464ea6c2c7866e14b2efc72d97087854.ppt
- Количество слайдов: 30

The UMU-PBNM Antonio F. Gomez Skarmeta Gregorio Martínez <skarmeta, gregorio@dif. um. es> University of Murcia (Spain) University of Murcia SPAIN
Agenda n Objective and Proposed Architecture n The UMU-PKIv 6 n UMU-PBNM Design n UMU-PBNM Implementation n Analysis of VPNs over IPv 6 n References
Objective and Proposed Architecture University of Murcia (Spain)
UMU-PBNM Main Objective n n Design and set-up a security framework to manage distributed communication systems using the PBNM paradigm Features: n n n Flexible Secure Service and application-independent Standard-based IP-based In collaboration with UCL-CS
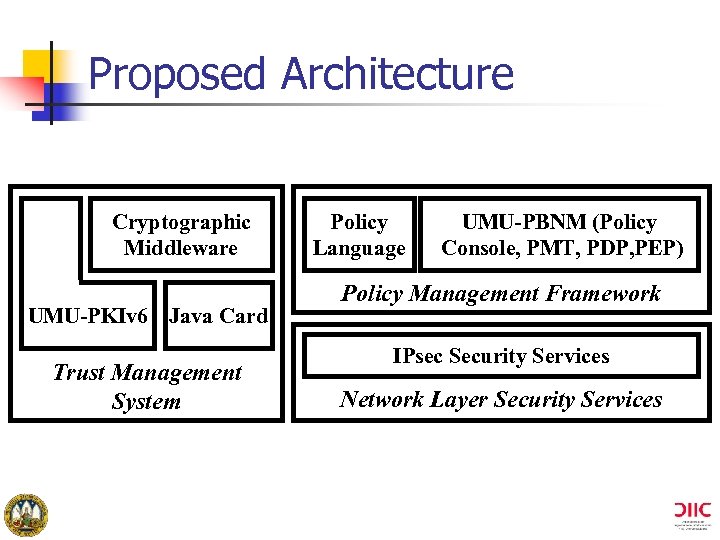
Proposed Architecture Cryptographic Middleware UMU-PKIv 6 Java Card Trust Management System Policy Language UMU-PBNM (Policy Console, PMT, PDP, PEP) Policy Management Framework IPsec Security Services Network Layer Security Services
The UMU-PKIv 6 University of Murcia (Spain)
UMU-PKIv 6 Description n n Main Objective. . . to establish a high security infrastructure for distributed systems Main Features: n n n PKI supporting the IPv 6 protocol Developed in Java running on every Operating System Issue, renew and revoke certificates for every entity belonging to one organisation Final users can use either RAs or Web browsers to make their own certification operations LDAPv 6 directory support
UMU-PKIv 6 Description (II) n Main Features: (II) n n n n Use of smart cards (file system, RSA or Java Cards). . . allowing user mobility and increasing security PKI Certification Policy (CPS) support VPN devices certification support (using the SCEP protocol) Support for the OCSP protocol and Time Stamp Web Administration Supports DNSsec Used in both Euro 6 IX and 6 NET projects (crosscertification)
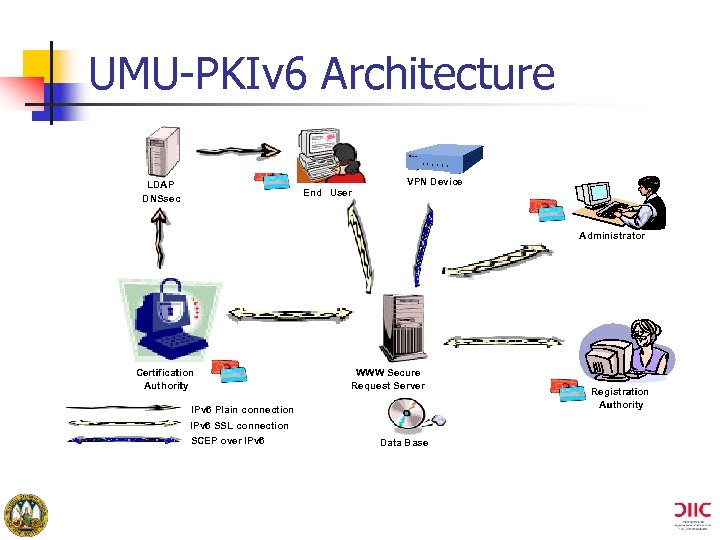
UMU-PKIv 6 Architecture LDAP DNSsec End User VPN Device Administrator Certification Authority WWW Secure Request Server IPv 6 Plain connection IPv 6 SSL connection SCEP over IPv 6 Data Base Registration Authority
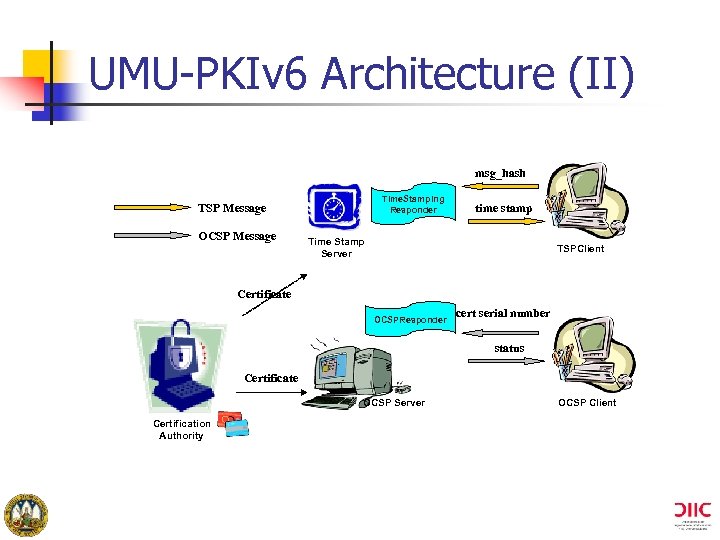
UMU-PKIv 6 Architecture (II) msg_hash Time. Stamping Responder TSP Message OCSP Message time stamp Time Stamp Server TSPClient Certificate OCSPResponder cert serial number status Certificate OCSP Server Certification Authority OCSP Client
UMU-PBNM Design University of Murcia (Spain)
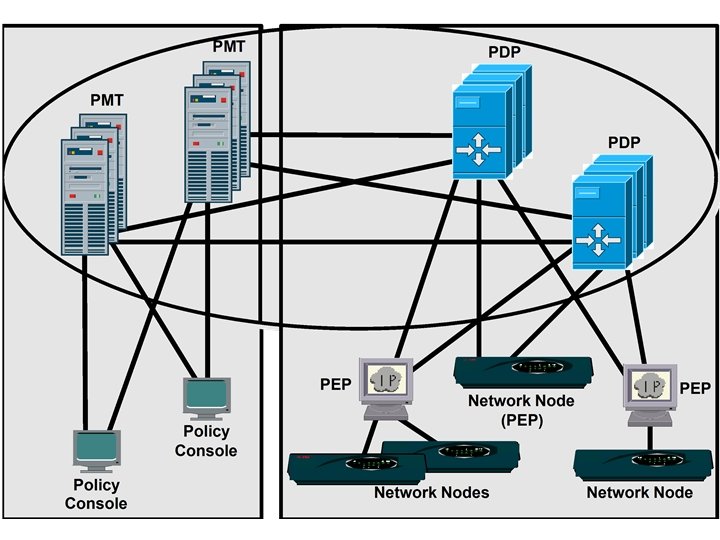
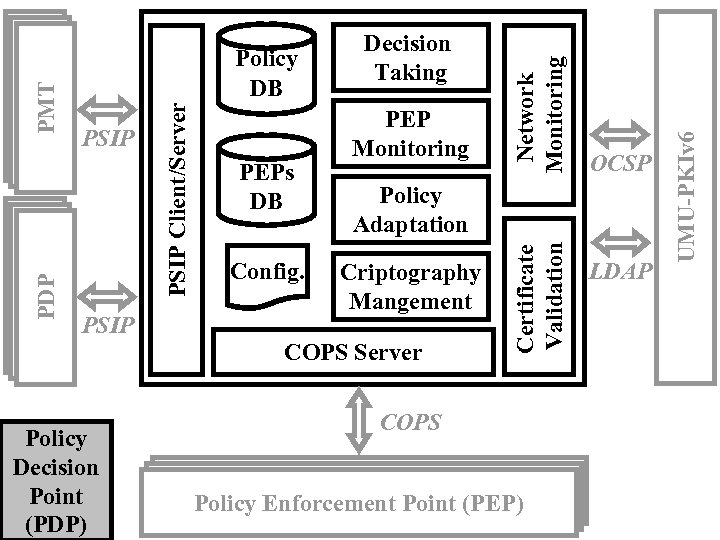
PSIP Policy Adaptation Criptography Mangement COPS Server Policy Decision Point (PDP) OCSP COPS Policy Enforcement Point (PEP) LDAP UMU-PKIv 6 Config. Network Monitoring PEPs DB PEP Monitoring Certificate Validation PSIP Client/Server PMT PDP Policy DB Decision Taking
Policy Management Process
Monitoring Process
UMU-PBNM Implementation University of Murcia (Spain)
Relevant Implementation Issues n Policy Console n n n PMT n n n Assistant module to define new policies Managing and storing XML policy documents according to one XML schema PDP and PEP n n n Web Browser Microsoft CSP (Cryptographic Service Provider) Using COPS and COPS-PR from Vocal 1. 5 New S-Type for XML (and XML Path) added PEP-Network Node interaction n VPN ETool
Analysis of VPNs over IPv 6 University of Murcia (Spain)
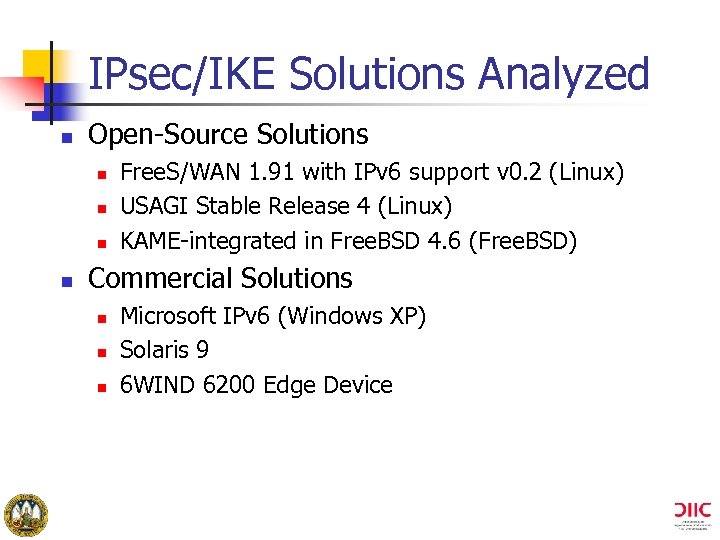
IPsec/IKE Solutions Analyzed n Open-Source Solutions n n Free. S/WAN 1. 91 with IPv 6 support v 0. 2 (Linux) USAGI Stable Release 4 (Linux) KAME-integrated in Free. BSD 4. 6 (Free. BSD) Commercial Solutions n n n Microsoft IPv 6 (Windows XP) Solaris 9 6 WIND 6200 Edge Device
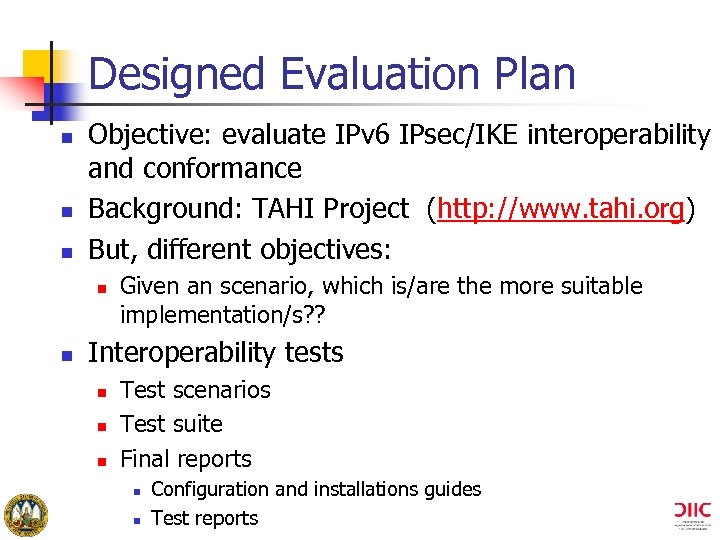
Designed Evaluation Plan n Objective: evaluate IPv 6 IPsec/IKE interoperability and conformance Background: TAHI Project (http: //www. tahi. org) But, different objectives: n n Given an scenario, which is/are the more suitable implementation/s? ? Interoperability tests n n n Test scenarios Test suite Final reports n n Configuration and installations guides Test reports
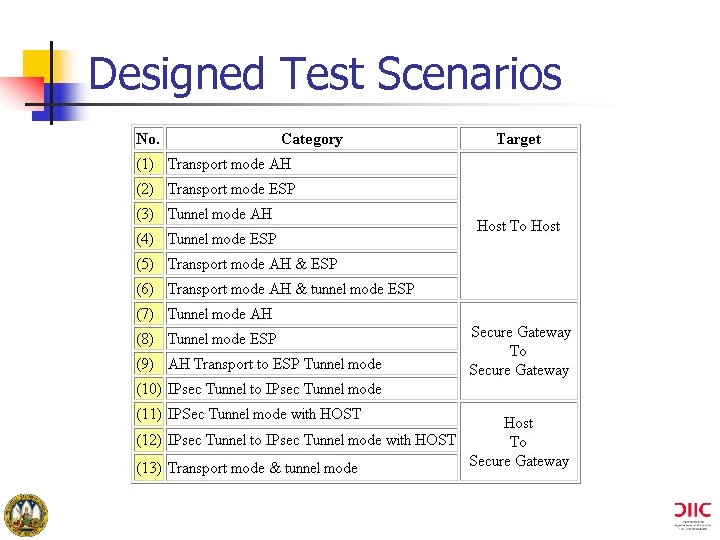
Designed Test Scenarios
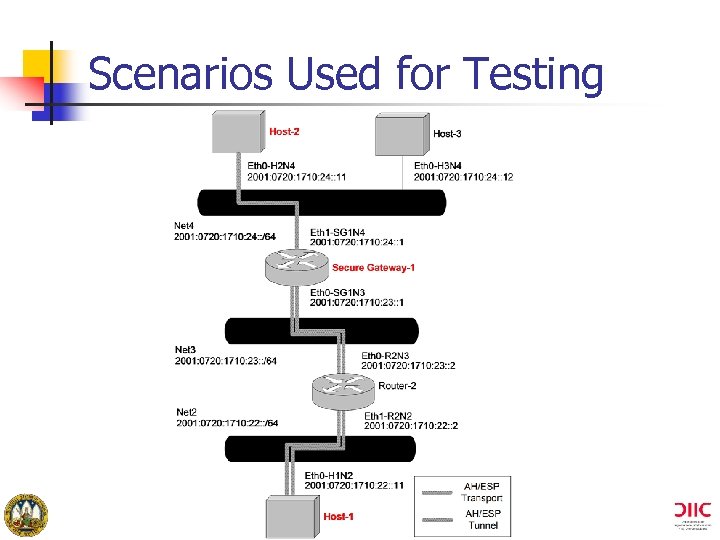
Scenarios Used for Testing
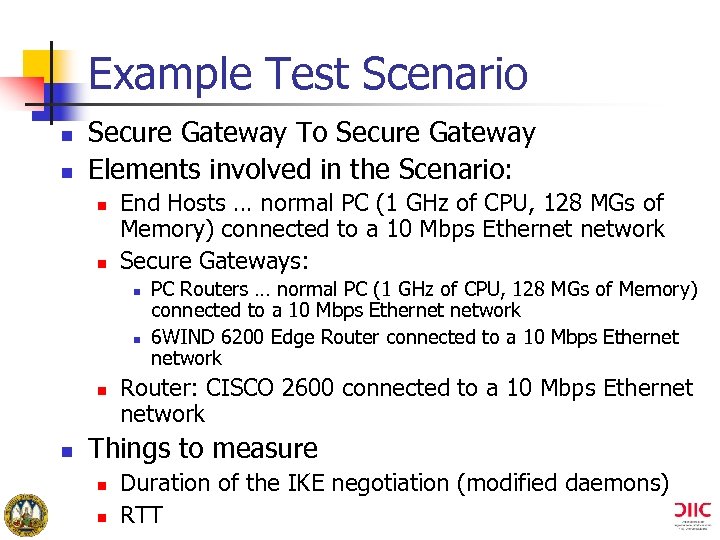
Example Test Scenario n n Secure Gateway To Secure Gateway Elements involved in the Scenario: n n End Hosts … normal PC (1 GHz of CPU, 128 MGs of Memory) connected to a 10 Mbps Ethernet network Secure Gateways: n n PC Routers … normal PC (1 GHz of CPU, 128 MGs of Memory) connected to a 10 Mbps Ethernet network 6 WIND 6200 Edge Router connected to a 10 Mbps Ethernet network Router: CISCO 2600 connected to a 10 Mbps Ethernet network Things to measure n n Duration of the IKE negotiation (modified daemons) RTT
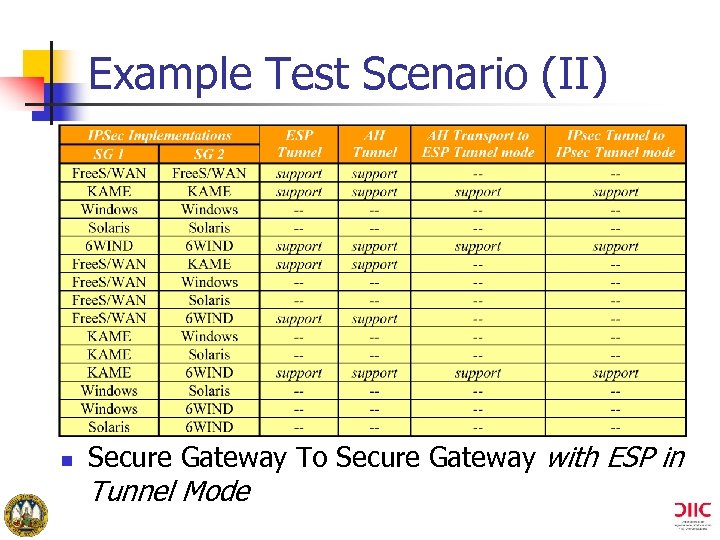
Example Test Scenario (II) n Secure Gateway To Secure Gateway with ESP in Tunnel Mode
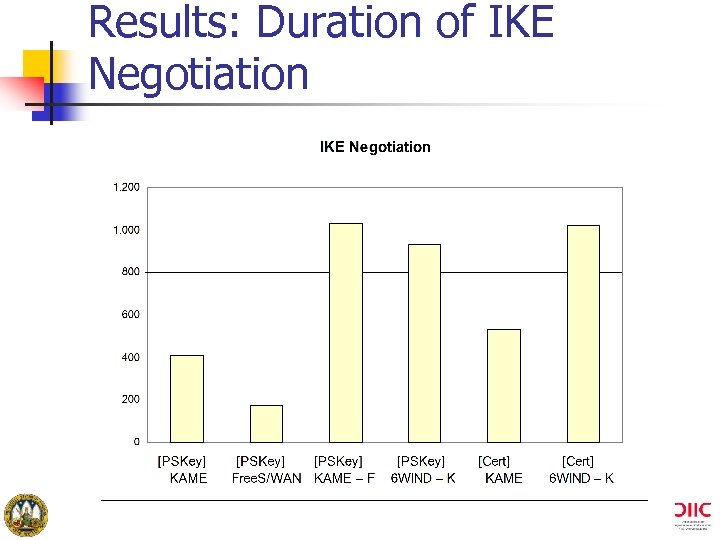
Results: Duration of IKE Negotiation
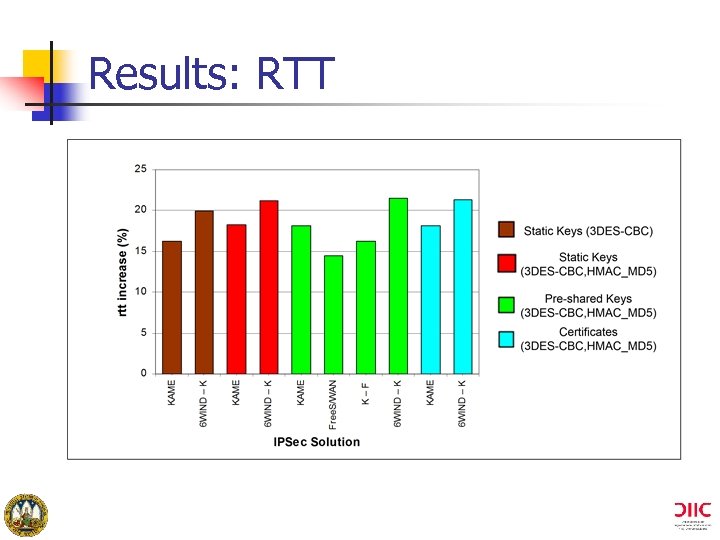
Results: RTT
Results: Conclusions n Duration of the IKE Negotiation n RTT n n n Use of certificates does not increment too much the delay Interoperability implies a strong increment Using authentication increases lowly the RTT The use of IPsec increases in 15 -20% the RTT But … n It is real that implementations are far from being mature
References University of Murcia (Spain)
Basic References n UMU-PKIv 6 - Public Key Infrastructure with IPv 6 support https: //eriador. dif. um. es/ https: //pippin. dif. um. es/ n VPN Enforcement Tool https: //shire. dif. um. es/ n UMU-Policy Mangement Tool (old version of the IPsec Policy Schema) https: //shire. dif. um. es/pmtool/

The UMU-PBNM Antonio F. Gomez Skarmeta Gregorio Martínez <skarmeta, gregorio@dif. um. es> University of Murcia (Spain) University of Murcia SPAIN
464ea6c2c7866e14b2efc72d97087854.ppt