9323448ff29d265a967b9be9867ce6eb.ppt
- Количество слайдов: 45
 Systems Analysis and Design in a Changing World, Fourth Edition 14
Systems Analysis and Design in a Changing World, Fourth Edition 14
 14 Learning Objectives u u u Discuss examples of system interfaces found in information systems Define system inputs and outputs based on the requirements of the application program Design printed and on-screen reports appropriate for recipients Explain the importance of integrity controls Identify required integrity controls for inputs, outputs, data, and processing Discuss issues related to security that affect the design and operation of information systems Systems Analysis and Design in a Changing World, 4 th Edition 2
14 Learning Objectives u u u Discuss examples of system interfaces found in information systems Define system inputs and outputs based on the requirements of the application program Design printed and on-screen reports appropriate for recipients Explain the importance of integrity controls Identify required integrity controls for inputs, outputs, data, and processing Discuss issues related to security that affect the design and operation of information systems Systems Analysis and Design in a Changing World, 4 th Edition 2
 14 Overview u This chapter focuses on system interfaces, system outputs, and system controls that do not require much human interaction u Many system interfaces are electronic transmissions or paper outputs to external agents u System developers need to design and implement integrity and security controls to protect system and its data u Outside threats from Internet and e-commerce are growing concern Systems Analysis and Design in a Changing World, 4 th Edition 3
14 Overview u This chapter focuses on system interfaces, system outputs, and system controls that do not require much human interaction u Many system interfaces are electronic transmissions or paper outputs to external agents u System developers need to design and implement integrity and security controls to protect system and its data u Outside threats from Internet and e-commerce are growing concern Systems Analysis and Design in a Changing World, 4 th Edition 3
 14 Identifying System Interfaces u System interfaces are broadly defined as inputs or outputs with minimal or no human intervention l Inputs from other systems (messages, EDI) l Highly automated input devices such as scanners, barcode reader. l Inputs that are from data in external databases l Outputs to external databases l Outputs with minimal HCI l Outputs to other systems l Process inputs, interact with other systems in real-time and distribute outputs with minimal human interaction Systems Analysis and Design in a Changing World, 4 th Edition 4
14 Identifying System Interfaces u System interfaces are broadly defined as inputs or outputs with minimal or no human intervention l Inputs from other systems (messages, EDI) l Highly automated input devices such as scanners, barcode reader. l Inputs that are from data in external databases l Outputs to external databases l Outputs with minimal HCI l Outputs to other systems l Process inputs, interact with other systems in real-time and distribute outputs with minimal human interaction Systems Analysis and Design in a Changing World, 4 th Edition 4
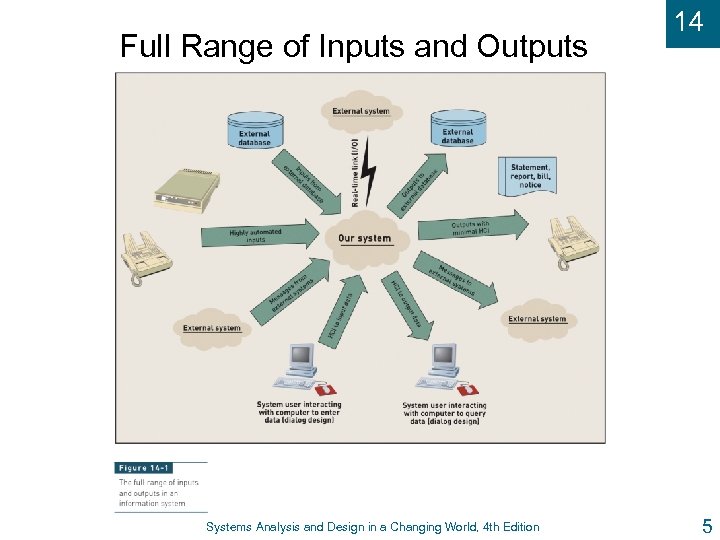 Full Range of Inputs and Outputs Systems Analysis and Design in a Changing World, 4 th Edition 14 5
Full Range of Inputs and Outputs Systems Analysis and Design in a Changing World, 4 th Edition 14 5
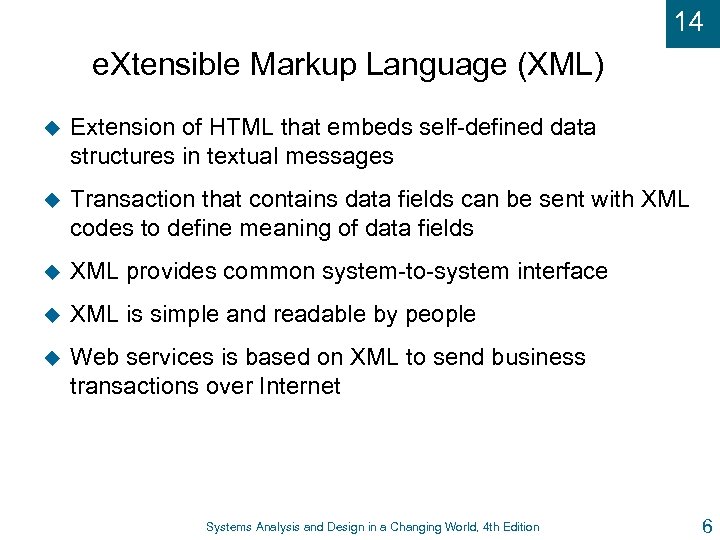 14 e. Xtensible Markup Language (XML) u Extension of HTML that embeds self-defined data structures in textual messages u Transaction that contains data fields can be sent with XML codes to define meaning of data fields u XML provides common system-to-system interface u XML is simple and readable by people u Web services is based on XML to send business transactions over Internet Systems Analysis and Design in a Changing World, 4 th Edition 6
14 e. Xtensible Markup Language (XML) u Extension of HTML that embeds self-defined data structures in textual messages u Transaction that contains data fields can be sent with XML codes to define meaning of data fields u XML provides common system-to-system interface u XML is simple and readable by people u Web services is based on XML to send business transactions over Internet Systems Analysis and Design in a Changing World, 4 th Edition 6
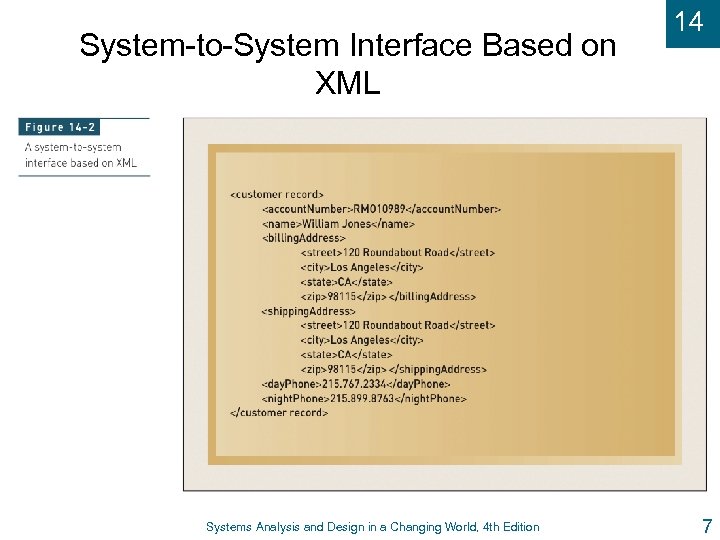 System-to-System Interface Based on XML Systems Analysis and Design in a Changing World, 4 th Edition 14 7
System-to-System Interface Based on XML Systems Analysis and Design in a Changing World, 4 th Edition 14 7
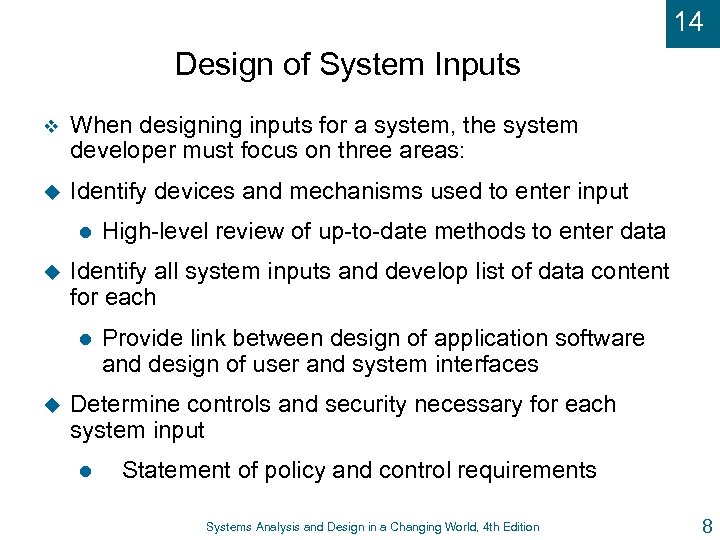 14 Design of System Inputs v When designing inputs for a system, the system developer must focus on three areas: u Identify devices and mechanisms used to enter input l u Identify all system inputs and develop list of data content for each l u High-level review of up-to-date methods to enter data Provide link between design of application software and design of user and system interfaces Determine controls and security necessary for each system input l Statement of policy and control requirements Systems Analysis and Design in a Changing World, 4 th Edition 8
14 Design of System Inputs v When designing inputs for a system, the system developer must focus on three areas: u Identify devices and mechanisms used to enter input l u Identify all system inputs and develop list of data content for each l u High-level review of up-to-date methods to enter data Provide link between design of application software and design of user and system interfaces Determine controls and security necessary for each system input l Statement of policy and control requirements Systems Analysis and Design in a Changing World, 4 th Edition 8
 14 Input Devices and Mechanisms v Several good practices can help to reduce input errors( error-free): u Capture data as close to original source as possible u Use electronic devices and automatic entry whenever possible to avoid human involvement as much as possible o Bar-code reader, touch screen and devices, electronics pen and writing interface, magnetic card strip reader, digitizers, such as digital cameras and digital audio devices u Seek information in electronic form to avoid data re-entry u Validate and correct information at entry point Systems Analysis and Design in a Changing World, 4 th Edition 9
14 Input Devices and Mechanisms v Several good practices can help to reduce input errors( error-free): u Capture data as close to original source as possible u Use electronic devices and automatic entry whenever possible to avoid human involvement as much as possible o Bar-code reader, touch screen and devices, electronics pen and writing interface, magnetic card strip reader, digitizers, such as digital cameras and digital audio devices u Seek information in electronic form to avoid data re-entry u Validate and correct information at entry point Systems Analysis and Design in a Changing World, 4 th Edition 9
 14 Defining the Details of System Inputs u Ensure all data inputs are identified and specified correctly u The idea is same for both structured and OO models. u Traditional structured approach: l Identify automation boundary u Use DFD fragments u Segment l by program boundaries Examine structure charts u Analyze u List each module and data couple individual data fields Systems Analysis and Design in a Changing World, 4 th Edition 10
14 Defining the Details of System Inputs u Ensure all data inputs are identified and specified correctly u The idea is same for both structured and OO models. u Traditional structured approach: l Identify automation boundary u Use DFD fragments u Segment l by program boundaries Examine structure charts u Analyze u List each module and data couple individual data fields Systems Analysis and Design in a Changing World, 4 th Edition 10
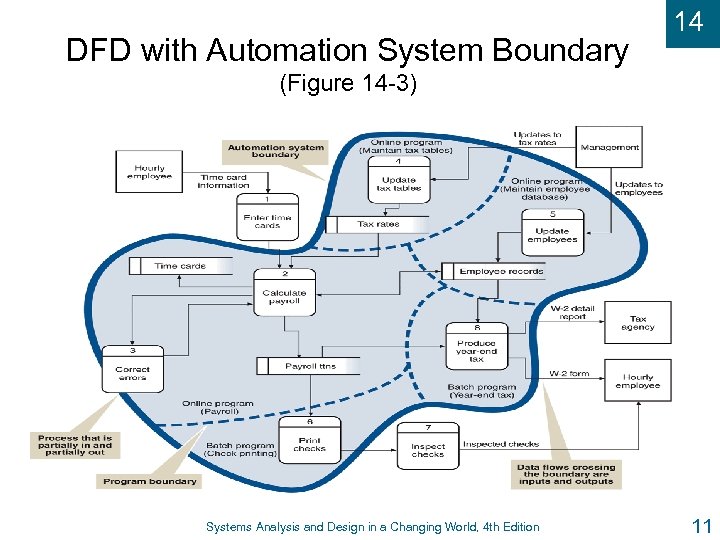 DFD with Automation System Boundary 14 (Figure 14 -3) Systems Analysis and Design in a Changing World, 4 th Edition 11
DFD with Automation System Boundary 14 (Figure 14 -3) Systems Analysis and Design in a Changing World, 4 th Edition 11
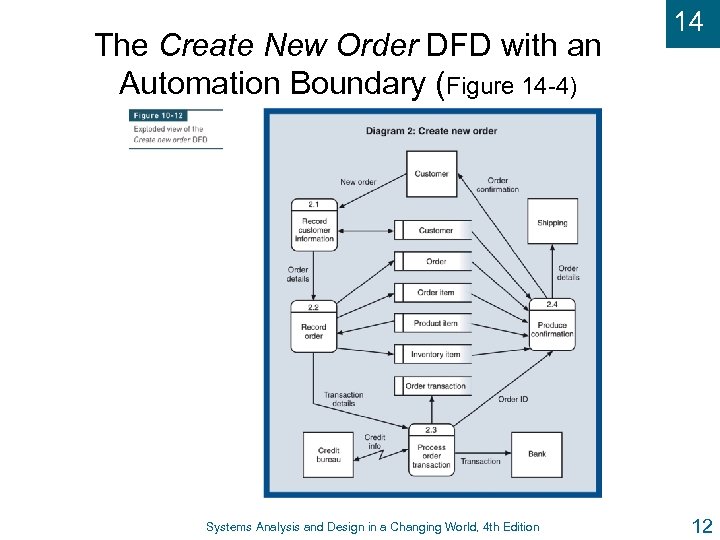 The Create New Order DFD with an Automation Boundary (Figure 14 -4) Systems Analysis and Design in a Changing World, 4 th Edition 14 12
The Create New Order DFD with an Automation Boundary (Figure 14 -4) Systems Analysis and Design in a Changing World, 4 th Edition 14 12
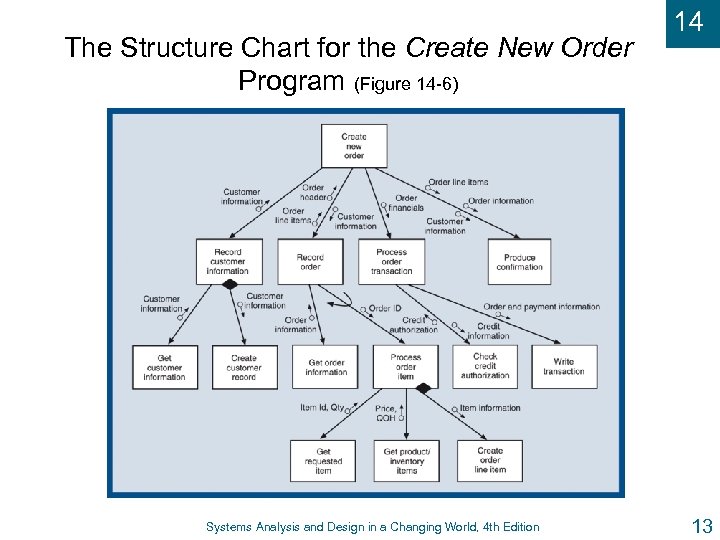 The Structure Chart for the Create New Order Program (Figure 14 -6) Systems Analysis and Design in a Changing World, 4 th Edition 14 13
The Structure Chart for the Create New Order Program (Figure 14 -6) Systems Analysis and Design in a Changing World, 4 th Edition 14 13
 14 Using Object-Oriented Models u Identifying user and system inputs with OO approach has same tasks as traditional approach u OO diagrams are used instead of DFDs and structure charts u System sequence diagrams identify each incoming message u Design class diagrams identify and describe input parameters and verify characteristics of inputs Systems Analysis and Design in a Changing World, 4 th Edition 14
14 Using Object-Oriented Models u Identifying user and system inputs with OO approach has same tasks as traditional approach u OO diagrams are used instead of DFDs and structure charts u System sequence diagrams identify each incoming message u Design class diagrams identify and describe input parameters and verify characteristics of inputs Systems Analysis and Design in a Changing World, 4 th Edition 14
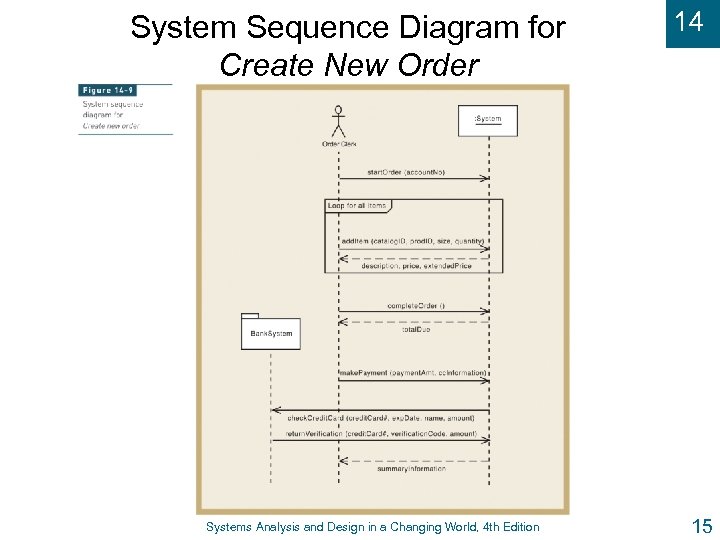 System Sequence Diagram for Create New Order Systems Analysis and Design in a Changing World, 4 th Edition 14 15
System Sequence Diagram for Create New Order Systems Analysis and Design in a Changing World, 4 th Edition 14 15
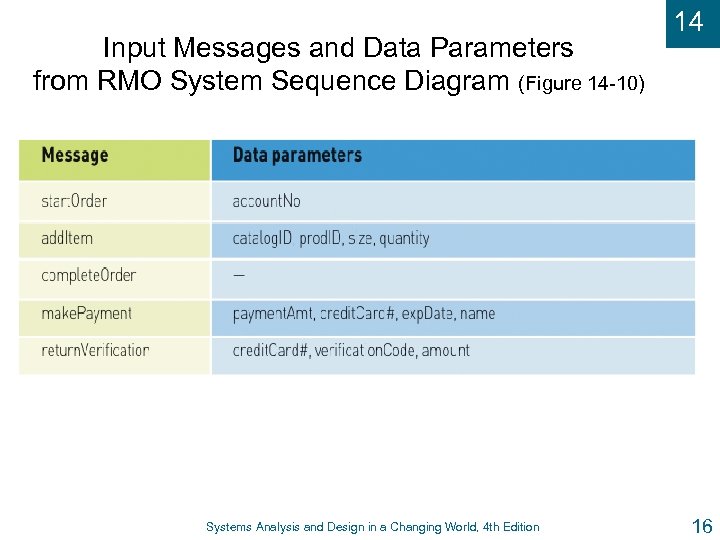 Input Messages and Data Parameters from RMO System Sequence Diagram (Figure 14 -10) Systems Analysis and Design in a Changing World, 4 th Edition 14 16
Input Messages and Data Parameters from RMO System Sequence Diagram (Figure 14 -10) Systems Analysis and Design in a Changing World, 4 th Edition 14 16
 14 Designing System Outputs v As with input design, the tasks in this activities accomplish four objectives: u Determine each type of the system output. u Make list of specific system outputs required based on application design u Specify any necessary controls to protect information provided in output u Design and prototype output layout u Ad hoc reports – designed as needed by user (tools and preformatted tools) Systems Analysis and Design in a Changing World, 4 th Edition 17
14 Designing System Outputs v As with input design, the tasks in this activities accomplish four objectives: u Determine each type of the system output. u Make list of specific system outputs required based on application design u Specify any necessary controls to protect information provided in output u Design and prototype output layout u Ad hoc reports – designed as needed by user (tools and preformatted tools) Systems Analysis and Design in a Changing World, 4 th Edition 17
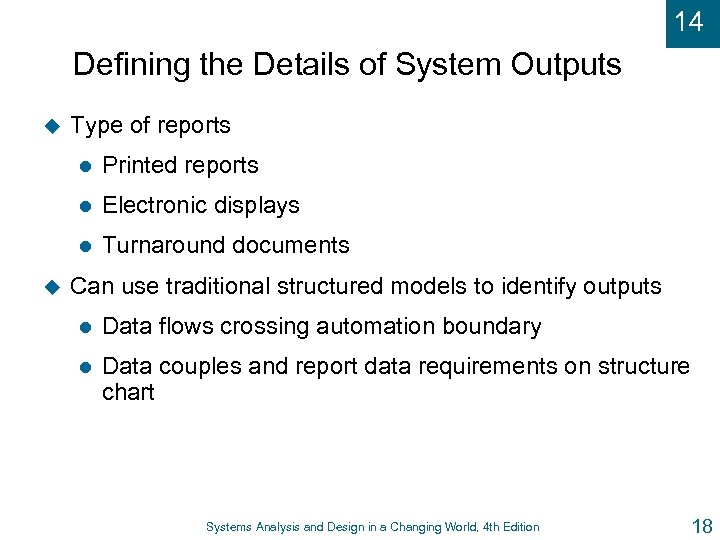 14 Defining the Details of System Outputs u Type of reports l l Electronic displays l u Printed reports Turnaround documents Can use traditional structured models to identify outputs l Data flows crossing automation boundary l Data couples and report data requirements on structure chart Systems Analysis and Design in a Changing World, 4 th Edition 18
14 Defining the Details of System Outputs u Type of reports l l Electronic displays l u Printed reports Turnaround documents Can use traditional structured models to identify outputs l Data flows crossing automation boundary l Data couples and report data requirements on structure chart Systems Analysis and Design in a Changing World, 4 th Edition 18
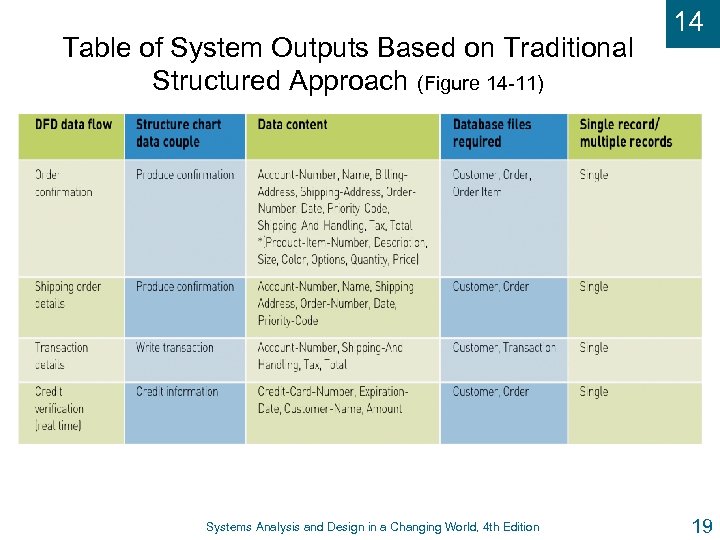 Table of System Outputs Based on Traditional Structured Approach (Figure 14 -11) Systems Analysis and Design in a Changing World, 4 th Edition 14 19
Table of System Outputs Based on Traditional Structured Approach (Figure 14 -11) Systems Analysis and Design in a Changing World, 4 th Edition 14 19
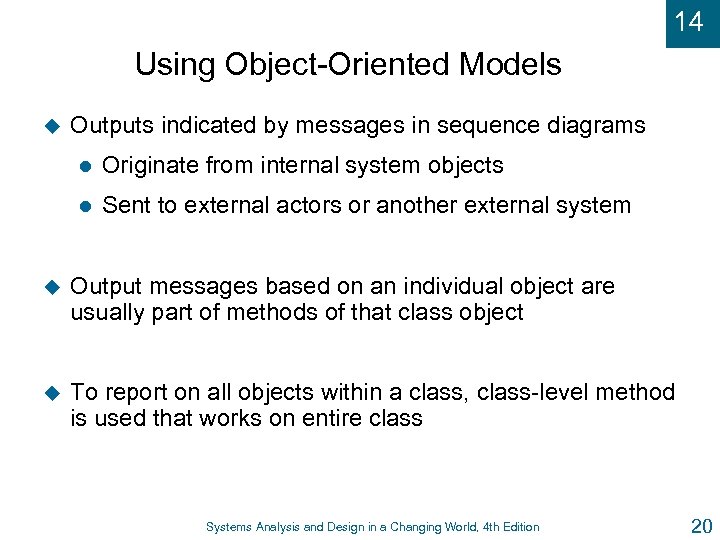 14 Using Object-Oriented Models u Outputs indicated by messages in sequence diagrams l Originate from internal system objects l Sent to external actors or another external system u Output messages based on an individual object are usually part of methods of that class object u To report on all objects within a class, class-level method is used that works on entire class Systems Analysis and Design in a Changing World, 4 th Edition 20
14 Using Object-Oriented Models u Outputs indicated by messages in sequence diagrams l Originate from internal system objects l Sent to external actors or another external system u Output messages based on an individual object are usually part of methods of that class object u To report on all objects within a class, class-level method is used that works on entire class Systems Analysis and Design in a Changing World, 4 th Edition 20
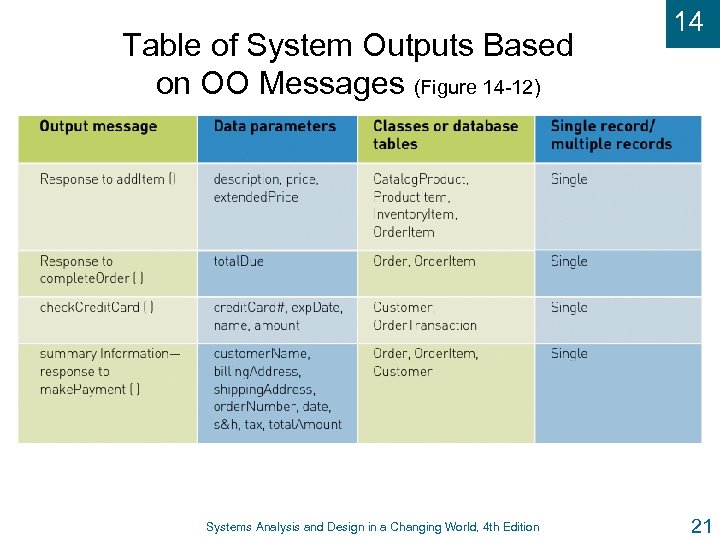 Table of System Outputs Based on OO Messages (Figure 14 -12) Systems Analysis and Design in a Changing World, 4 th Edition 14 21
Table of System Outputs Based on OO Messages (Figure 14 -12) Systems Analysis and Design in a Changing World, 4 th Edition 14 21
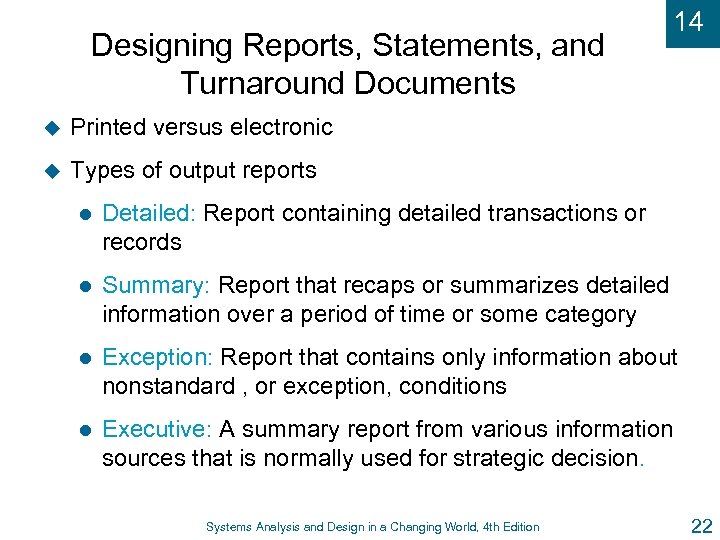 Designing Reports, Statements, and Turnaround Documents u Printed versus electronic u 14 Types of output reports l Detailed: Report containing detailed transactions or records l Summary: Report that recaps or summarizes detailed information over a period of time or some category l Exception: Report that contains only information about nonstandard , or exception, conditions l Executive: A summary report from various information sources that is normally used for strategic decision. Systems Analysis and Design in a Changing World, 4 th Edition 22
Designing Reports, Statements, and Turnaround Documents u Printed versus electronic u 14 Types of output reports l Detailed: Report containing detailed transactions or records l Summary: Report that recaps or summarizes detailed information over a period of time or some category l Exception: Report that contains only information about nonstandard , or exception, conditions l Executive: A summary report from various information sources that is normally used for strategic decision. Systems Analysis and Design in a Changing World, 4 th Edition 22
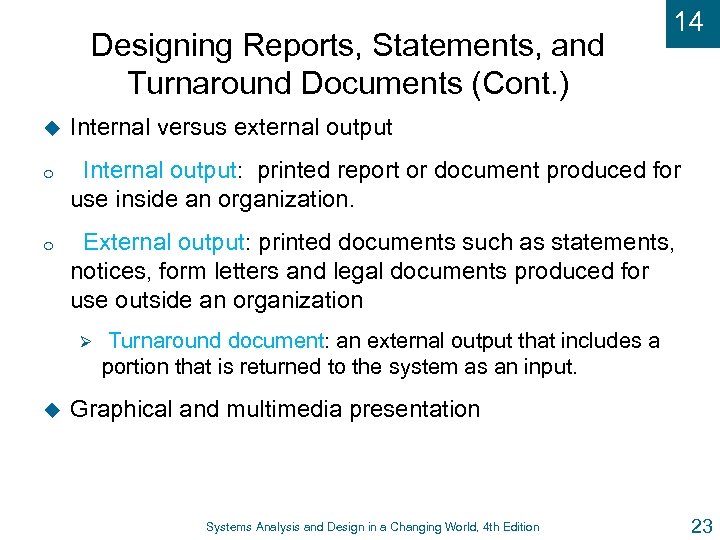 Designing Reports, Statements, and Turnaround Documents (Cont. ) 14 u Internal versus external output o Internal output: printed report or document produced for use inside an organization. o External output: printed documents such as statements, notices, form letters and legal documents produced for use outside an organization Ø u Turnaround document: an external output that includes a portion that is returned to the system as an input. Graphical and multimedia presentation Systems Analysis and Design in a Changing World, 4 th Edition 23
Designing Reports, Statements, and Turnaround Documents (Cont. ) 14 u Internal versus external output o Internal output: printed report or document produced for use inside an organization. o External output: printed documents such as statements, notices, form letters and legal documents produced for use outside an organization Ø u Turnaround document: an external output that includes a portion that is returned to the system as an input. Graphical and multimedia presentation Systems Analysis and Design in a Changing World, 4 th Edition 23
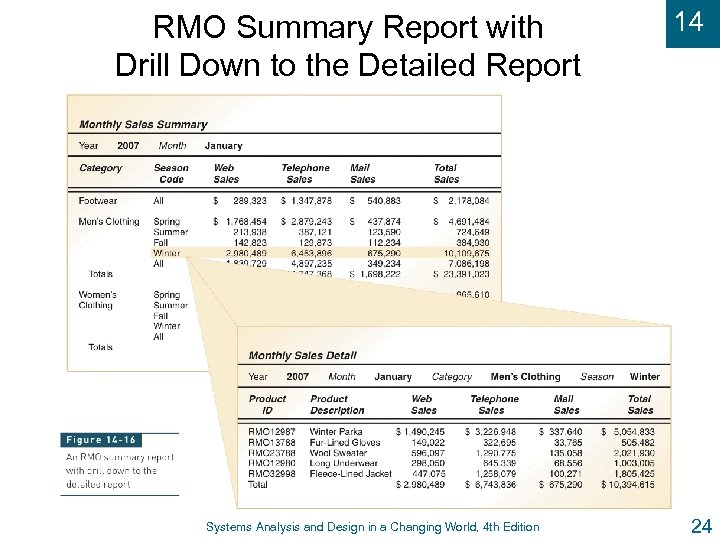 RMO Summary Report with Drill Down to the Detailed Report Systems Analysis and Design in a Changing World, 4 th Edition 14 24
RMO Summary Report with Drill Down to the Detailed Report Systems Analysis and Design in a Changing World, 4 th Edition 14 24
 14 Formatting Reports u What u Who is objective of report? is the intended audience? u What is media for presentation? u Avoid information overload u Format considerations include meaningful headings, date of information, date report produced, page numbers Systems Analysis and Design in a Changing World, 4 th Edition 25
14 Formatting Reports u What u Who is objective of report? is the intended audience? u What is media for presentation? u Avoid information overload u Format considerations include meaningful headings, date of information, date report produced, page numbers Systems Analysis and Design in a Changing World, 4 th Edition 25
 14 Designing Integrity Controls u Mechanisms and procedures built into an application system to safeguard the information contained within u Integrity controls l u Built into application and database system to safeguard information. Security controls l Built into operating system and network Systems Analysis and Design in a Changing World, 4 th Edition 26
14 Designing Integrity Controls u Mechanisms and procedures built into an application system to safeguard the information contained within u Integrity controls l u Built into application and database system to safeguard information. Security controls l Built into operating system and network Systems Analysis and Design in a Changing World, 4 th Edition 26
 14 Objectives of Integrity Controls u Ensure that only appropriate and correct business transactions occur u Ensure that transactions are recorded and processed correctly u Protect and safeguard assets of the organization l Software l Hardware l Information Systems Analysis and Design in a Changing World, 4 th Edition 27
14 Objectives of Integrity Controls u Ensure that only appropriate and correct business transactions occur u Ensure that transactions are recorded and processed correctly u Protect and safeguard assets of the organization l Software l Hardware l Information Systems Analysis and Design in a Changing World, 4 th Edition 27
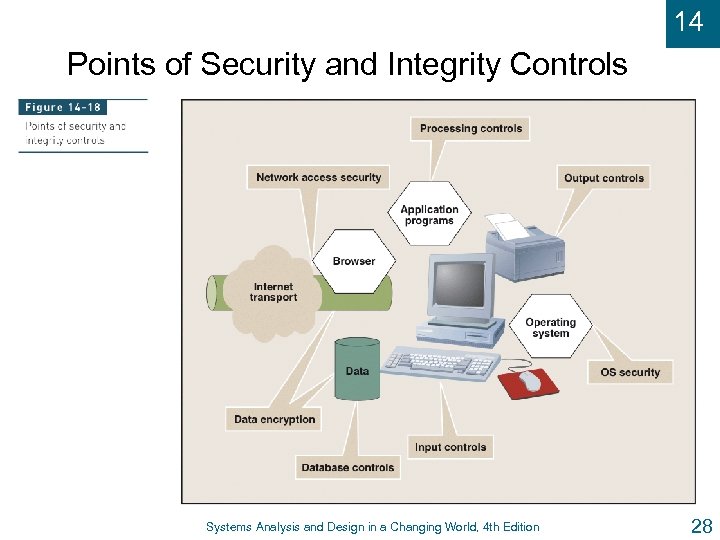 14 Points of Security and Integrity Controls Systems Analysis and Design in a Changing World, 4 th Edition 28
14 Points of Security and Integrity Controls Systems Analysis and Design in a Changing World, 4 th Edition 28
 14 Input Integrity Controls u Used with all input mechanisms u Additional level of verification to help reduce input errors u Common control techniques l Field combination controls: verifies the data in one field based on data in another field or fields ( on an insurance policy, the application date must be prior to the date the policy is place in force. l Value limit controls: identifies when a value in a field is too large or small. Systems Analysis and Design in a Changing World, 4 th Edition 29
14 Input Integrity Controls u Used with all input mechanisms u Additional level of verification to help reduce input errors u Common control techniques l Field combination controls: verifies the data in one field based on data in another field or fields ( on an insurance policy, the application date must be prior to the date the policy is place in force. l Value limit controls: identifies when a value in a field is too large or small. Systems Analysis and Design in a Changing World, 4 th Edition 29
 14 Input Integrity Controls (Cont. ) l Completeness controls: ensure that all necessary field on an input form have been entered ( If a dependent is entered on an insurance form, that person`s birthdays must be entered). l Data validation controls: ensure that the numeric fields that contain code are correct ( national ID numbers might be created with ten-digit) Systems Analysis and Design in a Changing World, 4 th Edition 30
14 Input Integrity Controls (Cont. ) l Completeness controls: ensure that all necessary field on an input form have been entered ( If a dependent is entered on an insurance form, that person`s birthdays must be entered). l Data validation controls: ensure that the numeric fields that contain code are correct ( national ID numbers might be created with ten-digit) Systems Analysis and Design in a Changing World, 4 th Edition 30
 14 Database Integrity Controls v Most DBMS include integrity control and security features. u Access controls u Data encryption u Transaction controls u Update controls u Backup and recovery protection Systems Analysis and Design in a Changing World, 4 th Edition 31
14 Database Integrity Controls v Most DBMS include integrity control and security features. u Access controls u Data encryption u Transaction controls u Update controls u Backup and recovery protection Systems Analysis and Design in a Changing World, 4 th Edition 31
 14 Output Integrity Controls u Ensure output arrives at proper destination and is correct, accurate, complete, and current u Destination controls - output is channeled to correct people u Completeness, accuracy, and correctness controls u Appropriate information present in output Systems Analysis and Design in a Changing World, 4 th Edition 32
14 Output Integrity Controls u Ensure output arrives at proper destination and is correct, accurate, complete, and current u Destination controls - output is channeled to correct people u Completeness, accuracy, and correctness controls u Appropriate information present in output Systems Analysis and Design in a Changing World, 4 th Edition 32
 14 Integrity Controls to Prevent Fraud u Three conditions are present in fraud cases l l Rationalizations, including “I will repay this money” or “I have this coming” l u Personal pressure, such as desire to maintain extravagant lifestyle Opportunity, such as unverified cash receipts Control of fraud requires both manual procedures and computer integrity controls Systems Analysis and Design in a Changing World, 4 th Edition 33
14 Integrity Controls to Prevent Fraud u Three conditions are present in fraud cases l l Rationalizations, including “I will repay this money” or “I have this coming” l u Personal pressure, such as desire to maintain extravagant lifestyle Opportunity, such as unverified cash receipts Control of fraud requires both manual procedures and computer integrity controls Systems Analysis and Design in a Changing World, 4 th Edition 33
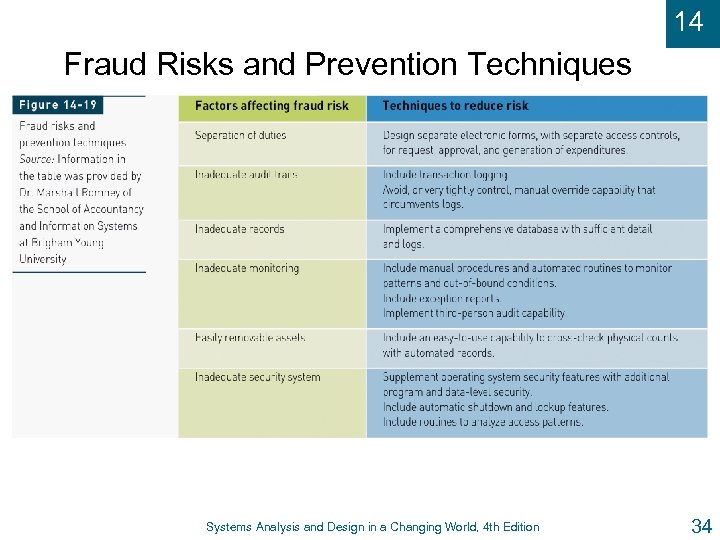 14 Fraud Risks and Prevention Techniques Systems Analysis and Design in a Changing World, 4 th Edition 34
14 Fraud Risks and Prevention Techniques Systems Analysis and Design in a Changing World, 4 th Edition 34
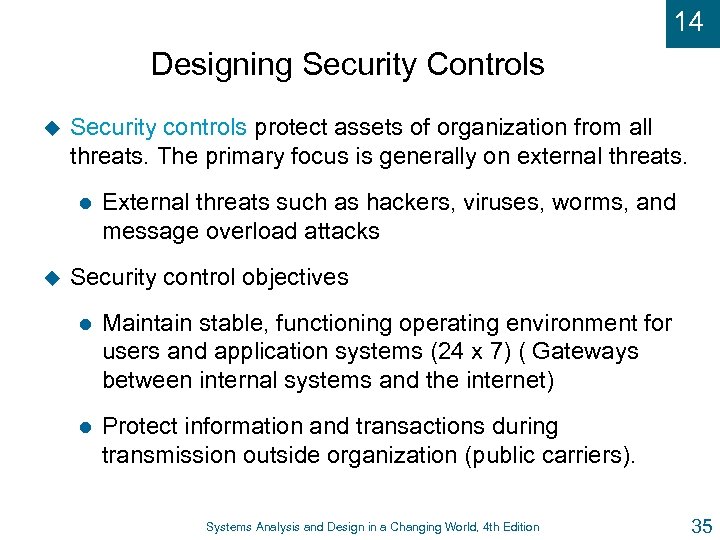 14 Designing Security Controls u Security controls protect assets of organization from all threats. The primary focus is generally on external threats. l u External threats such as hackers, viruses, worms, and message overload attacks Security control objectives l Maintain stable, functioning operating environment for users and application systems (24 x 7) ( Gateways between internal systems and the internet) l Protect information and transactions during transmission outside organization (public carriers). Systems Analysis and Design in a Changing World, 4 th Edition 35
14 Designing Security Controls u Security controls protect assets of organization from all threats. The primary focus is generally on external threats. l u External threats such as hackers, viruses, worms, and message overload attacks Security control objectives l Maintain stable, functioning operating environment for users and application systems (24 x 7) ( Gateways between internal systems and the internet) l Protect information and transactions during transmission outside organization (public carriers). Systems Analysis and Design in a Changing World, 4 th Edition 35
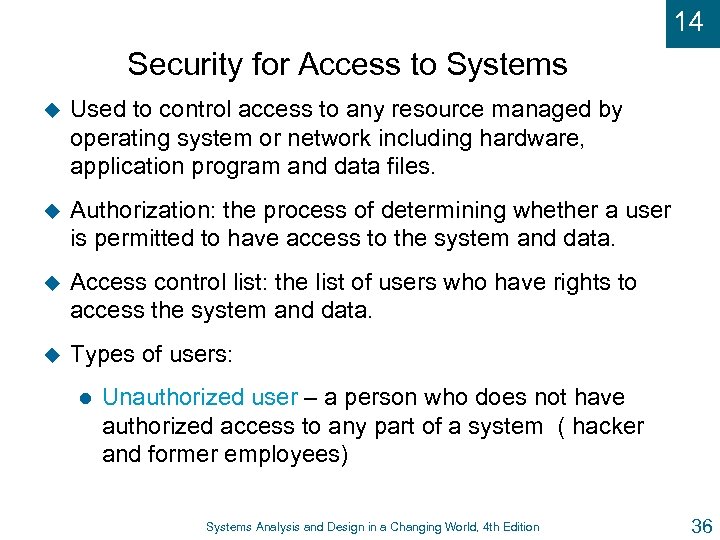 14 Security for Access to Systems u Used to control access to any resource managed by operating system or network including hardware, application program and data files. u Authorization: the process of determining whether a user is permitted to have access to the system and data. u Access control list: the list of users who have rights to access the system and data. u Types of users: l Unauthorized user – a person who does not have authorized access to any part of a system ( hacker and former employees) Systems Analysis and Design in a Changing World, 4 th Edition 36
14 Security for Access to Systems u Used to control access to any resource managed by operating system or network including hardware, application program and data files. u Authorization: the process of determining whether a user is permitted to have access to the system and data. u Access control list: the list of users who have rights to access the system and data. u Types of users: l Unauthorized user – a person who does not have authorized access to any part of a system ( hacker and former employees) Systems Analysis and Design in a Changing World, 4 th Edition 36
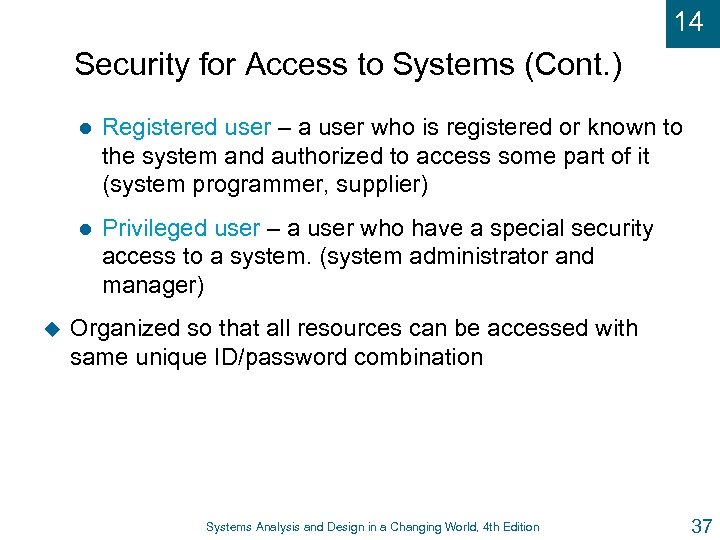 14 Security for Access to Systems (Cont. ) l l u Registered user – a user who is registered or known to the system and authorized to access some part of it (system programmer, supplier) Privileged user – a user who have a special security access to a system. (system administrator and manager) Organized so that all resources can be accessed with same unique ID/password combination Systems Analysis and Design in a Changing World, 4 th Edition 37
14 Security for Access to Systems (Cont. ) l l u Registered user – a user who is registered or known to the system and authorized to access some part of it (system programmer, supplier) Privileged user – a user who have a special security access to a system. (system administrator and manager) Organized so that all resources can be accessed with same unique ID/password combination Systems Analysis and Design in a Changing World, 4 th Edition 37
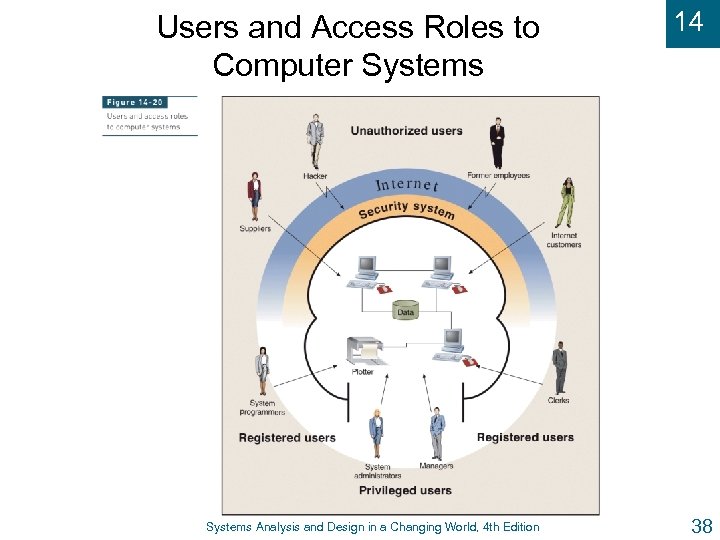 Users and Access Roles to Computer Systems Analysis and Design in a Changing World, 4 th Edition 14 38
Users and Access Roles to Computer Systems Analysis and Design in a Changing World, 4 th Edition 14 38
 14 Managing User Access u Most common technique is user ID / password u Authentication – the process of identifying a user to verify that he can access to the system u Smart card – computer-readable plastic card with embedded security information u Biometric devices – keystroke patterns, fingerprinting, retinal scans, voice characteristics Systems Analysis and Design in a Changing World, 4 th Edition 39
14 Managing User Access u Most common technique is user ID / password u Authentication – the process of identifying a user to verify that he can access to the system u Smart card – computer-readable plastic card with embedded security information u Biometric devices – keystroke patterns, fingerprinting, retinal scans, voice characteristics Systems Analysis and Design in a Changing World, 4 th Edition 39
 14 Data Security u Data and files themselves must be secure u Encryption – primary security method l u Altering data so unauthorized users cannot view. Decryption l Altering encrypted data back to its original state u Symmetric key – same key encrypts and decrypts u Asymmetric key – different key decrypts u Public key – public encrypts; private decrypts Systems Analysis and Design in a Changing World, 4 th Edition 40
14 Data Security u Data and files themselves must be secure u Encryption – primary security method l u Altering data so unauthorized users cannot view. Decryption l Altering encrypted data back to its original state u Symmetric key – same key encrypts and decrypts u Asymmetric key – different key decrypts u Public key – public encrypts; private decrypts Systems Analysis and Design in a Changing World, 4 th Edition 40
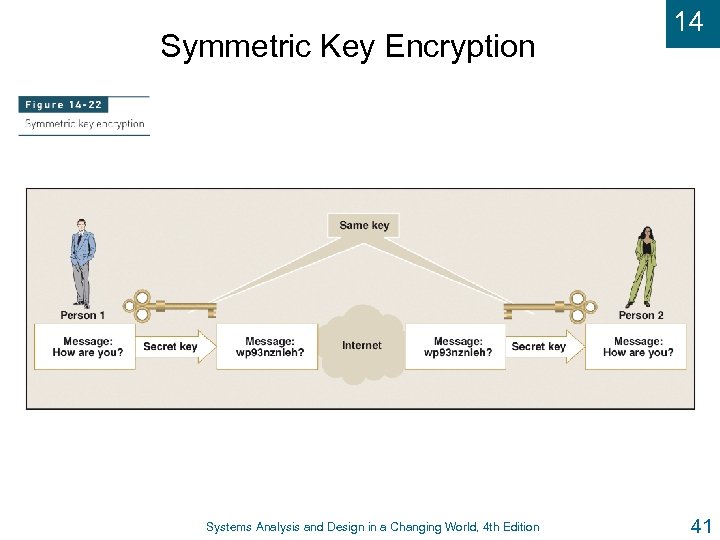 Symmetric Key Encryption Systems Analysis and Design in a Changing World, 4 th Edition 14 41
Symmetric Key Encryption Systems Analysis and Design in a Changing World, 4 th Edition 14 41
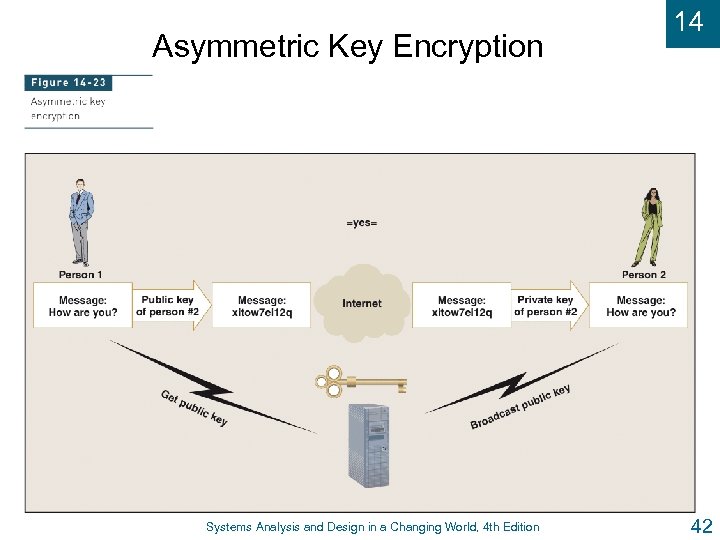 Asymmetric Key Encryption Systems Analysis and Design in a Changing World, 4 th Edition 14 42
Asymmetric Key Encryption Systems Analysis and Design in a Changing World, 4 th Edition 14 42
 14 Digital Signatures and Certificates u Encryption of messages enables secure exchange of information between two entities with appropriate keys u Digital signature encrypts document with private key to verify document author u Digital certificate is institution’s name and public key that is encrypted and certified by third party u Certifying authority l Veri. Sign or Equifax Systems Analysis and Design in a Changing World, 4 th Edition 43
14 Digital Signatures and Certificates u Encryption of messages enables secure exchange of information between two entities with appropriate keys u Digital signature encrypts document with private key to verify document author u Digital certificate is institution’s name and public key that is encrypted and certified by third party u Certifying authority l Veri. Sign or Equifax Systems Analysis and Design in a Changing World, 4 th Edition 43
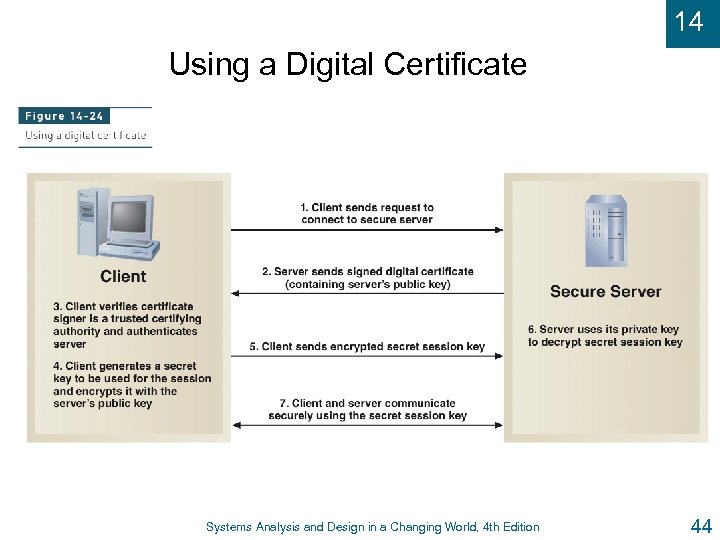 14 Using a Digital Certificate Systems Analysis and Design in a Changing World, 4 th Edition 44
14 Using a Digital Certificate Systems Analysis and Design in a Changing World, 4 th Edition 44
 14 Secure Transactions u Standard set of methods and protocols for authentication, authorization, privacy, integrity u Secure Sockets Layer (SSL) renamed as Transport Layer Security (TLS) – protocol for secure channel to send messages over Internet u IP Security (IPSec) – newer standard for transmitting Internet messages securely u Secure Hypertext Transport Protocol (HTTPS or HTTP-S) – standard for transmitting Web pages securely (encryption, digital signing, certificates) Systems Analysis and Design in a Changing World, 4 th Edition 45
14 Secure Transactions u Standard set of methods and protocols for authentication, authorization, privacy, integrity u Secure Sockets Layer (SSL) renamed as Transport Layer Security (TLS) – protocol for secure channel to send messages over Internet u IP Security (IPSec) – newer standard for transmitting Internet messages securely u Secure Hypertext Transport Protocol (HTTPS or HTTP-S) – standard for transmitting Web pages securely (encryption, digital signing, certificates) Systems Analysis and Design in a Changing World, 4 th Edition 45


