybersecurity Challenges • Most CERT/SOCs do not have the tools or capabilities to enable them to move past analysis of infections to analysis of threats. • A set of capabilities need to be developed and integrated in the following areas to enable better situational awareness and incident response. o o o Malware and Threat analysis Workflow and knowledge management Communications and Collaboration Resource Characterization and Visualization Mission Impact and COAs
 Traditional Malware Analysis is Difficult • • Requires lots of technical expertise Time consuming Expensive Doesn’t scale
Traditional Malware Analysis is Difficult • • Requires lots of technical expertise Time consuming Expensive Doesn’t scale
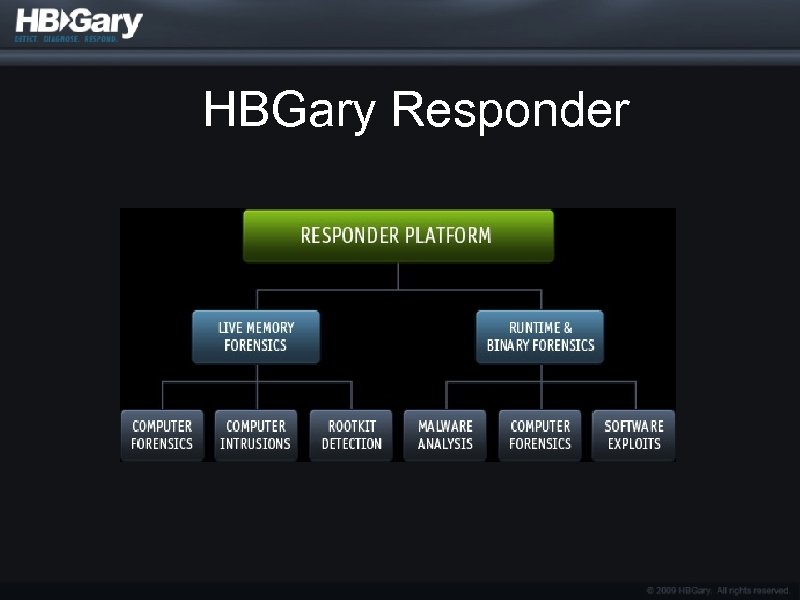 HBGary Responder
HBGary Responder
 Digital DNA • • Automated zero-day malware detection. Trait/Behavior based software classification system 3500 software and malware behavioral traits Example o Huge number of key logger variants in the wild o About 10 logical ways to build a key logger
Digital DNA • • Automated zero-day malware detection. Trait/Behavior based software classification system 3500 software and malware behavioral traits Example o Huge number of key logger variants in the wild o About 10 logical ways to build a key logger
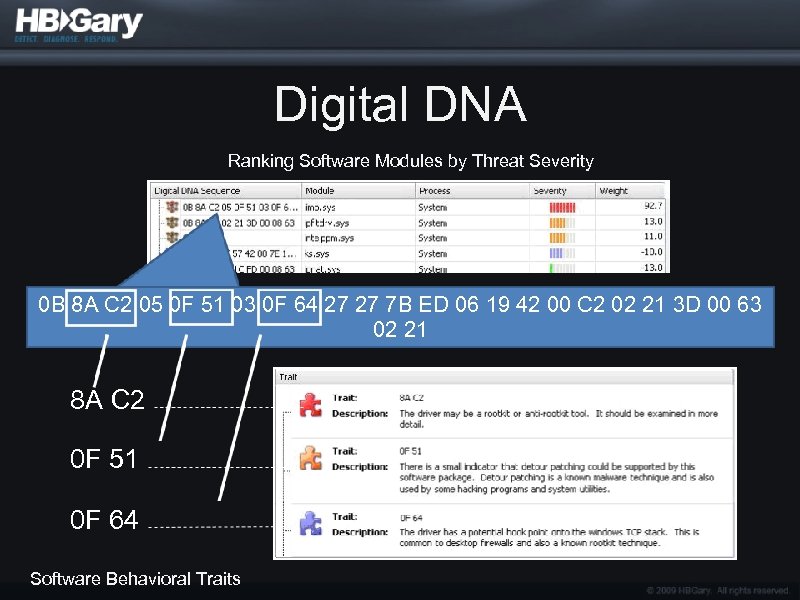 Digital DNA Ranking Software Modules by Threat Severity 0 B 8 A C 2 05 0 F 51 03 0 F 64 27 27 7 B ED 06 19 42 00 C 2 02 21 3 D 00 63 02 21 8 A C 2 0 F 51 0 F 64 Software Behavioral Traits
Digital DNA Ranking Software Modules by Threat Severity 0 B 8 A C 2 05 0 F 51 03 0 F 64 27 27 7 B ED 06 19 42 00 C 2 02 21 3 D 00 63 02 21 8 A C 2 0 F 51 0 F 64 Software Behavioral Traits
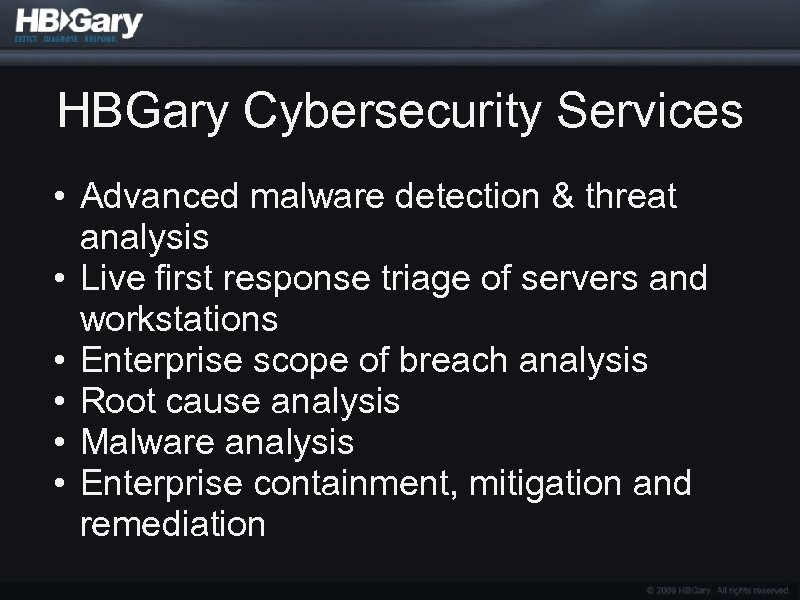 HBGary Cybersecurity Services • Advanced malware detection & threat analysis • Live first response triage of servers and workstations • Enterprise scope of breach analysis • Root cause analysis • Malware analysis • Enterprise containment, mitigation and remediation
HBGary Cybersecurity Services • Advanced malware detection & threat analysis • Live first response triage of servers and workstations • Enterprise scope of breach analysis • Root cause analysis • Malware analysis • Enterprise containment, mitigation and remediation
 HBGary Solutions • Blah
HBGary Solutions • Blah
 HBGary Chart
HBGary Chart
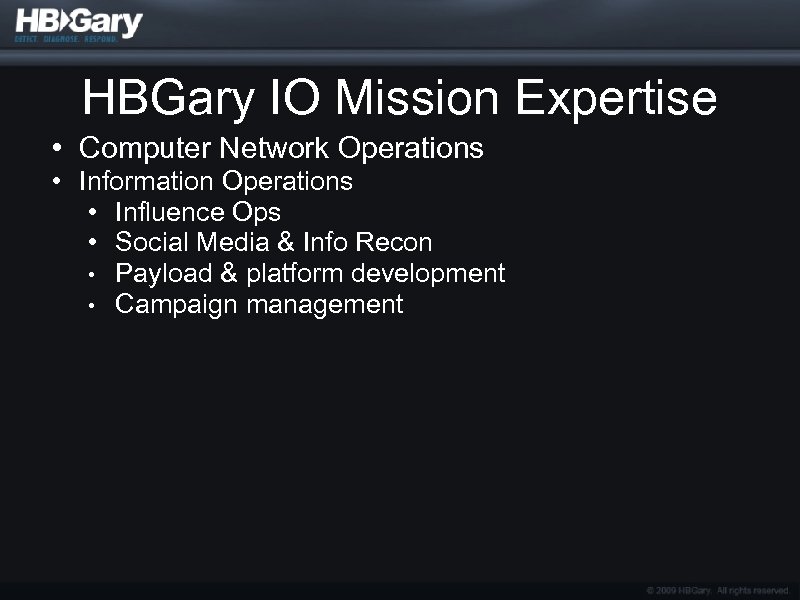 HBGary IO Mission Expertise • Computer Network Operations • Information Operations • Influence Ops • Social Media & Info Recon • Payload & platform development • Campaign management
HBGary IO Mission Expertise • Computer Network Operations • Information Operations • Influence Ops • Social Media & Info Recon • Payload & platform development • Campaign management
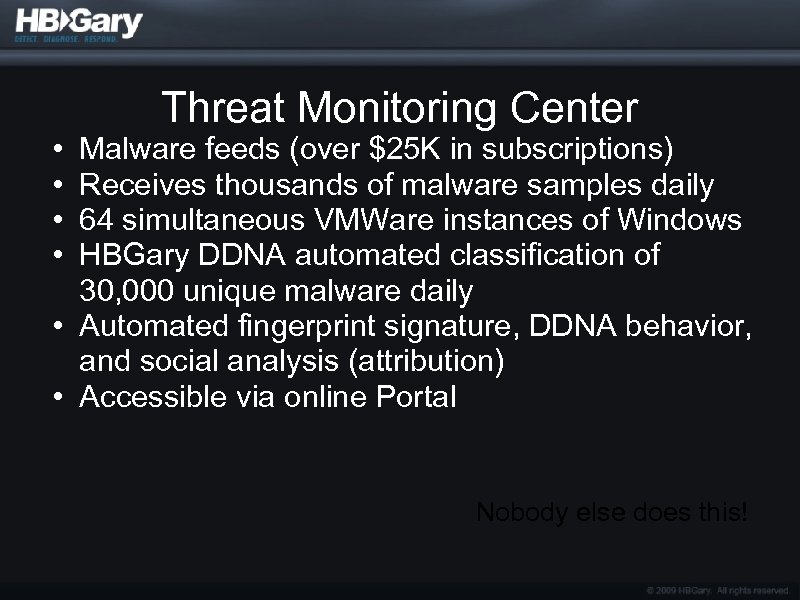 • • Threat Monitoring Center Malware feeds (over $25 K in subscriptions) Receives thousands of malware samples daily 64 simultaneous VMWare instances of Windows HBGary DDNA automated classification of 30, 000 unique malware daily • Automated fingerprint signature, DDNA behavior, and social analysis (attribution) • Accessible via online Portal Nobody else does this!
• • Threat Monitoring Center Malware feeds (over $25 K in subscriptions) Receives thousands of malware samples daily 64 simultaneous VMWare instances of Windows HBGary DDNA automated classification of 30, 000 unique malware daily • Automated fingerprint signature, DDNA behavior, and social analysis (attribution) • Accessible via online Portal Nobody else does this!
 Fingerprint. exe • Description / Snapshot Nobody else does this!
Fingerprint. exe • Description / Snapshot Nobody else does this!
 Palantir • Description / Snapshot Nobody else does this!
Palantir • Description / Snapshot Nobody else does this!
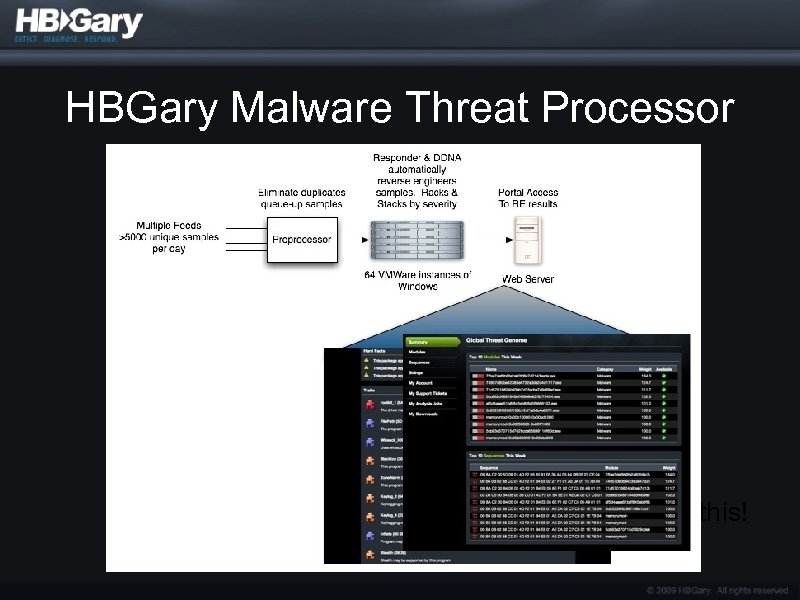 HBGary Malware Threat Processor Nobody else does this!
HBGary Malware Threat Processor Nobody else does this!
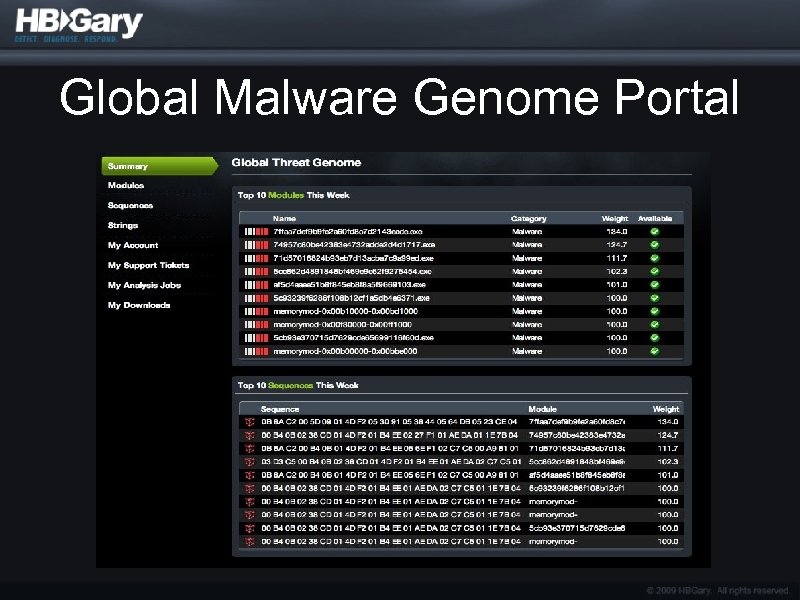 Global Malware Genome Portal
Global Malware Genome Portal
 Questions? Aaron Barr aaron@hbgary. com Ted Vera ted@hbgary. com
Questions? Aaron Barr aaron@hbgary. com Ted Vera ted@hbgary. com