 Testing the Tester Measuring Quality of Security Testing Ofer Maor CTO, Hacktics OWASP & OWASP Israel WASC App. Sec 2008 2007 Conference San Jose – Nov 2007 http: //www. webappsec. org/ Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/
Testing the Tester Measuring Quality of Security Testing Ofer Maor CTO, Hacktics OWASP & OWASP Israel WASC App. Sec 2008 2007 Conference San Jose – Nov 2007 http: //www. webappsec. org/ Copyright © 2007 - The OWASP Foundation Permission is granted to copy, distribute and/or modify this document under the terms of the Creative Commons Attribution-Share. Alike 2. 5 License. To view this license, visit http: //creativecommons. org/licenses/by-sa/2. 5/ The OWASP Foundation http: //www. owasp. org/
 Introduction
Introduction
 Introduction
Introduction
 Agenda
Agenda
 Quality of Security Testing OWASP Israel 2008 Conference – Sep 2008 5
Quality of Security Testing OWASP Israel 2008 Conference – Sep 2008 5
 Quality of Security Testing
Quality of Security Testing
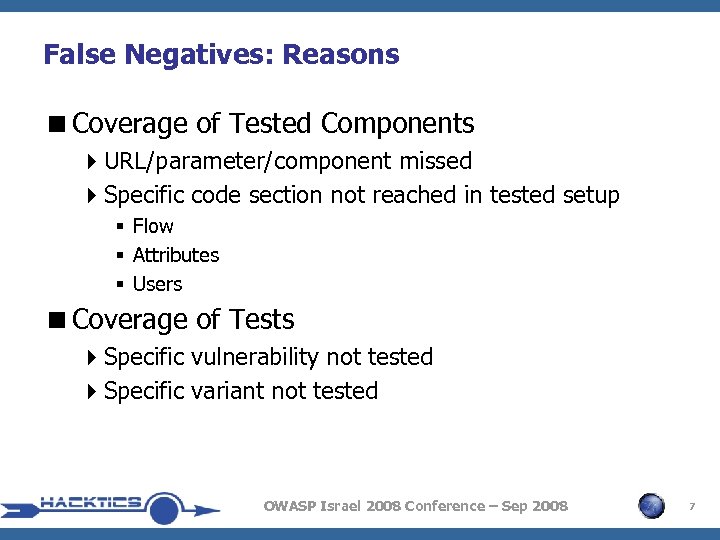 False Negatives: Reasons
False Negatives: Reasons
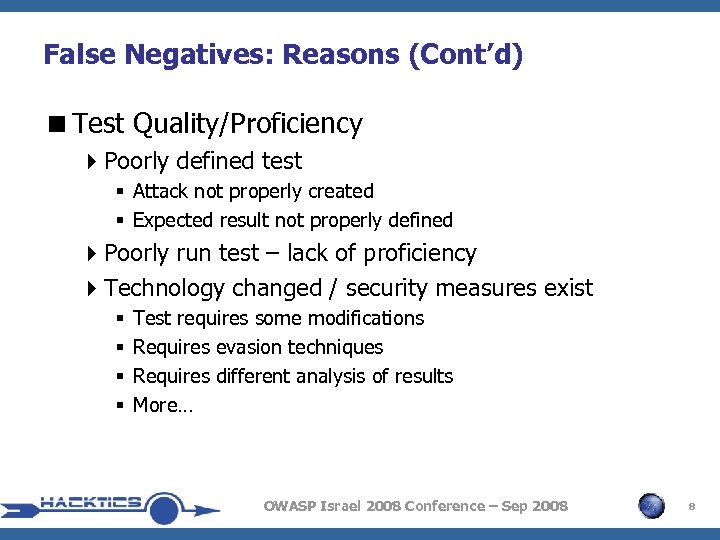 False Negatives: Reasons (Cont’d)
False Negatives: Reasons (Cont’d)
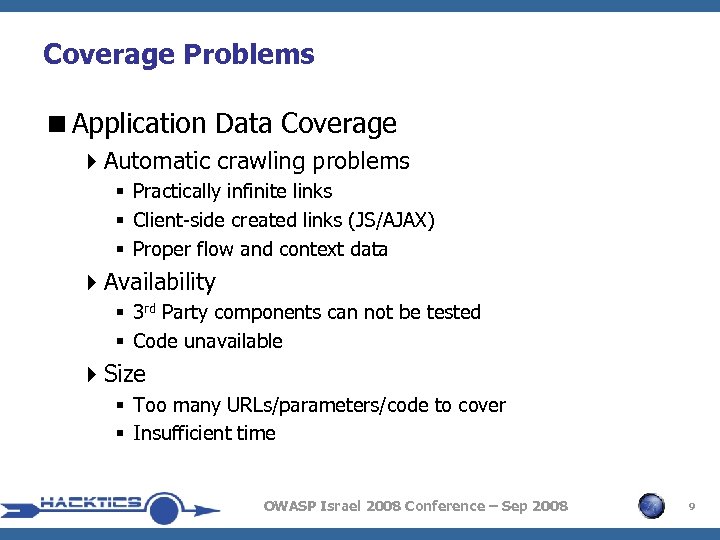 Coverage Problems
Coverage Problems
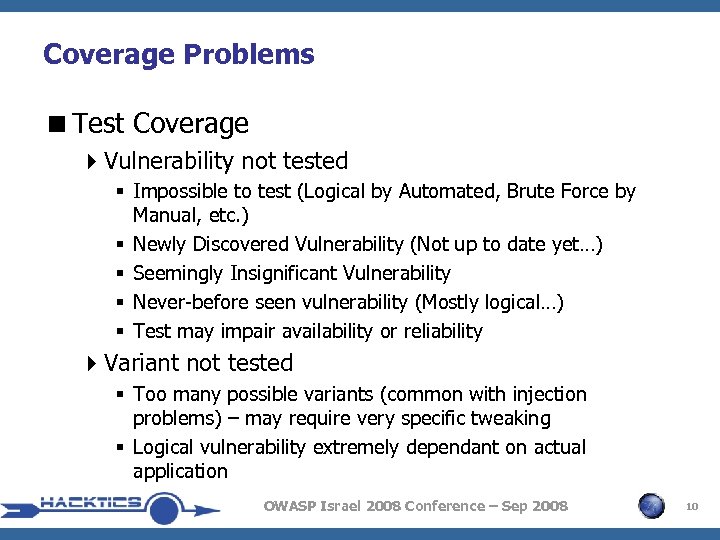 Coverage Problems
Coverage Problems
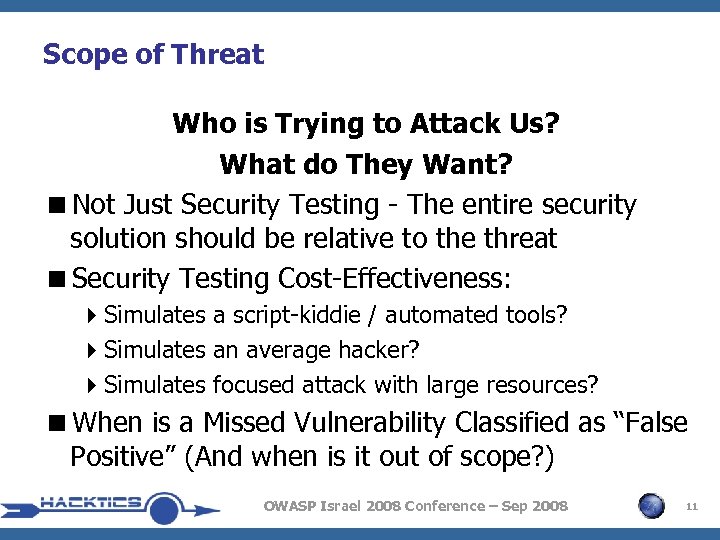 Scope of Threat Who is Trying to Attack Us? What do They Want?
Scope of Threat Who is Trying to Attack Us? What do They Want?
 False Positives: Reasons
False Positives: Reasons
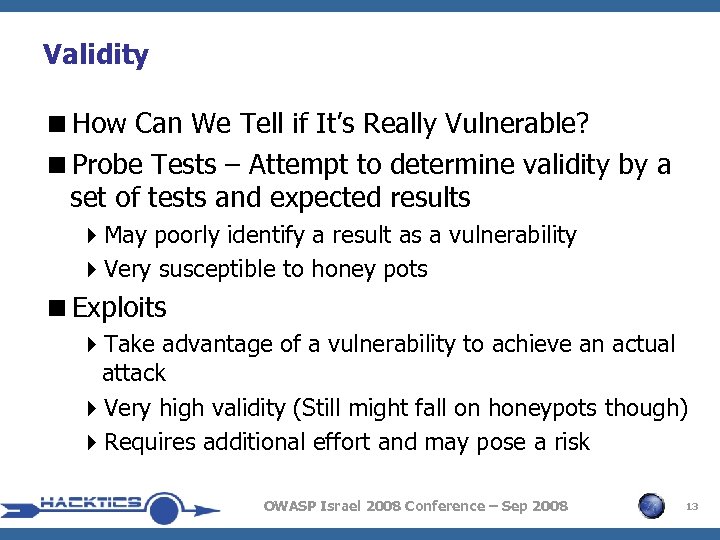 Validity
Validity
 Business Impact
Business Impact
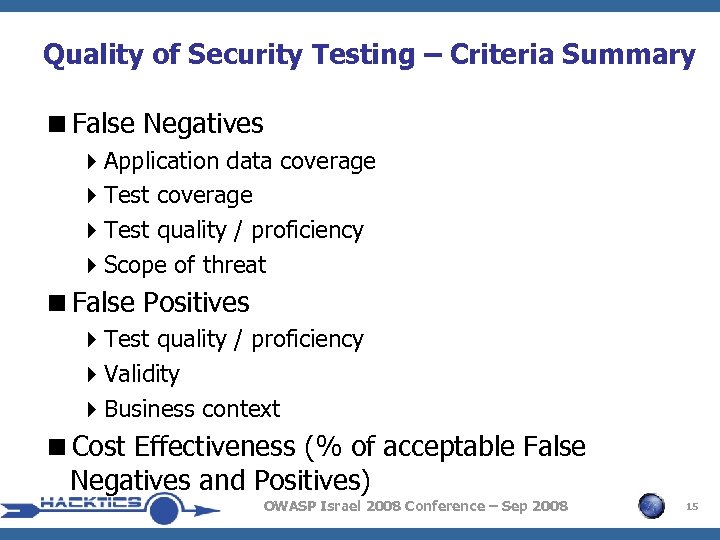 Quality of Security Testing – Criteria Summary
Quality of Security Testing – Criteria Summary
 Security Testing Approaches (Pros & Cons) OWASP Israel 2008 Conference – Sep 2008 16
Security Testing Approaches (Pros & Cons) OWASP Israel 2008 Conference – Sep 2008 16
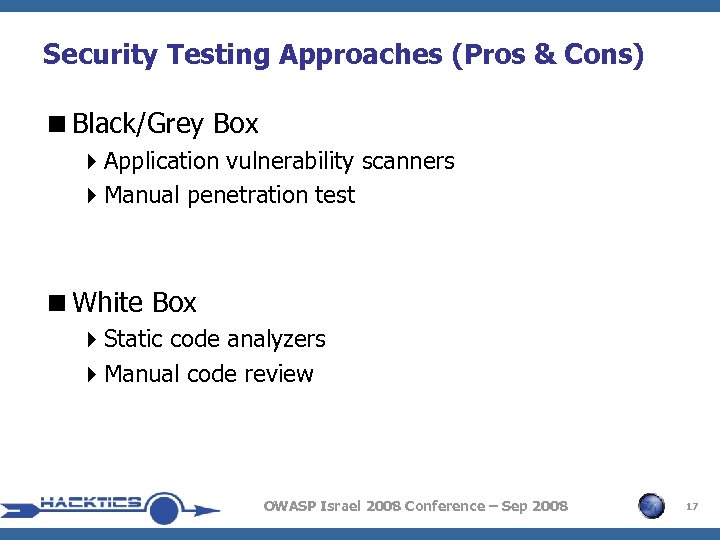 Security Testing Approaches (Pros & Cons)
Security Testing Approaches (Pros & Cons)
 Application Vulnerability Scanners
Application Vulnerability Scanners
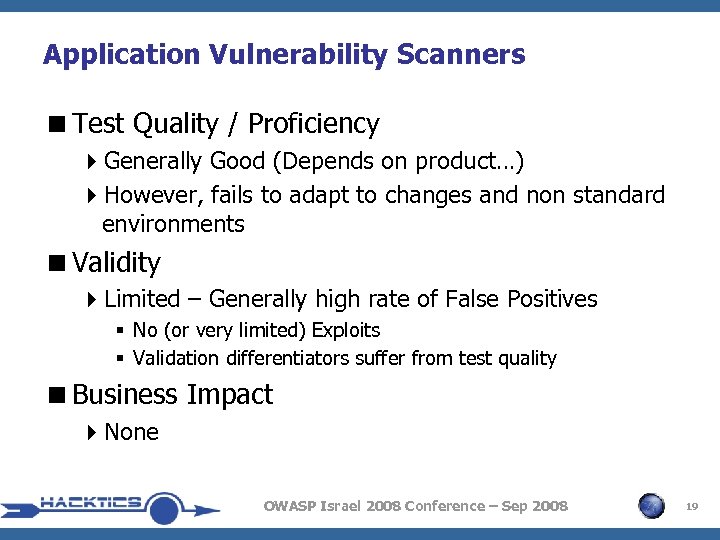 Application Vulnerability Scanners
Application Vulnerability Scanners
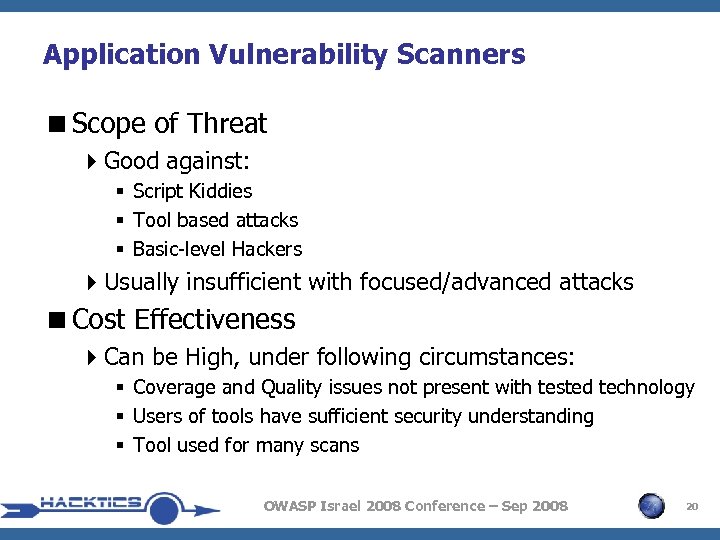 Application Vulnerability Scanners
Application Vulnerability Scanners
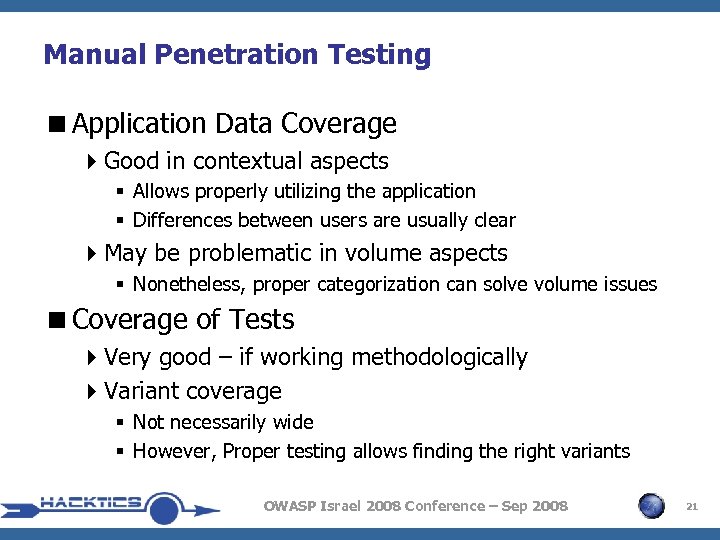 Manual Penetration Testing
Manual Penetration Testing
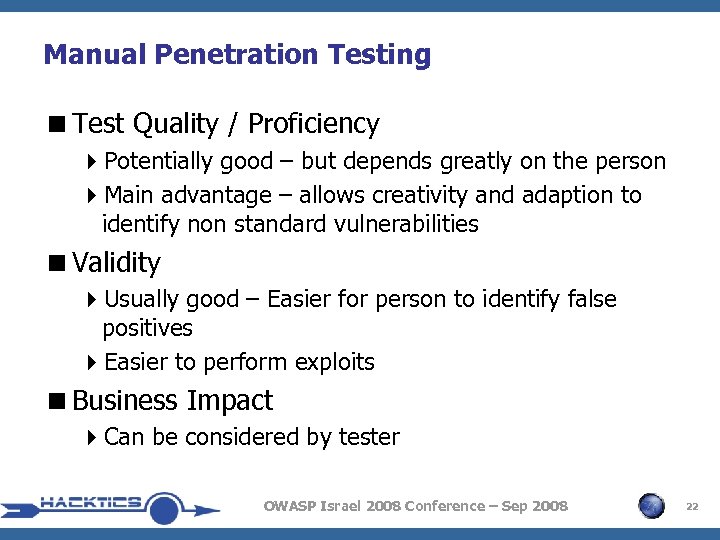 Manual Penetration Testing
Manual Penetration Testing
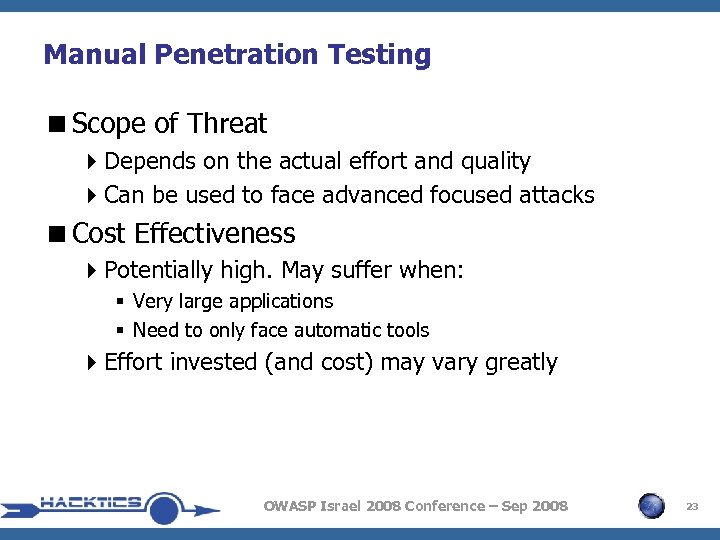 Manual Penetration Testing
Manual Penetration Testing
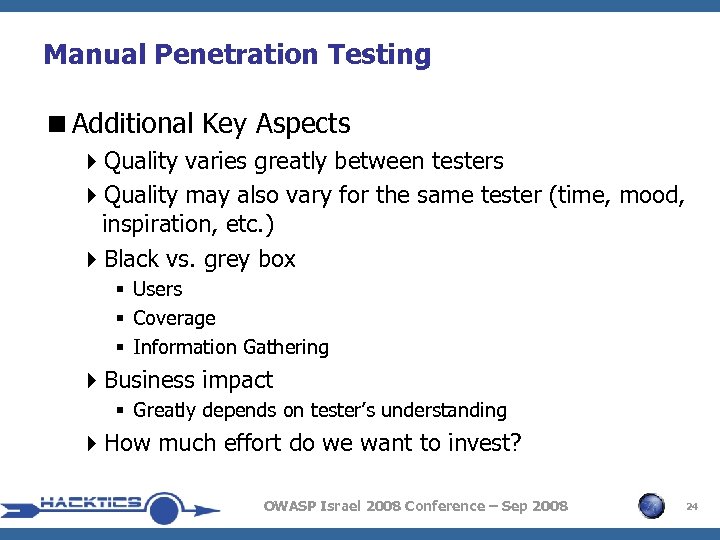 Manual Penetration Testing
Manual Penetration Testing
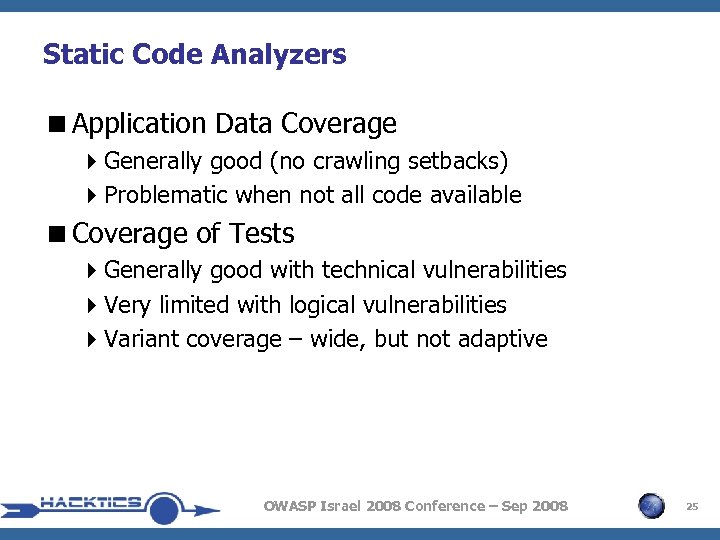 Static Code Analyzers
Static Code Analyzers
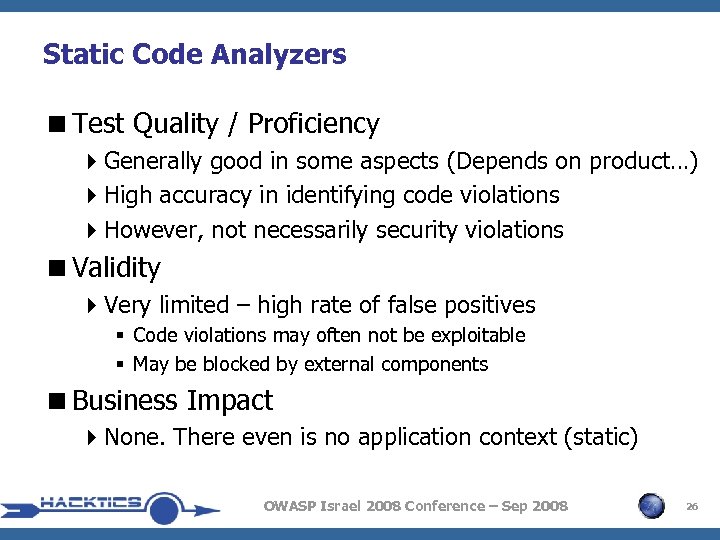 Static Code Analyzers
Static Code Analyzers
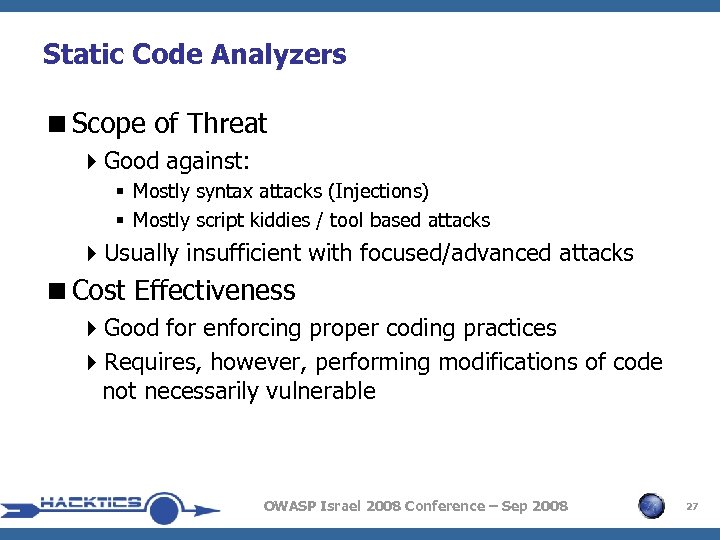 Static Code Analyzers
Static Code Analyzers
 Manual Code Review (Static)
Manual Code Review (Static)
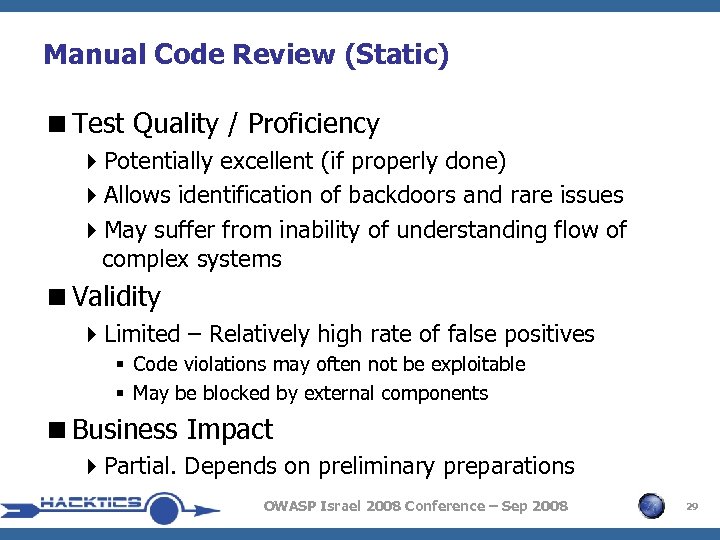 Manual Code Review (Static)
Manual Code Review (Static)
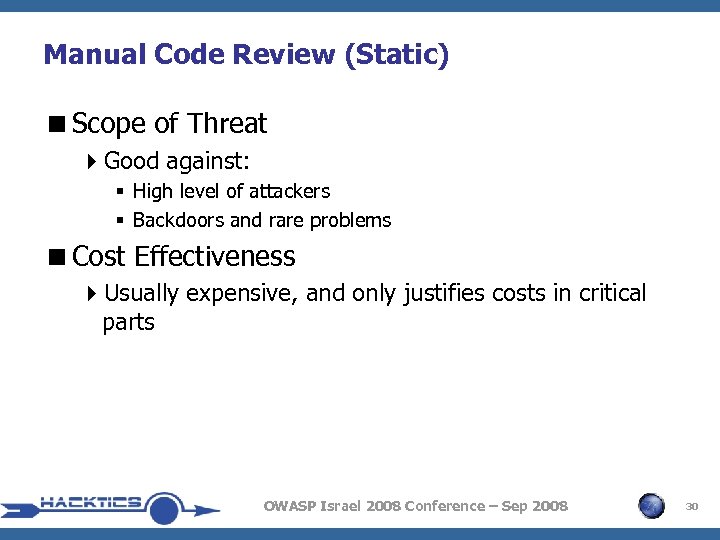 Manual Code Review (Static)
Manual Code Review (Static)
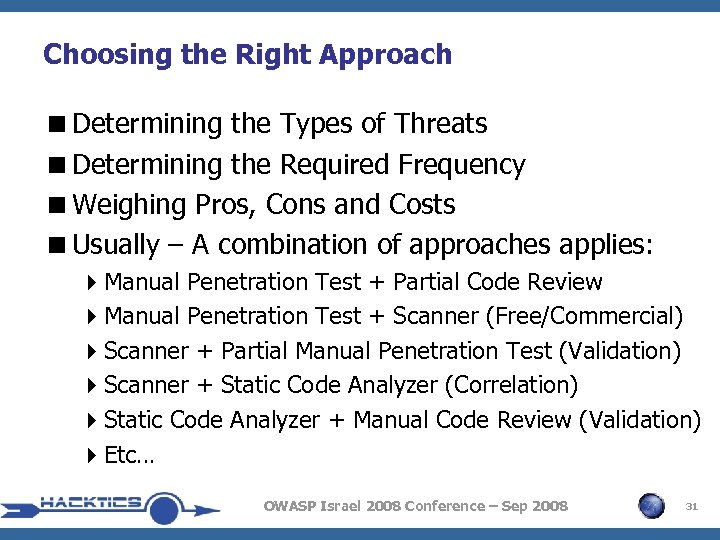 Choosing the Right Approach
Choosing the Right Approach
 Testing the Tester: Evaluating Quality of Security Testing OWASP Israel 2008 Conference – Sep 2008 32
Testing the Tester: Evaluating Quality of Security Testing OWASP Israel 2008 Conference – Sep 2008 32
 Testing the Tester
Testing the Tester
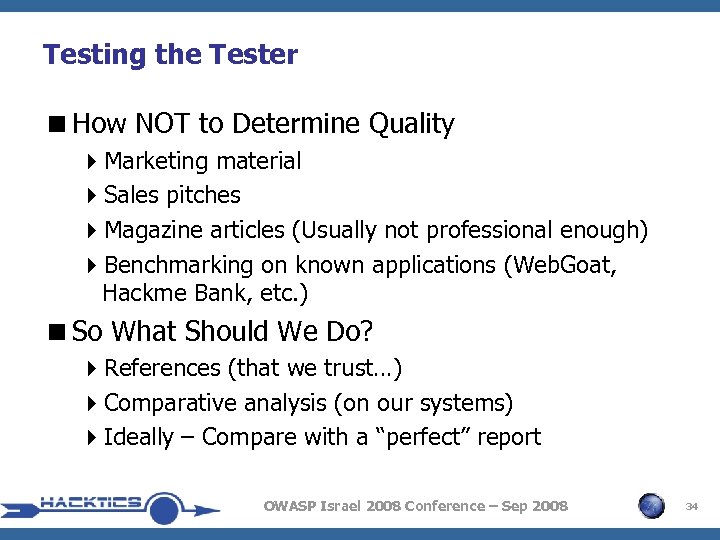 Testing the Tester
Testing the Tester
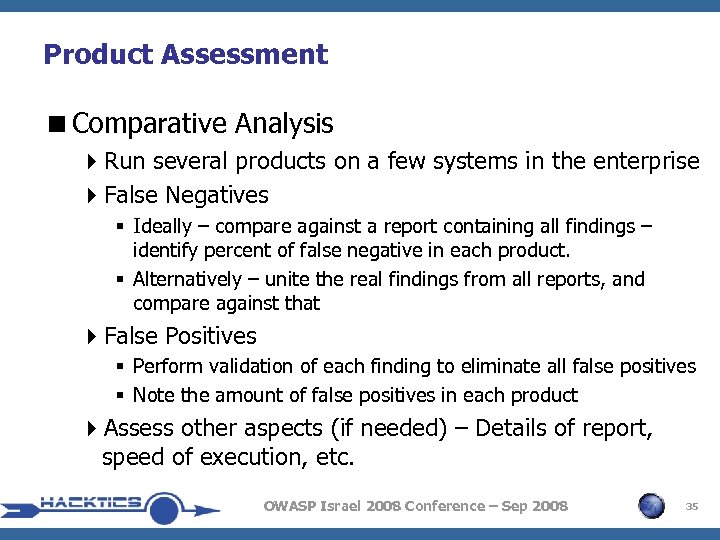 Product Assessment
Product Assessment
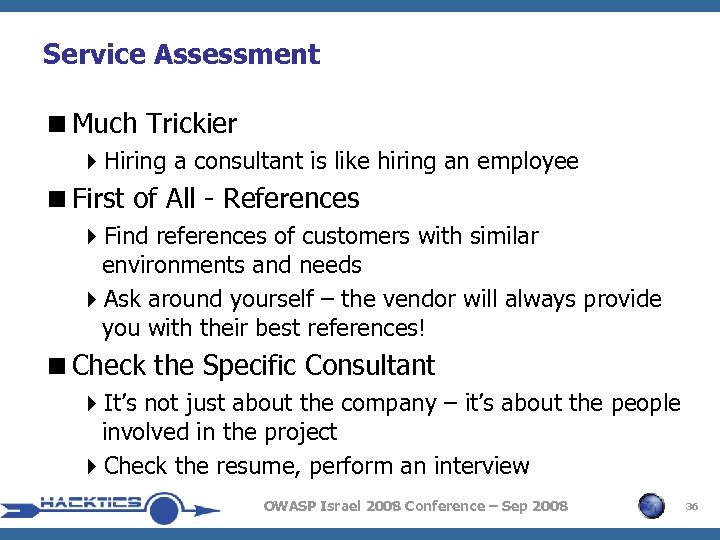 Service Assessment
Service Assessment
 Service Assessment
Service Assessment
 Some Techniques That (Sometimes) Help
Some Techniques That (Sometimes) Help
 Summary
Summary
 Thank You! Discussion & Questions OWASP Israel 2008 Conference – Sep 2008 40
Thank You! Discussion & Questions OWASP Israel 2008 Conference – Sep 2008 40