ced0b0b35974d10906580687ff7cb547.ppt
- Количество слайдов: 88
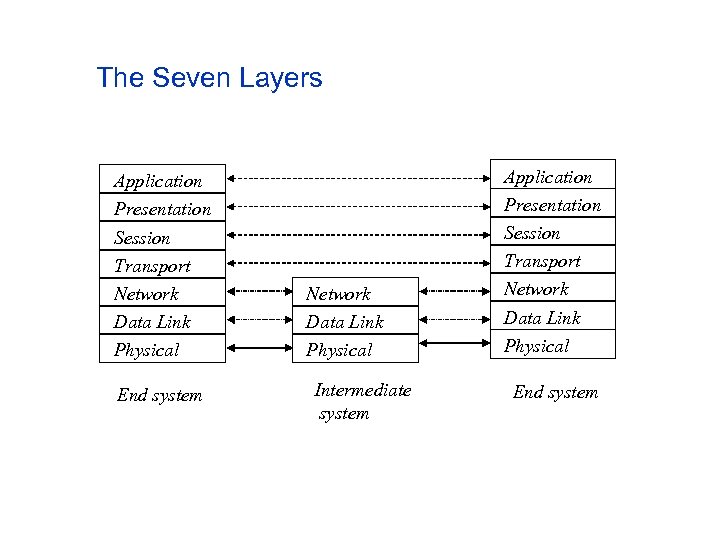 The Seven Layers Application Presentation Session Transport Network Data Link Physical End system Network Data Link Physical Intermediate system Application Presentation Session Transport Network Data Link Physical End system
The Seven Layers Application Presentation Session Transport Network Data Link Physical End system Network Data Link Physical Intermediate system Application Presentation Session Transport Network Data Link Physical End system
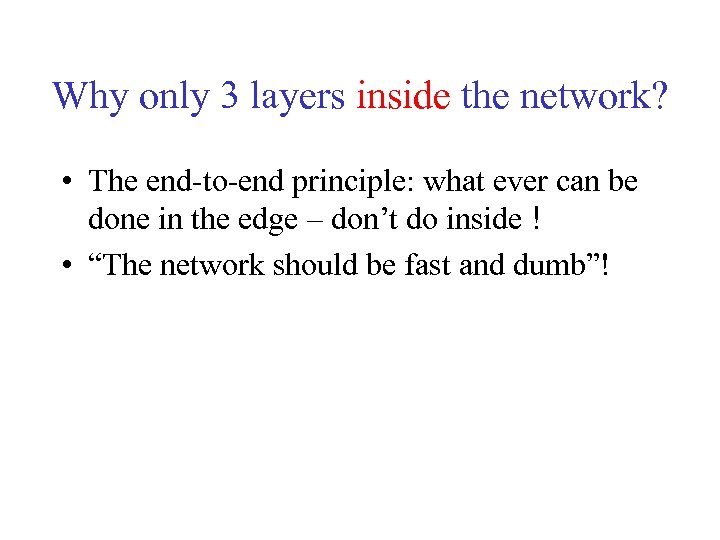 Why only 3 layers inside the network? • The end-to-end principle: what ever can be done in the edge – don’t do inside ! • “The network should be fast and dumb”!
Why only 3 layers inside the network? • The end-to-end principle: what ever can be done in the edge – don’t do inside ! • “The network should be fast and dumb”!
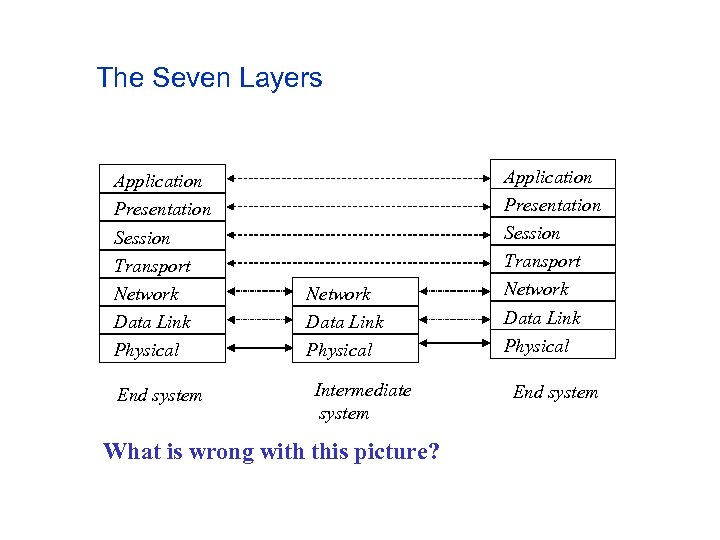 The Seven Layers Application Presentation Session Transport Network Data Link Physical End system Network Data Link Physical Intermediate system What is wrong with this picture? Application Presentation Session Transport Network Data Link Physical End system
The Seven Layers Application Presentation Session Transport Network Data Link Physical End system Network Data Link Physical Intermediate system What is wrong with this picture? Application Presentation Session Transport Network Data Link Physical End system
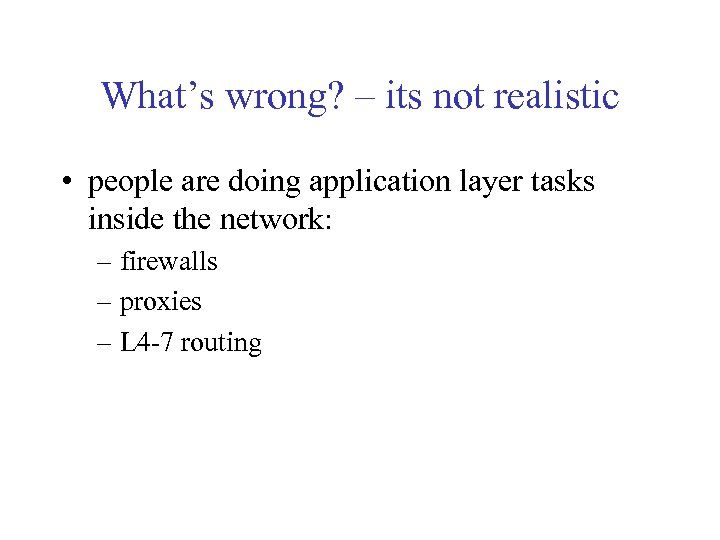 What’s wrong? – its not realistic • people are doing application layer tasks inside the network: – firewalls – proxies – L 4 -7 routing
What’s wrong? – its not realistic • people are doing application layer tasks inside the network: – firewalls – proxies – L 4 -7 routing
 Why not adding network support for applications • standards are very slooooow to develop – multicast! • we need a fast way to add features to our network core
Why not adding network support for applications • standards are very slooooow to develop – multicast! • we need a fast way to add features to our network core
 Solution • let’s agree on a standard interface for routers and let everyone run its own programs. • Questions: – who is everyone? – Do we have the cycles? – what about security?
Solution • let’s agree on a standard interface for routers and let everyone run its own programs. • Questions: – who is everyone? – Do we have the cycles? – what about security?
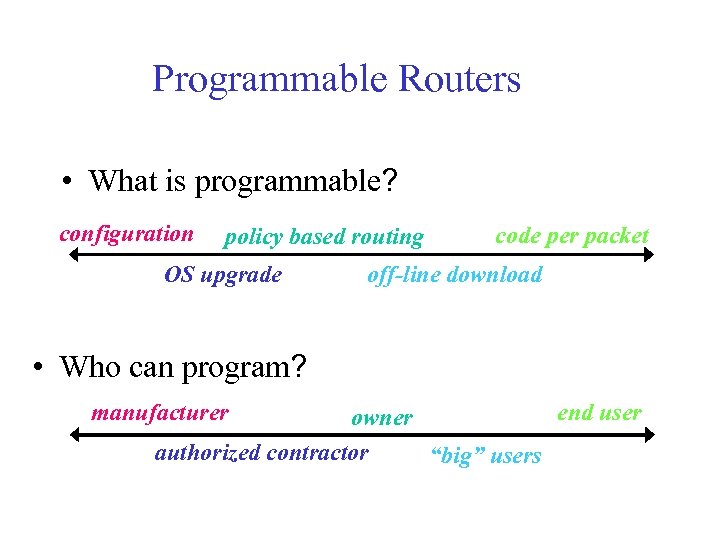 Programmable Routers • What is programmable? configuration policy based routing OS upgrade code per packet off-line download • Who can program? end user owner authorized contractor “big” users manufacturer
Programmable Routers • What is programmable? configuration policy based routing OS upgrade code per packet off-line download • Who can program? end user owner authorized contractor “big” users manufacturer
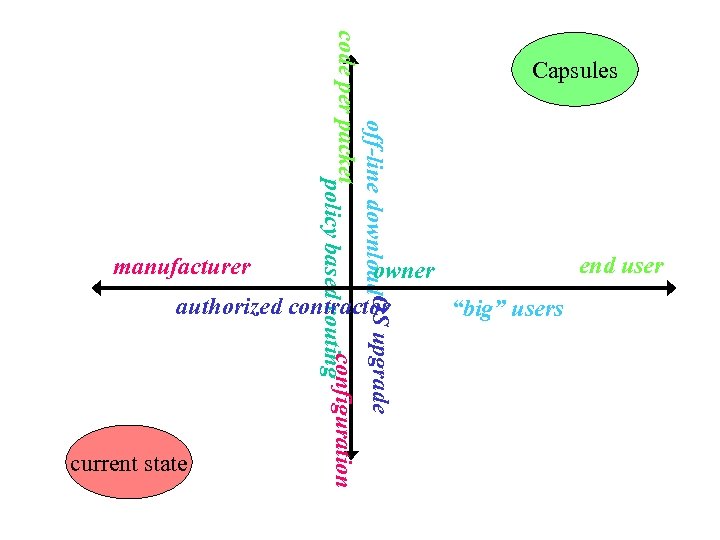 off-line download. OS upgrade code per packet configuration policy based routing Capsules end user owner authorized contractor “big” users manufacturer current state
off-line download. OS upgrade code per packet configuration policy based routing Capsules end user owner authorized contractor “big” users manufacturer current state
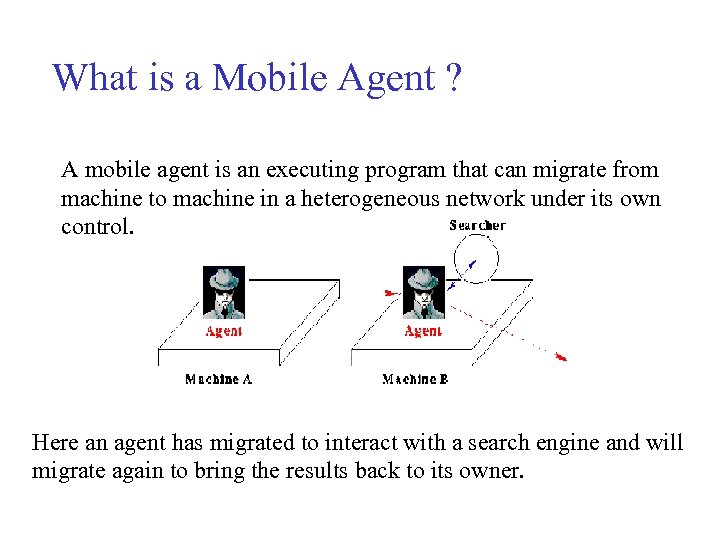 What is a Mobile Agent ? A mobile agent is an executing program that can migrate from machine to machine in a heterogeneous network under its own control. Here an agent has migrated to interact with a search engine and will migrate again to bring the results back to its owner.
What is a Mobile Agent ? A mobile agent is an executing program that can migrate from machine to machine in a heterogeneous network under its own control. Here an agent has migrated to interact with a search engine and will migrate again to bring the results back to its owner.
 Mobile Code • The basic idea is to allow code dispatching to remote sites where it is executed. • Move the programmer away from the rigid clientserver model to the more flexible peer-peer model • programs communicate as peers • act as either clients or servers depending on their current needs • Problems arising from mobility – heterogeneity of systems – security (as more parties are involved)
Mobile Code • The basic idea is to allow code dispatching to remote sites where it is executed. • Move the programmer away from the rigid clientserver model to the more flexible peer-peer model • programs communicate as peers • act as either clients or servers depending on their current needs • Problems arising from mobility – heterogeneity of systems – security (as more parties are involved)
 Mobile Agents • Mobile Agents are program instances that are able move within a network under their own control • mobile agents consist of: – code – data state (i. e. variables) – execution state (i. e. stack) • Some basic capabilities: – able to autonomously migrate between places – able to communicate to each other – some agents offer services or interfaces to legacy applications
Mobile Agents • Mobile Agents are program instances that are able move within a network under their own control • mobile agents consist of: – code – data state (i. e. variables) – execution state (i. e. stack) • Some basic capabilities: – able to autonomously migrate between places – able to communicate to each other – some agents offer services or interfaces to legacy applications
 Application for Mobile Agents • • • Distributed Information Retrieval Mobile computing Distributed Network Management Collaborative and workflow applications Active networks Electronic commerce
Application for Mobile Agents • • • Distributed Information Retrieval Mobile computing Distributed Network Management Collaborative and workflow applications Active networks Electronic commerce
 Distributed Network Computing • • More than one user More than one host More than one application Code can migrate from host to host • Who is in charge?
Distributed Network Computing • • More than one user More than one host More than one application Code can migrate from host to host • Who is in charge?
 Hosting Mobile Code • We want the code to perform tasks related to the network • Who will host the mobile agent? • How will the agent locate its optimal location for the task? • What type of services are needed? • Is the applet sandbox model good enough?
Hosting Mobile Code • We want the code to perform tasks related to the network • Who will host the mobile agent? • How will the agent locate its optimal location for the task? • What type of services are needed? • Is the applet sandbox model good enough?
 Open Routers • Addresses at least one aspect of the problem • Define an interface between the mobile code and the host • An interface is an agreed and shared contract, typically static knowledge that is not dynamically modified after the agreement
Open Routers • Addresses at least one aspect of the problem • Define an interface between the mobile code and the host • An interface is an agreed and shared contract, typically static knowledge that is not dynamically modified after the agreement
 Terminology • • Active Networks Mobile agents Mobile code Programmable networks No clear definitions, depends who is using it
Terminology • • Active Networks Mobile agents Mobile code Programmable networks No clear definitions, depends who is using it
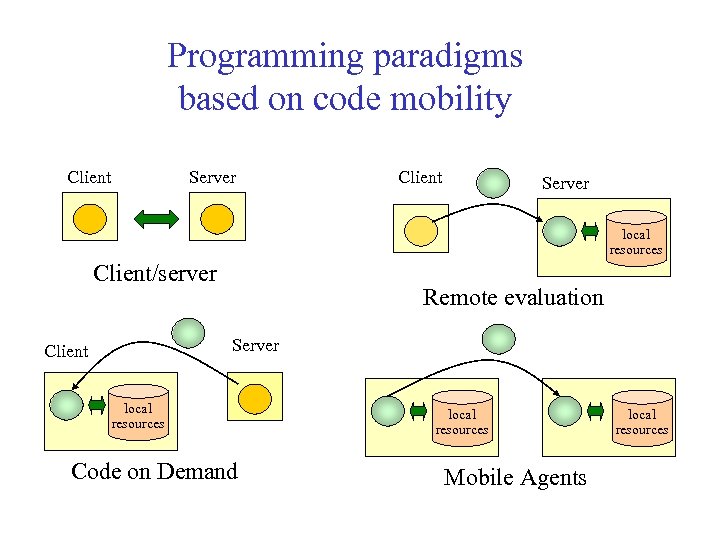 Programming paradigms based on code mobility Client Server local resources Client/server Remote evaluation Server Client local resources Code on Demand local resources Mobile Agents local resources
Programming paradigms based on code mobility Client Server local resources Client/server Remote evaluation Server Client local resources Code on Demand local resources Mobile Agents local resources
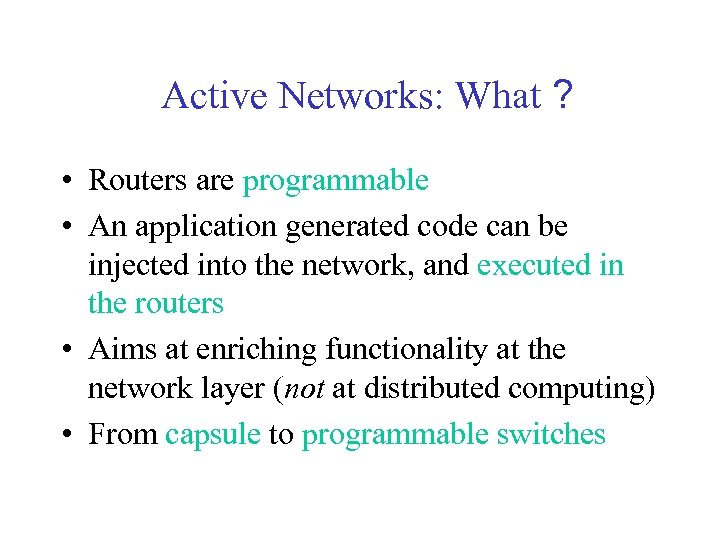 Active Networks: What ? • Routers are programmable • An application generated code can be injected into the network, and executed in the routers • Aims at enriching functionality at the network layer (not at distributed computing) • From capsule to programmable switches
Active Networks: What ? • Routers are programmable • An application generated code can be injected into the network, and executed in the routers • Aims at enriching functionality at the network layer (not at distributed computing) • From capsule to programmable switches
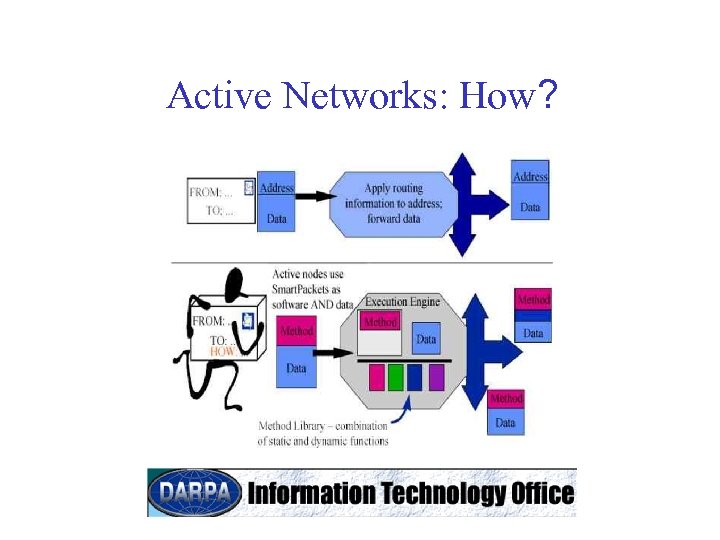 Active Networks: How?
Active Networks: How?
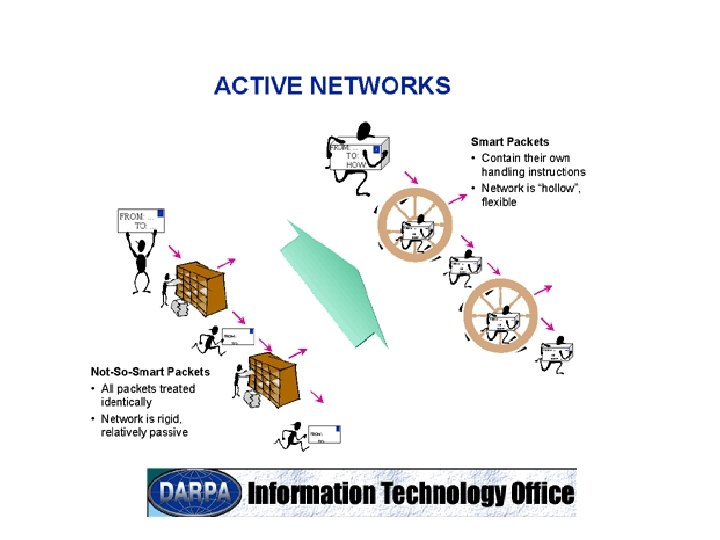
 Active Networks: Why? • Producing a new networking platform, flexible and extensible at runtime to accommodate the rapid evolution and deployment of networking technologies • To provide the increasingly sophisticated services demanded by defense applications • The packet itself is the basis for describing, provisioning, or tailoring resources to achieve the delivery and management requirements • A killer application ? !
Active Networks: Why? • Producing a new networking platform, flexible and extensible at runtime to accommodate the rapid evolution and deployment of networking technologies • To provide the increasingly sophisticated services demanded by defense applications • The packet itself is the basis for describing, provisioning, or tailoring resources to achieve the delivery and management requirements • A killer application ? !
 Goals • Quantifiable improvement in network services – audio/video synchronization and full-rate video over multicast – fewer retransmitted packets, 100% increase in useful data rate to end applications • Architecture creates solutions to future Do. D needs – e. g. , "addressless" networks, resource directed communication • Fault-tolerance mechanisms based in network • Multi-tiered mobile security – authentication forms basis for dynamic access control – separate traffic and administrative functions based on types and policy
Goals • Quantifiable improvement in network services – audio/video synchronization and full-rate video over multicast – fewer retransmitted packets, 100% increase in useful data rate to end applications • Architecture creates solutions to future Do. D needs – e. g. , "addressless" networks, resource directed communication • Fault-tolerance mechanisms based in network • Multi-tiered mobile security – authentication forms basis for dynamic access control – separate traffic and administrative functions based on types and policy
 Killer Application • • • Was (and still is) an important issue Do we really need one? How about network management? New services? What? The ability to create new services in the network level
Killer Application • • • Was (and still is) an important issue Do we really need one? How about network management? New services? What? The ability to create new services in the network level
 Challenges • Composite protocols: Smart. Packet processing must be efficient, secure and survivable • Enhanced network services – quickly and safely deploy new services – achieve widespread use without need for a standardization process – upgrade crucial network services to keep pace with network complexity (size, speed, variety) – develop new strategies for routing and service provisioning in large networks that have overlapping topologies and mobility requirements
Challenges • Composite protocols: Smart. Packet processing must be efficient, secure and survivable • Enhanced network services – quickly and safely deploy new services – achieve widespread use without need for a standardization process – upgrade crucial network services to keep pace with network complexity (size, speed, variety) – develop new strategies for routing and service provisioning in large networks that have overlapping topologies and mobility requirements
 Is It • Safe? – safety and security – comparing to IP • Efficient? – an AN node is always slower than a router – system view: fewer packets, shorter control loops, smarter algorithms • Feasible? – computation power, horizontal architecture
Is It • Safe? – safety and security – comparing to IP • Efficient? – an AN node is always slower than a router – system view: fewer packets, shorter control loops, smarter algorithms • Feasible? – computation power, horizontal architecture
 Are Active Networks Efficient? • An AN node is always slower than a router • Fast/slow track • System view: – fewer packets – shorter control loops – smarter algorithms
Are Active Networks Efficient? • An AN node is always slower than a router • Fast/slow track • System view: – fewer packets – shorter control loops – smarter algorithms
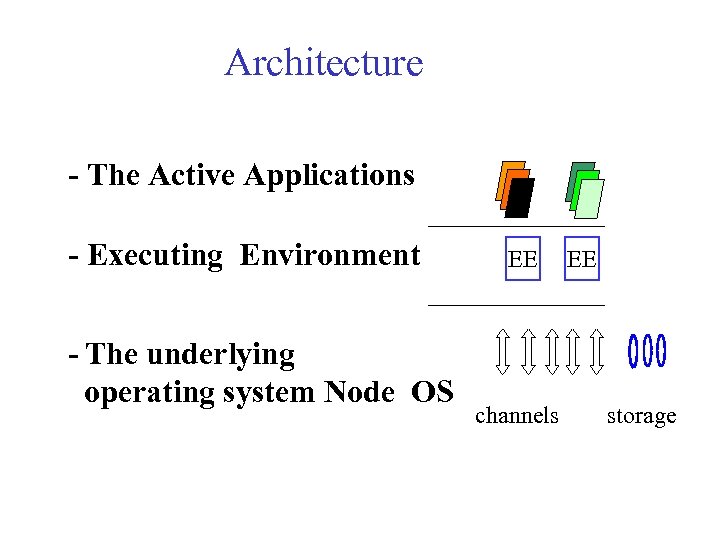 Architecture - The Active Applications - Executing Environment - The underlying operating system Node OS EE channels EE storage
Architecture - The Active Applications - Executing Environment - The underlying operating system Node OS EE channels EE storage
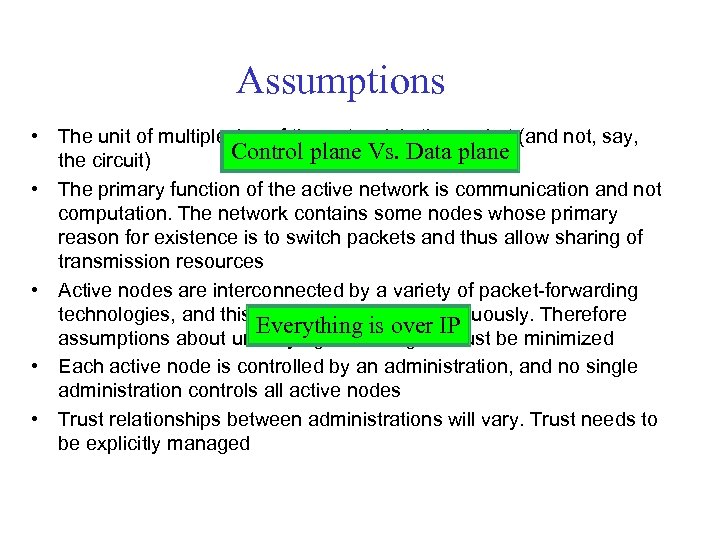 Assumptions • The unit of multiplexing of the network is the packet (and not, say, Control plane Vs. Data plane the circuit) • The primary function of the active network is communication and not computation. The network contains some nodes whose primary reason for existence is to switch packets and thus allow sharing of transmission resources • Active nodes are interconnected by a variety of packet-forwarding technologies, and this variety will evolve continuously. Therefore Everything is over IP assumptions about underlying technologies must be minimized • Each active node is controlled by an administration, and no single administration controls all active nodes • Trust relationships between administrations will vary. Trust needs to be explicitly managed
Assumptions • The unit of multiplexing of the network is the packet (and not, say, Control plane Vs. Data plane the circuit) • The primary function of the active network is communication and not computation. The network contains some nodes whose primary reason for existence is to switch packets and thus allow sharing of transmission resources • Active nodes are interconnected by a variety of packet-forwarding technologies, and this variety will evolve continuously. Therefore Everything is over IP assumptions about underlying technologies must be minimized • Each active node is controlled by an administration, and no single administration controls all active nodes • Trust relationships between administrations will vary. Trust needs to be explicitly managed
 Objectives • Minimize the amount of standardization required, and support dynamic modification of aspects of the network that do not require global agreement • Support fast-path processing optimizations in nodes. (The architecture should not preclude active nodes from performing standard IPv 4/IPv 6 forwarding at speeds comparable to non-active IP routers. ) • Support deployment of a base platform that permits onthe-fly experimentation. Backward compatibility, or at least the ability to fit existing network nodes into the architectural framework, is desirable
Objectives • Minimize the amount of standardization required, and support dynamic modification of aspects of the network that do not require global agreement • Support fast-path processing optimizations in nodes. (The architecture should not preclude active nodes from performing standard IPv 4/IPv 6 forwarding at speeds comparable to non-active IP routers. ) • Support deployment of a base platform that permits onthe-fly experimentation. Backward compatibility, or at least the ability to fit existing network nodes into the architectural framework, is desirable
 Objectives (2) • Scale to very large global active networks. The main implication for the node architecture is a requirement that network-scale parameters (e. g. number of principals using the entire active network) not be exposed at the individual node level • Provide mechanisms to ensure the security and robustness of active nodes individually. As with scalability, global security and robustness is the responsibility of each individual network architecture. However, the stability of individual nodes is necessary for that of the entire network • Support network management at all levels • Provide mechanisms to support different levels/qualities/classes of service
Objectives (2) • Scale to very large global active networks. The main implication for the node architecture is a requirement that network-scale parameters (e. g. number of principals using the entire active network) not be exposed at the individual node level • Provide mechanisms to ensure the security and robustness of active nodes individually. As with scalability, global security and robustness is the responsibility of each individual network architecture. However, the stability of individual nodes is necessary for that of the entire network • Support network management at all levels • Provide mechanisms to support different levels/qualities/classes of service
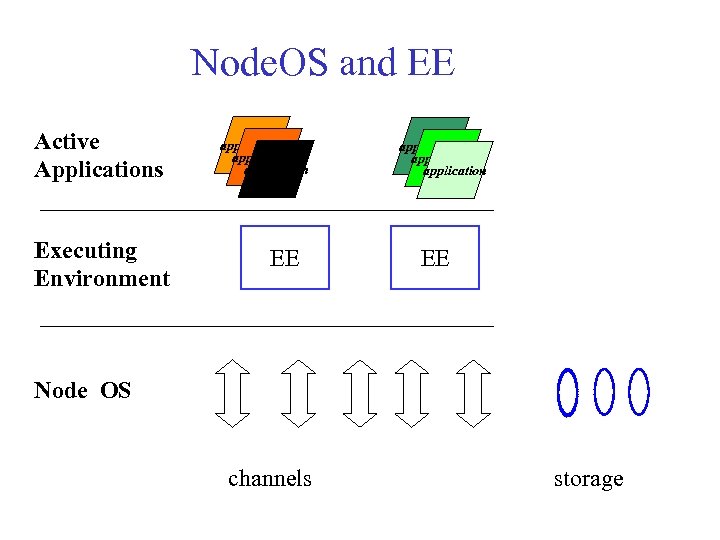 Node. OS and EE Active Applications Executing Environment application application EE Node OS channels storage
Node. OS and EE Active Applications Executing Environment application application EE Node OS channels storage
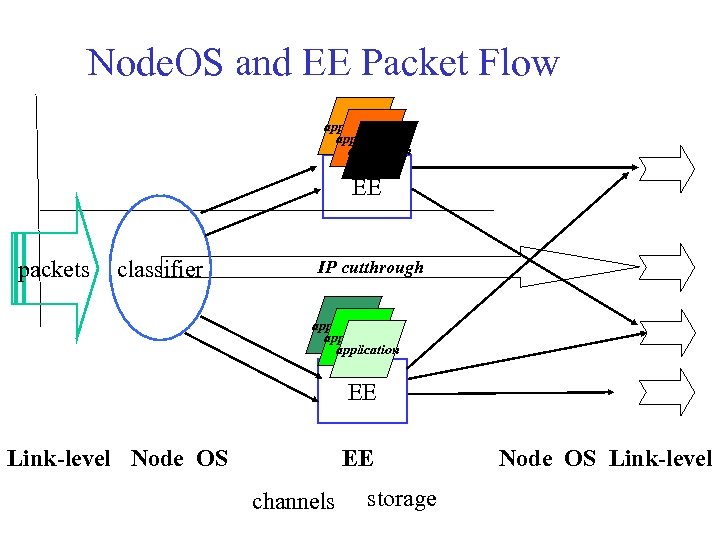 Node. OS and EE Packet Flow application EE packets classifier IP cutthrough application EE Link-level Node OS EE channels storage Node OS Link-level
Node. OS and EE Packet Flow application EE packets classifier IP cutthrough application EE Link-level Node OS EE channels storage Node OS Link-level
 Node. OS • Interfacing the link-level and the EEs • Controls resources: – CPU – memory – communications (channels) • Security • Routing
Node. OS • Interfacing the link-level and the EEs • Controls resources: – CPU – memory – communications (channels) • Security • Routing
 Node. OS Abstracts • Flows - the primary abstraction for accounting, admission control, and scheduling in the system • Thread pool - the primary abstraction for computation • Memory pool - the primary abstraction for memory • Channels - flows create channels to send, receive, and forward packets
Node. OS Abstracts • Flows - the primary abstraction for accounting, admission control, and scheduling in the system • Thread pool - the primary abstraction for computation • Memory pool - the primary abstraction for memory • Channels - flows create channels to send, receive, and forward packets
 Execution Environment • Interface to the Node. OS • The place where the actual active code is being executed • Application to application communication • EE to EE communication • Examples
Execution Environment • Interface to the Node. OS • The place where the actual active code is being executed • Application to application communication • EE to EE communication • Examples
 Node. OS/EE • • Do we really need it? The cost of abstraction? What about high-speed active networks? Channels for local information and control
Node. OS/EE • • Do we really need it? The cost of abstraction? What about high-speed active networks? Channels for local information and control
 Safety and Security • Crucial for deployment • Safety (i. e. robustness to bugs and failures) and security (i. e. against malicious attackers) • Basic tradeoff: flexibility Vs. security – adding more power to the applications can be used by the “bad guys” • Is this a (good) reason to give up progress?
Safety and Security • Crucial for deployment • Safety (i. e. robustness to bugs and failures) and security (i. e. against malicious attackers) • Basic tradeoff: flexibility Vs. security – adding more power to the applications can be used by the “bad guys” • Is this a (good) reason to give up progress?
 Possible Threats • Damage – an active packet damages the Node. OS/EE/networklevel code in the router – an active packet changes code in other active packets – the active router may interfere with the original active packet’s code • Denial of service – an active packet “takes over” a certain resource (CPU, memory) and deny services from other active packets
Possible Threats • Damage – an active packet damages the Node. OS/EE/networklevel code in the router – an active packet changes code in other active packets – the active router may interfere with the original active packet’s code • Denial of service – an active packet “takes over” a certain resource (CPU, memory) and deny services from other active packets
 Possible Threats (2) • Theft – an active packet may access and change information at a node (billing), or information used by other active pockets (passwords) • Compound attack – AN can be used to generate a coordinated attack aimed at a remote router. AN may allow a single attacker to generate traffic to a single destination with volume that is unlimited by the bandwidth of its own connection
Possible Threats (2) • Theft – an active packet may access and change information at a node (billing), or information used by other active pockets (passwords) • Compound attack – AN can be used to generate a coordinated attack aimed at a remote router. AN may allow a single attacker to generate traffic to a single destination with volume that is unlimited by the bandwidth of its own connection
 Security - Enabling Techniques • AAA: • authorization • authentication: someone else vouches for the packet • access control to resources such as the file system • Resource consumption monitoring (with policy based management) • PPC - Proof Carrying Code - the code can prove that it is safe
Security - Enabling Techniques • AAA: • authorization • authentication: someone else vouches for the packet • access control to resources such as the file system • Resource consumption monitoring (with policy based management) • PPC - Proof Carrying Code - the code can prove that it is safe
 Proof-Carrying Code (PCC) Peter Lee and George Necula • PCC is a technique by which a code consumer (e. g. , host) can verify that code provided by an untrusted code producer adheres to a predefined set of safety rules (safety policy). These rules are chosen by the code consumer in such a way that they are sufficient guarantees for safe behavior of programs. • The code producer is required to create a formal safety proof that attests to the fact that the code respects the defined safety policy. The code consumer is able to use a simple and fast proof validator to check, with certainty, that the proof is valid.
Proof-Carrying Code (PCC) Peter Lee and George Necula • PCC is a technique by which a code consumer (e. g. , host) can verify that code provided by an untrusted code producer adheres to a predefined set of safety rules (safety policy). These rules are chosen by the code consumer in such a way that they are sufficient guarantees for safe behavior of programs. • The code producer is required to create a formal safety proof that attests to the fact that the code respects the defined safety policy. The code consumer is able to use a simple and fast proof validator to check, with certainty, that the proof is valid.
 A Secure Active Environment • • Accept and authenticate the incoming packet Identify the sender(s) of the packet Authorize access to the appropriate resources Allow execution based on the authorization and the security policy • Monitor the resource utilization • Encrypt/decrypt code/data as needed • Who should do it: node. OS? EE?
A Secure Active Environment • • Accept and authenticate the incoming packet Identify the sender(s) of the packet Authorize access to the appropriate resources Allow execution based on the authorization and the security policy • Monitor the resource utilization • Encrypt/decrypt code/data as needed • Who should do it: node. OS? EE?
 DARPA Projects • • • ANTS at MIT Smart Packets at BBN Switchware at Upenn and Bellcore Netscript at Columbia Applications: • active reliable multicast, protocol boosters, active congestion control, Internet applications • ABone: a global AN network
DARPA Projects • • • ANTS at MIT Smart Packets at BBN Switchware at Upenn and Bellcore Netscript at Columbia Applications: • active reliable multicast, protocol boosters, active congestion control, Internet applications • ABone: a global AN network
 ANTS (MIT( • ANTS - an Active Node Transfer System – a Java-based toolkit for experimenting with active networks. It provides a node runtime that can participate in an active network, and a protocol programming model that allows users to customize the forwarding of their packets • The first EE to be developed • Uses capsules that do not contain all the code • A code distribution system distributes the code to the different active nodes.
ANTS (MIT( • ANTS - an Active Node Transfer System – a Java-based toolkit for experimenting with active networks. It provides a node runtime that can participate in an active network, and a protocol programming model that allows users to customize the forwarding of their packets • The first EE to be developed • Uses capsules that do not contain all the code • A code distribution system distributes the code to the different active nodes.
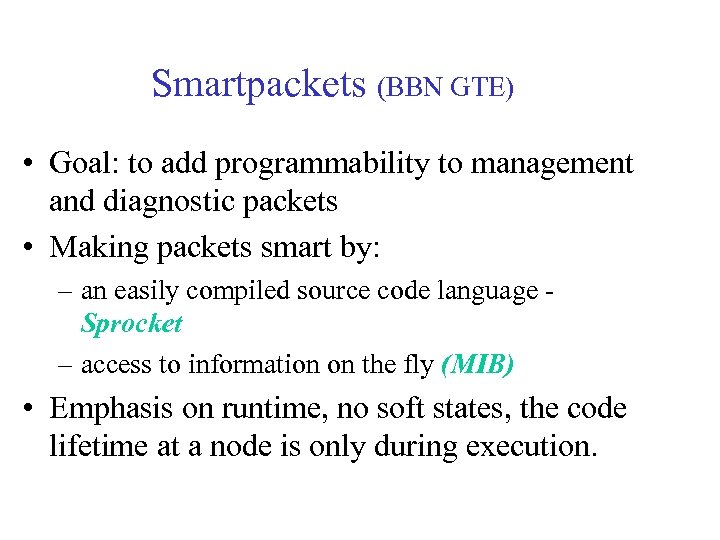 Smartpackets (BBN GTE) • Goal: to add programmability to management and diagnostic packets • Making packets smart by: – an easily compiled source code language Sprocket – access to information on the fly (MIB) • Emphasis on runtime, no soft states, the code lifetime at a node is only during execution.
Smartpackets (BBN GTE) • Goal: to add programmability to management and diagnostic packets • Making packets smart by: – an easily compiled source code language Sprocket – access to information on the fly (MIB) • Emphasis on runtime, no soft states, the code lifetime at a node is only during execution.
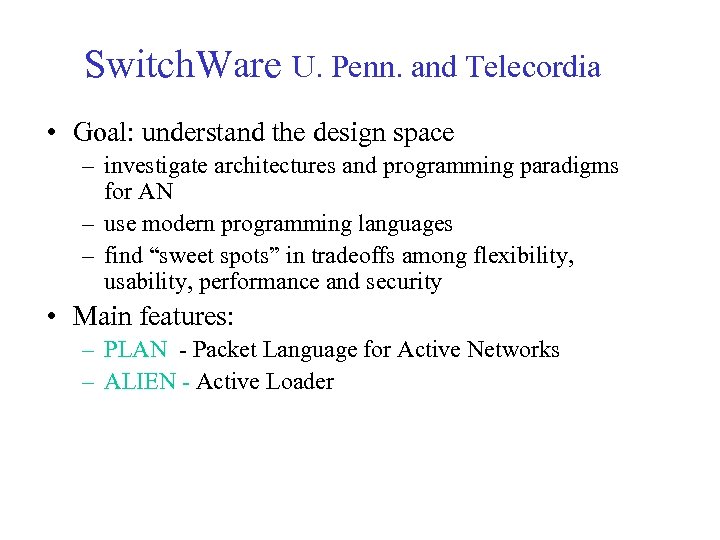 Switch. Ware U. Penn. and Telecordia • Goal: understand the design space – investigate architectures and programming paradigms for AN – use modern programming languages – find “sweet spots” in tradeoffs among flexibility, usability, performance and security • Main features: – PLAN - Packet Language for Active Networks – ALIEN - Active Loader
Switch. Ware U. Penn. and Telecordia • Goal: understand the design space – investigate architectures and programming paradigms for AN – use modern programming languages – find “sweet spots” in tradeoffs among flexibility, usability, performance and security • Main features: – PLAN - Packet Language for Active Networks – ALIEN - Active Loader
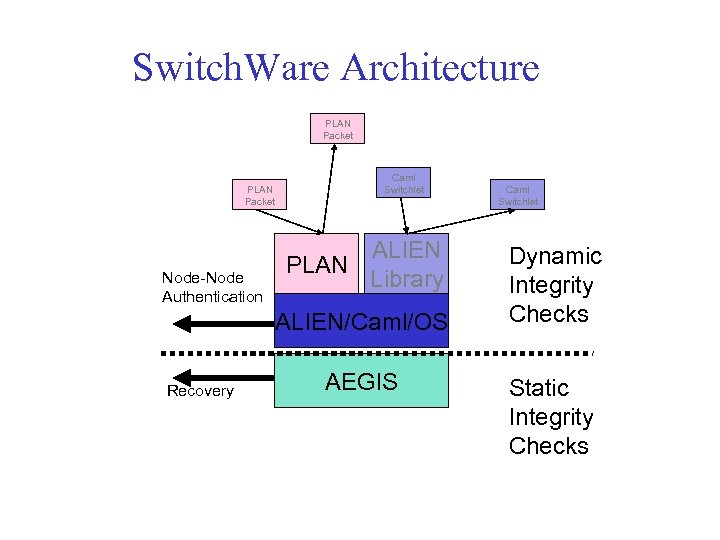 Switch. Ware Architecture PLAN Packet Node-Node Authentication Caml Switchlet ALIEN PLAN Library ALIEN/Caml/OS Recovery AEGIS Caml Switchlet Dynamic Integrity Checks Static Integrity Checks
Switch. Ware Architecture PLAN Packet Node-Node Authentication Caml Switchlet ALIEN PLAN Library ALIEN/Caml/OS Recovery AEGIS Caml Switchlet Dynamic Integrity Checks Static Integrity Checks
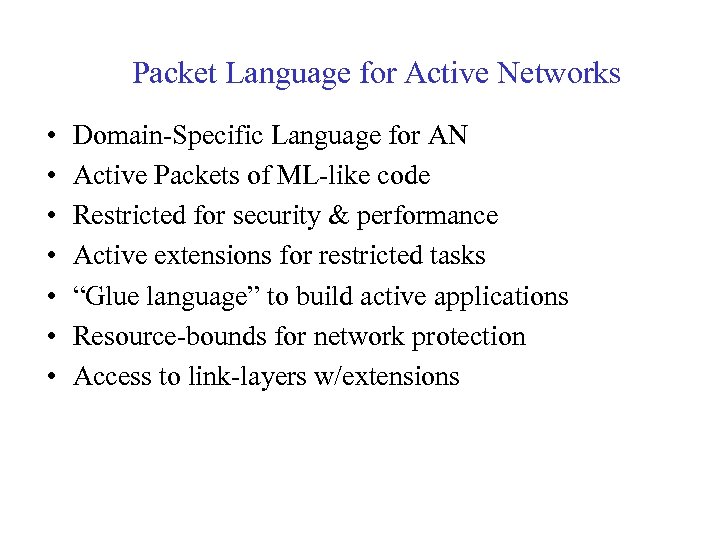 Packet Language for Active Networks • • Domain-Specific Language for AN Active Packets of ML-like code Restricted for security & performance Active extensions for restricted tasks “Glue language” to build active applications Resource-bounds for network protection Access to link-layers w/extensions
Packet Language for Active Networks • • Domain-Specific Language for AN Active Packets of ML-like code Restricted for security & performance Active extensions for restricted tasks “Glue language” to build active applications Resource-bounds for network protection Access to link-layers w/extensions
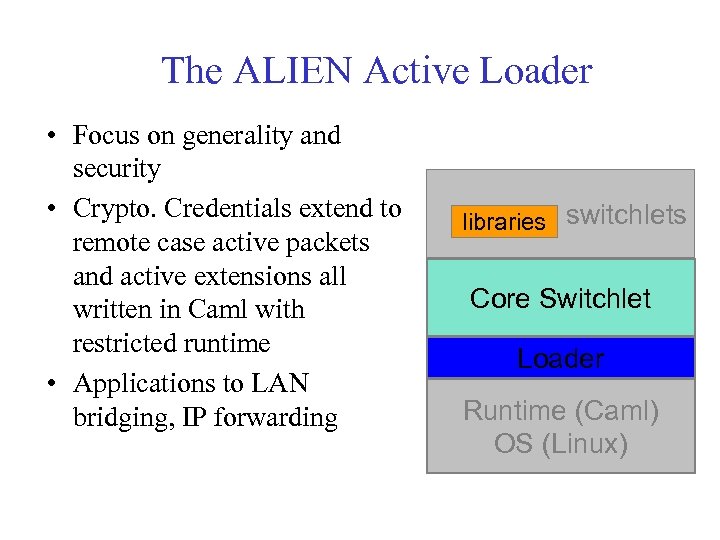 The ALIEN Active Loader • Focus on generality and security • Crypto. Credentials extend to remote case active packets and active extensions all written in Caml with restricted runtime • Applications to LAN bridging, IP forwarding libraries switchlets Core Switchlet Loader Runtime (Caml) OS (Linux)
The ALIEN Active Loader • Focus on generality and security • Crypto. Credentials extend to remote case active packets and active extensions all written in Caml with restricted runtime • Applications to LAN bridging, IP forwarding libraries switchlets Core Switchlet Loader Runtime (Caml) OS (Linux)
 Issues • Packets size: – how much code can fit into a single packet? – offline loading of code • A safe execution of the code – how much control – offline guaranties Vs. runtime verification • Interactions: – packet -- EE – packet -- packet
Issues • Packets size: – how much code can fit into a single packet? – offline loading of code • A safe execution of the code – how much control – offline guaranties Vs. runtime verification • Interactions: – packet -- EE – packet -- packet
 Netscript (Columbia( • A glue language to compose and manage active flow processing applications • Enable significant domain-specific capabilities: – computation over flows • Simplify programming active nets – high-level abstraction of flow processing: end-end composition & coordination • Compiler-generated support of key functions – manageability: security, resource allocation – optimization – map to heterogeneous node architectures from JVM to ASIC/FPLA…
Netscript (Columbia( • A glue language to compose and manage active flow processing applications • Enable significant domain-specific capabilities: – computation over flows • Simplify programming active nets – high-level abstraction of flow processing: end-end composition & coordination • Compiler-generated support of key functions – manageability: security, resource allocation – optimization – map to heterogeneous node architectures from JVM to ASIC/FPLA…
 Applications • Multicast – ARM (at MIT), PANAMA (U. Mass and TASC) • Caching – Adaptive Web Caching (UCLA) • Active congestion control – (USC/ISI, Ga. Tech) • Auctions – (MIT)
Applications • Multicast – ARM (at MIT), PANAMA (U. Mass and TASC) • Caching – Adaptive Web Caching (UCLA) • Active congestion control – (USC/ISI, Ga. Tech) • Auctions – (MIT)
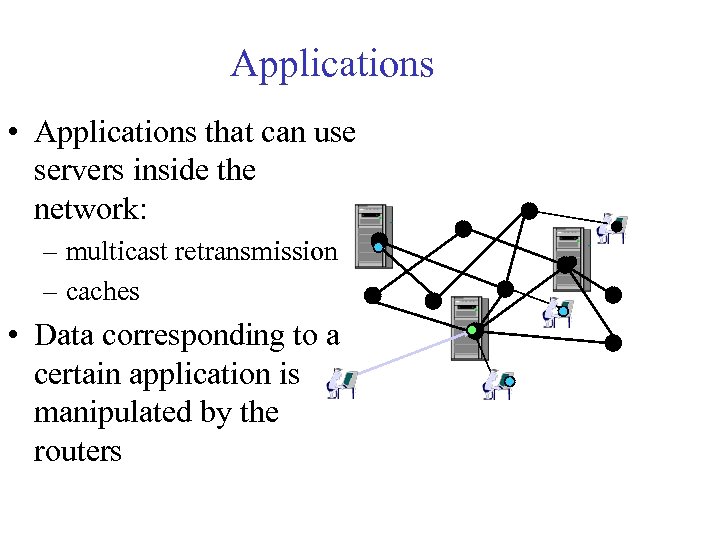 Applications • Applications that can use servers inside the network: – multicast retransmission – caches • Data corresponding to a certain application is manipulated by the routers
Applications • Applications that can use servers inside the network: – multicast retransmission – caches • Data corresponding to a certain application is manipulated by the routers
 ABone Active Network Backbone • An experimental network consisting of nodes from all over the world used to prototype and test new ideas related to Active Networking • ~96 nodes (October 2001) • Assembled from existing links and node, mainly Linux machine with ANetd: – a basic EE for Linux – a way to manage different EEs
ABone Active Network Backbone • An experimental network consisting of nodes from all over the world used to prototype and test new ideas related to Active Networking • ~96 nodes (October 2001) • Assembled from existing links and node, mainly Linux machine with ANetd: – a basic EE for Linux – a way to manage different EEs
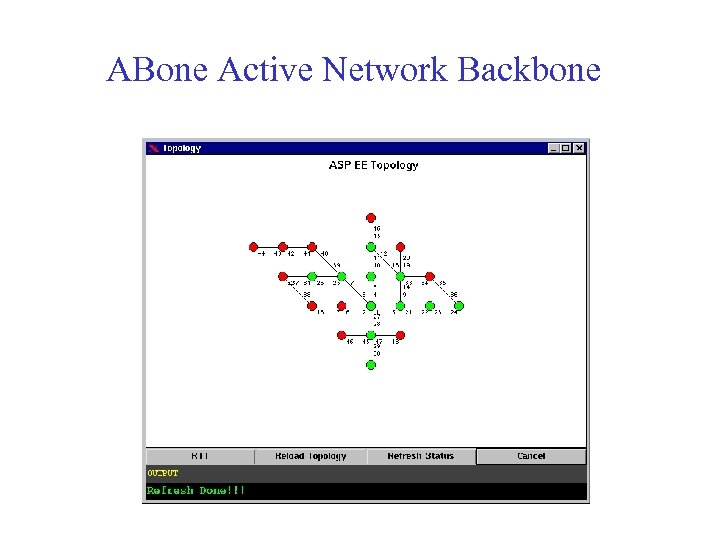 ABone Active Network Backbone
ABone Active Network Backbone
 AN Outside DARPA • IWAN since 1999 (International Working Conference on Active Networks – many of the papers deals with network management • EU research: large investment – FAIN - Future Active IP Networks • Network operators like BT, DT, AT&T, MCI see in the programmable switch/router paradigm a way to: – allow them to program their own networks to achieve better functionality/efficiently over competitors – offer big clients unique custom designed services in a very short time frame – shift some of the revenue opportunities from manufactures to service providers
AN Outside DARPA • IWAN since 1999 (International Working Conference on Active Networks – many of the papers deals with network management • EU research: large investment – FAIN - Future Active IP Networks • Network operators like BT, DT, AT&T, MCI see in the programmable switch/router paradigm a way to: – allow them to program their own networks to achieve better functionality/efficiently over competitors – offer big clients unique custom designed services in a very short time frame – shift some of the revenue opportunities from manufactures to service providers
 What is missing? • Access to the network: – local information: topology, interfaces, load – routing - access to routing tables and manipulation of routing/forwarding tables • Soft states: allowing a truly distributed application to run for a long period of time • Integration with current routers
What is missing? • Access to the network: – local information: topology, interfaces, load – routing - access to routing tables and manipulation of routing/forwarding tables • Soft states: allowing a truly distributed application to run for a long period of time • Integration with current routers
 ABLE (Active Bell Labs Engine) Introduce efficiency to network management using active networks technology • Shorter control loops • Fusion of control messages in the network • Exposing the actual cost to the programmer
ABLE (Active Bell Labs Engine) Introduce efficiency to network management using active networks technology • Shorter control loops • Fusion of control messages in the network • Exposing the actual cost to the programmer
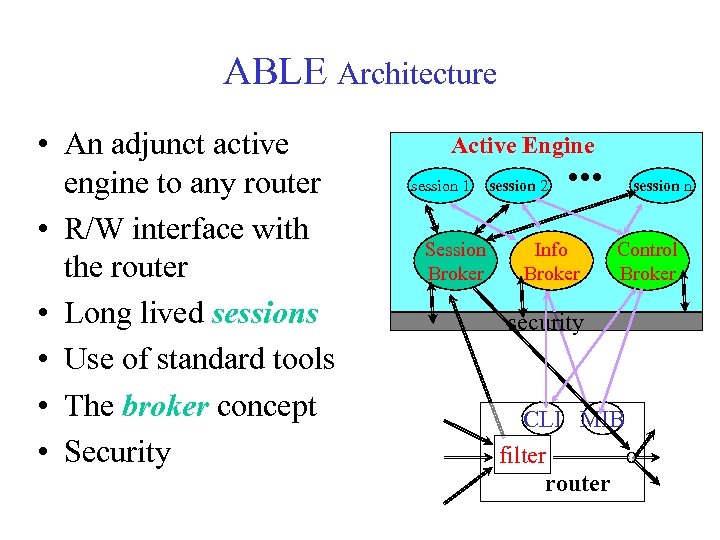 ABLE Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived sessions • Use of standard tools • The broker concept • Security Active Engine session 1 Session Broker session 2 Info Broker session n Control Broker security CLI MIB filter router
ABLE Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived sessions • Use of standard tools • The broker concept • Security Active Engine session 1 Session Broker session 2 Info Broker session n Control Broker security CLI MIB filter router
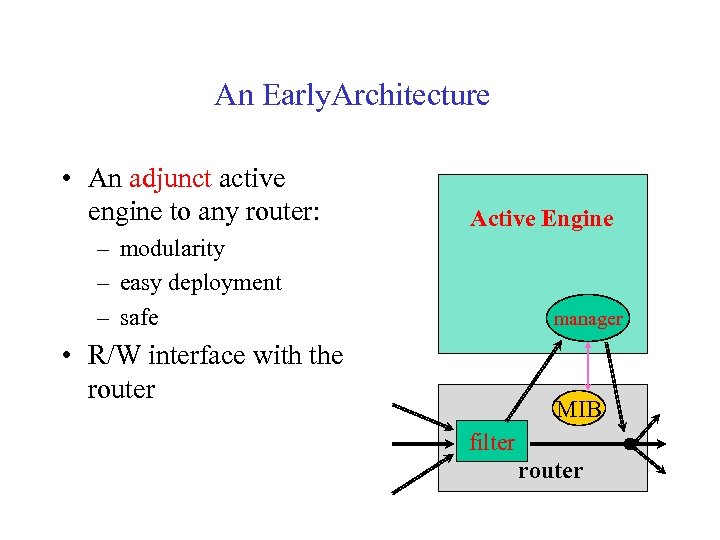 An Early. Architecture • An adjunct active engine to any router: Active Engine – modularity – easy deployment – safe manager • R/W interface with the router MIB filter router
An Early. Architecture • An adjunct active engine to any router: Active Engine – modularity – easy deployment – safe manager • R/W interface with the router MIB filter router
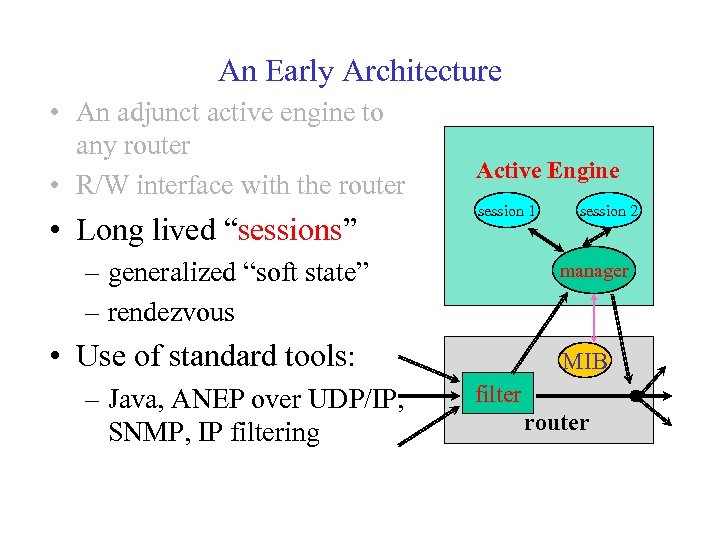 An Early Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived “sessions” Active Engine session 1 – generalized “soft state” – rendezvous manager • Use of standard tools: – Java, ANEP over UDP/IP, SNMP, IP filtering session 2 MIB filter router
An Early Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived “sessions” Active Engine session 1 – generalized “soft state” – rendezvous manager • Use of standard tools: – Java, ANEP over UDP/IP, SNMP, IP filtering session 2 MIB filter router
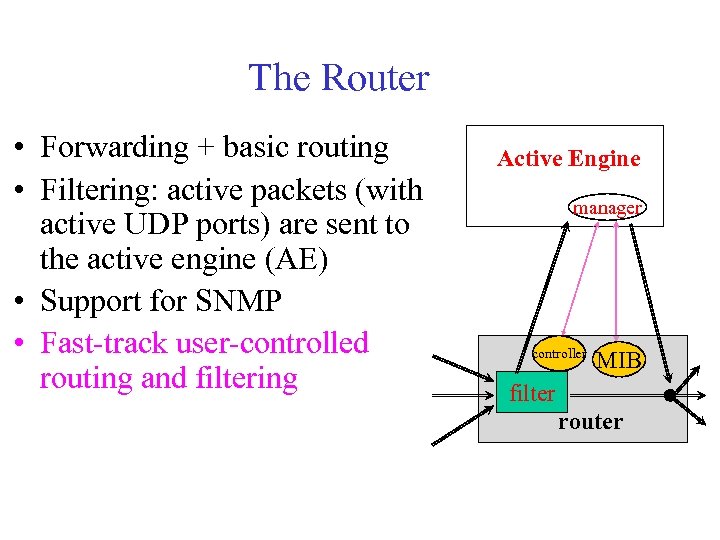 The Router • Forwarding + basic routing • Filtering: active packets (with active UDP ports) are sent to the active engine (AE) • Support for SNMP • Fast-track user-controlled routing and filtering Active Engine manager controller MIB filter router
The Router • Forwarding + basic routing • Filtering: active packets (with active UDP ports) are sent to the active engine (AE) • Support for SNMP • Fast-track user-controlled routing and filtering Active Engine manager controller MIB filter router
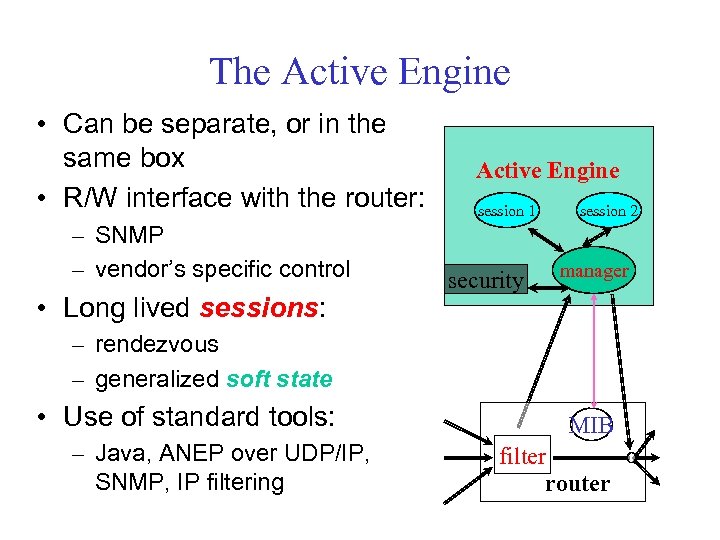 The Active Engine • Can be separate, or in the same box • R/W interface with the router: – SNMP – vendor’s specific control • Long lived sessions: Active Engine session 1 security session 2 manager – rendezvous – generalized soft state • Use of standard tools: – Java, ANEP over UDP/IP, SNMP, IP filtering MIB filter router
The Active Engine • Can be separate, or in the same box • R/W interface with the router: – SNMP – vendor’s specific control • Long lived sessions: Active Engine session 1 security session 2 manager – rendezvous – generalized soft state • Use of standard tools: – Java, ANEP over UDP/IP, SNMP, IP filtering MIB filter router
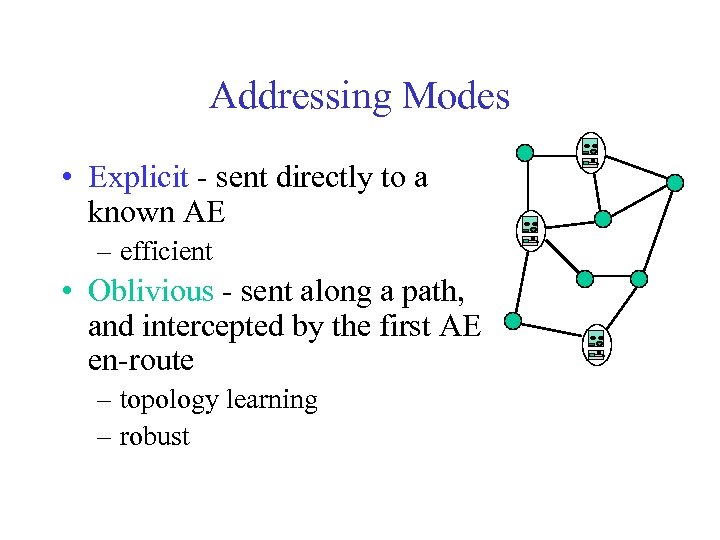 Addressing Modes • Explicit - sent directly to a known AE – efficient • Oblivious - sent along a path, and intercepted by the first AE en-route – topology learning – robust
Addressing Modes • Explicit - sent directly to a known AE – efficient • Oblivious - sent along a path, and intercepted by the first AE en-route – topology learning – robust
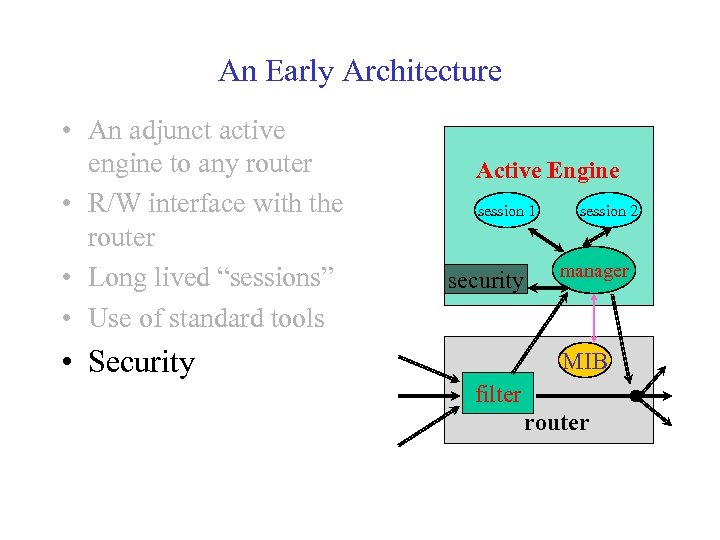 An Early Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived “sessions” • Use of standard tools Active Engine session 1 security • Security session 2 manager MIB filter router
An Early Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived “sessions” • Use of standard tools Active Engine session 1 security • Security session 2 manager MIB filter router
 Safety & Security • The active engine is separate from the router - regular IP traffic is safer • Inside the active engine: – AAA (authentication, authorization, access control) – blocking unauthorized TCP connections – monitoring resource consumption of sessions – Java Security. Manager: blocking native methods and foreign file access
Safety & Security • The active engine is separate from the router - regular IP traffic is safer • Inside the active engine: – AAA (authentication, authorization, access control) – blocking unauthorized TCP connections – monitoring resource consumption of sessions – Java Security. Manager: blocking native methods and foreign file access
 An Application Example: Bottleneck Detection • Currently can be done using the traceroute program: – inefficient and limited in scope (route + timing info) • An active solution: – efficient – versatile – can do much more
An Application Example: Bottleneck Detection • Currently can be done using the traceroute program: – inefficient and limited in scope (route + timing info) • An active solution: – efficient – versatile – can do much more
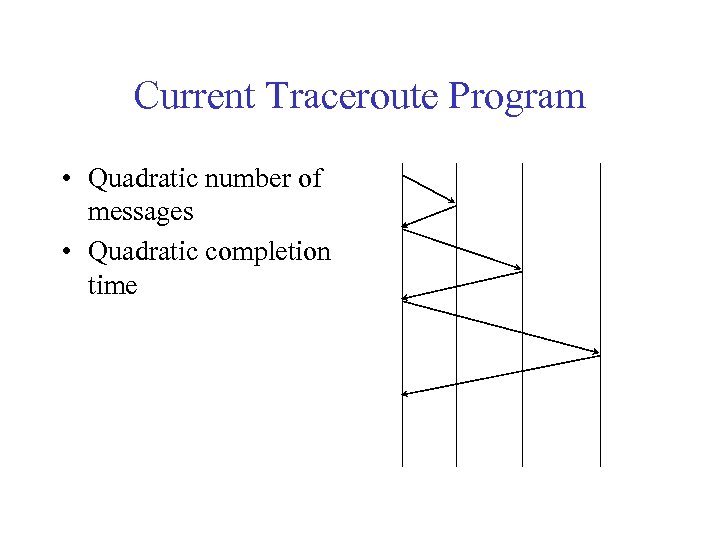 Current Traceroute Program • Quadratic number of messages • Quadratic completion time
Current Traceroute Program • Quadratic number of messages • Quadratic completion time
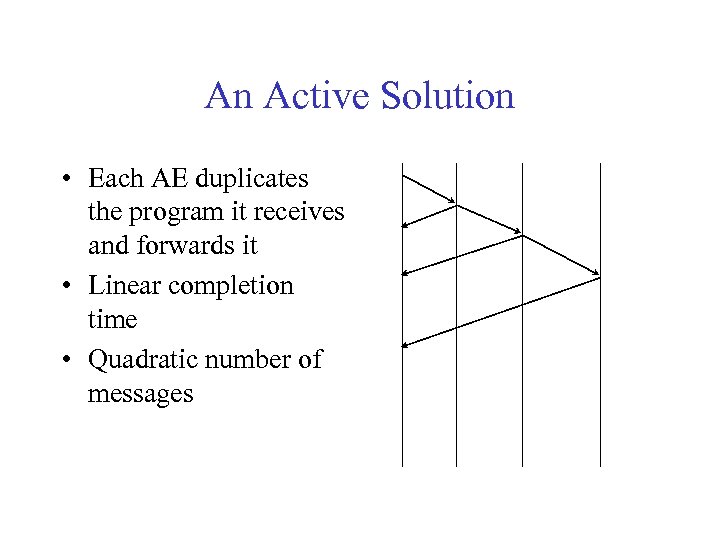 An Active Solution • Each AE duplicates the program it receives and forwards it • Linear completion time • Quadratic number of messages
An Active Solution • Each AE duplicates the program it receives and forwards it • Linear completion time • Quadratic number of messages
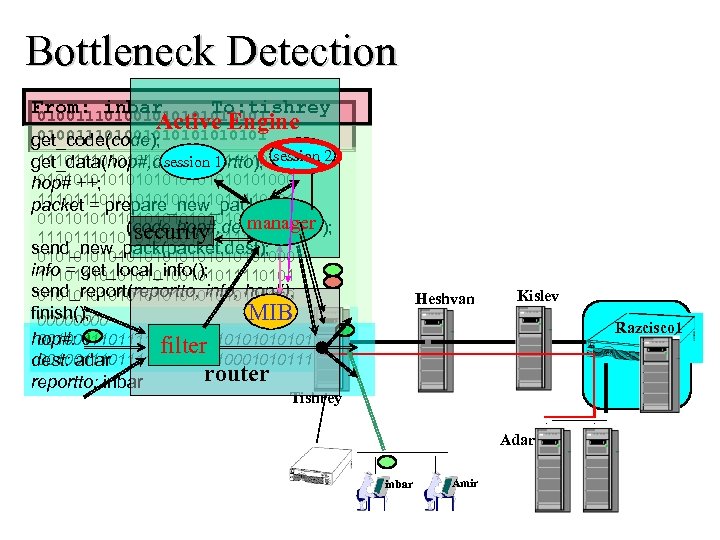 Bottleneck Detection From: inbar To: tishrey 010011101001010101 Active Engine 010011101001010101 get_code(code); 111010100101011110101 session 1 get_data(hop#, dest, reportto); session 2 01010101010101000 hop# ++; 111010100101011110101 packet = prepare_new_packet 01010101010101000 manager (code, hop#, dest, reportto); security 111010100101011110101 send_new_pack(packet, dest); 01010101010101000 info = get_local_info(); 111010100101011110101 send_report(reportto, info, hop#); 01010101010101000 finish(); MIB 0000 hop#: 0 0010011110111010101011 filter 0010011110100010101111 dest: adar router reportto: inbar Heshvan Kislev Razcisco 1 Tishrey Adar inbar Amir
Bottleneck Detection From: inbar To: tishrey 010011101001010101 Active Engine 010011101001010101 get_code(code); 111010100101011110101 session 1 get_data(hop#, dest, reportto); session 2 01010101010101000 hop# ++; 111010100101011110101 packet = prepare_new_packet 01010101010101000 manager (code, hop#, dest, reportto); security 111010100101011110101 send_new_pack(packet, dest); 01010101010101000 info = get_local_info(); 111010100101011110101 send_report(reportto, info, hop#); 01010101010101000 finish(); MIB 0000 hop#: 0 0010011110111010101011 filter 0010011110100010101111 dest: adar router reportto: inbar Heshvan Kislev Razcisco 1 Tishrey Adar inbar Amir
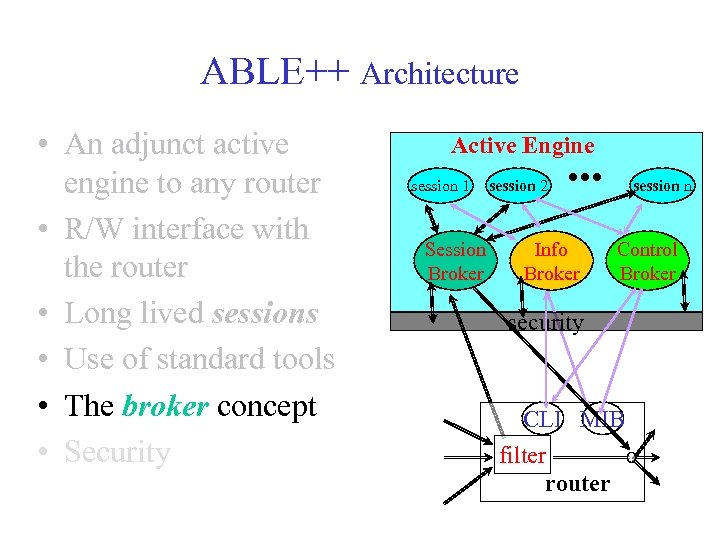 ABLE++ Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived sessions • Use of standard tools • The broker concept • Security Active Engine session 1 Session Broker session 2 Info Broker session n Control Broker security CLI MIB filter router
ABLE++ Architecture • An adjunct active engine to any router • R/W interface with the router • Long lived sessions • Use of standard tools • The broker concept • Security Active Engine session 1 Session Broker session 2 Info Broker session n Control Broker security CLI MIB filter router
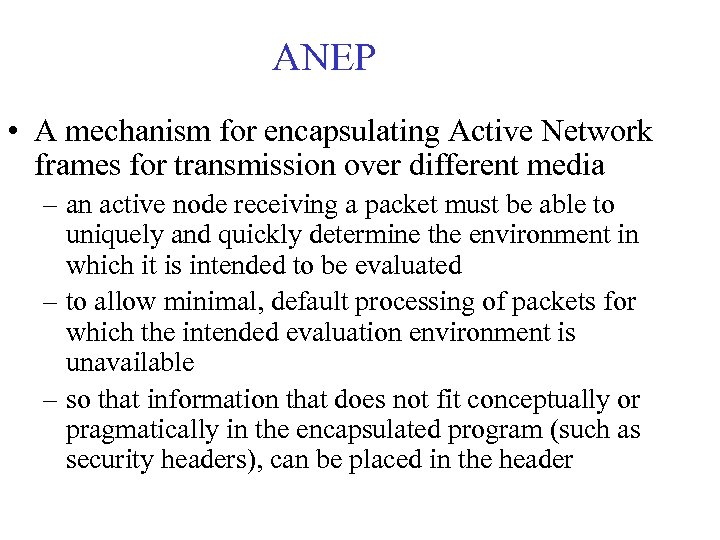 ANEP • A mechanism for encapsulating Active Network frames for transmission over different media – an active node receiving a packet must be able to uniquely and quickly determine the environment in which it is intended to be evaluated – to allow minimal, default processing of packets for which the intended evaluation environment is unavailable – so that information that does not fit conceptually or pragmatically in the encapsulated program (such as security headers), can be placed in the header
ANEP • A mechanism for encapsulating Active Network frames for transmission over different media – an active node receiving a packet must be able to uniquely and quickly determine the environment in which it is intended to be evaluated – to allow minimal, default processing of packets for which the intended evaluation environment is unavailable – so that information that does not fit conceptually or pragmatically in the encapsulated program (such as security headers), can be placed in the header
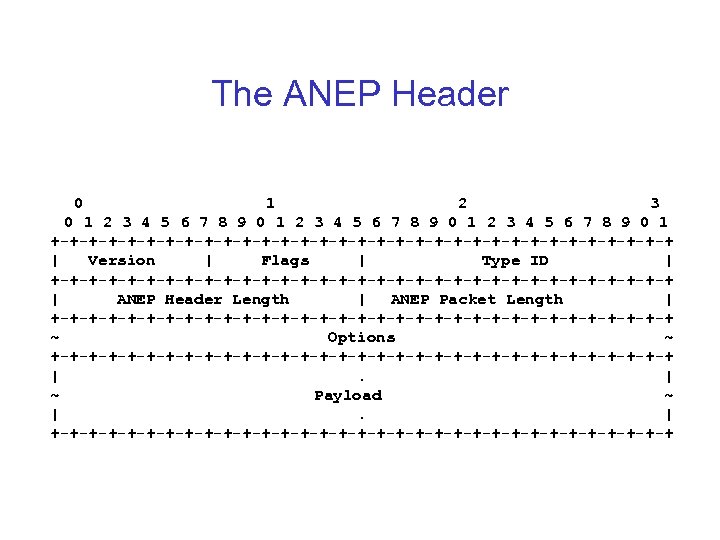 The ANEP Header 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Version | Flags | Type ID | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | ANEP Header Length | ANEP Packet Length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ ~ Options ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ |. | ~ Payload ~ |. | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
The ANEP Header 0 1 2 3 4 5 6 7 8 9 0 1 +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | Version | Flags | Type ID | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ | ANEP Header Length | ANEP Packet Length | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ ~ Options ~ +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+ |. | ~ Payload ~ |. | +-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+-+
 ANEP Header Fields • The Version field indicates the header format in use • Only the most significant bit of the flag field is used. It indicates what the node should do if it does not recognize the Type ID: 0 - try to forward, 1 - discard • The ANEP Header Length field specifies the length of the ANEP header in 32 bit words. If no options are included in the packet, then its value must be 2 • The ANEP Packet Length field specifies the length of the entire packet, including the packet payload, in octets
ANEP Header Fields • The Version field indicates the header format in use • Only the most significant bit of the flag field is used. It indicates what the node should do if it does not recognize the Type ID: 0 - try to forward, 1 - discard • The ANEP Header Length field specifies the length of the ANEP header in 32 bit words. If no options are included in the packet, then its value must be 2 • The ANEP Packet Length field specifies the length of the entire packet, including the packet payload, in octets
 ANEP Header Fields (2) • The Type ID field indicates the evaluation environment (EE) of the message • The proper authority for assigning Type ID values to interested parties is the Active Networks Assigned Numbers Authority (ANANA) (61 -64) • The Type ID value 0 is reserved for possible future network layer information and error messages • If the value contained in this field is not recognized, the node should check the value of the most significant bit of the Flags field when deciding how to handle the packet
ANEP Header Fields (2) • The Type ID field indicates the evaluation environment (EE) of the message • The proper authority for assigning Type ID values to interested parties is the Active Networks Assigned Numbers Authority (ANANA) (61 -64) • The Type ID value 0 is reserved for possible future network layer information and error messages • If the value contained in this field is not recognized, the node should check the value of the most significant bit of the Flags field when deciding how to handle the packet
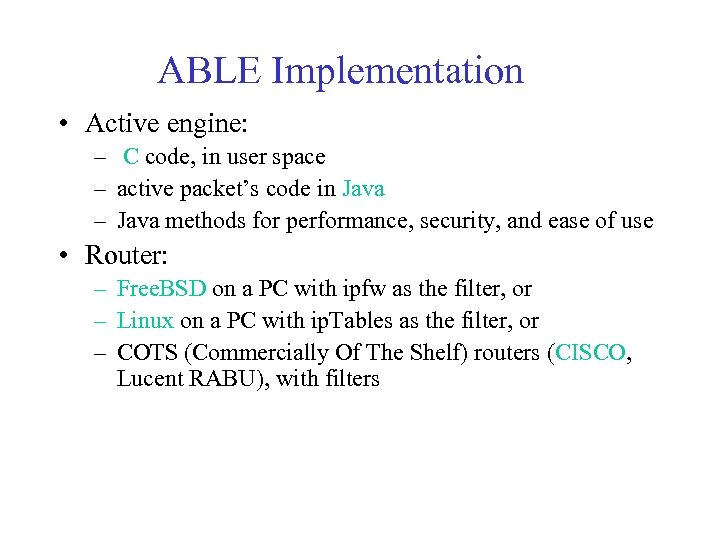 ABLE Implementation • Active engine: – C code, in user space – active packet’s code in Java – Java methods for performance, security, and ease of use • Router: – Free. BSD on a PC with ipfw as the filter, or – Linux on a PC with ip. Tables as the filter, or – COTS (Commercially Of The Shelf) routers (CISCO, Lucent RABU), with filters
ABLE Implementation • Active engine: – C code, in user space – active packet’s code in Java – Java methods for performance, security, and ease of use • Router: – Free. BSD on a PC with ipfw as the filter, or – Linux on a PC with ip. Tables as the filter, or – COTS (Commercially Of The Shelf) routers (CISCO, Lucent RABU), with filters
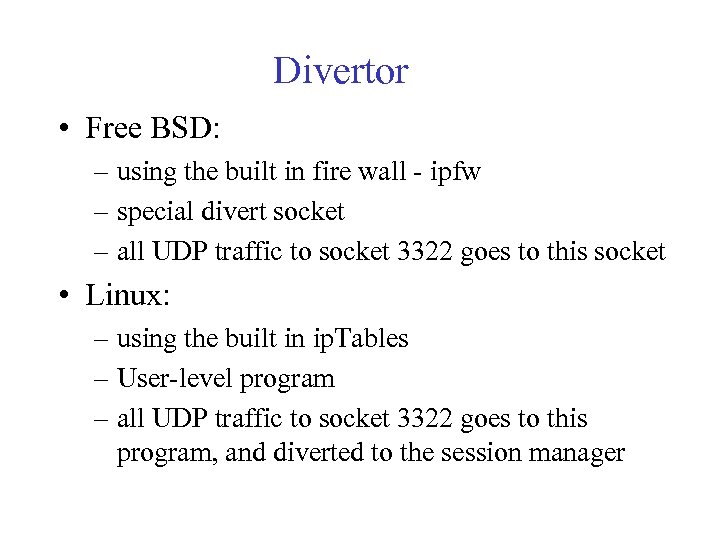 Divertor • Free BSD: – using the built in fire wall - ipfw – special divert socket – all UDP traffic to socket 3322 goes to this socket • Linux: – using the built in ip. Tables – User-level program – all UDP traffic to socket 3322 goes to this program, and diverted to the session manager
Divertor • Free BSD: – using the built in fire wall - ipfw – special divert socket – all UDP traffic to socket 3322 goes to this socket • Linux: – using the built in ip. Tables – User-level program – all UDP traffic to socket 3322 goes to this program, and diverted to the session manager
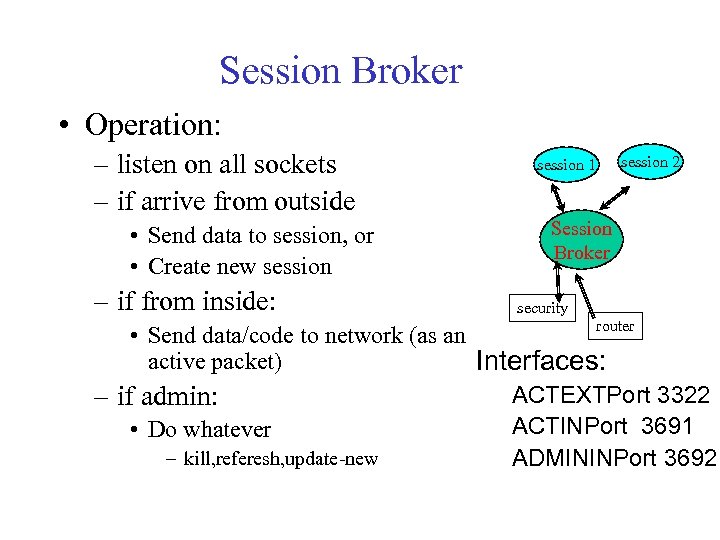 Session Broker • Operation: – listen on all sockets – if arrive from outside • Send data to session, or • Create new session – if from inside: session 1 session 2 Session Broker security router • Send data/code to network (as an active packet) Interfaces: ACTEXTPort 3322 – if admin: ACTINPort 3691 • Do whatever – kill, referesh, update-new ADMININPort 3692
Session Broker • Operation: – listen on all sockets – if arrive from outside • Send data to session, or • Create new session – if from inside: session 1 session 2 Session Broker security router • Send data/code to network (as an active packet) Interfaces: ACTEXTPort 3322 – if admin: ACTINPort 3691 • Do whatever – kill, referesh, update-new ADMININPort 3692
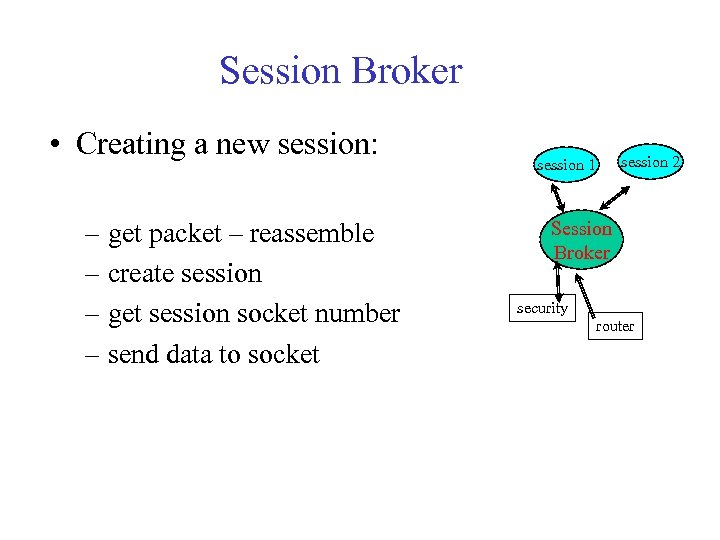 Session Broker • Creating a new session: – get packet – reassemble – create session – get session socket number – send data to socket session 2 session 1 Session Broker security router
Session Broker • Creating a new session: – get packet – reassemble – create session – get session socket number – send data to socket session 2 session 1 Session Broker security router
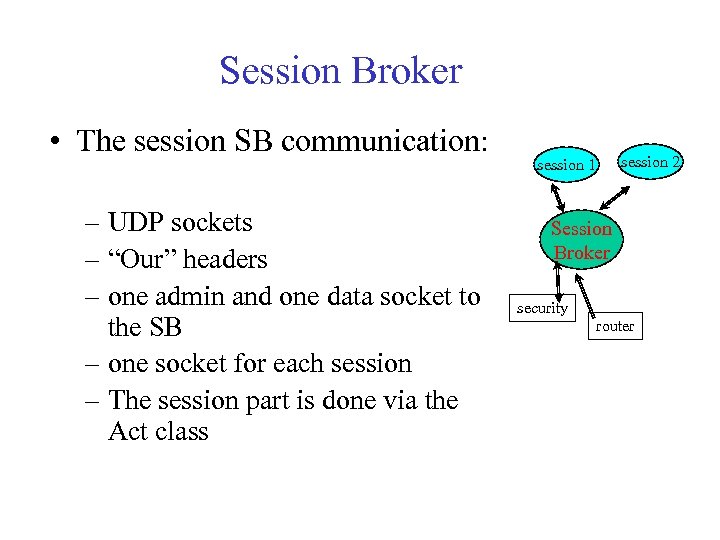 Session Broker • The session SB communication: – UDP sockets – “Our” headers – one admin and one data socket to the SB – one socket for each session – The session part is done via the Act class session 2 session 1 Session Broker security router
Session Broker • The session SB communication: – UDP sockets – “Our” headers – one admin and one data socket to the SB – one socket for each session – The session part is done via the Act class session 2 session 1 Session Broker security router
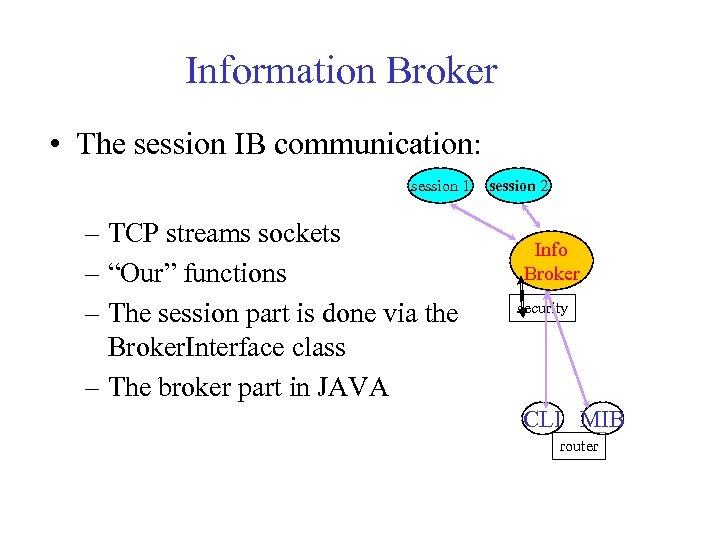 Information Broker • The session IB communication: session 1 – TCP streams sockets – “Our” functions – The session part is done via the Broker. Interface class – The broker part in JAVA session 2 Info Broker security CLI MIB router
Information Broker • The session IB communication: session 1 – TCP streams sockets – “Our” functions – The session part is done via the Broker. Interface class – The broker part in JAVA session 2 Info Broker security CLI MIB router
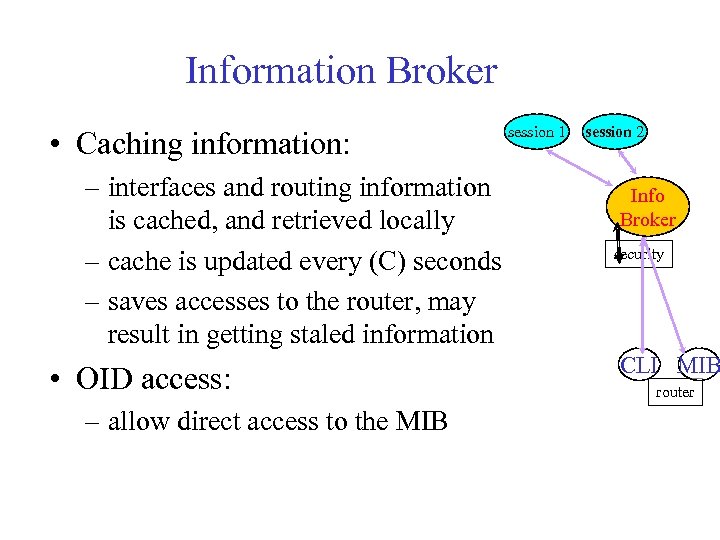 Information Broker • Caching information: – interfaces and routing information is cached, and retrieved locally – cache is updated every (C) seconds – saves accesses to the router, may result in getting staled information • OID access: – allow direct access to the MIB session 1 session 2 Info Broker security CLI MIB router
Information Broker • Caching information: – interfaces and routing information is cached, and retrieved locally – cache is updated every (C) seconds – saves accesses to the router, may result in getting staled information • OID access: – allow direct access to the MIB session 1 session 2 Info Broker security CLI MIB router
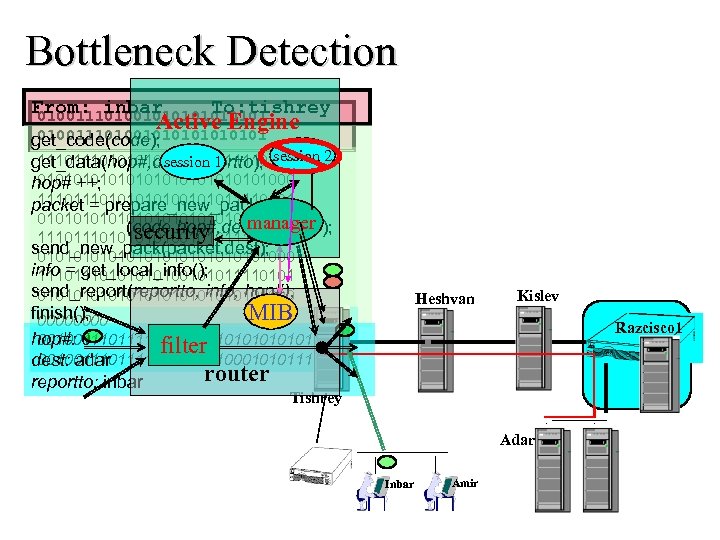 Bottleneck Detection From: inbar To: tishrey 010011101001010101 Active Engine 010011101001010101 get_code(code); 111010100101011110101 session 1 get_data(hop#, dest, reportto); session 2 01010101010101000 hop# ++; 111010100101011110101 packet = prepare_new_packet 01010101010101000 manager (code, hop#, dest, reportto); security 111010100101011110101 send_new_pack(packet, dest); 01010101010101000 info = get_local_info(); 111010100101011110101 send_report(reportto, info, hop#); 01010101010101000 finish(); MIB 0000 hop#: 0 0010011110111010101011 filter 0010011110100010101111 dest: adar router reportto: inbar Heshvan Kislev Razcisco 1 Tishrey Adar Inbar Amir
Bottleneck Detection From: inbar To: tishrey 010011101001010101 Active Engine 010011101001010101 get_code(code); 111010100101011110101 session 1 get_data(hop#, dest, reportto); session 2 01010101010101000 hop# ++; 111010100101011110101 packet = prepare_new_packet 01010101010101000 manager (code, hop#, dest, reportto); security 111010100101011110101 send_new_pack(packet, dest); 01010101010101000 info = get_local_info(); 111010100101011110101 send_report(reportto, info, hop#); 01010101010101000 finish(); MIB 0000 hop#: 0 0010011110111010101011 filter 0010011110100010101111 dest: adar router reportto: inbar Heshvan Kislev Razcisco 1 Tishrey Adar Inbar Amir
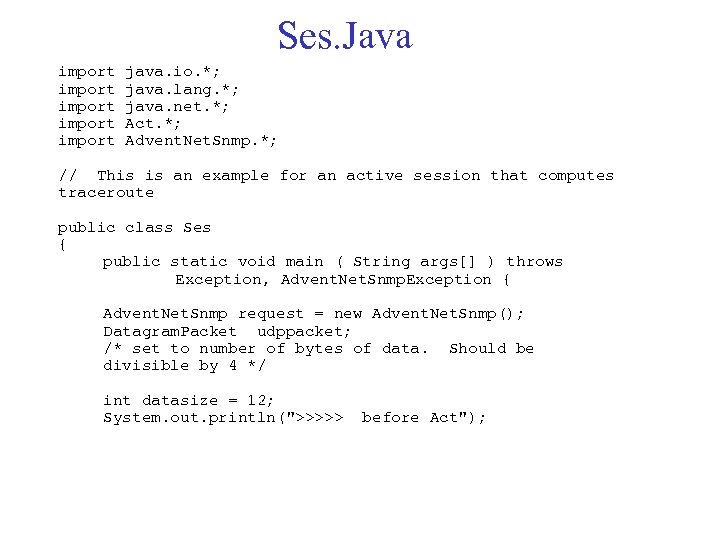 Ses. Java import import java. io. *; java. lang. *; java. net. *; Act. *; Advent. Net. Snmp. *; // This is an example for an active session that computes traceroute public class Ses { public static void main ( String args[] ) throws Exception, Advent. Net. Snmp. Exception { Advent. Net. Snmp request = new Advent. Net. Snmp(); Datagram. Packet udppacket; /* set to number of bytes of data. Should be divisible by 4 */ int datasize = 12; System. out. println(">>>>> before Act");
Ses. Java import import java. io. *; java. lang. *; java. net. *; Act. *; Advent. Net. Snmp. *; // This is an example for an active session that computes traceroute public class Ses { public static void main ( String args[] ) throws Exception, Advent. Net. Snmp. Exception { Advent. Net. Snmp request = new Advent. Net. Snmp(); Datagram. Packet udppacket; /* set to number of bytes of data. Should be divisible by 4 */ int datasize = 12; System. out. println(">>>>> before Act");
>>>> After Act");" src="https://present5.com/presentation/ced0b0b35974d10906580687ff7cb547/image-85.jpg" alt="Ses. Java Act session = new Act(datasize * -1); System. out. println(">>>>> After Act");" />
Ses. Java Act session = new Act(datasize * -1); System. out. println(">>>>> After Act"); byte[] p = session. get. Prog(); byte[] v = session. get. Init. Vars(); int[] senderip = new int[4]; byte[] destip = new byte[4]; byte[] udpmsg ; // get original sender IP address for (int i=0; i<4; i++) senderip[i] = (int) ((v[i] < 0 ) ? v[i]+256 : v[i]); String sendername = Integer. to. String(senderip[0]) + ". " + Integer. to. String(senderip[1]) + ". " + Integer. to. String(senderip[2]) + ". " + Integer. to. String(senderip[3]); // get target IP address System. out. println("Destination IP address"); for (int i=0; i<4; i++) {destip[i] = v[i+4]; System. out. println(destip[i] + ". "); } // get hop number int hopnum = (int) v[8]; System. out. println("Hop number" + hopnum); int dummy = (int) v[9];
![Ses. Java // prepare new message if (v[8]>127) System. out. println( Ses. Java // prepare new message if (v[8]>127) System. out. println(](https://present5.com/presentation/ced0b0b35974d10906580687ff7cb547/image-86.jpg) Ses. Java // prepare new message if (v[8]>127) System. out. println("too big. . "); else v[8]++; // send new message byte[] newpck = new byte[p. length+datasize]; for (int i=0; i
Ses. Java // prepare new message if (v[8]>127) System. out. println("too big. . "); else v[8]++; // send new message byte[] newpck = new byte[p. length+datasize]; for (int i=0; i
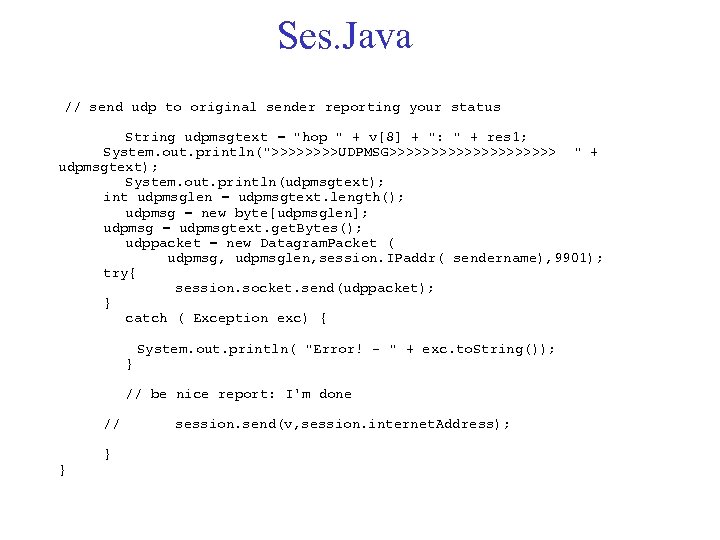 Ses. Java // send udp to original sender reporting your status String udpmsgtext = "hop " + v[8] + ": " + res 1; System. out. println(">>>>UDPMSG>>>>>>>>>> " + udpmsgtext); System. out. println(udpmsgtext); int udpmsglen = udpmsgtext. length(); udpmsg = new byte[udpmsglen]; udpmsg = udpmsgtext. get. Bytes(); udppacket = new Datagram. Packet ( udpmsg, udpmsglen, session. IPaddr( sendername), 9901); try{ session. socket. send(udppacket); } catch ( Exception exc) { } System. out. println( "Error! - " + exc. to. String()); // be nice report: I'm done // } } session. send(v, session. internet. Address);
Ses. Java // send udp to original sender reporting your status String udpmsgtext = "hop " + v[8] + ": " + res 1; System. out. println(">>>>UDPMSG>>>>>>>>>> " + udpmsgtext); System. out. println(udpmsgtext); int udpmsglen = udpmsgtext. length(); udpmsg = new byte[udpmsglen]; udpmsg = udpmsgtext. get. Bytes(); udppacket = new Datagram. Packet ( udpmsg, udpmsglen, session. IPaddr( sendername), 9901); try{ session. socket. send(udppacket); } catch ( Exception exc) { } System. out. println( "Error! - " + exc. to. String()); // be nice report: I'm done // } } session. send(v, session. internet. Address);
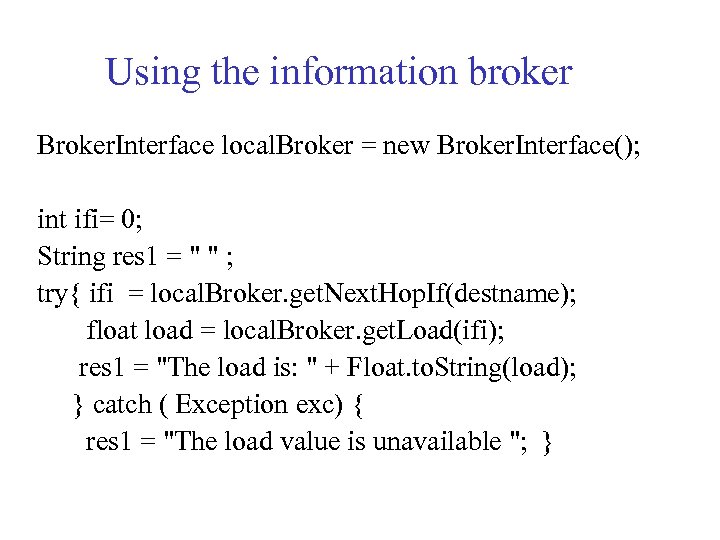 Using the information broker Broker. Interface local. Broker = new Broker. Interface(); int ifi= 0; String res 1 = " " ; try{ ifi = local. Broker. get. Next. Hop. If(destname); float load = local. Broker. get. Load(ifi); res 1 = "The load is: " + Float. to. String(load); } catch ( Exception exc) { res 1 = "The load value is unavailable "; }
Using the information broker Broker. Interface local. Broker = new Broker. Interface(); int ifi= 0; String res 1 = " " ; try{ ifi = local. Broker. get. Next. Hop. If(destname); float load = local. Broker. get. Load(ifi); res 1 = "The load is: " + Float. to. String(load); } catch ( Exception exc) { res 1 = "The load value is unavailable "; }


