a9b4ebba1b316b62bdca87c838eb3332.ppt
- Количество слайдов: 18
Strategic Considerations in Cyber Warfare OASIS PI Meeting, Santa Fe, NM July 25, 2001 Matt Stillerman, Ph. D Odyssey Research Associates 33 Thornwood Drive, Suite 500 Ithaca, NY 14850 matt@oracorp. com
Overview • Project title: Novel Applications of Military Science to Intrusion Tolerant Systems – Mining military theory for ideas about cyber warfare. • Universal theory of strategy (as expounded by Edward Luttwak) – Implications for cyber warfare • Summary 7/25/2001 SL 01 -018 2 Odyssey Research Associates Not for public release.
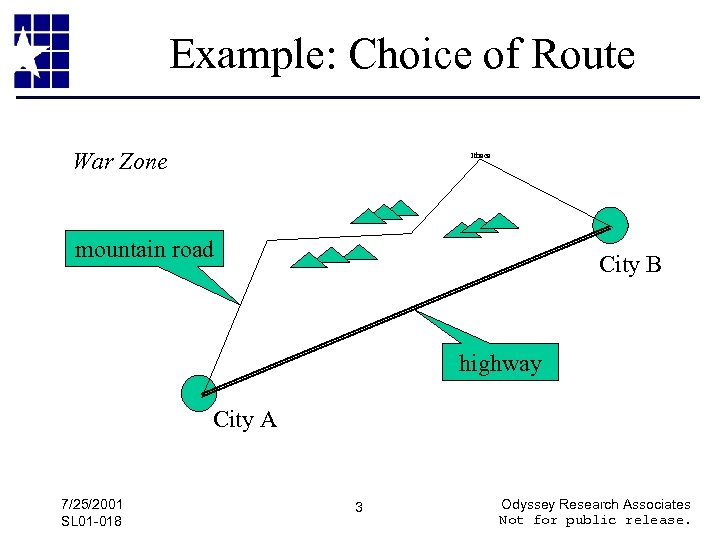
Example: Choice of Route War Zone Ithaca mountain road City B highway City A 7/25/2001 SL 01 -018 3 Odyssey Research Associates Not for public release.
Invasion of Lebanon, 1982 • Israel always maneuvered in non-obvious ways, was known to do this. • Syria expected Israel to advance via a round -about route, was initially able to block them, effectively. • Israel countered by advancing straight into the Vale of Lebanon, without opposition. 7/25/2001 SL 01 -018 4 Odyssey Research Associates Not for public release.
Paradoxical Logic • Counter-intuitive values (or effectiveness) in warfare • Convergence of opposites, eventual reversal of values over time. 7/25/2001 SL 01 -018 5 Odyssey Research Associates Not for public release.
Paradoxical Logic • Key difference between warfare and other human activities. • Universal: All wars, all theaters, all levels of war. • Caused by the ability and inclination of adversaries to anticipate actions and react to them. 7/25/2001 SL 01 -018 6 Odyssey Research Associates Not for public release.
Surprise = failure to anticipate 7/25/2001 SL 01 -018 7 Odyssey Research Associates Not for public release.
Strategy = Art of command in situations governed by paradoxical logic. • Anticipate the paradox. • Engineer surprise. – Change behavior – Deception 7/25/2001 SL 01 -018 8 Odyssey Research Associates Not for public release.
Let Many Flowers Bloom • Surprise attackers with novel counter-measures. • Avoid standardization of defenses. • Develop diverse overlapping defense techniques. – Less effective techniques have greater longevity. – Diversity of strategic choice. – Continuous stream of new techniques as old ones become stale. 7/25/2001 SL 01 -018 9 Odyssey Research Associates Not for public release.
Promote Obscurity • “Security by obscurity” – now a valid principle. • Obscurity can be relatively inexpensive. • Yet, while it persists, it can be just as effective as “real” security measures. • Measures designed to promote system-wide integration of security features may degrade obscurity. 7/25/2001 SL 01 -018 10 Odyssey Research Associates Not for public release.
Empower Strategists • Source of surprise is human perception and ingenuity. – Clausewitz calls this “genius. ” • Cyber Warriors must have: – Training – Technical choices – Authority • Automated cyber defenses amplify warriors, don’t replace them. 7/25/2001 SL 01 -018 11 Odyssey Research Associates Not for public release.
Guided Missiles vs. Tanks • Egyptian infantry easily destroyed Israeli tanks at the beginning of the 1973 War. • Suggests that tanks are obsolete. (wrong!) – Similar comments were made about bazookas • By the end of that war, a change in tactics largely restored tank effectiveness. 7/25/2001 SL 01 -018 12 Odyssey Research Associates Not for public release.
Electronic Warfare in WWII “In the ebb and flow of reciprocal development, the same device could be highly effective, totally useless, and positively dangerous within a matter of months…” -- Luttwak Example: rearward-looking radars on British bombers. 7/25/2001 SL 01 -018 13 Odyssey Research Associates Not for public release.
Battle of Berlin • Technical advances enabled Allied aircraft to blind German radar defenses. • This enabled a massive aerial bombardment that destroyed Hamburg. • Similar attack against Berlin attempted. • Germans responded, using searchlights to find the “streams” of bombers, ground commentary, and non-radar equipped fighters. 7/25/2001 SL 01 -018 14 Odyssey Research Associates Not for public release.
Pearls • Action and effective reaction may occur at different levels in the conflict. – Information technologists should try to anticipate tactical, operational, and strategic responses. – “Pure” cyber war will be fought on all levels. • Cycle of action/reaction may occur very swiftly in a hot war. – Explicitly manage the life-cycle of cyber defenses. 7/25/2001 SL 01 -018 15 Odyssey Research Associates Not for public release.
Life-cycle of Cyber Defenses • • Detect culminating point and act. Have new choices “on tap. ” Avoid complacency about solved problems. Prepare to innovate furiously and to deploy the results swiftly. – Active infosec research community – Native IT manufacturing capability 7/25/2001 SL 01 -018 16 Odyssey Research Associates Not for public release.
Levels of Cyber Warfare • Technical – e. g. firewall. • Tactical – e. g. How the firewall is deployed, configured. • Operational – Which information is created, how it is used in theater. Concerned with meaning, quality, and assurance. • Strategic – Role of meaning and quality in achieving war aims. 7/25/2001 SL 01 -018 17 Odyssey Research Associates Not for public release.
Reference • Edward N. Luttwak. Strategy: The Logic of War and Peace. Belknap Press, Harvard University, 1987. 7/25/2001 SL 01 -018 18 Odyssey Research Associates Not for public release.
a9b4ebba1b316b62bdca87c838eb3332.ppt