1ddf3d11a0505bac1b7dbf0aaec227a2.ppt
- Количество слайдов: 33

SMXL: Tailoring Technology to Collaboration
SMXL FAQ • Is SMXL a new web scripting language? • No, it is the art of tailoring Id. M and access control technology to collaborations • Why is there only Small, Medium, and XL (extra large)? Why is there no Large ? • VO’s don’t come in Large – as soon as they grow to L, they think of themselves as XL kjk@internet 2. edu
Topics • VO’s and their Id. M needs • • Nature of VO’s Identity and Access Controls Collaboration and Domain Apps The Bedrock Grant • The cloth we have • SAML and federated identity • Growing ability to integrate social identity • Group management with some privilege add-ons • Collaboration management platforms • Domesticated applications • Making the suit fit kjk@internet 2. edu
The art of tailoring • Fitting identity and access management systems to collaborations • Serve both the collaboration and domain apps • Leverage and plumb into emergent federated identity infrastructure • Collaborations are like snowflakes – no two are alike. A big variety in the needs and styles of collaborations • Work with the collaboration to analyze their needs – for most, “gee, we never thought about things this way…” kjk@internet 2. edu
General VO Characteristics • Multi-institutional, usually multi-national collaborations • Frequently centered on unique instruments (e. g. CERN, Sloan), data repositories (e. g. medical records, economic data), etc • A VO is distinct from a general collaboration by formal roles, ownership of resources, real budgets, scholarly deliverables, accountability and audit requirements, etc. • Use standard collaboration tools and domain tools, often in an integrated fashion • VO’s have business processes but they don’t know them… kjk@internet 2. edu
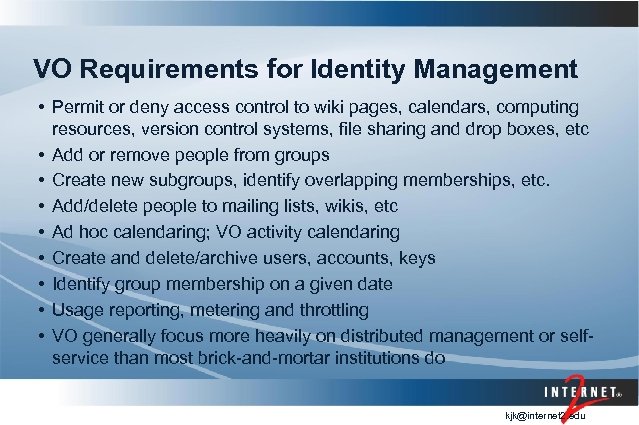
VO Requirements for Identity Management • Permit or deny access control to wiki pages, calendars, computing resources, version control systems, file sharing and drop boxes, etc • Add or remove people from groups • Create new subgroups, identify overlapping memberships, etc. • Add/delete people to mailing lists, wikis, etc • Ad hoc calendaring; VO activity calendaring • Create and delete/archive users, accounts, keys • Identify group membership on a given date • Usage reporting, metering and throttling • VO generally focus more heavily on distributed management or selfservice than most brick-and-mortar institutions do kjk@internet 2. edu
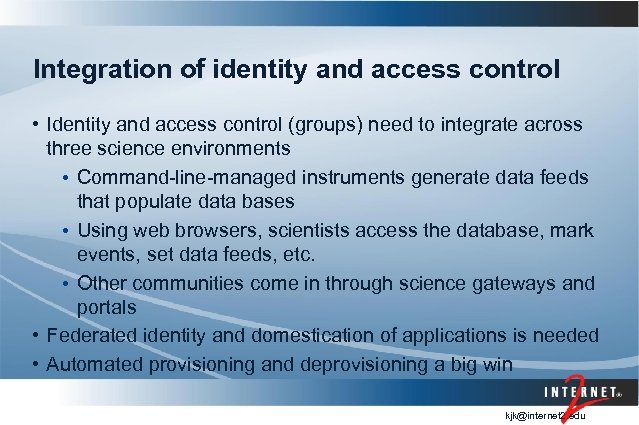
Integration of identity and access control • Identity and access control (groups) need to integrate across three science environments • Command-line-managed instruments generate data feeds that populate data bases • Using web browsers, scientists access the database, mark events, set data feeds, etc. • Other communities come in through science gateways and portals • Federated identity and domestication of applications is needed • Automated provisioning and deprovisioning a big win kjk@internet 2. edu
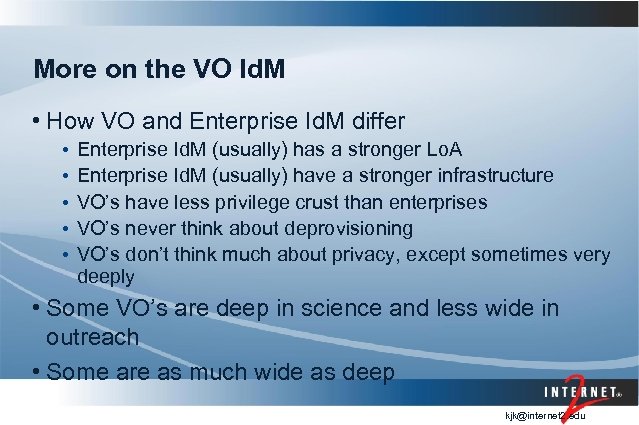
More on the VO Id. M • How VO and Enterprise Id. M differ • • • Enterprise Id. M (usually) has a stronger Lo. A Enterprise Id. M (usually) have a stronger infrastructure VO’s have less privilege crust than enterprises VO’s never think about deprovisioning VO’s don’t think much about privacy, except sometimes very deeply • Some VO’s are deep in science and less wide in outreach • Some are as much wide as deep kjk@internet 2. edu
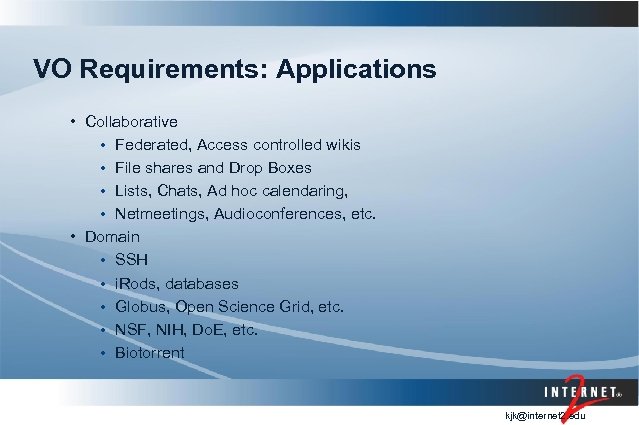
VO Requirements: Applications • Collaborative • Federated, Access controlled wikis • File shares and Drop Boxes • Lists, Chats, Ad hoc calendaring, • Netmeetings, Audioconferences, etc. • Domain • SSH • i. Rods, databases • Globus, Open Science Grid, etc. • NSF, NIH, Do. E, etc. • Biotorrent kjk@internet 2. edu
Meeting the VO Identity /Access Control needs • Leverage federated identity • Integrate institutional and VO attributes • Use groups for primary access control – understandable to most • Integrate with campus processes (identity management, course memberships, citizenship and other attributes) • Address security and privacy in ways that are appropriate, yet invisible to the user and the collaboration kjk@internet 2. edu
Single Profile • As VO’s get more data-centric in nature, profiles are the automated way to match users with new data sources, and a simple access control mechanism • Attributes with profile determine wiki permissions, db privileges • The controlled vocabulary/ontology aspects of profiles needs active management tools as well as storing the profiles and managing releases. • Some of the new NSF data nets are using multiple profiles; single profile is the next single sign-on…. • VIVO is an important building block for answers here http: //www. vivoweb. org/ kjk@internet 2. edu
The “Bedrock” Grant • Building from Bedrock: Infrastructure Improvements for Collaboration and Science – an NSF OCI grant (Fall, 2010) • Focus on further developing and integrating tools to allow collaborations to operate efficiently in the Id. M space • COmanage • Grouper • Shibboleth • Beginning the art of tailoring technology to collaboration http: //www. internet 2. edu/bedrock/ kjk@internet 2. edu
Engaged VO’s • LIGO – www. ligo. org - high profile international gravitional physics • i. Plant – www. iplantcollaborative. org - comprehensive cyberinfrastructure for Plant Biology • Bamboo - http: //projectbamboo. org/ - comprehensive cyberinfrastructure for Arts and Humanities • GENI – www. geni. net - NSF next generation Internet research • Earth Science Women’s Network http: //www. sage. wisc. edu/eswn/ - international peer-mentoring for women in earth sciences kjk@internet 2. edu
kjk@internet 2. edu
How collaborative is LIGO? • Blindly (secretly) injected simulated signal into data stream • Much activity ensued! • 7000 emails exchanged • 3 TB of data analysis output • 150 (long and detailed) wiki pages constructed • 50 people actively writing paper • All of this for one astrophysical (non) event… kjk@internet 2. edu
Observations from LIGO • Efficient collaboration begins with scalable and robust identity management infrastructure that can easily be leveraged and integrated with the wide spectrum of tools LIGO scientists use to collaborate and analyze the LIGO data. • Middleware, including Shibboleth and Grouper, is enabling more LIGO science through easier collaboration and access to resources. • Science VOs have little Id. M experience and need consulting to prevent repeating old mistakes • Id. M is the bedrock foundation but alone is not enough • Collaboration management platforms (CMP) needed • Efficiency for researchers is key • Need to spin up collaboration spaces quickly and easily kjk@internet 2. edu
The Cloth we work with • SAML and federated identity • A set of powerful attribute and authorization tools, connectable to Bedrock • Person registries and VO business processes • Group management with add-ons for permissions • Domesticated applications and back-ends kjk@internet 2. edu
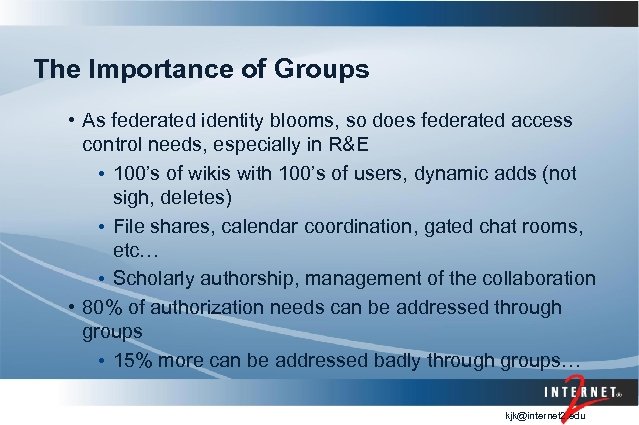
The Importance of Groups • As federated identity blooms, so does federated access control needs, especially in R&E • 100’s of wikis with 100’s of users, dynamic adds (not sigh, deletes) • File shares, calendar coordination, gated chat rooms, etc… • Scholarly authorship, management of the collaboration • 80% of authorization needs can be addressed through groups • 15% more can be addressed badly through groups… kjk@internet 2. edu

Collaboration Management Platforms • An integrated “collaboration identity management system” • Provides basic group and role management for a group of federated users • Plugs into federated infrastructure to permit automatic data management • A growing set of applications that derive their authentication and authorization needs from such external systems • Collaboration apps – wikis, lists, calendaring, netmeeting • Domain apps – instruments, databases, computers, storage kjk@internet 2. edu
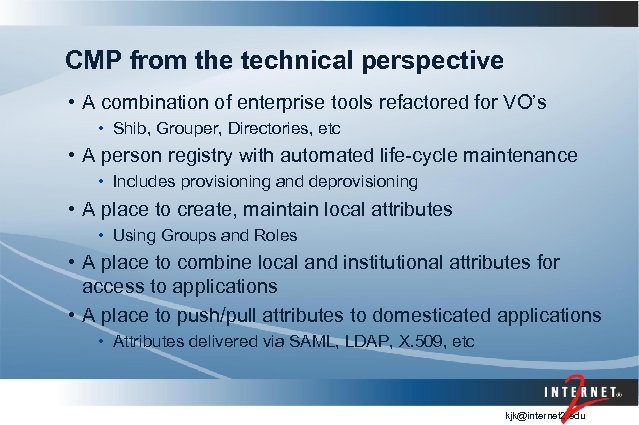
CMP from the technical perspective • A combination of enterprise tools refactored for VO’s • Shib, Grouper, Directories, etc • A person registry with automated life-cycle maintenance • Includes provisioning and deprovisioning • A place to create, maintain local attributes • Using Groups and Roles • A place to combine local and institutional attributes for access to applications • A place to push/pull attributes to domesticated applications • Attributes delivered via SAML, LDAP, X. 509, etc kjk@internet 2. edu
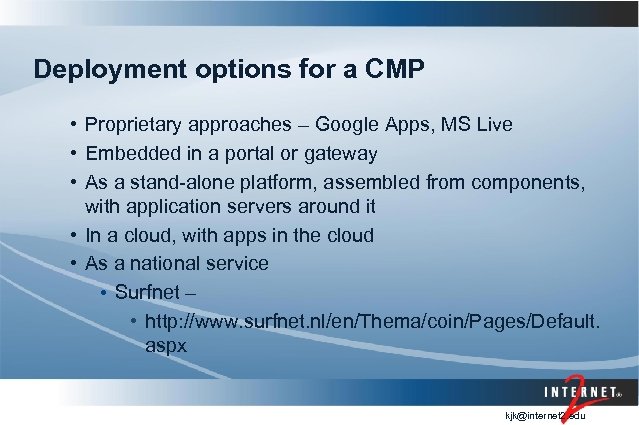
Deployment options for a CMP • Proprietary approaches – Google Apps, MS Live • Embedded in a portal or gateway • As a stand-alone platform, assembled from components, with application servers around it • In a cloud, with apps in the cloud • As a national service • Surfnet – • http: //www. surfnet. nl/en/Thema/coin/Pages/Default. aspx kjk@internet 2. edu
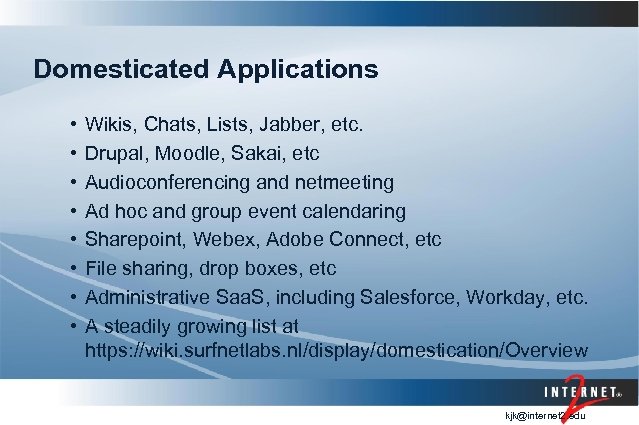
Domesticated Applications • • Wikis, Chats, Lists, Jabber, etc. Drupal, Moodle, Sakai, etc Audioconferencing and netmeeting Ad hoc and group event calendaring Sharepoint, Webex, Adobe Connect, etc File sharing, drop boxes, etc Administrative Saa. S, including Salesforce, Workday, etc. A steadily growing list at https: //wiki. surfnetlabs. nl/display/domestication/Overview kjk@internet 2. edu
http: //www. internet 2. edu/comanage/ • A set of replaceable modules: user console, person registry, Shibboleth Id. P and SP, Grouper, provisioning and deprovisioning, etc. • A set of domesticated apps • A kit, not a VM or a service • Funded by an NSF-SDCI grant and Internet 2 • API developed for the platform now in use at LIGO 23 – 3/16/2018, © 2011 INTERNET 2
The art of tailoring • Bringing powerful tools that can be used in VO and institutional contexts • Federated identity • Group and privilege management • Registries • Bringing in a different way of thinking • Of systemic business and collaborative processes • Of leveraging an attribute ecosystem • And listening and learning the organizational mission and culture • To make the VO look marvelous… kjk@internet 2. edu
Id. M geeks think differently… • A rich understanding of Internet identity • Bringing in an Id. M perspective • Separating roles and groups from identity • Life-cycle of privilege, triggers, thresholds, etc • Provisioning and deprovisioning • Starting with fresh new VO’s is good to avoid legacy bad code kjk@internet 2. edu
VO Assessment Tool • • • Culture and management Community – users, outreach, admin, etc Application Requirements Access Control and Profiles Existing Middleware infrastructure https: //spaces. internet 2. edu/display/COmanage/CO+Requi rements+Assessment kjk@internet 2. edu
Helping with basic VO Id. M infrastructure • Name space • Local schema • Multiple federation issues • Use of social identity • Attribute aggregation kjk@internet 2. edu
Tailoring dimensions - 1 • Breadth of outreach – influences identity approaches • Depth of science – impacts security and LOA • Size of the collaboration and capabilities of IT staff • Assemble piece parts or use an outsourced platform • Locus of collaborators • Global scheduling, availability of identities, etc. • Affects privacy and ARP issues kjk@internet 2. edu
Tailoring dimensions - 2 • Dataness of collaboration – affects needs for taxonomies, profiles, etc. • Management style of collaboration • Role of PI’s, collabmins, sources of authority • Separate instruments lead to more complex authorization • Nature of collaborators • Balance of tools, communicating styles, etc • Autonomy of collaborations • When to include vs. to do VO-federation kjk@internet 2. edu
Intake and Enrollment Process • The automatic enrollment of individuals into a CMP as a result of input from the participating institutions' central Id. M systems via federated tools such as Shibboleth or protocols such as OAuth. • Multi-stage process • Invitation or self-registration tool • Provisioning on the CMP • Identity intake – static or dynamic • Enrollment - The process of inviting, adding to groups, establishing authorizations in the CO kjk@internet 2. edu
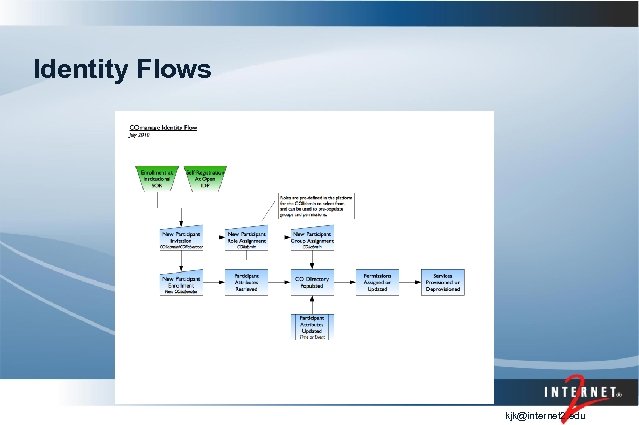
Identity Flows kjk@internet 2. edu
Typical Tailoring Issue: Where to Put the Access Control • At the Id. P or at the SP • At the portal or in the back-end db • E. g. domesticating i. Rods • Teach its internal policy engines to do attributes • Convert attributes to i. Rods policy at the portal • Use cases are diverse • May depend on meter and throttle needs Use personal allocations or group allocations kjk@internet 2. edu
Looking Ahead • Integrating international CMP standards • if LOFAR is using COIN and LIGO is using COmanage. . . • The metadata of a CMP (identifiers supported and indexed, name spaces, etc) • Managing attribute release better • Tagging apps and attribute bundles • Putting the informed into “informed consent” • Campuses bridging the gap to VO’s, rather than ignoring them • VO’s spreading the gospel… kjk@internet 2. edu
1ddf3d11a0505bac1b7dbf0aaec227a2.ppt