6ec212cf2ae8f6361eef840d683b84e3.ppt
- Количество слайдов: 81
 Spheres of Influence: Secure organization and coordination of diverse device communities Kevin Eustice Ph. D. Oral Qualifying Examination UCLA Computer Science April 20 th, 2005 1
Spheres of Influence: Secure organization and coordination of diverse device communities Kevin Eustice Ph. D. Oral Qualifying Examination UCLA Computer Science April 20 th, 2005 1
 Statement of Purpose • Design and implement a device community management framework supporting ubiquitous computing scenarios. • Contributions of this work: – Generalized concept of structured device communities applied to ubiquitous computing. – Framework prototype: Spheres of Influence. – Sample applications illustrating value and generality of framework 2
Statement of Purpose • Design and implement a device community management framework supporting ubiquitous computing scenarios. • Contributions of this work: – Generalized concept of structured device communities applied to ubiquitous computing. – Framework prototype: Spheres of Influence. – Sample applications illustrating value and generality of framework 2
 Roadmap Ø Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work • Design and Implementation • Related Work • Dissertation Plan 3
Roadmap Ø Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work • Design and Implementation • Related Work • Dissertation Plan 3
 What is ubiquitous computing? ting pu m Co ible vis In Context-Aw Ta ng ibl e. C om are Compu uting omp Tran ent C spar pu ti ting ng Pervas ive Co mputin g Smart Spaces Augmen ted Rea lity 4
What is ubiquitous computing? ting pu m Co ible vis In Context-Aw Ta ng ibl e. C om are Compu uting omp Tran ent C spar pu ti ting ng Pervas ive Co mputin g Smart Spaces Augmen ted Rea lity 4
 What is ubiquitous computing? “…the third wave in computing…” —Mark Weiser “Third Paradigm computing” —Alan Kay Common elements of ubiquitous computing visions: – Large number of devices in the environment – Pervasive communications infrastructure – Interactions support human activities 5
What is ubiquitous computing? “…the third wave in computing…” —Mark Weiser “Third Paradigm computing” —Alan Kay Common elements of ubiquitous computing visions: – Large number of devices in the environment – Pervasive communications infrastructure – Interactions support human activities 5
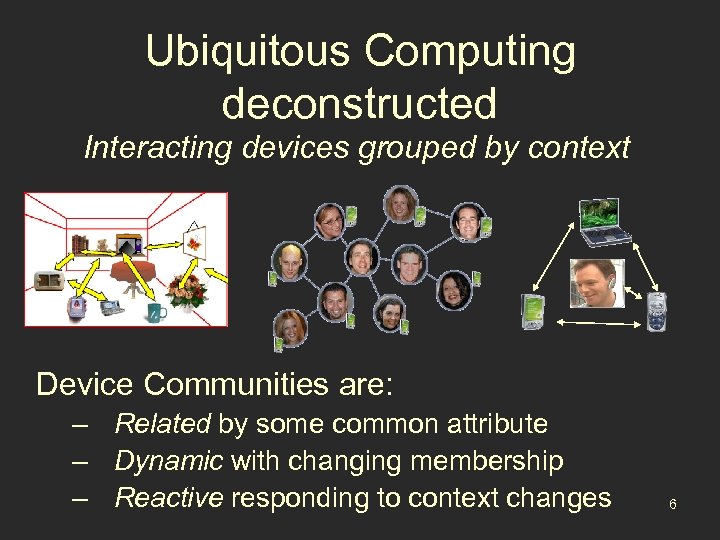 Ubiquitous Computing deconstructed Interacting devices grouped by context Device Communities are: – Related by some common attribute – Dynamic with changing membership – Reactive responding to context changes 6
Ubiquitous Computing deconstructed Interacting devices grouped by context Device Communities are: – Related by some common attribute – Dynamic with changing membership – Reactive responding to context changes 6
 Thesis Approach: • Divide world into self-managed, physically and logically grouped device communities. • Manage group transitions and interactions. • Provide common interface for group interaction. Benefits: • Simplifies high-level management through encapsulation. • Community takes on responsibility for coordinating members. 7
Thesis Approach: • Divide world into self-managed, physically and logically grouped device communities. • Manage group transitions and interactions. • Provide common interface for group interaction. Benefits: • Simplifies high-level management through encapsulation. • Community takes on responsibility for coordinating members. 7
 Applications benefiting from coordination • Mobile cluster management – At multiple levels • Policy driven applications – Ensure consistent policy across applications • Automatic proxy deployment • Multi-device applications – E. g. , multimedia applications 8
Applications benefiting from coordination • Mobile cluster management – At multiple levels • Policy driven applications – Ensure consistent policy across applications • Automatic proxy deployment • Multi-device applications – E. g. , multimedia applications 8
 Necessary Components • Membership Services – Secure Device Enrollment – Community Discovery – Relationship Management & Maintenance • Communication & Event Services – – Secure communication channels Interest management Event processing and dissemination Community-aware event semantics • Policy Engine • Application Support 9
Necessary Components • Membership Services – Secure Device Enrollment – Community Discovery – Relationship Management & Maintenance • Communication & Event Services – – Secure communication channels Interest management Event processing and dissemination Community-aware event semantics • Policy Engine • Application Support 9
 Necessary Components • Membership Services – Secure Device Enrollment – Community Discovery – Relationship Management & Maintenance • Communication & Event Services – – Secure communication channels Interest management Event processing and dissemination Community-aware event semantics • Policy Engine • Application Support 10
Necessary Components • Membership Services – Secure Device Enrollment – Community Discovery – Relationship Management & Maintenance • Communication & Event Services – – Secure communication channels Interest management Event processing and dissemination Community-aware event semantics • Policy Engine • Application Support 10
 Roadmap • Managing Ubiquitous Computing Ø Our approach: Spheres of Influence • Preliminary Work • Design and Implementation • Related Work • Dissertation Plan 11
Roadmap • Managing Ubiquitous Computing Ø Our approach: Spheres of Influence • Preliminary Work • Design and Implementation • Related Work • Dissertation Plan 11
 Approach: Spheres of Influence Sphere: a networked software container representing a device or a device community. The sphere serves as an interaction nexus for a community. 1 1. Eustice et al. "Enabling Secure Ubiquitous Interactions, " Proceedings of the First International 12 Workshop on Middleware for Pervasive and Ad-hoc Computing (MPAC 2003).
Approach: Spheres of Influence Sphere: a networked software container representing a device or a device community. The sphere serves as an interaction nexus for a community. 1 1. Eustice et al. "Enabling Secure Ubiquitous Interactions, " Proceedings of the First International 12 Workshop on Middleware for Pervasive and Ad-hoc Computing (MPAC 2003).
 Spheres of Influence are recursive Spheres can join with others to form larger, structured spheres – Coordinator of a sphere is the Sphere Leader Represents complex structures: – Locations – Organizations – Device Clusters 13
Spheres of Influence are recursive Spheres can join with others to form larger, structured spheres – Coordinator of a sphere is the Sphere Leader Represents complex structures: – Locations – Organizations – Device Clusters 13
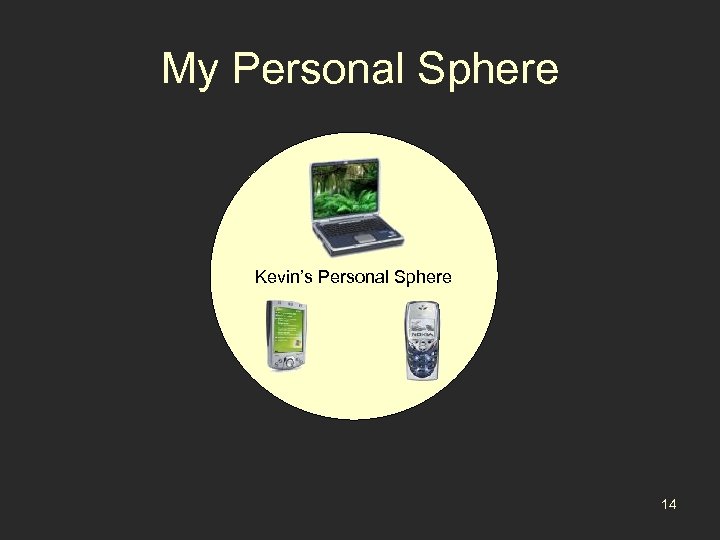 My Personal Sphere Kevin’s Personal Sphere 14
My Personal Sphere Kevin’s Personal Sphere 14
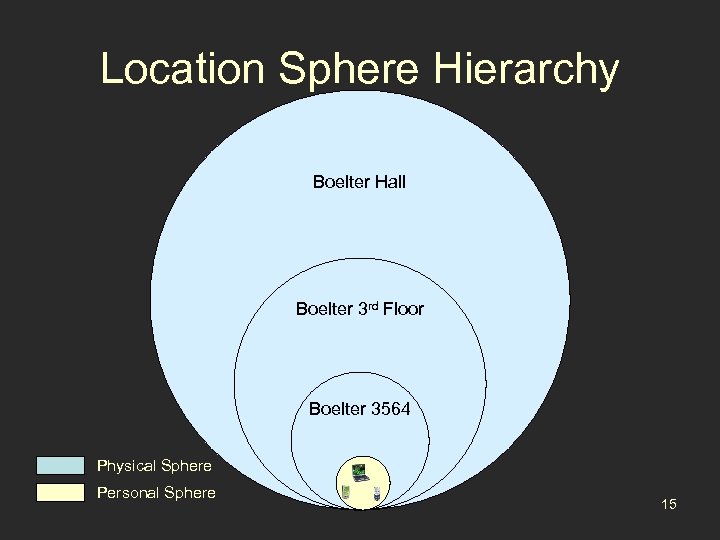 Location Sphere Hierarchy Boelter Hall Boelter 3 rd Floor Boelter 3564 Physical Sphere Personal Sphere 15
Location Sphere Hierarchy Boelter Hall Boelter 3 rd Floor Boelter 3564 Physical Sphere Personal Sphere 15
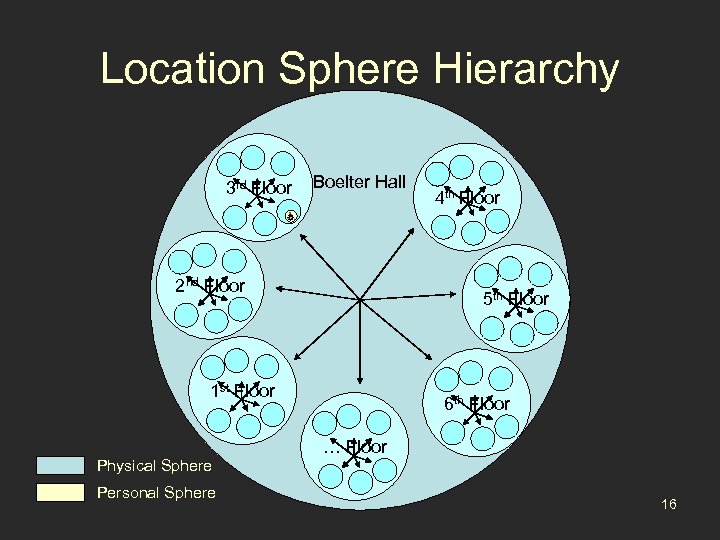 Location Sphere Hierarchy 3 rd Floor Boelter Hall 2 nd Floor 5 th Floor 1 st Floor Physical Sphere Personal Sphere 4 th Floor 6 th Floor … Floor 16
Location Sphere Hierarchy 3 rd Floor Boelter Hall 2 nd Floor 5 th Floor 1 st Floor Physical Sphere Personal Sphere 4 th Floor 6 th Floor … Floor 16
 Spheres of Influence Spheres serve as a scoping mechanism for: • Policy • Privilege • Event flow • Communication 17
Spheres of Influence Spheres serve as a scoping mechanism for: • Policy • Privilege • Event flow • Communication 17
 Spheres of Influence Operational Vision • Relationships adjust with behavior • Spheres negotiate for service • Applications leverage community context to customize user experience 18
Spheres of Influence Operational Vision • Relationships adjust with behavior • Spheres negotiate for service • Applications leverage community context to customize user experience 18
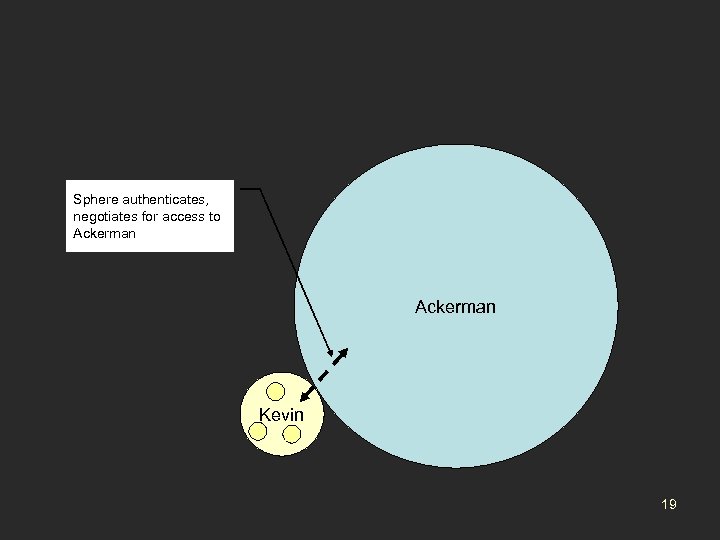 Sphere authenticates, negotiates for access to Ackerman Kevin 19
Sphere authenticates, negotiates for access to Ackerman Kevin 19
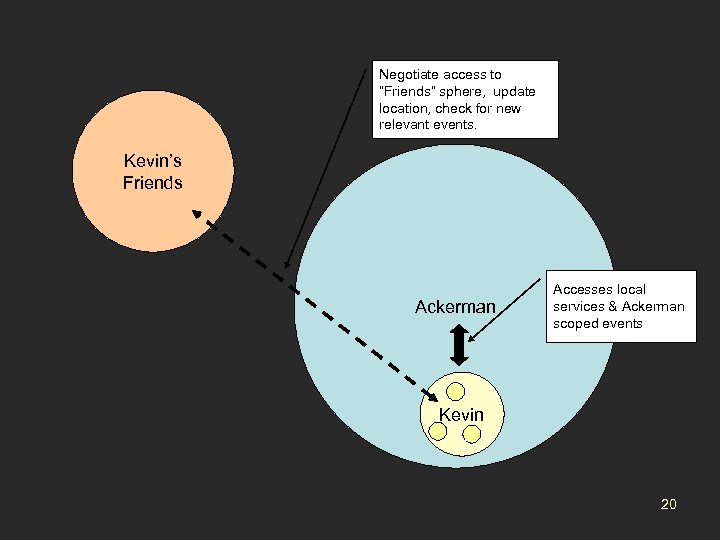 Negotiate access to “Friends” sphere, update location, check for new relevant events. Kevin’s Friends Ackerman Accesses local services & Ackerman scoped events Kevin 20
Negotiate access to “Friends” sphere, update location, check for new relevant events. Kevin’s Friends Ackerman Accesses local services & Ackerman scoped events Kevin 20
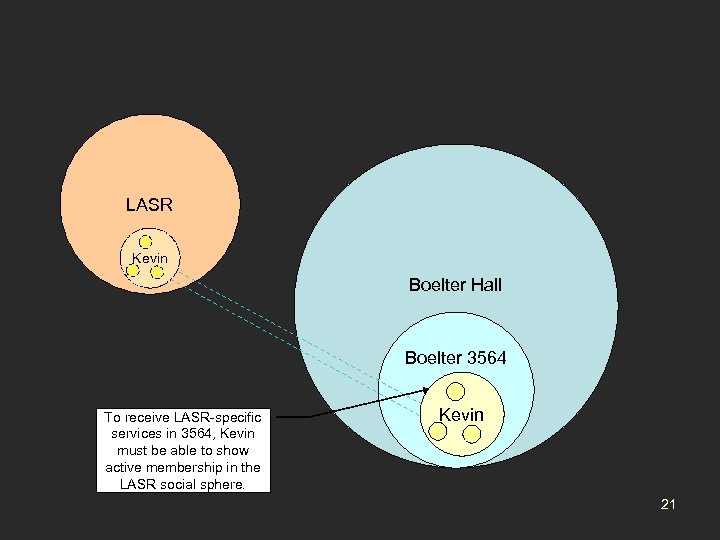 LASR Kevin Boelter Hall Ackerman Boelter 3564 To receive LASR-specific services in 3564, Kevin must be able to show active membership in the LASR social sphere. Kevin 21
LASR Kevin Boelter Hall Ackerman Boelter 3564 To receive LASR-specific services in 3564, Kevin must be able to show active membership in the LASR social sphere. Kevin 21
 Anticipated Benefits • • Community Coordination Improved Security Structured, Common Community Model Vehicle for Application Innovation 22
Anticipated Benefits • • Community Coordination Improved Security Structured, Common Community Model Vehicle for Application Innovation 22
 Community Coordination • • Group members are group-aware Preferences and policy exposed to group Group members can interact as peers Structure serves to improve scalability of communities Example: Group Mobility Optimization 23
Community Coordination • • Group members are group-aware Preferences and policy exposed to group Group members can interact as peers Structure serves to improve scalability of communities Example: Group Mobility Optimization 23
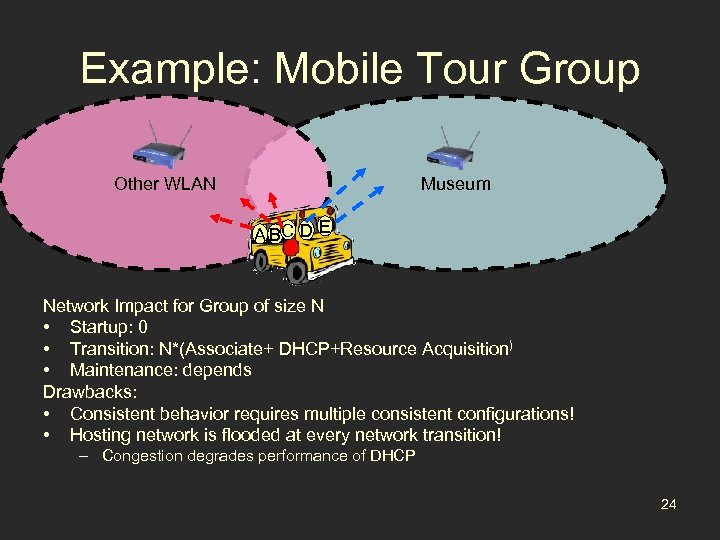 Example: Mobile Tour Group Other WLAN Museum A BC D E Network Impact for Group of size N • Startup: 0 • Transition: N*(Associate+ DHCP+Resource Acquisition) • Maintenance: depends Drawbacks: • Consistent behavior requires multiple consistent configurations! • Hosting network is flooded at every network transition! – Congestion degrades performance of DHCP 24
Example: Mobile Tour Group Other WLAN Museum A BC D E Network Impact for Group of size N • Startup: 0 • Transition: N*(Associate+ DHCP+Resource Acquisition) • Maintenance: depends Drawbacks: • Consistent behavior requires multiple consistent configurations! • Hosting network is flooded at every network transition! – Congestion degrades performance of DHCP 24
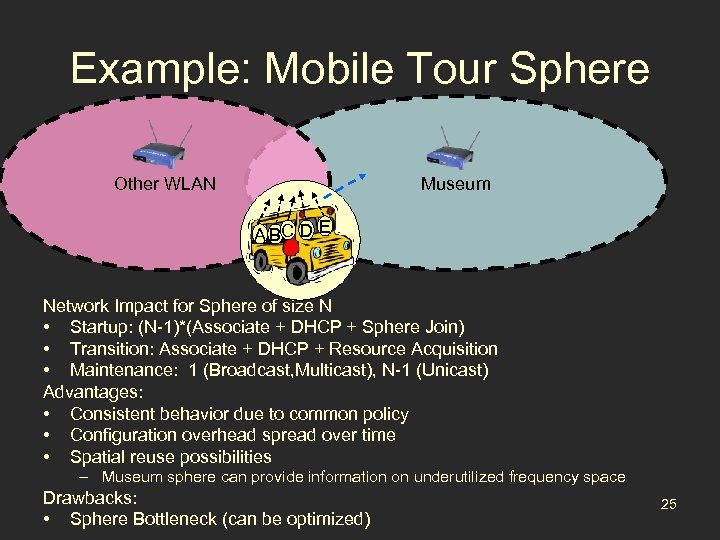 Example: Mobile Tour Sphere Other WLAN Museum A BC D E Network Impact for Sphere of size N • Startup: (N-1)*(Associate + DHCP + Sphere Join) • Transition: Associate + DHCP + Resource Acquisition • Maintenance: 1 (Broadcast, Multicast), N-1 (Unicast) Advantages: • Consistent behavior due to common policy • Configuration overhead spread over time • Spatial reuse possibilities – Museum sphere can provide information on underutilized frequency space Drawbacks: • Sphere Bottleneck (can be optimized) 25
Example: Mobile Tour Sphere Other WLAN Museum A BC D E Network Impact for Sphere of size N • Startup: (N-1)*(Associate + DHCP + Sphere Join) • Transition: Associate + DHCP + Resource Acquisition • Maintenance: 1 (Broadcast, Multicast), N-1 (Unicast) Advantages: • Consistent behavior due to common policy • Configuration overhead spread over time • Spatial reuse possibilities – Museum sphere can provide information on underutilized frequency space Drawbacks: • Sphere Bottleneck (can be optimized) 25
 Security Benefits • Security boundary – Sphere members protected from outside – Sphere join can include integrity analysis 1 • Membership services – Sphere access control – Wireless enrollment mechanisms 1. K. Eustice et al. "Securing Wi. Fi Nomads: The Case for Quarantine, Examination, and Decontamination, " Proceedings of the New Security Paradigms Workshop (NSPW) 2003. 26
Security Benefits • Security boundary – Sphere members protected from outside – Sphere join can include integrity analysis 1 • Membership services – Sphere access control – Wireless enrollment mechanisms 1. K. Eustice et al. "Securing Wi. Fi Nomads: The Case for Quarantine, Examination, and Decontamination, " Proceedings of the New Security Paradigms Workshop (NSPW) 2003. 26
 Applications Innovation • Spheres as collaboration nexus • Relationships used to customize behavior • Group as User – Semantics – Interfaces Example: Interactive Media 27
Applications Innovation • Spheres as collaboration nexus • Relationships used to customize behavior • Group as User – Semantics – Interfaces Example: Interactive Media 27
 Example: Interactive Media Multimedia application, using sphere behavior as input: • Transitions • Membership • Interactions Possible applications: • Campus-wide game • LACMA tour group application Locatio n Sphere Social Sphere 28
Example: Interactive Media Multimedia application, using sphere behavior as input: • Transitions • Membership • Interactions Possible applications: • Campus-wide game • LACMA tour group application Locatio n Sphere Social Sphere 28
 Structured Common Community Model • Multiple fidelity community membership • Shared structure scopes relevance • Simple standardized interface – Cross-community references – Diverse relations (Boelter 3564 and LASR) 29
Structured Common Community Model • Multiple fidelity community membership • Shared structure scopes relevance • Simple standardized interface – Cross-community references – Diverse relations (Boelter 3564 and LASR) 29
 Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence Ø Preliminary Work • Design and Implementation • Related Work • Dissertation Plan 30
Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence Ø Preliminary Work • Design and Implementation • Related Work • Dissertation Plan 30
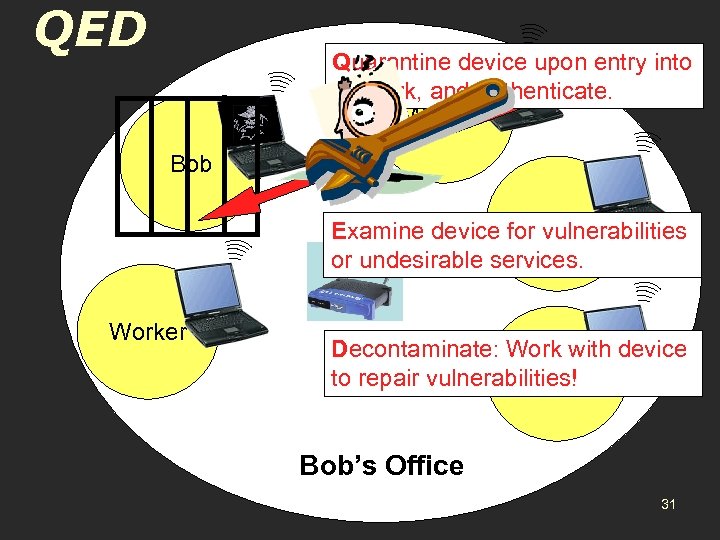 QED Quarantine device upon entry into network, and authenticate. Worker Bob Worker Examine device for vulnerabilities or undesirable services. Worker Decontaminate: Work with device Worker to repair vulnerabilities! Bob’s Office 31
QED Quarantine device upon entry into network, and authenticate. Worker Bob Worker Examine device for vulnerabilities or undesirable services. Worker Decontaminate: Work with device Worker to repair vulnerabilities! Bob’s Office 31
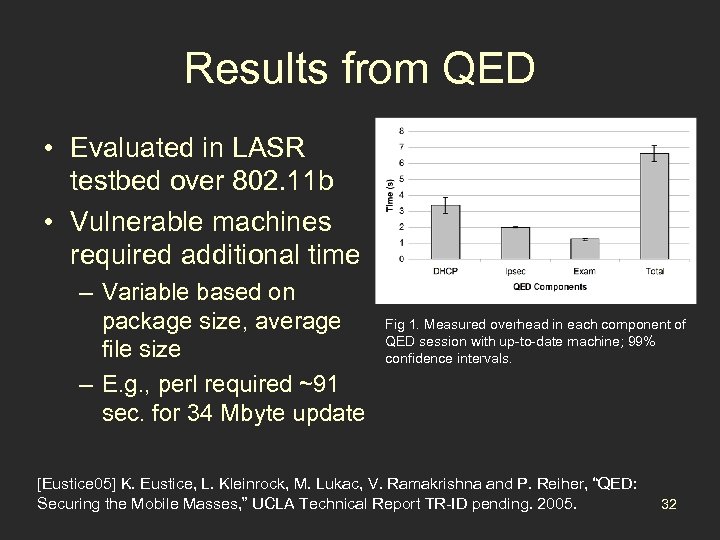 Results from QED • Evaluated in LASR testbed over 802. 11 b • Vulnerable machines required additional time – Variable based on package size, average file size – E. g. , perl required ~91 sec. for 34 Mbyte update Fig 1. Measured overhead in each component of QED session with up-to-date machine; 99% confidence intervals. [Eustice 05] K. Eustice, L. Kleinrock, M. Lukac, V. Ramakrishna and P. Reiher, “QED: Securing the Mobile Masses, ” UCLA Technical Report TR-ID pending. 2005. 32
Results from QED • Evaluated in LASR testbed over 802. 11 b • Vulnerable machines required additional time – Variable based on package size, average file size – E. g. , perl required ~91 sec. for 34 Mbyte update Fig 1. Measured overhead in each component of QED session with up-to-date machine; 99% confidence intervals. [Eustice 05] K. Eustice, L. Kleinrock, M. Lukac, V. Ramakrishna and P. Reiher, “QED: Securing the Mobile Masses, ” UCLA Technical Report TR-ID pending. 2005. 32
 Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work Ø Design and Implementation • Related Work • Dissertation Plan 33
Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work Ø Design and Implementation • Related Work • Dissertation Plan 33
 Major Systems Issues • • • Placement of Management Logic Sphere Discovery Relationship Management Fault Tolerance and Reliability Events and Event Semantics Application Primitives 34
Major Systems Issues • • • Placement of Management Logic Sphere Discovery Relationship Management Fault Tolerance and Reliability Events and Event Semantics Application Primitives 34
 Sphere Discovery • How do I find any sphere? – Broadcast & multicast – Reference-based maps • How do I find a specific sphere? – Lookup Server – DNS-based approach 35
Sphere Discovery • How do I find any sphere? – Broadcast & multicast – Reference-based maps • How do I find a specific sphere? – Lookup Server – DNS-based approach 35
 Relationship Management • Sphere Bindings – Which sphere is the right sphere for me? – Different devices will bind to different spheres • Approach • User/Application Preferences • Leverage existing relationships • Negotiation – resource/requirement matching 36
Relationship Management • Sphere Bindings – Which sphere is the right sphere for me? – Different devices will bind to different spheres • Approach • User/Application Preferences • Leverage existing relationships • Negotiation – resource/requirement matching 36
 Events and Event Semantics • Handling dynamic membership – Queuing events for inactive members – Interest registration • Event Semantics – Scoping events – Closest spheres may be most relevant – Event Ordering 37
Events and Event Semantics • Handling dynamic membership – Queuing events for inactive members – Interest registration • Event Semantics – Scoping events – Closest spheres may be most relevant – Event Ordering 37
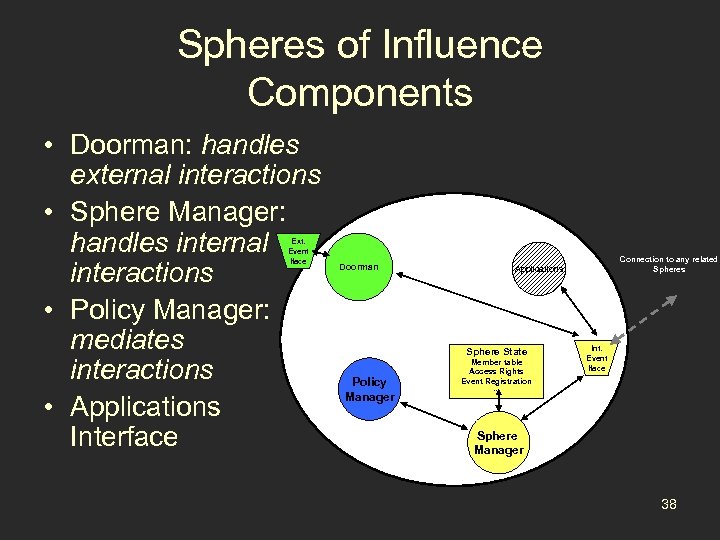 Spheres of Influence Components • Doorman: handles external interactions • Sphere Manager: handles internal interactions • Policy Manager: mediates interactions • Applications Interface Ext. Event Iface Doorman Sphere State Policy Manager Connection to any related Spheres Applications Member table Access Rights Event Registration Int. Event Iface … Sphere Manager 38
Spheres of Influence Components • Doorman: handles external interactions • Sphere Manager: handles internal interactions • Policy Manager: mediates interactions • Applications Interface Ext. Event Iface Doorman Sphere State Policy Manager Connection to any related Spheres Applications Member table Access Rights Event Registration Int. Event Iface … Sphere Manager 38
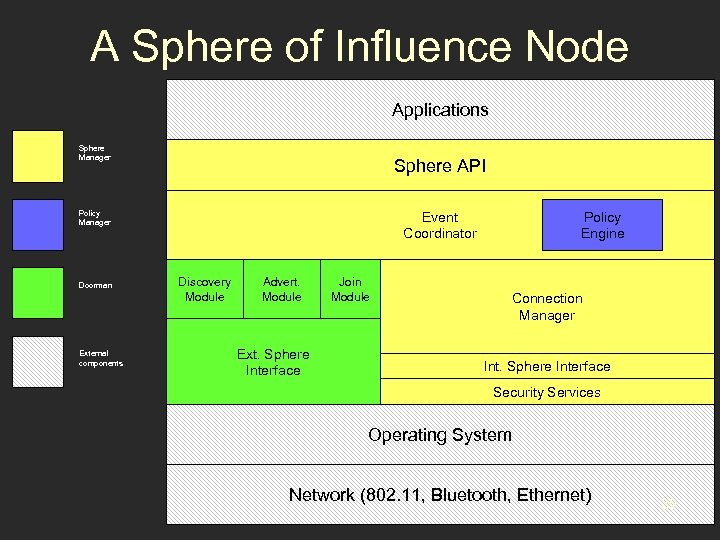 A Sphere of Influence Node Applications Sphere Manager Sphere API Policy Manager Doorman External components Event Coordinator Discovery Module Advert. Module Ext. Sphere Interface Join Module Policy Engine Connection Manager Int. Sphere Interface Security Services Operating System Network (802. 11, Bluetooth, Ethernet) 39
A Sphere of Influence Node Applications Sphere Manager Sphere API Policy Manager Doorman External components Event Coordinator Discovery Module Advert. Module Ext. Sphere Interface Join Module Policy Engine Connection Manager Int. Sphere Interface Security Services Operating System Network (802. 11, Bluetooth, Ethernet) 39
 Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work • Design and Implementation Ø Related Work • Dissertation Plan 40
Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work • Design and Implementation Ø Related Work • Dissertation Plan 40
![Related Work Social Group Applications [Wang’ 04] Spheres of Influence ? Personal Cluster Management Related Work Social Group Applications [Wang’ 04] Spheres of Influence ? Personal Cluster Management](https://present5.com/presentation/6ec212cf2ae8f6361eef840d683b84e3/image-41.jpg) Related Work Social Group Applications [Wang’ 04] Spheres of Influence ? Personal Cluster Management [Chetan’ 04] Service Groups? Others? Location-based Infrastructure [Roman’ 01, Undercoffer’ 02, Al. Muhtadi’ 04 …] 41
Related Work Social Group Applications [Wang’ 04] Spheres of Influence ? Personal Cluster Management [Chetan’ 04] Service Groups? Others? Location-based Infrastructure [Roman’ 01, Undercoffer’ 02, Al. Muhtadi’ 04 …] 41
 Related Work • Ubiquitous Computing Infrastructure – Intelligent Room/Project Oxygen, Gaia, Centaurus 2, one. world • Ubiquitous Group Management – Ephemeral Social Groups, Mobile Gaia, Super Spaces • Cluster Management – Open Cluster Framework, Mobile ad hoc clustering • Content Distribution/Pub-Sub Event Distribution – SIENA, REBECA • Secure Enrollment and Network Configuration – Resurrecting Duckling, Network-in-a-Box 42
Related Work • Ubiquitous Computing Infrastructure – Intelligent Room/Project Oxygen, Gaia, Centaurus 2, one. world • Ubiquitous Group Management – Ephemeral Social Groups, Mobile Gaia, Super Spaces • Cluster Management – Open Cluster Framework, Mobile ad hoc clustering • Content Distribution/Pub-Sub Event Distribution – SIENA, REBECA • Secure Enrollment and Network Configuration – Resurrecting Duckling, Network-in-a-Box 42
 Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work • Design and Implementation • Related Work Ø Dissertation Plan 43
Roadmap • Managing Ubiquitous Computing • Our approach: Spheres of Influence • Preliminary Work • Design and Implementation • Related Work Ø Dissertation Plan 43
 Planned Activities • • Complete Implementation Measure of Utility Evaluation Measure of Applicability 44
Planned Activities • • Complete Implementation Measure of Utility Evaluation Measure of Applicability 44
 Complete Implementation • The Spheres of Influence prototype will be completed as detailed in the prospectus. • Iterative development model for fast feedback. • Implementation will be made publicly available via Sourceforge. 45
Complete Implementation • The Spheres of Influence prototype will be completed as detailed in the prospectus. • Iterative development model for fast feedback. • Implementation will be made publicly available via Sourceforge. 45
 Measure of Utility Implementation and demonstration of two sample applications – A “coordinate and optimize” application – An application to show novelty, using community transitions and interactions as application input 46
Measure of Utility Implementation and demonstration of two sample applications – A “coordinate and optimize” application – An application to show novelty, using community transitions and interactions as application input 46
 System Evaluation • Framework Overhead • Application Performance • Methodology – Basic overhead measurements will be gathered in LASR testbed – Application results will also be gathered analyzed 47
System Evaluation • Framework Overhead • Application Performance • Methodology – Basic overhead measurements will be gathered in LASR testbed – Application results will also be gathered analyzed 47
 Measure of Applicability My assumption: devices will interact in different types of organized groups. • Provide a model to characterize ubiquitous applications in terms of group interactions. • Analysis of common applications. 48
Measure of Applicability My assumption: devices will interact in different types of organized groups. • Provide a model to characterize ubiquitous applications in terms of group interactions. • Analysis of common applications. 48
![Examples • Community Geo-annotation – mapping of social sphere[s] onto location spheres • Friend-finder Examples • Community Geo-annotation – mapping of social sphere[s] onto location spheres • Friend-finder](https://present5.com/presentation/6ec212cf2ae8f6361eef840d683b84e3/image-49.jpg) Examples • Community Geo-annotation – mapping of social sphere[s] onto location spheres • Friend-finder – mapping of location sphere[s] onto social spheres • Access-control applications – mapping of social spheres onto physical spheres • Location-aware Wireless Device Configuration – mapping of physical spheres from location sphere onto elemental device spheres 49
Examples • Community Geo-annotation – mapping of social sphere[s] onto location spheres • Friend-finder – mapping of location sphere[s] onto social spheres • Access-control applications – mapping of social spheres onto physical spheres • Location-aware Wireless Device Configuration – mapping of physical spheres from location sphere onto elemental device spheres 49
 Implementation Status Completed: – Communications framework – Sphere join protocol – Event registration and processing – Network configuration modules – Reference map-based discovery 50
Implementation Status Completed: – Communications framework – Sphere join protocol – Event registration and processing – Network configuration modules – Reference map-based discovery 50
 Statement of Purpose • Design and implement a device community management framework supporting ubiquitous computing scenarios. • Contributions of this work: – Generalized concept of structured device communities applied to ubiquitous computing. – Framework prototype: Spheres of Influence. – Sample applications illustrating value and generality of framework 51
Statement of Purpose • Design and implement a device community management framework supporting ubiquitous computing scenarios. • Contributions of this work: – Generalized concept of structured device communities applied to ubiquitous computing. – Framework prototype: Spheres of Influence. – Sample applications illustrating value and generality of framework 51
 Spheres of Influence: Secure organization and coordination of diverse device communities Kevin Eustice April 20 th, 2005 52
Spheres of Influence: Secure organization and coordination of diverse device communities Kevin Eustice April 20 th, 2005 52
 Extra Slides 53
Extra Slides 53
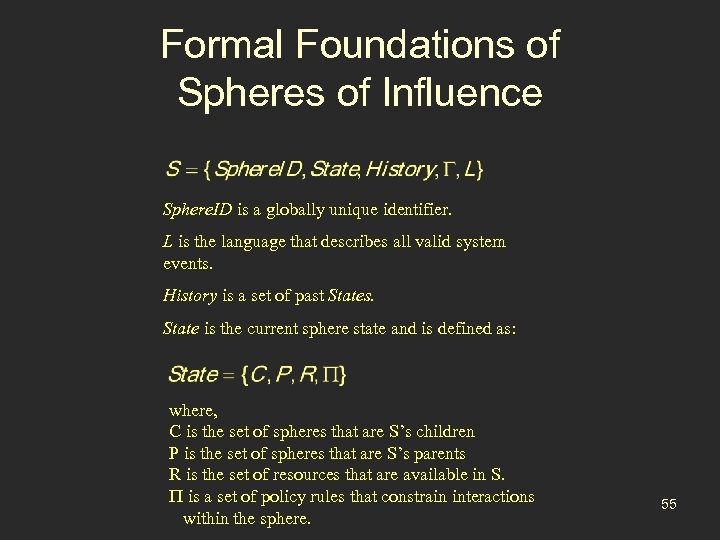 Formal Foundations of Spheres of Influence Sphere. ID is a globally unique identifier. L is the language that describes all valid system events. History is a set of past States. State is the current sphere state and is defined as: where, C is the set of spheres that are S’s children P is the set of spheres that are S’s parents R is the set of resources that are available in S. P is a set of policy rules that constrain interactions within the sphere. 55
Formal Foundations of Spheres of Influence Sphere. ID is a globally unique identifier. L is the language that describes all valid system events. History is a set of past States. State is the current sphere state and is defined as: where, C is the set of spheres that are S’s children P is the set of spheres that are S’s parents R is the set of resources that are available in S. P is a set of policy rules that constrain interactions within the sphere. 55
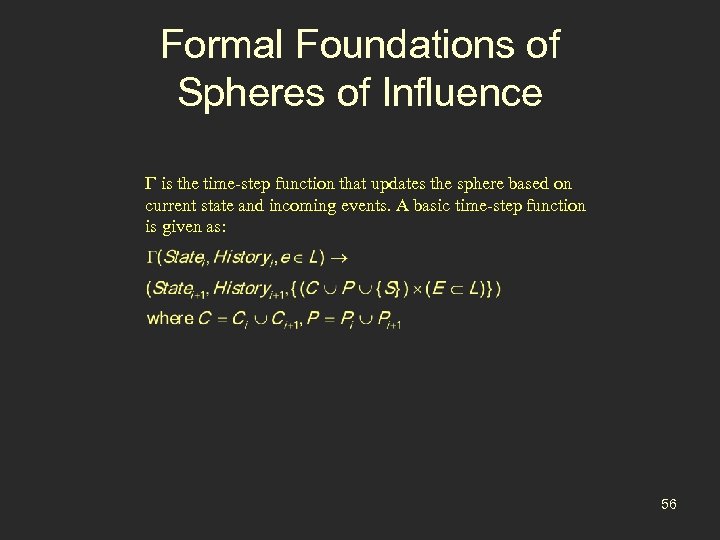 Formal Foundations of Spheres of Influence is the time-step function that updates the sphere based on current state and incoming events. A basic time-step function is given as: 56
Formal Foundations of Spheres of Influence is the time-step function that updates the sphere based on current state and incoming events. A basic time-step function is given as: 56
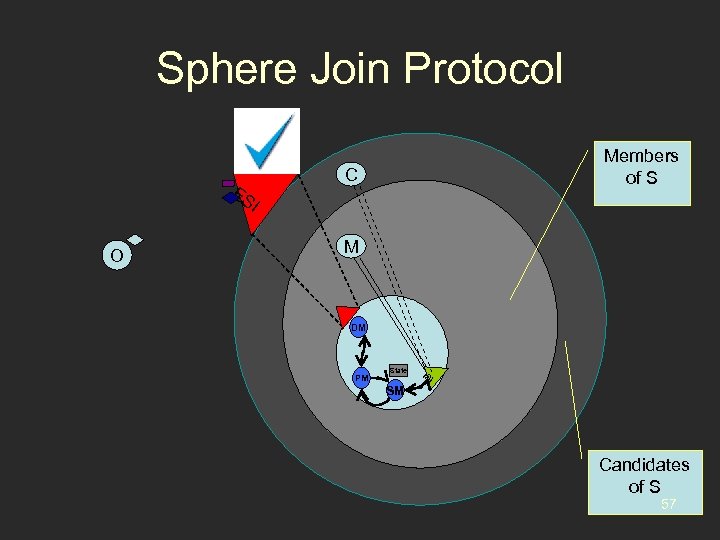 Sphere Join Protocol Members of S ES C I O M DM PM State SM IS I Candidates of S 57
Sphere Join Protocol Members of S ES C I O M DM PM State SM IS I Candidates of S 57
 Group Coordination through Sphere Events • Interest-based Event Management • Sphere structure scopes event flow – Event processing influenced by current connections – Different possible semantics • Policy regulates interactions 58
Group Coordination through Sphere Events • Interest-based Event Management • Sphere structure scopes event flow – Event processing influenced by current connections – Different possible semantics • Policy regulates interactions 58
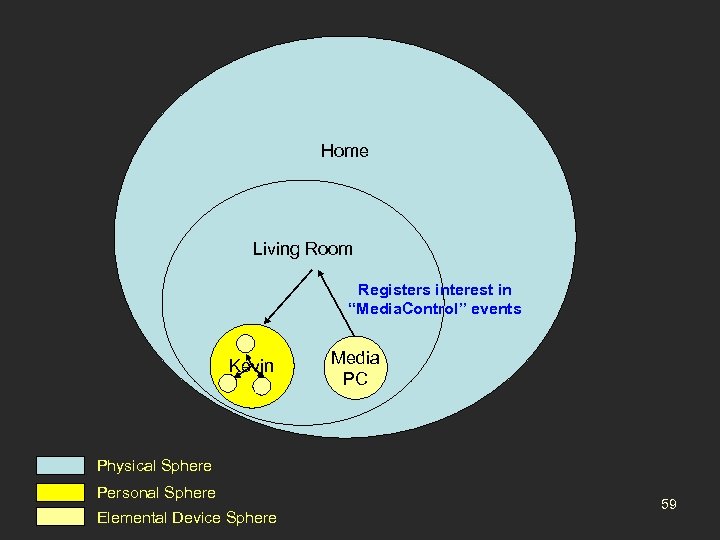 Home Living Room Registers interest in “Media. Control” events Kevin Media PC Physical Sphere Personal Sphere Elemental Device Sphere 59
Home Living Room Registers interest in “Media. Control” events Kevin Media PC Physical Sphere Personal Sphere Elemental Device Sphere 59
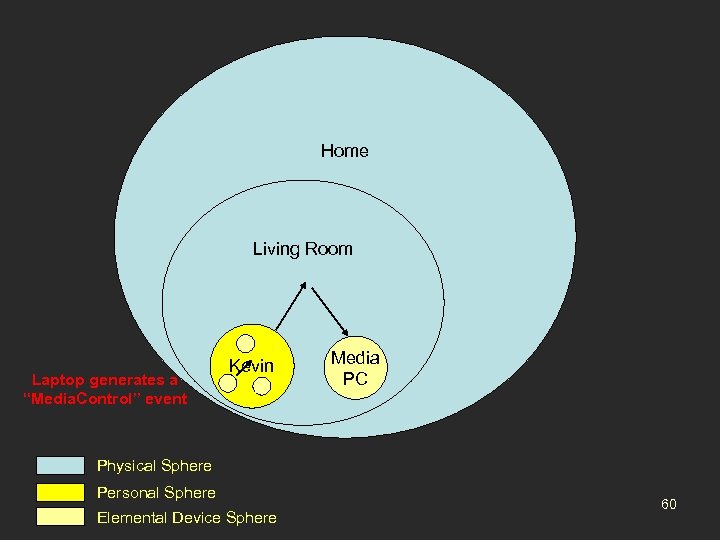 Home Living Room Laptop generates a “Media. Control” event Kevin Media PC Physical Sphere Personal Sphere Elemental Device Sphere 60
Home Living Room Laptop generates a “Media. Control” event Kevin Media PC Physical Sphere Personal Sphere Elemental Device Sphere 60
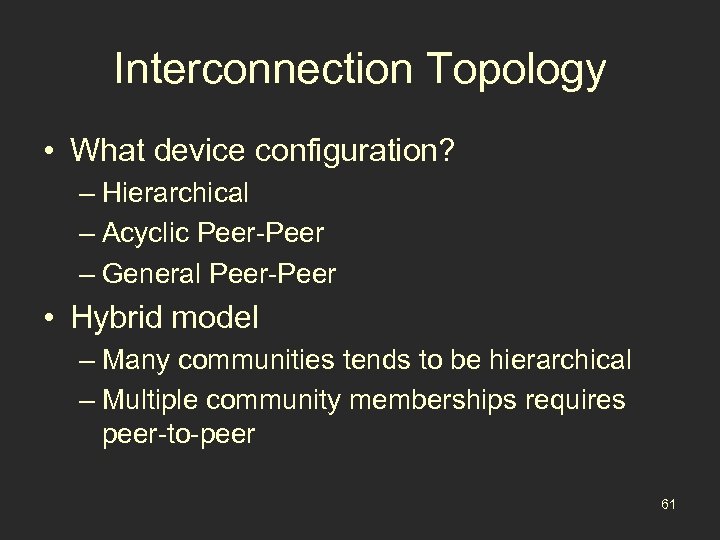 Interconnection Topology • What device configuration? – Hierarchical – Acyclic Peer-Peer – General Peer-Peer • Hybrid model – Many communities tends to be hierarchical – Multiple community memberships requires peer-to-peer 61
Interconnection Topology • What device configuration? – Hierarchical – Acyclic Peer-Peer – General Peer-Peer • Hybrid model – Many communities tends to be hierarchical – Multiple community memberships requires peer-to-peer 61
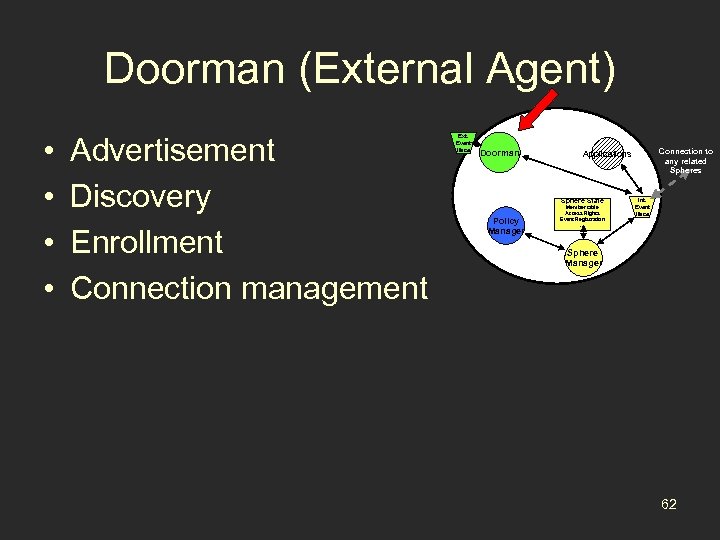 Doorman (External Agent) • • Advertisement Discovery Enrollment Connection management Ext. Event Iface Doorman Sphere State Policy Manager Connection to any related Spheres Applications Member table Access Rights Event Registration … Int. Event Iface Sphere Manager 62
Doorman (External Agent) • • Advertisement Discovery Enrollment Connection management Ext. Event Iface Doorman Sphere State Policy Manager Connection to any related Spheres Applications Member table Access Rights Event Registration … Int. Event Iface Sphere Manager 62
 Discovery/Advertisement Modes • Broadcast & Multicast – Most feasible for physical spheres – Technical issues regarding visibility of advertisements • Lookup Server – DNS-based approach – Most appropriate for abstract spheres • Static mappings – Most appropriate for locations – Staleness and Size – Dissemination modes? 63
Discovery/Advertisement Modes • Broadcast & Multicast – Most feasible for physical spheres – Technical issues regarding visibility of advertisements • Lookup Server – DNS-based approach – Most appropriate for abstract spheres • Static mappings – Most appropriate for locations – Staleness and Size – Dissemination modes? 63
 Planned Enrollment Techniques • USB/RFID location-limited sideband (Balfanz et al. ) – OOB exchange of hashed public keys – Tie identity to locality • Network Vouchers 64
Planned Enrollment Techniques • USB/RFID location-limited sideband (Balfanz et al. ) – OOB exchange of hashed public keys – Tie identity to locality • Network Vouchers 64
 Connection Manager • Initiates Sphere Joins • Handles incoming supplicants – Eligible supplicants handed to Sphere Manager – Else, reject connection • Eligibility is determined by policy manager 65
Connection Manager • Initiates Sphere Joins • Handles incoming supplicants – Eligible supplicants handed to Sphere Manager – Else, reject connection • Eligibility is determined by policy manager 65
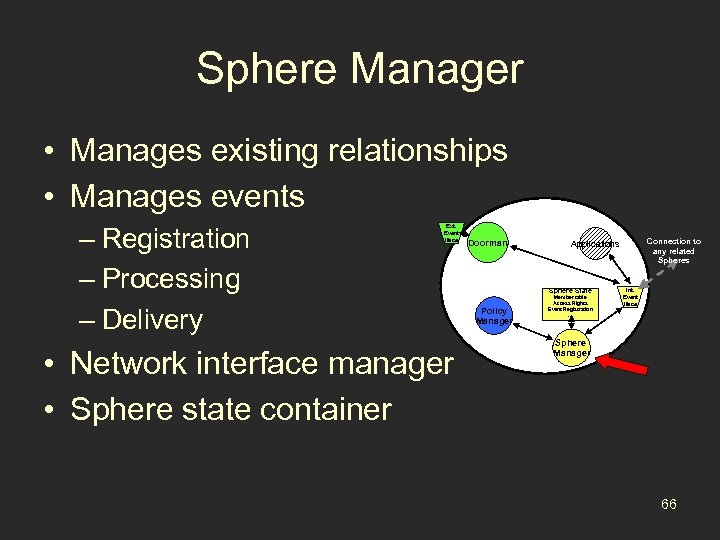 Sphere Manager • Manages existing relationships • Manages events – Registration – Processing – Delivery Ext. Event Iface • Network interface manager • Sphere state container Doorman Sphere State Policy Manager Connection to any related Spheres Applications Member table Access Rights Event Registration … Int. Event Iface Sphere Manager 66
Sphere Manager • Manages existing relationships • Manages events – Registration – Processing – Delivery Ext. Event Iface • Network interface manager • Sphere state container Doorman Sphere State Policy Manager Connection to any related Spheres Applications Member table Access Rights Event Registration … Int. Event Iface Sphere Manager 66
 Policy Manager • Policy Manager: – Policy database contains local policy rules – Policy engine answers questions regarding state changing interactions and local policy • Policy Language – Describes valid interactions in terms of relational, deontic, and temporal constraints – Logic-based • Policy resolution, conflict handling • Focus of V. Ramakrishna’s Dissertation 67
Policy Manager • Policy Manager: – Policy database contains local policy rules – Policy engine answers questions regarding state changing interactions and local policy • Policy Language – Describes valid interactions in terms of relational, deontic, and temporal constraints – Logic-based • Policy resolution, conflict handling • Focus of V. Ramakrishna’s Dissertation 67
 Applications Interface • Access local sphere via loopback interface • Device sphere maintains a per-application channel to allow event dissemination – Send/Receive Events – Query Sphere Status 68
Applications Interface • Access local sphere via loopback interface • Device sphere maintains a per-application channel to allow event dissemination – Send/Receive Events – Query Sphere Status 68
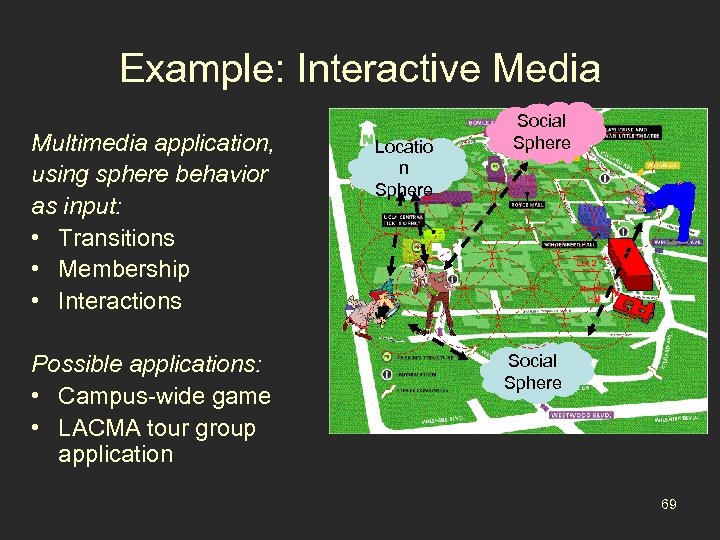 Example: Interactive Media Multimedia application, using sphere behavior as input: • Transitions • Membership • Interactions Possible applications: • Campus-wide game • LACMA tour group application Locatio n Sphere Social Sphere 69
Example: Interactive Media Multimedia application, using sphere behavior as input: • Transitions • Membership • Interactions Possible applications: • Campus-wide game • LACMA tour group application Locatio n Sphere Social Sphere 69
 Measure of Success • Effectiveness – Construct examples similar to those presented here • Low Overhead – Measure added complexity of sphere abstraction as a function of sphere size – Measure time-to-join compared to legacy network modes – Measure generation and evaluation time of relationship attestations. 70
Measure of Success • Effectiveness – Construct examples similar to those presented here • Low Overhead – Measure added complexity of sphere abstraction as a function of sphere size – Measure time-to-join compared to legacy network modes – Measure generation and evaluation time of relationship attestations. 70
 Measure of Success • Complete Implementation – Dynamic demo: automatically manage device community interactions in face of changing external context, cope with failure • Usability – Daily use by laboratory inhabitants • Task Management – LACMA application – UCLA Campus-based Multimedia Application 71
Measure of Success • Complete Implementation – Dynamic demo: automatically manage device community interactions in face of changing external context, cope with failure • Usability – Daily use by laboratory inhabitants • Task Management – LACMA application – UCLA Campus-based Multimedia Application 71
 Contributions • Model for a consistent representation of device membership spanning heterogeneous communities • Secure, active management of community memberships • Secure, cryptographic membership attestation • Intra- and Inter-community event registration and delivery • Evaluation of model with applications 72
Contributions • Model for a consistent representation of device membership spanning heterogeneous communities • Secure, active management of community memberships • Secure, cryptographic membership attestation • Intra- and Inter-community event registration and delivery • Evaluation of model with applications 72
 Placement of Management Logic • Where is sphere management located? – Centralized – Distributed – Partially Distributed • Security tradeoff – Centralized leadership simpler to secure – Distribute components based on trust 73
Placement of Management Logic • Where is sphere management located? – Centralized – Distributed – Partially Distributed • Security tradeoff – Centralized leadership simpler to secure – Distribute components based on trust 73
 Fault Tolerance and Reliability • Determining failure – Did the sphere fail or did I change contexts? – Analyze external state and see what’s changed • Approaches – Distribute management based on trust – Failover based on trust – Rediscover, rebind to sphere and coalesce 74
Fault Tolerance and Reliability • Determining failure – Did the sphere fail or did I change contexts? – Analyze external state and see what’s changed • Approaches – Distribute management based on trust – Failover based on trust – Rediscover, rebind to sphere and coalesce 74
 Application Primitives • Access to Relational Data – Membership information – Peer information – Request & verify attestations • Coordination Primitives – Gossiping – Consensus Gathering – Transaction Management 75
Application Primitives • Access to Relational Data – Membership information – Peer information – Request & verify attestations • Coordination Primitives – Gossiping – Consensus Gathering – Transaction Management 75
 Previous Work QED: mobile integrity management – Quarantine incoming mobile devices – Examine them for vulnerabilities – Decontaminate them, with repairs/updates • Deployed in LASR to secure laptops – RPM package examination – Package update as needed via secure tunnel • Measured overhead in QED phases 76
Previous Work QED: mobile integrity management – Quarantine incoming mobile devices – Examine them for vulnerabilities – Decontaminate them, with repairs/updates • Deployed in LASR to secure laptops – RPM package examination – Package update as needed via secure tunnel • Measured overhead in QED phases 76
![Related Work Structured Social Groups Structured Location Groups Gaia [Roman’ 02] Users Only Single Related Work Structured Social Groups Structured Location Groups Gaia [Roman’ 02] Users Only Single](https://present5.com/presentation/6ec212cf2ae8f6361eef840d683b84e3/image-76.jpg) Related Work Structured Social Groups Structured Location Groups Gaia [Roman’ 02] Users Only Single Location Registry Centaurus 2 [Undercoffer’ 03] Users Only X X Super Spaces [Al. Muhtadi’ 04] Users Only X Distributed Registry Mobile Gaia [Chetan’ 04] Ephemeral Social Spheres [Wang’ 04] Structured Service Groups Registry X Structured Comm. Groups Personal Device Cluster X 77
Related Work Structured Social Groups Structured Location Groups Gaia [Roman’ 02] Users Only Single Location Registry Centaurus 2 [Undercoffer’ 03] Users Only X X Super Spaces [Al. Muhtadi’ 04] Users Only X Distributed Registry Mobile Gaia [Chetan’ 04] Ephemeral Social Spheres [Wang’ 04] Structured Service Groups Registry X Structured Comm. Groups Personal Device Cluster X 77
 Other Approaches • Infrastructure projects (Gaia, Centaurus, AIRE/Project Oxygen) – Typical focus is centralized management of services within a physical space – Database, CORBA ORB, or local registry – Single administrative domain – Limited bootstrapping support 78
Other Approaches • Infrastructure projects (Gaia, Centaurus, AIRE/Project Oxygen) – Typical focus is centralized management of services within a physical space – Database, CORBA ORB, or local registry – Single administrative domain – Limited bootstrapping support 78
![Other Approaches • Gaia Super. Spaces [Al-Muhtadi’ 04] – Meta structure applied recursively to Other Approaches • Gaia Super. Spaces [Al-Muhtadi’ 04] – Meta structure applied recursively to](https://present5.com/presentation/6ec212cf2ae8f6361eef840d683b84e3/image-78.jpg) Other Approaches • Gaia Super. Spaces [Al-Muhtadi’ 04] – Meta structure applied recursively to multiple Gaia spaces • Mobile Gaia [Chetan’ 04] – Personal device cluster management • Ephemeral Social Groups [Wang’ 04] • Major Differences: – Multiple administrative domains. – Common representation model of different groups. 79
Other Approaches • Gaia Super. Spaces [Al-Muhtadi’ 04] – Meta structure applied recursively to multiple Gaia spaces • Mobile Gaia [Chetan’ 04] – Personal device cluster management • Ephemeral Social Groups [Wang’ 04] • Major Differences: – Multiple administrative domains. – Common representation model of different groups. 79
![Related Work • Cluster formation work [OCF] – Mobile ad hoc clustering protocols [many] Related Work • Cluster formation work [OCF] – Mobile ad hoc clustering protocols [many]](https://present5.com/presentation/6ec212cf2ae8f6361eef840d683b84e3/image-79.jpg) Related Work • Cluster formation work [OCF] – Mobile ad hoc clustering protocols [many] • Content distribution/pub-sub systems – SIENA [Carzaniga et al. ‘ 01] – REBECA [Műhl ‘ 02] 80
Related Work • Cluster formation work [OCF] – Mobile ad hoc clustering protocols [many] • Content distribution/pub-sub systems – SIENA [Carzaniga et al. ‘ 01] – REBECA [Műhl ‘ 02] 80
 Examples of emerging communities • Personal Device Communities Set of devices with a common owner • Location-based Device Communities Devices related by proximity • Social Device Communities Devices connected by user organization • And others (Interest, Task, Function, …. ) 81
Examples of emerging communities • Personal Device Communities Set of devices with a common owner • Location-based Device Communities Devices related by proximity • Social Device Communities Devices connected by user organization • And others (Interest, Task, Function, …. ) 81
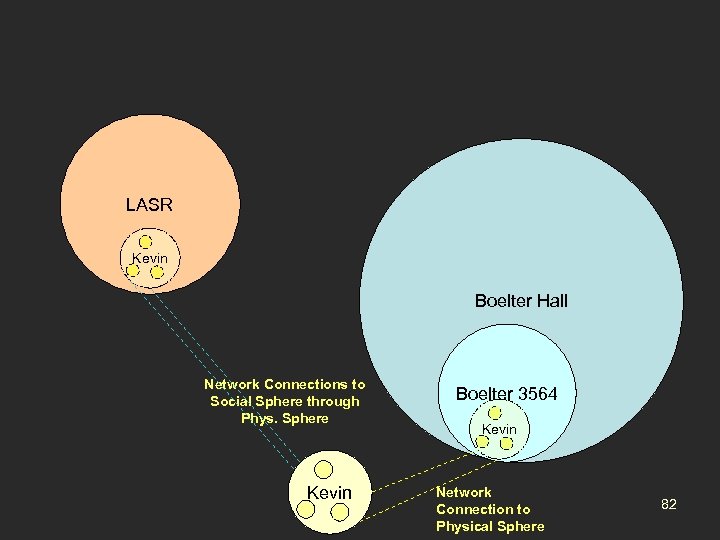 LASR Kevin Boelter Hall Network Connections to Social Sphere through Phys. Sphere Kevin Boelter 3564 Kevin Network Connection to Physical Sphere 82
LASR Kevin Boelter Hall Network Connections to Social Sphere through Phys. Sphere Kevin Boelter 3564 Kevin Network Connection to Physical Sphere 82


