 The Design of E-Traveler’s Check with Efficiency and Mutual Authentication Chair Professor Chin-Chen Chang Feng Chia University National Chung Cheng University National Tsing Hua University http: //msn. iecs. fcu. edu. tw/~ccc
The Design of E-Traveler’s Check with Efficiency and Mutual Authentication Chair Professor Chin-Chen Chang Feng Chia University National Chung Cheng University National Tsing Hua University http: //msn. iecs. fcu. edu. tw/~ccc
 Outline Ø Introduction Ø Proposed scheme Ø Discussions Ø Conclusions 2
Outline Ø Introduction Ø Proposed scheme Ø Discussions Ø Conclusions 2
 Introduction (1/5) Ø Why do we need the traveler’s check? Ø Some risks in abroad travel Case 1 Don’t kill me! I give you all my own money. Freeze! Give me some money or costly goods. robber traveler 3
Introduction (1/5) Ø Why do we need the traveler’s check? Ø Some risks in abroad travel Case 1 Don’t kill me! I give you all my own money. Freeze! Give me some money or costly goods. robber traveler 3
 Introduction (2/5) Case 2 Shopping shop traveler Walk fast Where is my wallet? traveler wallet 4
Introduction (2/5) Case 2 Shopping shop traveler Walk fast Where is my wallet? traveler wallet 4
 Introduction (3/5) ØMalicious guys may forge people’s credit cards I want to buy some goods. OK! Thank you. Forgery credit card Malicious man Sales man ØWe need traveler’s check to mitigate possible risks 5
Introduction (3/5) ØMalicious guys may forge people’s credit cards I want to buy some goods. OK! Thank you. Forgery credit card Malicious man Sales man ØWe need traveler’s check to mitigate possible risks 5
 Introduction (4/5) ØTraditional traveler’s check ØDeposit equivalent payment to bank issuing checks ØNeed to sign the traveler’s check and show their passport to the bank 6
Introduction (4/5) ØTraditional traveler’s check ØDeposit equivalent payment to bank issuing checks ØNeed to sign the traveler’s check and show their passport to the bank 6
 Introduction (5/5) ØTwo problems ØForging the traveler’s check or the passport ØImpersonating the legal check holder 7
Introduction (5/5) ØTwo problems ØForging the traveler’s check or the passport ØImpersonating the legal check holder 7
 Proposed scheme (1/7) ØLow computations ØMutual authentication 8
Proposed scheme (1/7) ØLow computations ØMutual authentication 8
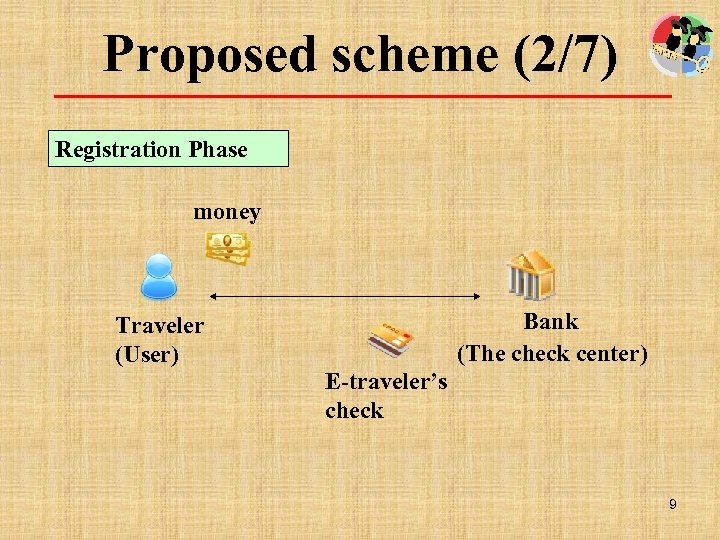 Proposed scheme (2/7) Registration Phase money Bank (The check center) Traveler (User) E-traveler’s check 9
Proposed scheme (2/7) Registration Phase money Bank (The check center) Traveler (User) E-traveler’s check 9
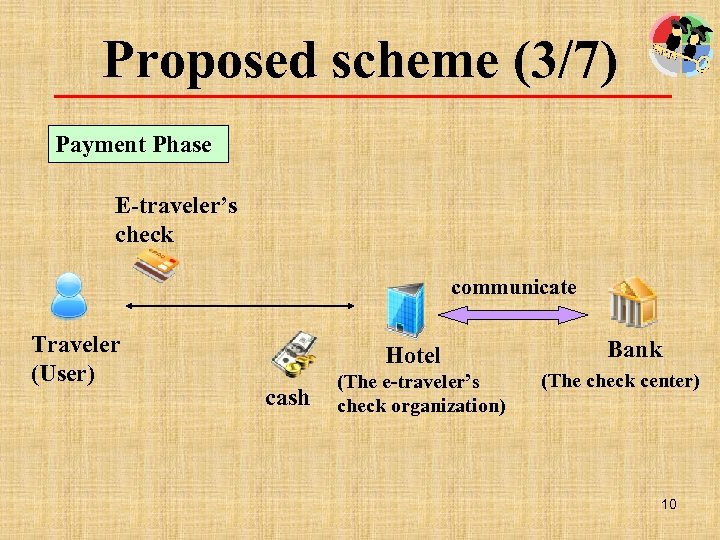 Proposed scheme (3/7) Payment Phase E-traveler’s check communicate Traveler (User) Hotel cash (The e-traveler’s check organization) Bank (The check center) 10
Proposed scheme (3/7) Payment Phase E-traveler’s check communicate Traveler (User) Hotel cash (The e-traveler’s check organization) Bank (The check center) 10
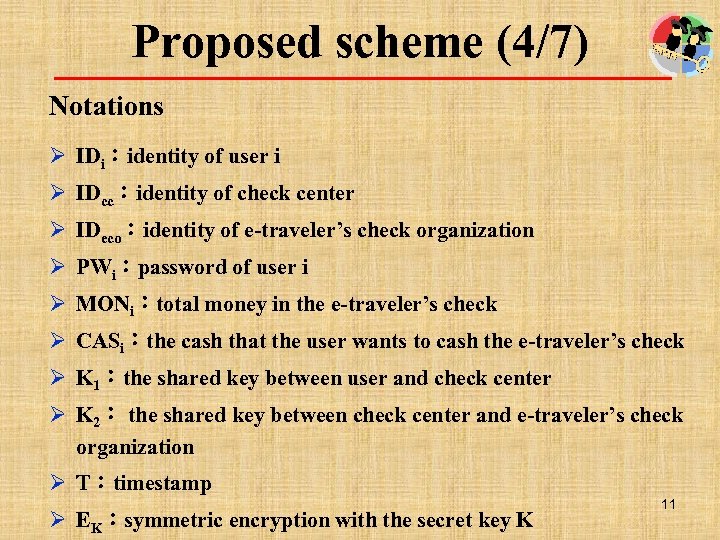 Proposed scheme (4/7) Notations Ø IDi:identity of user i Ø IDcc:identity of check center Ø IDeco:identity of e-traveler’s check organization Ø PWi:password of user i Ø MONi:total money in the e-traveler’s check Ø CASi:the cash that the user wants to cash the e-traveler’s check Ø K 1:the shared key between user and check center Ø K 2: the shared key between check center and e-traveler’s check organization Ø T:timestamp Ø EK:symmetric encryption with the secret key K 11
Proposed scheme (4/7) Notations Ø IDi:identity of user i Ø IDcc:identity of check center Ø IDeco:identity of e-traveler’s check organization Ø PWi:password of user i Ø MONi:total money in the e-traveler’s check Ø CASi:the cash that the user wants to cash the e-traveler’s check Ø K 1:the shared key between user and check center Ø K 2: the shared key between check center and e-traveler’s check organization Ø T:timestamp Ø EK:symmetric encryption with the secret key K 11
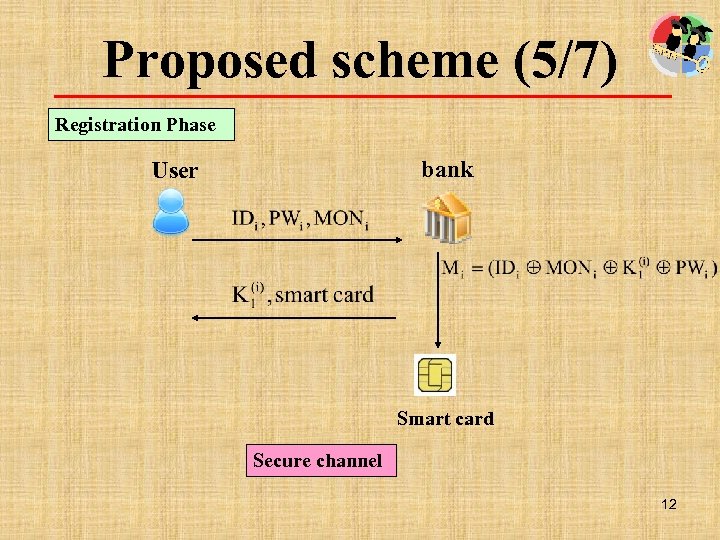 Proposed scheme (5/7) Registration Phase bank User Smart card Secure channel 12
Proposed scheme (5/7) Registration Phase bank User Smart card Secure channel 12
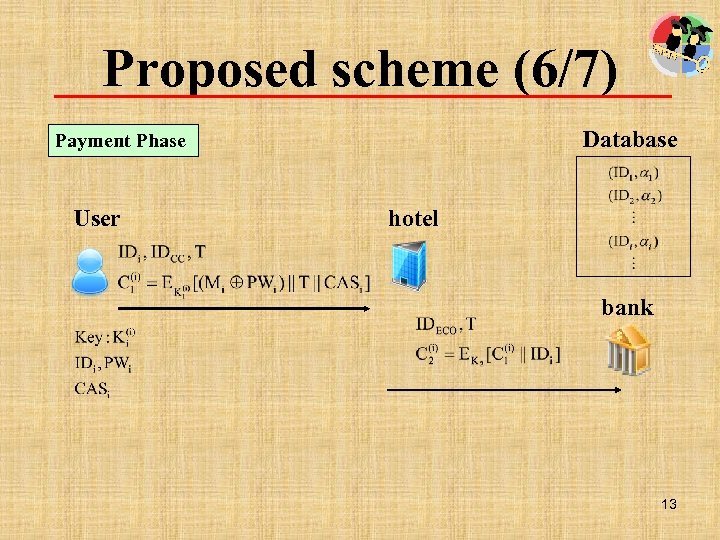 Proposed scheme (6/7) Database Payment Phase User hotel bank 13
Proposed scheme (6/7) Database Payment Phase User hotel bank 13
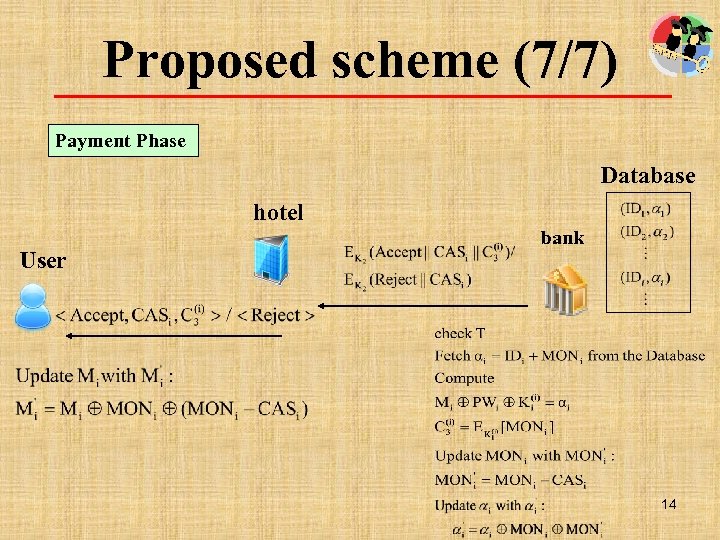 Proposed scheme (7/7) Payment Phase Database hotel User bank 14
Proposed scheme (7/7) Payment Phase Database hotel User bank 14
 Discussions (1/2) Ø Requirements: Ø The e-traveler’s check must have a unique identity Ø The e-traveler’s check can only be generated by the check-issuing bank or the authorized organization with the applicant Ø Only the legal check holder can have the e-traveler’s check cashed Ø The check-issuing bank, the check-cashing organization, and the e-traveler’s check holder can authenticate one another 15
Discussions (1/2) Ø Requirements: Ø The e-traveler’s check must have a unique identity Ø The e-traveler’s check can only be generated by the check-issuing bank or the authorized organization with the applicant Ø Only the legal check holder can have the e-traveler’s check cashed Ø The check-issuing bank, the check-cashing organization, and the e-traveler’s check holder can authenticate one another 15
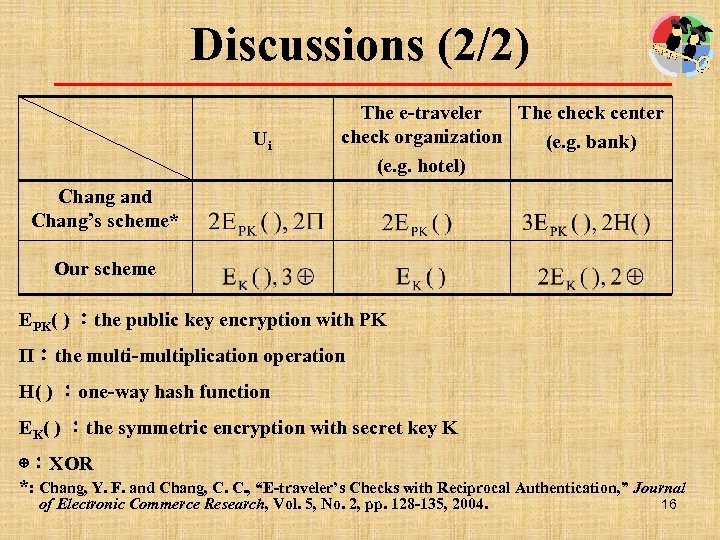 Discussions (2/2) Ui The e-traveler The check center check organization (e. g. bank) (e. g. hotel) Chang and Chang’s scheme* Our scheme EPK( ) :the public key encryption with PK Π:the multi-multiplication operation H( ) :one-way hash function EK( ) :the symmetric encryption with secret key K ⊕:XOR *: Chang, Y. F. and Chang, C. C. , “E-traveler’s Checks with Reciprocal Authentication, ” Journal of Electronic Commerce Research, Vol. 5, No. 2, pp. 128 -135, 2004. 16
Discussions (2/2) Ui The e-traveler The check center check organization (e. g. bank) (e. g. hotel) Chang and Chang’s scheme* Our scheme EPK( ) :the public key encryption with PK Π:the multi-multiplication operation H( ) :one-way hash function EK( ) :the symmetric encryption with secret key K ⊕:XOR *: Chang, Y. F. and Chang, C. C. , “E-traveler’s Checks with Reciprocal Authentication, ” Journal of Electronic Commerce Research, Vol. 5, No. 2, pp. 128 -135, 2004. 16
 Conclusions ØSimple and efficient ØMutual authentication 17
Conclusions ØSimple and efficient ØMutual authentication 17