bd62fbb87f87f06ce6da1e9c32a5df00.ppt
- Количество слайдов: 28
 Theft-protected Proprietary Certificates Jinhae Kim Graduate Student University of Minnesota
Theft-protected Proprietary Certificates Jinhae Kim Graduate Student University of Minnesota
 Contents n n n Introduction Building blocks Proprietary certificates Theft protection Alarm techniques and policies
Contents n n n Introduction Building blocks Proprietary certificates Theft protection Alarm techniques and policies
 Introduction n Proprietary certificate n n A way of implementing digital certificate that discourages unwanted sharing of resources Proprietary and collateral key Vulnerabilities of proprietary certificate Theft protection (real and CPU time delay)
Introduction n Proprietary certificate n n A way of implementing digital certificate that discourages unwanted sharing of resources Proprietary and collateral key Vulnerabilities of proprietary certificate Theft protection (real and CPU time delay)
 Example n n Subscribe web site (e. g. PCQuote. com, IEEE) Users pay per subscription (not pay per view) As we did before (all as we may want to do for expensive services), we can share password and payment How do we prevent this? (Do you want to? )
Example n n Subscribe web site (e. g. PCQuote. com, IEEE) Users pay per subscription (not pay per view) As we did before (all as we may want to do for expensive services), we can share password and payment How do we prevent this? (Do you want to? )
 Building Blocks (RSA/DL Keys) n RSA Setting n n Public key: (N, e) , secret key: (N, d) N: product of two k-bit primes (p , q) e ∈ ZN, coprime to φ(n), ed ≡ 1 mod φ(n) DL Setting n n Public key: (p, q, g, y) , secret key: (p, q, g, x) p: k-bit prime , q: prime such that q|p-1 g: a generator of the group of order q y = gx (x is element of Zq)
Building Blocks (RSA/DL Keys) n RSA Setting n n Public key: (N, e) , secret key: (N, d) N: product of two k-bit primes (p , q) e ∈ ZN, coprime to φ(n), ed ≡ 1 mod φ(n) DL Setting n n Public key: (p, q, g, y) , secret key: (p, q, g, x) p: k-bit prime , q: prime such that q|p-1 g: a generator of the group of order q y = gx (x is element of Zq)
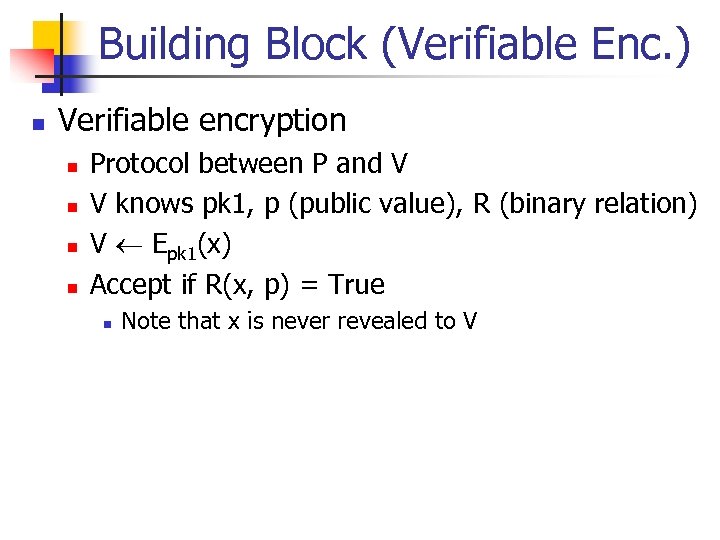 Building Block (Verifiable Enc. ) n Verifiable encryption n n Protocol between P and V V knows pk 1, p (public value), R (binary relation) V Epk 1(x) Accept if R(x, p) = True n Note that x is never revealed to V
Building Block (Verifiable Enc. ) n Verifiable encryption n n Protocol between P and V V knows pk 1, p (public value), R (binary relation) V Epk 1(x) Accept if R(x, p) = True n Note that x is never revealed to V
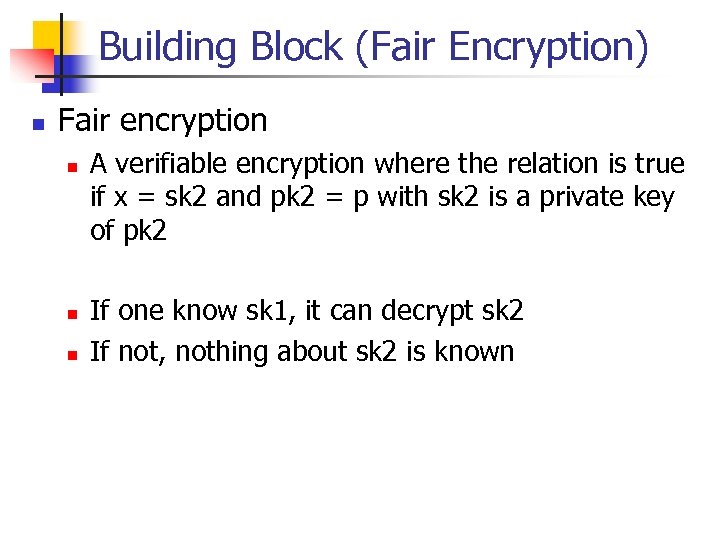 Building Block (Fair Encryption) n Fair encryption n A verifiable encryption where the relation is true if x = sk 2 and pk 2 = p with sk 2 is a private key of pk 2 If one know sk 1, it can decrypt sk 2 If not, nothing about sk 2 is known
Building Block (Fair Encryption) n Fair encryption n A verifiable encryption where the relation is true if x = sk 2 and pk 2 = p with sk 2 is a private key of pk 2 If one know sk 1, it can decrypt sk 2 If not, nothing about sk 2 is known
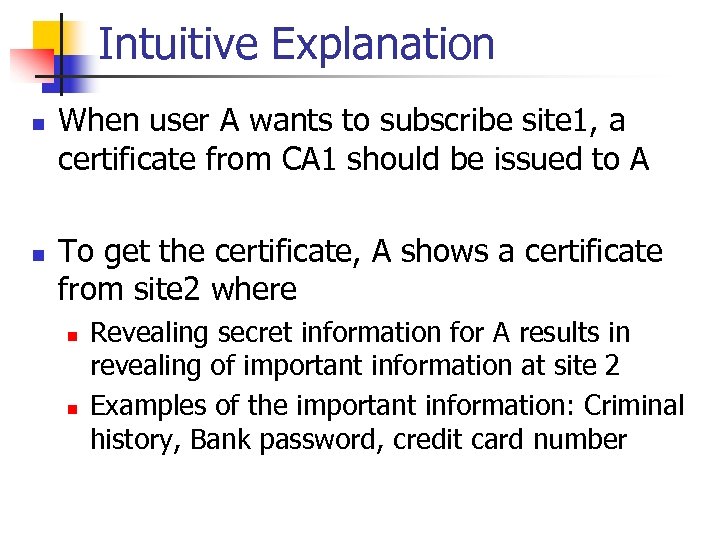 Intuitive Explanation n n When user A wants to subscribe site 1, a certificate from CA 1 should be issued to A To get the certificate, A shows a certificate from site 2 where n n Revealing secret information for A results in revealing of important information at site 2 Examples of the important information: Criminal history, Bank password, credit card number
Intuitive Explanation n n When user A wants to subscribe site 1, a certificate from CA 1 should be issued to A To get the certificate, A shows a certificate from site 2 where n n Revealing secret information for A results in revealing of important information at site 2 Examples of the important information: Criminal history, Bank password, credit card number
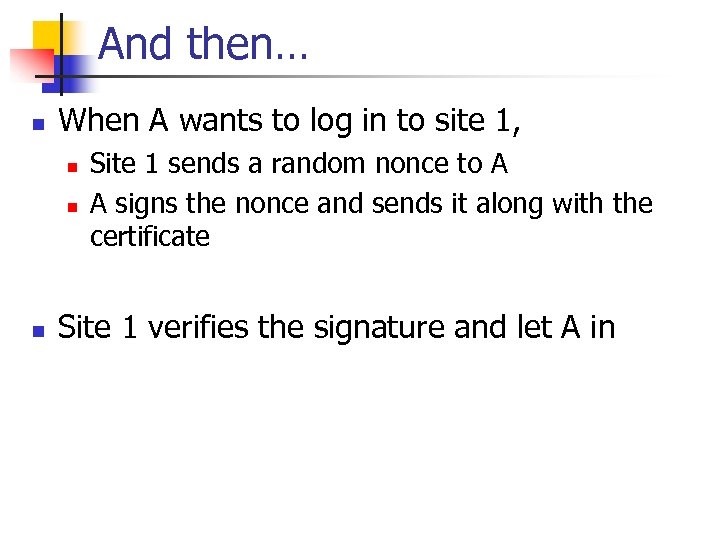 And then… n When A wants to log in to site 1, n n n Site 1 sends a random nonce to A A signs the nonce and sends it along with the certificate Site 1 verifies the signature and let A in
And then… n When A wants to log in to site 1, n n n Site 1 sends a random nonce to A A signs the nonce and sends it along with the certificate Site 1 verifies the signature and let A in
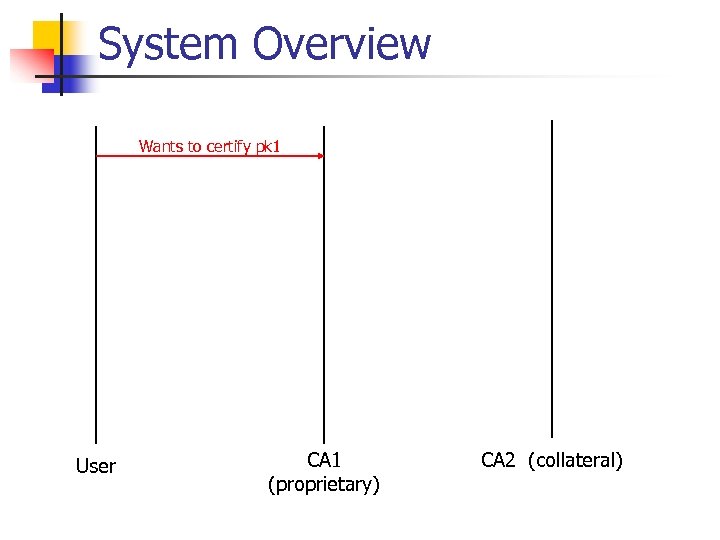 System Overview Wants to certify pk 1 User CA 1 (proprietary) CA 2 (collateral)
System Overview Wants to certify pk 1 User CA 1 (proprietary) CA 2 (collateral)
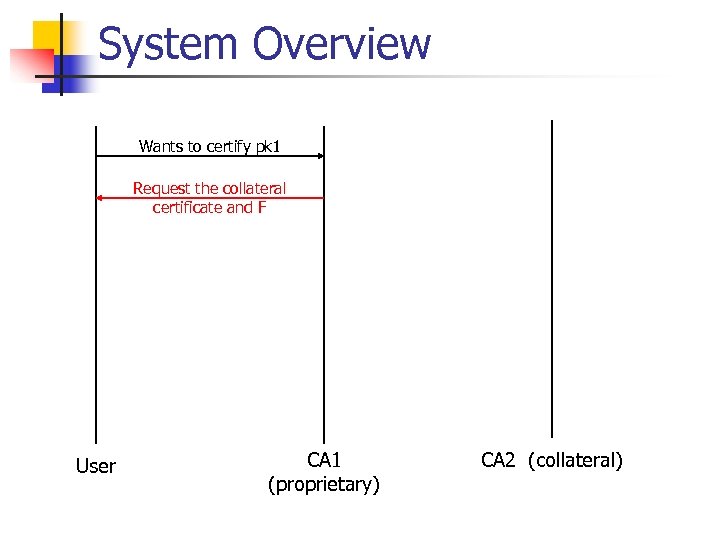 System Overview Wants to certify pk 1 Request the collateral certificate and F User CA 1 (proprietary) CA 2 (collateral)
System Overview Wants to certify pk 1 Request the collateral certificate and F User CA 1 (proprietary) CA 2 (collateral)
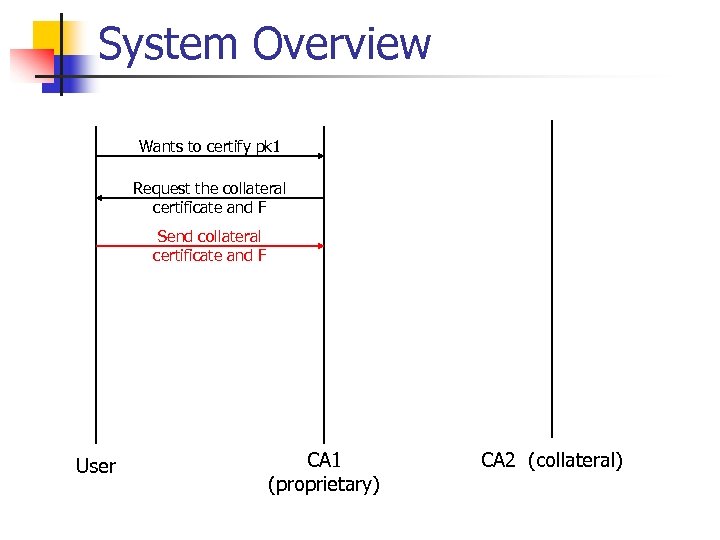 System Overview Wants to certify pk 1 Request the collateral certificate and F Send collateral certificate and F User CA 1 (proprietary) CA 2 (collateral)
System Overview Wants to certify pk 1 Request the collateral certificate and F Send collateral certificate and F User CA 1 (proprietary) CA 2 (collateral)
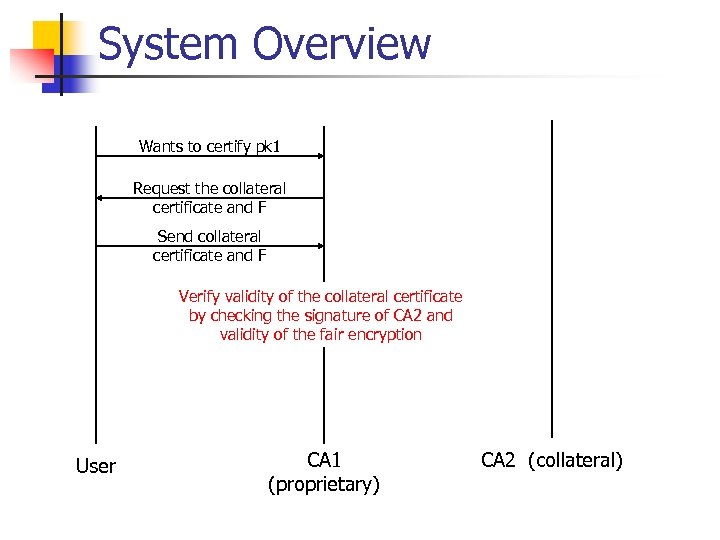 System Overview Wants to certify pk 1 Request the collateral certificate and F Send collateral certificate and F Verify validity of the collateral certificate by checking the signature of CA 2 and validity of the fair encryption User CA 1 (proprietary) CA 2 (collateral)
System Overview Wants to certify pk 1 Request the collateral certificate and F Send collateral certificate and F Verify validity of the collateral certificate by checking the signature of CA 2 and validity of the fair encryption User CA 1 (proprietary) CA 2 (collateral)
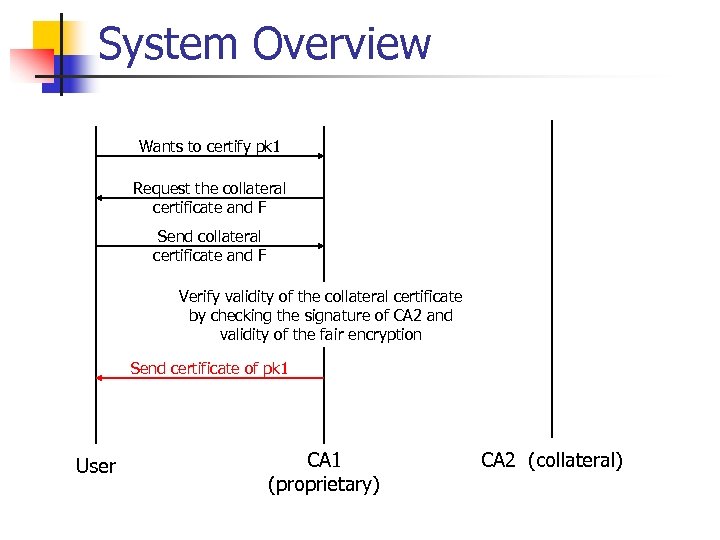 System Overview Wants to certify pk 1 Request the collateral certificate and F Send collateral certificate and F Verify validity of the collateral certificate by checking the signature of CA 2 and validity of the fair encryption Send certificate of pk 1 User CA 1 (proprietary) CA 2 (collateral)
System Overview Wants to certify pk 1 Request the collateral certificate and F Send collateral certificate and F Verify validity of the collateral certificate by checking the signature of CA 2 and validity of the fair encryption Send certificate of pk 1 User CA 1 (proprietary) CA 2 (collateral)
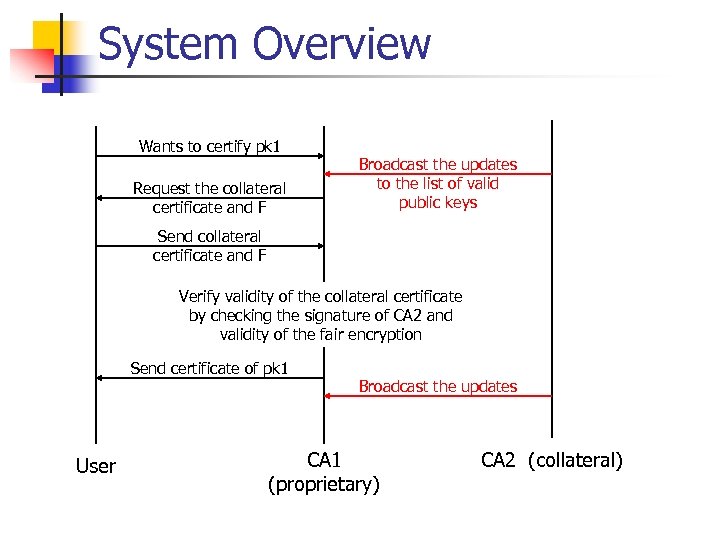 System Overview Wants to certify pk 1 Request the collateral certificate and F Broadcast the updates to the list of valid public keys Send collateral certificate and F Verify validity of the collateral certificate by checking the signature of CA 2 and validity of the fair encryption Send certificate of pk 1 User Broadcast the updates CA 1 (proprietary) CA 2 (collateral)
System Overview Wants to certify pk 1 Request the collateral certificate and F Broadcast the updates to the list of valid public keys Send collateral certificate and F Verify validity of the collateral certificate by checking the signature of CA 2 and validity of the fair encryption Send certificate of pk 1 User Broadcast the updates CA 1 (proprietary) CA 2 (collateral)
 Proprietary Certificates I n Non-transferablility n n Cryptosystem agility n n With knowing secret key of C 1, one can compute the SK of C 2 Proprietary and collateral services can use different cryptosystems Locality n n CA 1 does not need to interact with CA 2 directly Only the “light” version necessary: Broadcasting authentic public keys to CA 2
Proprietary Certificates I n Non-transferablility n n Cryptosystem agility n n With knowing secret key of C 1, one can compute the SK of C 2 Proprietary and collateral services can use different cryptosystems Locality n n CA 1 does not need to interact with CA 2 directly Only the “light” version necessary: Broadcasting authentic public keys to CA 2
 Proprietary Certificates II n Efficiency n n n C 1 is not larger than a regular certificate of its type The computational and communication requirements in establishing the proprietary/collateral relationship are resonable Security n n Any party does not learn any information about the SK 2 of C 2 No party besides CA 1 learns what other certificates the user has
Proprietary Certificates II n Efficiency n n n C 1 is not larger than a regular certificate of its type The computational and communication requirements in establishing the proprietary/collateral relationship are resonable Security n n Any party does not learn any information about the SK 2 of C 2 No party besides CA 1 learns what other certificates the user has
 Proprietary Certificates III CA 1: proprietary certification authority CA 2: collateral certification authority C 1, C 2: proprietary, collateral certificate FEpk 1(sk 2): fair encryption of the sk 2 under pk 1
Proprietary Certificates III CA 1: proprietary certification authority CA 2: collateral certification authority C 1, C 2: proprietary, collateral certificate FEpk 1(sk 2): fair encryption of the sk 2 under pk 1
 Proprietary Certificates IV n Certify the public key pk 1 by CA 1 n User present the certificate of pk 2 contained in C 2 issued by CA 2 and F to CA 1 n n F = FEpk 1(sk 2) CA 1 verifies validity of the collateral certificate n n Check the signature of CA 2 and validity of the fair encryption CA 2 must broadcast the updates to the list of valid public keys
Proprietary Certificates IV n Certify the public key pk 1 by CA 1 n User present the certificate of pk 2 contained in C 2 issued by CA 2 and F to CA 1 n n F = FEpk 1(sk 2) CA 1 verifies validity of the collateral certificate n n Check the signature of CA 2 and validity of the fair encryption CA 2 must broadcast the updates to the list of valid public keys
 Is this enough? n n n What if I lost my secret key for site 1 accidentally? This results in revealing more important information Easy solution: report when we lost it? n n How long does it take to detect it? So, we have to delay the secret key exposure of site 2
Is this enough? n n n What if I lost my secret key for site 1 accidentally? This results in revealing more important information Easy solution: report when we lost it? n n How long does it take to detect it? So, we have to delay the secret key exposure of site 2
 Theft Protection n involuntary proprietary key exposure n n n the user has time to detect the fact of theft and to contact proprietary and collateral service providers CPU delay: Time lock puzzle Real time delay: Delayed response to collateral information
Theft Protection n involuntary proprietary key exposure n n n the user has time to detect the fact of theft and to contact proprietary and collateral service providers CPU delay: Time lock puzzle Real time delay: Delayed response to collateral information
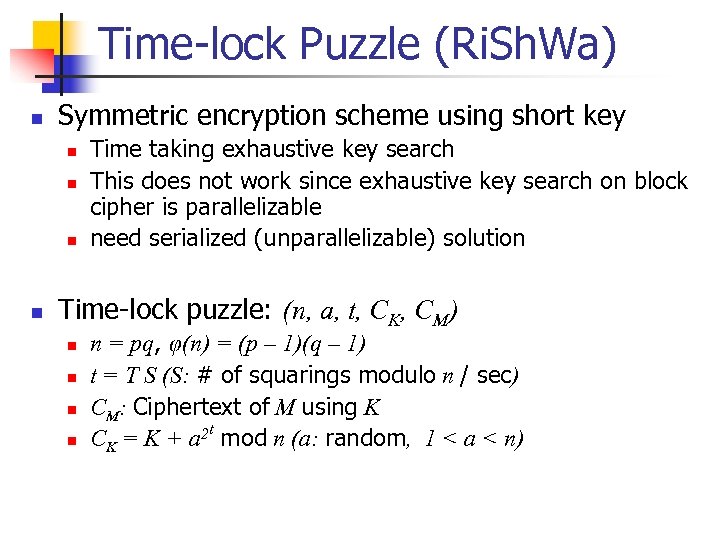 Time-lock Puzzle (Ri. Sh. Wa) n Symmetric encryption scheme using short key n n Time taking exhaustive key search This does not work since exhaustive key search on block cipher is parallelizable need serialized (unparallelizable) solution Time-lock puzzle: (n, a, t, CK, CM) n n n = pq, φ(n) = (p – 1)(q – 1) t = T S (S: # of squarings modulo n / sec) CM: Ciphertext of M using K CK = K + a 2 t mod n (a: random, 1 < a < n)
Time-lock Puzzle (Ri. Sh. Wa) n Symmetric encryption scheme using short key n n Time taking exhaustive key search This does not work since exhaustive key search on block cipher is parallelizable need serialized (unparallelizable) solution Time-lock puzzle: (n, a, t, CK, CM) n n n = pq, φ(n) = (p – 1)(q – 1) t = T S (S: # of squarings modulo n / sec) CM: Ciphertext of M using K CK = K + a 2 t mod n (a: random, 1 < a < n)
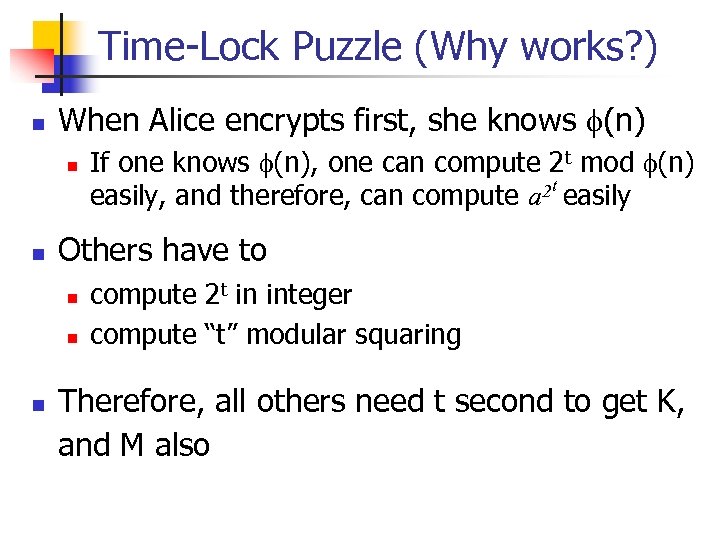 Time-Lock Puzzle (Why works? ) n When Alice encrypts first, she knows f(n) n n Others have to n n n If one knows f(n), one can compute 2 t mod f(n) 2 t easily, and therefore, can compute a compute 2 t in integer compute “t” modular squaring Therefore, all others need t second to get K, and M also
Time-Lock Puzzle (Why works? ) n When Alice encrypts first, she knows f(n) n n Others have to n n n If one knows f(n), one can compute 2 t mod f(n) 2 t easily, and therefore, can compute a compute 2 t in integer compute “t” modular squaring Therefore, all others need t second to get K, and M also
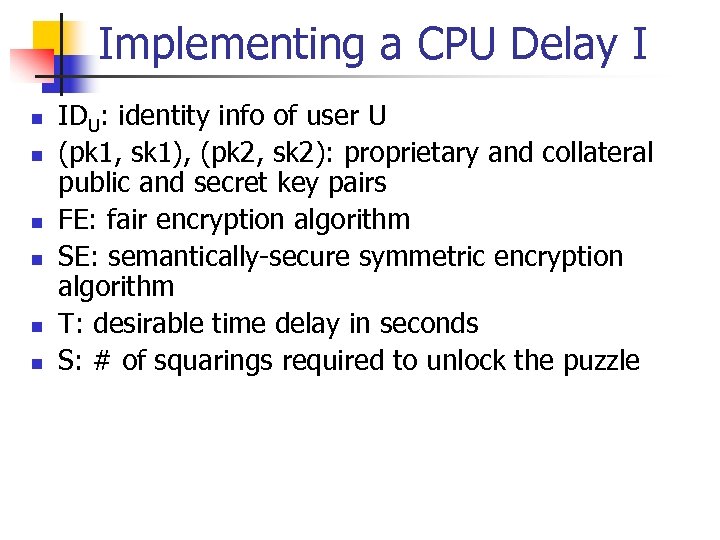 Implementing a CPU Delay I n n n IDU: identity info of user U (pk 1, sk 1), (pk 2, sk 2): proprietary and collateral public and secret key pairs FE: fair encryption algorithm SE: semantically-secure symmetric encryption algorithm T: desirable time delay in seconds S: # of squarings required to unlock the puzzle
Implementing a CPU Delay I n n n IDU: identity info of user U (pk 1, sk 1), (pk 2, sk 2): proprietary and collateral public and secret key pairs FE: fair encryption algorithm SE: semantically-secure symmetric encryption algorithm T: desirable time delay in seconds S: # of squarings required to unlock the puzzle
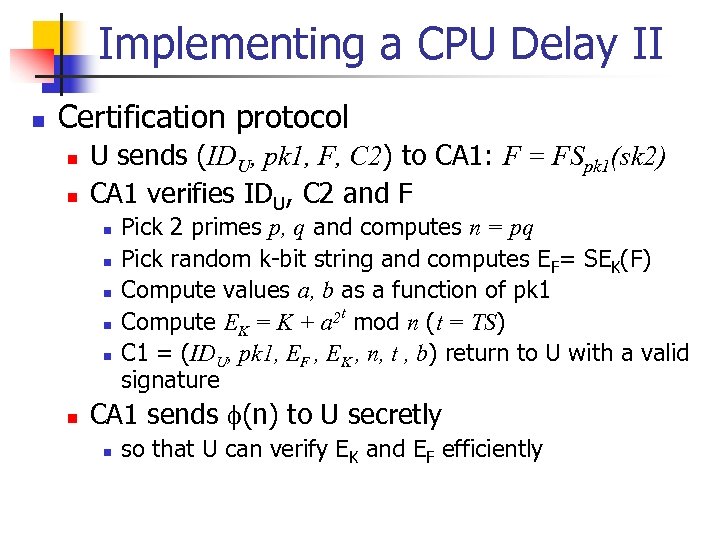 Implementing a CPU Delay II n Certification protocol n n U sends (IDU, pk 1, F, C 2) to CA 1: F = FSpk 1(sk 2) CA 1 verifies IDU, C 2 and F n n n Pick 2 primes p, q and computes n = pq Pick random k-bit string and computes EF= SEK(F) Compute values a, b as a function of pk 1 Compute EK = K + a 2 t mod n (t = TS) C 1 = (IDU, pk 1, EF , EK , n, t , b) return to U with a valid signature CA 1 sends f(n) to U secretly n so that U can verify EK and EF efficiently
Implementing a CPU Delay II n Certification protocol n n U sends (IDU, pk 1, F, C 2) to CA 1: F = FSpk 1(sk 2) CA 1 verifies IDU, C 2 and F n n n Pick 2 primes p, q and computes n = pq Pick random k-bit string and computes EF= SEK(F) Compute values a, b as a function of pk 1 Compute EK = K + a 2 t mod n (t = TS) C 1 = (IDU, pk 1, EF , EK , n, t , b) return to U with a valid signature CA 1 sends f(n) to U secretly n so that U can verify EK and EF efficiently
 Implementing a CPU Delay III n Use of RSA keys n n n Public key: (N, e) , Secret key: (N, d) a ∈ Z*N , b = ae mod N Use of DL keys n n Public key: (p, g, q, gx) , secret key: x b = gr (r ∈ Zq ), a = yr = grx (mod p)
Implementing a CPU Delay III n Use of RSA keys n n n Public key: (N, e) , Secret key: (N, d) a ∈ Z*N , b = ae mod N Use of DL keys n n Public key: (p, g, q, gx) , secret key: x b = gr (r ∈ Zq ), a = yr = grx (mod p)
 Implementing Real Time Delay n Certification Protocol n n n Similar to CPU delay CA stores F along with user’s information Derivation of collateral secret n After verifying the signature, CA waits the necessary time period and returns F
Implementing Real Time Delay n Certification Protocol n n n Similar to CPU delay CA stores F along with user’s information Derivation of collateral secret n After verifying the signature, CA waits the necessary time period and returns F
 References n n n A. Boldyreva and M. Jakobsson, "Theft-protected proprietary certificates, " ACM workshop on DRM '02 M. Jakobsson, A. Juels and P. Nguyen, “Proprietary Certificates, ” Proceedings of The Cryptographers’ Track at the RSA Conference 2002, LNCS Vol. 2271, Springer-Verlag, 2002 Jan Camenisch, Ivan Damgard, “Verifiable Encryption, Group Encryption, and Their Applications to Group Signatures and Signature Sharing Schemes, ” Advaces in Cryptology – ASIACRYPT ’ 00, LNCS Vol. 1976, T. Okamoto ed. , Springer-Verlag, 2000 n G. Poupard and J. Stern, “Fair encryption of RSA keys, ” Advaces in n R. Rivest, A. Shamir and D. Wagner, “Time-lock puzzles and timedrelease crypto, ” LCS technical memo MIT/LCS/TR-684, February 1996 Cryptology – Curocrypt ’ 00, LNCS Vol. 1807, B. Preneel ed. , Springer. Verlag, 2000
References n n n A. Boldyreva and M. Jakobsson, "Theft-protected proprietary certificates, " ACM workshop on DRM '02 M. Jakobsson, A. Juels and P. Nguyen, “Proprietary Certificates, ” Proceedings of The Cryptographers’ Track at the RSA Conference 2002, LNCS Vol. 2271, Springer-Verlag, 2002 Jan Camenisch, Ivan Damgard, “Verifiable Encryption, Group Encryption, and Their Applications to Group Signatures and Signature Sharing Schemes, ” Advaces in Cryptology – ASIACRYPT ’ 00, LNCS Vol. 1976, T. Okamoto ed. , Springer-Verlag, 2000 n G. Poupard and J. Stern, “Fair encryption of RSA keys, ” Advaces in n R. Rivest, A. Shamir and D. Wagner, “Time-lock puzzles and timedrelease crypto, ” LCS technical memo MIT/LCS/TR-684, February 1996 Cryptology – Curocrypt ’ 00, LNCS Vol. 1807, B. Preneel ed. , Springer. Verlag, 2000


