3420154169616de4109be17777719e2f.ppt
- Количество слайдов: 17
 The Rise of Standards in Security Roger L. Kay Founder and President k@ndpta. com
The Rise of Standards in Security Roger L. Kay Founder and President k@ndpta. com
 Agenda • • • Why standards? Arguments against Arguments for Examples of major deployments TPM forecast Conclusions
Agenda • • • Why standards? Arguments against Arguments for Examples of major deployments TPM forecast Conclusions
 Why Standards? • Most important is universal agreement • Trusted Computing Group (TCG): best overall technical solution with broad backing • Microsoft — Bit. Locker • Intel — Core logic? • Long list of OEMs and applications – Acer, ASUS, Dell, Gateway, Fujitsu, Lenovo, HP, Intel, Mitsubishi, Motion, MPC, NEC, Samsung, Sony, Toshiba – white box, gaming, hard drives, embedded • Mostly commercial notebooks for now
Why Standards? • Most important is universal agreement • Trusted Computing Group (TCG): best overall technical solution with broad backing • Microsoft — Bit. Locker • Intel — Core logic? • Long list of OEMs and applications – Acer, ASUS, Dell, Gateway, Fujitsu, Lenovo, HP, Intel, Mitsubishi, Motion, MPC, NEC, Samsung, Sony, Toshiba – white box, gaming, hard drives, embedded • Mostly commercial notebooks for now
 Two Arguments Against TCG • System dynamics do not promote development – No user pull; all vendor push • Shipments ≠ Deployments – Ecosystem doesn’t exist to support broad usage
Two Arguments Against TCG • System dynamics do not promote development – No user pull; all vendor push • Shipments ≠ Deployments – Ecosystem doesn’t exist to support broad usage
 Natural Selection • What good is half a wing? – Insects, pterosaurs, birds, bats developed flight – A fin is a limb is a wing – Scales to feathers: warmth, display, protection, stealth – Answer: gliding — squirrel’s tail aids jumping • How do complex eye structures evolve? – Answer: from simple ones
Natural Selection • What good is half a wing? – Insects, pterosaurs, birds, bats developed flight – A fin is a limb is a wing – Scales to feathers: warmth, display, protection, stealth – Answer: gliding — squirrel’s tail aids jumping • How do complex eye structures evolve? – Answer: from simple ones
 TPMs are Useful on Their Own • User authentication • Password management • File and folder encryption
TPMs are Useful on Their Own • User authentication • Password management • File and folder encryption
 Slow Deployment • Some merit to shipments ≠ deployments • But deployments are rolling out • Education is bringing the value of TCG to light • Tools are proliferating
Slow Deployment • Some merit to shipments ≠ deployments • But deployments are rolling out • Education is bringing the value of TCG to light • Tools are proliferating
 Help is on the Way • Centralized remote deployment and management tools (e. g. , Wave Systems’s ERAS) • TPM is used for platform access, data protection, secure messaging, and network security • Real time enforcement of employee policy through Active Directory – Ex. : If local TPM is informed of being removed from AD, user is cut off instantly • Standardized elements (e. g. , MS and TPM) based on root of trust secure identities and access
Help is on the Way • Centralized remote deployment and management tools (e. g. , Wave Systems’s ERAS) • TPM is used for platform access, data protection, secure messaging, and network security • Real time enforcement of employee policy through Active Directory – Ex. : If local TPM is informed of being removed from AD, user is cut off instantly • Standardized elements (e. g. , MS and TPM) based on root of trust secure identities and access
 Real World Examples • • Pharmaceutical company Pizza franchise Automobile rental Health care in Japan • Government & regulatory
Real World Examples • • Pharmaceutical company Pizza franchise Automobile rental Health care in Japan • Government & regulatory
 Pharmaceutical Company • • 20, 000 seats Who is connecting? Vulnerabilities: trade secrets and legal liabilities With VPN over public network, put TPMs on all clients • Access dependent on digital certificate • Verifies both user and machine • Hardware and software from Lenovo
Pharmaceutical Company • • 20, 000 seats Who is connecting? Vulnerabilities: trade secrets and legal liabilities With VPN over public network, put TPMs on all clients • Access dependent on digital certificate • Verifies both user and machine • Hardware and software from Lenovo
 Pizza Franchise • Hundreds of seats • Stores communicate sensitive information to HQ over public network • TPMs secure passwords and certificates • Email, PIM, bank access, credit cards encrypted • Integrated into MS Office; single icon click • Multifactor for some; single for others • Hardware by Dell; software by Wave Systems
Pizza Franchise • Hundreds of seats • Stores communicate sensitive information to HQ over public network • TPMs secure passwords and certificates • Email, PIM, bank access, credit cards encrypted • Integrated into MS Office; single icon click • Multifactor for some; single for others • Hardware by Dell; software by Wave Systems
 Car Rental Firm • Tens of thousands of seats • Local caching of sensitive customer data between transmissions – Limited expertise and language barriers • Simple deployment scripts to enable TPMs • Three steps: – Encrypt cached data – Auth. user & system to server with PKI bound to TPM – Flush cached data after synchronization • HP hardware and software
Car Rental Firm • Tens of thousands of seats • Local caching of sensitive customer data between transmissions – Limited expertise and language barriers • Simple deployment scripts to enable TPMs • Three steps: – Encrypt cached data – Auth. user & system to server with PKI bound to TPM – Flush cached data after synchronization • HP hardware and software
 Japanese Health Care Projects • Obligation to preserve data; METI funded • Public network, home-based patients • Distributed care givers – Field workers, hospitals, labs, medical databases, nursing records • • Differing levels of access require various auth. Hitachi’s TPM-based system for home health care IBM’s Trusted Virtual Domains Fujitsu’s TNC deployment verifies HW and app config for session of broadband telemedicine
Japanese Health Care Projects • Obligation to preserve data; METI funded • Public network, home-based patients • Distributed care givers – Field workers, hospitals, labs, medical databases, nursing records • • Differing levels of access require various auth. Hitachi’s TPM-based system for home health care IBM’s Trusted Virtual Domains Fujitsu’s TNC deployment verifies HW and app config for session of broadband telemedicine
 Government & Regulatory • National Security Agency – Full drive encryption – TCG for compatibility • U. S. Army – Network Enterprise Technology Command now requires TPM 1. 2 on new computers • F. D. I. C. – Promotes TPM usage to member banks
Government & Regulatory • National Security Agency – Full drive encryption – TCG for compatibility • U. S. Army – Network Enterprise Technology Command now requires TPM 1. 2 on new computers • F. D. I. C. – Promotes TPM usage to member banks
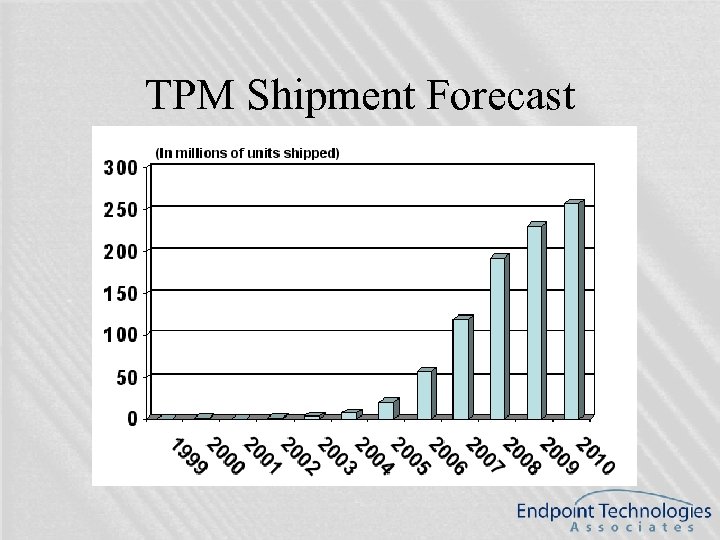 TPM Shipment Forecast
TPM Shipment Forecast
 Conclusions • Vendors are pushing, but users are pulling, too • Real world deployments are taking off • Working with standardized elements is in everyone’s best interest • Root of trust can anchor larger elements • Once the platforms are in place, more elegant structures can be erected • Trusted computing is real and it’s here
Conclusions • Vendors are pushing, but users are pulling, too • Real world deployments are taking off • Working with standardized elements is in everyone’s best interest • Root of trust can anchor larger elements • Once the platforms are in place, more elegant structures can be erected • Trusted computing is real and it’s here
 Questions?
Questions?


