1bb1ab151ac663cb384a20f6ab74b713.ppt
- Количество слайдов: 18
 Steganography JF Kalka CIS 450
Steganography JF Kalka CIS 450
 Steganography an Intro • • What is steganography Applications Methods References
Steganography an Intro • • What is steganography Applications Methods References
 Etymology • The word steganography comes from the Greek steganos (covered or secret) and graphy (writing or drawing) and thus means, literally, covered writing. Steganography is usually given as a synonym for cryptography but it is not normally used in that way. • Used in ancient Greece to present day
Etymology • The word steganography comes from the Greek steganos (covered or secret) and graphy (writing or drawing) and thus means, literally, covered writing. Steganography is usually given as a synonym for cryptography but it is not normally used in that way. • Used in ancient Greece to present day
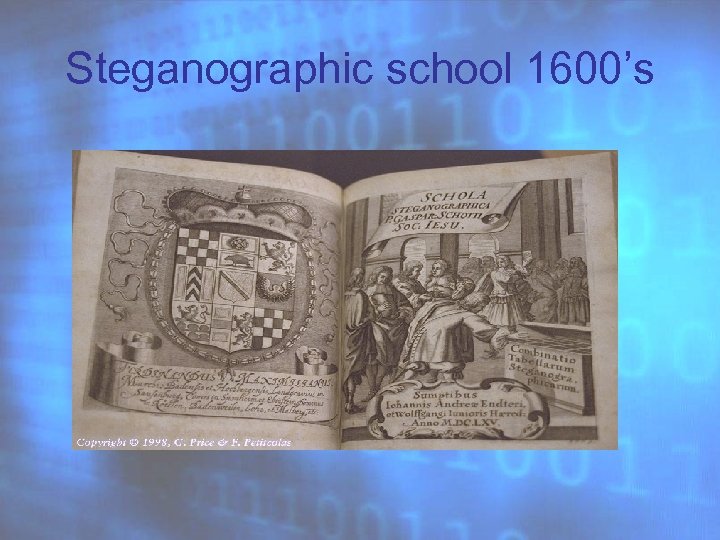 Steganographic school 1600’s
Steganographic school 1600’s
 Steganography • Means covered or hidden writing • Involves hiding a message in a carrier e. g. an image • Carrier is then sent to a receiver without anyone but the sender and receiver knowing it contains a message • Objective is not to prevent the message being read but to hide its existence • Important not to draw attention to the carrier
Steganography • Means covered or hidden writing • Involves hiding a message in a carrier e. g. an image • Carrier is then sent to a receiver without anyone but the sender and receiver knowing it contains a message • Objective is not to prevent the message being read but to hide its existence • Important not to draw attention to the carrier
 Uses for Steganography • Covert Communication – Civil Rights Organisations – Terrorists • Watermarking
Uses for Steganography • Covert Communication – Civil Rights Organisations – Terrorists • Watermarking
 • In the computer, an image is an array of numbers that represent light intensities at various points (pixels 1) in the image. A common image size is 640 by 480 and 256 colors (or 8 bits per pixel). Such an image could contain about 300 kilobits of data. • There are usually two type of files used when embedding data into an image. The innocent looking image which will hold the hidden information is a "container. " A "message" is the information to be hidden. A message may be plain-text, ciphertext, other images or any thing that can be embedded in the least significant bits (LSB) of an image.
• In the computer, an image is an array of numbers that represent light intensities at various points (pixels 1) in the image. A common image size is 640 by 480 and 256 colors (or 8 bits per pixel). Such an image could contain about 300 kilobits of data. • There are usually two type of files used when embedding data into an image. The innocent looking image which will hold the hidden information is a "container. " A "message" is the information to be hidden. A message may be plain-text, ciphertext, other images or any thing that can be embedded in the least significant bits (LSB) of an image.
 • Color is represented by a 6 -digit Hexadecimal 4 f 2 d 6 e • Actually 3 pairs on each for RGB • 100 % = FF or 255 or 1111
• Color is represented by a 6 -digit Hexadecimal 4 f 2 d 6 e • Actually 3 pairs on each for RGB • 100 % = FF or 255 or 1111
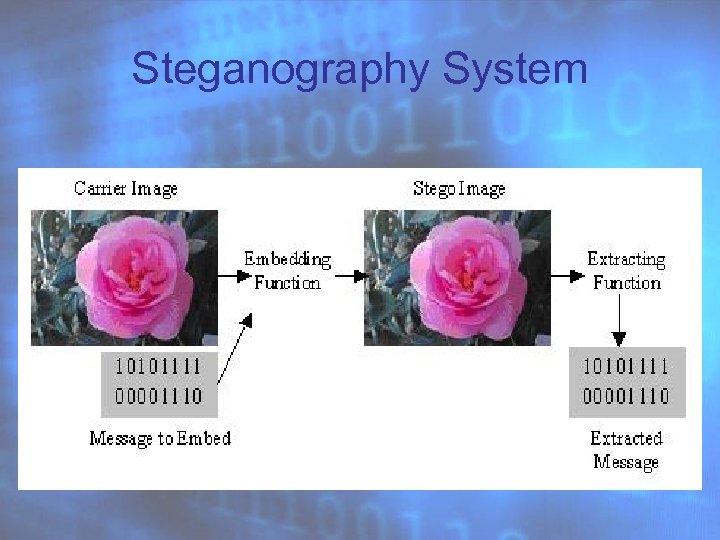 Steganography System
Steganography System
 • The importance is not whether the image is gray-scale or not, the importance is the degree to which the colors change between bit values. • Gray-scale images are very good because the shades gradually change from byte to byte. The following is a palette containing 256 shades of gray.
• The importance is not whether the image is gray-scale or not, the importance is the degree to which the colors change between bit values. • Gray-scale images are very good because the shades gradually change from byte to byte. The following is a palette containing 256 shades of gray.


 Applications • • • Pretty Good Envelope (Robert G. Durnal), hides data in almost any file. In fact it embeds a binary message in a larger binary file by appending the message to the covert file as well as a 4 -byte pointer to the start of the message. To retrieve the message, the last 4 bytes of the file are read, the file pointer is set to that value, and the file read from that point. Publimark (Gaëtan Le Guelvouit) is a command line tool to secretly embed text in an audio file. It uses a pair of keys: the public one can be shared, whereas the private one must be kept secret. Anybody can send a teganographic message, but only the private key owner s will be able read it. Secur. Engine (Adrien Pinet) hides files into 24 bitmap images (JPEG or BMP) or even text files. Files can be encrypted using GOST, Vernam or ‘ 3 -way’. Stealth (Adam Back) is a simple filter for PGP 2. x which strips of all identifying header information. Only the encrypted data (which looks like random noise) remains; thus it is suitable for steganographic use. Snow (Matthew Knaw, University of Melbourne, Australia) is used to conceal messages in ASCII text by appending white spaces to the end of lines. Steganography Tools 4 (Andy Brown) encrypts the data with IDEA, MPJ 2, DES, 3 DES and NSEA in CBC, ECB, CFB, OFB and PCBC modes and hides it inside graphics (by modifying the LSB of BMP files), digital audio (WAV files) or unused sectors of HD floppies. The embedded message is usually very small. Steganos (Demcom, Frankfurt, Germany) is an easy to use wizard style program to hide and/or encrypt files. Steganos encrypts files and hides them within various different types of files. It also include a text editor using the soft-tempest technology. Many other security features are included. Steghide (Stefan Hetzl, Austria) features hiding data in BMP, WAV and AU files, blowfish encryption, MD 5 hashing of assphrases to p blowfish keys and pseudo-random distribution of hidden bits in the cover-data. Stegodos (Black Wolf’s Picture Encoder) is a set of DOS programs that encodes messages into GIF or PCX images. It works only with 320 x 200 x 256 pictures. The data embedded by modifying the LSB of the picture is noticeable in most cases. Stegonosaurus (John Walker, Switzerland) is a Unix program that will convert any binary file into nonsense text, but which statistically resembles text in the language of the dictionary supplied. Stegono. Wav (Peter Heist) is a Java (JDK 1. 0) program that hides information in 16 -bit wav files using a spread spectrum technique. wb. Stego (Werner Bailer) let you hide data in bitmaps, text files and also HTML files. The data is encrypted before embedding. Two different user interfaces are proposed: ‘the wizard’ guides the user step by step and the ‘pro’ mode gives him full control.
Applications • • • Pretty Good Envelope (Robert G. Durnal), hides data in almost any file. In fact it embeds a binary message in a larger binary file by appending the message to the covert file as well as a 4 -byte pointer to the start of the message. To retrieve the message, the last 4 bytes of the file are read, the file pointer is set to that value, and the file read from that point. Publimark (Gaëtan Le Guelvouit) is a command line tool to secretly embed text in an audio file. It uses a pair of keys: the public one can be shared, whereas the private one must be kept secret. Anybody can send a teganographic message, but only the private key owner s will be able read it. Secur. Engine (Adrien Pinet) hides files into 24 bitmap images (JPEG or BMP) or even text files. Files can be encrypted using GOST, Vernam or ‘ 3 -way’. Stealth (Adam Back) is a simple filter for PGP 2. x which strips of all identifying header information. Only the encrypted data (which looks like random noise) remains; thus it is suitable for steganographic use. Snow (Matthew Knaw, University of Melbourne, Australia) is used to conceal messages in ASCII text by appending white spaces to the end of lines. Steganography Tools 4 (Andy Brown) encrypts the data with IDEA, MPJ 2, DES, 3 DES and NSEA in CBC, ECB, CFB, OFB and PCBC modes and hides it inside graphics (by modifying the LSB of BMP files), digital audio (WAV files) or unused sectors of HD floppies. The embedded message is usually very small. Steganos (Demcom, Frankfurt, Germany) is an easy to use wizard style program to hide and/or encrypt files. Steganos encrypts files and hides them within various different types of files. It also include a text editor using the soft-tempest technology. Many other security features are included. Steghide (Stefan Hetzl, Austria) features hiding data in BMP, WAV and AU files, blowfish encryption, MD 5 hashing of assphrases to p blowfish keys and pseudo-random distribution of hidden bits in the cover-data. Stegodos (Black Wolf’s Picture Encoder) is a set of DOS programs that encodes messages into GIF or PCX images. It works only with 320 x 200 x 256 pictures. The data embedded by modifying the LSB of the picture is noticeable in most cases. Stegonosaurus (John Walker, Switzerland) is a Unix program that will convert any binary file into nonsense text, but which statistically resembles text in the language of the dictionary supplied. Stegono. Wav (Peter Heist) is a Java (JDK 1. 0) program that hides information in 16 -bit wav files using a spread spectrum technique. wb. Stego (Werner Bailer) let you hide data in bitmaps, text files and also HTML files. The data is encrypted before embedding. Two different user interfaces are proposed: ‘the wizard’ guides the user step by step and the ‘pro’ mode gives him full control.
 Applications • • • EZStego (Stego Online, Stego Shareware, Romana Machado) is a Java based steganographic software which modifies the LSB of still pictures (supports only GIF and PICT formats) and rearrange the colour palette. (used to be at: http: //www. stego. com) Gif-It-Up v 1. 0 (Lee Nelson) is a stego program for Windows 95 that hides data in GIF files. It replaces colour indexes of the gif colour table with indexes of ‘colour friends’ (a colour friend is a colour in the same table and as close as possible). (used to be at: http: //www. cs. cf. ac. uk/User/L. Nelson/) Gifshuffle (Matthew Kwan) conceals a message in a GIF image by re-ordering the colour map. Source code, and a WIN 32 executable are provided. Hide and Seek (Colin Maroney) is a stego program that hide any data into GIF images. It flips the LSB of pseudorandomly chosen pixels. The data is first encrypted using the blowfish algorithm. JPEG-JSTEG (Derek Upham) hides data inside a JPEG file. (source code available) Mandel. Steg and GIFExtract (Henry Hastur) hide data in fractal GIF images. Mandel. Steg will create a Mandelbrot image (though it could be modified to produce other fractals), storing your data in the specified bit of the image pixels, after which GIFExtract can be used by the recipient to extract that bit-plane of the image. (source code available) MP 3 Stego (Fabien A. P. Petitcolas, Computer Laboratory, University of Cambridge) hides data in popular MP 3 sound files. Nicetext (Mark Chapman and George Davida, Department of EE & CS, University of Wisconsin Milwaukee) transforms cipher-text into innocuous text which can be transformed back into the original cipher-text. The expandable set of tools allows experimentation with custom dictionaries, automatic simulation of writing style, and the use of Context-Free-Grammars to control text generation. Out. Guess (Niels Provos) is a steganographic tool for still images. It support the PNM and JPEG image formats. Out. Guess ‘preserves statistics based on frequency counts. As a result, no known statistical test is able to detect the presence of steganographic content’.
Applications • • • EZStego (Stego Online, Stego Shareware, Romana Machado) is a Java based steganographic software which modifies the LSB of still pictures (supports only GIF and PICT formats) and rearrange the colour palette. (used to be at: http: //www. stego. com) Gif-It-Up v 1. 0 (Lee Nelson) is a stego program for Windows 95 that hides data in GIF files. It replaces colour indexes of the gif colour table with indexes of ‘colour friends’ (a colour friend is a colour in the same table and as close as possible). (used to be at: http: //www. cs. cf. ac. uk/User/L. Nelson/) Gifshuffle (Matthew Kwan) conceals a message in a GIF image by re-ordering the colour map. Source code, and a WIN 32 executable are provided. Hide and Seek (Colin Maroney) is a stego program that hide any data into GIF images. It flips the LSB of pseudorandomly chosen pixels. The data is first encrypted using the blowfish algorithm. JPEG-JSTEG (Derek Upham) hides data inside a JPEG file. (source code available) Mandel. Steg and GIFExtract (Henry Hastur) hide data in fractal GIF images. Mandel. Steg will create a Mandelbrot image (though it could be modified to produce other fractals), storing your data in the specified bit of the image pixels, after which GIFExtract can be used by the recipient to extract that bit-plane of the image. (source code available) MP 3 Stego (Fabien A. P. Petitcolas, Computer Laboratory, University of Cambridge) hides data in popular MP 3 sound files. Nicetext (Mark Chapman and George Davida, Department of EE & CS, University of Wisconsin Milwaukee) transforms cipher-text into innocuous text which can be transformed back into the original cipher-text. The expandable set of tools allows experimentation with custom dictionaries, automatic simulation of writing style, and the use of Context-Free-Grammars to control text generation. Out. Guess (Niels Provos) is a steganographic tool for still images. It support the PNM and JPEG image formats. Out. Guess ‘preserves statistics based on frequency counts. As a result, no known statistical test is able to detect the presence of steganographic content’.
 References • http: //www. wepin. com/pgp/stego. html • http: //www. petitcolas. net/fabien/steganogr aphy/steganographica/scholasteganographica-2. html • http: //www. securityfocus. com/infocus/1684 • http: //www. jjjtc. com/stegdoc/sec_306. html
References • http: //www. wepin. com/pgp/stego. html • http: //www. petitcolas. net/fabien/steganogr aphy/steganographica/scholasteganographica-2. html • http: //www. securityfocus. com/infocus/1684 • http: //www. jjjtc. com/stegdoc/sec_306. html



