8b0daecb308b21eae9189cf5e086dc74.ppt
- Количество слайдов: 50
 Security tools
Security tools
 Outline • • Firewalls and network design Honeybots IPTables Snort
Outline • • Firewalls and network design Honeybots IPTables Snort
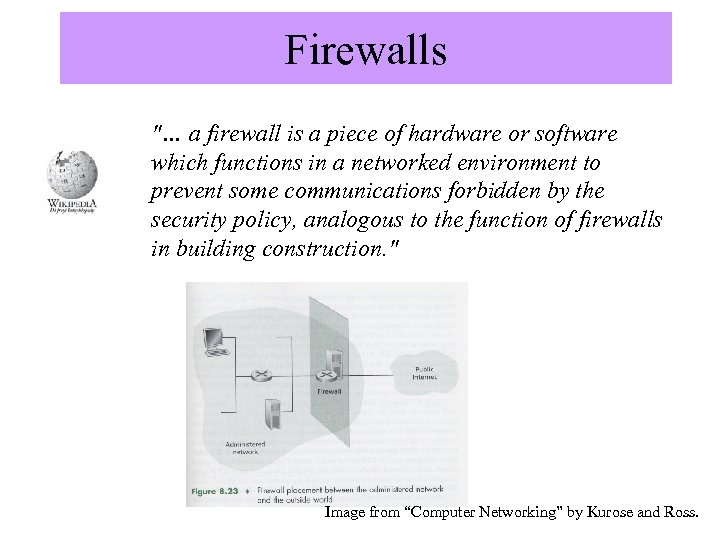 Firewalls "… a firewall is a piece of hardware or software which functions in a networked environment to prevent some communications forbidden by the security policy, analogous to the function of firewalls in building construction. " Image from “Computer Networking” by Kurose and Ross.
Firewalls "… a firewall is a piece of hardware or software which functions in a networked environment to prevent some communications forbidden by the security policy, analogous to the function of firewalls in building construction. " Image from “Computer Networking” by Kurose and Ross.
 Types of Firewalls • packet filtering gateways or screening routers • stateful inspection firewalls • application proxies • guards • personal firewalls From “Security in Computing” by Pfleeger and Pfleeger.
Types of Firewalls • packet filtering gateways or screening routers • stateful inspection firewalls • application proxies • guards • personal firewalls From “Security in Computing” by Pfleeger and Pfleeger.
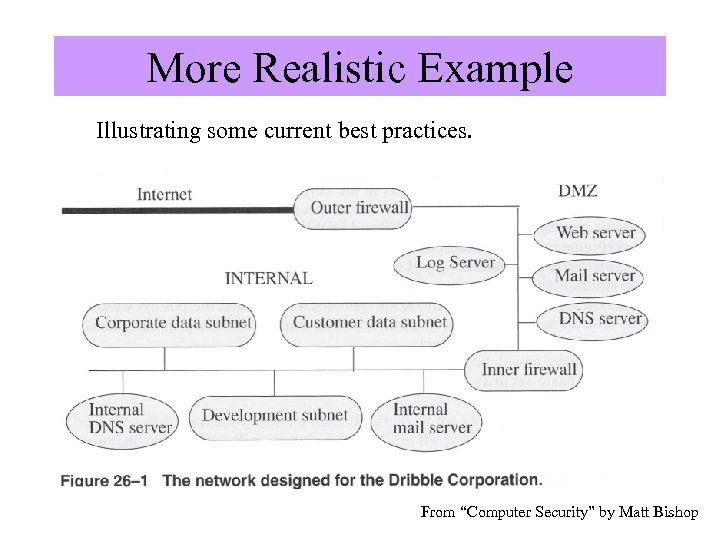 More Realistic Example Illustrating some current best practices. Image from “Computer Security” by Matt Bishop, Addison Wesley. From “Computer Security” by Matt Bishop
More Realistic Example Illustrating some current best practices. Image from “Computer Security” by Matt Bishop, Addison Wesley. From “Computer Security” by Matt Bishop
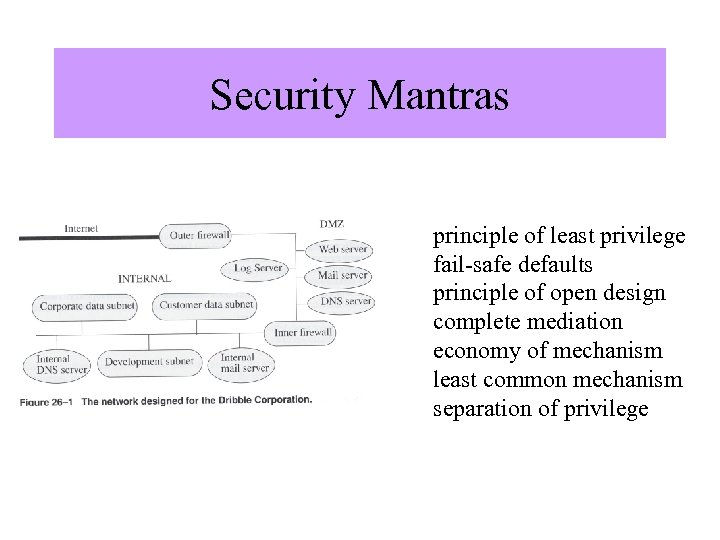 Security Mantras Image from “Computer Security” by Matt Bishop, Addison Wesley. principle of least privilege fail-safe defaults principle of open design complete mediation economy of mechanism least common mechanism separation of privilege
Security Mantras Image from “Computer Security” by Matt Bishop, Addison Wesley. principle of least privilege fail-safe defaults principle of open design complete mediation economy of mechanism least common mechanism separation of privilege
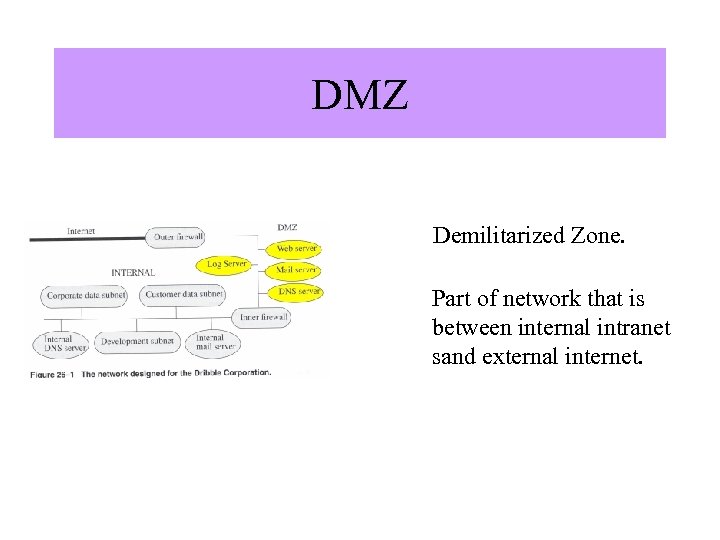 DMZ Demilitarized Zone. Image from “Computer Security” by Matt Bishop, Addison Wesley. Part of network that is between internal intranet sand external internet.
DMZ Demilitarized Zone. Image from “Computer Security” by Matt Bishop, Addison Wesley. Part of network that is between internal intranet sand external internet.
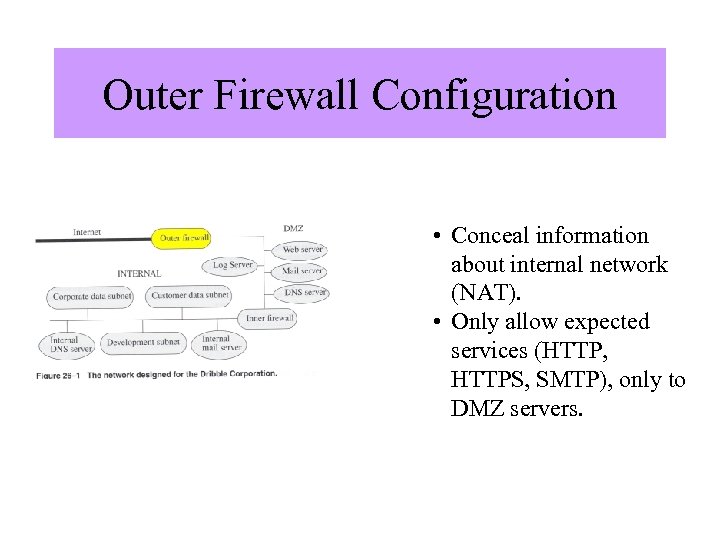 Outer Firewall Configuration Image from “Computer Security” by Matt Bishop, Addison Wesley. • Conceal information about internal network (NAT). • Only allow expected services (HTTP, HTTPS, SMTP), only to DMZ servers.
Outer Firewall Configuration Image from “Computer Security” by Matt Bishop, Addison Wesley. • Conceal information about internal network (NAT). • Only allow expected services (HTTP, HTTPS, SMTP), only to DMZ servers.
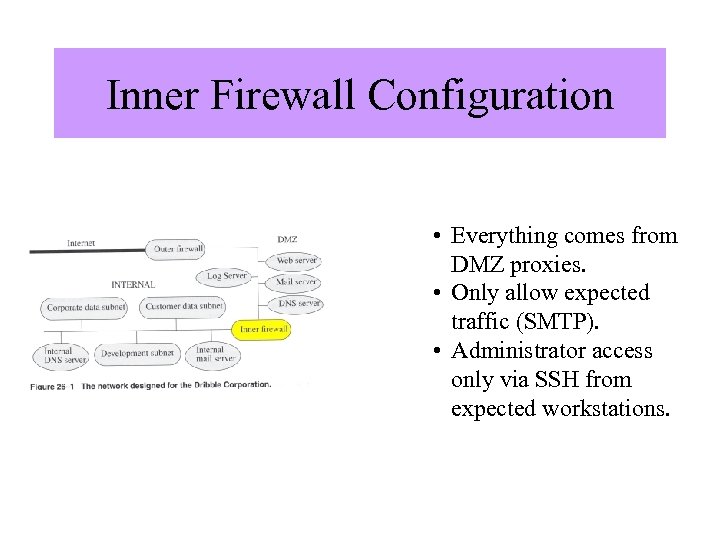 Inner Firewall Configuration Image from “Computer Security” by Matt Bishop, Addison Wesley. • Everything comes from DMZ proxies. • Only allow expected traffic (SMTP). • Administrator access only via SSH from expected workstations.
Inner Firewall Configuration Image from “Computer Security” by Matt Bishop, Addison Wesley. • Everything comes from DMZ proxies. • Only allow expected traffic (SMTP). • Administrator access only via SSH from expected workstations.
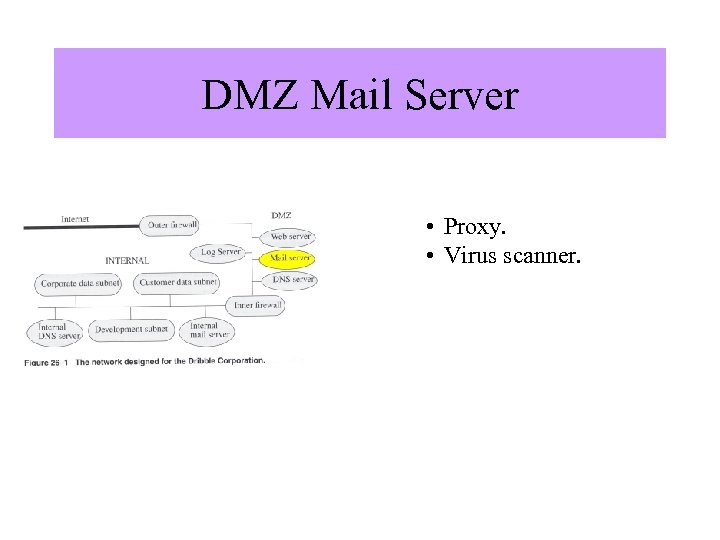 DMZ Mail Server Image from “Computer Security” by Matt Bishop, Addison Wesley. • Proxy. • Virus scanner.
DMZ Mail Server Image from “Computer Security” by Matt Bishop, Addison Wesley. • Proxy. • Virus scanner.
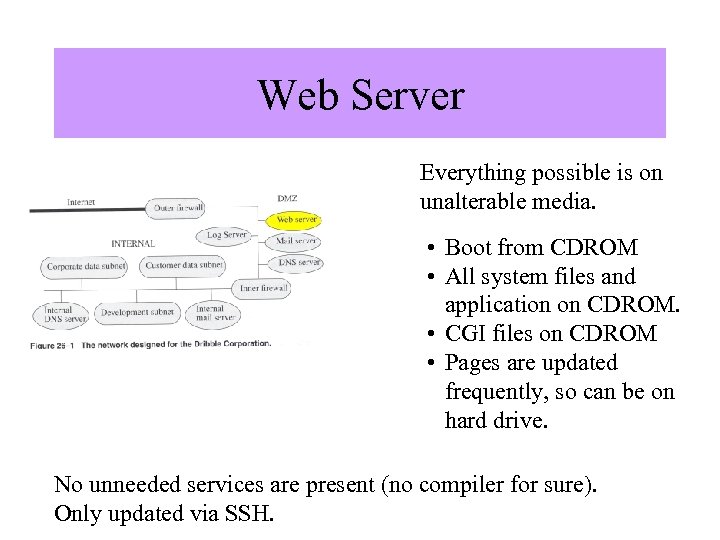 Web Server Everything possible is on unalterable media. Image from “Computer Security” by Matt Bishop, Addison Wesley. • Boot from CDROM • All system files and application on CDROM. • CGI files on CDROM • Pages are updated frequently, so can be on hard drive. No unneeded services are present (no compiler for sure). Only updated via SSH.
Web Server Everything possible is on unalterable media. Image from “Computer Security” by Matt Bishop, Addison Wesley. • Boot from CDROM • All system files and application on CDROM. • CGI files on CDROM • Pages are updated frequently, so can be on hard drive. No unneeded services are present (no compiler for sure). Only updated via SSH.
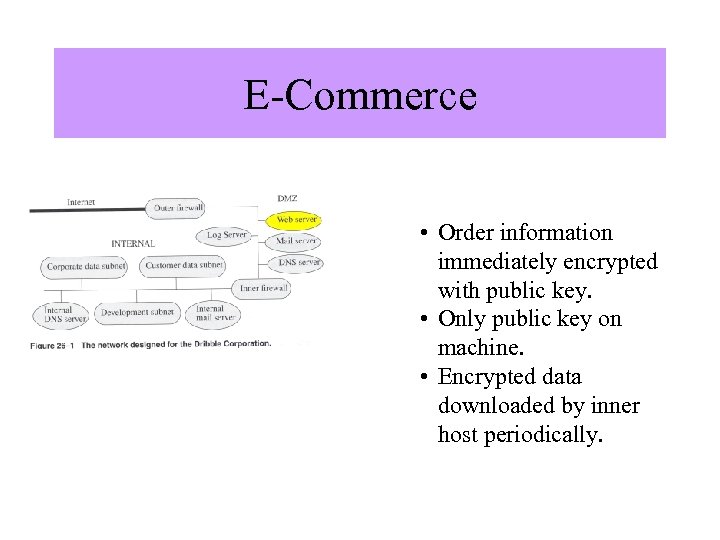 E-Commerce Image from “Computer Security” by Matt Bishop, Addison Wesley. • Order information immediately encrypted with public key. • Only public key on machine. • Encrypted data downloaded by inner host periodically.
E-Commerce Image from “Computer Security” by Matt Bishop, Addison Wesley. • Order information immediately encrypted with public key. • Only public key on machine. • Encrypted data downloaded by inner host periodically.
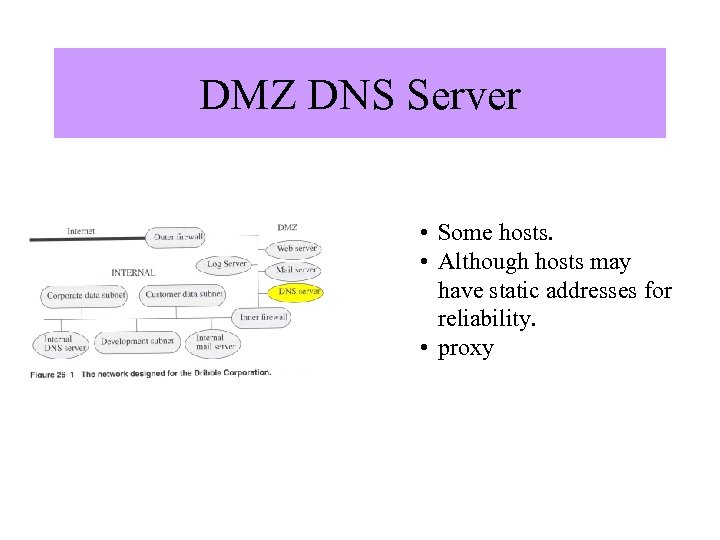 DMZ DNS Server Image from “Computer Security” by Matt Bishop, Addison Wesley. • Some hosts. • Although hosts may have static addresses for reliability. • proxy
DMZ DNS Server Image from “Computer Security” by Matt Bishop, Addison Wesley. • Some hosts. • Although hosts may have static addresses for reliability. • proxy
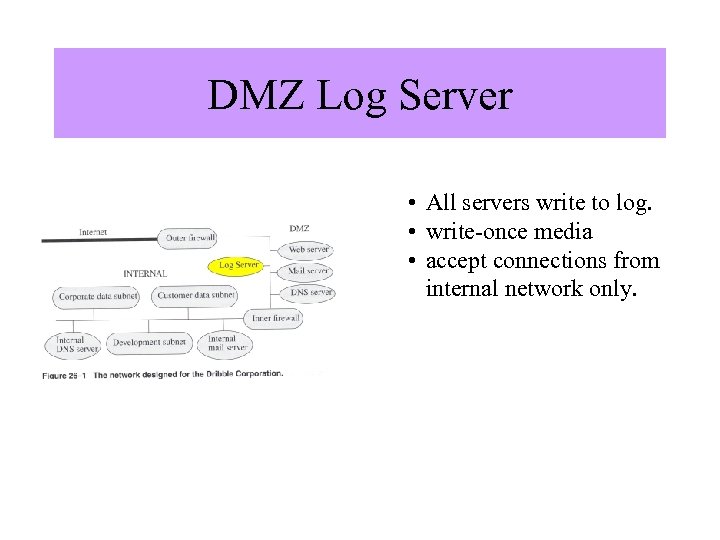 DMZ Log Server Image from “Computer Security” by Matt Bishop, Addison Wesley. • All servers write to log. • write-once media • accept connections from internal network only.
DMZ Log Server Image from “Computer Security” by Matt Bishop, Addison Wesley. • All servers write to log. • write-once media • accept connections from internal network only.
 Honeynets The Honeynet Project—www. honeynet. org. “To learn the tools, tactics and motives involved in computer and network attacks, and share the lessons learned. ” “Know Your Enemy, Learning about Security Threats”, by The Honeynet Project, Second Edition, Addison Wesley, ISBN 0 -321 -16646 -9.
Honeynets The Honeynet Project—www. honeynet. org. “To learn the tools, tactics and motives involved in computer and network attacks, and share the lessons learned. ” “Know Your Enemy, Learning about Security Threats”, by The Honeynet Project, Second Edition, Addison Wesley, ISBN 0 -321 -16646 -9.
 Definition "… a honeypot is a trap set to detect or deflect attempts at unauthorized use of information systems. Generally it consists of a computer, data or a network site that appears to be part of a network but which is actually isolated and protected, and which seems to contain information that would be of value to attackers. The primary value of a honeypot is in the information it provides, which can be used for things such as detection, early warning and prediction, or awareness. While often a computer, a honeypot can take on other forms, such as files or data records, or even unused IP space. Honeypots have no production value; they should not see any traffic or activity. If they do capture any activity, it is most likely malicious or unauthorized. Honeypots can carry risks to a network, and must be handled with care. If they are not properly walled off, an attacker can use them to actually break into a system. "
Definition "… a honeypot is a trap set to detect or deflect attempts at unauthorized use of information systems. Generally it consists of a computer, data or a network site that appears to be part of a network but which is actually isolated and protected, and which seems to contain information that would be of value to attackers. The primary value of a honeypot is in the information it provides, which can be used for things such as detection, early warning and prediction, or awareness. While often a computer, a honeypot can take on other forms, such as files or data records, or even unused IP space. Honeypots have no production value; they should not see any traffic or activity. If they do capture any activity, it is most likely malicious or unauthorized. Honeypots can carry risks to a network, and must be handled with care. If they are not properly walled off, an attacker can use them to actually break into a system. "
 Etymology The term "honeypot" is often understood to refer to the British children's character Winnie-the-Pooh, a stuffed bear who was lured into various predicaments by his desire for pots of honey. An alternative explanation for the term is a reflection of the sarcastic term for outhouses …
Etymology The term "honeypot" is often understood to refer to the British children's character Winnie-the-Pooh, a stuffed bear who was lured into various predicaments by his desire for pots of honey. An alternative explanation for the term is a reflection of the sarcastic term for outhouses …
 Firewalls, IDS and Honeypots • Firewalls are a prevention technology; they are network or host solutions that keep attackers out. • IDSs are a detection technology; their purpose is to detect and alert security professionals about unauthorized or malicious activity. • Honeypots are tougher to define because they can be involved in aspects of prevention, detection, information gathering, and much more.
Firewalls, IDS and Honeypots • Firewalls are a prevention technology; they are network or host solutions that keep attackers out. • IDSs are a detection technology; their purpose is to detect and alert security professionals about unauthorized or malicious activity. • Honeypots are tougher to define because they can be involved in aspects of prevention, detection, information gathering, and much more.
 Many types of Honeypots • a honeypot does not even have to be a computer. • It can be any type of digital entity (often called a honeytoken) that has no production value. • For example, a hospital could create a false set of electronic patient records labeled George W. Bush. Because these records are honeypots, nobody should be accessing or interacting with them. • These records could then be implanted into a hospital's patient database as a honeypot component. If any employee or attacker attempted to access these records, this would indicate unauthorized activity because no one should be using these records.
Many types of Honeypots • a honeypot does not even have to be a computer. • It can be any type of digital entity (often called a honeytoken) that has no production value. • For example, a hospital could create a false set of electronic patient records labeled George W. Bush. Because these records are honeypots, nobody should be accessing or interacting with them. • These records could then be implanted into a hospital's patient database as a honeypot component. If any employee or attacker attempted to access these records, this would indicate unauthorized activity because no one should be using these records.
 Advantages of Honeypots • Honeypots collect only small data sets. • Organizations that log thousands of alerts a day may log only a hundred alerts with honeypots. makes the data honeypots collect much easier to manage and analyze. • Honeypots reduce false positives. • One of the greatest challenges of most detection technologies is that they generate false positives or false alerts. • The larger the probability that a security technology produces a false positive, the less likely the technology will be useful. • Honeypots dramatically reduce false positives simply because almost any activity with honeypots is by definition unauthorized, making honeypots extremely efficient at detecting attacks.
Advantages of Honeypots • Honeypots collect only small data sets. • Organizations that log thousands of alerts a day may log only a hundred alerts with honeypots. makes the data honeypots collect much easier to manage and analyze. • Honeypots reduce false positives. • One of the greatest challenges of most detection technologies is that they generate false positives or false alerts. • The larger the probability that a security technology produces a false positive, the less likely the technology will be useful. • Honeypots dramatically reduce false positives simply because almost any activity with honeypots is by definition unauthorized, making honeypots extremely efficient at detecting attacks.
 Advantages of Honeypots (cont. ) • Honeypots can catch false negatives. • Another challenge inherent in traditional detection technologies is that they often fail to detect unknown attacks. • This is a critical difference between honeypots and traditional computer security technologies that rely upon known signatures or statistical detection. • Signature-based security technologies by definition imply that "someone is going to get hurt" before the new attack is discovered and a signature is distributed. • Statistical detection also suffers from probabilistic failures-there is some non-zero probability that a new kind of attack is going to go undetected. • Honeypots, on the other hand, are designed to identify and capture new attacks against them. Any activity with the honeypot is an anomaly, making new or unseen attacks stand out.
Advantages of Honeypots (cont. ) • Honeypots can catch false negatives. • Another challenge inherent in traditional detection technologies is that they often fail to detect unknown attacks. • This is a critical difference between honeypots and traditional computer security technologies that rely upon known signatures or statistical detection. • Signature-based security technologies by definition imply that "someone is going to get hurt" before the new attack is discovered and a signature is distributed. • Statistical detection also suffers from probabilistic failures-there is some non-zero probability that a new kind of attack is going to go undetected. • Honeypots, on the other hand, are designed to identify and capture new attacks against them. Any activity with the honeypot is an anomaly, making new or unseen attacks stand out.
 Advantages of Honeypots (cont. ) • Honeypots capture encrypted activity. • Even if an attack is encrypted, honeypots can capture the activity. • As more organizations adopt encryption (such as secure shell [SSH], IP Security Protocol [IPsec], and Secure Sockets Layer [SSL]) within their environments, this becomes a major issue. • Honeypots can do this because the encrypted probes and attacks interact with the honeypot as an end point, where the activity is decrypted by the honeypot.
Advantages of Honeypots (cont. ) • Honeypots capture encrypted activity. • Even if an attack is encrypted, honeypots can capture the activity. • As more organizations adopt encryption (such as secure shell [SSH], IP Security Protocol [IPsec], and Secure Sockets Layer [SSL]) within their environments, this becomes a major issue. • Honeypots can do this because the encrypted probes and attacks interact with the honeypot as an end point, where the activity is decrypted by the honeypot.
 Advantages of Honeypots (cont. ) • Honeypots are highly flexible. • Honeypots are extremely adaptable and can be used in a variety of environments, everything from a social security number embedded into a database to an entire network of computers designed to be broken into. • Honeypots require minimal resources. • Even on the largest of networks, honeypots require minimal resources. A simple, aging Pentium computer can monitor literally millions of IP addresses
Advantages of Honeypots (cont. ) • Honeypots are highly flexible. • Honeypots are extremely adaptable and can be used in a variety of environments, everything from a social security number embedded into a database to an entire network of computers designed to be broken into. • Honeypots require minimal resources. • Even on the largest of networks, honeypots require minimal resources. A simple, aging Pentium computer can monitor literally millions of IP addresses
 Disadvantages of Honeypots • Honeypots have a limited field of view. • Honeypots see only what interacts with them. • They do not see attacks against or interactions with other systems. • A honeypot will not tell you that another system has been compromised, unless that compromised system interacts with the honeypot. • Risk. Any time you deploy a new technology, that technology introduces risk-specifically, the risk of an attacker taking over that system and using it as a launching pad for other attacks against internal or external targets.
Disadvantages of Honeypots • Honeypots have a limited field of view. • Honeypots see only what interacts with them. • They do not see attacks against or interactions with other systems. • A honeypot will not tell you that another system has been compromised, unless that compromised system interacts with the honeypot. • Risk. Any time you deploy a new technology, that technology introduces risk-specifically, the risk of an attacker taking over that system and using it as a launching pad for other attacks against internal or external targets.
 Types of Honeypots Low interaction emulates services example: honeyd (www. honeyd. org) High interaction real OS and applications example: Symantec Decoy Server
Types of Honeypots Low interaction emulates services example: honeyd (www. honeyd. org) High interaction real OS and applications example: Symantec Decoy Server
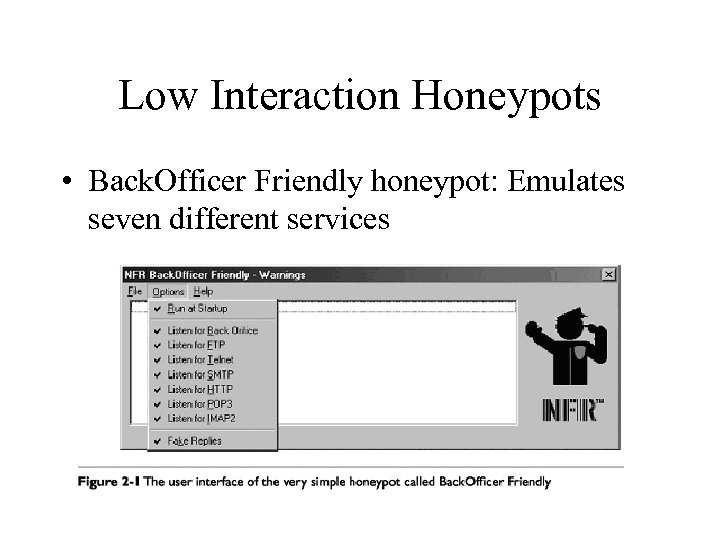 Low Interaction Honeypots • Back. Officer Friendly honeypot: Emulates seven different services
Low Interaction Honeypots • Back. Officer Friendly honeypot: Emulates seven different services
 Low Interaction Honeypots (cont. ) • Honeyd: emulates hundreds of different operating systems and services • An open source Honeypot • By editing the configuration file, you determine which IP addresses Honeyd will monitor, the types of operating systems it will emulate, and the services it will emulate. • For example, you can tell Honeyd to emulate a Linux 2. 4. 14 kernel system with an emulated File Transfer Protocol (FTP) server listening on port 21. – If attackers probe the honeypot, they will believe they are interacting with a Linux system. – If attackers connect to the FTP service, they will be deceived into thinking they are interacting with the wu-ftpd service.
Low Interaction Honeypots (cont. ) • Honeyd: emulates hundreds of different operating systems and services • An open source Honeypot • By editing the configuration file, you determine which IP addresses Honeyd will monitor, the types of operating systems it will emulate, and the services it will emulate. • For example, you can tell Honeyd to emulate a Linux 2. 4. 14 kernel system with an emulated File Transfer Protocol (FTP) server listening on port 21. – If attackers probe the honeypot, they will believe they are interacting with a Linux system. – If attackers connect to the FTP service, they will be deceived into thinking they are interacting with the wu-ftpd service.
 High Interaction Honeypots (cont. ) • Symantec Docy Server: is a commercial honeypot sold by Symantec. • As a high-interaction honeypot, Decoy Server does not emulate operating systems or services. • Instead, it creates real systems and real applications for attackers to interact with • system and creates up to four identical "cages, " each cage being a honeypot. • Each cage has a separate operating system with its own file system. • Attackers interact with the cages just as they would with real operating systems. • What attackers don't realize is that their every action and keystroke is being logged and recorded by the honeypot.
High Interaction Honeypots (cont. ) • Symantec Docy Server: is a commercial honeypot sold by Symantec. • As a high-interaction honeypot, Decoy Server does not emulate operating systems or services. • Instead, it creates real systems and real applications for attackers to interact with • system and creates up to four identical "cages, " each cage being a honeypot. • Each cage has a separate operating system with its own file system. • Attackers interact with the cages just as they would with real operating systems. • What attackers don't realize is that their every action and keystroke is being logged and recorded by the honeypot.
 (dis)Advantages of Low Interaction Honeypots • Easy to install and deploy; usually requires simply installing and configuring software on a computer • Minimal risk as the emulated services control what attackers can and cannot do • Captures limited amount of information, mainly transactional data and some limited interaction
(dis)Advantages of Low Interaction Honeypots • Easy to install and deploy; usually requires simply installing and configuring software on a computer • Minimal risk as the emulated services control what attackers can and cannot do • Captures limited amount of information, mainly transactional data and some limited interaction
 (dis)Advantages of High Interaction Honeypots • Can be complex to install or deploy (commercial versions tend to be much simpler) • Increased risk as attackers are provided real operating systems to interact with its own unique advantages and disadvantages. • Different organizations have different goals and therefore use different honeypots. One common trend is that, in general, commercial organizations (such as banks, manufacturing, or retail stores) prefer low-interaction honeypots as they are low risk, easy to deploy, and simple to maintain. • High-interaction honeypots are more common among organizations that need the unique capabilities of high-interaction solutions and manage the risk, such as military, government, and educational organizations • Can capture far more information than can low-interaction honeypots, including new tools, communications, or attacker keystrokes
(dis)Advantages of High Interaction Honeypots • Can be complex to install or deploy (commercial versions tend to be much simpler) • Increased risk as attackers are provided real operating systems to interact with its own unique advantages and disadvantages. • Different organizations have different goals and therefore use different honeypots. One common trend is that, in general, commercial organizations (such as banks, manufacturing, or retail stores) prefer low-interaction honeypots as they are low risk, easy to deploy, and simple to maintain. • High-interaction honeypots are more common among organizations that need the unique capabilities of high-interaction solutions and manage the risk, such as military, government, and educational organizations • Can capture far more information than can low-interaction honeypots, including new tools, communications, or attacker keystrokes
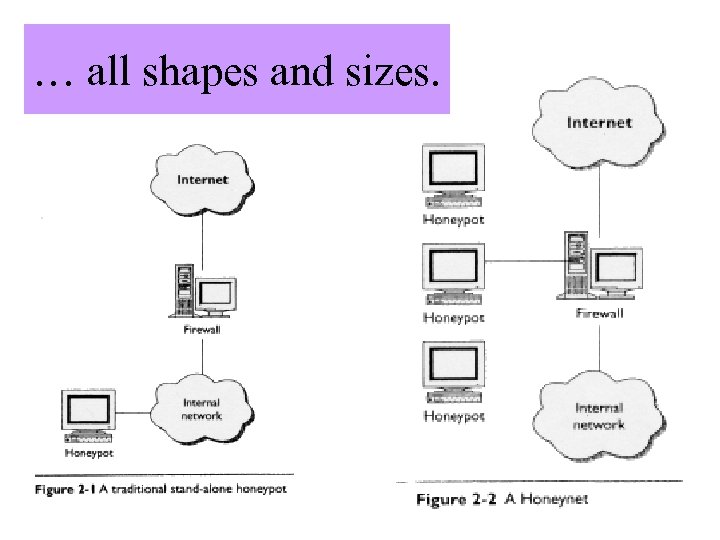 … all shapes and sizes. Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
… all shapes and sizes. Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
 Uses of Honeypots Preventing attacks Detecting attacks Responding to attacks Research
Uses of Honeypots Preventing attacks Detecting attacks Responding to attacks Research
 Preventing attacks • Honeypots can help prevent attacks in several ways. – For one, honeypots can prevent automated attacks, such as those launched by worms or auto-rooters. – These attacks are based on tools that randomly scan entire networks looking for vulnerable systems. – If vulnerable systems are found, these automated tools then attack and take over the system – One way that honeypots can help defend against such attacks is by slowing the scanning process, potentially even stopping it. Called "sticky honeypots, " these solutions monitor unused IP space. When probed by such scanning activity, the honeypots interact with and slow the attacker. – One such example of a sticky honeypot is La Brea Tar pit. Sticky honeypots are most often low-interaction solutions (you can almost call them "no-interaction solutions, " as they slow the attacker down to a crawl). • You can also use honeypots to protect your organization from human (that is, non-automated) attacks. – The concept is based on deception or deterrence. The idea is to confuse attackers, making them waste their time and resources interacting with honeypots. – Meanwhile, your organization is able to detect the attacker's activity and has the time to respond and stop it. – This can be taken one step farther. If attackers know your organization is using honeypots but they do not know which systems are honeypots and which systems are legitimate computers, they may be so concerned about being caught by honeypots that they decide not to attack your organization.
Preventing attacks • Honeypots can help prevent attacks in several ways. – For one, honeypots can prevent automated attacks, such as those launched by worms or auto-rooters. – These attacks are based on tools that randomly scan entire networks looking for vulnerable systems. – If vulnerable systems are found, these automated tools then attack and take over the system – One way that honeypots can help defend against such attacks is by slowing the scanning process, potentially even stopping it. Called "sticky honeypots, " these solutions monitor unused IP space. When probed by such scanning activity, the honeypots interact with and slow the attacker. – One such example of a sticky honeypot is La Brea Tar pit. Sticky honeypots are most often low-interaction solutions (you can almost call them "no-interaction solutions, " as they slow the attacker down to a crawl). • You can also use honeypots to protect your organization from human (that is, non-automated) attacks. – The concept is based on deception or deterrence. The idea is to confuse attackers, making them waste their time and resources interacting with honeypots. – Meanwhile, your organization is able to detect the attacker's activity and has the time to respond and stop it. – This can be taken one step farther. If attackers know your organization is using honeypots but they do not know which systems are honeypots and which systems are legitimate computers, they may be so concerned about being caught by honeypots that they decide not to attack your organization.
 Detecting attacks • Detection has traditionally proven to be an extremely difficult activity. • Technologies such as intrusion detection system and systems logs have proven ineffective for several reasons: – They generate far too much data and a large percentage of false positives, – they are unable to detect new attacks, – and they are unable to work in encrypted environments. • Honeypots address many of these traditional detection problems, – reducing false positives by capturing small data sets of high value, – capturing unknown attacks such as new exploits or polymorphic shellcode, – and working in encrypted environments
Detecting attacks • Detection has traditionally proven to be an extremely difficult activity. • Technologies such as intrusion detection system and systems logs have proven ineffective for several reasons: – They generate far too much data and a large percentage of false positives, – they are unable to detect new attacks, – and they are unable to work in encrypted environments. • Honeypots address many of these traditional detection problems, – reducing false positives by capturing small data sets of high value, – capturing unknown attacks such as new exploits or polymorphic shellcode, – and working in encrypted environments
 Responding to attacks • There are two problems compounding incidence response: – First, the very systems compromised often cannot be taken offline to be analyzed. – there is often so much data pollution that it can be very difficult to determine what the attackers did. • Honeypots can help address both problems : – they can quickly and easily be taken offline for a full forensic analysis without impacting day-to-day business operations. – Also, because the only activity a honeypot captures is unauthorized or malicious activity, this makes hacked honeypots much easier to analyze than hacked production systems, as any data you retrieve from a honeypot is most likely related to the attacker.
Responding to attacks • There are two problems compounding incidence response: – First, the very systems compromised often cannot be taken offline to be analyzed. – there is often so much data pollution that it can be very difficult to determine what the attackers did. • Honeypots can help address both problems : – they can quickly and easily be taken offline for a full forensic analysis without impacting day-to-day business operations. – Also, because the only activity a honeypot captures is unauthorized or malicious activity, this makes hacked honeypots much easier to analyze than hacked production systems, as any data you retrieve from a honeypot is most likely related to the attacker.
 Honeynet Architecture Data Control • need to allow an attacker enough freedom to reveal his tactics. • an attacker might use a compromised honeypot machine for malicious purposes. Neither should be evident to an attacker. Data Capture • monitoring and logging of activities • activity may be encrypted
Honeynet Architecture Data Control • need to allow an attacker enough freedom to reveal his tactics. • an attacker might use a compromised honeypot machine for malicious purposes. Neither should be evident to an attacker. Data Capture • monitoring and logging of activities • activity may be encrypted
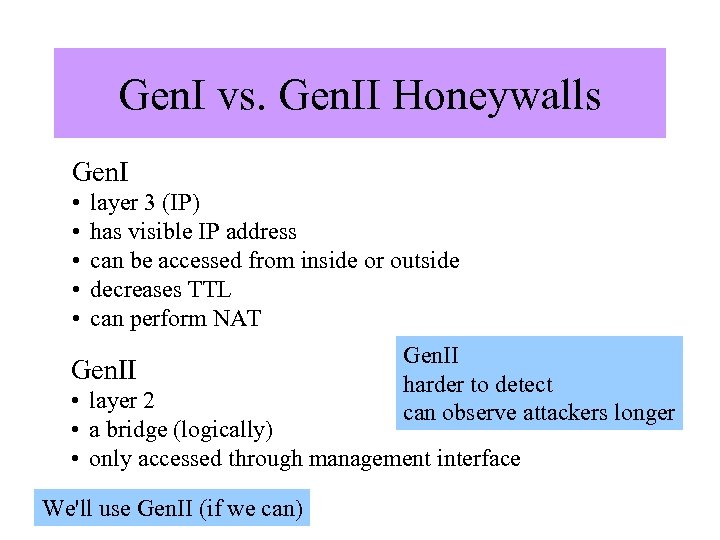 Gen. I vs. Gen. II Honeywalls Gen. I • • • layer 3 (IP) has visible IP address can be accessed from inside or outside decreases TTL can perform NAT Gen. II harder to detect can observe attackers longer • layer 2 • a bridge (logically) • only accessed through management interface We'll use Gen. II (if we can)
Gen. I vs. Gen. II Honeywalls Gen. I • • • layer 3 (IP) has visible IP address can be accessed from inside or outside decreases TTL can perform NAT Gen. II harder to detect can observe attackers longer • layer 2 • a bridge (logically) • only accessed through management interface We'll use Gen. II (if we can)
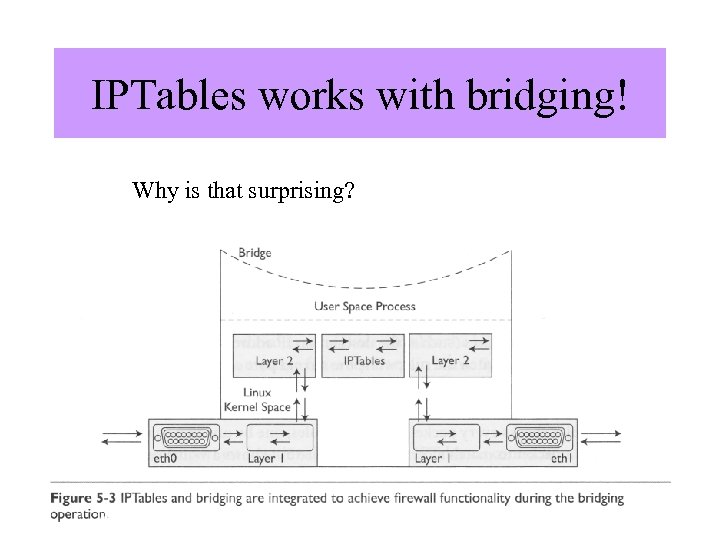 IPTables works with bridging! Why is that surprising? Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
IPTables works with bridging! Why is that surprising? Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
 IPTables Open source firewall. Home page: http: //www. netfilter. org/ Good intro: http: //www. justlinux. com/nhf/Security/IPtables_Basics. html Another good intro: http: //www. unixreview. com/documents/s=1236/urm 0104 l/0104 l. htm
IPTables Open source firewall. Home page: http: //www. netfilter. org/ Good intro: http: //www. justlinux. com/nhf/Security/IPtables_Basics. html Another good intro: http: //www. unixreview. com/documents/s=1236/urm 0104 l/0104 l. htm
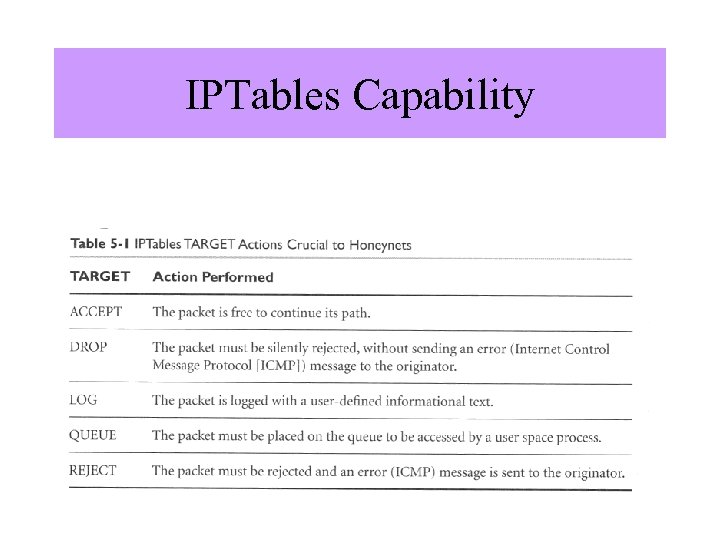 IPTables Capability Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
IPTables Capability Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
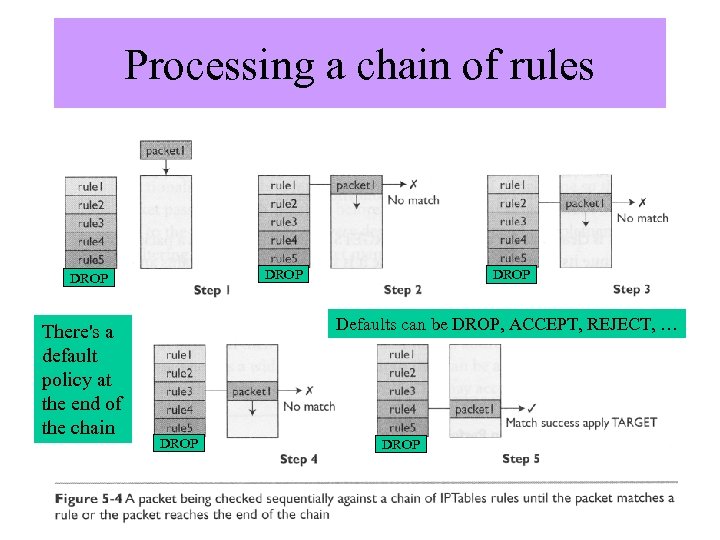 Processing a chain of rules DROP There's a default policy at the end of the chain Image from “Know Your DROP Enemy”, by The Honeynet Project, Addison Wesley, second edition. Defaults can be DROP, ACCEPT, REJECT, … DROP
Processing a chain of rules DROP There's a default policy at the end of the chain Image from “Know Your DROP Enemy”, by The Honeynet Project, Addison Wesley, second edition. Defaults can be DROP, ACCEPT, REJECT, … DROP
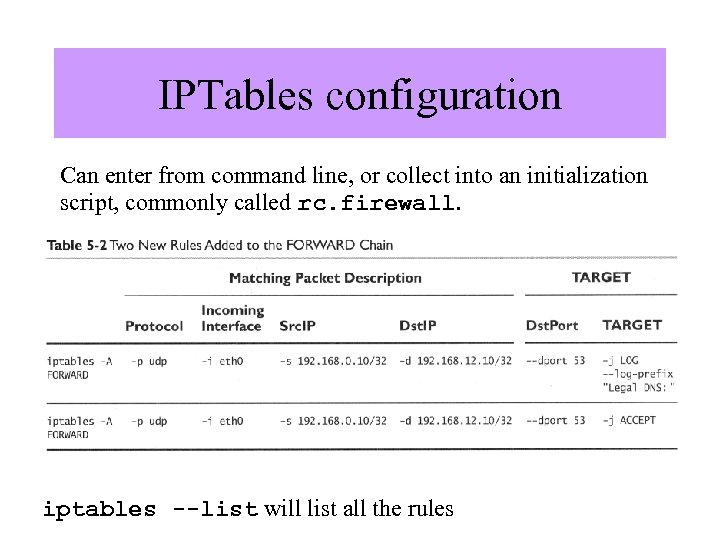 IPTables configuration Can enter from command line, or collect into an initialization script, commonly called rc. firewall. Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. iptables --list will list all the rules
IPTables configuration Can enter from command line, or collect into an initialization script, commonly called rc. firewall. Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. iptables --list will list all the rules
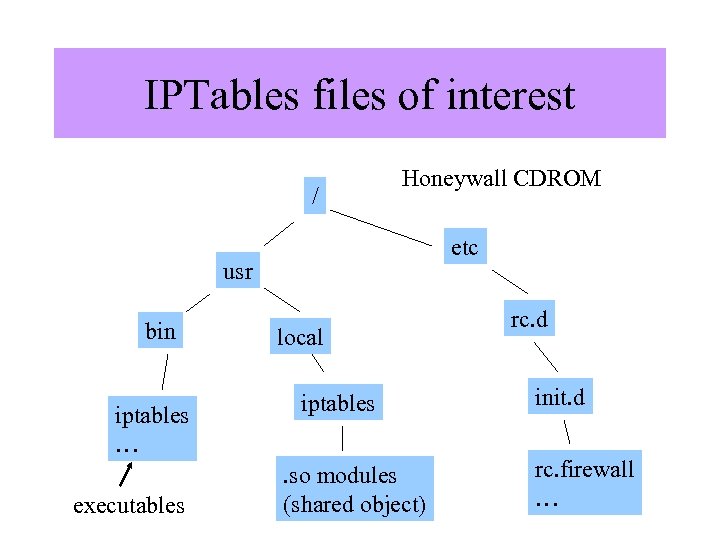 IPTables files of interest / Honeywall CDROM etc usr bin iptables … executables local iptables. so modules (shared object) rc. d init. d rc. firewall …
IPTables files of interest / Honeywall CDROM etc usr bin iptables … executables local iptables. so modules (shared object) rc. d init. d rc. firewall …
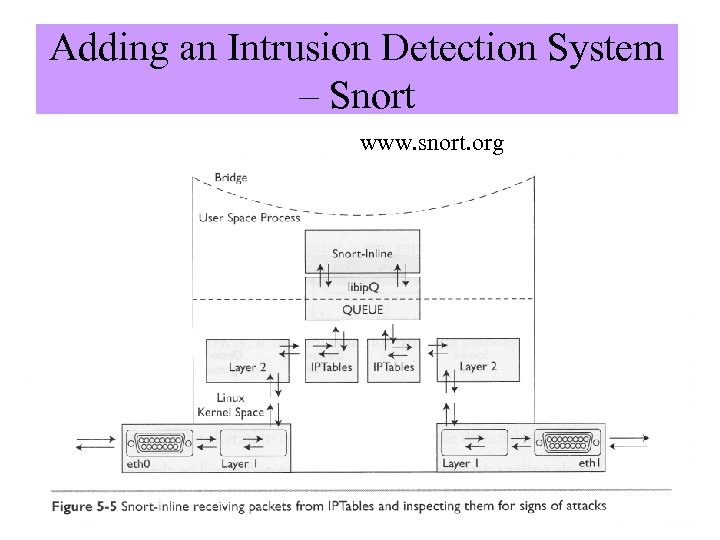 Adding an Intrusion Detection System – Snort www. snort. org Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
Adding an Intrusion Detection System – Snort www. snort. org Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
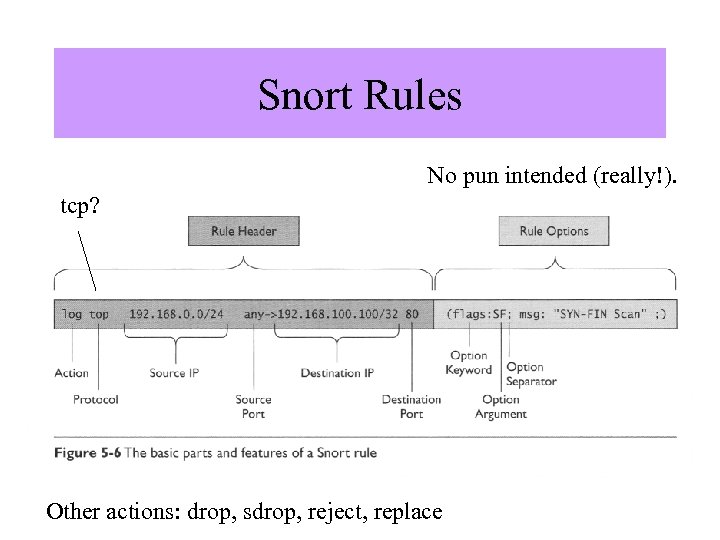 Snort Rules No pun intended (really!). tcp? Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. Other actions: drop, sdrop, reject, replace
Snort Rules No pun intended (really!). tcp? Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. Other actions: drop, sdrop, reject, replace
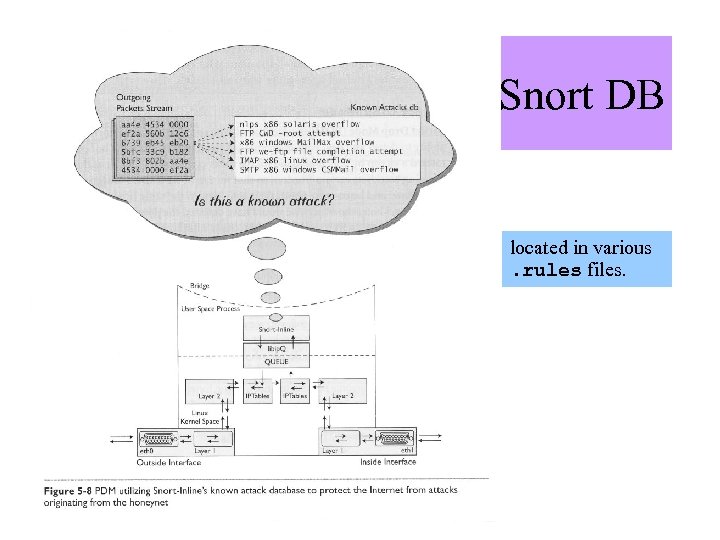 Snort DB Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. located in various. rules files.
Snort DB Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. located in various. rules files.
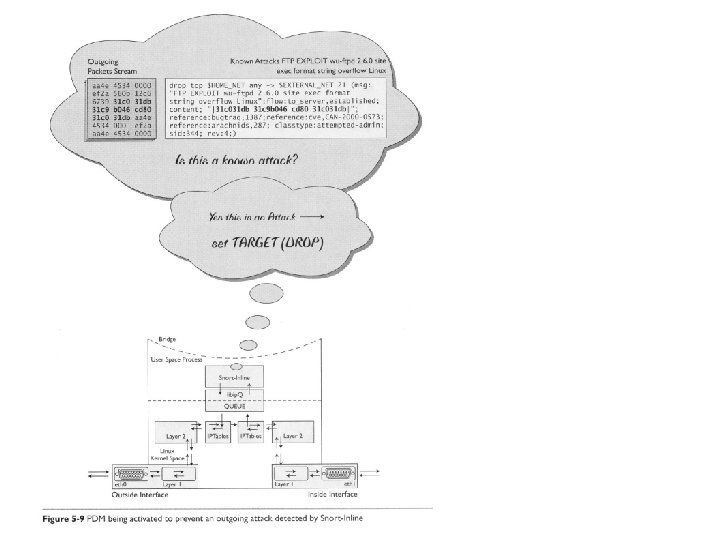 Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition.
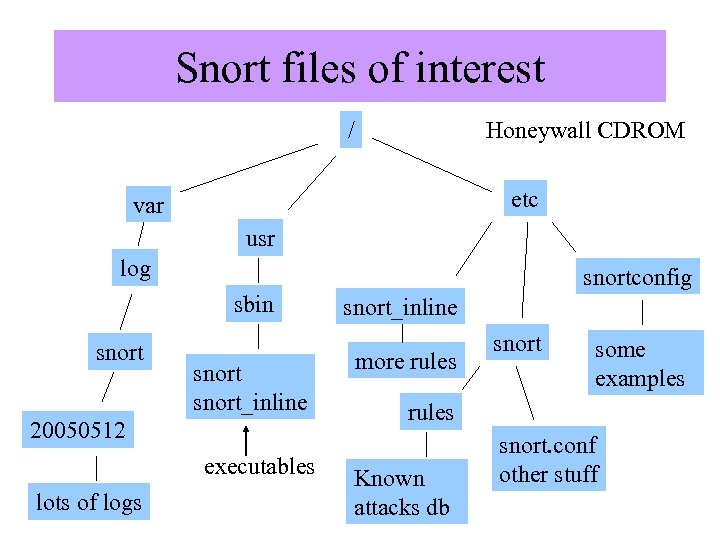 Snort files of interest / Honeywall CDROM etc var usr log snortconfig sbin snort_inline 20050512 executables lots of logs snort_inline more rules snort some examples rules Known attacks db snort. conf other stuff
Snort files of interest / Honeywall CDROM etc var usr log snortconfig sbin snort_inline 20050512 executables lots of logs snort_inline more rules snort some examples rules Known attacks db snort. conf other stuff
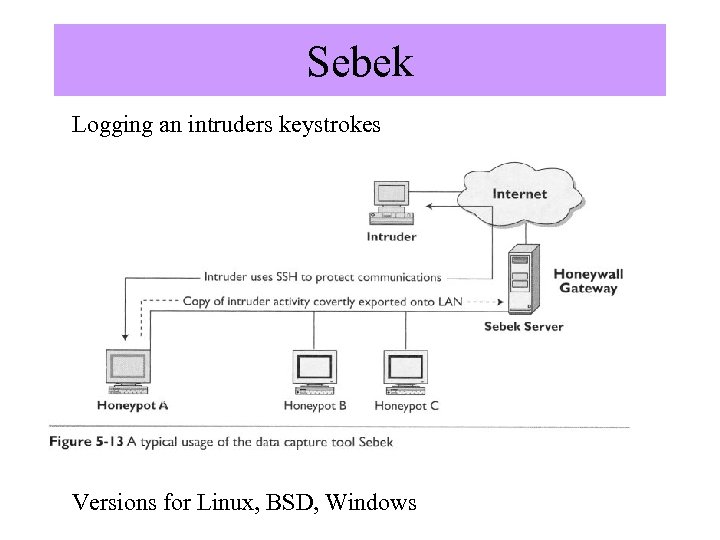 Sebek Logging an intruders keystrokes Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. Versions for Linux, BSD, Windows
Sebek Logging an intruders keystrokes Image from “Know Your Enemy”, by The Honeynet Project, Addison Wesley, second edition. Versions for Linux, BSD, Windows
 References • Know Your Enemy (2 nd Ed. ), Addison-Wesley, • http: //www. newsforge. com/article. pl? sid=0 4/09/24/1734245 • http: //www. netfilter. org/ • www. snort. org
References • Know Your Enemy (2 nd Ed. ), Addison-Wesley, • http: //www. newsforge. com/article. pl? sid=0 4/09/24/1734245 • http: //www. netfilter. org/ • www. snort. org


