f395888e3005f55447bf39afc35f526a.ppt
- Количество слайдов: 20
The Computer Labs are a valuable tool for learning at Challenger Middle School. While in the labs, students will • Follow appropriate code of conduct. • Adhere to copyright laws. • Practice safe Internet use.
Section 1 Rules of the Classroom
Store your books and personal items on the shelves provided as you come into the lab. There is not enough space next to the computers for these materials.
No food or drink is allowed in the computer lab.
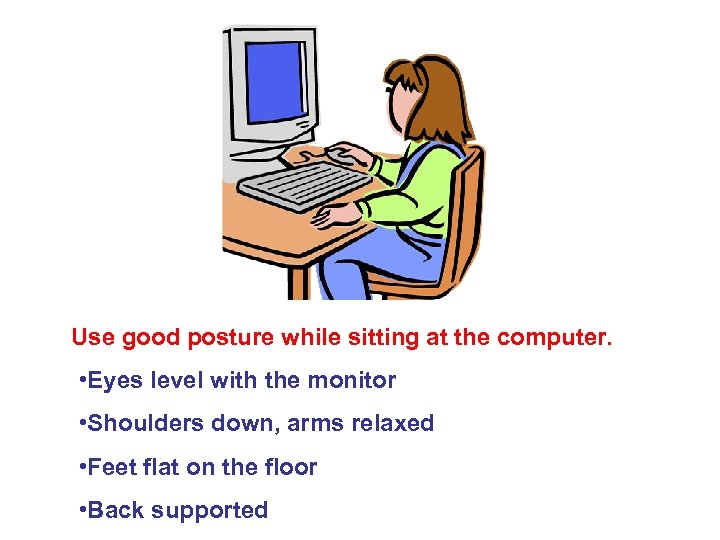
Use good posture while sitting at the computer. • Eyes level with the monitor • Shoulders down, arms relaxed • Feet flat on the floor • Back supported
The Computer Lab is a classroom. You are here to work on your assignment. You are not here to “play”. If you use the computer for any purpose other than your assignment, it will be considered computer misuse.
Students are not permitted to • • Change the desktop in any way. Change the screensaver. Delete, move, or rename any files. Install software downloaded from the Internet or any other source. • Open personal email accounts. • Install or open chat programs such as Instant Messenger. • Use computer games like Solitaire without teacher permission.
1 st Offense: Student is removed from computer for the rest of the class period and will work at a table. 2 nd Offense: Student is sent to In-House Suspension for remainder of class period. It is the classroom teacher’s decision to allow the student make up missed work. 3 rd Offense: Student has no more computer lab privileges. Students are responsible for repair or replacement of deliberately damaged equipment.
HACKING Unauthorized use of hardware or software can be considered to be “hacking. ” Huntsville City Schools Discipline Policy: Class 2 Offense (In or Out of School Suspension): When hacking does not cause damage to equipment and/or data. Class 3 Offense (Out of School Suspension or Expulsion): When hacking causes damage to equipment and/or data.
Section 2 Technology Ethics
Use good manners. Be polite. Have respect for the property of others. Be honest – do your own work.
(Insert a definition here from the cite below. ) © Merriam-Webster Dictionary http: //www. m-w. com/cgi-bin/dictionary Almost everything created after March 1, 1989 is protected by copyright. It does not have to have a copyright notice on it.
Music and software copyrighted. You buy the right to use the disc, but you do not own the product. It is illegal to copy CDs if you have not purchased the license to do so.
Information, pictures, and music acquired from the Internet is copyrighted. Students must cite the source of reference information and images used in multimedia presentations. Pictures must have copyright information next to the image: (Insert an image of Mickey Mouse here from the source on the next slide. If a different image is used, be sure to change the example on the next slide. )
When information is acquired from a website, the website author and Internet address of the site must be “cited” in a bibliography, works cited slide, etc. Example: "Mickey Mouse. " Britannica Student Encyclopedia. 2003. Encyclopædia Britannica Online. 17 June 2003. http: //search. eb. com/ebi/article? eu=354813.
Section 3 Internet Safety
Stay Safe While you Surf… • Never reveal personal information about yourself (name, address, age, phone number). • Never give anyone your Social Security number, credit card numbers, or your parents’ names. • Never arrange to meet someone face-to-face you have only met on-line. • Don’t share photos of yourself with someone you have only met on-line. • Don’t share passwords with anyone except your parents and teachers.
Computer Lab attendance is a privilege you should not take for granted. Following the guidelines presented today will help you have a successful experience.
f395888e3005f55447bf39afc35f526a.ppt