3d7810b0f656f490d357fc03f1aaf64d.ppt
- Количество слайдов: 23
 The Italian Academic Community’s Electronic Voting System Pierluigi Bonetti Lisbon, May 2000
The Italian Academic Community’s Electronic Voting System Pierluigi Bonetti Lisbon, May 2000
 What is CINECA üA Consortium of 15 Italian Universities ü Mission: to provide the most advanced computing and networking services to universities and industries ü Founded in 1969 ü About 150 full time researchers
What is CINECA üA Consortium of 15 Italian Universities ü Mission: to provide the most advanced computing and networking services to universities and industries ü Founded in 1969 ü About 150 full time researchers
 CINECA resources ü Cray T 3 E - 256 nodes ü IBM SP/2 - 32 nodes ü IBM SP/3 - 8 nodes ü SGI Onyx 2 ü SGI Origin 2000 ü SGI Challenge L-2 ü Gigabit backbone LAN ü 10+ Mbps connection to Internet ü The first and unique Virtual Theatre in Italy
CINECA resources ü Cray T 3 E - 256 nodes ü IBM SP/2 - 32 nodes ü IBM SP/3 - 8 nodes ü SGI Onyx 2 ü SGI Origin 2000 ü SGI Challenge L-2 ü Gigabit backbone LAN ü 10+ Mbps connection to Internet ü The first and unique Virtual Theatre in Italy
 How Italian Universities recruit teaching staff ü When a University offers a position, an evaluation committee is needed ü Members of the committee have to be elected amongst all the teaching staff in all the Italian Universities belonging to the scientific discipline related to the position offered ü Each offered position, therefore, requires a nation-wide election (!)
How Italian Universities recruit teaching staff ü When a University offers a position, an evaluation committee is needed ü Members of the committee have to be elected amongst all the teaching staff in all the Italian Universities belonging to the scientific discipline related to the position offered ü Each offered position, therefore, requires a nation-wide election (!)
 Complexity Thousands of elections, each with a different list of candidates and involving many thousands of electors Achieving this objective with traditional methods is impossible The Ministry for University and Scientific and Technologic Research asked us to build an Electronic Voting System
Complexity Thousands of elections, each with a different list of candidates and involving many thousands of electors Achieving this objective with traditional methods is impossible The Ministry for University and Scientific and Technologic Research asked us to build an Electronic Voting System
 Requirements As in a traditional election: ä Legitimacy: only those who have the right to vote can vote and can cast only one vote ä Secrecy: no one can read the vote until the polling phase ä Anonymity: the identity of the voter cannot be traced from the vote cast ä Integrity: the vote cannot be modified once it has been cast ü In addition: ä Acknowledge receipt of each vote cast ü
Requirements As in a traditional election: ä Legitimacy: only those who have the right to vote can vote and can cast only one vote ä Secrecy: no one can read the vote until the polling phase ä Anonymity: the identity of the voter cannot be traced from the vote cast ä Integrity: the vote cannot be modified once it has been cast ü In addition: ä Acknowledge receipt of each vote cast ü
 The Electronic Voting System üA Central Electoral Office for voting authorizations ü A Central Ballot-Box collecting votes ü Many Polling Stations distributed all over the country and directly connected to the two central entities ü Smart card based asymmetric cryptography
The Electronic Voting System üA Central Electoral Office for voting authorizations ü A Central Ballot-Box collecting votes ü Many Polling Stations distributed all over the country and directly connected to the two central entities ü Smart card based asymmetric cryptography
 The Polling Station
The Polling Station
 Voting operations The voter is identified at a Polling Station by an electoral committee ü He receives a one time use personal secret code ü He votes using a network terminal ü The printer prints out a record with the name of the voter and periodic accounting on the number of voters ü
Voting operations The voter is identified at a Polling Station by an electoral committee ü He receives a one time use personal secret code ü He votes using a network terminal ü The printer prints out a record with the name of the voter and periodic accounting on the number of voters ü
 Polling operations ü Each Recruitment Procedure Officer, using his smart card, gets the encrypted votes from the Central Ballot-Box and decrypt them ü He determines the results, signs them with the smart card and gets them published on the Web in real-time
Polling operations ü Each Recruitment Procedure Officer, using his smart card, gets the encrypted votes from the Central Ballot-Box and decrypt them ü He determines the results, signs them with the smart card and gets them published on the Web in real-time
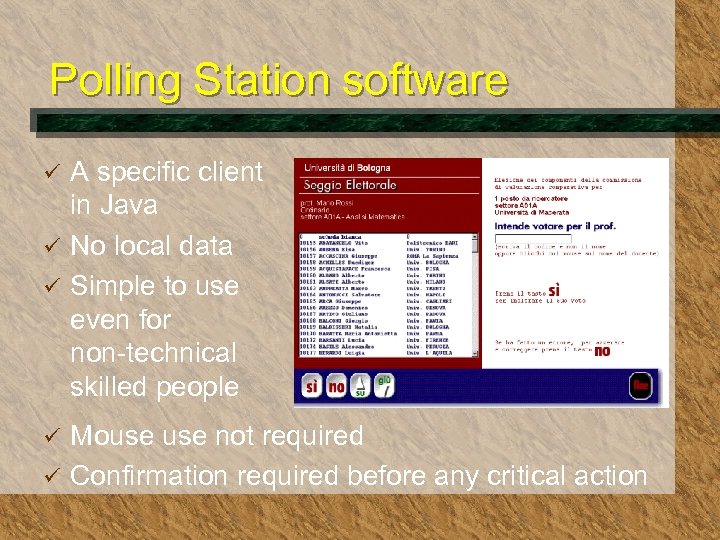 Polling Station software A specific client in Java ü No local data ü Simple to use even for non-technical skilled people ü Mouse not required ü Confirmation required before any critical action ü
Polling Station software A specific client in Java ü No local data ü Simple to use even for non-technical skilled people ü Mouse not required ü Confirmation required before any critical action ü
 The Certification Authority Issues X. 509 v 3 certificates for: Polling Stations Recruitment Procedure Officers
The Certification Authority Issues X. 509 v 3 certificates for: Polling Stations Recruitment Procedure Officers
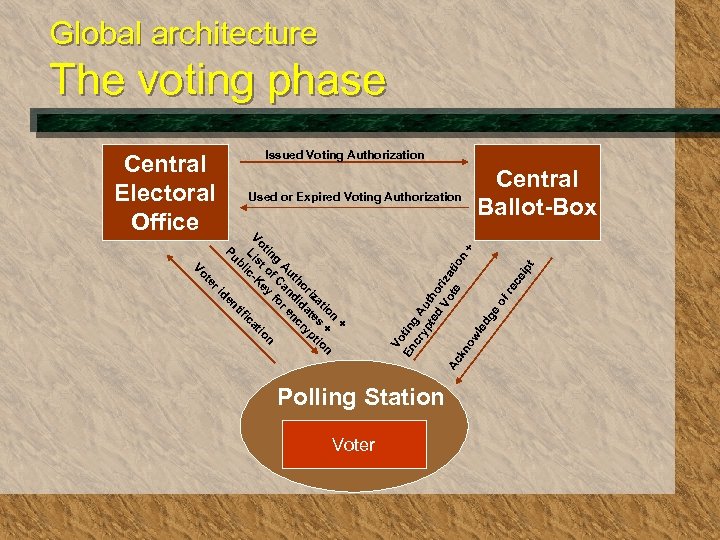 Global architecture The voting phase Issued Voting Authorization Central Electoral Office + n io + n at s tio riz ate yp ho id cr ut d n A an re g f C fo n tin t o ey tio Vo s K Li licca ifi b Pu nt de ri te Vo Vo En tin cr g A yp u te tho d Vo riza Ac te tio kn n + ow le dg e of re ce ip t Used or Expired Voting Authorization Polling Station Voter Central Ballot-Box
Global architecture The voting phase Issued Voting Authorization Central Electoral Office + n io + n at s tio riz ate yp ho id cr ut d n A an re g f C fo n tin t o ey tio Vo s K Li licca ifi b Pu nt de ri te Vo Vo En tin cr g A yp u te tho d Vo riza Ac te tio kn n + ow le dg e of re ce ip t Used or Expired Voting Authorization Polling Station Voter Central Ballot-Box
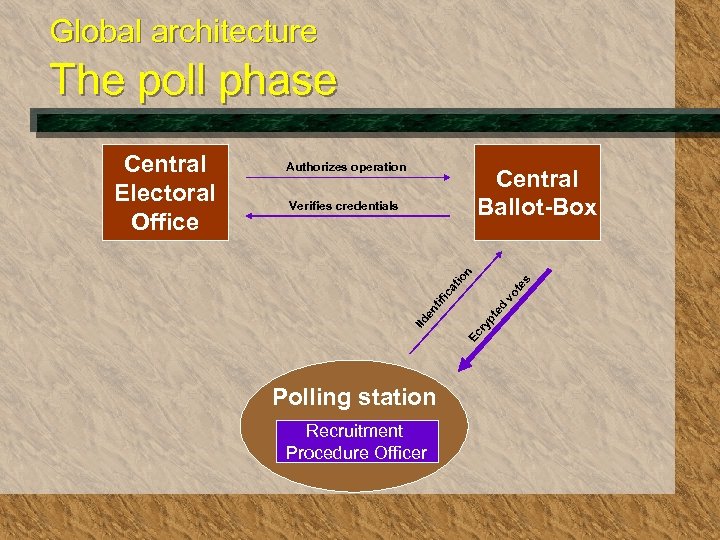 Global architecture The poll phase Authorizes operation Central Ballot-Box ed pt Ec ry en tif ic vo at te s io n Verifies credentials IId Central Electoral Office Polling station Recruitment Procedure Officer
Global architecture The poll phase Authorizes operation Central Ballot-Box ed pt Ec ry en tif ic vo at te s io n Verifies credentials IId Central Electoral Office Polling station Recruitment Procedure Officer
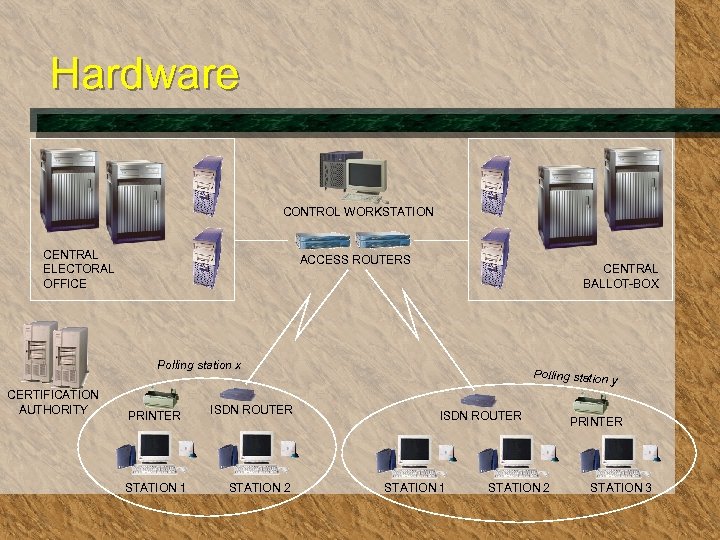 Hardware CONTROL WORKSTATION CENTRAL ELECTORAL OFFICE ACCESS ROUTERS CENTRAL BALLOT-BOX Polling station x CERTIFICATION AUTHORITY PRINTER STATION 1 ISDN ROUTER STATION 2 Polling station ISDN ROUTER STATION 1 STATION 2 y PRINTER STATION 3
Hardware CONTROL WORKSTATION CENTRAL ELECTORAL OFFICE ACCESS ROUTERS CENTRAL BALLOT-BOX Polling station x CERTIFICATION AUTHORITY PRINTER STATION 1 ISDN ROUTER STATION 2 Polling station ISDN ROUTER STATION 1 STATION 2 y PRINTER STATION 3
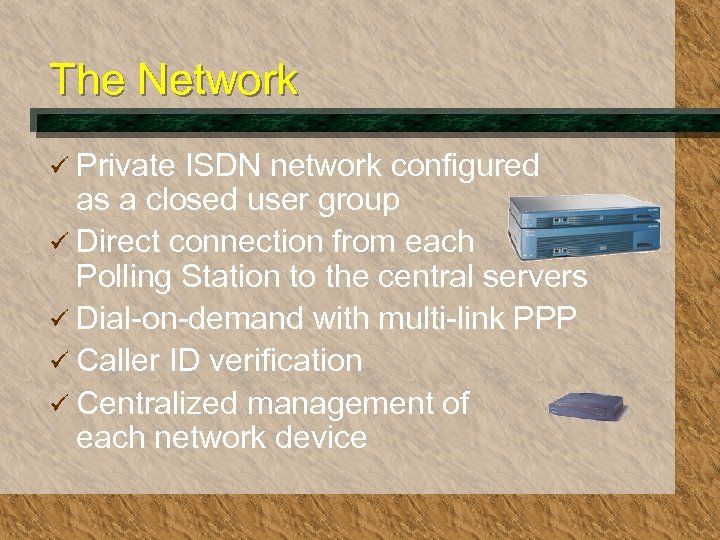 The Network ü Private ISDN network configured as a closed user group ü Direct connection from each Polling Station to the central servers ü Dial-on-demand with multi-link PPP ü Caller ID verification ü Centralized management of each network device
The Network ü Private ISDN network configured as a closed user group ü Direct connection from each Polling Station to the central servers ü Dial-on-demand with multi-link PPP ü Caller ID verification ü Centralized management of each network device
 Security systems Votes are protected by: ü Strong asymmetric cryptography based on smart card ü SSL authentication with X. 509 v 3 certificates ü Digital signature of the Polling Station
Security systems Votes are protected by: ü Strong asymmetric cryptography based on smart card ü SSL authentication with X. 509 v 3 certificates ü Digital signature of the Polling Station
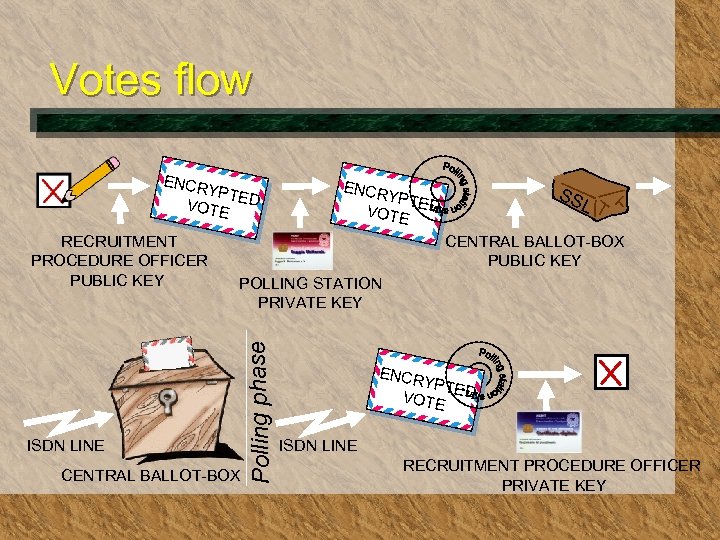 Votes flow ENCR YPTE VOTE D SS L YPTE VOTE D CENTRAL BALLOT-BOX PUBLIC KEY POLLING STATION PRIVATE KEY ISDN LINE CENTRAL BALLOT-BOX Polling phase RECRUITMENT PROCEDURE OFFICER PUBLIC KEY ENCR YPTE VOTE D ISDN LINE RECRUITMENT PROCEDURE OFFICER PRIVATE KEY
Votes flow ENCR YPTE VOTE D SS L YPTE VOTE D CENTRAL BALLOT-BOX PUBLIC KEY POLLING STATION PRIVATE KEY ISDN LINE CENTRAL BALLOT-BOX Polling phase RECRUITMENT PROCEDURE OFFICER PUBLIC KEY ENCR YPTE VOTE D ISDN LINE RECRUITMENT PROCEDURE OFFICER PRIVATE KEY
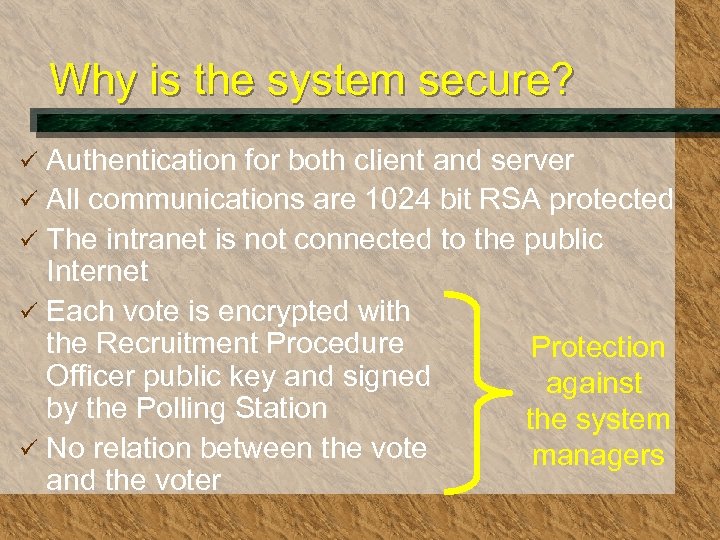 Why is the system secure? Authentication for both client and server ü All communications are 1024 bit RSA protected ü The intranet is not connected to the public Internet ü Each vote is encrypted with the Recruitment Procedure Protection Officer public key and signed against by the Polling Station the system ü No relation between the vote managers and the voter ü
Why is the system secure? Authentication for both client and server ü All communications are 1024 bit RSA protected ü The intranet is not connected to the public Internet ü Each vote is encrypted with the Recruitment Procedure Protection Officer public key and signed against by the Polling Station the system ü No relation between the vote managers and the voter ü
 System certification This solution has been checked and certified as safe by a Technical Committee on behalf of the Ministry for University and Scientific and Technologic Research
System certification This solution has been checked and certified as safe by a Technical Committee on behalf of the Ministry for University and Scientific and Technologic Research
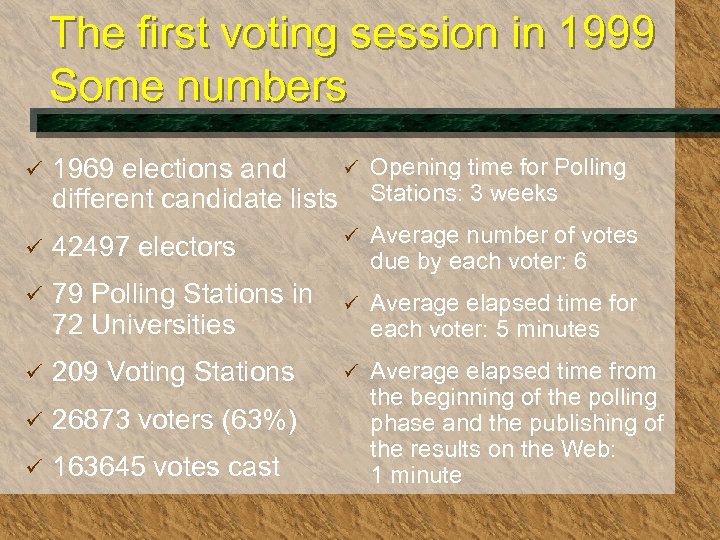 The first voting session in 1999 Some numbers ü ü Opening time for Polling 1969 elections and different candidate lists Stations: 3 weeks ü 42497 electors ü ü Average number of votes due by each voter: 6 79 Polling Stations in 72 Universities ü Average elapsed time for each voter: 5 minutes ü 209 Voting Stations ü ü 26873 voters (63%) ü 163645 votes cast Average elapsed time from the beginning of the polling phase and the publishing of the results on the Web: 1 minute
The first voting session in 1999 Some numbers ü ü Opening time for Polling 1969 elections and different candidate lists Stations: 3 weeks ü 42497 electors ü ü Average number of votes due by each voter: 6 79 Polling Stations in 72 Universities ü Average elapsed time for each voter: 5 minutes ü 209 Voting Stations ü ü 26873 voters (63%) ü 163645 votes cast Average elapsed time from the beginning of the polling phase and the publishing of the results on the Web: 1 minute
 Future extensions üA personal identity card for each voter instead of the one-time-use secret code ü Polling Stations on the public Internet ü Feasibility of voting from any PC ü Other kinds of elections. . .
Future extensions üA personal identity card for each voter instead of the one-time-use secret code ü Polling Stations on the public Internet ü Feasibility of voting from any PC ü Other kinds of elections. . .
 For any information evote@cineca. it
For any information evote@cineca. it


