6efb32450df2e3e263c0fe19ed731044.ppt
- Количество слайдов: 27

SOFTWARE ARCHITECTURE FOR CYBERMINER GLOBAL 14

Agenda a. Problem, Process and Solution b. Phase-wise Discussion a. Requirements Analysis b. Architecture c. Quality Assurance d. Implementation c. Demonstration d. Traceability e. Why Choose Us? f. Conclusion
Problem Description (summary) a. To architect a web search engine, Cyberminer, using the simple KWIC software system which you implemented as part of Project I b. use an Object-Oriented architectural style c. build a Java applet

Problem Description (requirements) Functional Requirements a. . shall accept a list of keywords and return a list of URLs whose descriptions contain any of the given keywords • . . . shall use. . . the KWIC system, as a component • . . . shall allow for two modes of operation: i) for building an initial KWIC indices; and ii) for growing the indices with later additions
Feature Requests a. Case sensitive search, b. Hyperlink enforcement, c. OR/AND/NOT Search, d. Multiple search engines, e. Deletion of out-of-date URL, f. Listing of query result in ascending alphabetical order; g. Setting the number of results to show per page, h. navigation between pages; i. and also possibly Autofill.
NFRS (The usual suspects). . . shall be a. easily understandable, • portable, • enhanceable • reusable • with good performance. • user-friendly, • responsive, • adaptable. • run with recent versions of popular web browsers

Development Process (Software)

Development Process (Team)

Requirements Analysis (FR Issue) OFR 2 Issue 1: The mode of interaction btw KWIC & Cyberminer? Option 1: Cyberminer will access the database provided by KWIC. Option 2: Cyberminer will implement the complete functionality of the KWIC system as a subset of Cyberminer’s functionality. Option 3: Cyberminer will take input from the user and send this behind the scenes to the KWIC system. The KWIC system will use this to search it’s database and return the search results back to Cyberminer which will then display them to the user. Choice/Rationale: Option 3
Requirments Analysis (NFR Issues) ONR 8 Issue 1: Popularity of web browsers? Option 1: month-by-month popularity rankings of the W 3 Consortium found at http: //www. w 3 schools. com/browsers_stats. asp Option 2: Wikipedia has a month-by-month rankings http: //en. wikipedia. org/wiki/Usage_share_of_web_browsers Option 3: A poll by http: //www. webdevelopersnotes. com/articles/popular-webbrowsers. php seems to suggest that the numbers cited in Options 1 and 2 do not necessarily reflexive of users’ preferences. Choice/Rationale: Option 2
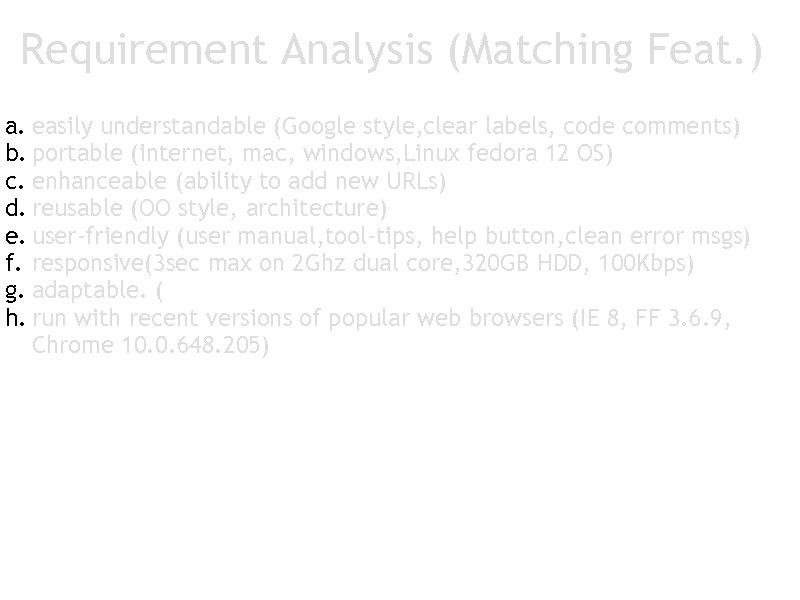
Requirement Analysis (Matching Feat. ) a. easily understandable (Google style, clear labels, code comments) b. portable (internet, mac, windows, Linux fedora 12 OS) c. enhanceable (ability to add new URLs) d. reusable (OO style, architecture) e. user-friendly (user manual, tool-tips, help button, clean error msgs) f. responsive(3 sec max on 2 Ghz dual core, 320 GB HDD, 100 Kbps) g. adaptable. (run in non-Internet environments e. g. intranets, single PC) h. run with recent versions of popular web browsers (IE 8, FF 3. 6. 9, Chrome 10. 0. 648. 205)
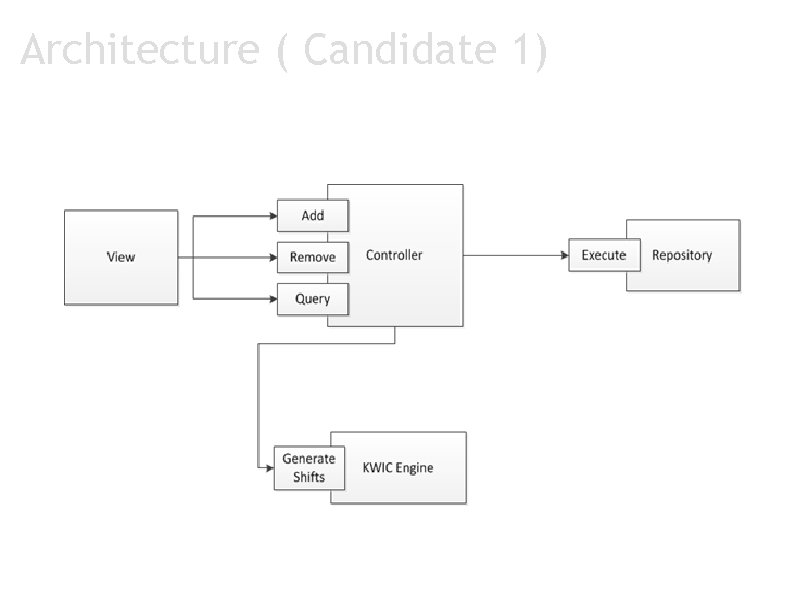
Architecture ( Candidate 1)
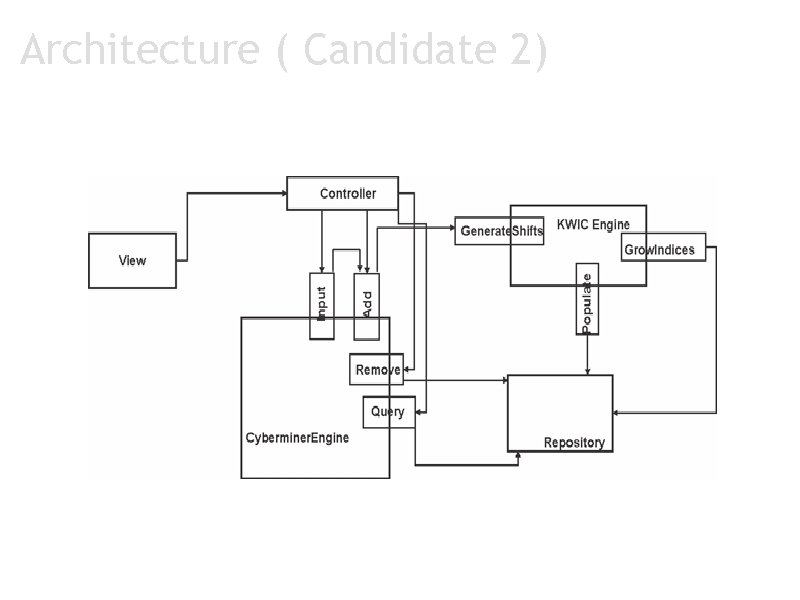
Architecture ( Candidate 2)
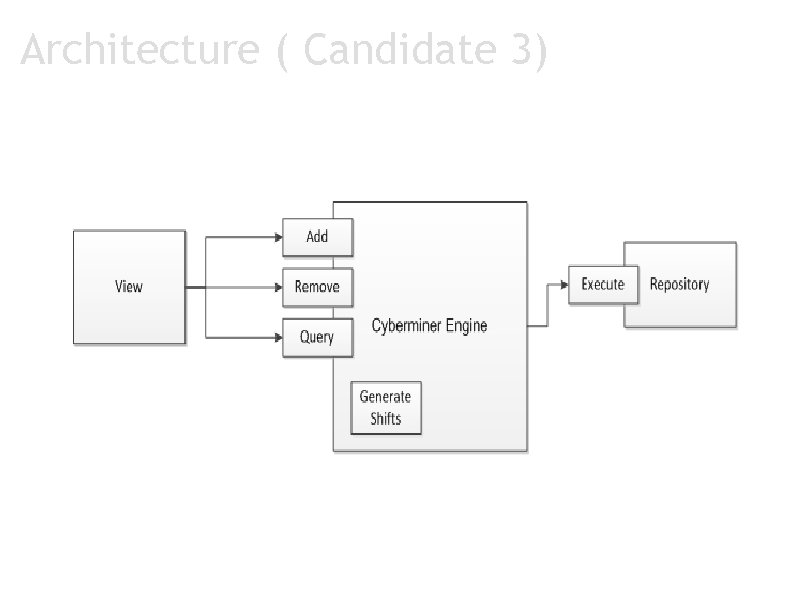
Architecture ( Candidate 3)
Architecture (Final Decision & Rationale) a. Selected Candidate 1 a. Candidate 3 too weak in enhanceability and reusability • Candidate 1 slightly outperforms Candidate 2 with respect to enhanceability Candidate 1: 92% Candidate 2: 83% Candidate 3: 33%
Architecture (Rationale)
Quality Assurance (Test Plan & Test Cases) a. Generated with requirement specification b. Example : • Traceability between test cases and requirement issues
Quality Assurance (User Scenarios) a. Add URL a. Add multiple URLs (one at a time) b. Add multiple Descriptors (one at a time) b. Remove URL a. Remove multiple URLs (one at a time) c. Searching a. Use keywords b. Use AND/OR/NOT searching d. Browse Search Results a. Visit available websites b. Increase viewable results c. View next/previous results pages
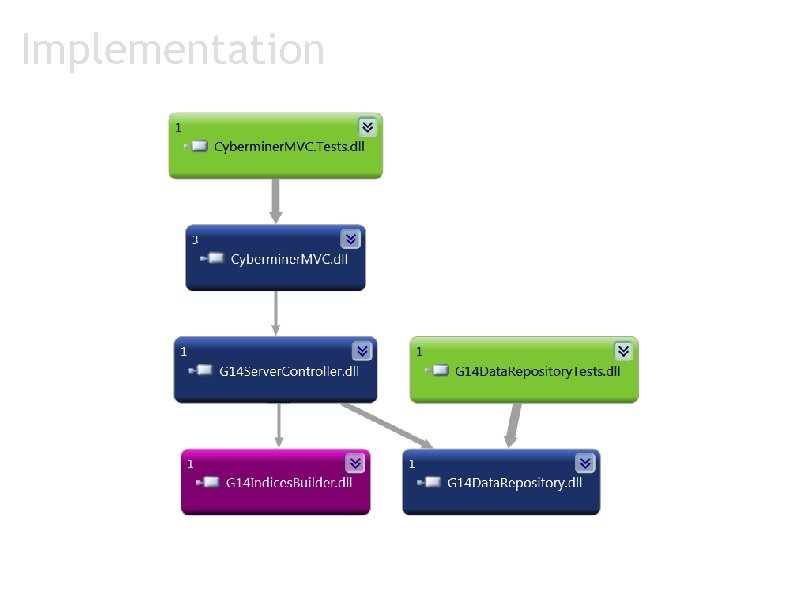
Implementation
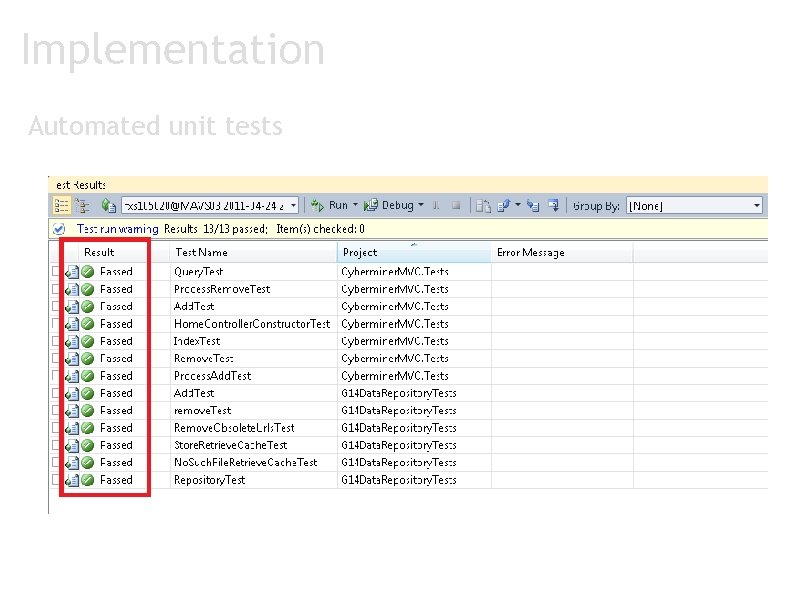
Implementation Automated unit tests
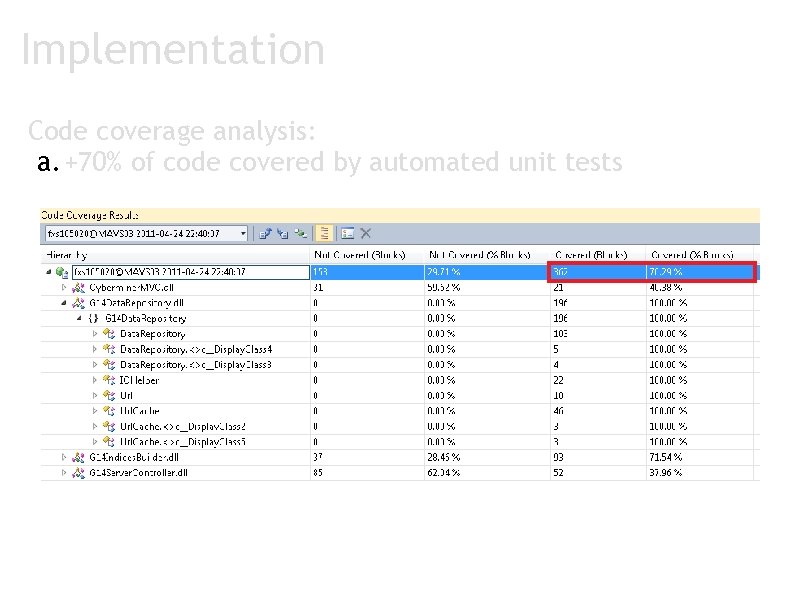
Implementation Code coverage analysis: a. +70% of code covered by automated unit tests

Demonstration Cyber. Miner http: //hypv 3355. appliedi. net/G 14 Cyberminer
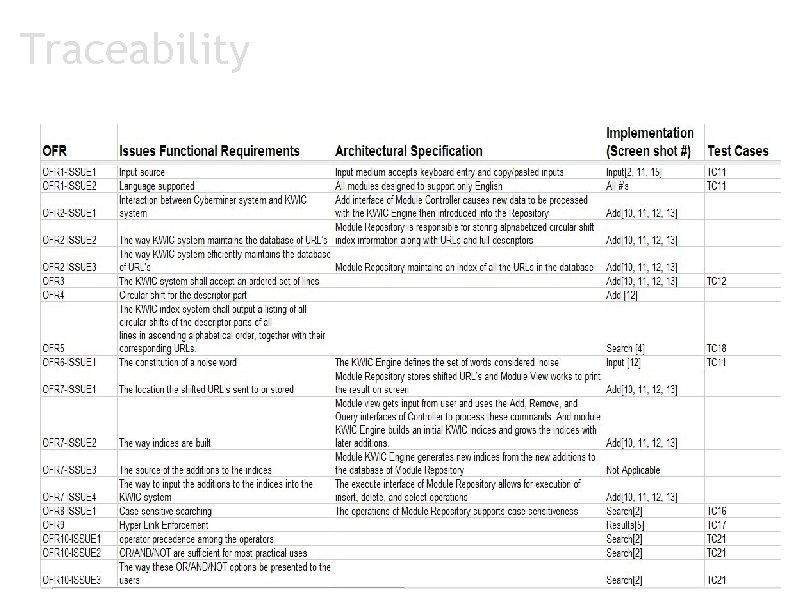
Traceability
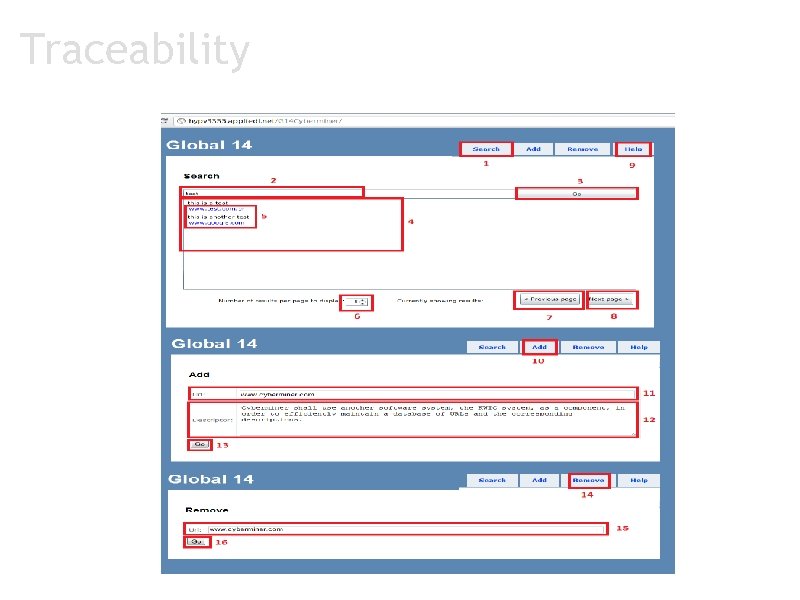
Traceability
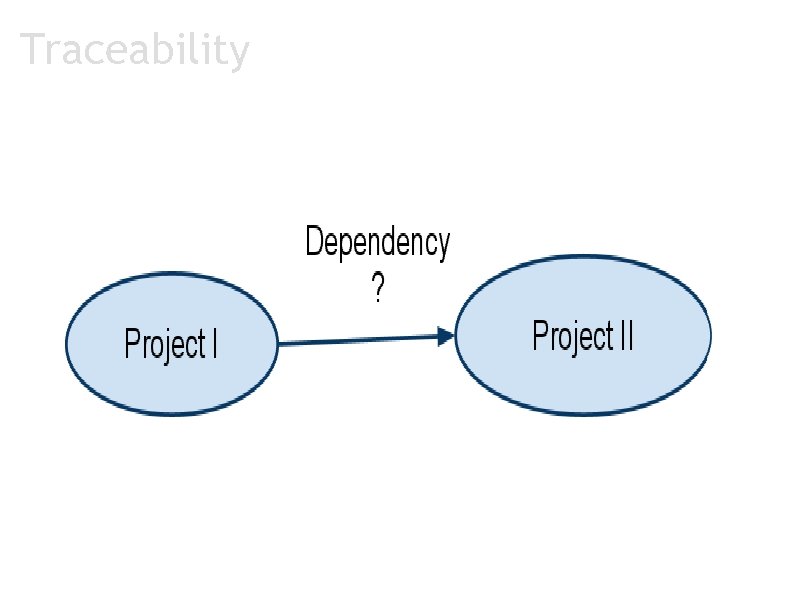
Traceability
Why Choose Us? a. Multiple candidate architectures considered for selection b. Automated unit testing and code coverage analysis c. Extensive work on traceability a. project Phase I to Phase II b. requirements to architecture c. architecture to implementation d. test plan to requirements and implementation d. KWIC architecture made Cyberminer development less difficult e. Team size, organization and expertise
Questions? Thank you
6efb32450df2e3e263c0fe19ed731044.ppt