9bef198fd8e99fd8f39e7ac3a684e2c4.ppt
- Количество слайдов: 52
Testing with Production Data? Best Practices in Data Privacy Luis Gasca, CIPP Data Management Specialist Copyright © 2007 Compuware Corporation. All rights ® reserved.
Abstract • Data privacy regulations, mitigating the risk of Personally Identifiable Information (PII) exposure, managing privacy policies throughout the data life cycle and obtaining privacy audit certifications are part of today’s IT priorities. • Research indicates that the greater privacy threats reside internally within an organization. Protecting sensitive data is paramount not only for production purposes, but also during application testing and quality assurance • Implementing business solutions for data privacy is usually a complex endeavor. Simplification is achieved through proven process models and technology to effectively deploy depersonalized data, and in turn, minimize risks, meet regulation compliance and maintain customer trust. 2 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Session Objectives • Inform the DB 2 Forum audience about the business needs for Data Privacy. • Describe the challenges and illustrate the opportunities in the management of Personally Identifiable Information for non-production purposes. • Provide IT professionals with practical advice to enable them to achieve better business results through implementation of Data Privacy solutions based on proven technology and best practice process models. 3 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Agenda • Information Privacy − Business drivers − Regulatory landscape & trends − Business impact • Privacy Challenges − Privacy threats − Corporate privacy • Practical Approach to Data Privacy − Standards, processes, practices − Project life cycle − Development life cycle − Privacy technology for DB 2 • Conclusions − Opportunities − Business benefits 4 Copyright © 2007 Compuware Corporation. All rights ® reserved.
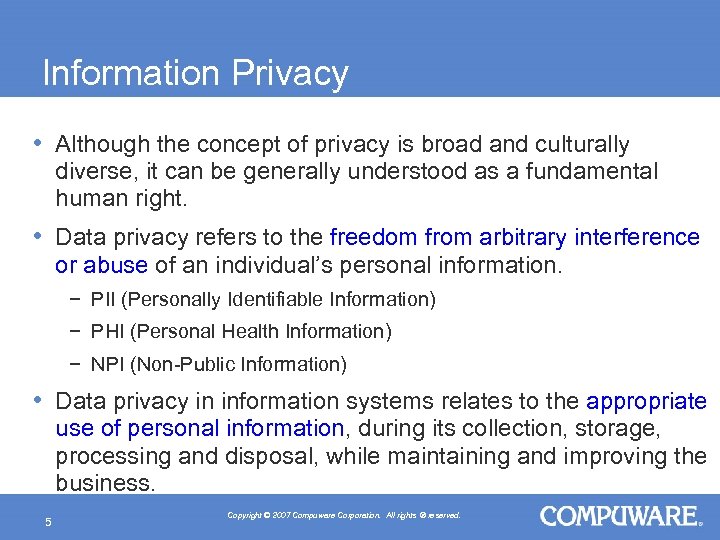
Information Privacy • Although the concept of privacy is broad and culturally diverse, it can be generally understood as a fundamental human right. • Data privacy refers to the freedom from arbitrary interference or abuse of an individual’s personal information. − PII (Personally Identifiable Information) − PHI (Personal Health Information) − NPI (Non-Public Information) • Data privacy in information systems relates to the appropriate use of personal information, during its collection, storage, processing and disposal, while maintaining and improving the business. 5 Copyright © 2007 Compuware Corporation. All rights ® reserved.
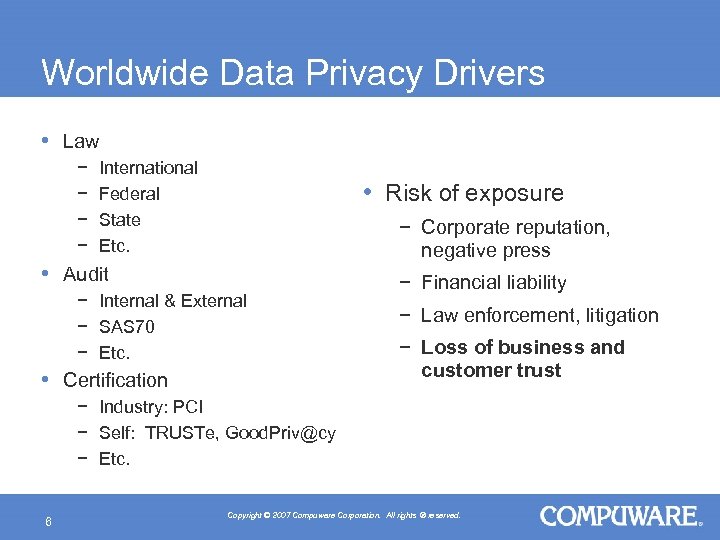
Worldwide Data Privacy Drivers • Law − − International Federal State Etc. • Risk of exposure − Corporate reputation, negative press • Audit − Internal & External − SAS 70 − Etc. • Certification − Financial liability − Law enforcement, litigation − Loss of business and customer trust − Industry: PCI − Self: TRUSTe, Good. Priv@cy − Etc. 6 Copyright © 2007 Compuware Corporation. All rights ® reserved.

Regulatory Landscape − United States • Gramm-Leach-Bliley Act • Dept. Of Commerce Safe Harbor Provision • Fair Credit Reporting Act • Health Insurance Portability and Accountability Act (HIPAA) • California SB 1386 − European Union Personal Data Protection Directive, 1998 − Australia Privacy Amendment Act of 2000 − Japanese Personal Information Protection Law − Canadian Personal Information Protection and Electronic Documents Act (PIPEDA) − Etc. 7 Copyright © 2007 Compuware Corporation. All rights ® reserved.
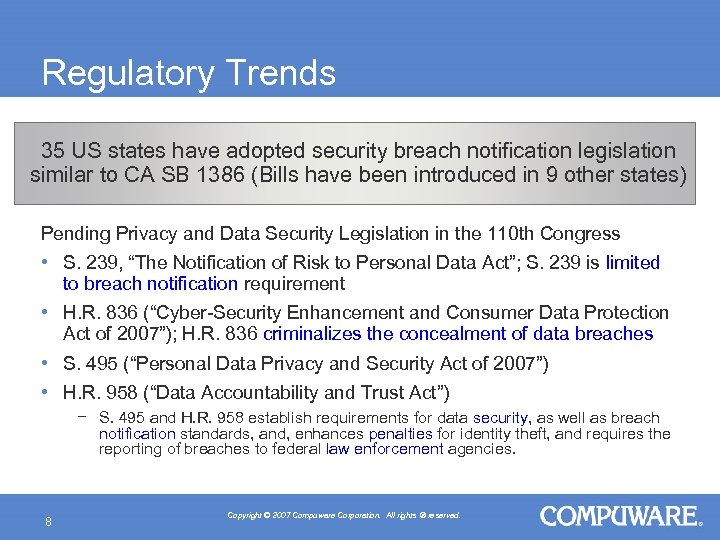
Regulatory Trends 35 US states have adopted security breach notification legislation similar to CA SB 1386 (Bills have been introduced in 9 other states) Pending Privacy and Data Security Legislation in the 110 th Congress • S. 239, “The Notification of Risk to Personal Data Act”; S. 239 is limited to breach notification requirement • H. R. 836 (“Cyber-Security Enhancement and Consumer Data Protection Act of 2007”); H. R. 836 criminalizes the concealment of data breaches • S. 495 (“Personal Data Privacy and Security Act of 2007”) • H. R. 958 (“Data Accountability and Trust Act”) − S. 495 and H. R. 958 establish requirements for data security, as well as breach notification standards, and, enhances penalties for identity theft, and requires the reporting of breaches to federal law enforcement agencies. 8 Copyright © 2007 Compuware Corporation. All rights ® reserved.
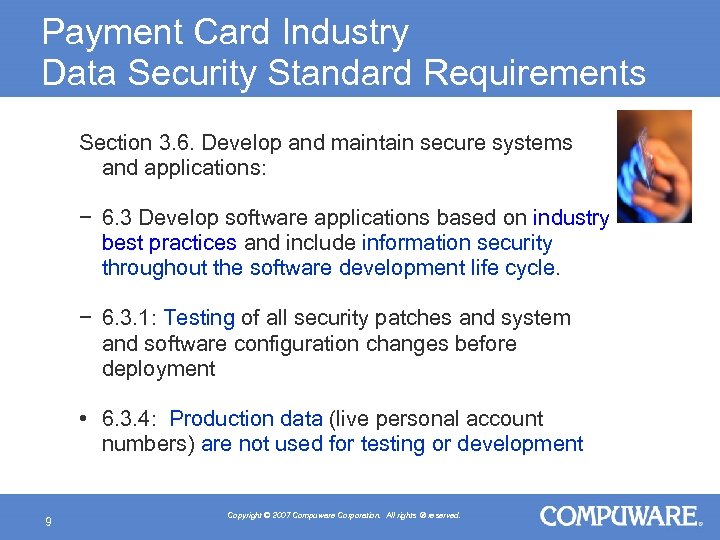
Payment Card Industry Data Security Standard Requirements Section 3. 6. Develop and maintain secure systems and applications: − 6. 3 Develop software applications based on industry best practices and include information security throughout the software development life cycle. − 6. 3. 1: Testing of all security patches and system and software configuration changes before deployment • 6. 3. 4: Production data (live personal account numbers) are not used for testing or development 9 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Why Should Businesses Care? • Penalties for non-compliance to PCI 1. 1! − Possible restrictions on the merchant or permanent prohibition of the merchant’s participation in credit card programs − No credit cards means no business for many − Starting October 1 st, 2007: New fine structure that starts at $10, 000 per month and can go as high as $100, 000 per month! • PCI its becoming the law ! Adoption of PCI standard by the State of Minnesota as a state law, in review in other state legislatures, like Texas. 10 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Business Impact • 217 Million Consumers Impacted through 12 -31 -2007* • The catalyst for reporting data breaches to the affected individuals has been the California law that requires notice of security breaches, the first of its kind in the nation, implemented July 2003. • Personal information compromised includes data elements useful for identity theft, such as Social Security numbers, account numbers, and driver's license numbers. *A Chronology of Data Breaches Reported Since the Choice. Point Incident Privacy Rights Clearinghouse, April 8, 2007 11 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Business Impact Ponemon Institute estimates an average cost of $6. 3 M per security breach incident • Study examines costs incurred by 35 companies after experiencing a data breach • Breaches ranged from less than 4, 000 records to more than 125, 000 records • The average cost per lost customer record was $197 U. S. in 2007, up 8% from 2006 • Breaches by third-party organizations such as outsourcers, contractors, consultants, and business partners were reported by 40% of respondents, up from 29% in 2006 • Cost of lost business increased more than 30%, averaging $4. 1 M or $128 per record compromised. Lost business accounts for 65% of data breach costs. Ponemon Institute 2007 Annual Study: Cost of a Data Breach 12 Copyright © 2007 Compuware Corporation. All rights ® reserved.
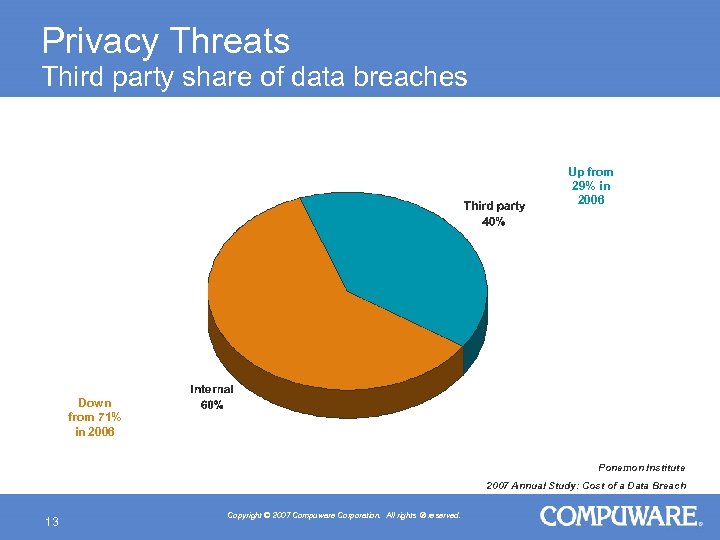
Privacy Threats Third party share of data breaches Up from 29% in 2006 Down from 71% in 2006 Ponemon Institute 2007 Annual Study: Cost of a Data Breach 13 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Privacy Threats “It is a serious mistake to think that mainframe applications are safe by default. They are not…. . Enterprises should not experience a false sense of security simply because their mission-critical applications run on mainframes. Yet, they are often defenseless against insiders equipped with in - depth knowledge of the applications' logic and security policies — those using legitimate means to ill-exploit the system. Most attacks on legacies come from inside the enterprises, committed by their own employees. . . Applications should be protected from the inside out. ” Joseph Feiman, Gartner Research, September 29 2006 Implementing Security for Mainframe Legacy Applications - Worth the Investment 14 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Corporate Privacy • Privacy Program − Corporate values − Organization goals − Consumer expectations − Employee commitment − Communication • Privacy Policy − Collection − Use − Choice − Security − Redress 15 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Corporate Privacy But … • How do you support your Privacy initiatives ? • How do you mitigate the risks ? 16 Copyright © 2007 Compuware Corporation. All rights ® reserved.
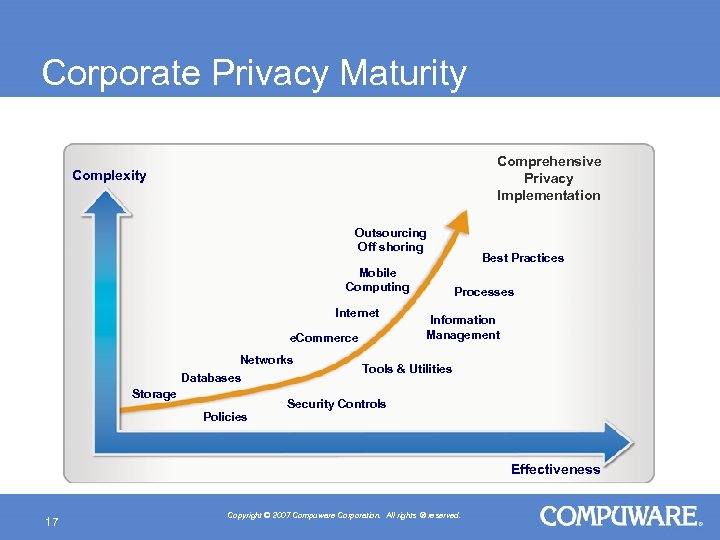
Corporate Privacy Maturity Comprehensive Privacy Implementation Complexity Outsourcing Off shoring Mobile Computing Internet e. Commerce Networks Databases Storage Policies Best Practices Processes Information Management Tools & Utilities Security Controls Effectiveness 17 Copyright © 2007 Compuware Corporation. All rights ® reserved.
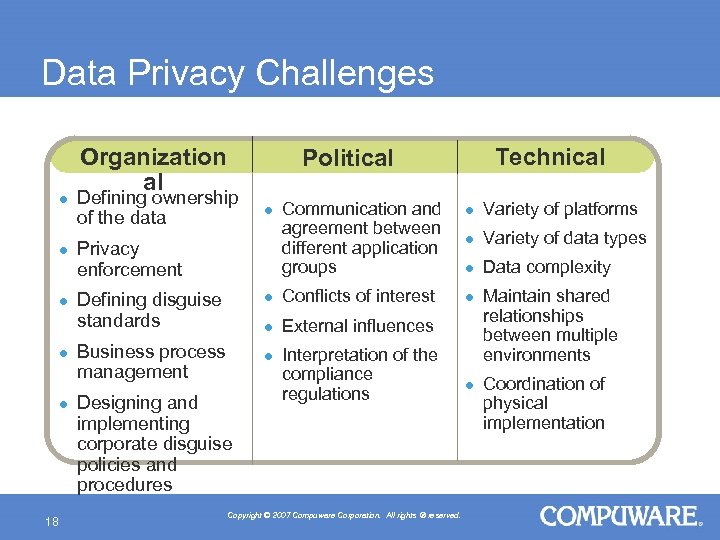
Data Privacy Challenges l l l 18 Organization al Technical Political Defining ownership of the data l Privacy enforcement Communication and Variety of platforms l agreement between l Variety of data types different application groups l Data complexity l Business process management Designing and implementing corporate disguise policies and procedures Conflicts of interest l Defining disguise standards External influences l l Maintain shared relationships between multiple environments Interpretation of the compliance l Coordination of regulations physical implementation Copyright © 2007 Compuware Corporation. All rights ® reserved.
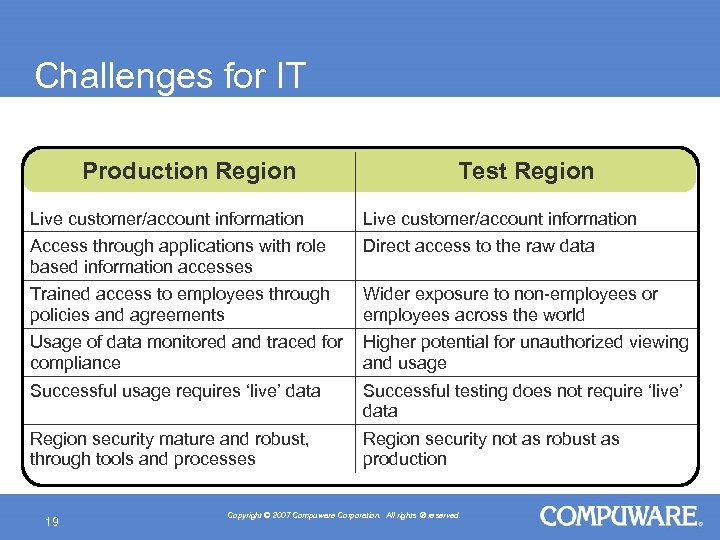
Challenges for IT Production Region Test Region Live customer/account information Access through applications with role based information accesses Direct access to the raw data Trained access to employees through policies and agreements Wider exposure to non-employees or employees across the world Usage of data monitored and traced for Higher potential for unauthorized viewing compliance and usage Successful usage requires ‘live’ data Successful testing does not require ‘live’ data Region security mature and robust, through tools and processes Region security not as robust as production 19 Copyright © 2007 Compuware Corporation. All rights ® reserved.

Supporting Corporate Privacy Initiatives Technology People Best Practices Methodology How do we get there ? 20 Copyright © 2007 Compuware Corporation. All rights ® reserved.
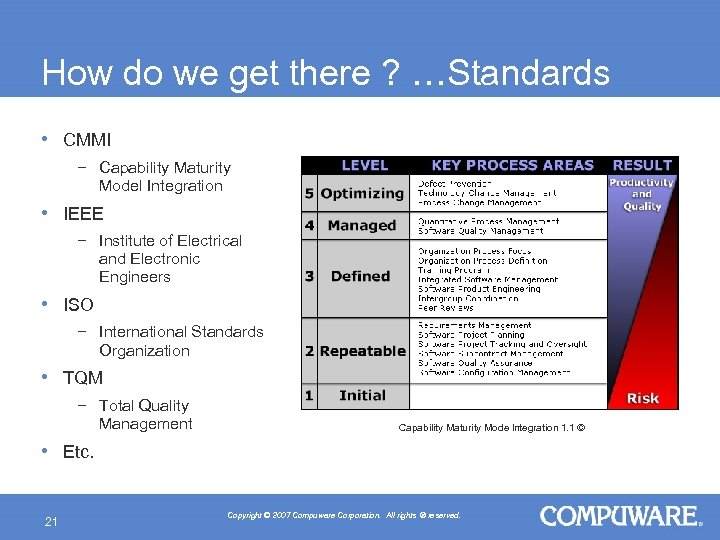
How do we get there ? …Standards • CMMI − Capability Maturity Model Integration • IEEE − Institute of Electrical and Electronic Engineers • ISO − International Standards Organization • TQM − Total Quality Management • Etc. Capability Maturity Mode lntegration 1. 1 © 21 Copyright © 2007 Compuware Corporation. All rights ® reserved.
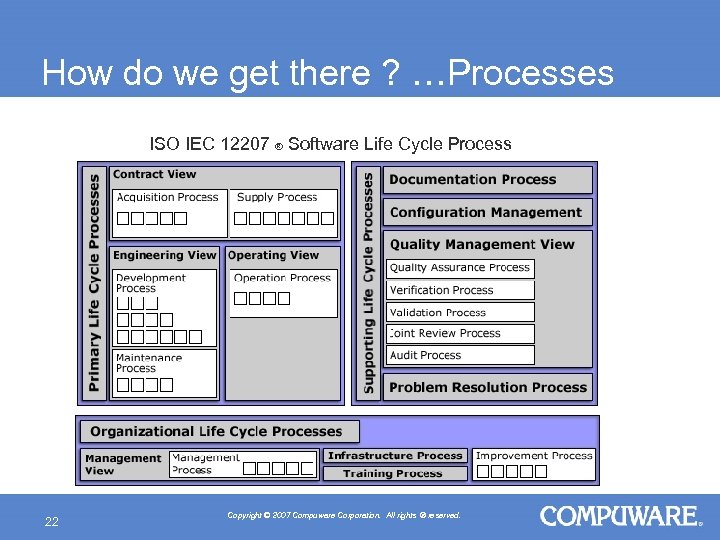
How do we get there ? …Processes ISO IEC 12207 ® Software Life Cycle Process 22 Copyright © 2007 Compuware Corporation. All rights ® reserved.
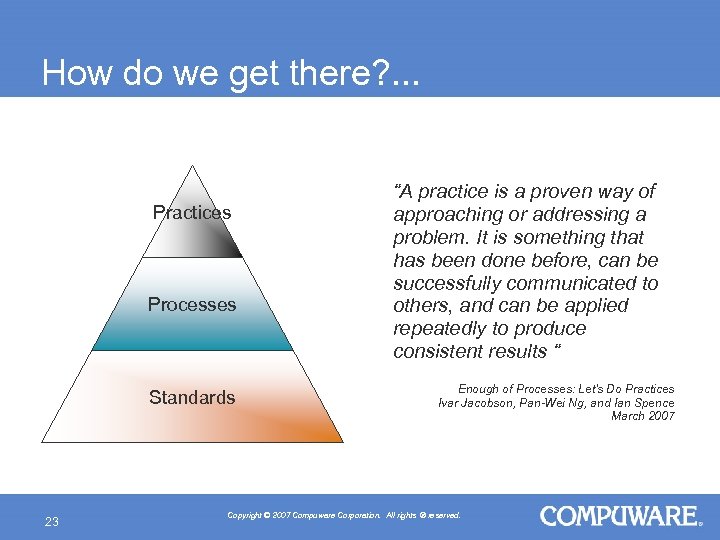
How do we get there? . . . Practices Processes Standards 23 “A practice is a proven way of approaching or addressing a problem. It is something that has been done before, can be successfully communicated to others, and can be applied repeatedly to produce consistent results “ Enough of Processes: Let's Do Practices Ivar Jacobson, Pan-Wei Ng, and Ian Spence March 2007 Copyright © 2007 Compuware Corporation. All rights ® reserved.
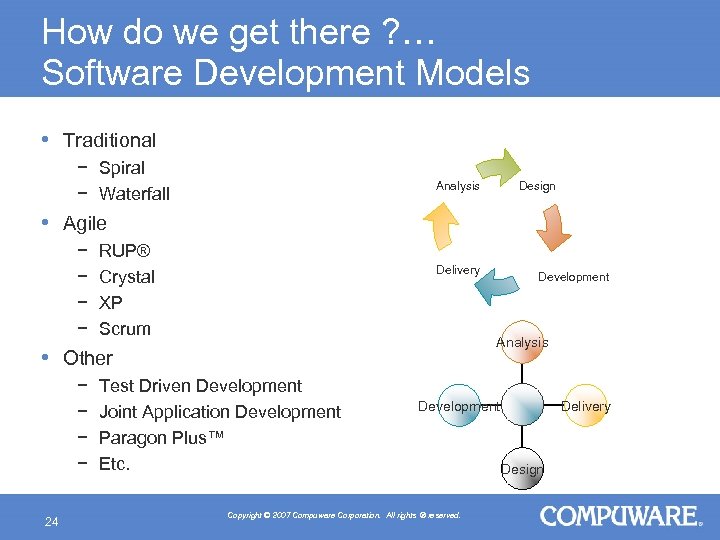
How do we get there ? … Software Development Models • Traditional − Spiral − Waterfall Design Analysis • Agile − − RUP® Crystal XP Scrum Delivery Analysis • Other − − 24 Development Test Driven Development Joint Application Development Paragon Plus™ Etc. Development Copyright © 2007 Compuware Corporation. All rights ® reserved. Delivery Design
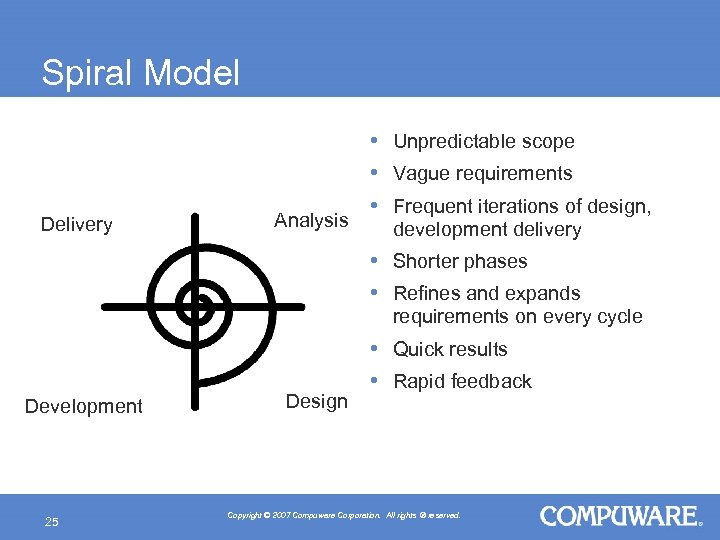
Spiral Model Delivery Analysis • Unpredictable scope • Vague requirements • Frequent iterations of design, development delivery • Shorter phases • Refines and expands requirements on every cycle Development 25 Design • Quick results • Rapid feedback Copyright © 2007 Compuware Corporation. All rights ® reserved.
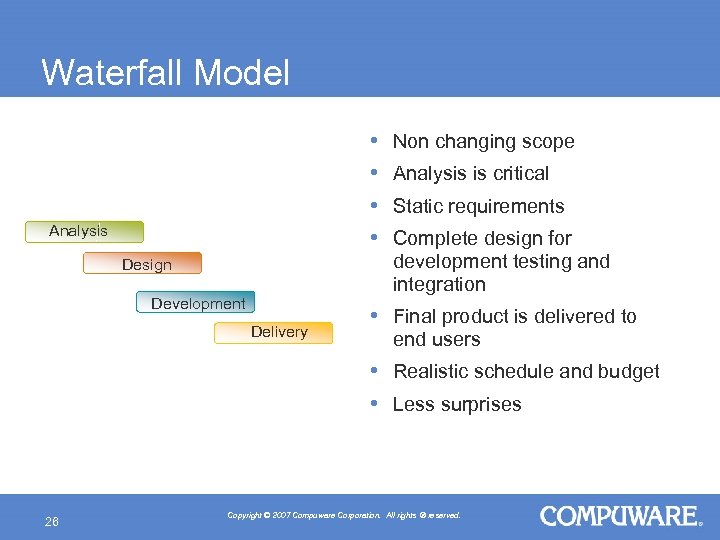
Waterfall Model • • Analysis Design Development Delivery Non changing scope Analysis is critical Static requirements Complete design for development testing and integration • Final product is delivered to end users • Realistic schedule and budget • Less surprises 26 Copyright © 2007 Compuware Corporation. All rights ® reserved.
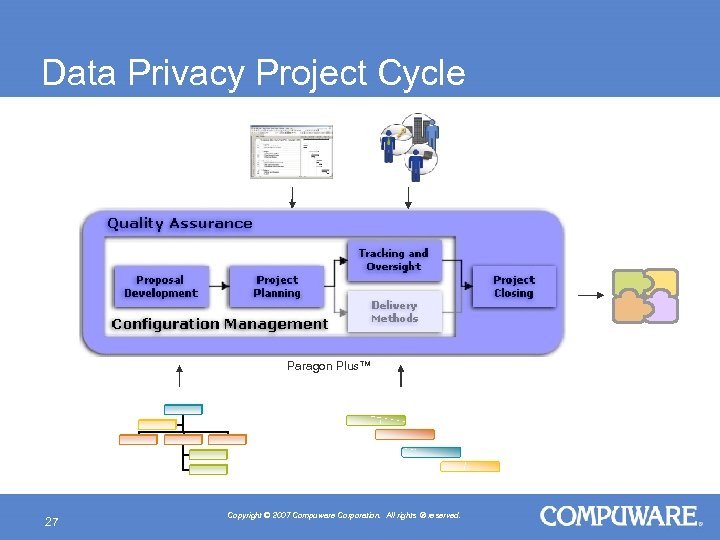
Data Privacy Project Cycle Paragon Plus™ 27 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Proposal Development • Executive Sponsorship − CEO, CSO, CPO, CIO − Legal Counsel • Strategic Direction • Organizational Plan − − • • 28 Compliance team Business SMEs Privacy team Quality Assurance team Risk Assessment Scope Analysis Project Definition Privacy Requirements Copyright © 2007 Compuware Corporation. All rights ® reserved.
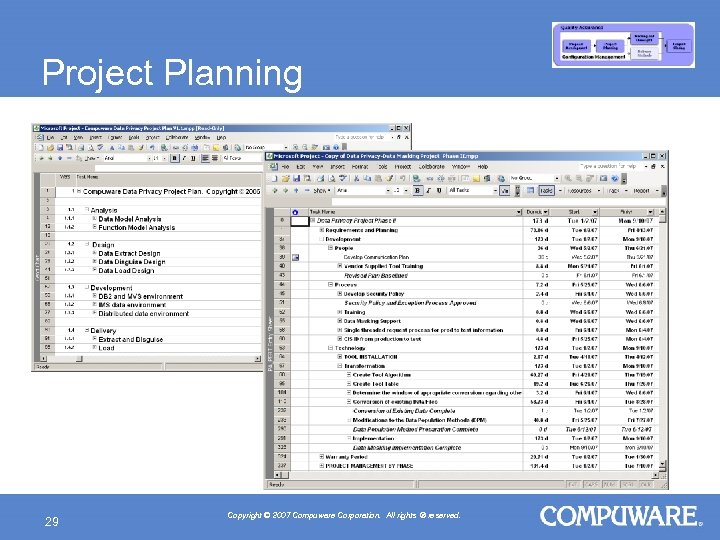
Project Planning 29 Copyright © 2007 Compuware Corporation. All rights ® reserved.
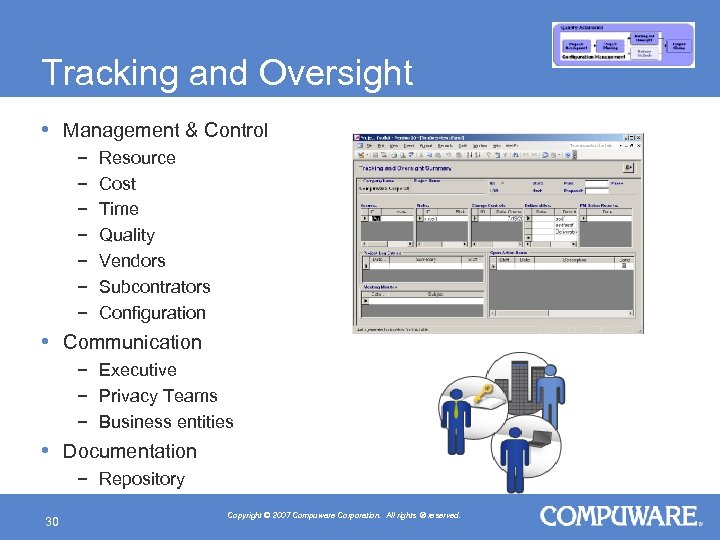
Tracking and Oversight • Management & Control − − − − Resource Cost Time Quality Vendors Subcontrators Configuration • Communication − Executive − Privacy Teams − Business entities • Documentation − Repository 30 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Delivery Method Analysis Design Development Implementation 31 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Analysis • What sensitive information do we have ? − PII, PHI, NPI • What are the protection requirements ? • What risks are we mitigating ? • Where is the sensitive information and where does it need to be protected ? • How is sensitive information processed ? • How is sensitive data used outside of production ? 32 Copyright © 2007 Compuware Corporation. All rights ® reserved.
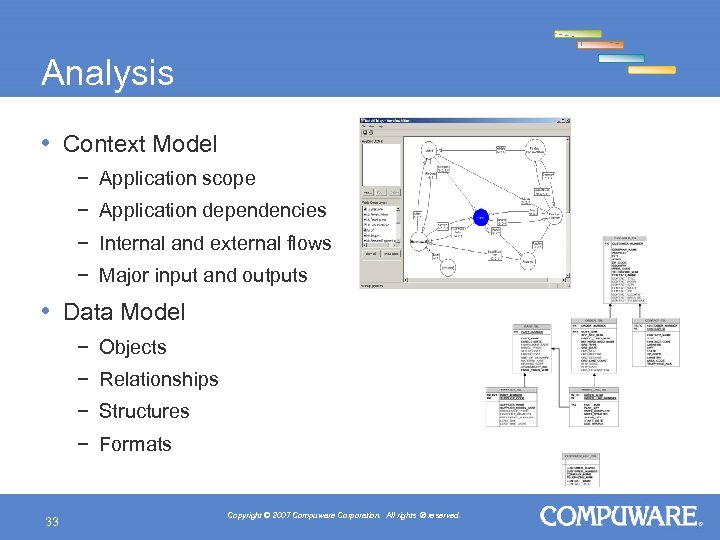
Analysis • Context Model − Application scope − Application dependencies − Internal and external flows − Major input and outputs • Data Model − Objects − Relationships − Structures − Formats 33 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Analysis • Function Model − Processes dependencies − Methods − States − Flows • QA Model − Test requirements − Environments − Migration paths − Test cases − Test scripts 34 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Design • Privacy implementation strategy • • • 35 Access to source data Extract criteria Privacy rules Delivery methods Security rules How will technology be used to support the process ? Copyright © 2007 Compuware Corporation. All rights ® reserved.
Design • Privacy architecture − Components − Configuration • Extract rules − Criteria specifications − Scope specifications • Privacy rules − Privacy techniques − Integrity − Consistency − Usability • Load rules • Technical Specifications 36 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Design Considerations • Integrity − Intact relationships and dependencies of data within and across applications. • Consistency − Repeatability of results regardless of data source. • Usability − Data should be valid for the business and meaningful to the users. 37 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Design Privacy Techniques • Scramble • • 38 − Replace sensitive values with formulated data based on a userdefined key. Translate − Replace sensitive values with meaningful, readable data from an alternate source. Mask − Ability to partially identify and conceal individual fragments of data. Age − Replace sensitive dates with calculated values accurately. Generate − Produce fictitious data from scratch using business oriented algorithms. Copyright © 2007 Compuware Corporation. All rights ® reserved.
Development Privacy Enabling Technology (PET) 39 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Development Privacy Enabling Technology (PET) or Write code 40 Use software products Copyright © 2007 Compuware Corporation. All rights ® reserved.
Development Privacy Enabling Technology • How does the PET address privacy requirements? − Data management − Privacy management − Auditing • How does the PET address testing requirements ? − Manipulation − Generation − Validation − Administration − Extract and load 41 Copyright © 2007 Compuware Corporation. All rights ® reserved.
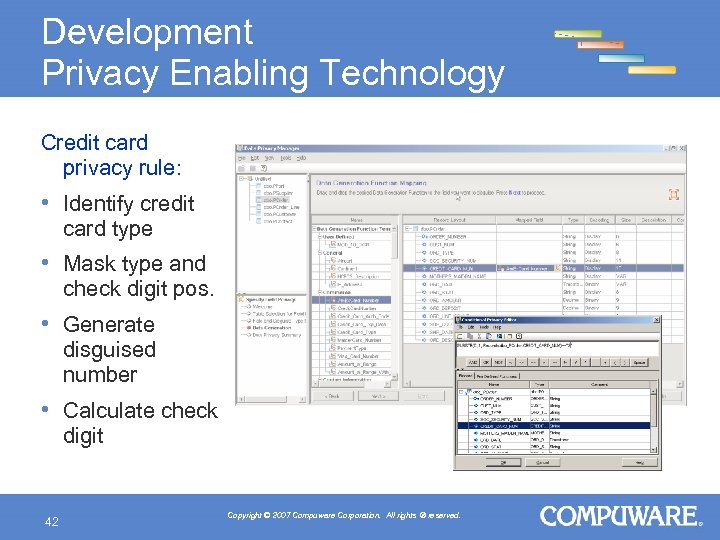
Development Privacy Enabling Technology Credit card privacy rule: • Identify credit card type • Mask type and check digit pos. • Generate disguised number • Calculate check digit 42 Copyright © 2007 Compuware Corporation. All rights ® reserved.
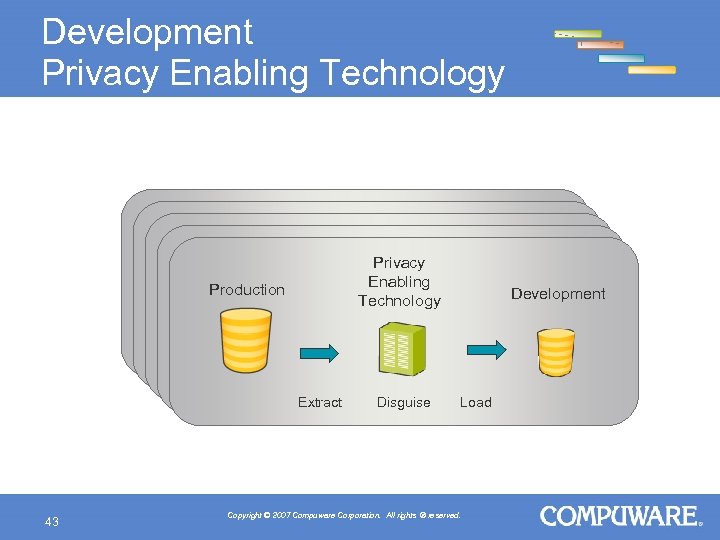
Development Privacy Enabling Technology Production Production Privacy Enabling Privacy Technology Enabling Technology Development Development Load Disguise Extract Load Disguise Extract 43 Copyright © 2007 Compuware Corporation. All rights ® reserved.
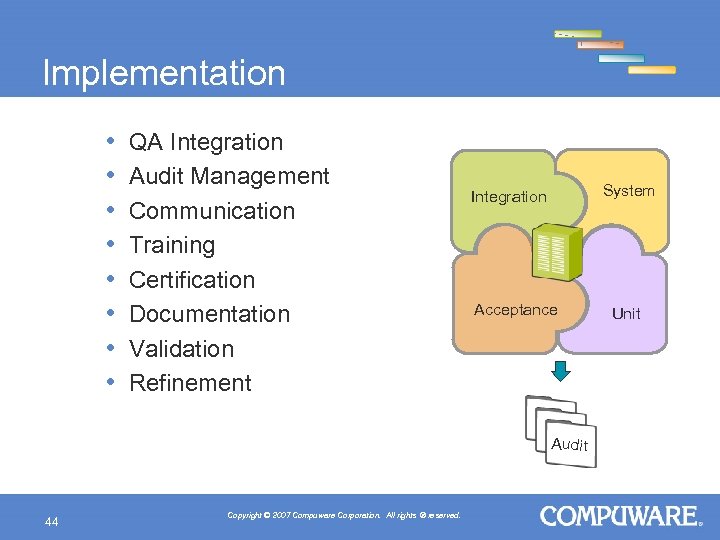
Implementation • • QA Integration Audit Management Communication Training Certification Documentation Validation Refinement System Integration Acceptance Audit 44 Copyright © 2007 Compuware Corporation. All rights ® reserved. Unit
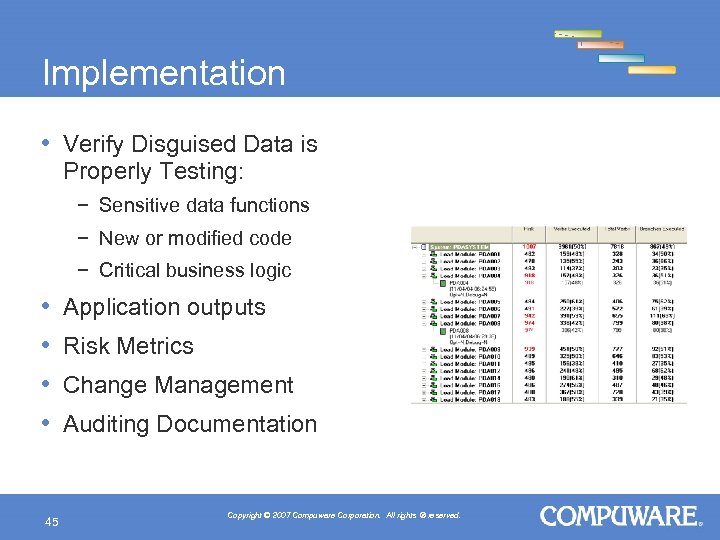
Implementation • Verify Disguised Data is Properly Testing: − Sensitive data functions − New or modified code − Critical business logic • • 45 Application outputs Risk Metrics Change Management Auditing Documentation Copyright © 2007 Compuware Corporation. All rights ® reserved.
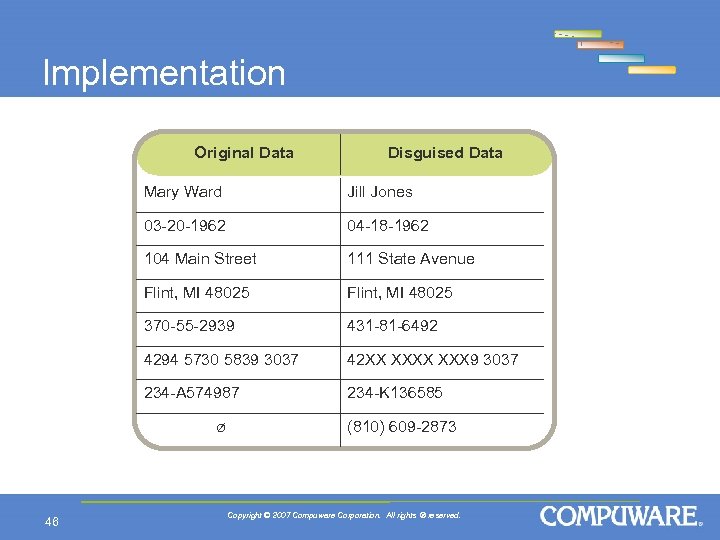
Implementation Original Data Disguised Data Mary Ward Jill Jones 03 -20 -1962 04 -18 -1962 104 Main Street 111 State Avenue Flint, MI 48025 370 -55 -2939 431 -81 -6492 4294 5730 5839 3037 42 XX XXX 9 3037 234 -A 574987 234 -K 136585 ø 46 (810) 609 -2873 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Data Privacy Project Closure Next steps: • • • Discuss lessons learned Assess and communicate data privacy results Use managed processes to bridge privacy gaps Formalize privacy roles and functions Identify improvements to employee, vendor and technology management • Prepare to respond to incidents • Use metrics for compliance 47 Copyright © 2007 Compuware Corporation. All rights ® reserved.
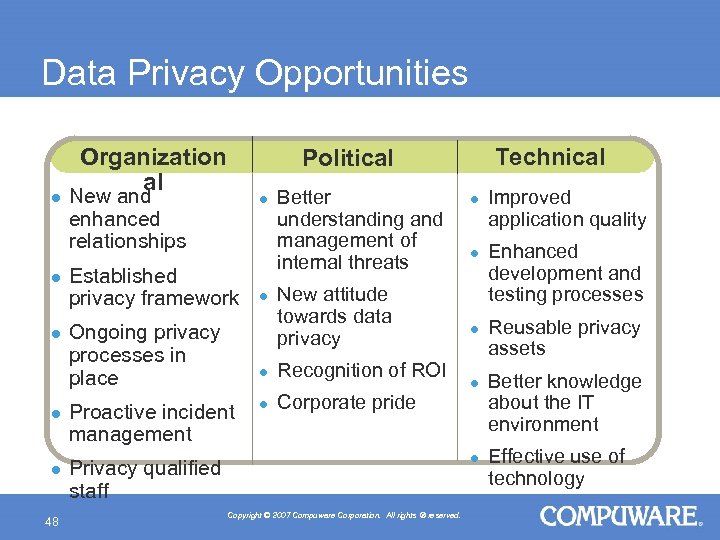
Data Privacy Opportunities l l l 48 Organization al Technical Political New and enhanced relationships l Established privacy framework Ongoing privacy processes in place l Better understanding and management of internal threats New attitude towards data privacy l Proactive incident management Recognition of ROI l l Corporate pride l l Privacy qualified staff Copyright © 2007 Compuware Corporation. All rights ® reserved. Improved application quality Enhanced development and testing processes Reusable privacy assets Better knowledge about the IT environment Effective use of technology
Benefits to the Business A Comprehensive Data Privacy Solution: • • • 49 Supports corporate privacy initiatives Simplifies the management of privacy projects Improves test data quality while maximizing efficiency Lowers cost of regulatory compliance Reduces risk and liability associated with data privacy Maintains customer trust and loyalty Copyright © 2007 Compuware Corporation. All rights ® reserved.
Conclusions • Organizations face internal risks they need to protect against • A comprehensive data privacy solution is key to compliance requirements • Use any variety of standards and methods that work for the business • Best practices are proven ways to achieve data privacy and provide for a blueprint to deliver results • Technology plays a critical role • Business is evolving, best practices should too • Partner with vendors with the ability to bridge gaps between software features and working solutions 50 Copyright © 2007 Compuware Corporation. All rights ® reserved.
Thank You ! Testing with Production Data? Best Practices in Data Privacy Luis Gasca, CIPP Data Management Specialist Compuware Corporation luis. gasca@compuware. com 51 Copyright © 2007 Compuware Corporation. All rights ® reserved.

9bef198fd8e99fd8f39e7ac3a684e2c4.ppt