a498bf2ab4aca0081408d7c213daa276.ppt
- Количество слайдов: 55
 Setting up SAFEGUARD: Safe and Easy A Users Perspective Carl Weber Green. House Software & Consulting 14 Oct 2003, 14: 45 – 15: 45 MEA-18 -U, Room C 1/2
Setting up SAFEGUARD: Safe and Easy A Users Perspective Carl Weber Green. House Software & Consulting 14 Oct 2003, 14: 45 – 15: 45 MEA-18 -U, Room C 1/2
 And you think you have stress…
And you think you have stress…
 Brief Intro Carl Weber l l 7 years of process computer background prior to Tandem (HW & SW) Started with Tandem Germany 1978 First cryptographic TAL procedure written in 1979 (causing 1 st trouble with the US…) First contact to SAFEGUARD in 1985 (known as OBI at that time; ask Tim Chou…) l Since 1985 product responsibility for all security related Tandem products in Germany
Brief Intro Carl Weber l l 7 years of process computer background prior to Tandem (HW & SW) Started with Tandem Germany 1978 First cryptographic TAL procedure written in 1979 (causing 1 st trouble with the US…) First contact to SAFEGUARD in 1985 (known as OBI at that time; ask Tim Chou…) l Since 1985 product responsibility for all security related Tandem products in Germany
 Brief Intro Carl Weber l l l Management of the two successful system evaluations at GISA (German Information Security Agency) 1989 and 1993 Participation in the NCSC evaluation incl. ceremony in Baltimore (1993) Left Tandem 1994 and started Green. House as Alliance Partner, specialized in - Security Tools and Products - Security Consulting & Education (from policy development up to implementation) - System programming (TAL/p. TAL, PRIV code)
Brief Intro Carl Weber l l l Management of the two successful system evaluations at GISA (German Information Security Agency) 1989 and 1993 Participation in the NCSC evaluation incl. ceremony in Baltimore (1993) Left Tandem 1994 and started Green. House as Alliance Partner, specialized in - Security Tools and Products - Security Consulting & Education (from policy development up to implementation) - System programming (TAL/p. TAL, PRIV code)
 Brief Intro Carl Weber l I still maintain a close contact to Cupertino and the SAFEGUARD development group by - E-Mail - At least a yearly visit in Cupertino
Brief Intro Carl Weber l I still maintain a close contact to Cupertino and the SAFEGUARD development group by - E-Mail - At least a yearly visit in Cupertino
 Brief Intro Green. House l Green. House runs a K 122 and S 7000, connected by EXPAND over IP (Itanium system is planned for end 2004) l l Using most recent versions of GUARDIAN/NSK/OSS Investment necessary to offer good quality, services, and products (you need the right tools to do a good job!)
Brief Intro Green. House l Green. House runs a K 122 and S 7000, connected by EXPAND over IP (Itanium system is planned for end 2004) l l Using most recent versions of GUARDIAN/NSK/OSS Investment necessary to offer good quality, services, and products (you need the right tools to do a good job!)
 SAFEGUARD History l Development triggered in 1984 by: - Security Pacific Bank, LA - Do. D agencies (indirect) - Roy Capaldo, Tandem (driving force Marketing) - Tim Chou, Tandem (technical expert, designer) with the target of reaching C 2 equivalent security functionality
SAFEGUARD History l Development triggered in 1984 by: - Security Pacific Bank, LA - Do. D agencies (indirect) - Roy Capaldo, Tandem (driving force Marketing) - Tim Chou, Tandem (technical expert, designer) with the target of reaching C 2 equivalent security functionality
 SAFEGUARD History l Original development team: - Tim Chou, product and code design, coding, ‘heavy lifting’ - Bill Lamb, developed SAFECOM; later owner of entire code Newton, manuals - Tim - Ian Earnest, QA - Matt Mathews, education - Kevin Coughlin, support - many more, part time from other development areas
SAFEGUARD History l Original development team: - Tim Chou, product and code design, coding, ‘heavy lifting’ - Bill Lamb, developed SAFECOM; later owner of entire code Newton, manuals - Tim - Ian Earnest, QA - Matt Mathews, education - Kevin Coughlin, support - many more, part time from other development areas
 SAFEGUARD History l l Bill Lamb still is in charge of SAFEGUARD He is around – talk to him to get more insight information!
SAFEGUARD History l l Bill Lamb still is in charge of SAFEGUARD He is around – talk to him to get more insight information!
 General Security Statement l Security is another word for - Arrangement - Order - Organization
General Security Statement l Security is another word for - Arrangement - Order - Organization
 General Security Statement l Identify Assets and Threats l Topics to plan: - Awareness (assessment of what assets are at risk ) - Accountability (who owns the asset and who needs access ) - Appropriateness (what level of access and degree of auditing is needed ) - Education (NOT product education, but: Why do we do security)
General Security Statement l Identify Assets and Threats l Topics to plan: - Awareness (assessment of what assets are at risk ) - Accountability (who owns the asset and who needs access ) - Appropriateness (what level of access and degree of auditing is needed ) - Education (NOT product education, but: Why do we do security)
 General Security Statement l l Have a Plan (Security Policy) describing the target to reach It is a generic plan, fitting all platforms in your company! It is a one page thing! It needs to be approved by the board of directors!
General Security Statement l l Have a Plan (Security Policy) describing the target to reach It is a generic plan, fitting all platforms in your company! It is a one page thing! It needs to be approved by the board of directors!
 General Security Statement l l Make a Plan describing the way to go Before installing mechanisms, bring order into your system e. g. introduce and follow naming conventions l Relate Security Functions to persons
General Security Statement l l Make a Plan describing the way to go Before installing mechanisms, bring order into your system e. g. introduce and follow naming conventions l Relate Security Functions to persons
 General Security Statement l Educate your employees NOT product usage, but WHY you are doing it!
General Security Statement l Educate your employees NOT product usage, but WHY you are doing it!
 General Security Statement l No Plan(s) – No Security!
General Security Statement l No Plan(s) – No Security!
 General Security Statement l l SAFEGUARD is a tool to enforce order on your system It does NOT bring more security, but more granularity and new functionality! (an error 48 from GUARDIAN is as solid as an error 48 from SAFEGUARD!) l Use SAFEGUARD and its features with sense of proportion
General Security Statement l l SAFEGUARD is a tool to enforce order on your system It does NOT bring more security, but more granularity and new functionality! (an error 48 from GUARDIAN is as solid as an error 48 from SAFEGUARD!) l Use SAFEGUARD and its features with sense of proportion
 General Security Statement l l In case GUARDIAN security solves your requirements, do NOT add SAFEGUARD rules (ACLs)! Introducing and activating SAFEGUARD is: - 99% decision making (make the plan!) (who owns what; who needs access; who is responsible, etc. ) - 1% real work with SAFECOM (normally the creation and execution of an OBEY file)
General Security Statement l l In case GUARDIAN security solves your requirements, do NOT add SAFEGUARD rules (ACLs)! Introducing and activating SAFEGUARD is: - 99% decision making (make the plan!) (who owns what; who needs access; who is responsible, etc. ) - 1% real work with SAFECOM (normally the creation and execution of an OBEY file)
 SAFEGUARD l SAFEGUARD covers these functions: - Authentication (more than GUARDIAN) - Authorization (more than GUARDIAN) - Auditing (new) - Administration (much more than GUARDIAN)
SAFEGUARD l SAFEGUARD covers these functions: - Authentication (more than GUARDIAN) - Authorization (more than GUARDIAN) - Auditing (new) - Administration (much more than GUARDIAN)
 SAFEGUARD l Purchasing SAFEGUARD and paying a yearly license fee does NOT secure your system! l You have to - Run - Configure and - Maintain SAFEGUARD as well!
SAFEGUARD l Purchasing SAFEGUARD and paying a yearly license fee does NOT secure your system! l You have to - Run - Configure and - Maintain SAFEGUARD as well!
 Running SAFEGUARD l Methods to run SAFEGUARD - Started ‘by hand’ (strongly recommended for beginners) - Through the CIIN file at system cold load time (OK for experts; satisfies 99% of all customers) - Generated into the OS (sysgened) (only needed in high risk shops; may cause outages)
Running SAFEGUARD l Methods to run SAFEGUARD - Started ‘by hand’ (strongly recommended for beginners) - Through the CIIN file at system cold load time (OK for experts; satisfies 99% of all customers) - Generated into the OS (sysgened) (only needed in high risk shops; may cause outages)
![Running SAFEGUARD l Command: [run] OSMP/NAME $ZSMP, NOWAIT, PRI 199, CPU 0/1 l This Running SAFEGUARD l Command: [run] OSMP/NAME $ZSMP, NOWAIT, PRI 199, CPU 0/1 l This](https://present5.com/presentation/a498bf2ab4aca0081408d7c213daa276/image-21.jpg) Running SAFEGUARD l Command: [run] OSMP/NAME $ZSMP, NOWAIT, PRI 199, CPU 0/1 l This creates the $ZSMP monitor process as well as $ZSnn processes, and - activates all SAFEGUARD default settings or - configured settings!
Running SAFEGUARD l Command: [run] OSMP/NAME $ZSMP, NOWAIT, PRI 199, CPU 0/1 l This creates the $ZSMP monitor process as well as $ZSnn processes, and - activates all SAFEGUARD default settings or - configured settings!
 Configuring SAFEGUARD l l l Configuring SAFEGUARD is essential SAFEGUARD without, or with insufficient, configuration is a massive security breach! Configuration areas are: - Management rights - Global settings - Audit file handling - Access Control Lists (ACL)
Configuring SAFEGUARD l l l Configuring SAFEGUARD is essential SAFEGUARD without, or with insufficient, configuration is a massive security breach! Configuration areas are: - Management rights - Global settings - Audit file handling - Access Control Lists (ACL)
 Configuring SAFEGUARD Management l SAFEGUARD has its own internal security system, allowing different persons to manage - SAFEGUARD management - SAFEGUARD global configuration attributes - Users - Access rights (ACLs)
Configuring SAFEGUARD Management l SAFEGUARD has its own internal security system, allowing different persons to manage - SAFEGUARD management - SAFEGUARD global configuration attributes - Users - Access rights (ACLs)
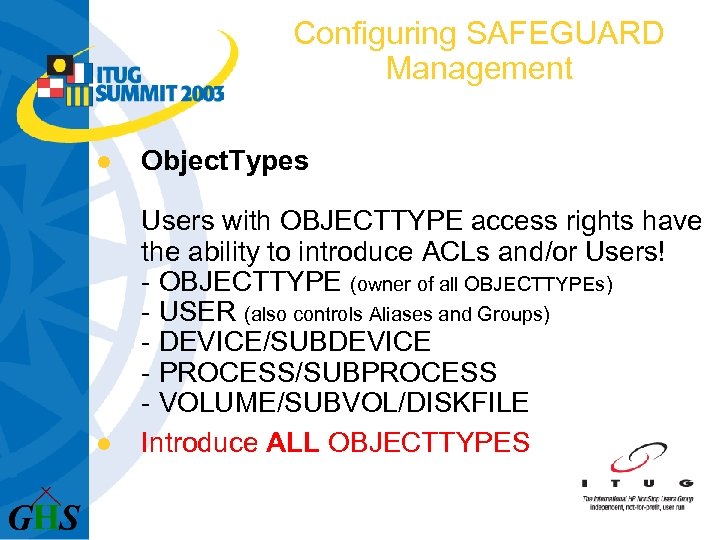 Configuring SAFEGUARD Management l Object. Types l Users with OBJECTTYPE access rights have the ability to introduce ACLs and/or Users! - OBJECTTYPE (owner of all OBJECTTYPEs) - USER (also controls Aliases and Groups) - DEVICE/SUBDEVICE - PROCESS/SUBPROCESS - VOLUME/SUBVOL/DISKFILE Introduce ALL OBJECTTYPES
Configuring SAFEGUARD Management l Object. Types l Users with OBJECTTYPE access rights have the ability to introduce ACLs and/or Users! - OBJECTTYPE (owner of all OBJECTTYPEs) - USER (also controls Aliases and Groups) - DEVICE/SUBDEVICE - PROCESS/SUBPROCESS - VOLUME/SUBVOL/DISKFILE Introduce ALL OBJECTTYPES
 Configuring SAFEGUARD Management l Security Groups Security Group users have management access rights in SAFEGUARD l Introduce the two Security Groups - System-Operator - Security-Administrator
Configuring SAFEGUARD Management l Security Groups Security Group users have management access rights in SAFEGUARD l Introduce the two Security Groups - System-Operator - Security-Administrator
 Configuring SAFEGUARD Audit Service l Audit System Allows definition of - audit service management - audit file handling - audit file size and location
Configuring SAFEGUARD Audit Service l Audit System Allows definition of - audit service management - audit file handling - audit file size and location
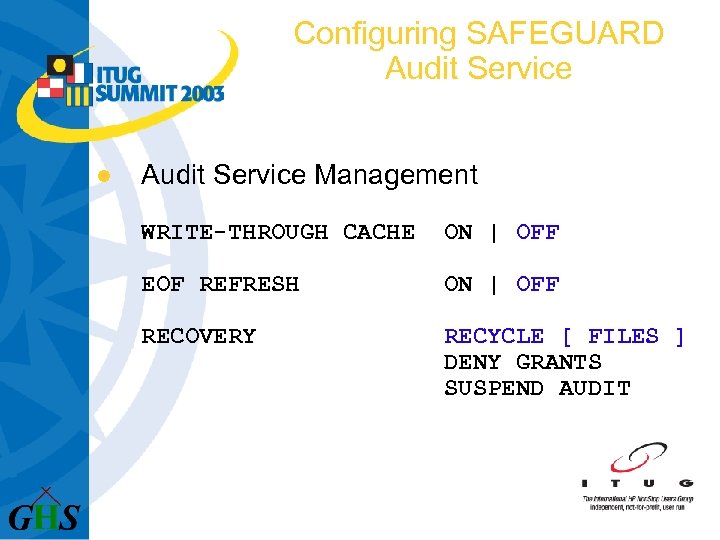 Configuring SAFEGUARD Audit Service l Audit Service Management WRITE-THROUGH CACHE ON | OFF EOF REFRESH ON | OFF RECOVERY RECYCLE [ FILES ] DENY GRANTS SUSPEND AUDIT
Configuring SAFEGUARD Audit Service l Audit Service Management WRITE-THROUGH CACHE ON | OFF EOF REFRESH ON | OFF RECOVERY RECYCLE [ FILES ] DENY GRANTS SUSPEND AUDIT
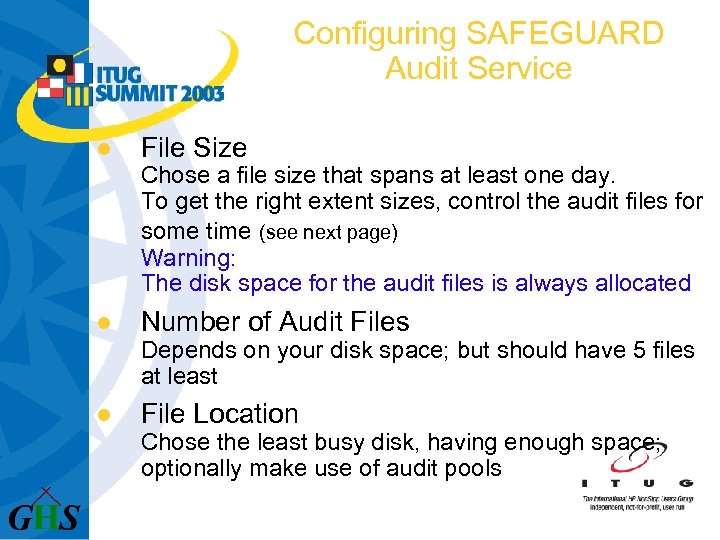 Configuring SAFEGUARD Audit Service l File Size Chose a file size that spans at least one day. To get the right extent sizes, control the audit files for some time (see next page) Warning: The disk space for the audit files is always allocated l Number of Audit Files Depends on your disk space; but should have 5 files at least l File Location Chose the least busy disk, having enough space; optionally make use of audit pools
Configuring SAFEGUARD Audit Service l File Size Chose a file size that spans at least one day. To get the right extent sizes, control the audit files for some time (see next page) Warning: The disk space for the audit files is always allocated l Number of Audit Files Depends on your disk space; but should have 5 files at least l File Location Chose the least busy disk, having enough space; optionally make use of audit pools
 Configuring SAFEGUARD Audit Service l l Auditing is some kind of religious question: - interested in fails (= hacks)? - interested in passes (= who really was it? ) Invoke your Audit department to get your company rules! When you audit events – CHECK the audits as well! Keep audit files for some time (e. g. tape backups for 3 months)
Configuring SAFEGUARD Audit Service l l Auditing is some kind of religious question: - interested in fails (= hacks)? - interested in passes (= who really was it? ) Invoke your Audit department to get your company rules! When you audit events – CHECK the audits as well! Keep audit files for some time (e. g. tape backups for 3 months)
 Configuring SAFEGUARD Global Settings l Global SAFEGUARD settings - Authentication attributes - Password attributes - ACL use and evaluation rules - Global CI - Global Auditing - Miscellaneous
Configuring SAFEGUARD Global Settings l Global SAFEGUARD settings - Authentication attributes - Password attributes - ACL use and evaluation rules - Global CI - Global Auditing - Miscellaneous
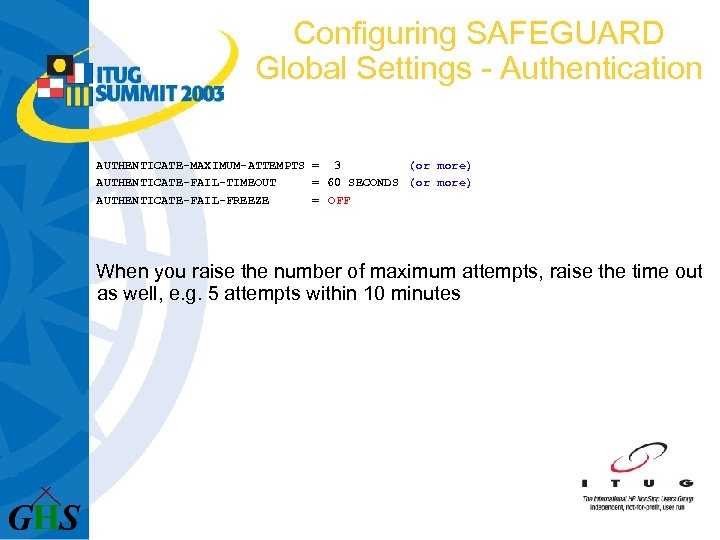 Configuring SAFEGUARD Global Settings - Authentication AUTHENTICATE-MAXIMUM-ATTEMPTS = 3 (or more) AUTHENTICATE-FAIL-TIMEOUT = 60 SECONDS (or more) AUTHENTICATE-FAIL-FREEZE = OFF When you raise the number of maximum attempts, raise the time out as well, e. g. 5 attempts within 10 minutes
Configuring SAFEGUARD Global Settings - Authentication AUTHENTICATE-MAXIMUM-ATTEMPTS = 3 (or more) AUTHENTICATE-FAIL-TIMEOUT = 60 SECONDS (or more) AUTHENTICATE-FAIL-FREEZE = OFF When you raise the number of maximum attempts, raise the time out as well, e. g. 5 attempts within 10 minutes
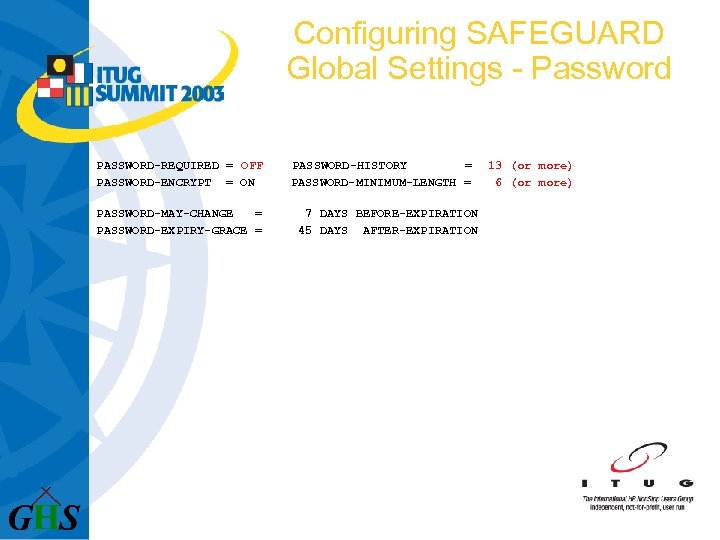 Configuring SAFEGUARD Global Settings - Password PASSWORD-REQUIRED = OFF PASSWORD-ENCRYPT = ON PASSWORD-MAY-CHANGE = PASSWORD-EXPIRY-GRACE = PASSWORD-HISTORY = PASSWORD-MINIMUM-LENGTH = 7 DAYS BEFORE-EXPIRATION 45 DAYS AFTER-EXPIRATION 13 (or more) 6 (or more)
Configuring SAFEGUARD Global Settings - Password PASSWORD-REQUIRED = OFF PASSWORD-ENCRYPT = ON PASSWORD-MAY-CHANGE = PASSWORD-EXPIRY-GRACE = PASSWORD-HISTORY = PASSWORD-MINIMUM-LENGTH = 7 DAYS BEFORE-EXPIRATION 45 DAYS AFTER-EXPIRATION 13 (or more) 6 (or more)
 Configuring SAFEGUARD Global Settings - Warning. Mode WARNING-MODE = OFF WARNING-FALLBACK-SECURITY = GUARDIAN
Configuring SAFEGUARD Global Settings - Warning. Mode WARNING-MODE = OFF WARNING-FALLBACK-SECURITY = GUARDIAN
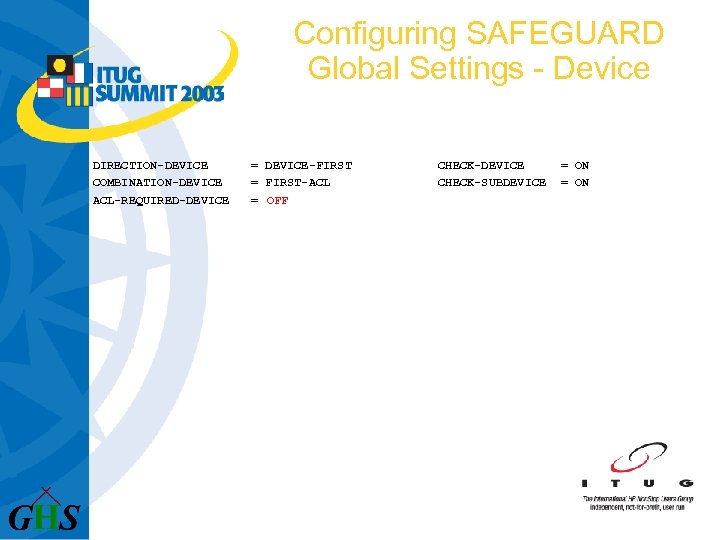 Configuring SAFEGUARD Global Settings - Device DIRECTION-DEVICE COMBINATION-DEVICE ACL-REQUIRED-DEVICE = DEVICE-FIRST = FIRST-ACL = OFF CHECK-DEVICE CHECK-SUBDEVICE = ON
Configuring SAFEGUARD Global Settings - Device DIRECTION-DEVICE COMBINATION-DEVICE ACL-REQUIRED-DEVICE = DEVICE-FIRST = FIRST-ACL = OFF CHECK-DEVICE CHECK-SUBDEVICE = ON
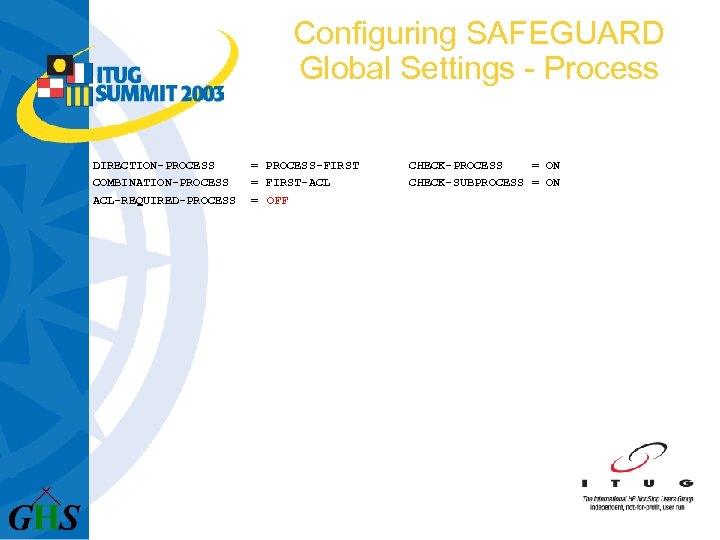 Configuring SAFEGUARD Global Settings - Process DIRECTION-PROCESS COMBINATION-PROCESS ACL-REQUIRED-PROCESS = PROCESS-FIRST = FIRST-ACL = OFF CHECK-PROCESS = ON CHECK-SUBPROCESS = ON
Configuring SAFEGUARD Global Settings - Process DIRECTION-PROCESS COMBINATION-PROCESS ACL-REQUIRED-PROCESS = PROCESS-FIRST = FIRST-ACL = OFF CHECK-PROCESS = ON CHECK-SUBPROCESS = ON
 Configuring SAFEGUARD Global Settings – Disk File DIRECTION-DISKFILE COMBINATION-DISKFILE ACL-REQUIRED-DISKFILE CLEARONPURGE-DISKFILE = = FILENAME-FIRST-ACL OFF CHECK-VOLUME CHECK-SUBVOLUME CHECK-FILENAME = OFF = ON
Configuring SAFEGUARD Global Settings – Disk File DIRECTION-DISKFILE COMBINATION-DISKFILE ACL-REQUIRED-DISKFILE CLEARONPURGE-DISKFILE = = FILENAME-FIRST-ACL OFF CHECK-VOLUME CHECK-SUBVOLUME CHECK-FILENAME = OFF = ON
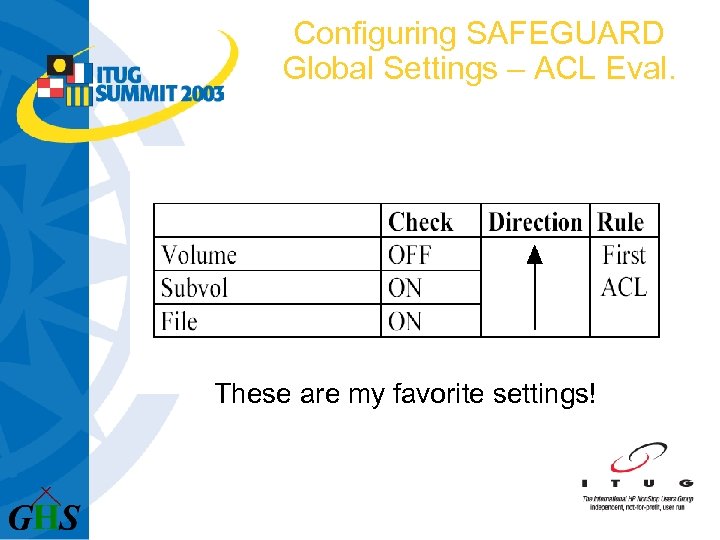 Configuring SAFEGUARD Global Settings – ACL Eval. These are my favorite settings!
Configuring SAFEGUARD Global Settings – ACL Eval. These are my favorite settings!
 Configuring SAFEGUARD Global Settings – ACL Eval. l These settings allow: - an easy understanding of ACLs - A clear structure - Protection against non allowed file and subvol creates
Configuring SAFEGUARD Global Settings – ACL Eval. l These settings allow: - an easy understanding of ACLs - A clear structure - Protection against non allowed file and subvol creates
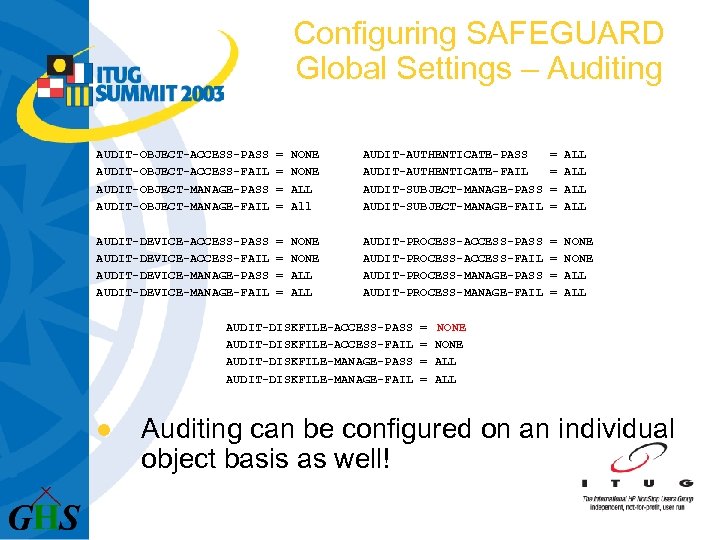 Configuring SAFEGUARD Global Settings – Auditing AUDIT-OBJECT-ACCESS-PASS AUDIT-OBJECT-ACCESS-FAIL AUDIT-OBJECT-MANAGE-PASS AUDIT-OBJECT-MANAGE-FAIL = = NONE ALL All AUDIT-AUTHENTICATE-PASS AUDIT-AUTHENTICATE-FAIL AUDIT-SUBJECT-MANAGE-PASS AUDIT-SUBJECT-MANAGE-FAIL = = ALL ALL AUDIT-DEVICE-ACCESS-PASS AUDIT-DEVICE-ACCESS-FAIL AUDIT-DEVICE-MANAGE-PASS AUDIT-DEVICE-MANAGE-FAIL = = NONE ALL AUDIT-PROCESS-ACCESS-PASS AUDIT-PROCESS-ACCESS-FAIL AUDIT-PROCESS-MANAGE-PASS AUDIT-PROCESS-MANAGE-FAIL = = NONE ALL AUDIT-DISKFILE-ACCESS-PASS AUDIT-DISKFILE-ACCESS-FAIL AUDIT-DISKFILE-MANAGE-PASS AUDIT-DISKFILE-MANAGE-FAIL l = = NONE ALL Auditing can be configured on an individual object basis as well!
Configuring SAFEGUARD Global Settings – Auditing AUDIT-OBJECT-ACCESS-PASS AUDIT-OBJECT-ACCESS-FAIL AUDIT-OBJECT-MANAGE-PASS AUDIT-OBJECT-MANAGE-FAIL = = NONE ALL All AUDIT-AUTHENTICATE-PASS AUDIT-AUTHENTICATE-FAIL AUDIT-SUBJECT-MANAGE-PASS AUDIT-SUBJECT-MANAGE-FAIL = = ALL ALL AUDIT-DEVICE-ACCESS-PASS AUDIT-DEVICE-ACCESS-FAIL AUDIT-DEVICE-MANAGE-PASS AUDIT-DEVICE-MANAGE-FAIL = = NONE ALL AUDIT-PROCESS-ACCESS-PASS AUDIT-PROCESS-ACCESS-FAIL AUDIT-PROCESS-MANAGE-PASS AUDIT-PROCESS-MANAGE-FAIL = = NONE ALL AUDIT-DISKFILE-ACCESS-PASS AUDIT-DISKFILE-ACCESS-FAIL AUDIT-DISKFILE-MANAGE-PASS AUDIT-DISKFILE-MANAGE-FAIL l = = NONE ALL Auditing can be configured on an individual object basis as well!
 Configuring SAFEGUARD Global Settings – Audit Client AUDIT-CLIENT-SERVICE = ON
Configuring SAFEGUARD Global Settings – Audit Client AUDIT-CLIENT-SERVICE = ON
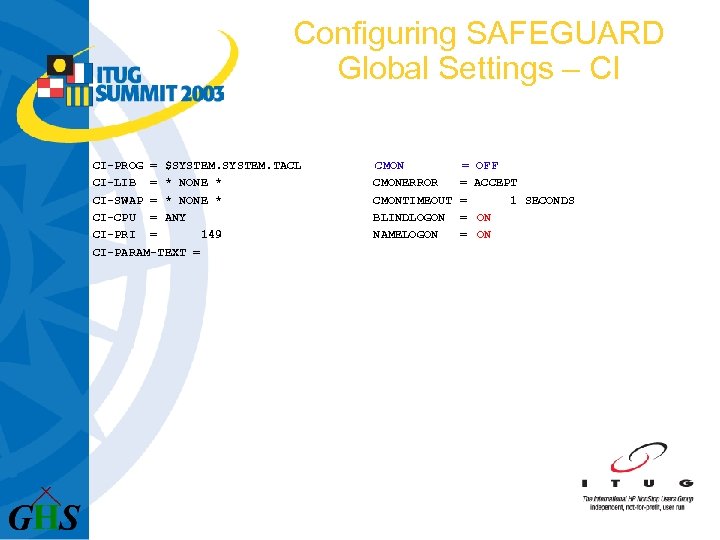 Configuring SAFEGUARD Global Settings – CI CI-PROG = $SYSTEM. TACL CI-LIB = * NONE * CI-SWAP = * NONE * CI-CPU = ANY CI-PRI = 149 CI-PARAM-TEXT = CMONERROR CMONTIMEOUT BLINDLOGON NAMELOGON = = = OFF ACCEPT 1 SECONDS ON ON
Configuring SAFEGUARD Global Settings – CI CI-PROG = $SYSTEM. TACL CI-LIB = * NONE * CI-SWAP = * NONE * CI-CPU = ANY CI-PRI = 149 CI-PARAM-TEXT = CMONERROR CMONTIMEOUT BLINDLOGON NAMELOGON = = = OFF ACCEPT 1 SECONDS ON ON
 Configuring SAFEGUARD Global Settings – Terminal TERMINAL-EXCLUSIVE-ACCESS = OFF
Configuring SAFEGUARD Global Settings – Terminal TERMINAL-EXCLUSIVE-ACCESS = OFF
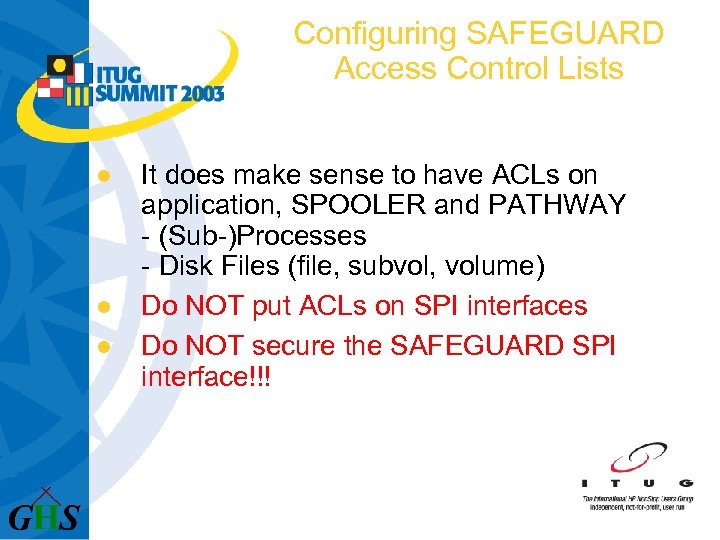 Configuring SAFEGUARD Access Control Lists l l l It does make sense to have ACLs on application, SPOOLER and PATHWAY - (Sub-)Processes - Disk Files (file, subvol, volume) Do NOT put ACLs on SPI interfaces Do NOT secure the SAFEGUARD SPI interface!!!
Configuring SAFEGUARD Access Control Lists l l l It does make sense to have ACLs on application, SPOOLER and PATHWAY - (Sub-)Processes - Disk Files (file, subvol, volume) Do NOT put ACLs on SPI interfaces Do NOT secure the SAFEGUARD SPI interface!!!
 Configuring SAFEGUARD Access Control Lists l l I don’t know of DEVICES to be secured, except - X. 25 lines - tape drives Use the highest possible level to minimize number of ACLs
Configuring SAFEGUARD Access Control Lists l l I don’t know of DEVICES to be secured, except - X. 25 lines - tape drives Use the highest possible level to minimize number of ACLs
 Configuring SAFEGUARD Access Control Lists l l Introduction of Terminals does make sense only with fixed named terminals. All other terminal types should use: $SYSTEM. LOGON as initial resource, or service (IP)
Configuring SAFEGUARD Access Control Lists l l Introduction of Terminals does make sense only with fixed named terminals. All other terminal types should use: $SYSTEM. LOGON as initial resource, or service (IP)
 Configuring SAFEGUARD Initial Command Interpreter l Initial Command Interpreter - Requires a SAFEGUARD controlled terminal - Can be defined - on the User (first check) - on the Terminal (next check) - globally (last check)
Configuring SAFEGUARD Initial Command Interpreter l Initial Command Interpreter - Requires a SAFEGUARD controlled terminal - Can be defined - on the User (first check) - on the Terminal (next check) - globally (last check)
 Configuring SAFEGUARD Initial Command Interpreter l Benefits: - A LOGON starts a pre-defined resource - the password handling can be done at logon time - LOGON- as well as LOGOFF-events are recorded
Configuring SAFEGUARD Initial Command Interpreter l Benefits: - A LOGON starts a pre-defined resource - the password handling can be done at logon time - LOGON- as well as LOGOFF-events are recorded
 Maintaining SAFEGUARD l l Never change global SAFEGUARD settings ‘on the fly’, or for test purposes: You for sure end up in big trouble! All that needs maintenance is: - Users (add, delete, alter) - ACLs (add, delete, alter) - Possibly Audit file sizes and locations - Rarely management rights
Maintaining SAFEGUARD l l Never change global SAFEGUARD settings ‘on the fly’, or for test purposes: You for sure end up in big trouble! All that needs maintenance is: - Users (add, delete, alter) - ACLs (add, delete, alter) - Possibly Audit file sizes and locations - Rarely management rights
 Conclusion l l Have a plan (Security Policy) in place BEFORE you start Relate security functions to persons Make a plan to run and configure SAFEGUARD Check audit information – at least keep it for some time (…for a post mortal analysis)
Conclusion l l Have a plan (Security Policy) in place BEFORE you start Relate security functions to persons Make a plan to run and configure SAFEGUARD Check audit information – at least keep it for some time (…for a post mortal analysis)
 Conclusion l Most important: Educate your employees! Not about security products, but about security as a method, and why you are going to use it!
Conclusion l Most important: Educate your employees! Not about security products, but about security as a method, and why you are going to use it!
 Conclusion Bad news l l Security costs - money - CPU cycles - disk space - time - nerves Security causes - trouble
Conclusion Bad news l l Security costs - money - CPU cycles - disk space - time - nerves Security causes - trouble
 Conclusion Good News l Security - gives you a system that is much easier to maintain - makes you sleep better ([not only] at home) - is worth the effort!
Conclusion Good News l Security - gives you a system that is much easier to maintain - makes you sleep better ([not only] at home) - is worth the effort!
 Helpful Gadgets l Check www. Green. House. de for supported Free. Ware and Share. Ware tools and products, making life with SAFEGUARD much easier! l Come to my tools presentation tomorrow at 11: 30 in this room (C 1)
Helpful Gadgets l Check www. Green. House. de for supported Free. Ware and Share. Ware tools and products, making life with SAFEGUARD much easier! l Come to my tools presentation tomorrow at 11: 30 in this room (C 1)
 l Questions? l (please. . . )
l Questions? l (please. . . )
 Thank you for your time and attention! Enjoy the conference!
Thank you for your time and attention! Enjoy the conference!


