0e26e594d98af82ad1e9e94c8a83da2d.ppt
- Количество слайдов: 16
 Security in Self-organizing Systems Refik Molva Institut EURECOM refik. molva@eurecom. fr http: //www. eurecom. fr/ce/researchce/nsteam. en. htm
Security in Self-organizing Systems Refik Molva Institut EURECOM refik. molva@eurecom. fr http: //www. eurecom. fr/ce/researchce/nsteam. en. htm
 Self-organizing Systems • System or Network consists of a Collection of Ordinary Components • No fixed infrastructure • No (or limited) organization • • Ad Hoc Networks Sensor Networks P 2 P Applications Ubiquitous computing
Self-organizing Systems • System or Network consists of a Collection of Ordinary Components • No fixed infrastructure • No (or limited) organization • • Ad Hoc Networks Sensor Networks P 2 P Applications Ubiquitous computing
 Security Challenges Self-organizing • No(or limited) infrastructure • Lack of organization Wireless & Mobile • • Scarcity of Resources Limited Energy Lack of physical security Lack of connectivity • Comm. Security • Key management • Trust Management • Cooperation • Privacy Context-awareness
Security Challenges Self-organizing • No(or limited) infrastructure • Lack of organization Wireless & Mobile • • Scarcity of Resources Limited Energy Lack of physical security Lack of connectivity • Comm. Security • Key management • Trust Management • Cooperation • Privacy Context-awareness
 Communication Security Ø Secure Routing Ø ARAN, SRP, ARIADNE, SEAD, TIK Ø New Challenges Ø Network coding and security [Gkantsidis, Rodriguez] Ø Data aggregation [Girao, Schneider, Westhoff] [Castellucia, Tsudik]
Communication Security Ø Secure Routing Ø ARAN, SRP, ARIADNE, SEAD, TIK Ø New Challenges Ø Network coding and security [Gkantsidis, Rodriguez] Ø Data aggregation [Girao, Schneider, Westhoff] [Castellucia, Tsudik]
 Key Management Challenges • Lack of (or limited) – Security infrastructure • Key servers (KDC, CA, RA) – Organization (a priori trust) • p 2 p • Authentication is not sufficient to build trust Bootstrapping security associations from scratch Fully distributed Minimum dependency
Key Management Challenges • Lack of (or limited) – Security infrastructure • Key servers (KDC, CA, RA) – Organization (a priori trust) • p 2 p • Authentication is not sufficient to build trust Bootstrapping security associations from scratch Fully distributed Minimum dependency
 Key Management • Symmetric : – Key pre-distribution – Key agreement • Asymmetric Keys – PK Certificate = (ID, PK)CA • Self-organized CA • Web of trust(PGP) – Certificate-less • Crypto-based IDs: ID = h(PK) • ID-based Crypto: PK = f(ID) • Context-awareness – Distance Bounding Protocols – Seeing-is-believing
Key Management • Symmetric : – Key pre-distribution – Key agreement • Asymmetric Keys – PK Certificate = (ID, PK)CA • Self-organized CA • Web of trust(PGP) – Certificate-less • Crypto-based IDs: ID = h(PK) • ID-based Crypto: PK = f(ID) • Context-awareness – Distance Bounding Protocols – Seeing-is-believing
 Key pre-distribution • Sensor Networks – TTP-based [Eschenauer, Gligor ACM CCS’ 02, H. Chan, A. Perrig et al, Oakland’ 03] [Wenliang Du et al, INFOCOM’ 04] • Ad Hoc version – no TTP [A. Chan, INFOCOM’ 04] Distributed key setup by randomly choosing key rings from a public key space • Cover-Free Family Algorithm • Neighbors determine intersection of their key rings using homomorphic encryption
Key pre-distribution • Sensor Networks – TTP-based [Eschenauer, Gligor ACM CCS’ 02, H. Chan, A. Perrig et al, Oakland’ 03] [Wenliang Du et al, INFOCOM’ 04] • Ad Hoc version – no TTP [A. Chan, INFOCOM’ 04] Distributed key setup by randomly choosing key rings from a public key space • Cover-Free Family Algorithm • Neighbors determine intersection of their key rings using homomorphic encryption
![(ID, PK) binding Self-organized CA [Zhou, Haas] [Kong, et al. ] [Yi, Kravets] [Lehane, (ID, PK) binding Self-organized CA [Zhou, Haas] [Kong, et al. ] [Yi, Kravets] [Lehane,](https://present5.com/presentation/0e26e594d98af82ad1e9e94c8a83da2d/image-8.jpg) (ID, PK) binding Self-organized CA [Zhou, Haas] [Kong, et al. ] [Yi, Kravets] [Lehane, et al. ] [Bechler et al, INFOCOM’ 04] • Based on threshold cryptography [cert(PKi)]SK 1 PKi [cert(PKi)]SKi CERT(PKi)SK [cert(PKi)]SK 1 [cert(PKi)]SK 2 … [cert(PKi)]SK 2 [cert(PKi)]Ski … Verification of CERT(PKi)SK by any node using well known PK • PROs: distributed, self-organized • CONs: share distribution during bootstrap phase, network density, Sybil attack
(ID, PK) binding Self-organized CA [Zhou, Haas] [Kong, et al. ] [Yi, Kravets] [Lehane, et al. ] [Bechler et al, INFOCOM’ 04] • Based on threshold cryptography [cert(PKi)]SK 1 PKi [cert(PKi)]SKi CERT(PKi)SK [cert(PKi)]SK 1 [cert(PKi)]SK 2 … [cert(PKi)]SK 2 [cert(PKi)]Ski … Verification of CERT(PKi)SK by any node using well known PK • PROs: distributed, self-organized • CONs: share distribution during bootstrap phase, network density, Sybil attack
![(ID, PK) binding Web of Trust (PGP) [Hubaux, Buttyan, Capkun] • No CA • (ID, PK) binding Web of Trust (PGP) [Hubaux, Buttyan, Capkun] • No CA •](https://present5.com/presentation/0e26e594d98af82ad1e9e94c8a83da2d/image-9.jpg) (ID, PK) binding Web of Trust (PGP) [Hubaux, Buttyan, Capkun] • No CA • Alice Bob and Bob Eve Alice Eve • Merging of certificate repositories • PROs: no centralized TTP • CONs: initialization, storage, transitivity of trust
(ID, PK) binding Web of Trust (PGP) [Hubaux, Buttyan, Capkun] • No CA • Alice Bob and Bob Eve Alice Eve • Merging of certificate repositories • PROs: no centralized TTP • CONs: initialization, storage, transitivity of trust
![(ID, PK) binding Crypto-based ID • SPKI [Rivest] • Statistically Unique Cryptographically Verifiable IDs (ID, PK) binding Crypto-based ID • SPKI [Rivest] • Statistically Unique Cryptographically Verifiable IDs](https://present5.com/presentation/0e26e594d98af82ad1e9e94c8a83da2d/image-10.jpg) (ID, PK) binding Crypto-based ID • SPKI [Rivest] • Statistically Unique Cryptographically Verifiable IDs [O’Shea, Roe] [Montenegro, Castellucia] IPv 6 @ = NW Prefix | h(PK) • DSR using SUCV-based IP addresses [Bobba, et al] PROs: no certificates, no CA CONs: generation of bogus IDs
(ID, PK) binding Crypto-based ID • SPKI [Rivest] • Statistically Unique Cryptographically Verifiable IDs [O’Shea, Roe] [Montenegro, Castellucia] IPv 6 @ = NW Prefix | h(PK) • DSR using SUCV-based IP addresses [Bobba, et al] PROs: no certificates, no CA CONs: generation of bogus IDs
![(ID, PK) binding ID-based Crypto [Halili, Katz, Arbaugh] Based on [Boneh, Franklin, CRYPTO 2001] (ID, PK) binding ID-based Crypto [Halili, Katz, Arbaugh] Based on [Boneh, Franklin, CRYPTO 2001]](https://present5.com/presentation/0e26e594d98af82ad1e9e94c8a83da2d/image-11.jpg) (ID, PK) binding ID-based Crypto [Halili, Katz, Arbaugh] Based on [Boneh, Franklin, CRYPTO 2001] • ID-based – PK = h(ID) – SK computed by TTP • Threshold Crypto to distribute TTP PROs: no certificates, no centralized server CONs: distribution of initial shares
(ID, PK) binding ID-based Crypto [Halili, Katz, Arbaugh] Based on [Boneh, Franklin, CRYPTO 2001] • ID-based – PK = h(ID) – SK computed by TTP • Threshold Crypto to distribute TTP PROs: no certificates, no centralized server CONs: distribution of initial shares
 Trust • Managed environment – A-priori trust – Authentication trustworthiness – But: • requirement for infrastructure • scarcity of computing resources (sensors) • lack of connectivity (sensors, ad hoc nw) • Open environment – No a-priori trust – authentication does not guarantee correct operation → New paradigms – Trust establishment protocols (history, e-cash, …) [Bussard, Molva, Roudier, Per. Com’ 04, Per. Sec’ 04, i. Trust’ 04] – Reputation
Trust • Managed environment – A-priori trust – Authentication trustworthiness – But: • requirement for infrastructure • scarcity of computing resources (sensors) • lack of connectivity (sensors, ad hoc nw) • Open environment – No a-priori trust – authentication does not guarantee correct operation → New paradigms – Trust establishment protocols (history, e-cash, …) [Bussard, Molva, Roudier, Per. Com’ 04, Per. Sec’ 04, i. Trust’ 04] – Reputation
![Cooperation enforcement Token-based [Yang, Meng, Lu] Nuglets [Buttyan, Hubaux] SPRITE [Zhong, Chen, Yang] Threshold Cooperation enforcement Token-based [Yang, Meng, Lu] Nuglets [Buttyan, Hubaux] SPRITE [Zhong, Chen, Yang] Threshold](https://present5.com/presentation/0e26e594d98af82ad1e9e94c8a83da2d/image-13.jpg) Cooperation enforcement Token-based [Yang, Meng, Lu] Nuglets [Buttyan, Hubaux] SPRITE [Zhong, Chen, Yang] Threshold cryptography Micro-payment CONFIDANT[Buchegger, Le Boudec] CORE [Michiardi, Molva] Beta-Reputation [Josang, Ismail] Reputation-based Bittorrent (P 2 P) Built-in with Application
Cooperation enforcement Token-based [Yang, Meng, Lu] Nuglets [Buttyan, Hubaux] SPRITE [Zhong, Chen, Yang] Threshold cryptography Micro-payment CONFIDANT[Buchegger, Le Boudec] CORE [Michiardi, Molva] Beta-Reputation [Josang, Ismail] Reputation-based Bittorrent (P 2 P) Built-in with Application
 Summary • Main research focus – Bootstrapping from scratch – New trust paradigms – Optimization (computation, bandwidth) • Solutions yet to come. . . • Interesting applications of cryptography • Some untruths and non-sense Room for creativity
Summary • Main research focus – Bootstrapping from scratch – New trust paradigms – Optimization (computation, bandwidth) • Solutions yet to come. . . • Interesting applications of cryptography • Some untruths and non-sense Room for creativity
 New Challenges • Opportunistic Communications – No end-to-end connectivity – Collapsed system (Application=network) – Data eventually reaches destination Ø Trust management Ø Forwarding of encrypted data Ø Network coding and cryptography Ø Data aggregation
New Challenges • Opportunistic Communications – No end-to-end connectivity – Collapsed system (Application=network) – Data eventually reaches destination Ø Trust management Ø Forwarding of encrypted data Ø Network coding and cryptography Ø Data aggregation
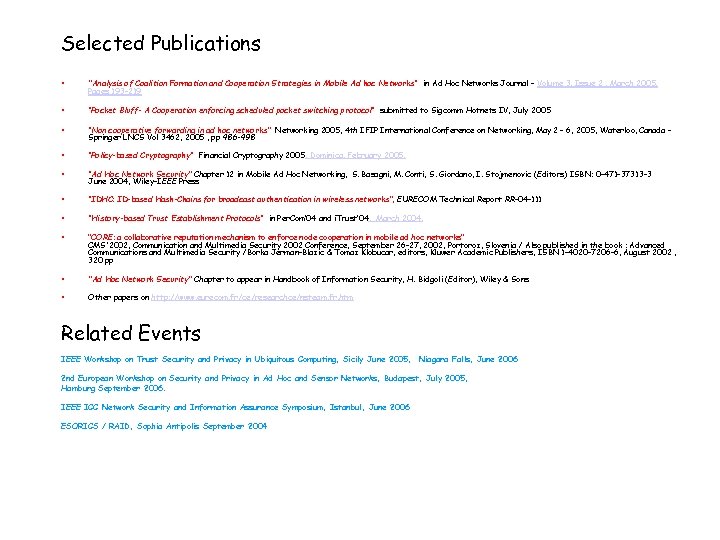 Selected Publications • "Analysis of Coalition Formation and Cooperation Strategies in Mobile Ad hoc Networks“ in Ad Hoc Networks Journal – Volume 3, Issue 2 , March 2005, Pages 193 -219 • “Pocket Bluff- A Cooperation enforcing scheduled pocket switching protocol“ submitted to Sigcomm Hotnets IV, July 2005 • “Non cooperative forwarding in ad hoc networks” Networking 2005, 4 th IFIP International Conference on Networking, May 2 - 6, 2005, Waterloo, Canada Springer LNCS Vol 3462, 2005 , pp 486 -498 • “Policy-based Cryptography“ Financial Cryptography 2005, Dominica, February 2005. • “Ad Hoc Network Security” Chapter 12 in Mobile Ad Hoc Networking, S. Basagni, M. Conti, S. Giordano, I. Stojmenovic (Editors) ISBN: 0 -471 -37313 -3 June 2004, Wiley-IEEE Press • “IDHC: ID-based Hash-Chains for broadcast authentication in wireless networks”, EURECOM Technical Report RR-04 -111 • “History-based Trust Establishment Protocols“ in Per. Com’ 04 and i. Trust’ 04, March 2004. • “CORE: a collaborative reputation mechanism to enforce node cooperation in mobile ad hoc networks” CMS'2002, Communication and Multimedia Security 2002 Conference, September 26 -27, 2002, Portoroz, Slovenia / Also published in the book : Advanced Communications and Multimedia Security /Borka Jerman-Blazic & Tomaz Klobucar, editors, Kluwer Academic Publishers, ISBN 1 -4020 -7206 -6, August 2002 , 320 pp • "Ad Hoc Network Security" Chapter to appear in Handbook of Information Security, H. Bidgoli (Editor), Wiley & Sons • Other papers on http: //www. eurecom. fr/ce/researchce/nsteam. fr. htm Related Events IEEE Workshop on Trust Security and Privacy in Ubiquitous Computing, Sicily June 2005, Niagara Falls, June 2006 2 nd European Workshop on Security and Privacy in Ad Hoc and Sensor Networks, Budapest, July 2005, Hamburg September 2006. IEEE ICC Network Security and Information Assurance Symposium, Istanbul, June 2006 ESORICS / RAID, Sophia Antipolis September 2004
Selected Publications • "Analysis of Coalition Formation and Cooperation Strategies in Mobile Ad hoc Networks“ in Ad Hoc Networks Journal – Volume 3, Issue 2 , March 2005, Pages 193 -219 • “Pocket Bluff- A Cooperation enforcing scheduled pocket switching protocol“ submitted to Sigcomm Hotnets IV, July 2005 • “Non cooperative forwarding in ad hoc networks” Networking 2005, 4 th IFIP International Conference on Networking, May 2 - 6, 2005, Waterloo, Canada Springer LNCS Vol 3462, 2005 , pp 486 -498 • “Policy-based Cryptography“ Financial Cryptography 2005, Dominica, February 2005. • “Ad Hoc Network Security” Chapter 12 in Mobile Ad Hoc Networking, S. Basagni, M. Conti, S. Giordano, I. Stojmenovic (Editors) ISBN: 0 -471 -37313 -3 June 2004, Wiley-IEEE Press • “IDHC: ID-based Hash-Chains for broadcast authentication in wireless networks”, EURECOM Technical Report RR-04 -111 • “History-based Trust Establishment Protocols“ in Per. Com’ 04 and i. Trust’ 04, March 2004. • “CORE: a collaborative reputation mechanism to enforce node cooperation in mobile ad hoc networks” CMS'2002, Communication and Multimedia Security 2002 Conference, September 26 -27, 2002, Portoroz, Slovenia / Also published in the book : Advanced Communications and Multimedia Security /Borka Jerman-Blazic & Tomaz Klobucar, editors, Kluwer Academic Publishers, ISBN 1 -4020 -7206 -6, August 2002 , 320 pp • "Ad Hoc Network Security" Chapter to appear in Handbook of Information Security, H. Bidgoli (Editor), Wiley & Sons • Other papers on http: //www. eurecom. fr/ce/researchce/nsteam. fr. htm Related Events IEEE Workshop on Trust Security and Privacy in Ubiquitous Computing, Sicily June 2005, Niagara Falls, June 2006 2 nd European Workshop on Security and Privacy in Ad Hoc and Sensor Networks, Budapest, July 2005, Hamburg September 2006. IEEE ICC Network Security and Information Assurance Symposium, Istanbul, June 2006 ESORICS / RAID, Sophia Antipolis September 2004


