02ea4b5059d72ee98aa19338eaa5be37.ppt
- Количество слайдов: 23
 Security Protocols Analysis Internet Security - Farkas
Security Protocols Analysis Internet Security - Farkas
 Reading l This Class: – Modelling and Analysis of Security Protocols: chapters 0. 9 -0. 12 – C. Meadows: Formal Methods for Cryptographic Protocol Analysis: Emerging Issues and Trends, http: //citeseer. ist. psu. edu/meadows 03 formal. html l Next class: – Modelling and Analysis of Security Protocols: chapter 1 Internet Security - Farkas 2
Reading l This Class: – Modelling and Analysis of Security Protocols: chapters 0. 9 -0. 12 – C. Meadows: Formal Methods for Cryptographic Protocol Analysis: Emerging Issues and Trends, http: //citeseer. ist. psu. edu/meadows 03 formal. html l Next class: – Modelling and Analysis of Security Protocols: chapter 1 Internet Security - Farkas 2
 What is Protocol Analysis l Cryptographic Protocols l Attackers’ capabilities l Security? – Hostile environment l Vulnerabilities – Weakness of cryptography – Incorrect specifications Internet Security - Farkas 3
What is Protocol Analysis l Cryptographic Protocols l Attackers’ capabilities l Security? – Hostile environment l Vulnerabilities – Weakness of cryptography – Incorrect specifications Internet Security - Farkas 3
 Cryptographic Protocols l Two or more parties l Communication over insecure network l Cryptography used to achieve goal – Exchange secret keys – Verify identity (authentication) – Secure transaction processing Internet Security - Farkas 4
Cryptographic Protocols l Two or more parties l Communication over insecure network l Cryptography used to achieve goal – Exchange secret keys – Verify identity (authentication) – Secure transaction processing Internet Security - Farkas 4
 Emerging Properties of Protocols l l l Greater interoperation Negotiation of policy Greater complexity Group-oriented protocols Emerging security threats Internet Security - Farkas 5
Emerging Properties of Protocols l l l Greater interoperation Negotiation of policy Greater complexity Group-oriented protocols Emerging security threats Internet Security - Farkas 5
 Attackers’ Capabilities l Read traffic l Modify traffic l Delete traffic l Perform cryptographic operations l Control over network principals Internet Security - Farkas 6
Attackers’ Capabilities l Read traffic l Modify traffic l Delete traffic l Perform cryptographic operations l Control over network principals Internet Security - Farkas 6
 Attacks l Known attacks – Can be picked up by careful inspection l Nonintuitive attacks – Not easily apparent – May not depend on flaws or weaknesses of cryptographic algs. – Use variety of methods, e. g. , statistical analysis, subtle properties of crypto algs. , etc. Internet Security - Farkas 7
Attacks l Known attacks – Can be picked up by careful inspection l Nonintuitive attacks – Not easily apparent – May not depend on flaws or weaknesses of cryptographic algs. – Use variety of methods, e. g. , statistical analysis, subtle properties of crypto algs. , etc. Internet Security - Farkas 7
 Formal Methods l Combination of a mathematical or logical model of a system and its requirements and l Effective procedures for determining whether a proof that a system satisfies its requirements is correct. Can be automated! Internet Security - Farkas 8
Formal Methods l Combination of a mathematical or logical model of a system and its requirements and l Effective procedures for determining whether a proof that a system satisfies its requirements is correct. Can be automated! Internet Security - Farkas 8
 Example: Needham. Schroeder l Famous simple example (page 30 -31) – Protocol published and known for 10 years – Gavin Lowe discovered unintended property while preparing formal analysis using FDR system l Subsequently rediscovered by every analysis method From: J. Mitchell Internet Security - Farkas 9
Example: Needham. Schroeder l Famous simple example (page 30 -31) – Protocol published and known for 10 years – Gavin Lowe discovered unintended property while preparing formal analysis using FDR system l Subsequently rediscovered by every analysis method From: J. Mitchell Internet Security - Farkas 9
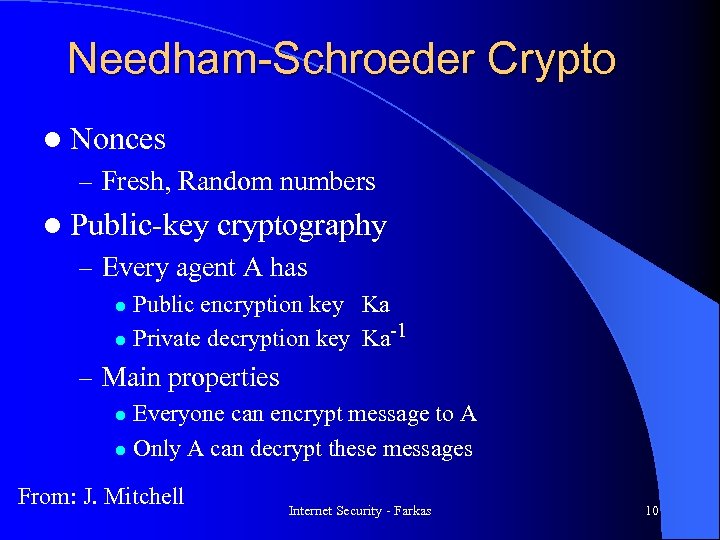 Needham-Schroeder Crypto l Nonces – Fresh, Random numbers l Public-key cryptography – Every agent A has Public encryption key Ka -1 l Private decryption key Ka l – Main properties Everyone can encrypt message to A l Only A can decrypt these messages l From: J. Mitchell Internet Security - Farkas 10
Needham-Schroeder Crypto l Nonces – Fresh, Random numbers l Public-key cryptography – Every agent A has Public encryption key Ka -1 l Private decryption key Ka l – Main properties Everyone can encrypt message to A l Only A can decrypt these messages l From: J. Mitchell Internet Security - Farkas 10
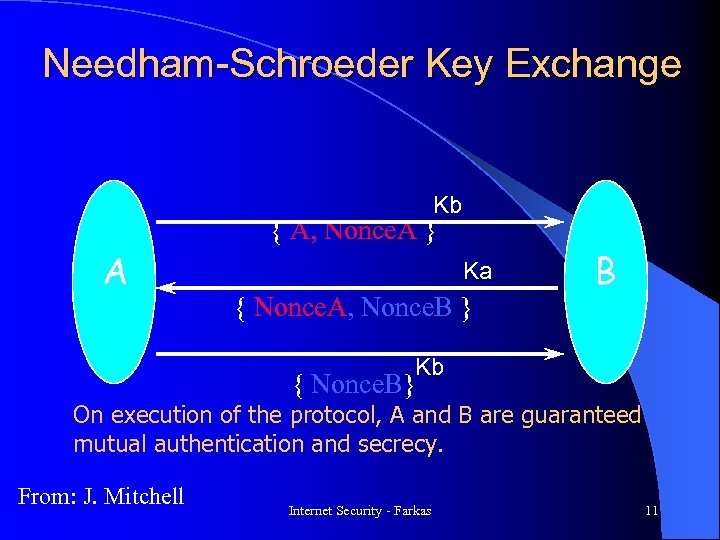 Needham-Schroeder Key Exchange Kb A { A, Nonce. A } Ka { Nonce. A, Nonce. B } B Kb { Nonce. B} On execution of the protocol, A and B are guaranteed mutual authentication and secrecy. From: J. Mitchell Internet Security - Farkas 11
Needham-Schroeder Key Exchange Kb A { A, Nonce. A } Ka { Nonce. A, Nonce. B } B Kb { Nonce. B} On execution of the protocol, A and B are guaranteed mutual authentication and secrecy. From: J. Mitchell Internet Security - Farkas 11
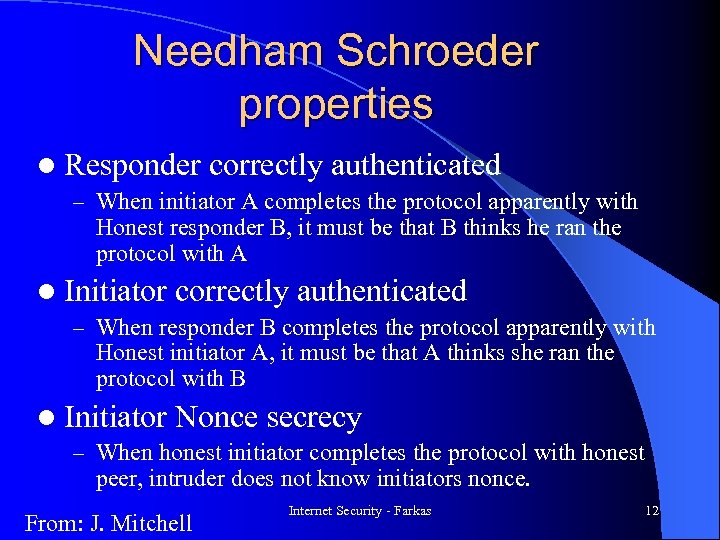 Needham Schroeder properties l Responder correctly authenticated – When initiator A completes the protocol apparently with Honest responder B, it must be that B thinks he ran the protocol with A l Initiator correctly authenticated – When responder B completes the protocol apparently with Honest initiator A, it must be that A thinks she ran the protocol with B l Initiator Nonce secrecy – When honest initiator completes the protocol with honest peer, intruder does not know initiators nonce. From: J. Mitchell Internet Security - Farkas 12
Needham Schroeder properties l Responder correctly authenticated – When initiator A completes the protocol apparently with Honest responder B, it must be that B thinks he ran the protocol with A l Initiator correctly authenticated – When responder B completes the protocol apparently with Honest initiator A, it must be that A thinks she ran the protocol with B l Initiator Nonce secrecy – When honest initiator completes the protocol with honest peer, intruder does not know initiators nonce. From: J. Mitchell Internet Security - Farkas 12
![[Lowe] Anomaly in Needham-Schroeder { A, NA } Ke A E { NA, NB [Lowe] Anomaly in Needham-Schroeder { A, NA } Ke A E { NA, NB](https://present5.com/presentation/02ea4b5059d72ee98aa19338eaa5be37/image-13.jpg) [Lowe] Anomaly in Needham-Schroeder { A, NA } Ke A E { NA, NB } Ka { NB } Ke Evil agent E tricks honest A into revealing private key NB from B Evil E can then fool B { NA, NB } { A, NA } Ka Kb B Internet Security - Farkas 13 From: J. Mitchell
[Lowe] Anomaly in Needham-Schroeder { A, NA } Ke A E { NA, NB } Ka { NB } Ke Evil agent E tricks honest A into revealing private key NB from B Evil E can then fool B { NA, NB } { A, NA } Ka Kb B Internet Security - Farkas 13 From: J. Mitchell
 Requirements and Properties l Authentication – Authentication, Secrecy l Trading – Fairness l Special applications (e. g. , voting) – Anonymity and Accountability Internet Security - Farkas 14
Requirements and Properties l Authentication – Authentication, Secrecy l Trading – Fairness l Special applications (e. g. , voting) – Anonymity and Accountability Internet Security - Farkas 14
 Security Analysis l Understand system requirements l Model – System – Attacker l Evaluate security properties – Under normal operation (no attacker) – In the presence of attacker l Security results: under given assumptions about system and about the capabilities of the attackers. Internet Security - Farkas 15
Security Analysis l Understand system requirements l Model – System – Attacker l Evaluate security properties – Under normal operation (no attacker) – In the presence of attacker l Security results: under given assumptions about system and about the capabilities of the attackers. Internet Security - Farkas 15
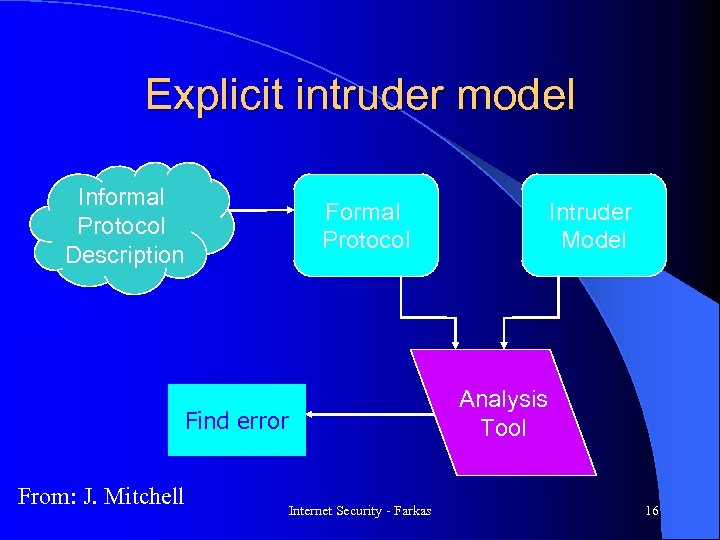 Explicit intruder model Informal Protocol Description Formal Protocol Analysis Tool Find error From: J. Mitchell Intruder Model Internet Security - Farkas 16
Explicit intruder model Informal Protocol Description Formal Protocol Analysis Tool Find error From: J. Mitchell Intruder Model Internet Security - Farkas 16
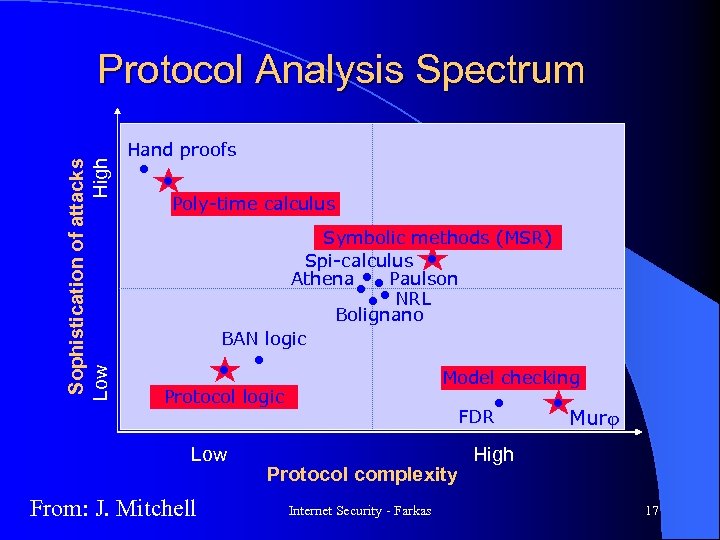 Sophistication of attacks High Low Protocol Analysis Spectrum Hand proofs Poly-time calculus Symbolic methods (MSR) Spi-calculus Athena Paulson NRL Bolignano BAN logic Model checking Protocol logic Low From: J. Mitchell FDR Protocol complexity Internet Security - Farkas Murj High 17
Sophistication of attacks High Low Protocol Analysis Spectrum Hand proofs Poly-time calculus Symbolic methods (MSR) Spi-calculus Athena Paulson NRL Bolignano BAN logic Model checking Protocol logic Low From: J. Mitchell FDR Protocol complexity Internet Security - Farkas Murj High 17
 Analysis of Discrete Systems l Properties of discrete – Requirements – Attackers systems l Attack: sequence of finite set of operations l Evaluate different paths an attacker may take l State the environmental assumptions precisely Internet Security - Farkas 18
Analysis of Discrete Systems l Properties of discrete – Requirements – Attackers systems l Attack: sequence of finite set of operations l Evaluate different paths an attacker may take l State the environmental assumptions precisely Internet Security - Farkas 18
 First Analysis Method Dolev-Yao Set of polynomial-time algorithms for deciding security of a restricted class of protocols l First to develop formal model of environment in which l l – Multiple executions of the protocol can be running concurrently – Cryptographic algorithms considered as “black boxes” – Includes intrudes model l Tools based on Dolev-Yao – NRL protocol analyzer – Longley-Rigby tool Internet Security - Farkas 19
First Analysis Method Dolev-Yao Set of polynomial-time algorithms for deciding security of a restricted class of protocols l First to develop formal model of environment in which l l – Multiple executions of the protocol can be running concurrently – Cryptographic algorithms considered as “black boxes” – Includes intrudes model l Tools based on Dolev-Yao – NRL protocol analyzer – Longley-Rigby tool Internet Security - Farkas 19
 Model checking l Two components – Finite state system – Specification of properties l Exhaustive search the state space to determine security Internet Security - Farkas 20
Model checking l Two components – Finite state system – Specification of properties l Exhaustive search the state space to determine security Internet Security - Farkas 20
 Theorem Prover l Theorems: properties of protocols l Prove or check proofs automatically l Could find flaws not detected by manual analysis l Do not give counterexamples like the model checkers Internet Security - Farkas 21
Theorem Prover l Theorems: properties of protocols l Prove or check proofs automatically l Could find flaws not detected by manual analysis l Do not give counterexamples like the model checkers Internet Security - Farkas 21
 Logic l l l Burrows, Abadi, and Needham (BAN) logic Logic of belief Set of modal operators: describing the relationship of principal to data Set of possible beliefs Inference rules Seems to be promising but weaker than state exploration tools and theorem proving (higher level abstraction) Internet Security - Farkas 22
Logic l l l Burrows, Abadi, and Needham (BAN) logic Logic of belief Set of modal operators: describing the relationship of principal to data Set of possible beliefs Inference rules Seems to be promising but weaker than state exploration tools and theorem proving (higher level abstraction) Internet Security - Farkas 22
 Next week CSP Internet Security - Farkas
Next week CSP Internet Security - Farkas


