a4aadd5918c19e2bc6517e9471c0ce0b.ppt
- Количество слайдов: 33
 TERRORIST USE OF THE INTERNET AS AN OPERATIONAL TOOL IN INDONESIA IT & Cyber Crime Unit of INP 1
TERRORIST USE OF THE INTERNET AS AN OPERATIONAL TOOL IN INDONESIA IT & Cyber Crime Unit of INP 1
 INTRODUCTION THE GROWTH OF INFORMATION TECHNOLOGY AS WELL AS INTERNET HAS BROUGHT US BOTH POSITIVE AND NEGATIVE IMPACT. ONE OF THE NEGATIVE IMPACTS IS THE USAGE OF INTERNET FOR ACHIEVING TERRORIST GROUPS’ GOALS. IN MANY CASES, TERRORIST GROUPS ARE AHEAD OF GOVERNMENTS IN USING THIS TECHNOLOGY TO FURTHER THEIR ACTIVITIES. TERRORISTS IN INDONESIA IN FACT HAVE USED IT AS THEIR TOOLS AS WELL AS COMMUNICATION MEDIA TO SUPPORT THEIR TERROR ACTIVITIES AND ACHIEVE THEIR CERTAIN GOALS. WE CLASSIFIED IT AS CYBER TERRORISM. IT & Cyber Crime Unit of INP 2
INTRODUCTION THE GROWTH OF INFORMATION TECHNOLOGY AS WELL AS INTERNET HAS BROUGHT US BOTH POSITIVE AND NEGATIVE IMPACT. ONE OF THE NEGATIVE IMPACTS IS THE USAGE OF INTERNET FOR ACHIEVING TERRORIST GROUPS’ GOALS. IN MANY CASES, TERRORIST GROUPS ARE AHEAD OF GOVERNMENTS IN USING THIS TECHNOLOGY TO FURTHER THEIR ACTIVITIES. TERRORISTS IN INDONESIA IN FACT HAVE USED IT AS THEIR TOOLS AS WELL AS COMMUNICATION MEDIA TO SUPPORT THEIR TERROR ACTIVITIES AND ACHIEVE THEIR CERTAIN GOALS. WE CLASSIFIED IT AS CYBER TERRORISM. IT & Cyber Crime Unit of INP 2
 CYBER TERRORISM IT & Cyber Crime Unit of INP 3
CYBER TERRORISM IT & Cyber Crime Unit of INP 3
 WHAT IS CYBER TERRORISM? CYBER TERRORISM IS A PREMEDITATED, POLITICALLY MOTIVATED ACT AGAINST INFORMATION, COMPUTER SYSTEMS, AND DATA WHICH RESULT IN VIOLENCE AGAINST NONCOMBATANT TARGETS BY SUB NATIONAL GROUPS OR CLANDESTINE AGENTS (POLLITS, 2002). IN INDONESIA, WE DEFINE CYBER TERRORISM AS: ANY TERRORISM ACTS USING INFORMATION TECHNOLOGY AND COMMUNICATION SPECIALLY INTERNET AS A TOOL TO CONDUCT FUND RAISING, COLLECT INFORMATION, CAMPAIGN ANY PARTICULAR ISSUES THAT ARE CAUSING FEAR AS WELL AS TO EXECUTE ANY TERRORIST ATTACKS. IT & Cyber Crime Unit of INP 4
WHAT IS CYBER TERRORISM? CYBER TERRORISM IS A PREMEDITATED, POLITICALLY MOTIVATED ACT AGAINST INFORMATION, COMPUTER SYSTEMS, AND DATA WHICH RESULT IN VIOLENCE AGAINST NONCOMBATANT TARGETS BY SUB NATIONAL GROUPS OR CLANDESTINE AGENTS (POLLITS, 2002). IN INDONESIA, WE DEFINE CYBER TERRORISM AS: ANY TERRORISM ACTS USING INFORMATION TECHNOLOGY AND COMMUNICATION SPECIALLY INTERNET AS A TOOL TO CONDUCT FUND RAISING, COLLECT INFORMATION, CAMPAIGN ANY PARTICULAR ISSUES THAT ARE CAUSING FEAR AS WELL AS TO EXECUTE ANY TERRORIST ATTACKS. IT & Cyber Crime Unit of INP 4
 TERRORISTS’ MOTIVATION IN INDONESIA • THE ESSENCE OF TERRORISM IS TO IMPOSE INTEREST FACTOR OR ACTION OR THREATEN HARASSMENT, CAUSING FEAR, TARGETING CIVIL CITIZEN (NON-MILITARY/NONCOMBATANT), AND HAS PARTICULAR TARGETS, USUALLY POLITICAL AGENDA. • FOUR WAVES OF MODERN TERRORISM: – – ANARCHIST/REVOLUTIONARY TERRORISM ANTI COLONIAL; NATIONALIST TERRORISM NEW LEFT (IDEOLOGICAL) TERRORISM RADICAL RELIGIOUS TERRORISM • IN INDONESIA, MOST TERRORISTS ARE MOTIVATED BY RELIGIOUS RADICALISM SO THAT CLASSIFIED AS RADICAL RELIGIOUS TERRORISM. IT & Cyber Crime Unit of INP 5
TERRORISTS’ MOTIVATION IN INDONESIA • THE ESSENCE OF TERRORISM IS TO IMPOSE INTEREST FACTOR OR ACTION OR THREATEN HARASSMENT, CAUSING FEAR, TARGETING CIVIL CITIZEN (NON-MILITARY/NONCOMBATANT), AND HAS PARTICULAR TARGETS, USUALLY POLITICAL AGENDA. • FOUR WAVES OF MODERN TERRORISM: – – ANARCHIST/REVOLUTIONARY TERRORISM ANTI COLONIAL; NATIONALIST TERRORISM NEW LEFT (IDEOLOGICAL) TERRORISM RADICAL RELIGIOUS TERRORISM • IN INDONESIA, MOST TERRORISTS ARE MOTIVATED BY RELIGIOUS RADICALISM SO THAT CLASSIFIED AS RADICAL RELIGIOUS TERRORISM. IT & Cyber Crime Unit of INP 5
 TERRORISTS USED THE INTERNET THE TERRORISTS EXPLOIT INTERNET FOR: – MEDIA COMMUNICATION • • • NETWORKING WITHIN GROUPS CAMPAIGN AND PROPAGANDA MEMBERS RECRUITMENT FUND RAISING COLLECT INFORMATION AND LEARNING MEDIA – EXECUTING ANY ATTACK IN CYBER SPACE. IT & Cyber Crime Unit of INP 6
TERRORISTS USED THE INTERNET THE TERRORISTS EXPLOIT INTERNET FOR: – MEDIA COMMUNICATION • • • NETWORKING WITHIN GROUPS CAMPAIGN AND PROPAGANDA MEMBERS RECRUITMENT FUND RAISING COLLECT INFORMATION AND LEARNING MEDIA – EXECUTING ANY ATTACK IN CYBER SPACE. IT & Cyber Crime Unit of INP 6
 TERRORISTS ACTIVITIES VIA INTERNET CREATING WEBSITE/BLOG COMMUNICATION VIA EMAIL OR CHATTING DISCUSSION VIA CHAT ROOM E-TRANSACTION (E-COMMERCE/E-BANKING) USING SEARCHING MACHINE TO COLLECT DATA OR FINDING INFORMATION PHISHING/HACKING MANY OTHER TYPES SUCH AS VIRUSES, WORM, TROJAN, ROOTKIT, MALICIOUS CODE, AND DDOS ATTACK. IT & Cyber Crime Unit of INP 7
TERRORISTS ACTIVITIES VIA INTERNET CREATING WEBSITE/BLOG COMMUNICATION VIA EMAIL OR CHATTING DISCUSSION VIA CHAT ROOM E-TRANSACTION (E-COMMERCE/E-BANKING) USING SEARCHING MACHINE TO COLLECT DATA OR FINDING INFORMATION PHISHING/HACKING MANY OTHER TYPES SUCH AS VIRUSES, WORM, TROJAN, ROOTKIT, MALICIOUS CODE, AND DDOS ATTACK. IT & Cyber Crime Unit of INP 7
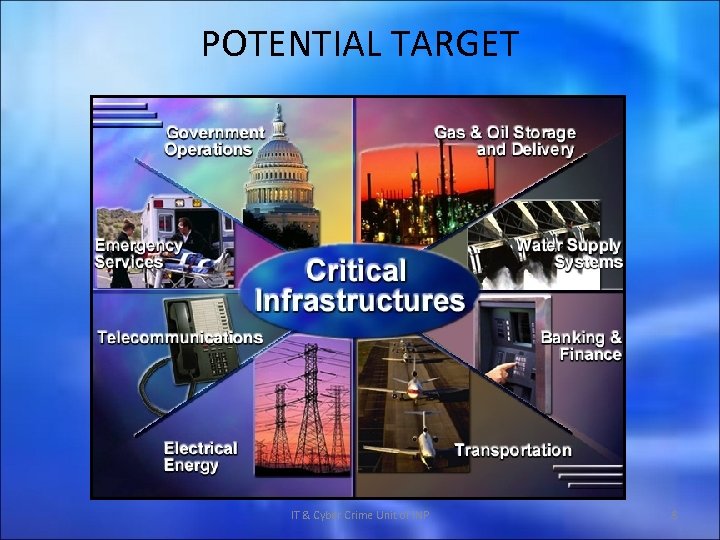 POTENTIAL TARGET IT & Cyber Crime Unit of INP 8
POTENTIAL TARGET IT & Cyber Crime Unit of INP 8
 OFFICIAL WEBSITES – THESE ARE IDENTIFIED AS GOVERNMENT WEB SITES THAT ARE AVAILABLE TO THE PUBLIC FOR INFORMATION ON GOVERNMENTAL SERVICES. THE VAST MAJORITY OF GOVERNMENT WEB SITES ARE HOSTED BY PRIVATE INDUSTRY INTERNET SERVICE PROVIDERS. TERRORIST ORGANIZATIONS CAN GATHER INFORMATION FROM OFFICIAL GOVERNMENT WEBSITES ON LAW ENFORCEMENT AND MILITARY PERSONNEL AND ACTIVITIES. GOVERNMENT AGENCIES SHOULD CONDUCT PERIODIC REVIEWS OF THEIR WEBSITES IN ORDER TO DETERMINE IF CRITICAL INFORMATION IS BEING POSTED TO THE SITE. IT & Cyber Crime Unit of INP 9
OFFICIAL WEBSITES – THESE ARE IDENTIFIED AS GOVERNMENT WEB SITES THAT ARE AVAILABLE TO THE PUBLIC FOR INFORMATION ON GOVERNMENTAL SERVICES. THE VAST MAJORITY OF GOVERNMENT WEB SITES ARE HOSTED BY PRIVATE INDUSTRY INTERNET SERVICE PROVIDERS. TERRORIST ORGANIZATIONS CAN GATHER INFORMATION FROM OFFICIAL GOVERNMENT WEBSITES ON LAW ENFORCEMENT AND MILITARY PERSONNEL AND ACTIVITIES. GOVERNMENT AGENCIES SHOULD CONDUCT PERIODIC REVIEWS OF THEIR WEBSITES IN ORDER TO DETERMINE IF CRITICAL INFORMATION IS BEING POSTED TO THE SITE. IT & Cyber Crime Unit of INP 9
 OFFICIAL WEBSITES TERRORIST GROUPS CAN LAUNCH DISTRIBUTED DENIAL OF SERVICE (DDOS) ATTACKS AGAINST GOVERNMENT WEBSITES TO DISRUPT SERVICE. WEBSITES MAY BE ATTACKED BY TERRORIST ORGANIZATIONS IN ORDER TO GAIN ACCESS TO GOVERNMENT NETWORKS WHERE CRITICAL INFORMATION IS STORED. THE CYBER ATTACKS OCCUR DUE TO THE LACK OF SECURITY MECHANISMS ON COMPUTER SYSTEMS. IT & Cyber Crime Unit of INP 10
OFFICIAL WEBSITES TERRORIST GROUPS CAN LAUNCH DISTRIBUTED DENIAL OF SERVICE (DDOS) ATTACKS AGAINST GOVERNMENT WEBSITES TO DISRUPT SERVICE. WEBSITES MAY BE ATTACKED BY TERRORIST ORGANIZATIONS IN ORDER TO GAIN ACCESS TO GOVERNMENT NETWORKS WHERE CRITICAL INFORMATION IS STORED. THE CYBER ATTACKS OCCUR DUE TO THE LACK OF SECURITY MECHANISMS ON COMPUTER SYSTEMS. IT & Cyber Crime Unit of INP 10
 FINANCIAL & MONETARY INSTITUTIONS - THE VERY NATURE OF A NATION-STATES EXISTENCE RELIES ON ITS ABILITY TO FUNCTION ECONOMICALLY. THREATS TO THE FINANCIAL SYSTEMS WILL HAVE DIRE CONSEQUENCES FOR A NATIONS ABILITY TO OPERATE EFFECTIVELY AND EFFICIENTLY. THE VAST MAJORITY OF FINANCIAL AND BANKING SYSTEMS NOW HAVE A PRESENCE ON THE INTERNET. THE PRESENCE OF BANKING ON THE INTERNET ALSO EXPOSES THE FINANCIAL SYSTEMS TO RISKS FROM CYBER TERRORIST ATTACKS. PRIVATE INDUSTRY AND GOVERNMENT MUST ENSURE THAT THEY SECURE THEIR COMPUTER SYSTEMS. IT & Cyber Crime Unit of INP 11
FINANCIAL & MONETARY INSTITUTIONS - THE VERY NATURE OF A NATION-STATES EXISTENCE RELIES ON ITS ABILITY TO FUNCTION ECONOMICALLY. THREATS TO THE FINANCIAL SYSTEMS WILL HAVE DIRE CONSEQUENCES FOR A NATIONS ABILITY TO OPERATE EFFECTIVELY AND EFFICIENTLY. THE VAST MAJORITY OF FINANCIAL AND BANKING SYSTEMS NOW HAVE A PRESENCE ON THE INTERNET. THE PRESENCE OF BANKING ON THE INTERNET ALSO EXPOSES THE FINANCIAL SYSTEMS TO RISKS FROM CYBER TERRORIST ATTACKS. PRIVATE INDUSTRY AND GOVERNMENT MUST ENSURE THAT THEY SECURE THEIR COMPUTER SYSTEMS. IT & Cyber Crime Unit of INP 11
 WATER SYSTEMS WATER SOURCES – THE WATER FACILITIES, PLANTS AND DAMS THAT CONTAIN AND PROVIDE WATER AND ENERGY TO COMMUNITIES. THESE FACILITIES ARE CONTROLLED BY SUPERVISORY CONTROL AND DATA ACQUISITION SYSTEMS (SCADA). IMAGINE THE IMPLICATIONS OF A CYBER TERRORIST GAINING ACCESS TO THE SCADA NETWORK THAT CONTROLS A LARGE DAM AND THEN RELEASING THE WATER UPON AN UNSUSPECTING TOWN OR CITY. THE VULNERABILITIES OF SCADA ARE WELL KNOWN AND DOCUMENTED. IT & Cyber Crime Unit of INP 12
WATER SYSTEMS WATER SOURCES – THE WATER FACILITIES, PLANTS AND DAMS THAT CONTAIN AND PROVIDE WATER AND ENERGY TO COMMUNITIES. THESE FACILITIES ARE CONTROLLED BY SUPERVISORY CONTROL AND DATA ACQUISITION SYSTEMS (SCADA). IMAGINE THE IMPLICATIONS OF A CYBER TERRORIST GAINING ACCESS TO THE SCADA NETWORK THAT CONTROLS A LARGE DAM AND THEN RELEASING THE WATER UPON AN UNSUSPECTING TOWN OR CITY. THE VULNERABILITIES OF SCADA ARE WELL KNOWN AND DOCUMENTED. IT & Cyber Crime Unit of INP 12
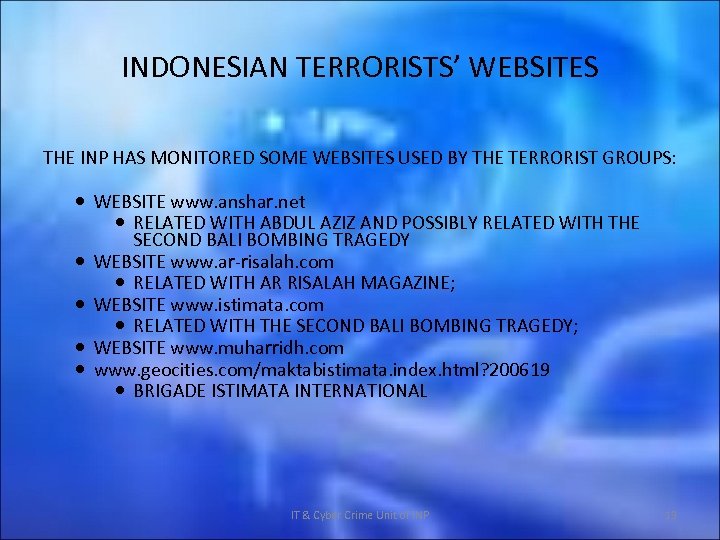 INDONESIAN TERRORISTS’ WEBSITES THE INP HAS MONITORED SOME WEBSITES USED BY THE TERRORIST GROUPS: WEBSITE www. anshar. net RELATED WITH ABDUL AZIZ AND POSSIBLY RELATED WITH THE SECOND BALI BOMBING TRAGEDY WEBSITE www. ar-risalah. com RELATED WITH AR RISALAH MAGAZINE; WEBSITE www. istimata. com RELATED WITH THE SECOND BALI BOMBING TRAGEDY; WEBSITE www. muharridh. com www. geocities. com/maktabistimata. index. html? 200619 BRIGADE ISTIMATA INTERNATIONAL IT & Cyber Crime Unit of INP 13
INDONESIAN TERRORISTS’ WEBSITES THE INP HAS MONITORED SOME WEBSITES USED BY THE TERRORIST GROUPS: WEBSITE www. anshar. net RELATED WITH ABDUL AZIZ AND POSSIBLY RELATED WITH THE SECOND BALI BOMBING TRAGEDY WEBSITE www. ar-risalah. com RELATED WITH AR RISALAH MAGAZINE; WEBSITE www. istimata. com RELATED WITH THE SECOND BALI BOMBING TRAGEDY; WEBSITE www. muharridh. com www. geocities. com/maktabistimata. index. html? 200619 BRIGADE ISTIMATA INTERNATIONAL IT & Cyber Crime Unit of INP 13
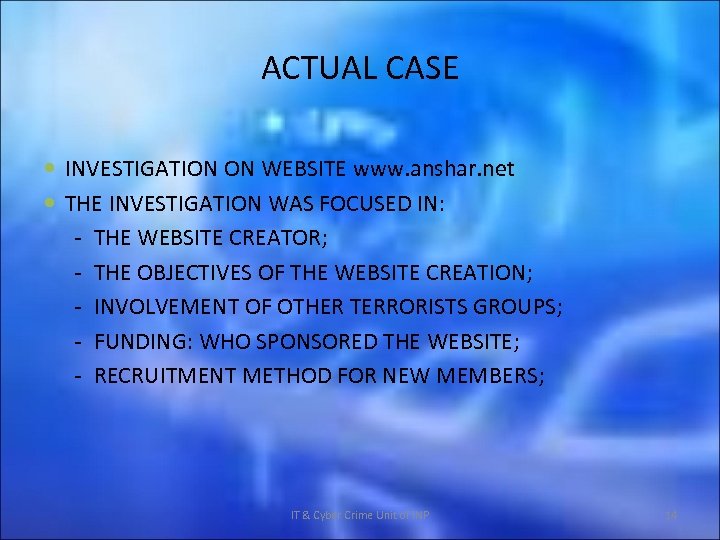 ACTUAL CASE INVESTIGATION ON WEBSITE www. anshar. net THE INVESTIGATION WAS FOCUSED IN: - THE WEBSITE CREATOR; - THE OBJECTIVES OF THE WEBSITE CREATION; - INVOLVEMENT OF OTHER TERRORISTS GROUPS; - FUNDING: WHO SPONSORED THE WEBSITE; - RECRUITMENT METHOD FOR NEW MEMBERS; IT & Cyber Crime Unit of INP 14
ACTUAL CASE INVESTIGATION ON WEBSITE www. anshar. net THE INVESTIGATION WAS FOCUSED IN: - THE WEBSITE CREATOR; - THE OBJECTIVES OF THE WEBSITE CREATION; - INVOLVEMENT OF OTHER TERRORISTS GROUPS; - FUNDING: WHO SPONSORED THE WEBSITE; - RECRUITMENT METHOD FOR NEW MEMBERS; IT & Cyber Crime Unit of INP 14
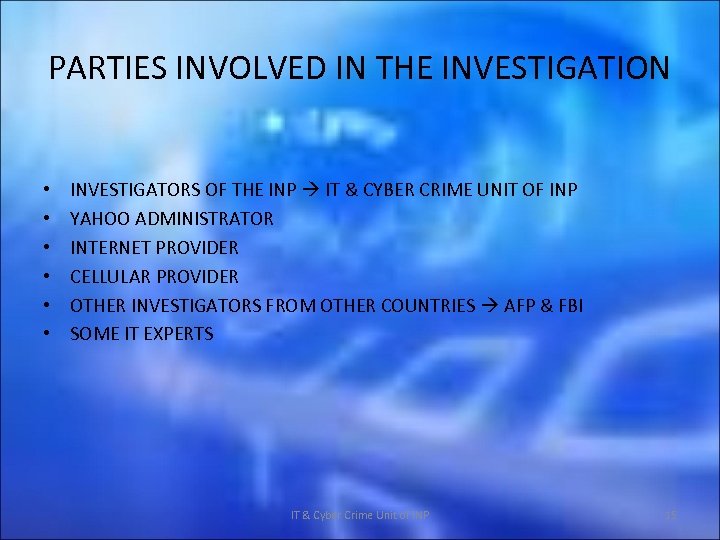 PARTIES INVOLVED IN THE INVESTIGATION • • • INVESTIGATORS OF THE INP IT & CYBER CRIME UNIT OF INP YAHOO ADMINISTRATOR INTERNET PROVIDER CELLULAR PROVIDER OTHER INVESTIGATORS FROM OTHER COUNTRIES AFP & FBI SOME IT EXPERTS IT & Cyber Crime Unit of INP 15
PARTIES INVOLVED IN THE INVESTIGATION • • • INVESTIGATORS OF THE INP IT & CYBER CRIME UNIT OF INP YAHOO ADMINISTRATOR INTERNET PROVIDER CELLULAR PROVIDER OTHER INVESTIGATORS FROM OTHER COUNTRIES AFP & FBI SOME IT EXPERTS IT & Cyber Crime Unit of INP 15
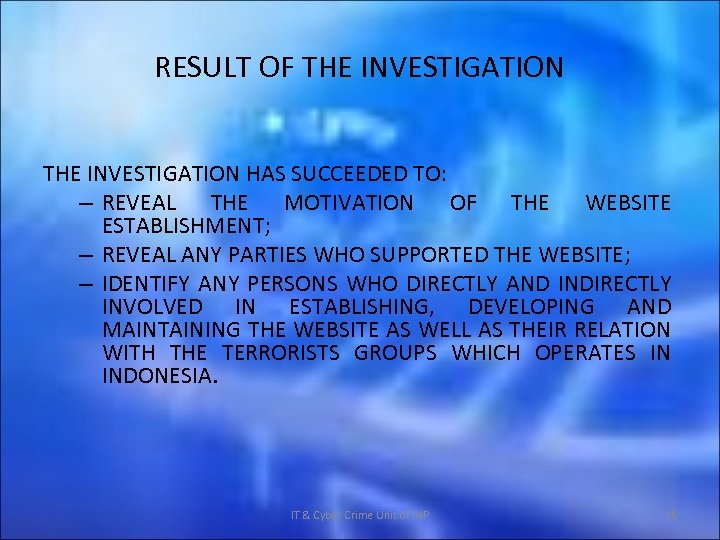 RESULT OF THE INVESTIGATION HAS SUCCEEDED TO: – REVEAL THE MOTIVATION OF THE WEBSITE ESTABLISHMENT; – REVEAL ANY PARTIES WHO SUPPORTED THE WEBSITE; – IDENTIFY ANY PERSONS WHO DIRECTLY AND INDIRECTLY INVOLVED IN ESTABLISHING, DEVELOPING AND MAINTAINING THE WEBSITE AS WELL AS THEIR RELATION WITH THE TERRORISTS GROUPS WHICH OPERATES IN INDONESIA. IT & Cyber Crime Unit of INP 16
RESULT OF THE INVESTIGATION HAS SUCCEEDED TO: – REVEAL THE MOTIVATION OF THE WEBSITE ESTABLISHMENT; – REVEAL ANY PARTIES WHO SUPPORTED THE WEBSITE; – IDENTIFY ANY PERSONS WHO DIRECTLY AND INDIRECTLY INVOLVED IN ESTABLISHING, DEVELOPING AND MAINTAINING THE WEBSITE AS WELL AS THEIR RELATION WITH THE TERRORISTS GROUPS WHICH OPERATES IN INDONESIA. IT & Cyber Crime Unit of INP 16
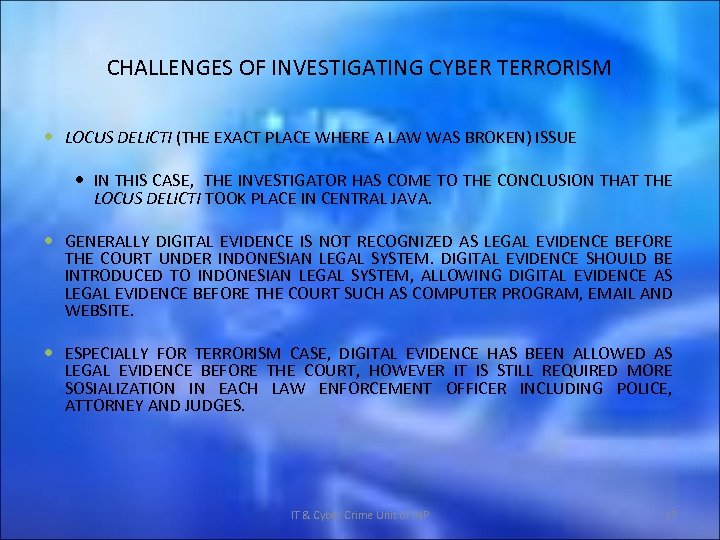 CHALLENGES OF INVESTIGATING CYBER TERRORISM LOCUS DELICTI (THE EXACT PLACE WHERE A LAW WAS BROKEN) ISSUE IN THIS CASE, THE INVESTIGATOR HAS COME TO THE CONCLUSION THAT THE LOCUS DELICTI TOOK PLACE IN CENTRAL JAVA. GENERALLY DIGITAL EVIDENCE IS NOT RECOGNIZED AS LEGAL EVIDENCE BEFORE THE COURT UNDER INDONESIAN LEGAL SYSTEM. DIGITAL EVIDENCE SHOULD BE INTRODUCED TO INDONESIAN LEGAL SYSTEM, ALLOWING DIGITAL EVIDENCE AS LEGAL EVIDENCE BEFORE THE COURT SUCH AS COMPUTER PROGRAM, EMAIL AND WEBSITE. ESPECIALLY FOR TERRORISM CASE, DIGITAL EVIDENCE HAS BEEN ALLOWED AS LEGAL EVIDENCE BEFORE THE COURT, HOWEVER IT IS STILL REQUIRED MORE SOSIALIZATION IN EACH LAW ENFORCEMENT OFFICER INCLUDING POLICE, ATTORNEY AND JUDGES. IT & Cyber Crime Unit of INP 17
CHALLENGES OF INVESTIGATING CYBER TERRORISM LOCUS DELICTI (THE EXACT PLACE WHERE A LAW WAS BROKEN) ISSUE IN THIS CASE, THE INVESTIGATOR HAS COME TO THE CONCLUSION THAT THE LOCUS DELICTI TOOK PLACE IN CENTRAL JAVA. GENERALLY DIGITAL EVIDENCE IS NOT RECOGNIZED AS LEGAL EVIDENCE BEFORE THE COURT UNDER INDONESIAN LEGAL SYSTEM. DIGITAL EVIDENCE SHOULD BE INTRODUCED TO INDONESIAN LEGAL SYSTEM, ALLOWING DIGITAL EVIDENCE AS LEGAL EVIDENCE BEFORE THE COURT SUCH AS COMPUTER PROGRAM, EMAIL AND WEBSITE. ESPECIALLY FOR TERRORISM CASE, DIGITAL EVIDENCE HAS BEEN ALLOWED AS LEGAL EVIDENCE BEFORE THE COURT, HOWEVER IT IS STILL REQUIRED MORE SOSIALIZATION IN EACH LAW ENFORCEMENT OFFICER INCLUDING POLICE, ATTORNEY AND JUDGES. IT & Cyber Crime Unit of INP 17
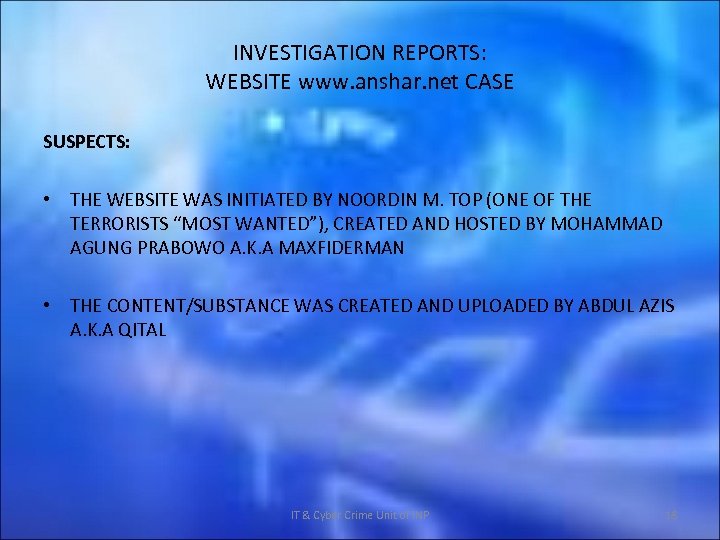 INVESTIGATION REPORTS: WEBSITE www. anshar. net CASE SUSPECTS: • THE WEBSITE WAS INITIATED BY NOORDIN M. TOP (ONE OF THE TERRORISTS “MOST WANTED”), CREATED AND HOSTED BY MOHAMMAD AGUNG PRABOWO A. K. A MAXFIDERMAN • THE CONTENT/SUBSTANCE WAS CREATED AND UPLOADED BY ABDUL AZIS A. K. A QITAL IT & Cyber Crime Unit of INP 18
INVESTIGATION REPORTS: WEBSITE www. anshar. net CASE SUSPECTS: • THE WEBSITE WAS INITIATED BY NOORDIN M. TOP (ONE OF THE TERRORISTS “MOST WANTED”), CREATED AND HOSTED BY MOHAMMAD AGUNG PRABOWO A. K. A MAXFIDERMAN • THE CONTENT/SUBSTANCE WAS CREATED AND UPLOADED BY ABDUL AZIS A. K. A QITAL IT & Cyber Crime Unit of INP 18
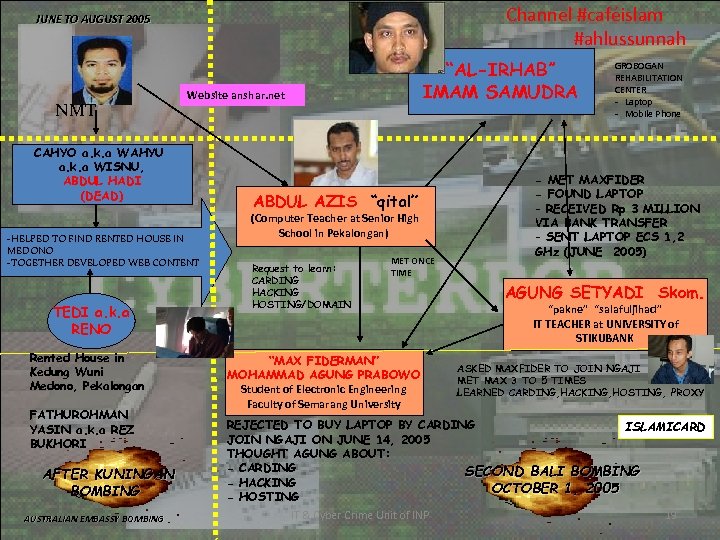 Channel #caféislam #ahlussunnah JUNE TO AUGUST 2005 NMT Website anshar. net CAHYO a. k. a WAHYU a. k. a WISNU, ABDUL HADI (DEAD) -HELPED TO FIND RENTED HOUSE IN MEDONO -TOGETHER DEVELOPED WEB CONTENT TEDI a. k. a RENO Rented House in Kedung Wuni Medono, Pekalongan FATHUROHMAN YASIN a. k. a REZ BUKHORI AFTER KUNINGAN BOMBING AUSTRALIAN EMBASSY BOMBING “AL-IRHAB” IMAM SAMUDRA ABDUL AZIS “qital” (Computer Teacher at Senior High School in Pekalongan) Request to learn: CARDING HACKING HOSTING/DOMAIN MET ONCE TIME “MAX FIDERMAN” MOHAMMAD AGUNG PRABOWO Student of Electronic Engineering Faculty of Semarang University GROBOGAN REHABILITATION CENTER - Laptop - Mobile Phone - MET MAXFIDER - FOUND LAPTOP - RECEIVED Rp 3 MILLION VIA BANK TRANSFER - SENT LAPTOP ECS 1, 2 GHz (JUNE 2005) AGUNG SETYADI Skom. “pakne” “salafuljihad” IT TEACHER at UNIVERSITY of STIKUBANK ASKED MAXFIDER TO JOIN NGAJI MET MAX 3 TO 5 TIMES LEARNED CARDING, HACKING, HOSTING, PROXY REJECTED TO BUY LAPTOP BY CARDING ISLAMICARD JOIN NGAJI ON JUNE 14, 2005 THOUGHT AGUNG ABOUT: - CARDING SECOND BALI BOMBING - HACKING OCTOBER 1, 2005 - HOSTING IT & Cyber Crime Unit of INP 19
Channel #caféislam #ahlussunnah JUNE TO AUGUST 2005 NMT Website anshar. net CAHYO a. k. a WAHYU a. k. a WISNU, ABDUL HADI (DEAD) -HELPED TO FIND RENTED HOUSE IN MEDONO -TOGETHER DEVELOPED WEB CONTENT TEDI a. k. a RENO Rented House in Kedung Wuni Medono, Pekalongan FATHUROHMAN YASIN a. k. a REZ BUKHORI AFTER KUNINGAN BOMBING AUSTRALIAN EMBASSY BOMBING “AL-IRHAB” IMAM SAMUDRA ABDUL AZIS “qital” (Computer Teacher at Senior High School in Pekalongan) Request to learn: CARDING HACKING HOSTING/DOMAIN MET ONCE TIME “MAX FIDERMAN” MOHAMMAD AGUNG PRABOWO Student of Electronic Engineering Faculty of Semarang University GROBOGAN REHABILITATION CENTER - Laptop - Mobile Phone - MET MAXFIDER - FOUND LAPTOP - RECEIVED Rp 3 MILLION VIA BANK TRANSFER - SENT LAPTOP ECS 1, 2 GHz (JUNE 2005) AGUNG SETYADI Skom. “pakne” “salafuljihad” IT TEACHER at UNIVERSITY of STIKUBANK ASKED MAXFIDER TO JOIN NGAJI MET MAX 3 TO 5 TIMES LEARNED CARDING, HACKING, HOSTING, PROXY REJECTED TO BUY LAPTOP BY CARDING ISLAMICARD JOIN NGAJI ON JUNE 14, 2005 THOUGHT AGUNG ABOUT: - CARDING SECOND BALI BOMBING - HACKING OCTOBER 1, 2005 - HOSTING IT & Cyber Crime Unit of INP 19
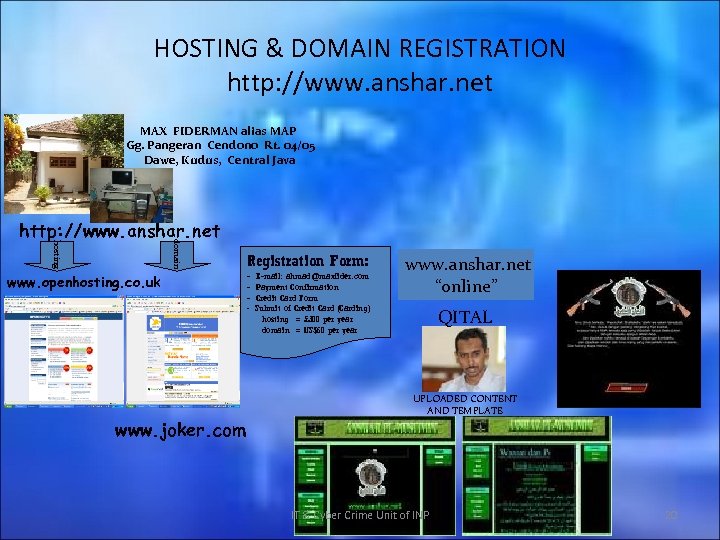 HOSTING & DOMAIN REGISTRATION http: //www. anshar. net MAX FIDERMAN alias MAP Gg. Pangeran Cendono Rt. 04/05 Dawe, Kudus, Central Java hosting domain http: //www. anshar. net www. openhosting. co. uk www. joker. com Registration Form: - E-mail: ahmad@maxfider. com - Payment Confirmation - Credit Card Form - Submit of Credit Card (Carding) hosting = £ 300 per year domain = US$60 per year www. anshar. net “online” QITAL UPLOADED CONTENT AND TEMPLATE IT & Cyber Crime Unit of INP 20
HOSTING & DOMAIN REGISTRATION http: //www. anshar. net MAX FIDERMAN alias MAP Gg. Pangeran Cendono Rt. 04/05 Dawe, Kudus, Central Java hosting domain http: //www. anshar. net www. openhosting. co. uk www. joker. com Registration Form: - E-mail: ahmad@maxfider. com - Payment Confirmation - Credit Card Form - Submit of Credit Card (Carding) hosting = £ 300 per year domain = US$60 per year www. anshar. net “online” QITAL UPLOADED CONTENT AND TEMPLATE IT & Cyber Crime Unit of INP 20
 INVESTIGATION REPORTS: WEBSITE www. anshar. net PURPOSE OF THE WEBSITE ESTABLISHMENT: – PROPAGANDA; – PUBLICATION OF EXECUTION OF THE AL-JAMAAH AL-ISLAMIYAH GROUPS; – DISTRIBUTION OF TRAINING MATERIAL FOR THE ASKARIYAH (SOLDIERS). IT & Cyber Crime Unit of INP 21
INVESTIGATION REPORTS: WEBSITE www. anshar. net PURPOSE OF THE WEBSITE ESTABLISHMENT: – PROPAGANDA; – PUBLICATION OF EXECUTION OF THE AL-JAMAAH AL-ISLAMIYAH GROUPS; – DISTRIBUTION OF TRAINING MATERIAL FOR THE ASKARIYAH (SOLDIERS). IT & Cyber Crime Unit of INP 21
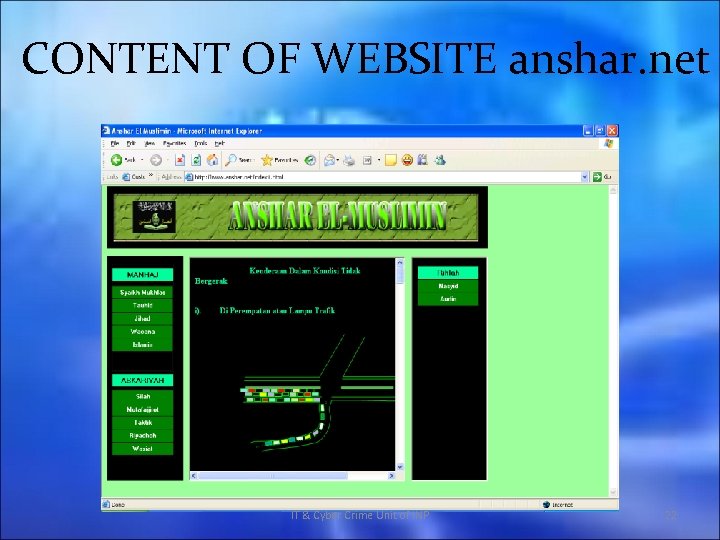 CONTENT OF WEBSITE anshar. net IT & Cyber Crime Unit of INP 22
CONTENT OF WEBSITE anshar. net IT & Cyber Crime Unit of INP 22
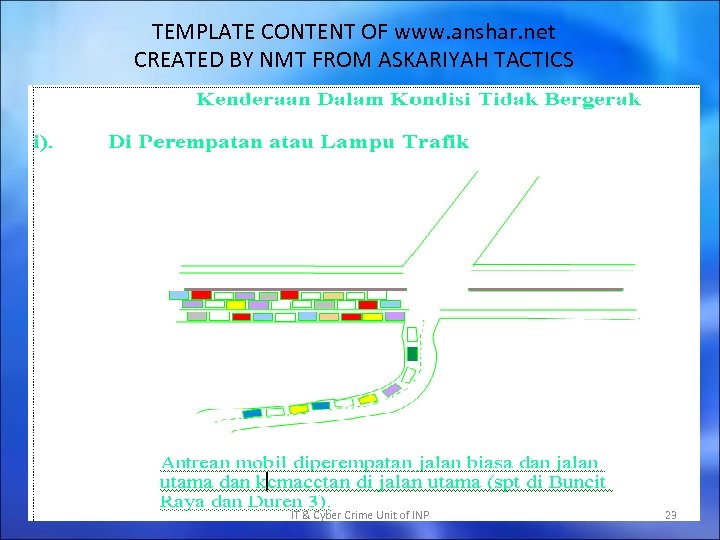 TEMPLATE CONTENT OF www. anshar. net CREATED BY NMT FROM ASKARIYAH TACTICS IT & Cyber Crime Unit of INP 23
TEMPLATE CONTENT OF www. anshar. net CREATED BY NMT FROM ASKARIYAH TACTICS IT & Cyber Crime Unit of INP 23
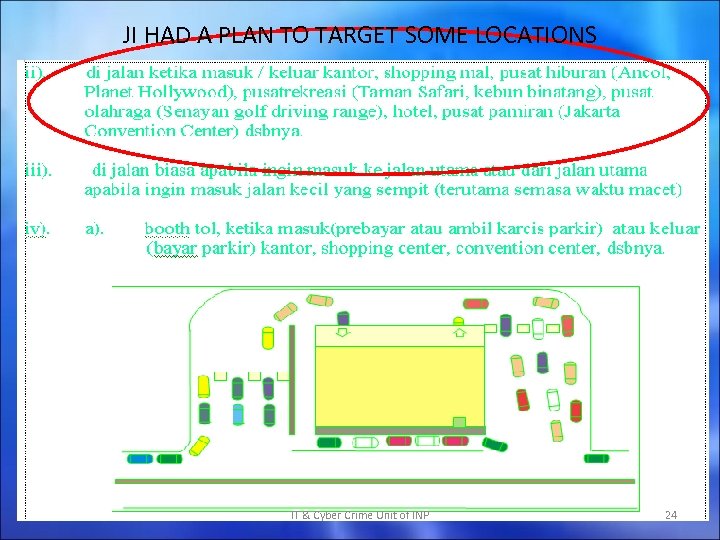 JI HAD A PLAN TO TARGET SOME LOCATIONS IT & Cyber Crime Unit of INP 24
JI HAD A PLAN TO TARGET SOME LOCATIONS IT & Cyber Crime Unit of INP 24
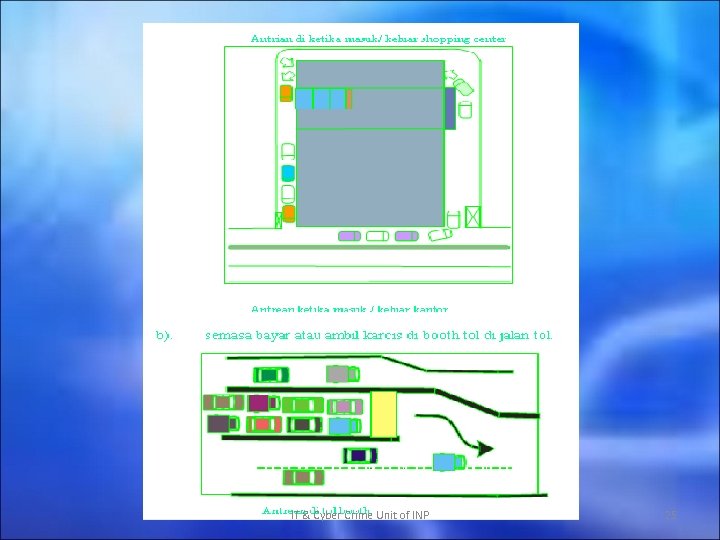 IT & Cyber Crime Unit of INP 25
IT & Cyber Crime Unit of INP 25
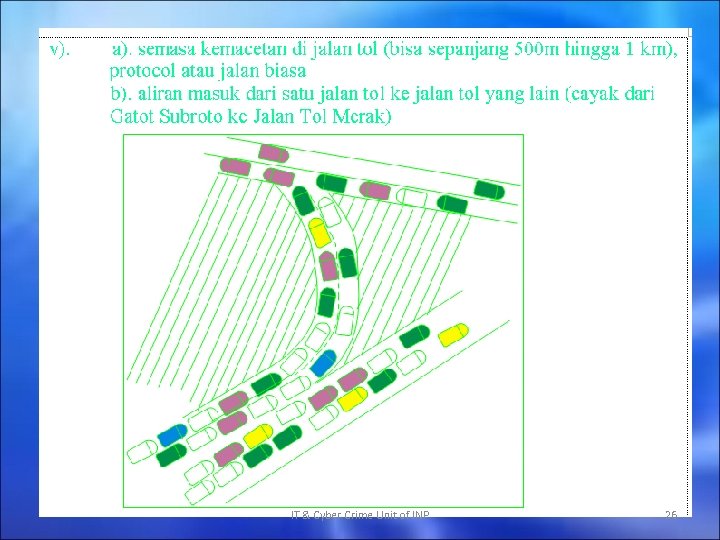 IT & Cyber Crime Unit of INP 26
IT & Cyber Crime Unit of INP 26
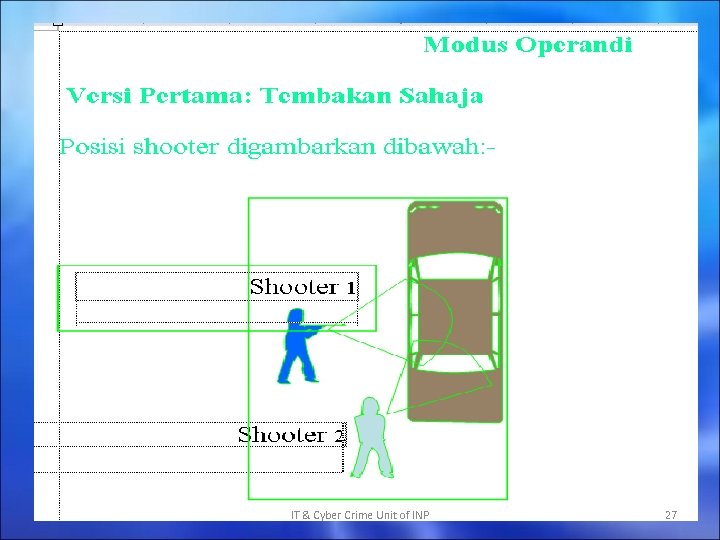 IT & Cyber Crime Unit of INP 27
IT & Cyber Crime Unit of INP 27
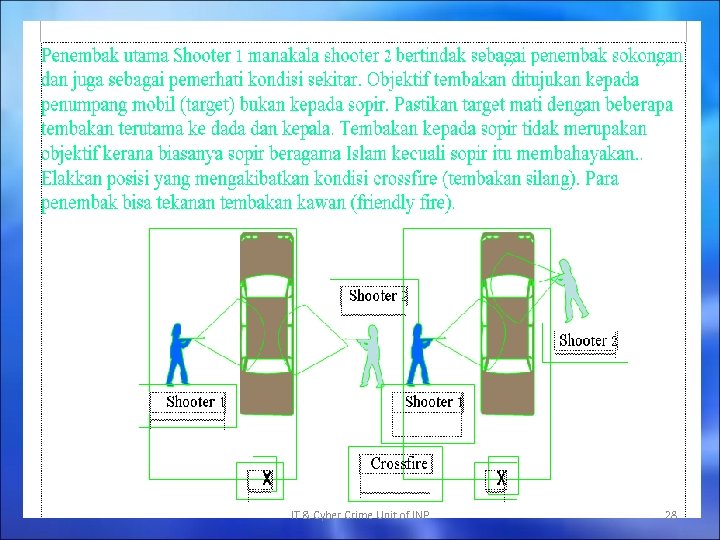 IT & Cyber Crime Unit of INP 28
IT & Cyber Crime Unit of INP 28
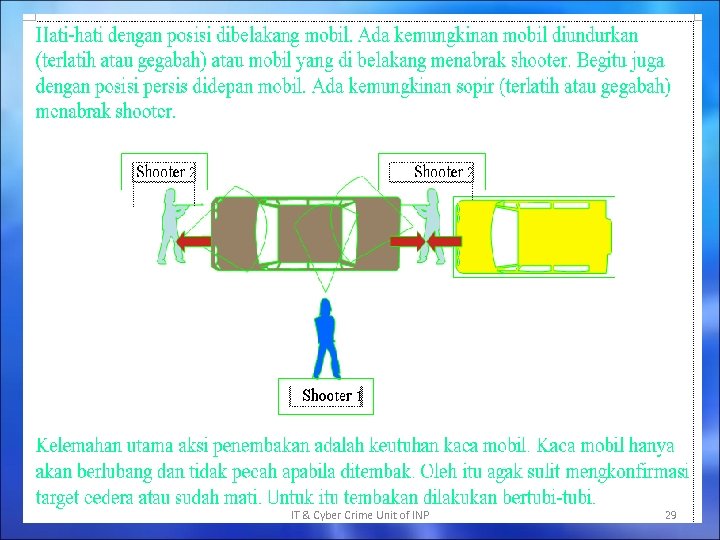 IT & Cyber Crime Unit of INP 29
IT & Cyber Crime Unit of INP 29
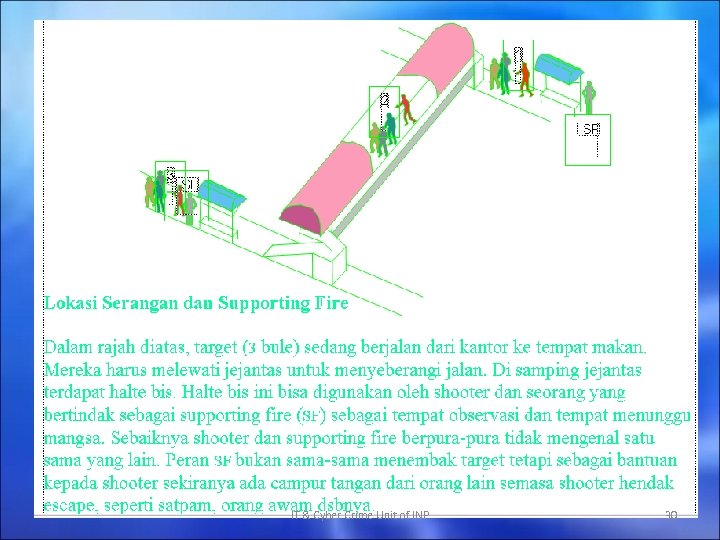 IT & Cyber Crime Unit of INP 30
IT & Cyber Crime Unit of INP 30
 IT & Cyber Crime Unit of INP 31
IT & Cyber Crime Unit of INP 31
 CONCLUSION THE INTERNET WILL FACILITATE THE ABILITY OF TERRORIST ORGANIZATIONS TO COMMUNICATE AMONG THEIR CELLS, RECRUIT NEW MEMBERS, ADVOCATE THEIR VIEWS WITH PROPAGANDA, GATHER INTELLIGENCE OR LAUNCH DEVASTATING ATTACKS ON AN UNPROTECTED CRITICAL INFRASTRUCTURE. NATIONS NEED TO BE AWARE OF AND BE PREPARED TO RESPOND TO TERRORISM ON THE INTERNET. FROM WEBSITE INTENSIVE INVESTIGATION, WE WILL FIND OUT THE PARTIES WHO ACTIVELY INVOLVED IN TERRORIST GROUPS, AND COUNTER THE TERRORISTS THREAT. IT & Cyber Crime Unit of INP 32
CONCLUSION THE INTERNET WILL FACILITATE THE ABILITY OF TERRORIST ORGANIZATIONS TO COMMUNICATE AMONG THEIR CELLS, RECRUIT NEW MEMBERS, ADVOCATE THEIR VIEWS WITH PROPAGANDA, GATHER INTELLIGENCE OR LAUNCH DEVASTATING ATTACKS ON AN UNPROTECTED CRITICAL INFRASTRUCTURE. NATIONS NEED TO BE AWARE OF AND BE PREPARED TO RESPOND TO TERRORISM ON THE INTERNET. FROM WEBSITE INTENSIVE INVESTIGATION, WE WILL FIND OUT THE PARTIES WHO ACTIVELY INVOLVED IN TERRORIST GROUPS, AND COUNTER THE TERRORISTS THREAT. IT & Cyber Crime Unit of INP 32
 THE END IT & Cyber Crime Unit of INP 33
THE END IT & Cyber Crime Unit of INP 33


