0f38677b1e38227f0cd4dd16e7ea277d.ppt
- Количество слайдов: 40

Security Management 安全管理 陳彥錚 (Yen-Cheng Chen) yencheng@mcu. edu. tw http: //www. im. tj. mcu. edu. tw/~ycchen/
Security Management The process of protecting access to sensitive information found on systems attached to a data network.
安全管理之功能 FThe creation, deletion, and control of security services and mechanisms. FThe distribution of security-relevant information. FThe reporting of security-relevant events.

資訊 安全之重點 F機密性 (Confidentiality) F真實性 (Authentication) F完整性 (Integrity) F不可否認性 (Non-repudiation) F存取控制 (Access control) F可用性 (Availability)
安全管理實施步驟 1. Identifying the sensitive information to be protected 2. Finding the access points 3. Securing the access points 4. Maintaining the access points

Access Point FA piece of network hardware or software that allows access to the data network. – Software services – Hardware components – Network media
Finding the Access Points FPhysical Wiring/Media FNetwork Services – Remote Login – File Transfer – E-mail – Remote Execution – Directory Service –… FNMS
Securing the Access Points (1). Packet Filtering (2). Host Authentication (3). User Authentication (4). Key Authentication (5). Encryption
(1). Packet Filtering FPacket filtering usually can be performed in bridges, switches, and routers. FPacket filtering stops packets to or from unsecured hosts before they reach an access point. FIssues – Each network device to perform packet filtering must be configured. – Packet filtering doesn't work if the unsecured host changes its address.

Packet-Filtering Routers Users Protected Network Router with ACLs ISP and Internet Micro Webserver E-mail Server Micro Webserver zip 100 Users Web Server Public Access

(2). Host Authentication FAllow access to a service based on a source host identifier, e. g. network address. Service Remote Login File Transfer Directory … Allow Host-B, Host-C, 140. 131. 59. 20 Host-A, Host-B, PC-bmw, Host-C, 140. 131. 62. 211, PC-benz … FIssues – A host can change its network address. – Different users in the same host have the same authority.

(3). User Authentication FEnable service to identify each user before allowing that user access. FPassword Mechanism – Generally, passwords are transferred on the network without any encryption. – Use encrypted passwords. – Users tend to make passwords easy to remember. – If the passwords are not common words, users will write them down. FHost Authentication + User Authentication

(4). Key Authentication FKey – A unique piece of information that authenticates the data in a transaction. FKey Authentication – The destination host requires the source host of a transaction to present a key for the transaction. FKey Server – A server that validates requests for transactions between hosts by giving out keys.

Source (S) Key Server (K) Destination (D) 1. S requests remote login to D S 2. S requests a key to K. S K S 3. K validates the request. K 4. K send a key to S. K 5. S requests login with valid key to D. S D

(5). Encryption Network atek 49 ffdlffffe ffdsfsfsff … encryption ciphertext Dear John: I am happy to know. . . plaintext atek 49 ffdlffffe ffdsfsfsff … decryption ciphertext Dear John: I am happy to know. . . plaintext

Cryptography / Encryption FEncryption – Encode, Scramble, or Encipher the plaintext information to be sent. FEncryption Algorithm – The method performed in encryption. FEncryption Key – A stream of bits that control the encryption algorithm. FPlaintext – The text which is to be encrypted. FCiphertext – the text after encryption is performed.

Encryption Key Encryption Algorithm Ciphertext atek 49 ffdlffffe ffdsfsfsff … Plaintext Dear John: I am happy to know. . .

Decryption Key Decryption Algorithm Plaintext Dear John: I am happy to know. . . Ciphertext atek 49 ffdlffffe ffdsfsfsff …

Encryption / Decryption

Encryption Techniques FPrivate Key Encryption – Encryption Key = Decryption Key – Also called Symmetric-Key Encryption, Secret. Encryption Key Encryption, or Conventional Cryptography. Encryption FPublic Key Encryption – Encryption Key Decryption Key – Also called Asymmetric Encryption

Private Key Encryption: - DES (Data Encryption Standard) FAdopted by U. S. Federal Government. FBoth the sender and receiver must know the same secret key code to encrypt and decrypt messages with DES FOperates on 64 -bit blocks with a 56 -bit key FDES is a fast encryption scheme and works well for bulk encryption. FIssues: – How to deliver the key to the sender safely?
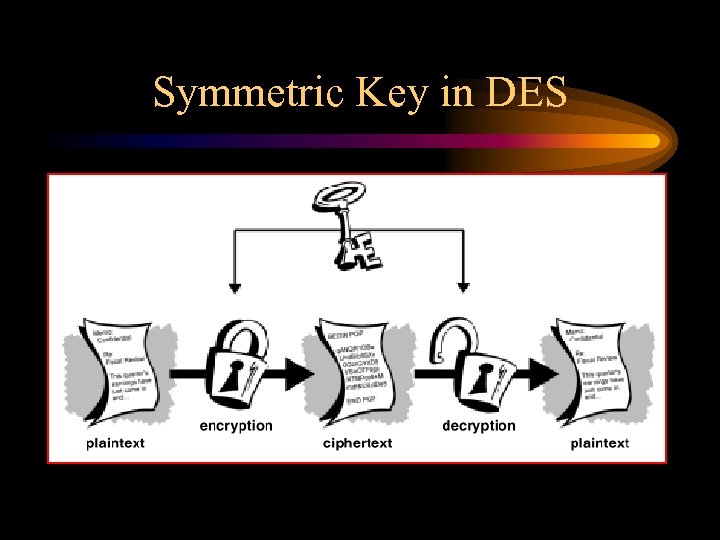
Symmetric Key in DES

Other Symmetric Key Encryption Techniques F 3 DES – Triple DES FRC 2, RC 4 FIDEA – International Data Encryption Algorithm

Key Size Matters! Information Lifetime Centuries Decades 168 -bits Years 56 -bits Hours 40 -bits 100’s 10 K 1 M 10 M Budget ($) 100 M *Triple-DES (recommended for commercial & corporate information)

Public Key Encryption: - RSA FThe public key is disseminated as widely as possible. The secrete key is only known by the receiver. FNamed after its inventors Ron Rivest, Adi Shamir, and Leonard Adleman FRSA is well established as a de facto standard FRSA is fine for encrypting small messages

Asymmetric Key in RSA

Key Length Average Time for Exhaustive Key Search 32 32 Bits Symmetric Cipher (Conventional) 40 56 64 80 96 112 120 128 192 Bits Bits Bits Asymmetric (RSA/D-H) 274 384 512 1024 1536 2048 2560 3072 10240 Performance 30~200 Bits Bits Bits Number of Possible Key 2 56 Bits 2 128 16 = 7. 2 X 10 38 = 3. 4 X 10 31 32 Bits ==> 2 usec =36 min 55 Time required at 1 Encryption/u. SEC 56 Bits ==> 2 usec =1142 Years 127 128 Bits ==> 2 24 usec =5 X 10 Years 32 Bits ==> 2 millsec Time required at 6 10 Encryption/u. SEC 1 56 = 4. 3 X 10 9 56 Bits ==> 10 Hours 18 128 Bits ==> 5 X 10 Years
Hybrid Encryption Technology: PGP (Pretty Good Privacy) FHybrid Encryption Technique – First compresses the plaintext. – Then creates a session key, which is a one-time-only secret key. – Using the session key, apply a fast conventional encryption algorithm to encrypt the plaintext. – The session key is then encrypted to the recipient’s public key. – This public key-encrypted session key is transmitted along with the ciphertext to the recipient.
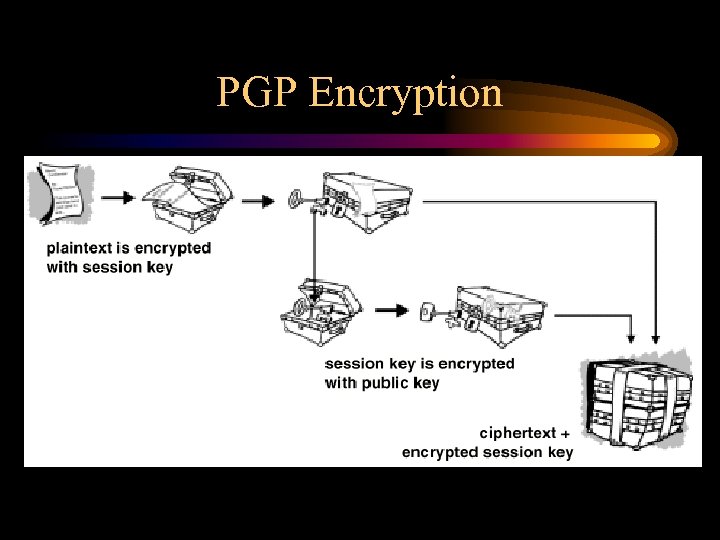
PGP Encryption

PGP Decryption FThe recipient uses its private key to recover the temporary session key FUse the session key to decrypt the conventionally-encrypted ciphertext.

PGP Decryption

Digital Signatures FDigital signatures enable the recipient of information to verify the authenticity of the information’s origin, and also verify that the information is intact. FPublic key digital signatures provide – authentication – data integrity – non-repudiation FTechnique: public key cryptography
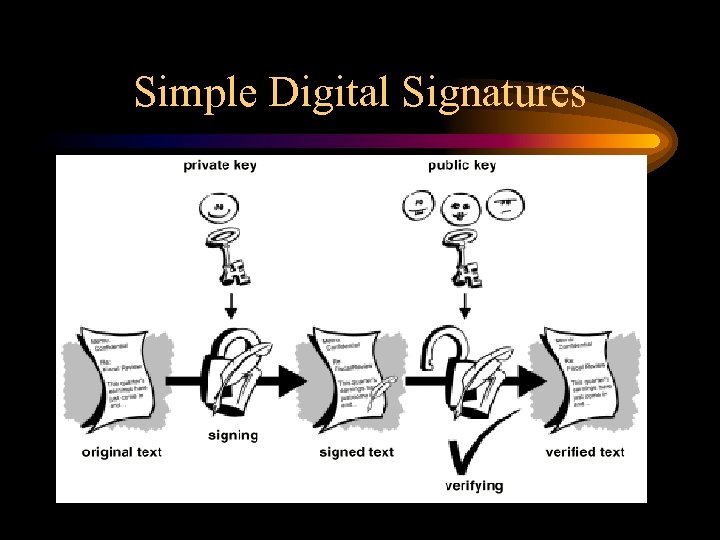
Simple Digital Signatures

Secure Digital Signatures
Maintaining the Secure Access Points FLocate potential and actual security breaches. FAudit Trail FSecurity Test Programs

Attaching to a Public Network FNo Access FFull Access – All individual computers should have security management. FLimited Access – Use a firewall to enforce security between private and public networks.

防火牆 (Firewall) F Firewall為一組軟硬體系統,用來控制 內部與外部網路間之 通訊。 F Firewall建置方式 – Packet Filtering Firewall – Dual-Homed Host Firewall – Screened Subnet Firewall http: //www. movies. acmecity. com/silent/6/doc/fwppt. zip

VPN (Virtual Private Network) F VPN: 虛擬私人網路 – 藉由虛擬的方式,在公眾數據網路 上建立一個能夠秘密通訊的私 人 網 路。 F VPN所使用之 公眾數據網路 • X. 25 • Frame Relay • ATM • Internet

VPN (Virtual Private Network)

VPN技術 F 穿隧技術 (Tunneling) – IPSec (IP Security) – PPTP (Point-to-Point Tunneling Protocol) – L 2 TP (Layer 2 Tunneling Protocol) F 加解密技術 (Encryption/Decryption) – Private/Public/Hybrid Key Encryption F 密鑰管理 (Key Management) – SKIP (Simple Key Management for IP) – IKE (ISAKMP/Oakley) F 使用者與設備身份認證技術 (Authentication) – Username/Password + Token Number – X. 509 Certificate by Certificate Authority (CA)
0f38677b1e38227f0cd4dd16e7ea277d.ppt