2a9336265d5d6ebd2c527235cfae711f.ppt
- Количество слайдов: 48
 SMT Solvers for Software Security George Nosenko, Security researcher at Digital Security
SMT Solvers for Software Security George Nosenko, Security researcher at Digital Security
 SMT Solvers for Software Security #whoami • Member of DSec. RG. • System Developer • Reverse Engineer • Security Researcher © 2002— 2013, Digital Security
SMT Solvers for Software Security #whoami • Member of DSec. RG. • System Developer • Reverse Engineer • Security Researcher © 2002— 2013, Digital Security
 SMT Solvers in very simple terms What is a SMT Solver? Just like the first time using a SMT constraint solver © 2002— 2013, Digital Security
SMT Solvers in very simple terms What is a SMT Solver? Just like the first time using a SMT constraint solver © 2002— 2013, Digital Security
 SMT Solvers in very simple terms What is a SMT Solver? Ø Solver is a program Ø You ask a question “What is the meaning of life? ” Ø Solver tries to answer “ 42” © 2002— 2013, Digital Security
SMT Solvers in very simple terms What is a SMT Solver? Ø Solver is a program Ø You ask a question “What is the meaning of life? ” Ø Solver tries to answer “ 42” © 2002— 2013, Digital Security
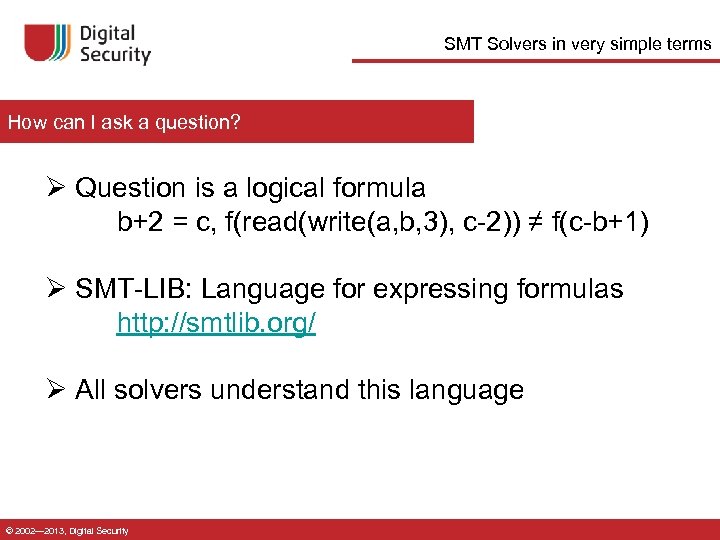 SMT Solvers in very simple terms How can I ask a question? Ø Question is a logical formula b+2 = c, f(read(write(a, b, 3), c-2)) ≠ f(c-b+1) Ø SMT-LIB: Language for expressing formulas http: //smtlib. org/ Ø All solvers understand this language © 2002— 2013, Digital Security
SMT Solvers in very simple terms How can I ask a question? Ø Question is a logical formula b+2 = c, f(read(write(a, b, 3), c-2)) ≠ f(c-b+1) Ø SMT-LIB: Language for expressing formulas http: //smtlib. org/ Ø All solvers understand this language © 2002— 2013, Digital Security
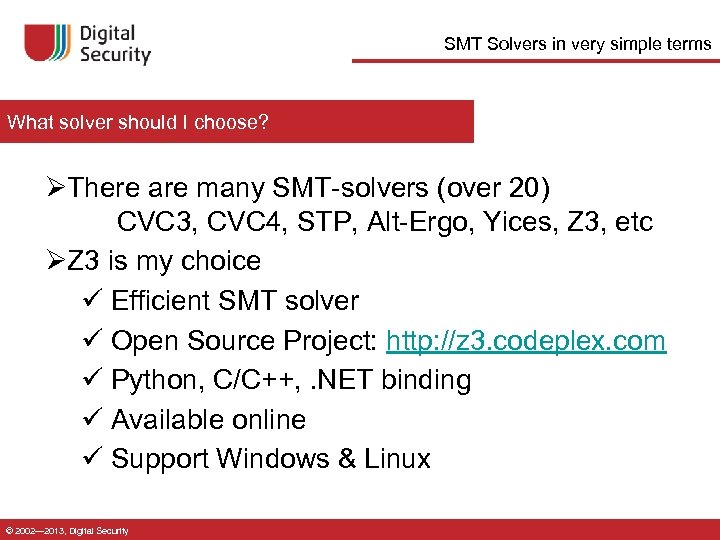 SMT Solvers in very simple terms What solver should I choose? ØThere are many SMT-solvers (over 20) CVC 3, CVC 4, STP, Alt-Ergo, Yices, Z 3, etc ØZ 3 is my choice ü Efficient SMT solver ü Open Source Project: http: //z 3. codeplex. com ü Python, C/C++, . NET binding ü Available online ü Support Windows & Linux © 2002— 2013, Digital Security
SMT Solvers in very simple terms What solver should I choose? ØThere are many SMT-solvers (over 20) CVC 3, CVC 4, STP, Alt-Ergo, Yices, Z 3, etc ØZ 3 is my choice ü Efficient SMT solver ü Open Source Project: http: //z 3. codeplex. com ü Python, C/C++, . NET binding ü Available online ü Support Windows & Linux © 2002— 2013, Digital Security
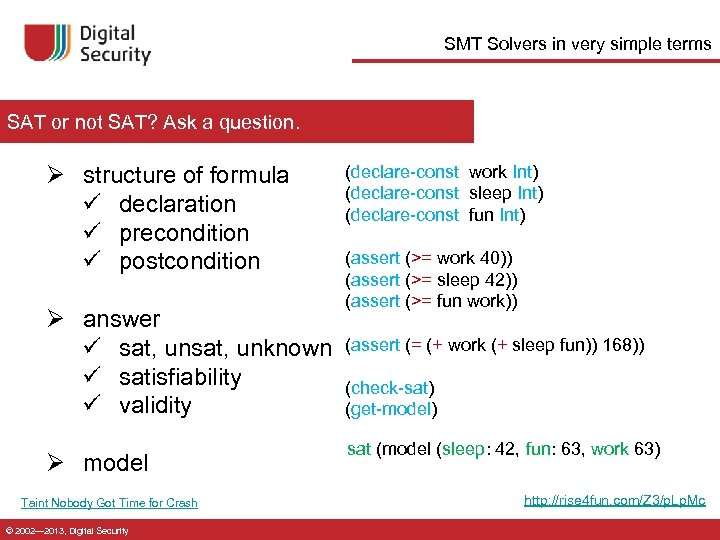 SMT Solvers in very simple terms SAT or not SAT? Ask a question. Ø structure of formula ü declaration ü precondition ü postcondition Ø answer ü sat, unknown ü satisfiability ü validity Ø model Taint Nobody Got Time for Crash © 2002— 2013, Digital Security (declare-const work Int) (declare-const sleep Int) (declare-const fun Int) (assert (>= work 40)) (assert (>= sleep 42)) (assert (>= fun work)) (assert (= (+ work (+ sleep fun)) 168)) (check-sat) (get-model) sat (model (sleep: 42, fun: 63, work 63) http: //rise 4 fun. com/Z 3/p. Lp. Mc
SMT Solvers in very simple terms SAT or not SAT? Ask a question. Ø structure of formula ü declaration ü precondition ü postcondition Ø answer ü sat, unknown ü satisfiability ü validity Ø model Taint Nobody Got Time for Crash © 2002— 2013, Digital Security (declare-const work Int) (declare-const sleep Int) (declare-const fun Int) (assert (>= work 40)) (assert (>= sleep 42)) (assert (>= fun work)) (assert (= (+ work (+ sleep fun)) 168)) (check-sat) (get-model) sat (model (sleep: 42, fun: 63, work 63) http: //rise 4 fun. com/Z 3/p. Lp. Mc
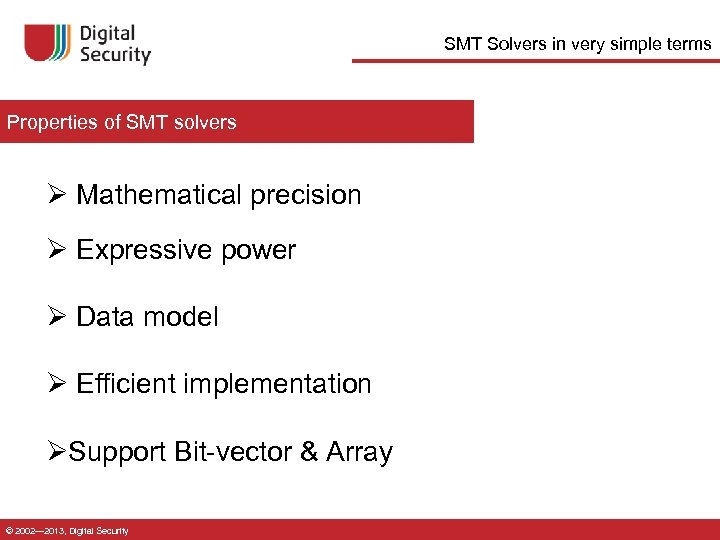 SMT Solvers in very simple terms Properties of SMT solvers Ø Mathematical precision Ø Expressive power Ø Data model Ø Efficient implementation ØSupport Bit-vector & Array © 2002— 2013, Digital Security
SMT Solvers in very simple terms Properties of SMT solvers Ø Mathematical precision Ø Expressive power Ø Data model Ø Efficient implementation ØSupport Bit-vector & Array © 2002— 2013, Digital Security
 SMT Solvers for Software Security © 2002— 2013, Digital Security
SMT Solvers for Software Security © 2002— 2013, Digital Security
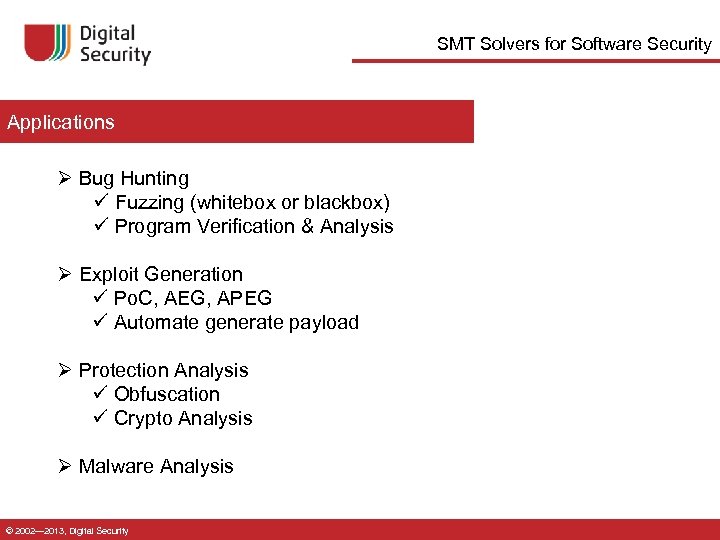 SMT Solvers for Software Security Applications Ø Bug Hunting ü Fuzzing (whitebox or blackbox) ü Program Verification & Analysis Ø Exploit Generation ü Po. C, AEG, APEG ü Automate generate payload Ø Protection Analysis ü Obfuscation ü Crypto Analysis Ø Malware Analysis © 2002— 2013, Digital Security
SMT Solvers for Software Security Applications Ø Bug Hunting ü Fuzzing (whitebox or blackbox) ü Program Verification & Analysis Ø Exploit Generation ü Po. C, AEG, APEG ü Automate generate payload Ø Protection Analysis ü Obfuscation ü Crypto Analysis Ø Malware Analysis © 2002— 2013, Digital Security
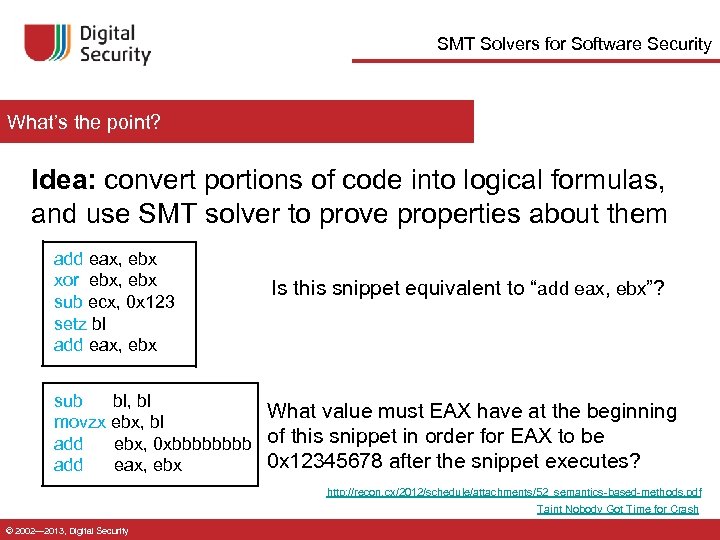 SMT Solvers for Software Security What’s the point? Idea: convert portions of code into logical formulas, and use SMT solver to prove properties about them add eax, ebx xor ebx, ebx sub ecx, 0 x 123 setz bl add eax, ebx Is this snippet equivalent to “add eax, ebx”? sub bl, bl What value must EAX have at the beginning movzx ebx, bl add ebx, 0 xbbbb of this snippet in order for EAX to be 0 x 12345678 after the snippet executes? add eax, ebx http: //recon. cx/2012/schedule/attachments/52_semantics-based-methods. pdf Taint Nobody Got Time for Crash © 2002— 2013, Digital Security
SMT Solvers for Software Security What’s the point? Idea: convert portions of code into logical formulas, and use SMT solver to prove properties about them add eax, ebx xor ebx, ebx sub ecx, 0 x 123 setz bl add eax, ebx Is this snippet equivalent to “add eax, ebx”? sub bl, bl What value must EAX have at the beginning movzx ebx, bl add ebx, 0 xbbbb of this snippet in order for EAX to be 0 x 12345678 after the snippet executes? add eax, ebx http: //recon. cx/2012/schedule/attachments/52_semantics-based-methods. pdf Taint Nobody Got Time for Crash © 2002— 2013, Digital Security
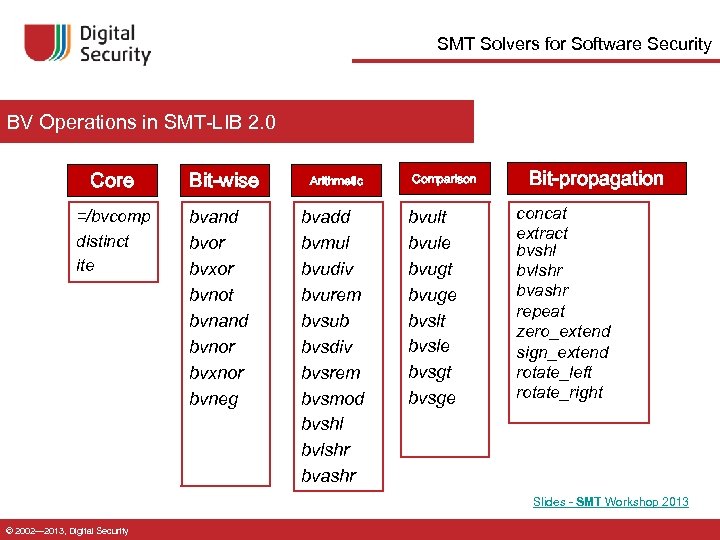 SMT Solvers for Software Security BV Operations in SMT-LIB 2. 0 Core =/bvcomp distinct ite Bit-wise bvand bvor bvxor bvnot bvnand bvnor bvxnor bvneg Arithmetic bvadd bvmul bvudiv bvurem bvsub bvsdiv bvsrem bvsmod bvshl bvlshr bvashr Comparison bvult bvule bvugt bvuge bvslt bvsle bvsgt bvsge Bit-propagation concat extract bvshl bvlshr bvashr repeat zero_extend sign_extend rotate_left rotate_right Slides - SMT Workshop 2013 © 2002— 2013, Digital Security
SMT Solvers for Software Security BV Operations in SMT-LIB 2. 0 Core =/bvcomp distinct ite Bit-wise bvand bvor bvxor bvnot bvnand bvnor bvxnor bvneg Arithmetic bvadd bvmul bvudiv bvurem bvsub bvsdiv bvsrem bvsmod bvshl bvlshr bvashr Comparison bvult bvule bvugt bvuge bvslt bvsle bvsgt bvsge Bit-propagation concat extract bvshl bvlshr bvashr repeat zero_extend sign_extend rotate_left rotate_right Slides - SMT Workshop 2013 © 2002— 2013, Digital Security
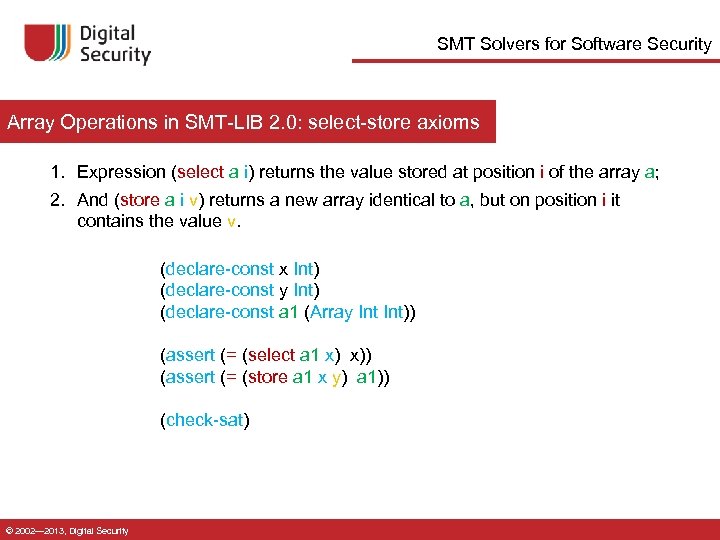 SMT Solvers for Software Security Array Operations in SMT-LIB 2. 0: select-store axioms 1. Expression (select a i) returns the value stored at position i of the array a; 2. And (store a i v) returns a new array identical to a, but on position i it contains the value v. (declare-const x Int) (declare-const y Int) (declare-const a 1 (Array Int)) (assert (= (select a 1 x) x)) (assert (= (store a 1 x y) a 1)) (check-sat) © 2002— 2013, Digital Security
SMT Solvers for Software Security Array Operations in SMT-LIB 2. 0: select-store axioms 1. Expression (select a i) returns the value stored at position i of the array a; 2. And (store a i v) returns a new array identical to a, but on position i it contains the value v. (declare-const x Int) (declare-const y Int) (declare-const a 1 (Array Int)) (assert (= (select a 1 x) x)) (assert (= (store a 1 x y) a 1)) (check-sat) © 2002— 2013, Digital Security
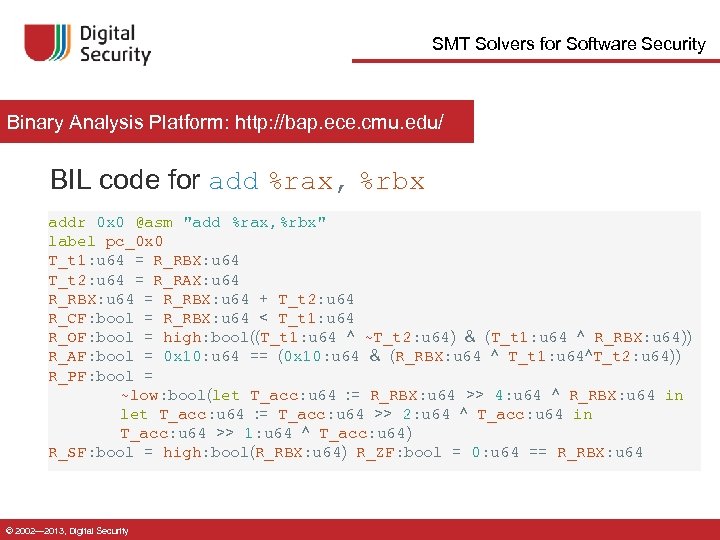 SMT Solvers for Software Security Binary Analysis Platform: http: //bap. ece. cmu. edu/ BIL code for add %rax, %rbx addr 0 x 0 @asm "add %rax, %rbx" label pc_0 x 0 T_t 1: u 64 = R_RBX: u 64 T_t 2: u 64 = R_RAX: u 64 R_RBX: u 64 = R_RBX: u 64 + T_t 2: u 64 R_CF: bool = R_RBX: u 64 < T_t 1: u 64 R_OF: bool = high: bool((T_t 1: u 64 ^ ~T_t 2: u 64) & (T_t 1: u 64 ^ R_RBX: u 64)) R_AF: bool = 0 x 10: u 64 == (0 x 10: u 64 & (R_RBX: u 64 ^ T_t 1: u 64^T_t 2: u 64)) R_PF: bool = ~low: bool(let T_acc: u 64 : = R_RBX: u 64 >> 4: u 64 ^ R_RBX: u 64 in let T_acc: u 64 : = T_acc: u 64 >> 2: u 64 ^ T_acc: u 64 in T_acc: u 64 >> 1: u 64 ^ T_acc: u 64) R_SF: bool = high: bool(R_RBX: u 64) R_ZF: bool = 0: u 64 == R_RBX: u 64 © 2002— 2013, Digital Security
SMT Solvers for Software Security Binary Analysis Platform: http: //bap. ece. cmu. edu/ BIL code for add %rax, %rbx addr 0 x 0 @asm "add %rax, %rbx" label pc_0 x 0 T_t 1: u 64 = R_RBX: u 64 T_t 2: u 64 = R_RAX: u 64 R_RBX: u 64 = R_RBX: u 64 + T_t 2: u 64 R_CF: bool = R_RBX: u 64 < T_t 1: u 64 R_OF: bool = high: bool((T_t 1: u 64 ^ ~T_t 2: u 64) & (T_t 1: u 64 ^ R_RBX: u 64)) R_AF: bool = 0 x 10: u 64 == (0 x 10: u 64 & (R_RBX: u 64 ^ T_t 1: u 64^T_t 2: u 64)) R_PF: bool = ~low: bool(let T_acc: u 64 : = R_RBX: u 64 >> 4: u 64 ^ R_RBX: u 64 in let T_acc: u 64 : = T_acc: u 64 >> 2: u 64 ^ T_acc: u 64 in T_acc: u 64 >> 1: u 64 ^ T_acc: u 64) R_SF: bool = high: bool(R_RBX: u 64) R_ZF: bool = 0: u 64 == R_RBX: u 64 © 2002— 2013, Digital Security
 SMT Solvers for Software Security Bug Hunting © 2002— 2013, Digital Security
SMT Solvers for Software Security Bug Hunting © 2002— 2013, Digital Security
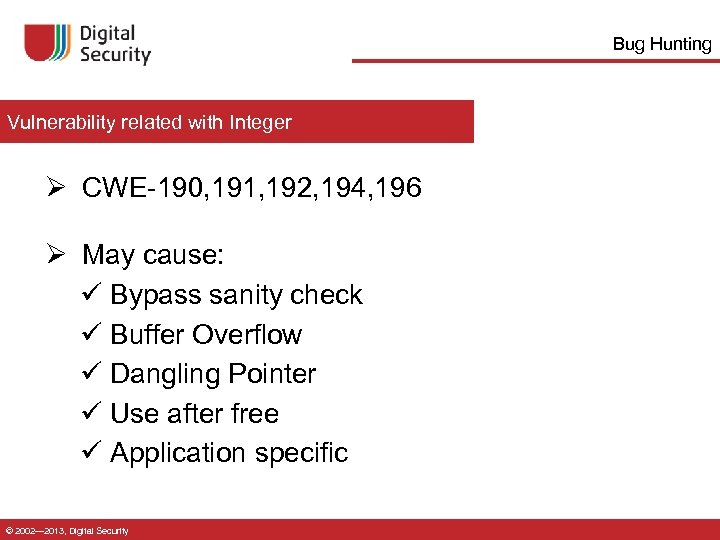 Bug Hunting Vulnerability related with Integer Ø CWE-190, 191, 192, 194, 196 Ø May cause: ü Bypass sanity check ü Buffer Overflow ü Dangling Pointer ü Use after free ü Application specific © 2002— 2013, Digital Security
Bug Hunting Vulnerability related with Integer Ø CWE-190, 191, 192, 194, 196 Ø May cause: ü Bypass sanity check ü Buffer Overflow ü Dangling Pointer ü Use after free ü Application specific © 2002— 2013, Digital Security
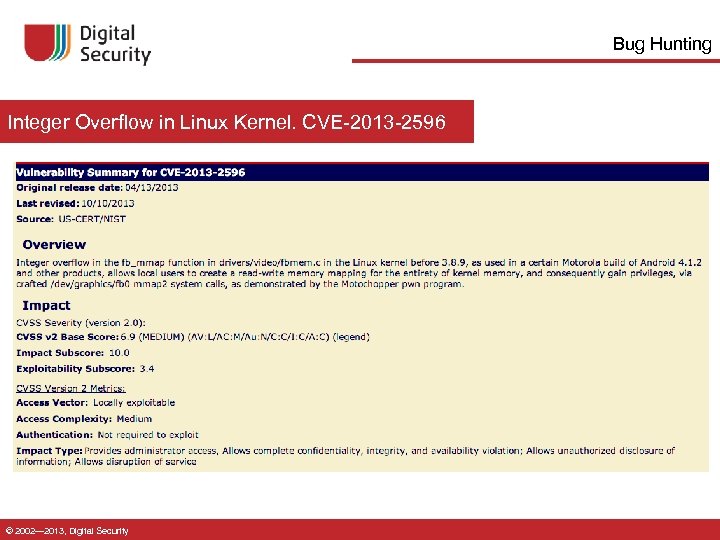 Bug Hunting Integer Overflow in Linux Kernel. CVE-2013 -2596 © 2002— 2013, Digital Security
Bug Hunting Integer Overflow in Linux Kernel. CVE-2013 -2596 © 2002— 2013, Digital Security
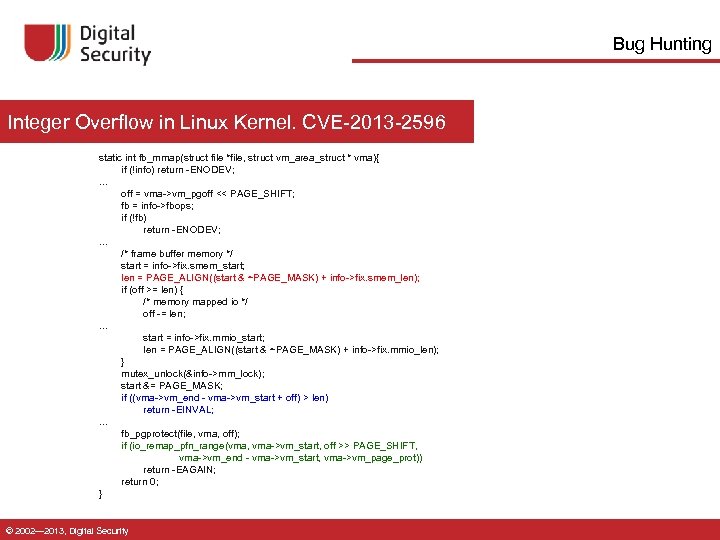 Bug Hunting Integer Overflow in Linux Kernel. CVE-2013 -2596 static int fb_mmap(struct file *file, struct vm_area_struct * vma){ if (!info) return -ENODEV; . . . off = vma->vm_pgoff << PAGE_SHIFT; fb = info->fbops; if (!fb) return -ENODEV; . . . /* frame buffer memory */ start = info->fix. smem_start; len = PAGE_ALIGN((start & ~PAGE_MASK) + info->fix. smem_len); if (off >= len) { /* memory mapped io */ off -= len; . . . start = info->fix. mmio_start; len = PAGE_ALIGN((start & ~PAGE_MASK) + info->fix. mmio_len); } mutex_unlock(&info->mm_lock); start &= PAGE_MASK; if ((vma->vm_end - vma->vm_start + off) > len) return -EINVAL; . . . fb_pgprotect(file, vma, off); if (io_remap_pfn_range(vma, vma->vm_start, off >> PAGE_SHIFT, vma->vm_end - vma->vm_start, vma->vm_page_prot)) return -EAGAIN; return 0; } © 2002— 2013, Digital Security
Bug Hunting Integer Overflow in Linux Kernel. CVE-2013 -2596 static int fb_mmap(struct file *file, struct vm_area_struct * vma){ if (!info) return -ENODEV; . . . off = vma->vm_pgoff << PAGE_SHIFT; fb = info->fbops; if (!fb) return -ENODEV; . . . /* frame buffer memory */ start = info->fix. smem_start; len = PAGE_ALIGN((start & ~PAGE_MASK) + info->fix. smem_len); if (off >= len) { /* memory mapped io */ off -= len; . . . start = info->fix. mmio_start; len = PAGE_ALIGN((start & ~PAGE_MASK) + info->fix. mmio_len); } mutex_unlock(&info->mm_lock); start &= PAGE_MASK; if ((vma->vm_end - vma->vm_start + off) > len) return -EINVAL; . . . fb_pgprotect(file, vma, off); if (io_remap_pfn_range(vma, vma->vm_start, off >> PAGE_SHIFT, vma->vm_end - vma->vm_start, vma->vm_page_prot)) return -EAGAIN; return 0; } © 2002— 2013, Digital Security
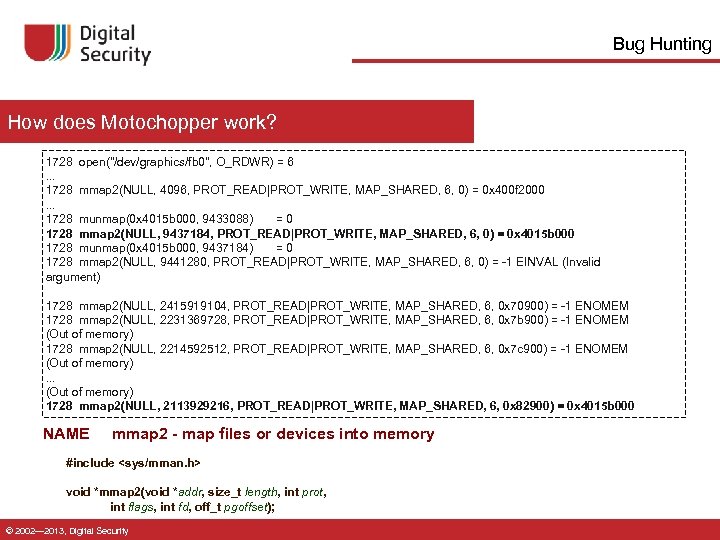 Bug Hunting How does Motochopper work? 1728 open("/dev/graphics/fb 0", O_RDWR) = 6. . . 1728 mmap 2(NULL, 4096, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0) = 0 x 400 f 2000. . . 1728 munmap(0 x 4015 b 000, 9433088) = 0 1728 mmap 2(NULL, 9437184, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0) = 0 x 4015 b 000 1728 munmap(0 x 4015 b 000, 9437184) = 0 1728 mmap 2(NULL, 9441280, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0) = -1 EINVAL (Invalid argument) 1728 mmap 2(NULL, 2415919104, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 70900) = -1 ENOMEM 1728 mmap 2(NULL, 2231369728, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 7 b 900) = -1 ENOMEM (Out of memory) 1728 mmap 2(NULL, 2214592512, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 7 c 900) = -1 ENOMEM (Out of memory). . . (Out of memory) 1728 mmap 2(NULL, 2113929216, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 82900) = 0 x 4015 b 000 NAME mmap 2 - map files or devices into memory #include
Bug Hunting How does Motochopper work? 1728 open("/dev/graphics/fb 0", O_RDWR) = 6. . . 1728 mmap 2(NULL, 4096, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0) = 0 x 400 f 2000. . . 1728 munmap(0 x 4015 b 000, 9433088) = 0 1728 mmap 2(NULL, 9437184, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0) = 0 x 4015 b 000 1728 munmap(0 x 4015 b 000, 9437184) = 0 1728 mmap 2(NULL, 9441280, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0) = -1 EINVAL (Invalid argument) 1728 mmap 2(NULL, 2415919104, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 70900) = -1 ENOMEM 1728 mmap 2(NULL, 2231369728, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 7 b 900) = -1 ENOMEM (Out of memory) 1728 mmap 2(NULL, 2214592512, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 7 c 900) = -1 ENOMEM (Out of memory). . . (Out of memory) 1728 mmap 2(NULL, 2113929216, PROT_READ|PROT_WRITE, MAP_SHARED, 6, 0 x 82900) = 0 x 4015 b 000 NAME mmap 2 - map files or devices into memory #include
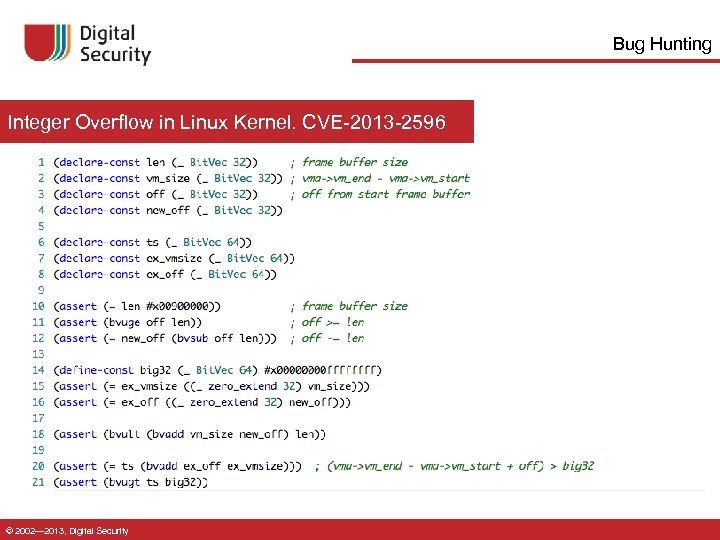 Bug Hunting Integer Overflow in Linux Kernel. CVE-2013 -2596 © 2002— 2013, Digital Security
Bug Hunting Integer Overflow in Linux Kernel. CVE-2013 -2596 © 2002— 2013, Digital Security
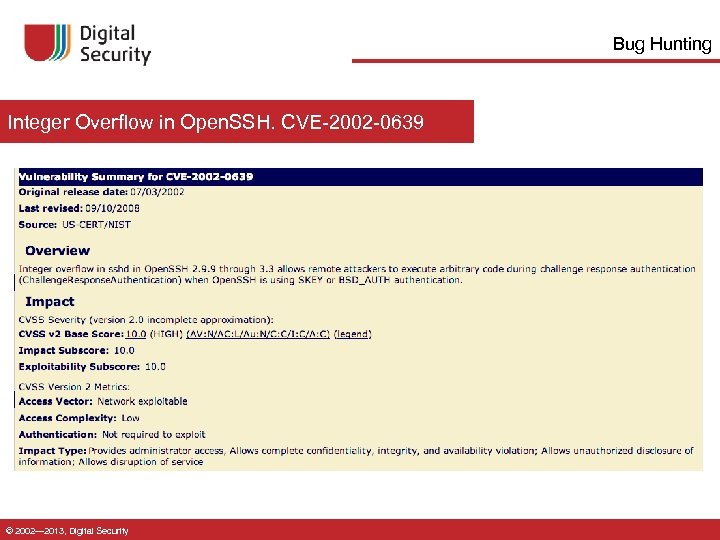 Bug Hunting Integer Overflow in Open. SSH. CVE-2002 -0639 © 2002— 2013, Digital Security
Bug Hunting Integer Overflow in Open. SSH. CVE-2002 -0639 © 2002— 2013, Digital Security
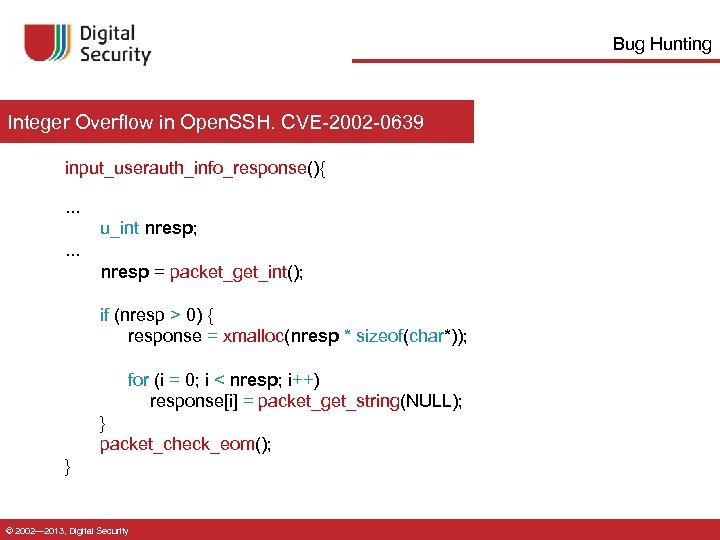 Bug Hunting Integer Overflow in Open. SSH. CVE-2002 -0639 input_userauth_info_response(){. . . u_int nresp; . . . nresp = packet_get_int(); if (nresp > 0) { response = xmalloc(nresp * sizeof(char*)); for (i = 0; i < nresp; i++) response[i] = packet_get_string(NULL); } packet_check_eom(); } © 2002— 2013, Digital Security
Bug Hunting Integer Overflow in Open. SSH. CVE-2002 -0639 input_userauth_info_response(){. . . u_int nresp; . . . nresp = packet_get_int(); if (nresp > 0) { response = xmalloc(nresp * sizeof(char*)); for (i = 0; i < nresp; i++) response[i] = packet_get_string(NULL); } packet_check_eom(); } © 2002— 2013, Digital Security
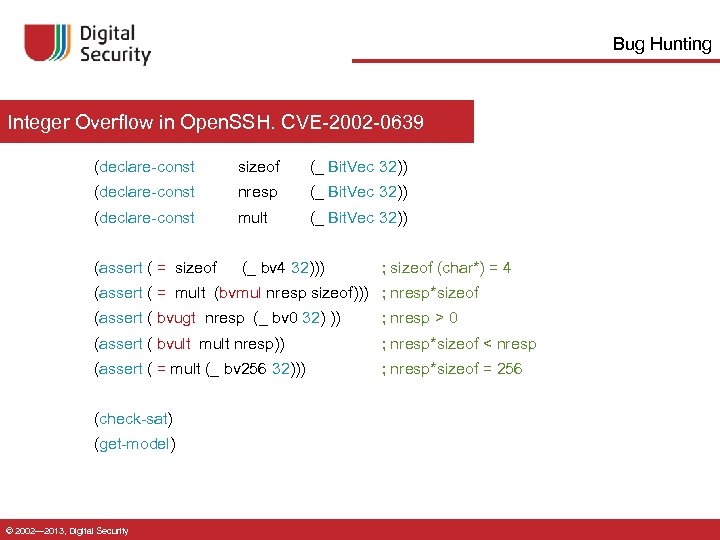 Bug Hunting Integer Overflow in Open. SSH. CVE-2002 -0639 (declare-const sizeof (_ Bit. Vec 32)) (declare-const nresp (_ Bit. Vec 32)) (declare-const mult (_ Bit. Vec 32)) (assert ( = sizeof (_ bv 4 32))) ; sizeof (char*) = 4 (assert ( = mult (bvmul nresp sizeof))) ; nresp*sizeof (assert ( bvugt nresp (_ bv 0 32) )) ; nresp > 0 (assert ( bvult mult nresp)) ; nresp*sizeof < nresp (assert ( = mult (_ bv 256 32))) ; nresp*sizeof = 256 (check-sat) (get-model) © 2002— 2013, Digital Security
Bug Hunting Integer Overflow in Open. SSH. CVE-2002 -0639 (declare-const sizeof (_ Bit. Vec 32)) (declare-const nresp (_ Bit. Vec 32)) (declare-const mult (_ Bit. Vec 32)) (assert ( = sizeof (_ bv 4 32))) ; sizeof (char*) = 4 (assert ( = mult (bvmul nresp sizeof))) ; nresp*sizeof (assert ( bvugt nresp (_ bv 0 32) )) ; nresp > 0 (assert ( bvult mult nresp)) ; nresp*sizeof < nresp (assert ( = mult (_ bv 256 32))) ; nresp*sizeof = 256 (check-sat) (get-model) © 2002— 2013, Digital Security
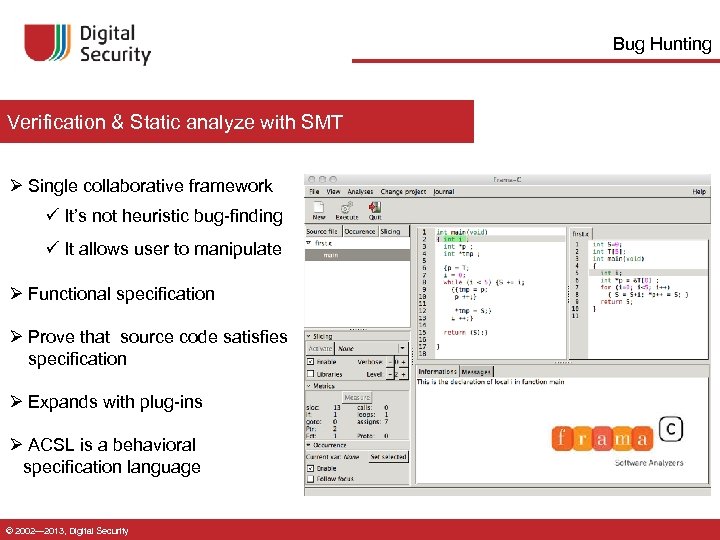 Bug Hunting Verification & Static analyze with SMT Ø Single collaborative framework ü It’s not heuristic bug-finding ü It allows user to manipulate Ø Functional specification Ø Prove that source code satisfies specification Ø Expands with plug-ins Ø ACSL is a behavioral specification language © 2002— 2013, Digital Security
Bug Hunting Verification & Static analyze with SMT Ø Single collaborative framework ü It’s not heuristic bug-finding ü It allows user to manipulate Ø Functional specification Ø Prove that source code satisfies specification Ø Expands with plug-ins Ø ACSL is a behavioral specification language © 2002— 2013, Digital Security
 Bug Hunting Jessie: verification tools for C programs Ø Jessie is a plug-in for the Frama-C Ø Functional Checking Ø Safety Checking ü Memory Safety ü Integer Overflow ü Checking Termination © 2002— 2013, Digital Security
Bug Hunting Jessie: verification tools for C programs Ø Jessie is a plug-in for the Frama-C Ø Functional Checking Ø Safety Checking ü Memory Safety ü Integer Overflow ü Checking Termination © 2002— 2013, Digital Security
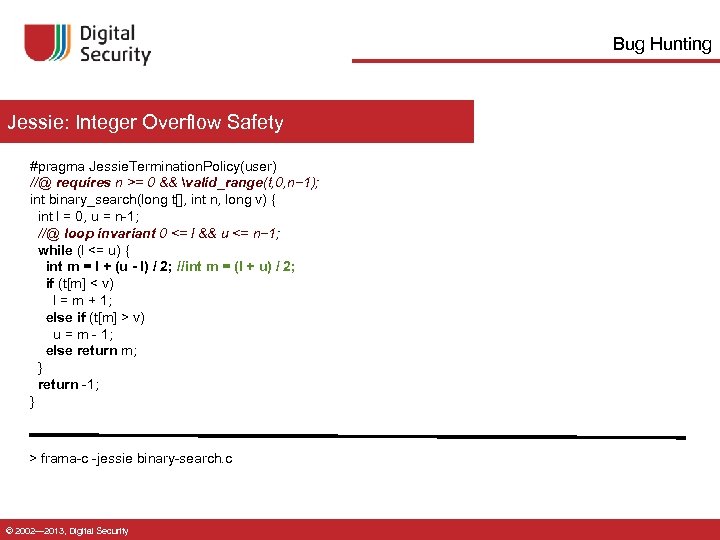 Bug Hunting Jessie: Integer Overflow Safety #pragma Jessie. Termination. Policy(user) //@ requires n >= 0 && valid_range(t, 0, n− 1); int binary_search(long t[], int n, long v) { int l = 0, u = n-1; //@ loop invariant 0 <= l && u <= n− 1; while (l <= u) { int m = l + (u - l) / 2; //int m = (l + u) / 2; if (t[m] < v) l = m + 1; else if (t[m] > v) u = m - 1; else return m; } return -1; } > frama-c -jessie binary-search. c © 2002— 2013, Digital Security
Bug Hunting Jessie: Integer Overflow Safety #pragma Jessie. Termination. Policy(user) //@ requires n >= 0 && valid_range(t, 0, n− 1); int binary_search(long t[], int n, long v) { int l = 0, u = n-1; //@ loop invariant 0 <= l && u <= n− 1; while (l <= u) { int m = l + (u - l) / 2; //int m = (l + u) / 2; if (t[m] < v) l = m + 1; else if (t[m] > v) u = m - 1; else return m; } return -1; } > frama-c -jessie binary-search. c © 2002— 2013, Digital Security
 Bug Hunting Immunity Debugger & SMT: Infrastructure Sequence. Analyzer – Models x 86 as operations over a set of SMT primitives. Solver – Ctypes interface to the CVC 3 SMT solver API. Supports a variety of theories including quantifier free, bit-vector arithmetic, linear arithmetic etc. Code. Graph/Path. Generator – Purely static CFG building and path generation. Path. Walker – SMT based path traversal. Each conditional jump is checked for feasibility and the path discarded if not SAT. Bug. Checker – Subclasses provide the check_ins method which will be passed the SMT context representing the current path. © 2002— 2013, Digital Security
Bug Hunting Immunity Debugger & SMT: Infrastructure Sequence. Analyzer – Models x 86 as operations over a set of SMT primitives. Solver – Ctypes interface to the CVC 3 SMT solver API. Supports a variety of theories including quantifier free, bit-vector arithmetic, linear arithmetic etc. Code. Graph/Path. Generator – Purely static CFG building and path generation. Path. Walker – SMT based path traversal. Each conditional jump is checked for feasibility and the path discarded if not SAT. Bug. Checker – Subclasses provide the check_ins method which will be passed the SMT context representing the current path. © 2002— 2013, Digital Security
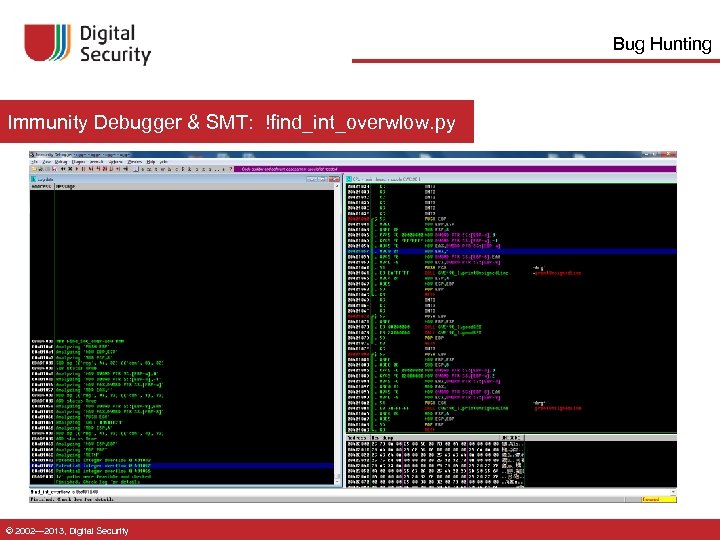 Bug Hunting Immunity Debugger & SMT: !find_int_overwlow. py © 2002— 2013, Digital Security
Bug Hunting Immunity Debugger & SMT: !find_int_overwlow. py © 2002— 2013, Digital Security
 SMT in protection analysis PROTECTION ANALYSIS © 2002— 2013, Digital Security
SMT in protection analysis PROTECTION ANALYSIS © 2002— 2013, Digital Security
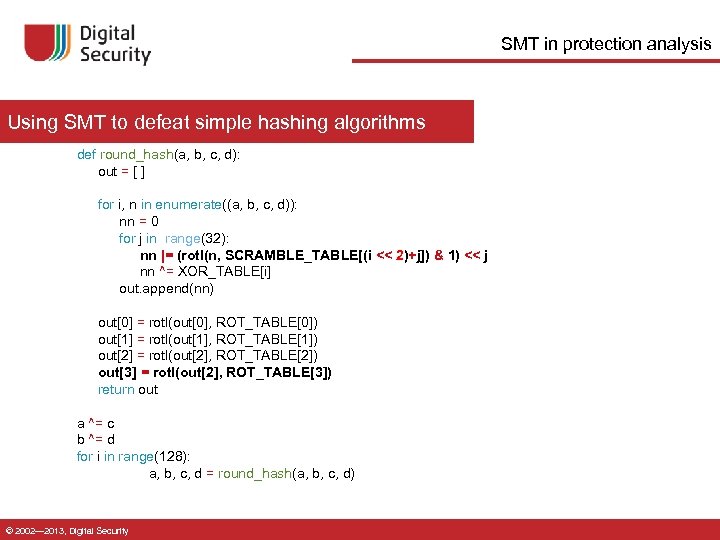 SMT in protection analysis Using SMT to defeat simple hashing algorithms def round_hash(a, b, c, d): out = [ ] for i, n in enumerate((a, b, c, d)): nn = 0 for j in range(32): nn |= (rotl(n, SCRAMBLE_TABLE[(i << 2)+j]) & 1) << j nn ^= XOR_TABLE[i] out. append(nn) out[0] = rotl(out[0], ROT_TABLE[0]) out[1] = rotl(out[1], ROT_TABLE[1]) out[2] = rotl(out[2], ROT_TABLE[2]) out[3] = rotl(out[2], ROT_TABLE[3]) return out a ^= c b ^= d for i in range(128): a, b, c, d = round_hash(a, b, c, d) © 2002— 2013, Digital Security
SMT in protection analysis Using SMT to defeat simple hashing algorithms def round_hash(a, b, c, d): out = [ ] for i, n in enumerate((a, b, c, d)): nn = 0 for j in range(32): nn |= (rotl(n, SCRAMBLE_TABLE[(i << 2)+j]) & 1) << j nn ^= XOR_TABLE[i] out. append(nn) out[0] = rotl(out[0], ROT_TABLE[0]) out[1] = rotl(out[1], ROT_TABLE[1]) out[2] = rotl(out[2], ROT_TABLE[2]) out[3] = rotl(out[2], ROT_TABLE[3]) return out a ^= c b ^= d for i in range(128): a, b, c, d = round_hash(a, b, c, d) © 2002— 2013, Digital Security
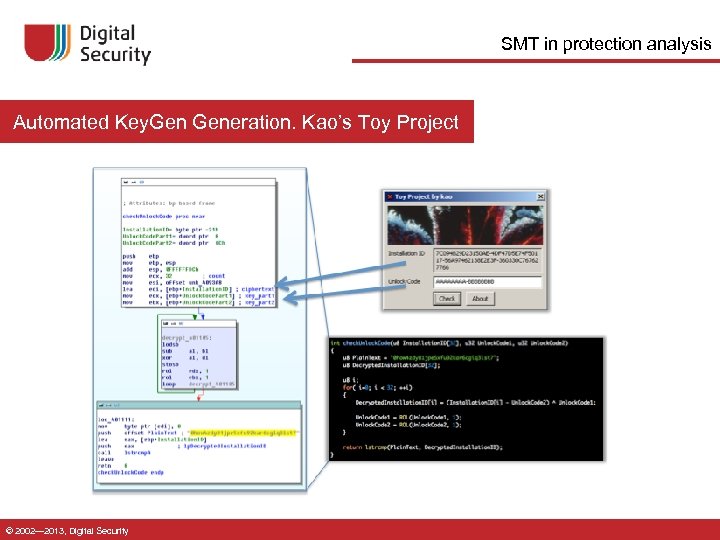 SMT in protection analysis Automated Key. Generation. Kao’s Toy Project © 2002— 2013, Digital Security
SMT in protection analysis Automated Key. Generation. Kao’s Toy Project © 2002— 2013, Digital Security
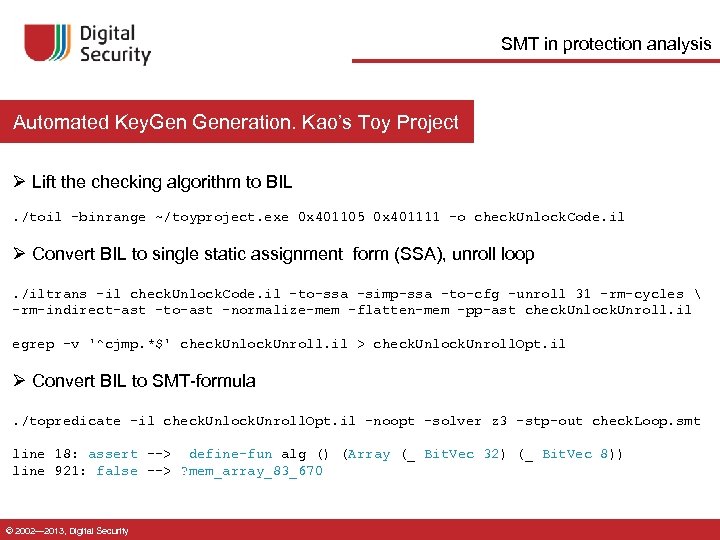 SMT in protection analysis Automated Key. Generation. Kao’s Toy Project Ø Lift the checking algorithm to BIL. /toil -binrange ~/toyproject. exe 0 x 401105 0 x 401111 -o check. Unlock. Code. il Ø Convert BIL to single static assignment form (SSA), unroll loop. /iltrans -il check. Unlock. Code. il -to-ssa -simp-ssa -to-cfg -unroll 31 -rm-cycles -rm-indirect-ast -to-ast -normalize-mem -flatten-mem -pp-ast check. Unlock. Unroll. il egrep -v '^cjmp. *$' check. Unlock. Unroll. il > check. Unlock. Unroll. Opt. il Ø Convert BIL to SMT-formula. /topredicate -il check. Unlock. Unroll. Opt. il -noopt -solver z 3 -stp-out check. Loop. smt line 18: assert --> define-fun alg () (Array (_ Bit. Vec 32) (_ Bit. Vec 8)) line 921: false --> ? mem_array_83_670 © 2002— 2013, Digital Security
SMT in protection analysis Automated Key. Generation. Kao’s Toy Project Ø Lift the checking algorithm to BIL. /toil -binrange ~/toyproject. exe 0 x 401105 0 x 401111 -o check. Unlock. Code. il Ø Convert BIL to single static assignment form (SSA), unroll loop. /iltrans -il check. Unlock. Code. il -to-ssa -simp-ssa -to-cfg -unroll 31 -rm-cycles -rm-indirect-ast -to-ast -normalize-mem -flatten-mem -pp-ast check. Unlock. Unroll. il egrep -v '^cjmp. *$' check. Unlock. Unroll. il > check. Unlock. Unroll. Opt. il Ø Convert BIL to SMT-formula. /topredicate -il check. Unlock. Unroll. Opt. il -noopt -solver z 3 -stp-out check. Loop. smt line 18: assert --> define-fun alg () (Array (_ Bit. Vec 32) (_ Bit. Vec 8)) line 921: false --> ? mem_array_83_670 © 2002— 2013, Digital Security
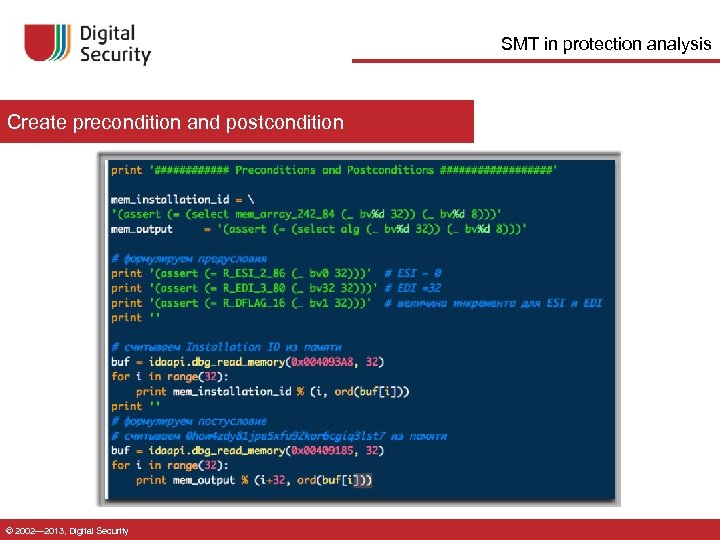 SMT in protection analysis Create precondition and postcondition © 2002— 2013, Digital Security
SMT in protection analysis Create precondition and postcondition © 2002— 2013, Digital Security
 AEG Automatic Exploit Generation Ø Automatically craft an input that redirects control flow Loosely defined as “Given a program and a vulnerability, automatically craft an input that redirects control flow to malicious code” Ø Automated Payload Creation © 2002— 2013, Digital Security
AEG Automatic Exploit Generation Ø Automatically craft an input that redirects control flow Loosely defined as “Given a program and a vulnerability, automatically craft an input that redirects control flow to malicious code” Ø Automated Payload Creation © 2002— 2013, Digital Security
 AEG Automatically craft an input that hijacks control flow Ø Get the trace to vulnerable code Ø Convert the trace into set of constraints Freach Ø Generate the set of conditions that make code exploitable Fexploit = Cval U Caddr Ø Solve (Freach U Fexploit) Ø SMT-solver defines required input © 2002— 2013, Digital Security
AEG Automatically craft an input that hijacks control flow Ø Get the trace to vulnerable code Ø Convert the trace into set of constraints Freach Ø Generate the set of conditions that make code exploitable Fexploit = Cval U Caddr Ø Solve (Freach U Fexploit) Ø SMT-solver defines required input © 2002— 2013, Digital Security
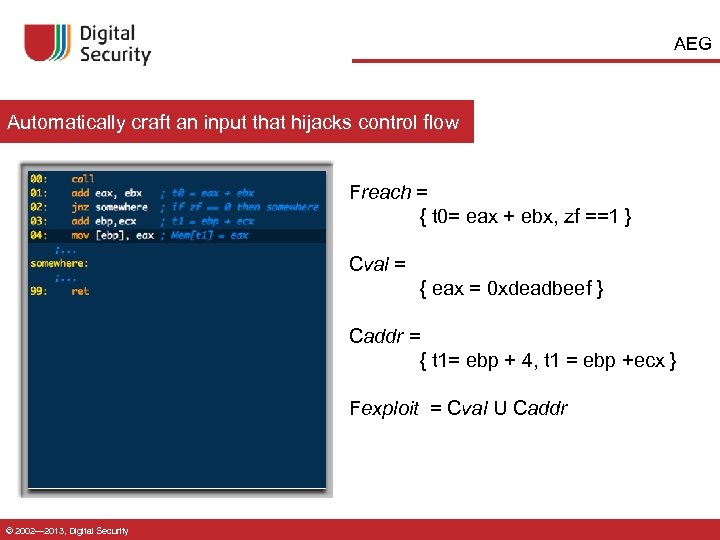 AEG Automatically craft an input that hijacks control flow Freach = { t 0= eax + ebx, zf ==1 } Cval = { eax = 0 xdeadbeef } Caddr = { t 1= ebp + 4, t 1 = ebp +ecx } Fexploit = Cval U Caddr © 2002— 2013, Digital Security
AEG Automatically craft an input that hijacks control flow Freach = { t 0= eax + ebx, zf ==1 } Cval = { eax = 0 xdeadbeef } Caddr = { t 1= ebp + 4, t 1 = ebp +ecx } Fexploit = Cval U Caddr © 2002— 2013, Digital Security
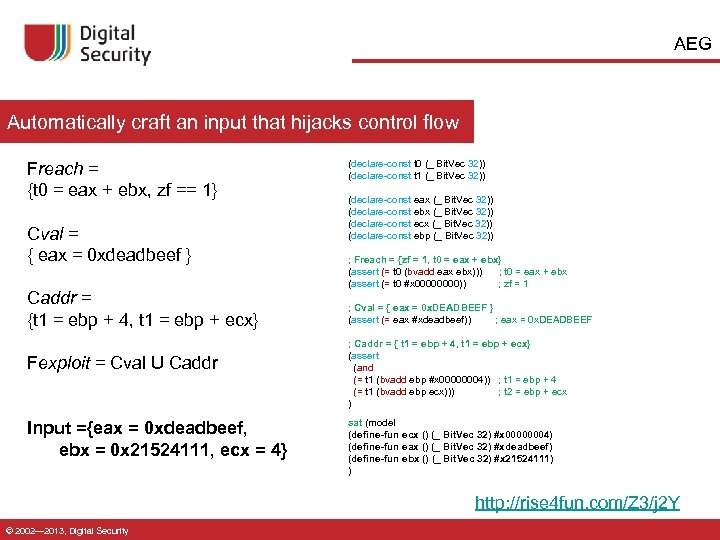 AEG Automatically craft an input that hijacks control flow Freach = {t 0 = eax + ebx, zf == 1} Cval = { eax = 0 xdeadbeef } Caddr = {t 1 = ebp + 4, t 1 = ebp + ecx} Fexploit = Cval U Caddr Input ={eax = 0 xdeadbeef, ebx = 0 x 21524111, ecx = 4} (declare-const t 0 (_ Bit. Vec 32)) (declare-const t 1 (_ Bit. Vec 32)) (declare-const eax (_ Bit. Vec 32)) (declare-const ebx (_ Bit. Vec 32)) (declare-const ecx (_ Bit. Vec 32)) (declare-const ebp (_ Bit. Vec 32)) ; Freach = {zf = 1, t 0 = eax + ebx} (assert (= t 0 (bvadd eax ebx))) ; t 0 = eax + ebx (assert (= t 0 #x 0000)) ; zf = 1 ; Cval = { eax = 0 x. DEADBEEF } (assert (= eax #xdeadbeef)) ; eax = 0 x. DEADBEEF ; Caddr = { t 1 = ebp + 4, t 1 = ebp + ecx} (assert (and (= t 1 (bvadd ebp #x 00000004)) ; t 1 = ebp + 4 (= t 1 (bvadd ebp ecx))) ; t 2 = ebp + ecx ) sat (model (define-fun ecx () (_ Bit. Vec 32) #x 00000004) (define-fun eax () (_ Bit. Vec 32) #xdeadbeef) (define-fun ebx () (_ Bit. Vec 32) #x 21524111) ) http: //rise 4 fun. com/Z 3/j 2 Y © 2002— 2013, Digital Security
AEG Automatically craft an input that hijacks control flow Freach = {t 0 = eax + ebx, zf == 1} Cval = { eax = 0 xdeadbeef } Caddr = {t 1 = ebp + 4, t 1 = ebp + ecx} Fexploit = Cval U Caddr Input ={eax = 0 xdeadbeef, ebx = 0 x 21524111, ecx = 4} (declare-const t 0 (_ Bit. Vec 32)) (declare-const t 1 (_ Bit. Vec 32)) (declare-const eax (_ Bit. Vec 32)) (declare-const ebx (_ Bit. Vec 32)) (declare-const ecx (_ Bit. Vec 32)) (declare-const ebp (_ Bit. Vec 32)) ; Freach = {zf = 1, t 0 = eax + ebx} (assert (= t 0 (bvadd eax ebx))) ; t 0 = eax + ebx (assert (= t 0 #x 0000)) ; zf = 1 ; Cval = { eax = 0 x. DEADBEEF } (assert (= eax #xdeadbeef)) ; eax = 0 x. DEADBEEF ; Caddr = { t 1 = ebp + 4, t 1 = ebp + ecx} (assert (and (= t 1 (bvadd ebp #x 00000004)) ; t 1 = ebp + 4 (= t 1 (bvadd ebp ecx))) ; t 2 = ebp + ecx ) sat (model (define-fun ecx () (_ Bit. Vec 32) #x 00000004) (define-fun eax () (_ Bit. Vec 32) #xdeadbeef) (define-fun ebx () (_ Bit. Vec 32) #x 21524111) ) http: //rise 4 fun. com/Z 3/j 2 Y © 2002— 2013, Digital Security
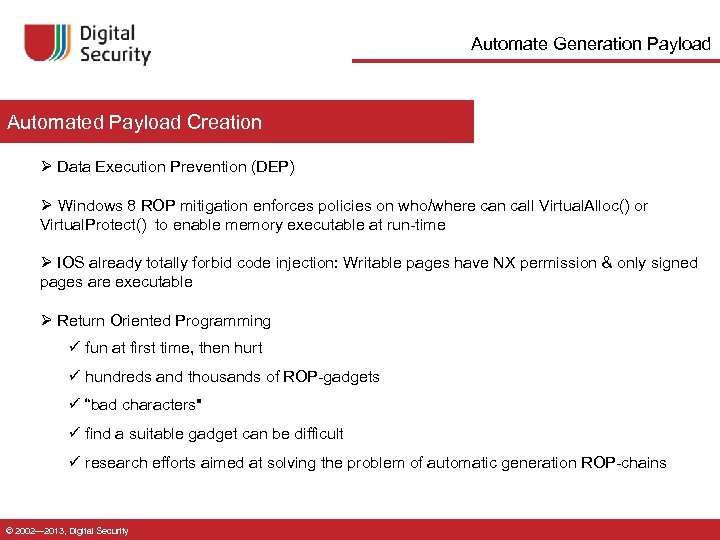 Automate Generation Payload Automated Payload Creation Ø Data Execution Prevention (DEP) Ø Windows 8 ROP mitigation enforces policies on who/where can call Virtual. Alloc() or Virtual. Protect() to enable memory executable at run-time Ø IOS already totally forbid code injection: Writable pages have NX permission & only signed pages are executable Ø Return Oriented Programming ü fun at first time, then hurt ü hundreds and thousands of ROP-gadgets ü “bad characters" ü find a suitable gadget can be difficult ü research efforts aimed at solving the problem of automatic generation ROP-chains © 2002— 2013, Digital Security
Automate Generation Payload Automated Payload Creation Ø Data Execution Prevention (DEP) Ø Windows 8 ROP mitigation enforces policies on who/where can call Virtual. Alloc() or Virtual. Protect() to enable memory executable at run-time Ø IOS already totally forbid code injection: Writable pages have NX permission & only signed pages are executable Ø Return Oriented Programming ü fun at first time, then hurt ü hundreds and thousands of ROP-gadgets ü “bad characters" ü find a suitable gadget can be difficult ü research efforts aimed at solving the problem of automatic generation ROP-chains © 2002— 2013, Digital Security
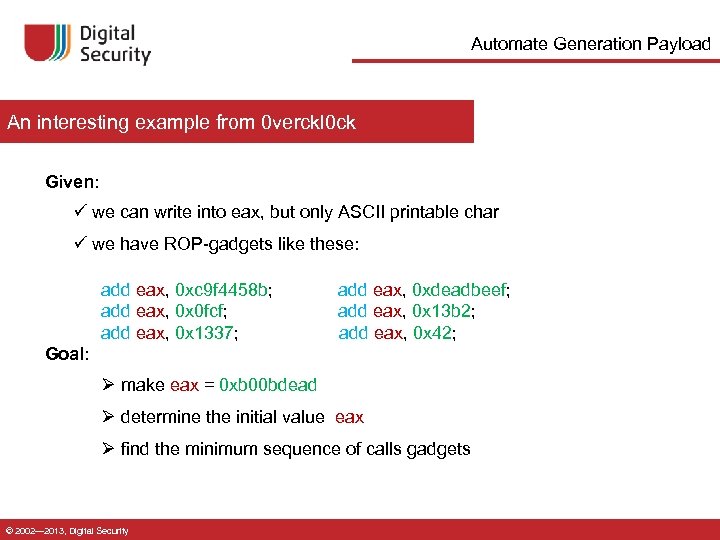 Automate Generation Payload An interesting example from 0 verckl 0 ck Given: ü we can write into eax, but only ASCII printable char ü we have ROP-gadgets like these: add eax, 0 xc 9 f 4458 b; add eax, 0 xdeadbeef; add eax, 0 x 0 fcf; add eax, 0 x 13 b 2; add eax, 0 x 1337; add eax, 0 x 42; Goal: Ø make eax = 0 xb 00 bdead Ø determine the initial value eax Ø find the minimum sequence of calls gadgets © 2002— 2013, Digital Security
Automate Generation Payload An interesting example from 0 verckl 0 ck Given: ü we can write into eax, but only ASCII printable char ü we have ROP-gadgets like these: add eax, 0 xc 9 f 4458 b; add eax, 0 xdeadbeef; add eax, 0 x 0 fcf; add eax, 0 x 13 b 2; add eax, 0 x 1337; add eax, 0 x 42; Goal: Ø make eax = 0 xb 00 bdead Ø determine the initial value eax Ø find the minimum sequence of calls gadgets © 2002— 2013, Digital Security
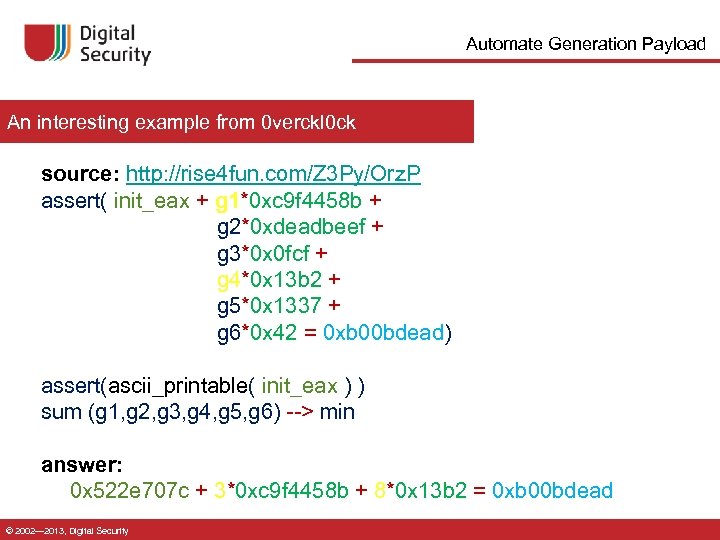 Automate Generation Payload An interesting example from 0 verckl 0 ck source: http: //rise 4 fun. com/Z 3 Py/Orz. P assert( init_eax + g 1*0 xc 9 f 4458 b + g 2*0 xdeadbeef + g 3*0 x 0 fcf + g 4*0 x 13 b 2 + g 5*0 x 1337 + g 6*0 x 42 = 0 xb 00 bdead) assert(ascii_printable( init_eax ) ) sum (g 1, g 2, g 3, g 4, g 5, g 6) --> min answer: 0 x 522 e 707 c + 3*0 xc 9 f 4458 b + 8*0 x 13 b 2 = 0 xb 00 bdead © 2002— 2013, Digital Security
Automate Generation Payload An interesting example from 0 verckl 0 ck source: http: //rise 4 fun. com/Z 3 Py/Orz. P assert( init_eax + g 1*0 xc 9 f 4458 b + g 2*0 xdeadbeef + g 3*0 x 0 fcf + g 4*0 x 13 b 2 + g 5*0 x 1337 + g 6*0 x 42 = 0 xb 00 bdead) assert(ascii_printable( init_eax ) ) sum (g 1, g 2, g 3, g 4, g 5, g 6) --> min answer: 0 x 522 e 707 c + 3*0 xc 9 f 4458 b + 8*0 x 13 b 2 = 0 xb 00 bdead © 2002— 2013, Digital Security
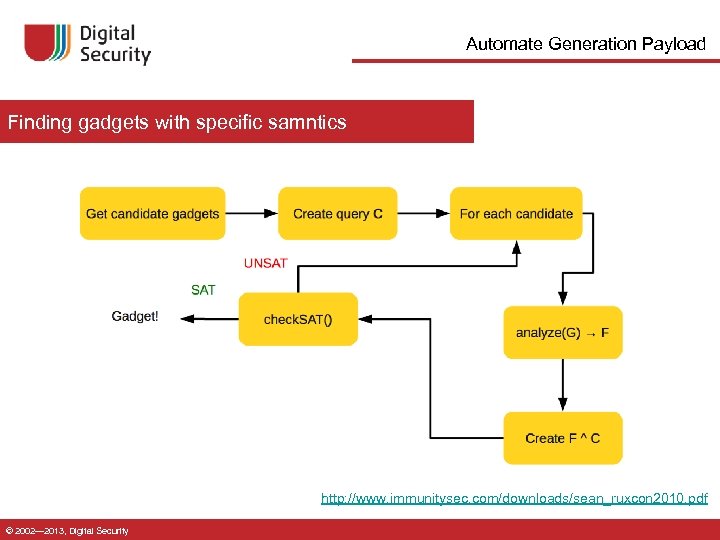 Automate Generation Payload Finding gadgets with specific samntics http: //www. immunitysec. com/downloads/sean_ruxcon 2010. pdf © 2002— 2013, Digital Security
Automate Generation Payload Finding gadgets with specific samntics http: //www. immunitysec. com/downloads/sean_ruxcon 2010. pdf © 2002— 2013, Digital Security
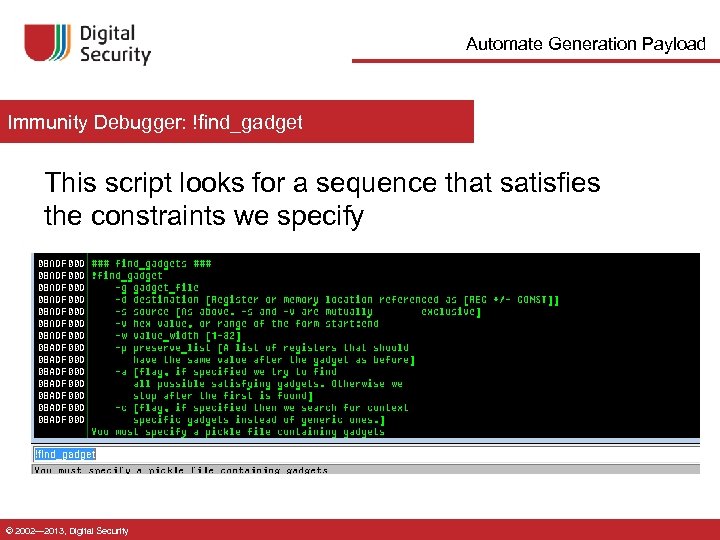 Automate Generation Payload Immunity Debugger: !find_gadget This script looks for a sequence that satisfies the constraints we specify © 2002— 2013, Digital Security
Automate Generation Payload Immunity Debugger: !find_gadget This script looks for a sequence that satisfies the constraints we specify © 2002— 2013, Digital Security
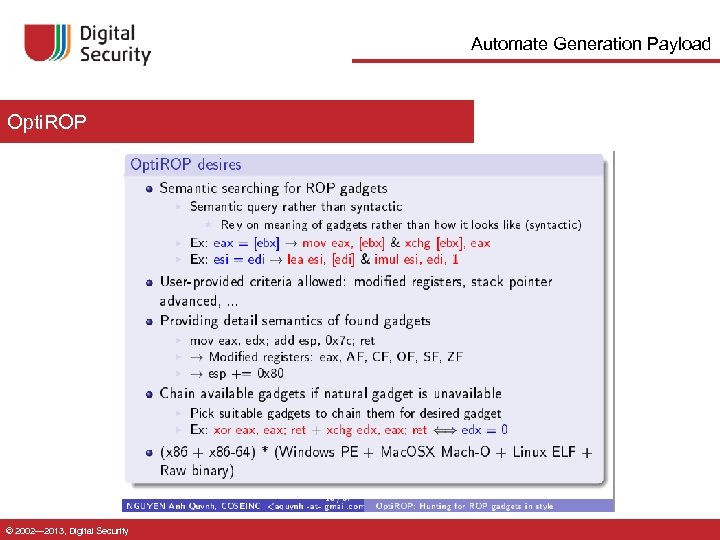 Automate Generation Payload Opti. ROP © 2002— 2013, Digital Security
Automate Generation Payload Opti. ROP © 2002— 2013, Digital Security
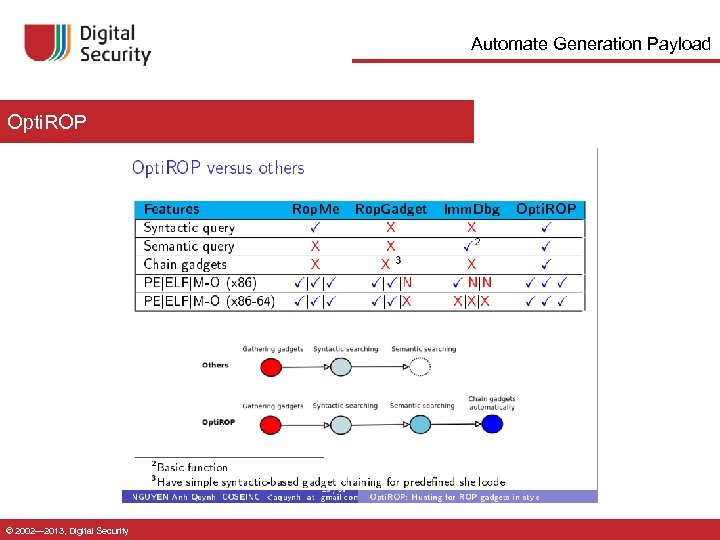 Automate Generation Payload Opti. ROP © 2002— 2013, Digital Security
Automate Generation Payload Opti. ROP © 2002— 2013, Digital Security
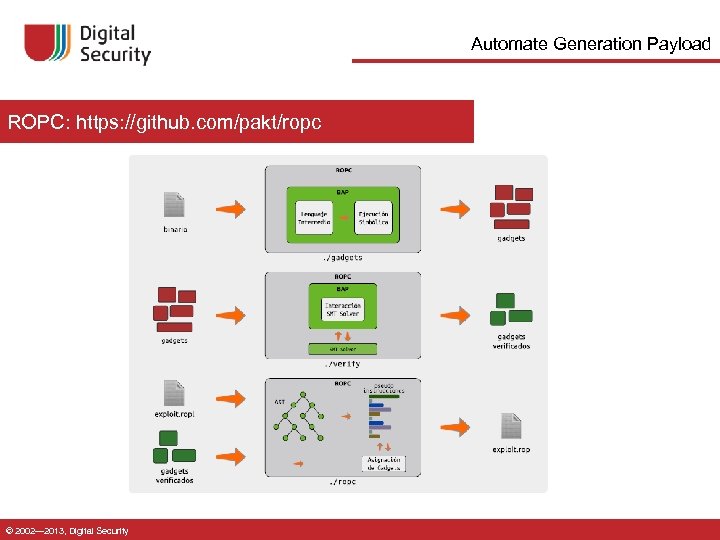 Automate Generation Payload ROPC: https: //github. com/pakt/ropc © 2002— 2013, Digital Security
Automate Generation Payload ROPC: https: //github. com/pakt/ropc © 2002— 2013, Digital Security
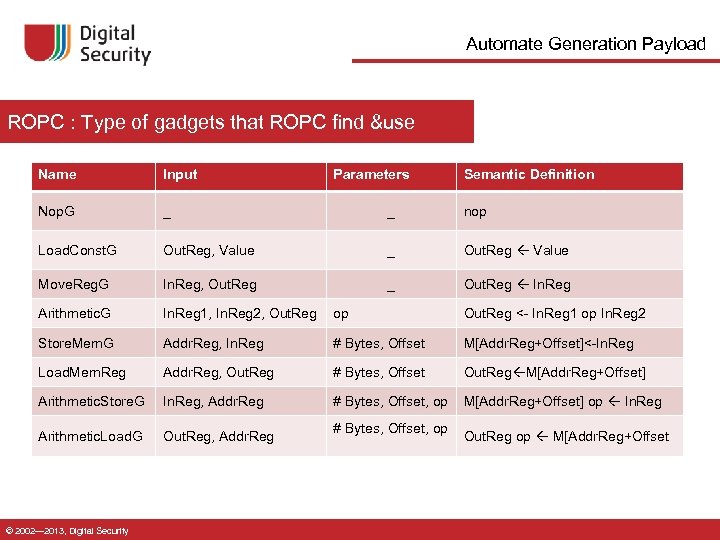 Automate Generation Payload ROPC : Type of gadgets that ROPC find &use Name Input Nop. G _ _ nop Load. Const. G Out. Reg, Value _ Out. Reg Value Move. Reg. G In. Reg, Out. Reg _ Out. Reg In. Reg Arithmetic. G In. Reg 1, In. Reg 2, Out. Reg op Out. Reg <- In. Reg 1 op In. Reg 2 Store. Mem. G Addr. Reg, In. Reg # Bytes, Offset M[Addr. Reg+Offset]<-In. Reg Load. Mem. Reg Addr. Reg, Out. Reg # Bytes, Offset Out. Reg M[Addr. Reg+Offset] Arithmetic. Store. G In. Reg, Addr. Reg # Bytes, Offset, op M[Addr. Reg+Offset] op In. Reg Arithmetic. Load. G Out. Reg, Addr. Reg © 2002— 2013, Digital Security Parameters # Bytes, Offset, op Semantic Definition Out. Reg op M[Addr. Reg+Offset
Automate Generation Payload ROPC : Type of gadgets that ROPC find &use Name Input Nop. G _ _ nop Load. Const. G Out. Reg, Value _ Out. Reg Value Move. Reg. G In. Reg, Out. Reg _ Out. Reg In. Reg Arithmetic. G In. Reg 1, In. Reg 2, Out. Reg op Out. Reg <- In. Reg 1 op In. Reg 2 Store. Mem. G Addr. Reg, In. Reg # Bytes, Offset M[Addr. Reg+Offset]<-In. Reg Load. Mem. Reg Addr. Reg, Out. Reg # Bytes, Offset Out. Reg M[Addr. Reg+Offset] Arithmetic. Store. G In. Reg, Addr. Reg # Bytes, Offset, op M[Addr. Reg+Offset] op In. Reg Arithmetic. Load. G Out. Reg, Addr. Reg © 2002— 2013, Digital Security Parameters # Bytes, Offset, op Semantic Definition Out. Reg op M[Addr. Reg+Offset
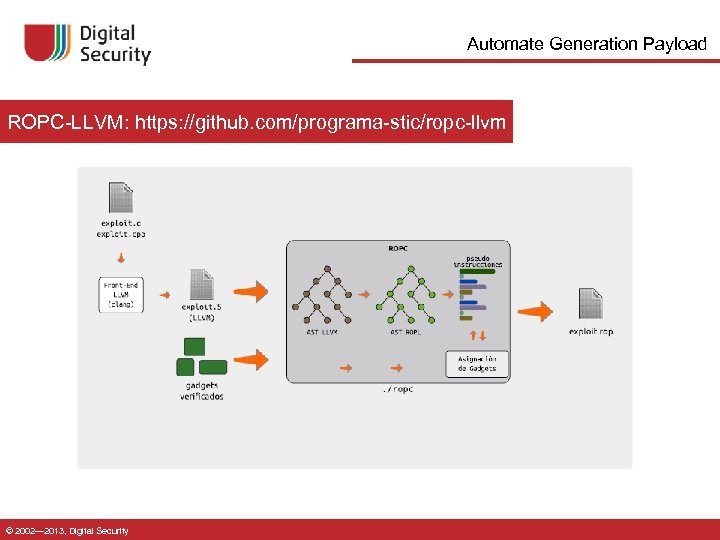 Automate Generation Payload ROPC-LLVM: https: //github. com/programa-stic/ropc-llvm © 2002— 2013, Digital Security
Automate Generation Payload ROPC-LLVM: https: //github. com/programa-stic/ropc-llvm © 2002— 2013, Digital Security
 SMT Solvers for Software Security Questions ? © 2002— 2013, Digital Security
SMT Solvers for Software Security Questions ? © 2002— 2013, Digital Security


