f11ee61547d86ebdc4fa52098addf698.ppt
- Количество слайдов: 85
 The Future of Our Privacy Jay Stanley Senior Policy Analyst Speech, Privacy and Technology Program Editor, Free Future blog jstanley@aclu. org 202 -715 -0818
The Future of Our Privacy Jay Stanley Senior Policy Analyst Speech, Privacy and Technology Program Editor, Free Future blog jstanley@aclu. org 202 -715 -0818
 I. THE CHALLENGE TO OUR PRIVACY
I. THE CHALLENGE TO OUR PRIVACY
 The challenge to our privacy: Technology revolution A burgeoning security establishment Profit Motives
The challenge to our privacy: Technology revolution A burgeoning security establishment Profit Motives
 The challenge to our privacy: Technology revolution A burgeoning security establishment Profit Motives
The challenge to our privacy: Technology revolution A burgeoning security establishment Profit Motives
 Change at light speed
Change at light speed
 “Disruptive technologies”
“Disruptive technologies”
 Smart grid
Smart grid
 DNA
DNA
 Video surveillance
Video surveillance
 Video Surveillance: a new era
Video Surveillance: a new era
 Face recognition
Face recognition
 Iris recognition
Iris recognition
 Behavioral analytics
Behavioral analytics
 License plate recognition
License plate recognition
 Location-tracking
Location-tracking
 The ultimate in location tracking:
The ultimate in location tracking:
 Drones
Drones
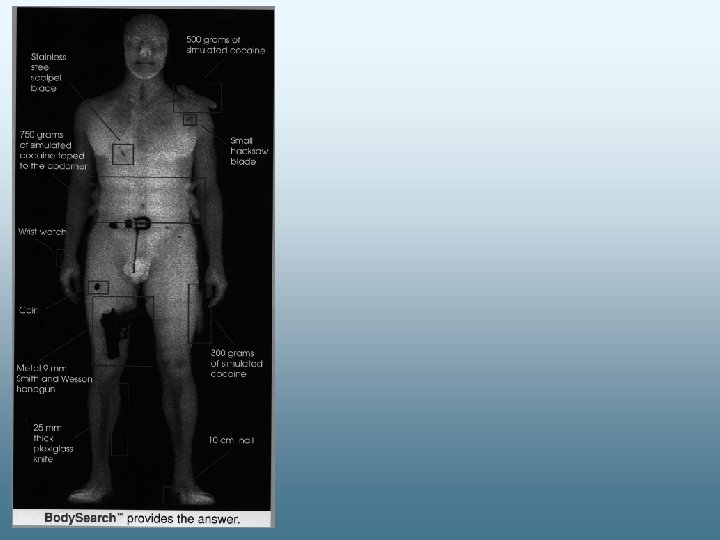
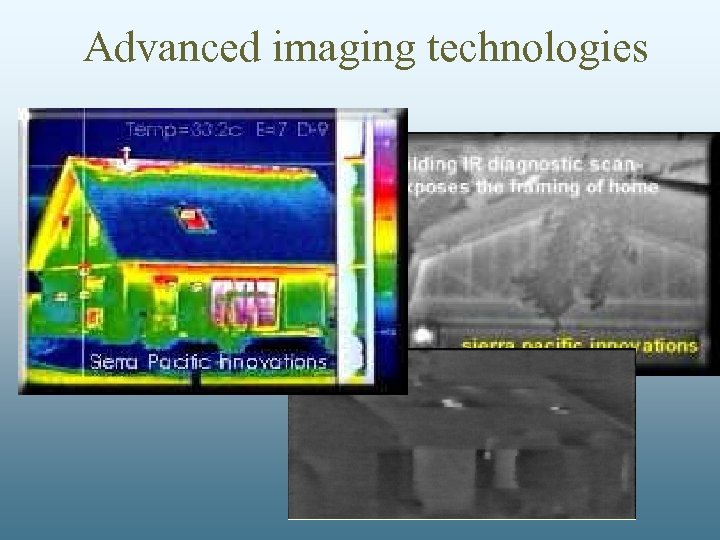 Advanced imaging technologies
Advanced imaging technologies
 The Ultimate Example: Total Information Awareness
The Ultimate Example: Total Information Awareness
 NYC/Microsoft “Domain Awareness System”
NYC/Microsoft “Domain Awareness System”
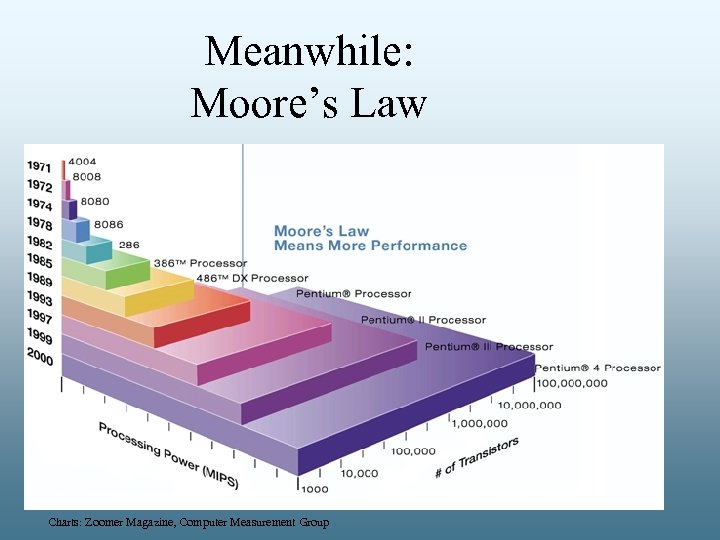 Meanwhile: Moore’s Law Charts: Zoomer Magazine, Computer Measurement Group
Meanwhile: Moore’s Law Charts: Zoomer Magazine, Computer Measurement Group
 The Future of Moore’s Law Intel Core i 7 -2600 Processor: $294. 99 on Newegg
The Future of Moore’s Law Intel Core i 7 -2600 Processor: $294. 99 on Newegg
 The Future of Moore’s Law Today: $294. 99
The Future of Moore’s Law Today: $294. 99
 The Future of Moore’s Law Today: $294. 99 In 20 years: $0. 03
The Future of Moore’s Law Today: $294. 99 In 20 years: $0. 03
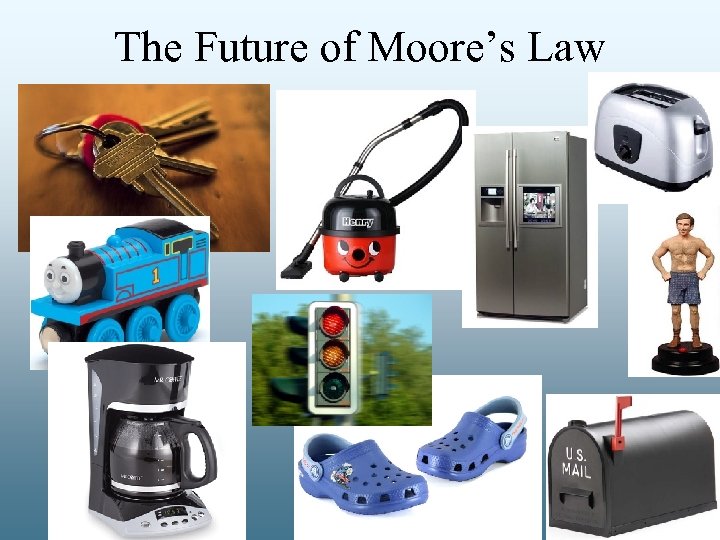 The Future of Moore’s Law
The Future of Moore’s Law
 Also following Moore’s Law 20 years: 1, 000 -32, 000 x today’s power
Also following Moore’s Law 20 years: 1, 000 -32, 000 x today’s power
 Faster, cheaper – and smarter
Faster, cheaper – and smarter
 Hans Moravec: 2020 s
Hans Moravec: 2020 s
 In whose interest?
In whose interest?
 How will AI be used?
How will AI be used?
 Are we ready for all this?
Are we ready for all this?
 The challenge to our privacy: Technology revolution A burgeoning security establishment
The challenge to our privacy: Technology revolution A burgeoning security establishment
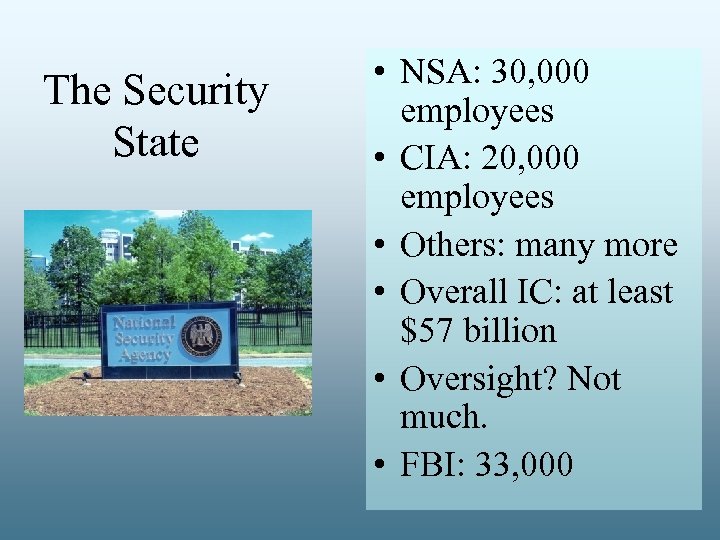 The Security State • NSA: 30, 000 employees • CIA: 20, 000 employees • Others: many more • Overall IC: at least $57 billion • Oversight? Not much. • FBI: 33, 000
The Security State • NSA: 30, 000 employees • CIA: 20, 000 employees • Others: many more • Overall IC: at least $57 billion • Oversight? Not much. • FBI: 33, 000
 Swinging the telescope inward
Swinging the telescope inward

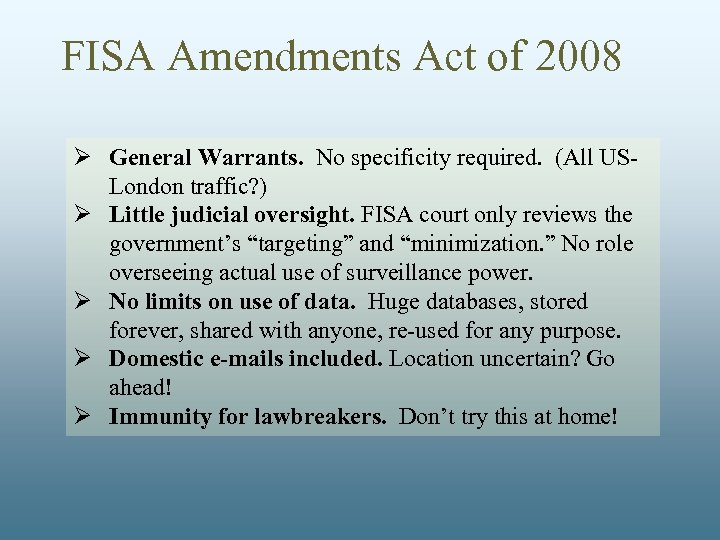 FISA Amendments Act of 2008 Ø General Warrants. No specificity required. (All USLondon traffic? ) Ø Little judicial oversight. FISA court only reviews the government’s “targeting” and “minimization. ” No role overseeing actual use of surveillance power. Ø No limits on use of data. Huge databases, stored forever, shared with anyone, re-used for any purpose. Ø Domestic e-mails included. Location uncertain? Go ahead! Ø Immunity for lawbreakers. Don’t try this at home!
FISA Amendments Act of 2008 Ø General Warrants. No specificity required. (All USLondon traffic? ) Ø Little judicial oversight. FISA court only reviews the government’s “targeting” and “minimization. ” No role overseeing actual use of surveillance power. Ø No limits on use of data. Huge databases, stored forever, shared with anyone, re-used for any purpose. Ø Domestic e-mails included. Location uncertain? Go ahead! Ø Immunity for lawbreakers. Don’t try this at home!
 Cybersecurity
Cybersecurity
 The challenge to our privacy: Technology revolution A burgeoning security establishment Profit Motives
The challenge to our privacy: Technology revolution A burgeoning security establishment Profit Motives
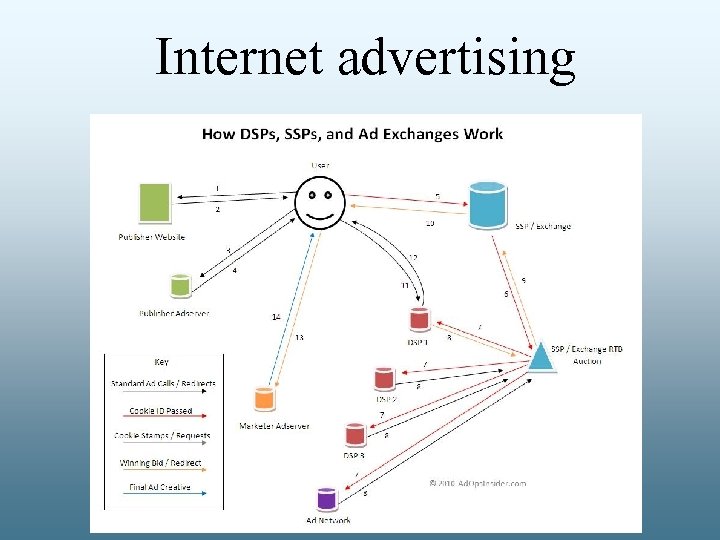 Internet advertising
Internet advertising
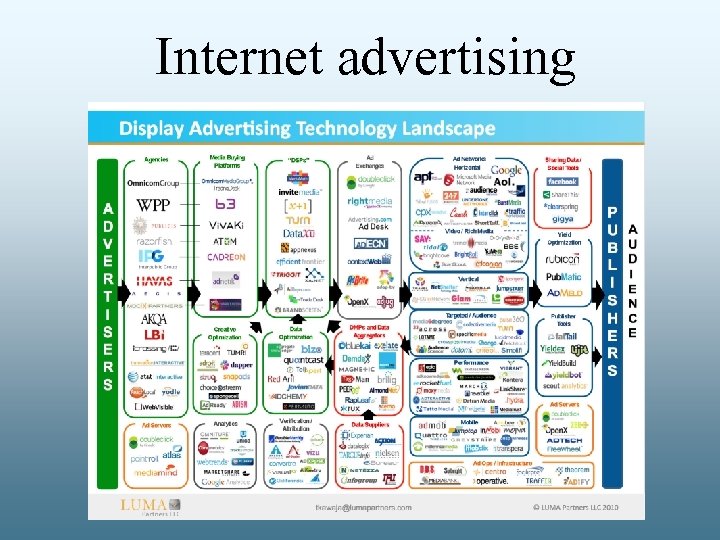 Internet advertising
Internet advertising
 Data brokers & “big data”
Data brokers & “big data”
 www. aclu. org/freefuture
www. aclu. org/freefuture
 An emerging surveillanceindustrial complex q Recruiting or pressing private companies into service q Partnerships with data companies q Lobbying by companies for more surveillance
An emerging surveillanceindustrial complex q Recruiting or pressing private companies into service q Partnerships with data companies q Lobbying by companies for more surveillance
 Many options for accessing private data 1. 2. 3. 4. 5. Ask for data to be shared voluntarily Simply buy information Demand it using legal powers “Bake in” surveillance Create regularized systems for standing access to records of private activities
Many options for accessing private data 1. 2. 3. 4. 5. Ask for data to be shared voluntarily Simply buy information Demand it using legal powers “Bake in” surveillance Create regularized systems for standing access to records of private activities
 Are we ready for all this?
Are we ready for all this?
 Jurisprudence off-track Reasonable expectation” standard Third-party doctrine
Jurisprudence off-track Reasonable expectation” standard Third-party doctrine
 Arbitrary situation
Arbitrary situation
 Congress isn’t keeping up either: Just a few things have changed since ECPA drafted in 1986… 1990: World Wide Web created 1994: Yahoo & Amazon founded 1998: Google founded 2004: Facebook launched
Congress isn’t keeping up either: Just a few things have changed since ECPA drafted in 1986… 1990: World Wide Web created 1994: Yahoo & Amazon founded 1998: Google founded 2004: Facebook launched
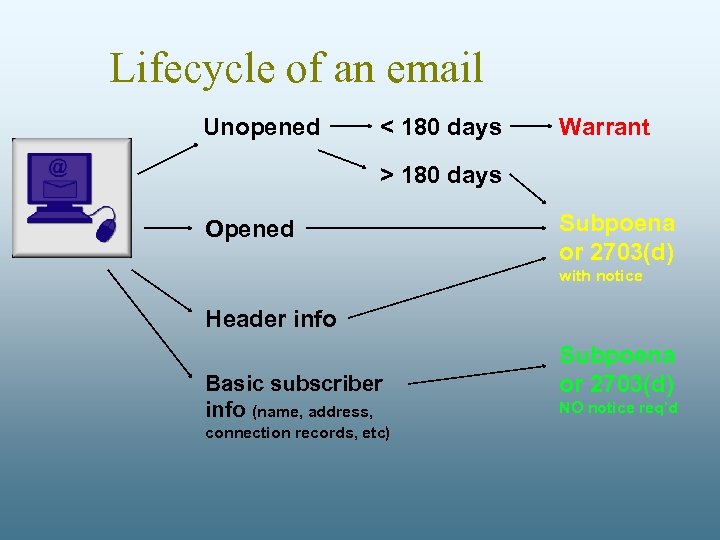 Lifecycle of an email Unopened < 180 days Warrant > 180 days Opened Subpoena or 2703(d) with notice Header info Basic subscriber info (name, address, connection records, etc) Subpoena or 2703(d) NO notice req’d
Lifecycle of an email Unopened < 180 days Warrant > 180 days Opened Subpoena or 2703(d) with notice Header info Basic subscriber info (name, address, connection records, etc) Subpoena or 2703(d) NO notice req’d
 And email was one of the specific technologies that existed in 1986! What about… Ø Search Ø Location-based services Ø Cloud Computing
And email was one of the specific technologies that existed in 1986! What about… Ø Search Ø Location-based services Ø Cloud Computing
 FISA Amendments Act
FISA Amendments Act
 How this plays forward 1. Behavior changes
How this plays forward 1. Behavior changes
 Human are social animals Constantly monitoring, finely aware of how we’re perceived by those around us
Human are social animals Constantly monitoring, finely aware of how we’re perceived by those around us
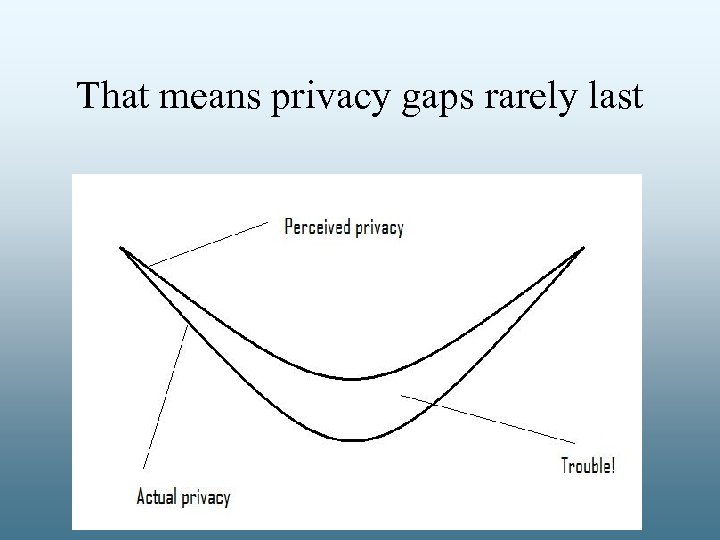 That means privacy gaps rarely last
That means privacy gaps rarely last
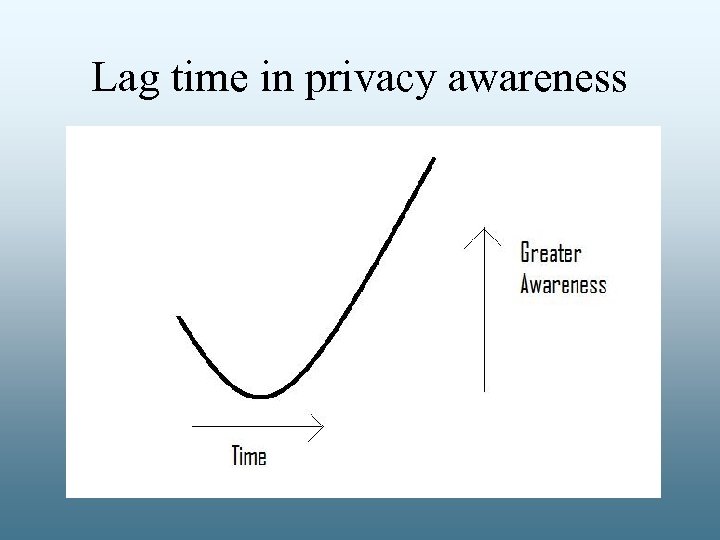 Lag time in privacy awareness
Lag time in privacy awareness
 Chilling Effects: The Facebook “blandification” effect
Chilling Effects: The Facebook “blandification” effect
 Chilling effects can also be spurred by many technologies • Surveillance cameras • Government eavesdropping • Offline data collection
Chilling effects can also be spurred by many technologies • Surveillance cameras • Government eavesdropping • Offline data collection
 How this plays forward 1. Behavior changes
How this plays forward 1. Behavior changes
 How this plays forward 1. Behavior changes 2. Law/practice changes
How this plays forward 1. Behavior changes 2. Law/practice changes
 Where we just find invasions intolerable and change the world to end them • ECPA reform • Commercial privacy regulation • Drone regulation
Where we just find invasions intolerable and change the world to end them • ECPA reform • Commercial privacy regulation • Drone regulation
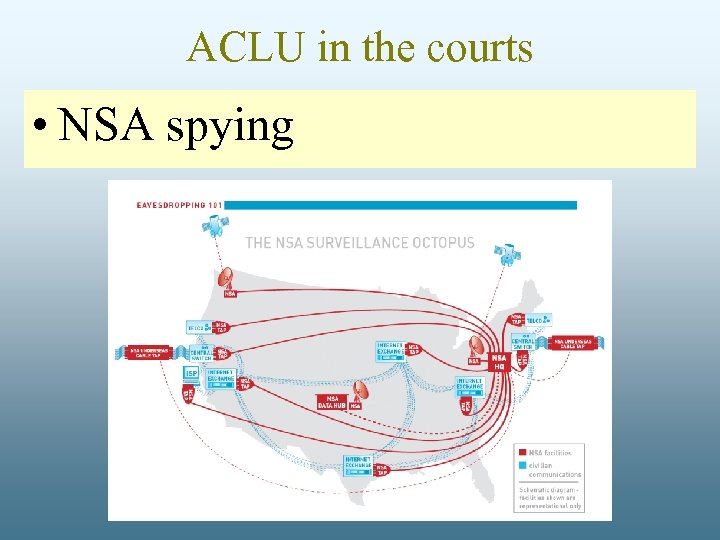 ACLU in the courts • NSA spying
ACLU in the courts • NSA spying
 ACLU in the courts • National Security Letters
ACLU in the courts • National Security Letters
 ACLU in the courts • Cell phone location data
ACLU in the courts • Cell phone location data
 ACLU in the courts • Laptops at the border
ACLU in the courts • Laptops at the border
 How this plays forward 1. Behavior changes 2. Law/practice changes
How this plays forward 1. Behavior changes 2. Law/practice changes
 How this plays forward 1. Behavior changes 2. Law/practice changes 3. Expectations change
How this plays forward 1. Behavior changes 2. Law/practice changes 3. Expectations change
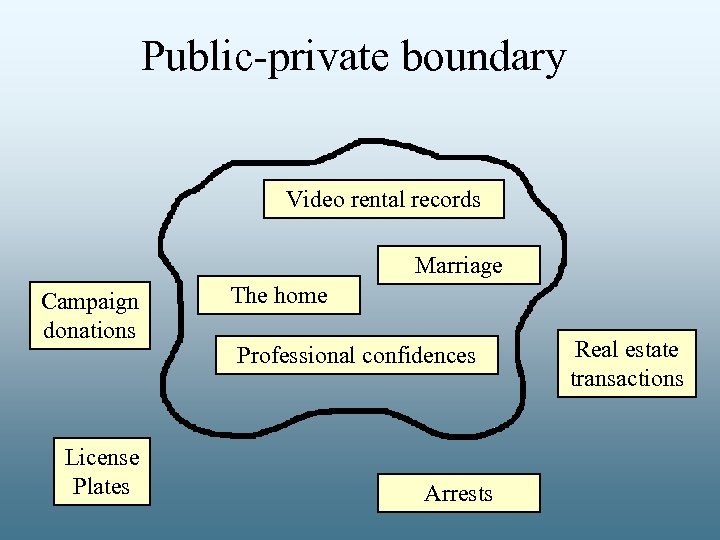 Public-private boundary Video rental records Marriage Campaign donations License Plates The home Professional confidences Arrests Real estate transactions
Public-private boundary Video rental records Marriage Campaign donations License Plates The home Professional confidences Arrests Real estate transactions
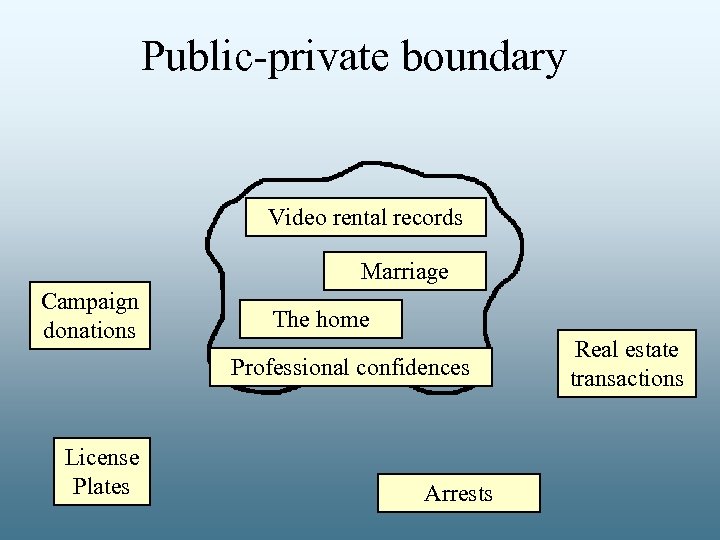 Public-private boundary Video rental records Marriage Campaign donations The home Professional confidences License Plates Arrests Real estate transactions
Public-private boundary Video rental records Marriage Campaign donations The home Professional confidences License Plates Arrests Real estate transactions
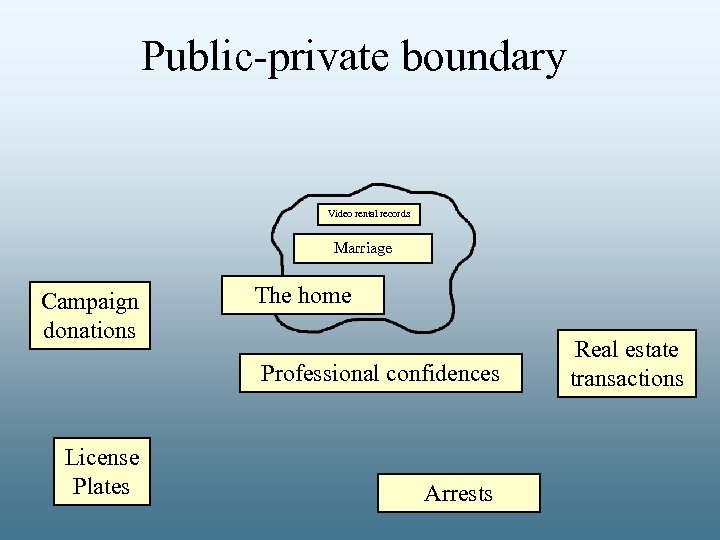 Public-private boundary Video rental records Marriage Campaign donations The home Professional confidences License Plates Arrests Real estate transactions
Public-private boundary Video rental records Marriage Campaign donations The home Professional confidences License Plates Arrests Real estate transactions
 How this plays forward 1. Behavior changes 2. Law/practice changes 3. Expectations change
How this plays forward 1. Behavior changes 2. Law/practice changes 3. Expectations change
 How this plays forward 1. Behavior changes 2. Law/practice changes 3. Expectations change 4. Things just get worse
How this plays forward 1. Behavior changes 2. Law/practice changes 3. Expectations change 4. Things just get worse
 III. WHAT MUST BE DONE?
III. WHAT MUST BE DONE?
 What Must Be Done? 1. Enact comprehensive privacy laws
What Must Be Done? 1. Enact comprehensive privacy laws
 What Must Be Done? 2. Enact technology-specific privacy laws
What Must Be Done? 2. Enact technology-specific privacy laws
 What Must Be Done? 3. Create institutions to enforce privacy laws
What Must Be Done? 3. Create institutions to enforce privacy laws
 What Must Be Done? 4. Revive the 4 th Amendment
What Must Be Done? 4. Revive the 4 th Amendment

 Contact info: Jay Stanley Speech, Privacy and Technology Program Free Future blog: www. aclu. org/nationalsecurity/amnesty-et-al-v-clapper jstanley@aclu. org 202 -715 -0818
Contact info: Jay Stanley Speech, Privacy and Technology Program Free Future blog: www. aclu. org/nationalsecurity/amnesty-et-al-v-clapper jstanley@aclu. org 202 -715 -0818
 asdf ASDF
asdf ASDF

 asdf
asdf


