d4198f28ce28bce735c57e3ae3f6576c.ppt
- Количество слайдов: 36
The Internet Real-Time Laboratory Prof. Henning Schulzrinne Feb 2006 http: //www. cs. columbia. edu/IRT

Current members n n IRT lab: 1 faculty, 1 post-doc, 13 Ph. D, 6 MS GRAs, 2 visitors and a researcher: total 24 China, Germany, Hong Kong, India, Italy, Israel, Japan, Korea, Pakistan, USA

Sponsors Equipment grants and student support: past and present
Research topics Internet Real-Time Systems Security Service discovery Reliability and scalability Multimedia collaboration Mobile and ad hoc Peer-to-peer systems Enterprise IP telephony 911 calls on Internet Ubiquitous computing presence Wireless telephony Programmable services
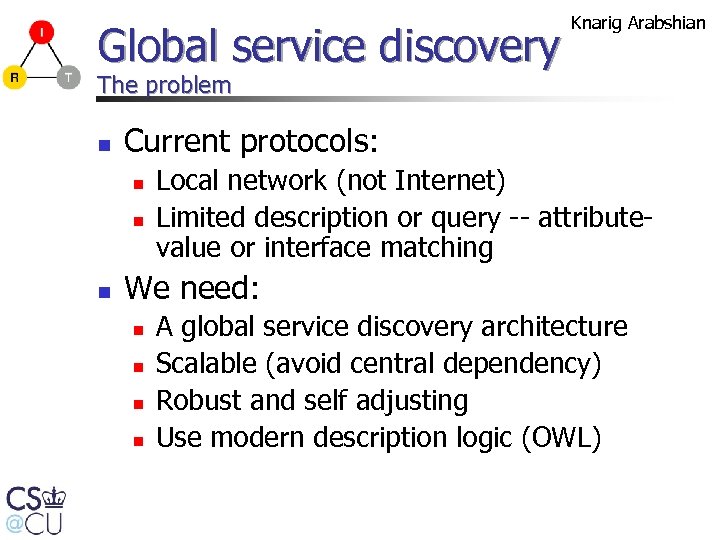
Global service discovery Knarig Arabshian The problem n Current protocols: n n n Local network (not Internet) Limited description or query -- attributevalue or interface matching We need: n n A global service discovery architecture Scalable (avoid central dependency) Robust and self adjusting Use modern description logic (OWL)
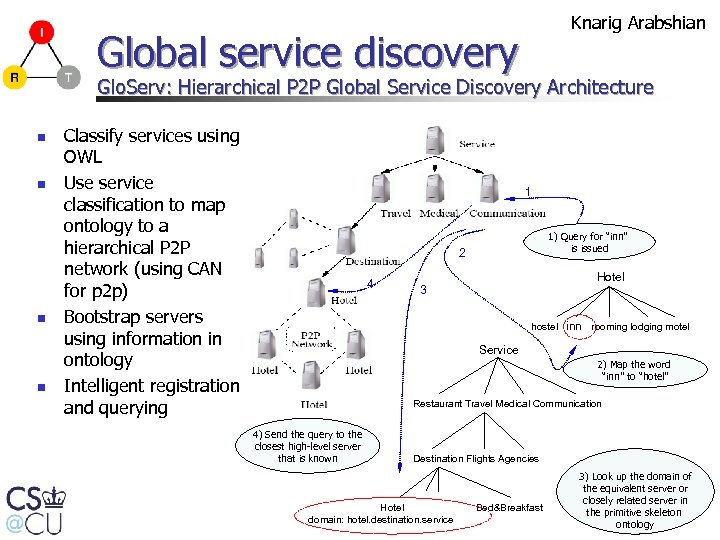
Knarig Arabshian Global service discovery Glo. Serv: Hierarchical P 2 P Global Service Discovery Architecture n n Classify services using OWL Use service classification to map ontology to a hierarchical P 2 P network (using CAN for p 2 p) Bootstrap servers using information in ontology Intelligent registration and querying 1 1) Query for “inn” is issued 2 4 Hotel 3 hostel inn rooming lodging motel Service 2) Map the word “inn” to “hotel” Restaurant Travel Medical Communication 4) Send the query to the closest high-level server that is known Destination Flights Agencies Hotel domain: hotel. destination. service Bed&Breakfast 3) Look up the domain of the equivalent server or closely related server in the primitive skeleton ontology
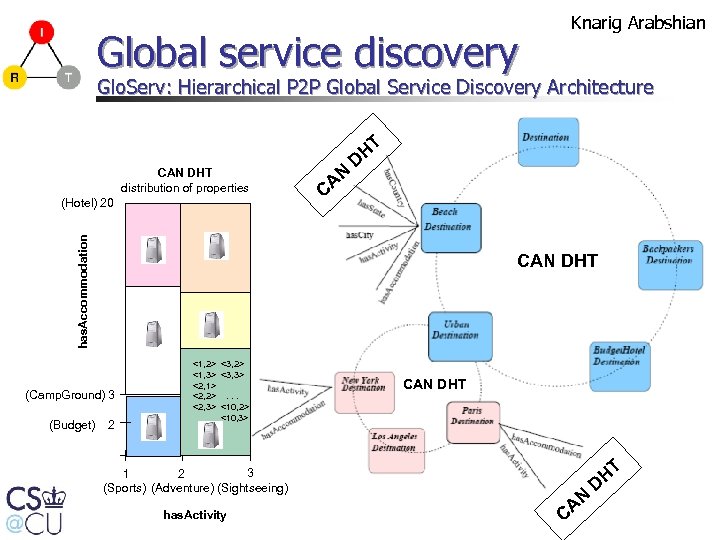
Global service discovery Knarig Arabshian Glo. Serv: Hierarchical P 2 P Global Service Discovery Architecture CAN DHT distribution of properties has. Accommodation (Hotel) 20 AN C HT D CAN DHT (Camp. Ground) 3 (Budget) 2 <1, 2> <3, 2> <1, 3> <3, 3> <2, 1> <2, 2>. . . <2, 3> <10, 2> <10, 3> 3 1 2 (Sightseeing) (Sports) (Adventure) has. Activity CAN DHT AN C HT D
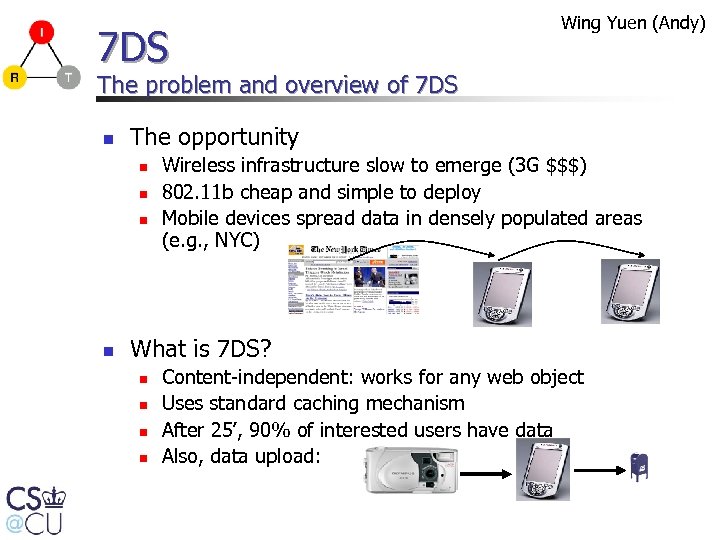
7 DS Wing Yuen (Andy) The problem and overview of 7 DS n The opportunity n n Wireless infrastructure slow to emerge (3 G $$$) 802. 11 b cheap and simple to deploy Mobile devices spread data in densely populated areas (e. g. , NYC) What is 7 DS? n n Content-independent: works for any web object Uses standard caching mechanism After 25’, 90% of interested users have data Also, data upload:
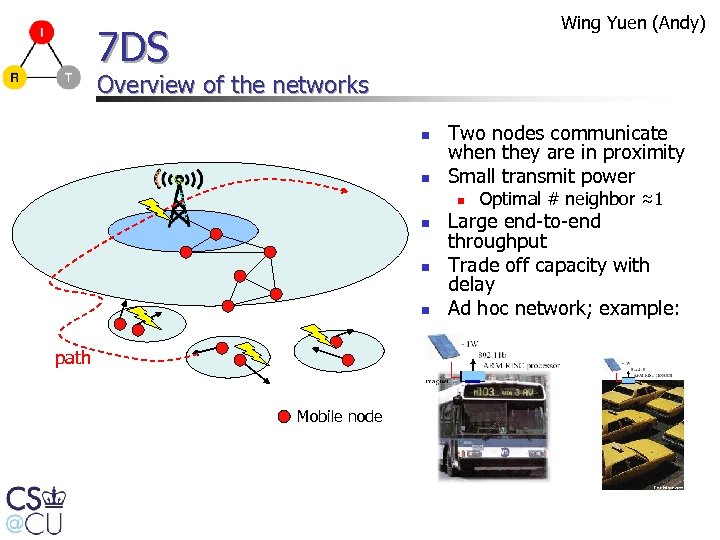
Wing Yuen (Andy) 7 DS Overview of the networks n n Two nodes communicate when they are in proximity Small transmit power n n path Mobile node Optimal # neighbor ≈1 Large end-to-end throughput Trade off capacity with delay Ad hoc network; example:
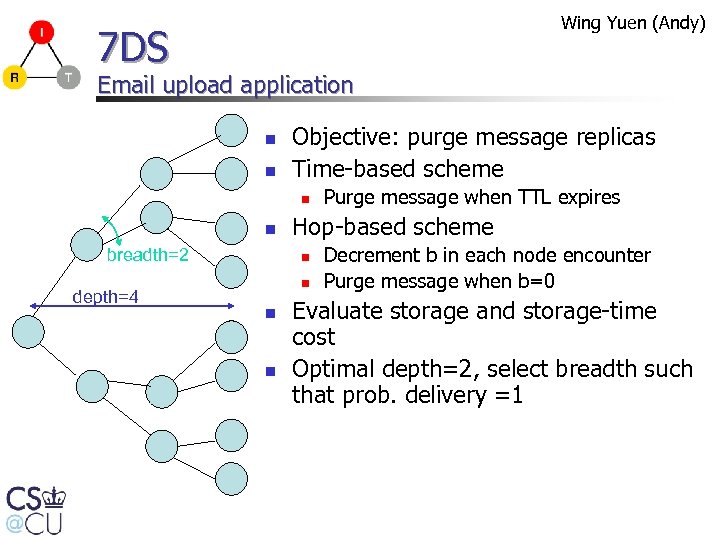
Wing Yuen (Andy) 7 DS Email upload application n n Objective: purge message replicas Time-based scheme n n breadth=2 depth=4 Hop-based scheme n n Purge message when TTL expires Decrement b in each node encounter Purge message when b=0 Evaluate storage and storage-time cost Optimal depth=2, select breadth such that prob. delivery =1
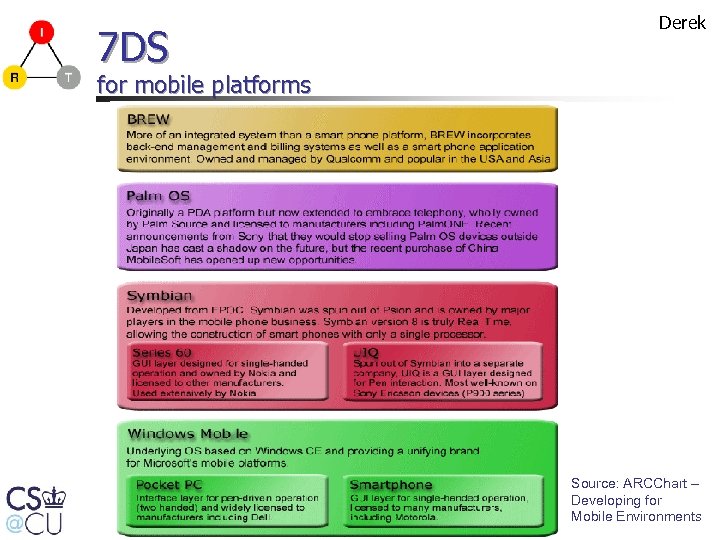
7 DS Derek for mobile platforms Source: ARCChart – Developing for Mobile Environments
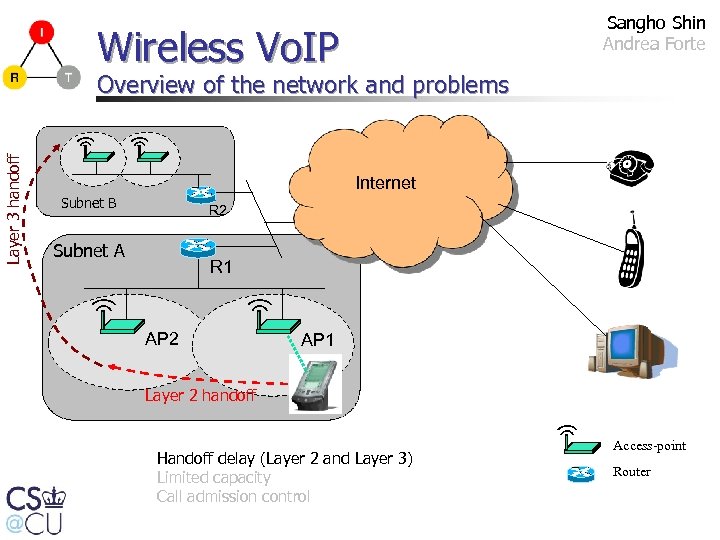
Sangho Shin Andrea Forte Wireless Vo. IP Layer 3 handoff Overview of the network and problems Internet Subnet B R 2 Subnet A R 1 AP 2 AP 1 Layer 2 handoff Handoff delay (Layer 2 and Layer 3) Limited capacity Call admission control Access-point Router
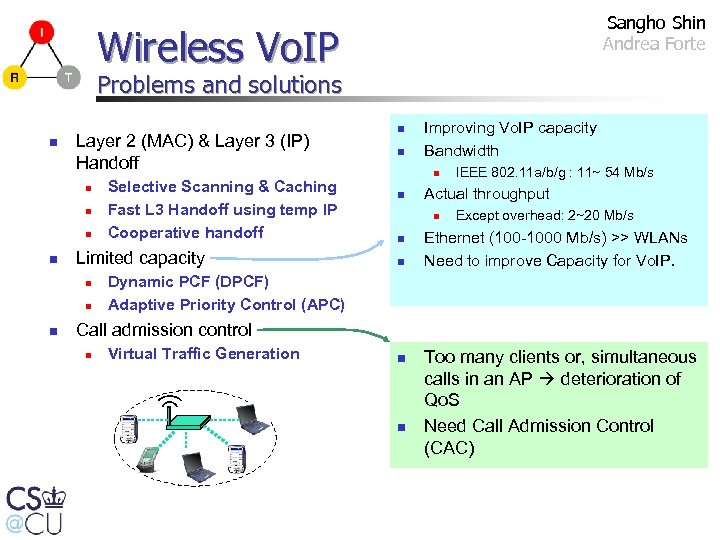
Sangho Shin Andrea Forte Wireless Vo. IP Problems and solutions n Layer 2 (MAC) & Layer 3 (IP) Handoff n n Limited capacity n n n Selective Scanning & Caching Fast L 3 Handoff using temp IP Cooperative handoff n n Improving Vo. IP capacity Bandwidth n n Actual throughput n n n IEEE 802. 11 a/b/g : 11~ 54 Mb/s Except overhead: 2~20 Mb/s Ethernet (100 -1000 Mb/s) >> WLANs Need to improve Capacity for Vo. IP. Dynamic PCF (DPCF) Adaptive Priority Control (APC) Call admission control n Virtual Traffic Generation n n Too many clients or, simultaneous calls in an AP deterioration of Qo. S Need Call Admission Control (CAC)
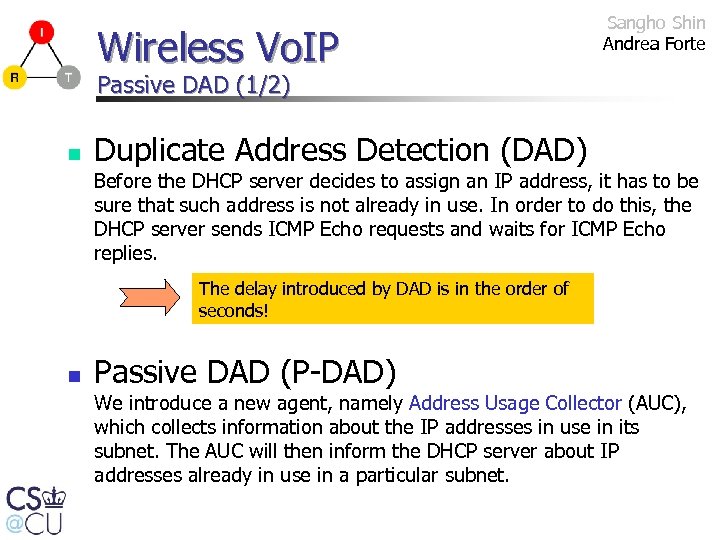
Wireless Vo. IP Sangho Shin Andrea Forte Passive DAD (1/2) n Duplicate Address Detection (DAD) Before the DHCP server decides to assign an IP address, it has to be sure that such address is not already in use. In order to do this, the DHCP server sends ICMP Echo requests and waits for ICMP Echo replies. The delay introduced by DAD is in the order of seconds! n Passive DAD (P-DAD) We introduce a new agent, namely Address Usage Collector (AUC), which collects information about the IP addresses in use in its subnet. The AUC will then inform the DHCP server about IP addresses already in use in a particular subnet.
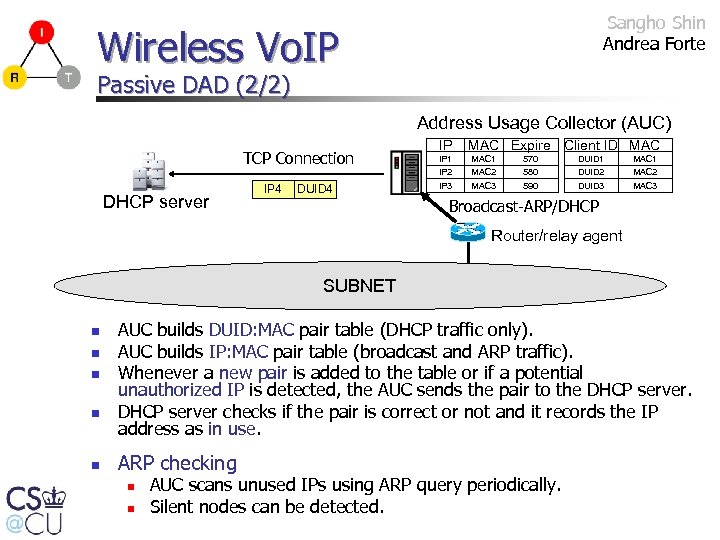
Sangho Shin Andrea Forte Wireless Vo. IP Passive DAD (2/2) Address Usage Collector (AUC) TCP Connection DHCP server IP 4 DUID 4 IP MAC Expire Client ID MAC IP 1 IP 2 MAC 1 MAC 2 570 580 IP 3 MAC 3 590 DUID 1 DUID 2 DUID 3 MAC 1 MAC 2 MAC 3 Broadcast-ARP/DHCP Router/relay agent SUBNET n n n AUC builds DUID: MAC pair table (DHCP traffic only). AUC builds IP: MAC pair table (broadcast and ARP traffic). Whenever a new pair is added to the table or if a potential unauthorized IP is detected, the AUC sends the pair to the DHCP server checks if the pair is correct or not and it records the IP address as in use. ARP checking n n AUC scans unused IPs using ARP query periodically. Silent nodes can be detected.
Wireless Vo. IP Sangho Shin Andrea Forte Problems of the current DAD n n n In wireless networks, it takes long time to get ICMP echo response, or even the response can be lost when the channel is very congested. Windows XP SP 2 activates the firewall, and the firewall blocks incoming ICMP echo by default. ISC DHCP software has a bug in the DAD timer, and the timer value is decided between 0 ~ 1 sec randomly.
Vo. IP real world app. Venkata S. Malladi Anurag Chakravarti Training air traffic controllers at FAA n Existing communication system n n n What the project is? n n n Voice communications network n Analog, fixed point-to-point connections Fast Ethernet data network Video network Depends on analog, hard-wired communication systems that use obsolete parts no longer available without custom manufacture Simulate a FAA classroom Classroom has student, pilot and an instructor workstation Student plays the role of an ATC, who is trained by the pilot. Student and pilot communicate to each other, via a notion of frequency (unicast) and facility (multicast) What am I doing? n n n Feature enhancements Get the project successfully deployed on-site Development of robust audio tool on Windows platform
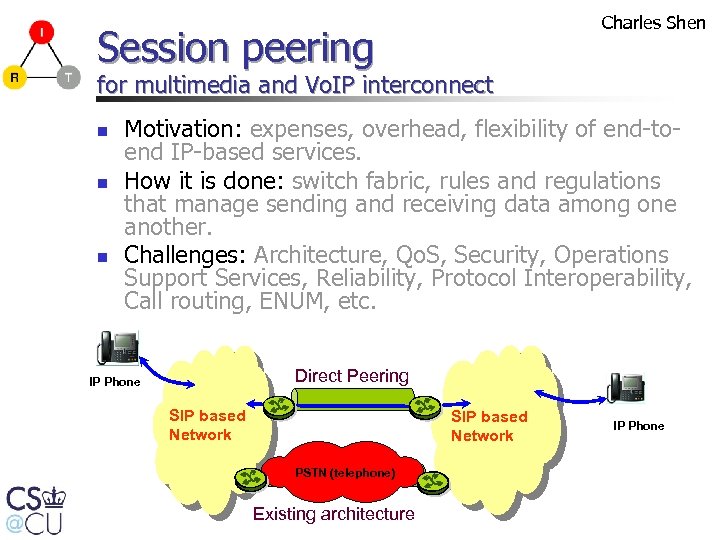
Charles Shen Session peering for multimedia and Vo. IP interconnect n n n Motivation: expenses, overhead, flexibility of end-toend IP-based services. How it is done: switch fabric, rules and regulations that manage sending and receiving data among one another. Challenges: Architecture, Qo. S, Security, Operations Support Services, Reliability, Protocol Interoperability, Call routing, ENUM, etc. Direct Peering IP Phone SIP based Network PSTN (telephone) Existing architecture IP Phone
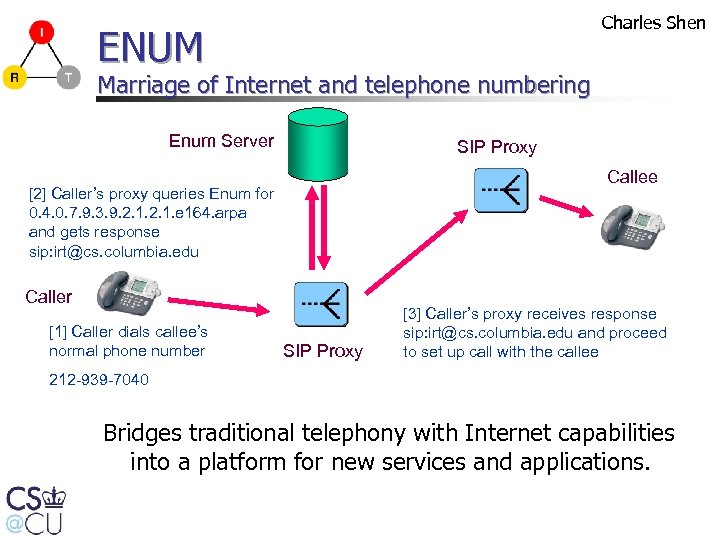
Charles Shen ENUM Marriage of Internet and telephone numbering Enum Server SIP Proxy Callee [2] Caller’s proxy queries Enum for 0. 4. 0. 7. 9. 3. 9. 2. 1. e 164. arpa and gets response sip: irt@cs. columbia. edu Caller [1] Caller dials callee’s normal phone number SIP Proxy [3] Caller’s proxy receives response sip: irt@cs. columbia. edu and proceed to set up call with the callee 212 -939 -7040 Bridges traditional telephony with Internet capabilities into a platform for new services and applications.
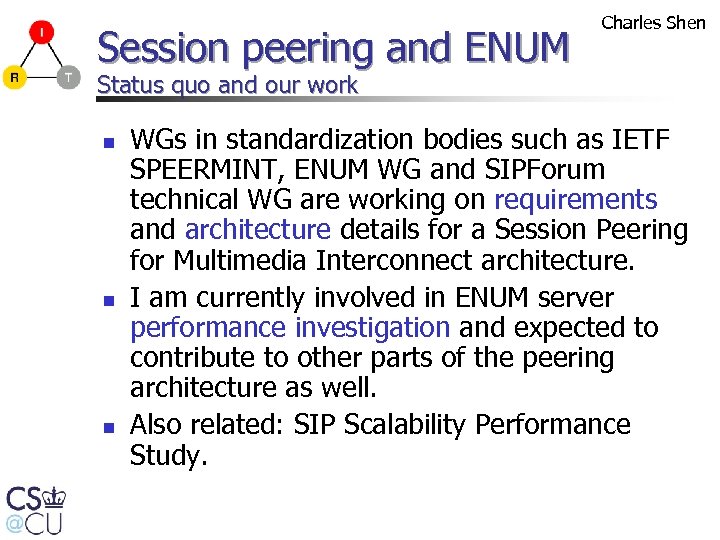
Session peering and ENUM Charles Shen Status quo and our work n n n WGs in standardization bodies such as IETF SPEERMINT, ENUM WG and SIPForum technical WG are working on requirements and architecture details for a Session Peering for Multimedia Interconnect architecture. I am currently involved in ENUM server performance investigation and expected to contribute to other parts of the peering architecture as well. Also related: SIP Scalability Performance Study.
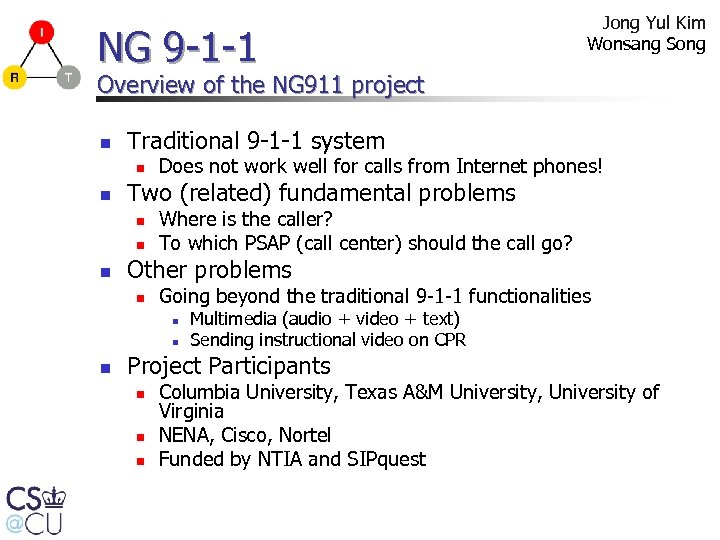
NG 9 -1 -1 Jong Yul Kim Wonsang Song Overview of the NG 911 project n Traditional 9 -1 -1 system n n Two (related) fundamental problems n n n Does not work well for calls from Internet phones! Where is the caller? To which PSAP (call center) should the call go? Other problems n Going beyond the traditional 9 -1 -1 functionalities n n n Multimedia (audio + video + text) Sending instructional video on CPR Project Participants n n n Columbia University, Texas A&M University, University of Virginia NENA, Cisco, Nortel Funded by NTIA and SIPquest
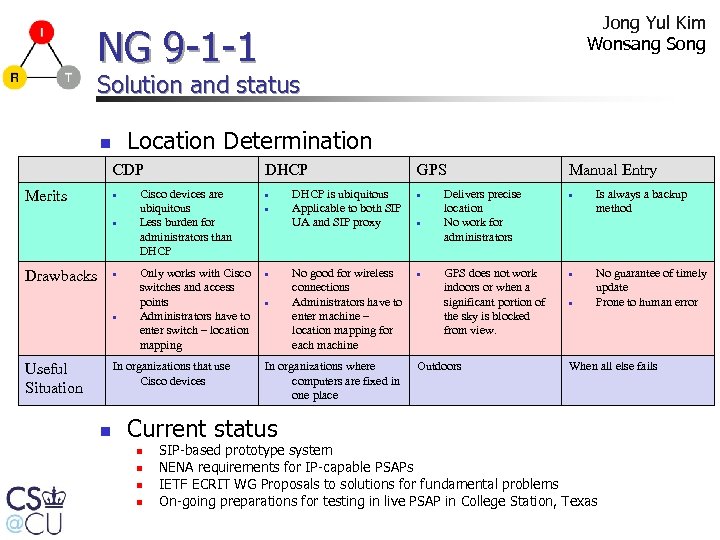
Jong Yul Kim Wonsang Song NG 9 -1 -1 Solution and status Location Determination n CDP Merits Drawbacks DHCP Cisco devices are ubiquitous Less burden for administrators than DHCP Only works with Cisco switches and access points Administrators have to enter switch – location mapping In organizations that use Cisco devices Useful Situation n DHCP is ubiquitous Applicable to both SIP UA and SIP proxy No good for wireless connections Administrators have to enter machine – location mapping for each machine In organizations where computers are fixed in one place Current status GPS Manual Entry Delivers precise location No work for administrators Is always a backup method GPS does not work indoors or when a significant portion of the sky is blocked from view. No guarantee of timely update Prone to human error Outdoors When all else fails SIP-based prototype system NENA requirements for IP-capable PSAPs IETF ECRIT WG Proposals to solutions for fundamental problems On-going preparations for testing in live PSAP in College Station, Texas
Vo. IP security Eilon Yardeni Denial of Service (Do. S) attacks: the problem n n n Do. S attacks are still prevalent in the Internet Telephony services are exposed as they move to the IP network The E 911 service is specifically vulnerable How to distinguish between a human and machine request? Detection and Mitigation
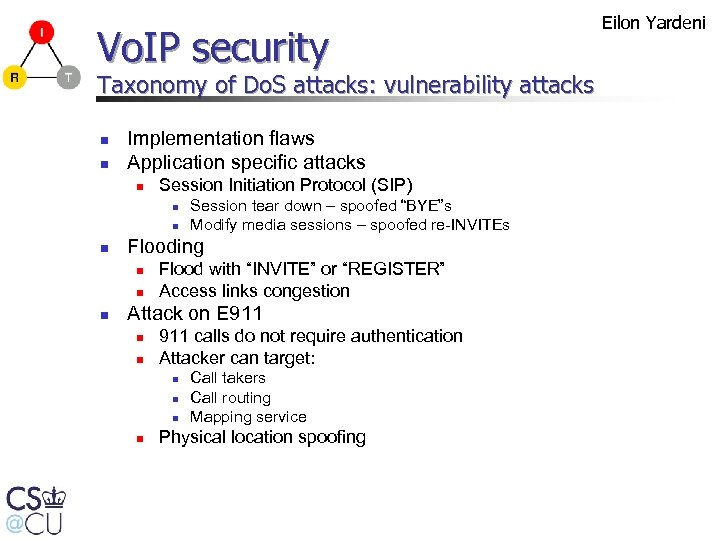
Vo. IP security Taxonomy of Do. S attacks: vulnerability attacks n n Implementation flaws Application specific attacks n Session Initiation Protocol (SIP) n n n Flooding n n n Session tear down – spoofed “BYE”s Modify media sessions – spoofed re-INVITEs Flood with “INVITE” or “REGISTER” Access links congestion Attack on E 911 n n 911 calls do not require authentication Attacker can target: n n Call takers Call routing Mapping service Physical location spoofing Eilon Yardeni
Vo. IP security Defense against Do. S attacks n Fake location n Signed location Location verification First level filtering heuristics n n IP-to-geo location comparison List of legitimate subnets Eilon Yardeni
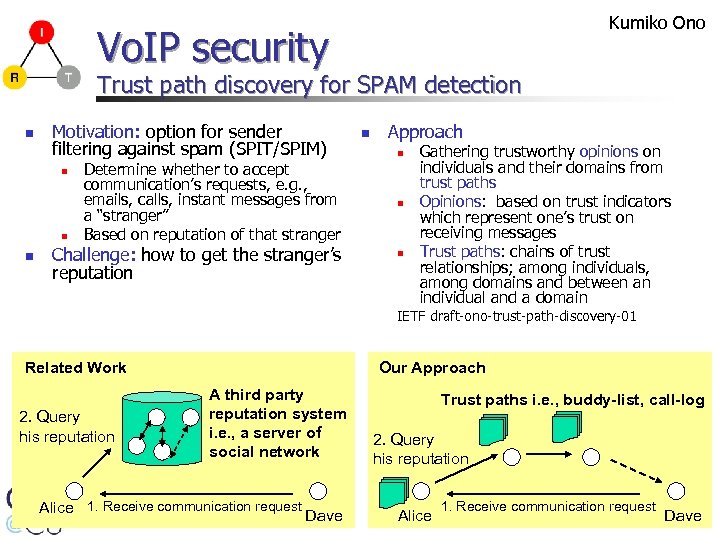
Kumiko Ono Vo. IP security Trust path discovery for SPAM detection n Motivation: option for sender filtering against spam (SPIT/SPIM) n n n Determine whether to accept communication’s requests, e. g. , emails, calls, instant messages from a “stranger” Based on reputation of that stranger Challenge: how to get the stranger’s reputation n Approach n n n Gathering trustworthy opinions on individuals and their domains from trust paths Opinions: based on trust indicators which represent one’s trust on receiving messages Trust paths: chains of trust relationships; among individuals, among domains and between an individual and a domain IETF draft-ono-trust-path-discovery-01 Related Work 2. Query his reputation Our Approach A third party reputation system i. e. , a server of social network Alice 1. Receive communication request Dave Trust paths i. e. , buddy-list, call-log 2. Query his reputation Alice 1. Receive communication request Dave
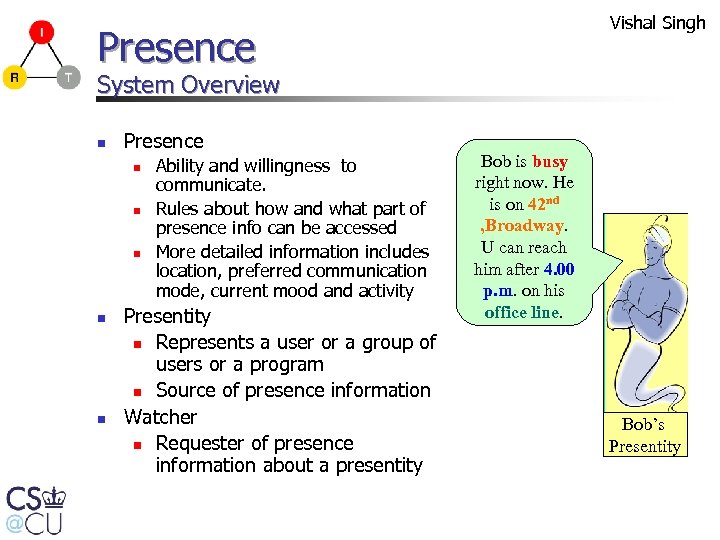
Vishal Singh Presence System Overview n Presence n n n Ability and willingness to communicate. Rules about how and what part of presence info can be accessed More detailed information includes location, preferred communication mode, current mood and activity Presentity n Represents a user or a group of users or a program n Source of presence information Watcher n Requester of presence information about a presentity Bob is busy right now. He is on 42 nd , Broadway. U can reach him after 4. 00 p. m. on his office line. Bob’s Presentity
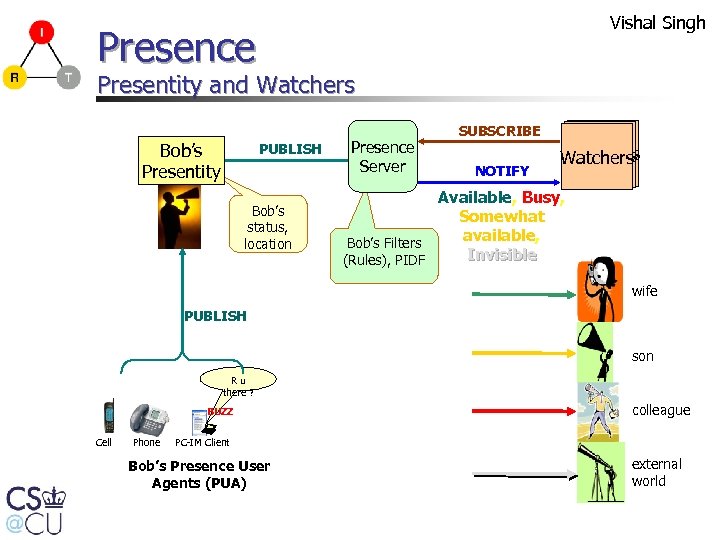
Vishal Singh Presence Presentity and Watchers Bob’s Presentity PUBLISH Bob’s status, location Presence Server SUBSCRIBE NOTIFY Watchers Available, Busy, Somewhat available, Bob’s Filters Invisible (Rules), PIDF wife PUBLISH son Ru there ? BUZZ Cell Phone colleague PC-IM Client Bob’s Presence User Agents (PUA) external world
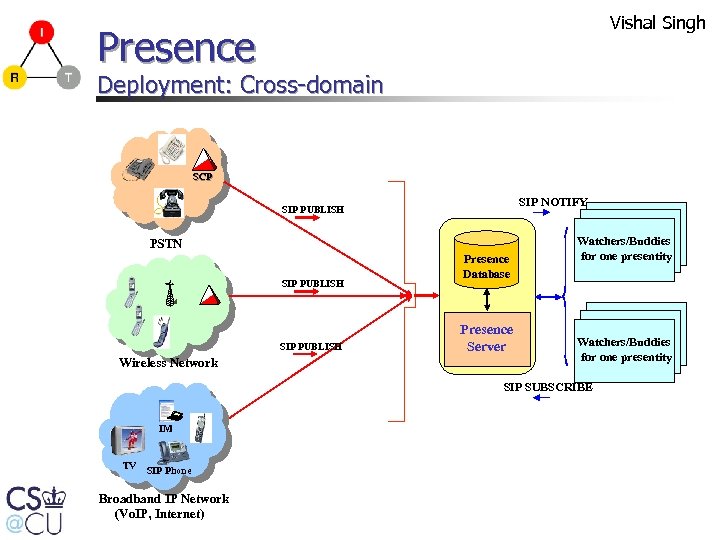
Vishal Singh Presence Deployment: Cross-domain SCP SIP NOTIFY SIP PUBLISH Presence Server PSTN SIP PUBLISH Wireless Network Presence Database Presence Server Watchers/Buddies for one presentity SIP SUBSCRIBE IM TV SIP Phone Broadband IP Network (Vo. IP, Internet) Presence Server Watchers/Buddies for one presentity
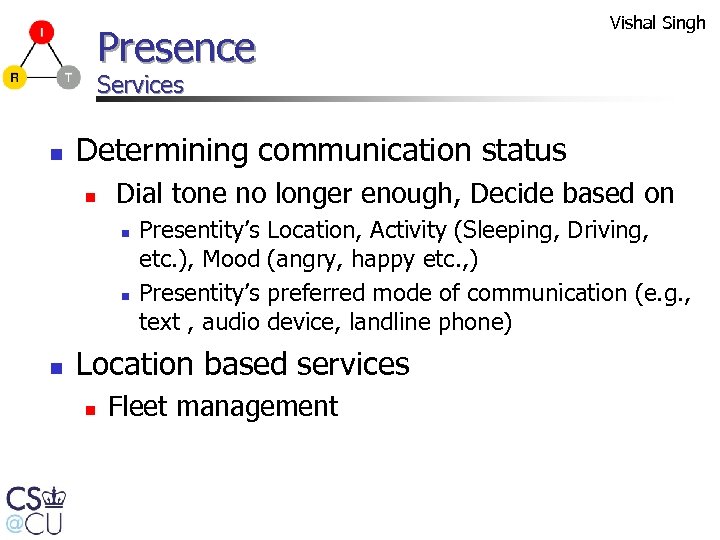
Vishal Singh Presence Services n Determining communication status n Dial tone no longer enough, Decide based on n Presentity’s etc. ), Mood Presentity’s text , audio Location, Activity (Sleeping, Driving, (angry, happy etc. , ) preferred mode of communication (e. g. , device, landline phone) Location based services n Fleet management
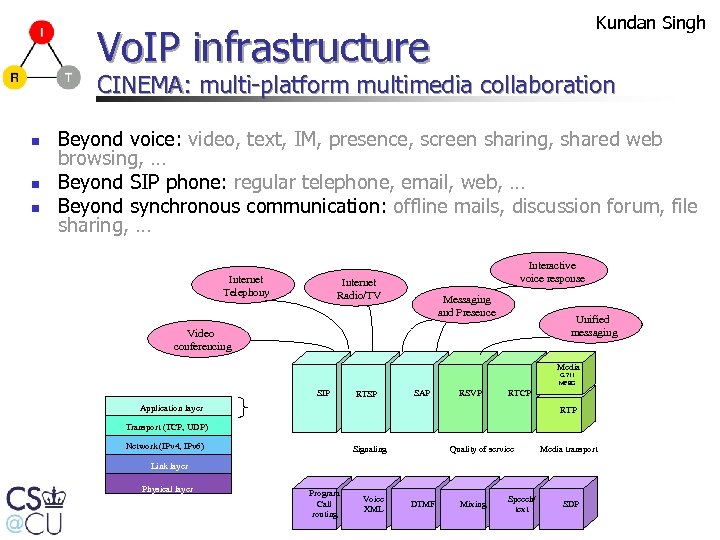
Kundan Singh Vo. IP infrastructure CINEMA: multi-platform multimedia collaboration n Beyond voice: video, text, IM, presence, screen sharing, shared web browsing, … Beyond SIP phone: regular telephone, email, web, … Beyond synchronous communication: offline mails, discussion forum, file sharing, … Internet Telephony Interactive voice response Internet Radio/TV Messaging and Presence Unified messaging Video conferencing Media G. 711 MPEG SIP RTSP SAP RSVP RTCP Application layer RTP Transport (TCP, UDP) Network (IPv 4, IPv 6) Quality of service Signaling Media transport Link layer Physical layer Program Call routing Voice XML DTMF Mixing Speech/ text SDP
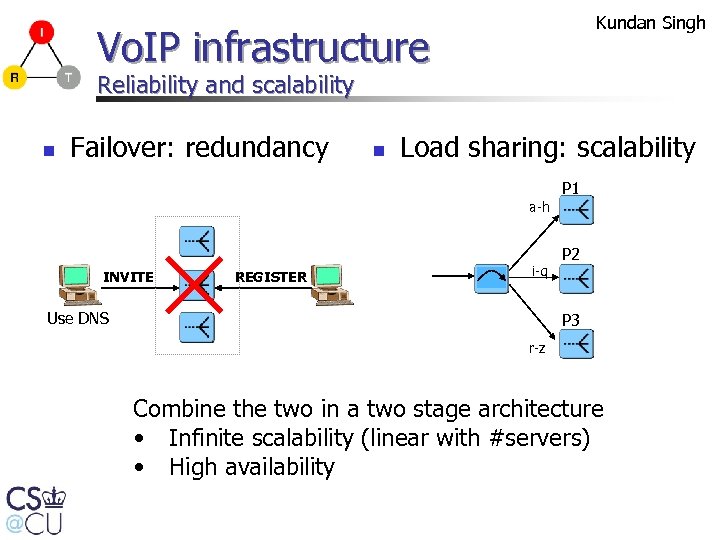
Kundan Singh Vo. IP infrastructure Reliability and scalability n Failover: redundancy n Load sharing: scalability P 1 a-h INVITE REGISTER i-q Use DNS P 2 P 3 r-z Combine the two in a two stage architecture • Infinite scalability (linear with #servers) • High availability
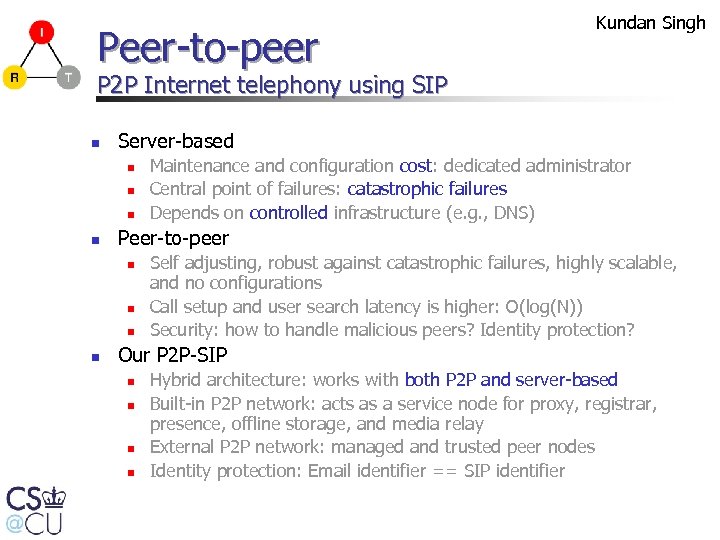
Peer-to-peer Kundan Singh P 2 P Internet telephony using SIP n Server-based n n Peer-to-peer n n Maintenance and configuration cost: dedicated administrator Central point of failures: catastrophic failures Depends on controlled infrastructure (e. g. , DNS) Self adjusting, robust against catastrophic failures, highly scalable, and no configurations Call setup and user search latency is higher: O(log(N)) Security: how to handle malicious peers? Identity protection? Our P 2 P-SIP n n Hybrid architecture: works with both P 2 P and server-based Built-in P 2 P network: acts as a service node for proxy, registrar, presence, offline storage, and media relay External P 2 P network: managed and trusted peer nodes Identity protection: Email identifier == SIP identifier
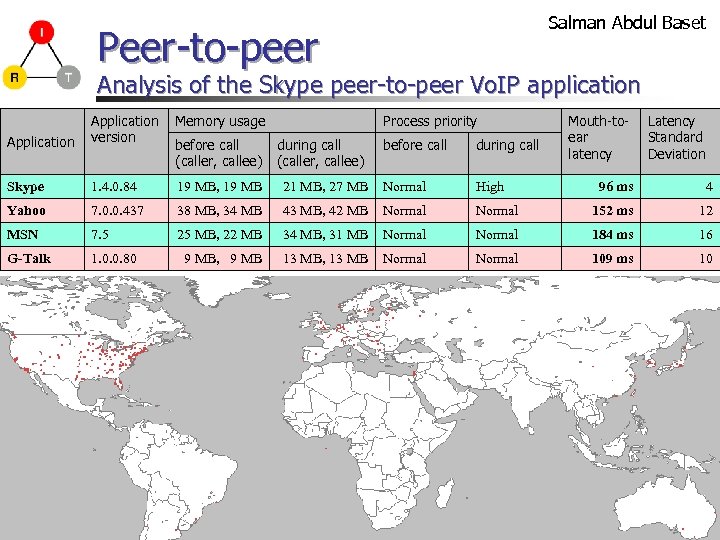
Salman Abdul Baset Peer-to-peer Analysis of the Skype peer-to-peer Vo. IP application Memory usage Application version Skype 1. 4. 0. 84 19 MB, 19 MB Yahoo 7. 0. 0. 437 MSN 7. 5 G-Talk 1. 0. 0. 80 before call (caller, callee) Process priority during call (caller, callee) before call during call 21 MB, 27 MB Normal High 38 MB, 34 MB 43 MB, 42 MB Normal 25 MB, 22 MB 34 MB, 31 MB 9 MB, 9 MB 13 MB, 13 MB Mouth-toear latency Latency Standard Deviation 96 ms 4 Normal 152 ms 12 Normal 184 ms 16 Normal 109 ms 10
Peer-to-peer Salman Abdul Baset Churn in small scale p 2 p networks n n n Small scale: nodes count 5 to 1000 Churn: node arrival/departure rate Office: high churn at 9: 00 am and 5: 00 pm Is distributed hash table (DHT) better than flooding? Correlated and un-correlated failures
Summary n Internet Real-Time Systems n n n Service discovery, 7 DS, wireless Vo. IP, Security, NG 911, reliability, scalability, peer-to-peer Other projects: SIP user agent, CPL/sipcgi/LESS scripts, session mobility, Dot. Slash, … Questions?
d4198f28ce28bce735c57e3ae3f6576c.ppt