4dbd62a4a0ac9bd3b4770234ffbf01e1.ppt
- Количество слайдов: 17
“So You Want To Take Your Business Electronic” -- The Sequel Implementing electronic records and signatures across a corporate platform -- A round-up of pivotal issues R. David Whitaker Senior Company Counsel Strategy & Operational Risk Group Wells Fargo Bank, N. A.
Agenda s “When last we left our heroes…” A review of key points from last year’s program s “Aim low, boys, they’re ridin’ Shetland ponies”* The “small wins” strategy s “Howdy, stranger” Addressing attribution and authority to sign s “Them varmints have cut the telegraph wires!” Dealing with notice and delivery issues s “Showdown at the OK Corral” Managing electronic records s “Riding off into the sunset” *With apologies to Lewis Grizzard
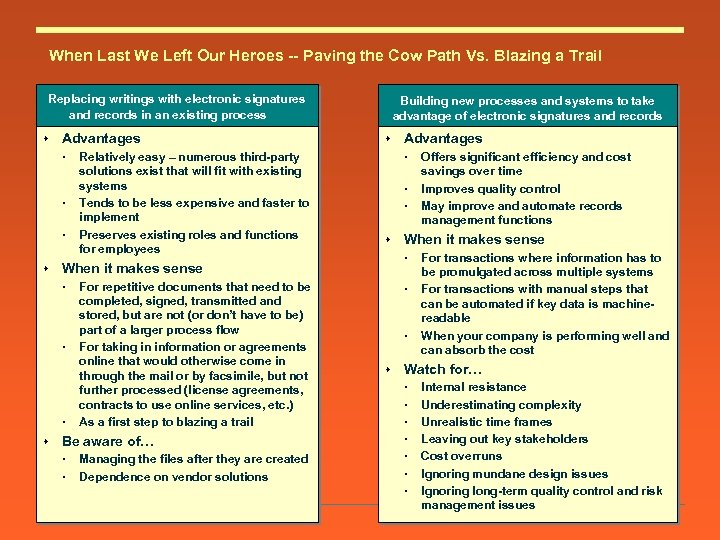
When Last We Left Our Heroes -- Paving the Cow Path Vs. Blazing a Trail Replacing writings with electronic signatures and records in an existing process s Advantages s s For repetitive documents that need to be completed, signed, transmitted and stored, but are not (or don’t have to be) part of a larger process flow For taking in information or agreements online that would otherwise come in through the mail or by facsimile, but not further processed (license agreements, contracts to use online services, etc. ) As a first step to blazing a trail Be aware of… Managing the files after they are created Dependence on vendor solutions Advantages s s Offers significant efficiency and cost savings over time Improves quality control May improve and automate records management functions When it makes sense s Relatively easy – numerous third-party solutions exist that will fit with existing systems Tends to be less expensive and faster to implement Preserves existing roles and functions for employees Building new processes and systems to take advantage of electronic signatures and records For transactions where information has to be promulgated across multiple systems For transactions with manual steps that can be automated if key data is machinereadable When your company is performing well and can absorb the cost Watch for… Internal resistance Underestimating complexity Unrealistic time frames Leaving out key stakeholders Cost overruns Ignoring mundane design issues Ignoring long-term quality control and risk management issues
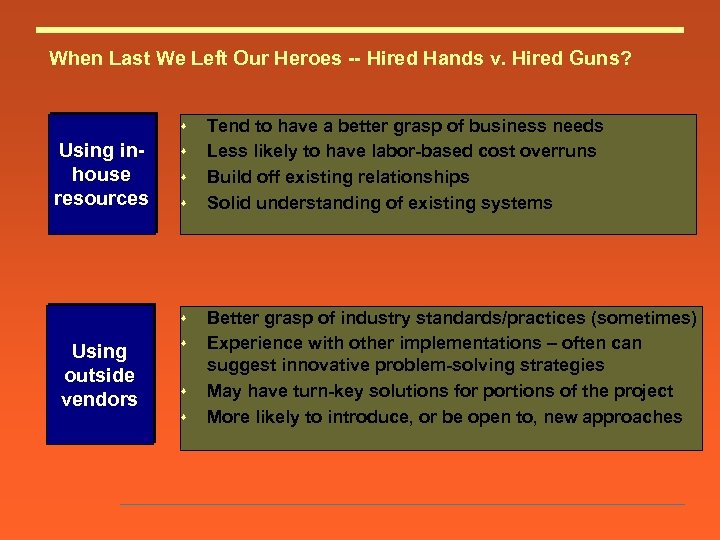
When Last We Left Our Heroes -- Hired Hands v. Hired Guns? s Using inhouse resources s s Using outside vendors s Tend to have a better grasp of business needs Less likely to have labor-based cost overruns Build off existing relationships Solid understanding of existing systems Better grasp of industry standards/practices (sometimes) Experience with other implementations – often can suggest innovative problem-solving strategies May have turn-key solutions for portions of the project More likely to introduce, or be open to, new approaches
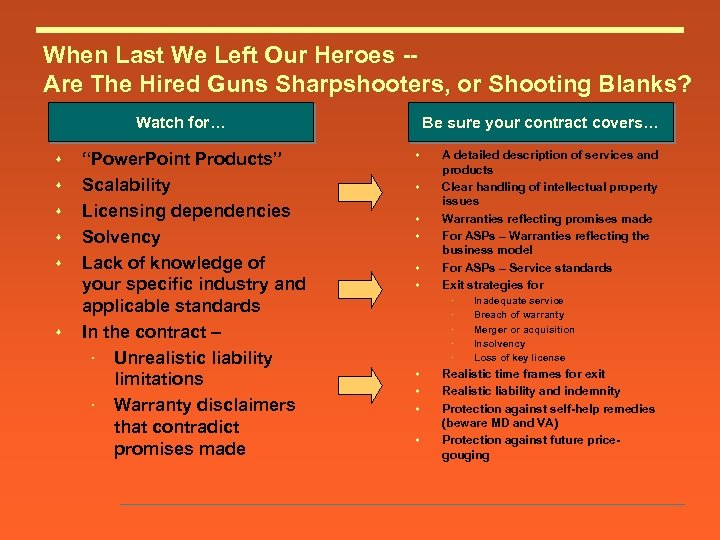
When Last We Left Our Heroes -Are The Hired Guns Sharpshooters, or Shooting Blanks? Watch for… s s s “Power. Point Products” Scalability Licensing dependencies Solvency Lack of knowledge of your specific industry and applicable standards In the contract – Unrealistic liability limitations Warranty disclaimers that contradict promises made Be sure your contract covers… s s s A detailed description of services and products Clear handling of intellectual property issues Warranties reflecting promises made For ASPs – Warranties reflecting the business model For ASPs – Service standards Exit strategies for s s Inadequate service Breach of warranty Merger or acquisition Insolvency Loss of key license Realistic time frames for exit Realistic liability and indemnity Protection against self-help remedies (beware MD and VA) Protection against future pricegouging
When Last We Left Our Heroes -- Herding Cats s Blazing a trail often means leaving comfortable roles behind s Internal resistance and roadblocks may come from: Those who see their role/importance diminished Those who see their role eliminated Those who will be required to learn new skills Those who will be required to revise system designs/infrastructure Those who will be asked to take responsibility
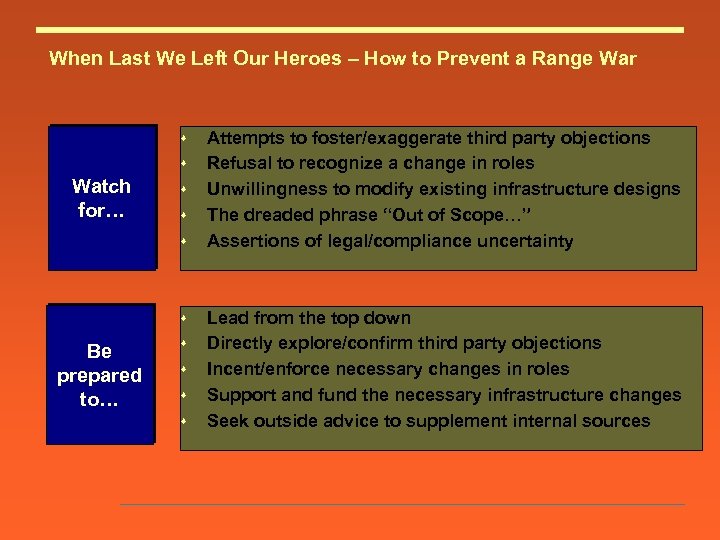
When Last We Left Our Heroes – How to Prevent a Range War s s Watch for… s s Be prepared to… s s Attempts to foster/exaggerate third party objections Refusal to recognize a change in roles Unwillingness to modify existing infrastructure designs The dreaded phrase “Out of Scope…” Assertions of legal/compliance uncertainty Lead from the top down Directly explore/confirm third party objections Incent/enforce necessary changes in roles Support and fund the necessary infrastructure changes Seek outside advice to supplement internal sources
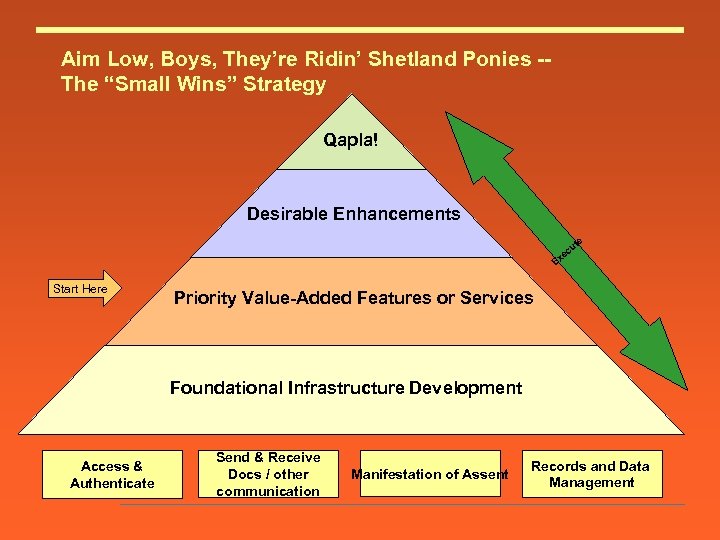
Aim Low, Boys, They’re Ridin’ Shetland Ponies -The “Small Wins” Strategy Qapla! Desirable Enhancements e ut c xe E Start Here Priority Value-Added Features or Services Foundational Infrastructure Development Access & Authenticate Send & Receive Docs / other communication Manifestation of Assent Records and Data Management
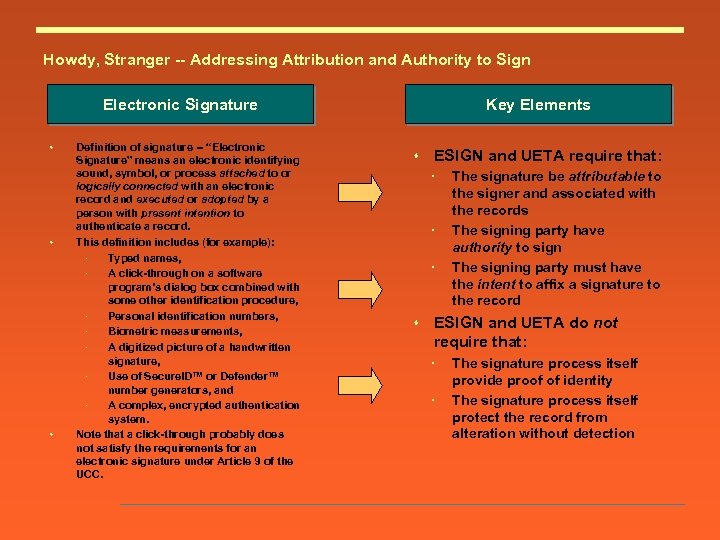
Howdy, Stranger -- Addressing Attribution and Authority to Sign Electronic Signature s s s Definition of signature -- “Electronic Signature” means an electronic identifying sound, symbol, or process attached to or logically connected with an electronic record and executed or adopted by a person with present intention to authenticate a record. This definition includes (for example): Typed names, A click-through on a software program’s dialog box combined with some other identification procedure, Personal identification numbers, Biometric measurements, A digitized picture of a handwritten signature, Use of Secure. ID™ or Defender™ number generators, and A complex, encrypted authentication system. Note that a click-through probably does not satisfy the requirements for an electronic signature under Article 9 of the UCC. Key Elements s ESIGN and UETA require that: s The signature be attributable to the signer and associated with the records The signing party have authority to sign The signing party must have the intent to affix a signature to the record ESIGN and UETA do not require that: The signature process itself provide proof of identity The signature process itself protect the record from alteration without detection
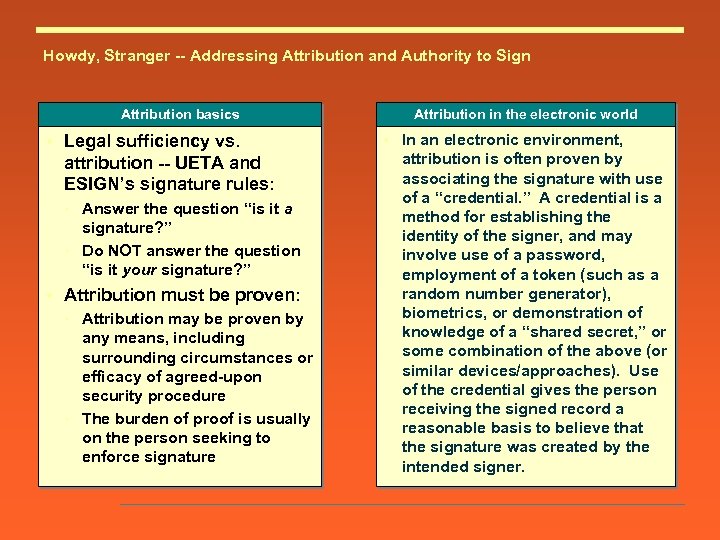
Howdy, Stranger -- Addressing Attribution and Authority to Sign Attribution basics s Legal sufficiency vs. attribution -- UETA and ESIGN’s signature rules: Answer the question “is it a signature? ” Do NOT answer the question “is it your signature? ” s Attribution must be proven: Attribution may be proven by any means, including surrounding circumstances or efficacy of agreed-upon security procedure The burden of proof is usually on the person seeking to enforce signature Attribution in the electronic world s In an electronic environment, attribution is often proven by associating the signature with use of a “credential. ” A credential is a method for establishing the identity of the signer, and may involve use of a password, employment of a token (such as a random number generator), biometrics, or demonstration of knowledge of a “shared secret, ” or some combination of the above (or similar devices/approaches). Use of the credential gives the person receiving the signed record a reasonable basis to believe that the signature was created by the intended signer.
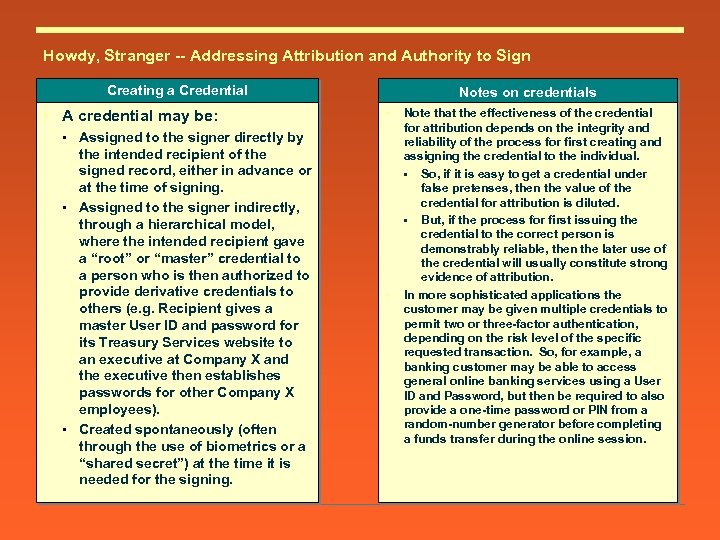
Howdy, Stranger -- Addressing Attribution and Authority to Sign Creating a Credential s A credential may be: • Assigned to the signer directly by the intended recipient of the signed record, either in advance or at the time of signing. • Assigned to the signer indirectly, through a hierarchical model, where the intended recipient gave a “root” or “master” credential to a person who is then authorized to provide derivative credentials to others (e. g. Recipient gives a master User ID and password for its Treasury Services website to an executive at Company X and the executive then establishes passwords for other Company X employees). • Created spontaneously (often through the use of biometrics or a “shared secret”) at the time it is needed for the signing. Notes on credentials s s Note that the effectiveness of the credential for attribution depends on the integrity and reliability of the process for first creating and assigning the credential to the individual. • So, if it is easy to get a credential under false pretenses, then the value of the credential for attribution is diluted. • But, if the process for first issuing the credential to the correct person is demonstrably reliable, then the later use of the credential will usually constitute strong evidence of attribution. In more sophisticated applications the customer may be given multiple credentials to permit two or three-factor authentication, depending on the risk level of the specific requested transaction. So, for example, a banking customer may be able to access general online banking services using a User ID and Password, but then be required to also provide a one-time password or PIN from a random-number generator before completing a funds transfer during the online session.
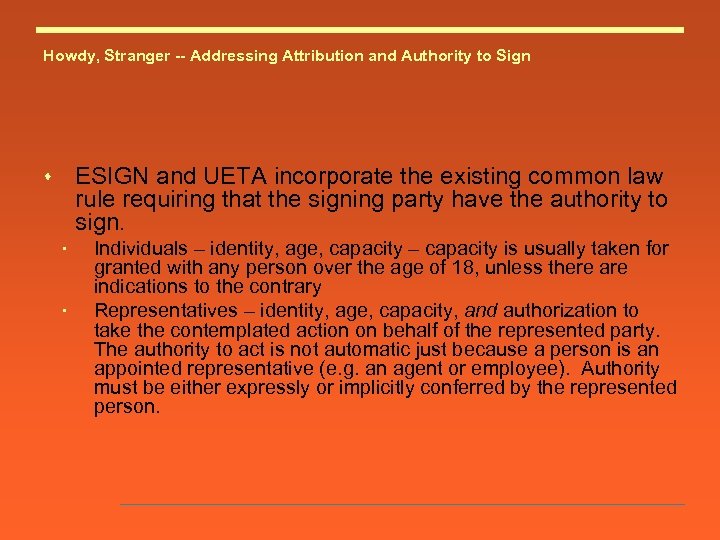
Howdy, Stranger -- Addressing Attribution and Authority to Sign ESIGN and UETA incorporate the existing common law rule requiring that the signing party have the authority to sign. s Individuals – identity, age, capacity – capacity is usually taken for granted with any person over the age of 18, unless there are indications to the contrary Representatives – identity, age, capacity, and authorization to take the contemplated action on behalf of the represented party. The authority to act is not automatic just because a person is an appointed representative (e. g. an agent or employee). Authority must be either expressly or implicitly conferred by the represented person.
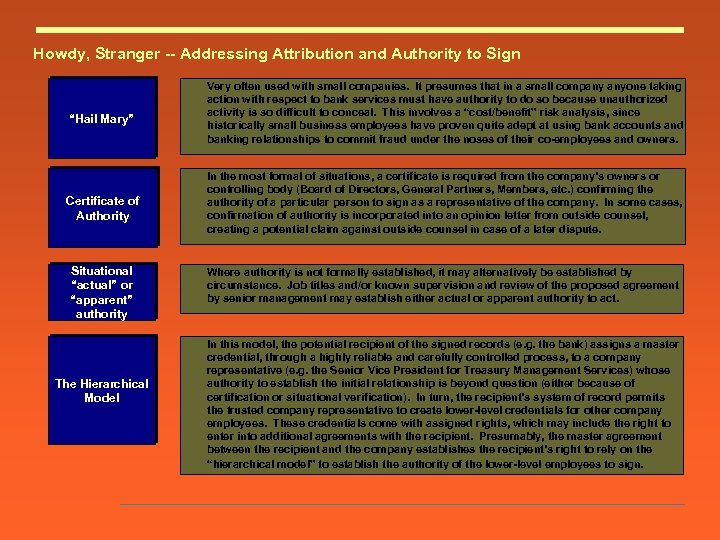
Howdy, Stranger -- Addressing Attribution and Authority to Sign “Hail Mary” Certificate of Authority Situational “actual” or “apparent” authority The Hierarchical Model Very often used with small companies. It presumes that in a small company anyone taking action with respect to bank services must have authority to do so because unauthorized activity is so difficult to conceal. This involves a “cost/benefit” risk analysis, since historically small business employees have proven quite adept at using bank accounts and banking relationships to commit fraud under the noses of their co-employees and owners. In the most formal of situations, a certificate is required from the company’s owners or controlling body (Board of Directors, General Partners, Members, etc. ) confirming the authority of a particular person to sign as a representative of the company. In some cases, confirmation of authority is incorporated into an opinion letter from outside counsel, creating a potential claim against outside counsel in case of a later dispute. Where authority is not formally established, it may alternatively be established by circumstance. Job titles and/or known supervision and review of the proposed agreement by senior management may establish either actual or apparent authority to act. In this model, the potential recipient of the signed records (e. g. the bank) assigns a master credential, through a highly reliable and carefully controlled process, to a company representative (e. g. the Senior Vice President for Treasury Management Services) whose authority to establish the initial relationship is beyond question (either because of certification or situational verification). In turn, the recipient’s system of record permits the trusted company representative to create lower-level credentials for other company employees. These credentials come with assigned rights, which may include the right to enter into additional agreements with the recipient. Presumably, the master agreement between the recipient and the company establishes the recipient’s right to rely on the “hierarchical model” to establish the authority of the lower-level employees to sign.
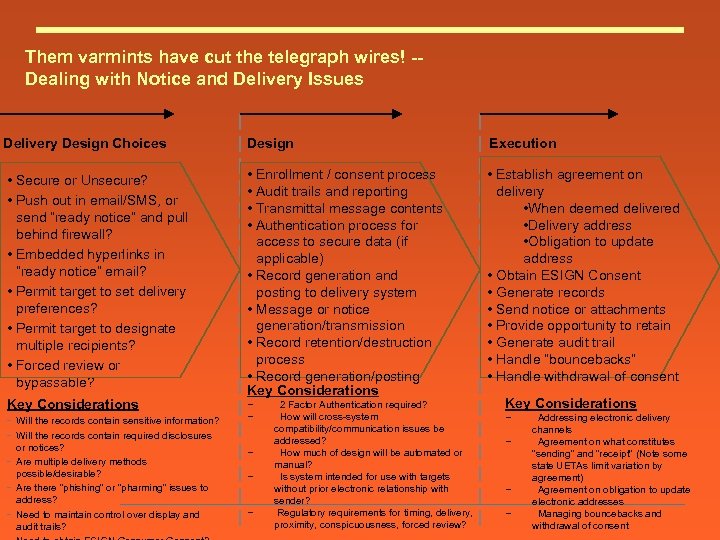
Them varmints have cut the telegraph wires! -Dealing with Notice and Delivery Issues Delivery Design Choices Design Execution • Secure or Unsecure? • Push out in email/SMS, or send “ready notice” and pull behind firewall? • Embedded hyperlinks in “ready notice” email? • Permit target to set delivery preferences? • Permit target to designate multiple recipients? • Forced review or bypassable? • Enrollment / consent process • Audit trails and reporting • Transmittal message contents • Authentication process for access to secure data (if applicable) • Record generation and posting to delivery system • Message or notice generation/transmission • Record retention/destruction process • Record generation/posting Key Considerations • Establish agreement on delivery • When deemed delivered • Delivery address • Obligation to update address • Obtain ESIGN Consent • Generate records • Send notice or attachments • Provide opportunity to retain • Generate audit trail • Handle “bouncebacks” • Handle withdrawal of consent Key Considerations - Will the records contain sensitive information? Will the records contain required disclosures or notices? Are multiple delivery methods possible/desirable? Are there “phishing” or “pharming” issues to address? Need to maintain control over display and audit trails? − − − 2 Factor Authentication required? How will cross-system compatibility/communication issues be addressed? How much of design will be automated or manual? Is system intended for use with targets without prior electronic relationship with sender? Regulatory requirements for timing, delivery, proximity, conspicuousness, forced review? Key Considerations − − Addressing electronic delivery channels Agreement on what constitutes “sending” and “receipt” (Note some state UETAs limit variation by agreement) Agreement on obligation to update electronic addresses Managing bouncebacks and withdrawal of consent
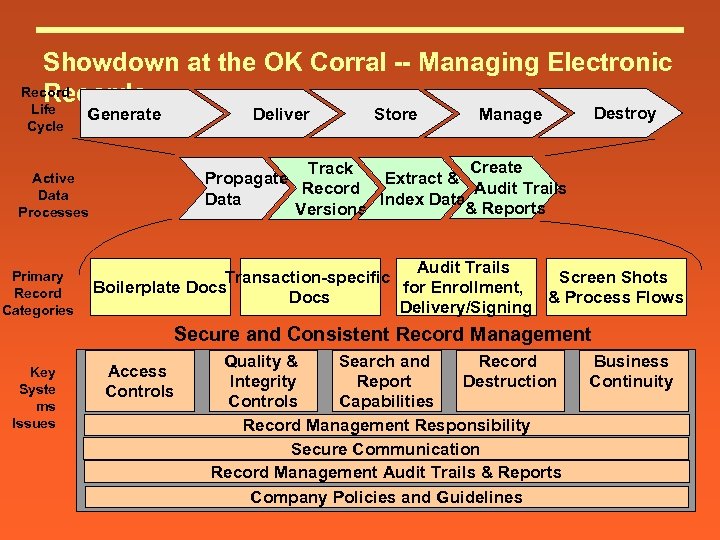
Showdown at the OK Corral -- Managing Electronic Records Life Cycle Generate Deliver Destroy Manage Create Track Propagate Extract & Audit Trails Record Data Index Data & Reports Versions Active Data Processes Primary Record Categories Store Audit Trails Transaction-specific Screen Shots Boilerplate Docs for Enrollment, Docs & Process Flows Delivery/Signing Secure and Consistent Record Management Key Syste ms Issues Access Controls Record Quality & Search and Destruction Integrity Report Controls Capabilities Record Management Responsibility Secure Communication Record Management Audit Trails & Reports Company Policies and Guidelines Business Continuity
Who was that masked man?
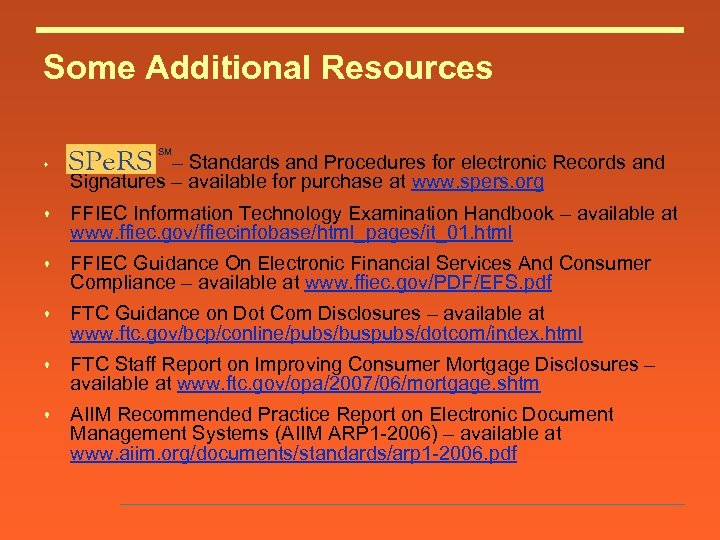
Some Additional Resources SM s – Standards and Procedures for electronic Records and Signatures – available for purchase at www. spers. org s FFIEC Information Technology Examination Handbook – available at www. ffiec. gov/ffiecinfobase/html_pages/it_01. html s FFIEC Guidance On Electronic Financial Services And Consumer Compliance – available at www. ffiec. gov/PDF/EFS. pdf s FTC Guidance on Dot Com Disclosures – available at www. ftc. gov/bcp/conline/pubs/buspubs/dotcom/index. html s FTC Staff Report on Improving Consumer Mortgage Disclosures – available at www. ftc. gov/opa/2007/06/mortgage. shtm s AIIM Recommended Practice Report on Electronic Document Management Systems (AIIM ARP 1 -2006) – available at www. aiim. org/documents/standards/arp 1 -2006. pdf
4dbd62a4a0ac9bd3b4770234ffbf01e1.ppt