add2824a500cdc5fe14d008b0e3029f1.ppt
- Количество слайдов: 6
 TC 57 IEC TC 57 WG 15 - Security Status & Roadmap, TC 57 Plenary, May 2007 Frances Cleveland Convenor WG 15 Presented at Plenary by Herb Falk US Representative to WG 15
TC 57 IEC TC 57 WG 15 - Security Status & Roadmap, TC 57 Plenary, May 2007 Frances Cleveland Convenor WG 15 Presented at Plenary by Herb Falk US Representative to WG 15
 TC 57 Scope of WG 15 on Security 4 Undertake the development of standards for security of the communication protocols defined by the IEC TC 57, specifically the IEC 60870 -5 series, the IEC 60870 -6 series, the IEC 61850 series, the IEC 61970 series, and the IEC 61968 series. 4 Undertake the development of standards and/or technical reports on end-to-end security issues. 4 Other notes of Interest: 4 WG 15 started as Adhoc Working 06 in 1997 (this is the WG’s 10 year anniversary). 4 13 Participating Countries, 32 individuals WG 15 Status October 2005 2
TC 57 Scope of WG 15 on Security 4 Undertake the development of standards for security of the communication protocols defined by the IEC TC 57, specifically the IEC 60870 -5 series, the IEC 60870 -6 series, the IEC 61850 series, the IEC 61970 series, and the IEC 61968 series. 4 Undertake the development of standards and/or technical reports on end-to-end security issues. 4 Other notes of Interest: 4 WG 15 started as Adhoc Working 06 in 1997 (this is the WG’s 10 year anniversary). 4 13 Participating Countries, 32 individuals WG 15 Status October 2005 2
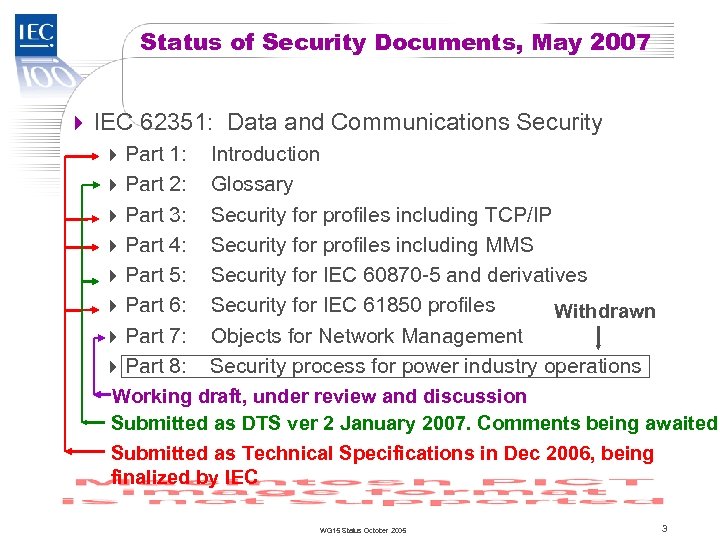 TC 57 Status of Security Documents, May 2007 4 IEC 62351: Data and Communications Security 4 Part 1: Introduction 4 Part 2: Glossary 4 Part 3: Security for profiles including TCP/IP 4 Part 4: Security for profiles including MMS 4 Part 5: Security for IEC 60870 -5 and derivatives 4 Part 6: Security for IEC 61850 profiles Withdrawn 4 Part 7: Objects for Network Management 4 Part 8: Security process for power industry operations Working draft, under review and discussion Submitted as DTS ver 2 January 2007. Comments being awaited Submitted as Technical Specifications in Dec 2006, being finalized by IEC WG 15 Status October 2005 3
TC 57 Status of Security Documents, May 2007 4 IEC 62351: Data and Communications Security 4 Part 1: Introduction 4 Part 2: Glossary 4 Part 3: Security for profiles including TCP/IP 4 Part 4: Security for profiles including MMS 4 Part 5: Security for IEC 60870 -5 and derivatives 4 Part 6: Security for IEC 61850 profiles Withdrawn 4 Part 7: Objects for Network Management 4 Part 8: Security process for power industry operations Working draft, under review and discussion Submitted as DTS ver 2 January 2007. Comments being awaited Submitted as Technical Specifications in Dec 2006, being finalized by IEC WG 15 Status October 2005 3
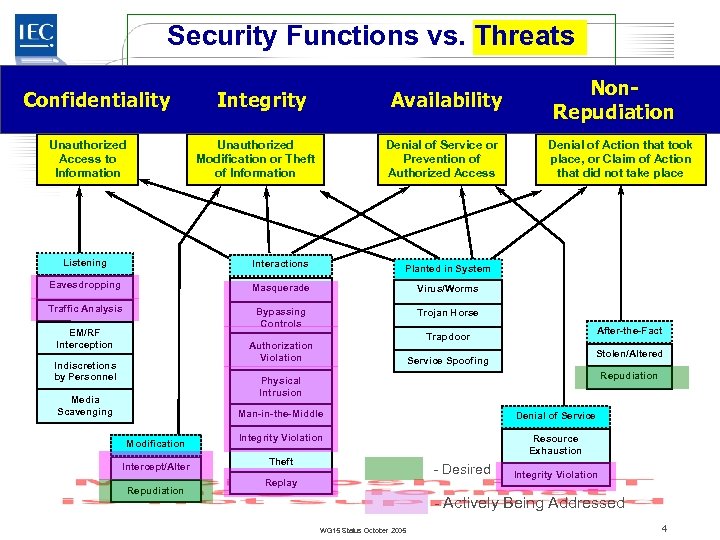 Security Functions vs. Threats TC 57 Confidentiality Unauthorized Access to Information Integrity Availability Unauthorized Modification or Theft of Information Denial of Service or Prevention of Authorized Access Listening Interactions Masquerade Virus/Worms Traffic Analysis Bypassing Controls Denial of Action that took place, or Claim of Action that did not take place Planted in System Eavesdropping Non. Repudiation Trojan Horse EM/RF Interception Authorization Violation Indiscretions by Personnel After-the-Fact Trapdoor Stolen/Altered Service Spoofing Repudiation Physical Intrusion Media Scavenging Man-in-the-Middle Modification Intercept/Alter Repudiation Denial of Service Integrity Violation Resource Exhaustion Theft - Desired Replay Integrity Violation - Actively Being Addressed WG 15 Status October 2005 4
Security Functions vs. Threats TC 57 Confidentiality Unauthorized Access to Information Integrity Availability Unauthorized Modification or Theft of Information Denial of Service or Prevention of Authorized Access Listening Interactions Masquerade Virus/Worms Traffic Analysis Bypassing Controls Denial of Action that took place, or Claim of Action that did not take place Planted in System Eavesdropping Non. Repudiation Trojan Horse EM/RF Interception Authorization Violation Indiscretions by Personnel After-the-Fact Trapdoor Stolen/Altered Service Spoofing Repudiation Physical Intrusion Media Scavenging Man-in-the-Middle Modification Intercept/Alter Repudiation Denial of Service Integrity Violation Resource Exhaustion Theft - Desired Replay Integrity Violation - Actively Being Addressed WG 15 Status October 2005 4
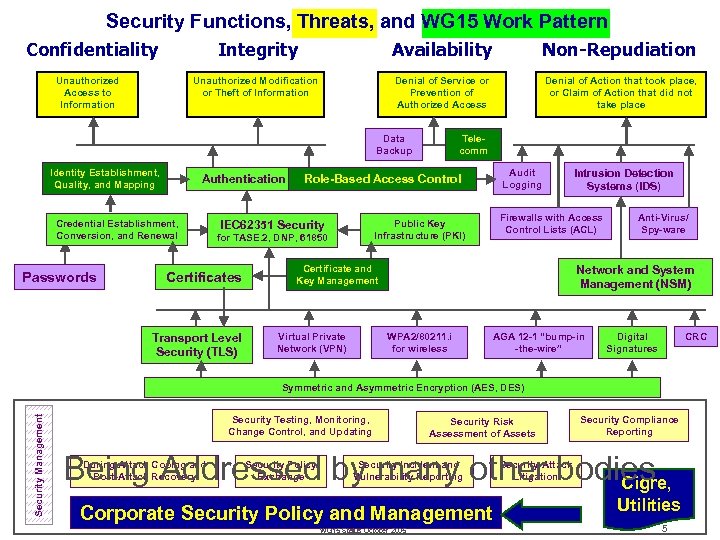 Security Functions, Threats, and WG 15 Work Pattern Integrity Availability Non-Repudiation Unauthorized Modification or Theft of Information Denial of Service or Prevention of Authorized Access Denial of Action that took place, or Claim of Action that did not take place Confidentiality Unauthorized Access to Information Data Backup Identity Establishment, Quality, and Mapping Authentication Credential Establishment, Conversion, and Renewal Passwords Certificate and Key Management Virtual Private Network (VPN) Intrusion Detection Systems (IDS) Firewalls with Access Control Lists (ACL) Public Key Infrastructure (PKI) for TASE. 2, DNP, 61850 Transport Level Security (TLS) Audit Logging Role-Based Access Control IEC 62351 Security Certificates Telecomm Anti-Virus/ Spy-ware Network and System Management (NSM) WPA 2/80211. i for wireless AGA 12 -1 “bump-in -the-wire” Digital Signatures CRC Security Management Symmetric and Asymmetric Encryption (AES, DES) Security Testing, Monitoring, Change Control, and Updating Security Risk Assessment of Assets Security Compliance Reporting Being Addressed by many other bodies Cigre, During-Attack Coping and Post-Attack Recovery Security Policy Exchange Security Incident and Vulnerability Reporting Corporate Security Policy and Management WG 15 Status October 2005 Security Attack Litigation Utilities 5
Security Functions, Threats, and WG 15 Work Pattern Integrity Availability Non-Repudiation Unauthorized Modification or Theft of Information Denial of Service or Prevention of Authorized Access Denial of Action that took place, or Claim of Action that did not take place Confidentiality Unauthorized Access to Information Data Backup Identity Establishment, Quality, and Mapping Authentication Credential Establishment, Conversion, and Renewal Passwords Certificate and Key Management Virtual Private Network (VPN) Intrusion Detection Systems (IDS) Firewalls with Access Control Lists (ACL) Public Key Infrastructure (PKI) for TASE. 2, DNP, 61850 Transport Level Security (TLS) Audit Logging Role-Based Access Control IEC 62351 Security Certificates Telecomm Anti-Virus/ Spy-ware Network and System Management (NSM) WPA 2/80211. i for wireless AGA 12 -1 “bump-in -the-wire” Digital Signatures CRC Security Management Symmetric and Asymmetric Encryption (AES, DES) Security Testing, Monitoring, Change Control, and Updating Security Risk Assessment of Assets Security Compliance Reporting Being Addressed by many other bodies Cigre, During-Attack Coping and Post-Attack Recovery Security Policy Exchange Security Incident and Vulnerability Reporting Corporate Security Policy and Management WG 15 Status October 2005 Security Attack Litigation Utilities 5
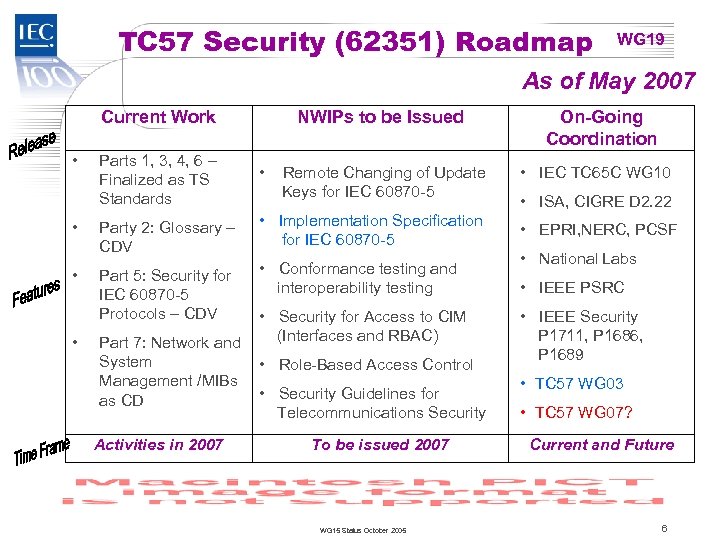 TC 57 Security (62351) Roadmap WG 19 As of May 2007 Current Work • • NWIPs to be Issued Parts 1, 3, 4, 6 – Finalized as TS Standards • Party 2: Glossary – CDV • Implementation Specification for IEC 60870 -5 Part 5: Security for IEC 60870 -5 Protocols – CDV • Conformance testing and interoperability testing Part 7: Network and System Management /MIBs as CD Activities in 2007 Remote Changing of Update Keys for IEC 60870 -5 • Security for Access to CIM (Interfaces and RBAC) • Role-Based Access Control • Security Guidelines for Telecommunications Security To be issued 2007 WG 15 Status October 2005 On-Going Coordination • IEC TC 65 C WG 10 • ISA, CIGRE D 2. 22 • EPRI, NERC, PCSF • National Labs • IEEE PSRC • IEEE Security P 1711, P 1686, P 1689 • TC 57 WG 03 • TC 57 WG 07? Current and Future 6
TC 57 Security (62351) Roadmap WG 19 As of May 2007 Current Work • • NWIPs to be Issued Parts 1, 3, 4, 6 – Finalized as TS Standards • Party 2: Glossary – CDV • Implementation Specification for IEC 60870 -5 Part 5: Security for IEC 60870 -5 Protocols – CDV • Conformance testing and interoperability testing Part 7: Network and System Management /MIBs as CD Activities in 2007 Remote Changing of Update Keys for IEC 60870 -5 • Security for Access to CIM (Interfaces and RBAC) • Role-Based Access Control • Security Guidelines for Telecommunications Security To be issued 2007 WG 15 Status October 2005 On-Going Coordination • IEC TC 65 C WG 10 • ISA, CIGRE D 2. 22 • EPRI, NERC, PCSF • National Labs • IEEE PSRC • IEEE Security P 1711, P 1686, P 1689 • TC 57 WG 03 • TC 57 WG 07? Current and Future 6


