f2f71e0ca44b8be79a3a02c381b91921.ppt
- Количество слайдов: 40
 Security in OPC Unified Architecture (UA) Dick Oyen Industrial. Sys. Dev, Inc.
Security in OPC Unified Architecture (UA) Dick Oyen Industrial. Sys. Dev, Inc.
 Introducing Myself Dick Oyen, Industrial. Sys. Dev, Inc. • Editor of the Security part of OPC UA • ISA SP 99 contributor • Developed control systems as a Sr R&D Engineer with ABB and Bailey Controls since 1977 • Started Industrial. Sys. Dev in Sept 2006
Introducing Myself Dick Oyen, Industrial. Sys. Dev, Inc. • Editor of the Security part of OPC UA • ISA SP 99 contributor • Developed control systems as a Sr R&D Engineer with ABB and Bailey Controls since 1977 • Started Industrial. Sys. Dev in Sept 2006
 Who are you in the audience? You … 1. have heard of OPC? 2. know that UA replaces DA, AE, HDA? 3. know something about SSL/TLS or PKI?
Who are you in the audience? You … 1. have heard of OPC? 2. know that UA replaces DA, AE, HDA? 3. know something about SSL/TLS or PKI?
 Topics • • What OPC UA is Security objectives OPC UA security architecture UA meets the objectives
Topics • • What OPC UA is Security objectives OPC UA security architecture UA meets the objectives
 Topics ØWhat OPC UA is • Security objectives • OPC UA security architecture • UA meets the objectives
Topics ØWhat OPC UA is • Security objectives • OPC UA security architecture • UA meets the objectives
 OPC until Now • A client-server standard for communicating process information • Until now, an object model based on COM – uses DCOM • Three parallel standards – OPC DA – OPC AE – OPC HDA
OPC until Now • A client-server standard for communicating process information • Until now, an object model based on COM – uses DCOM • Three parallel standards – OPC DA – OPC AE – OPC HDA
 Starting now; OPC UA • “Unified Architecture” • Unifies the three OPC standards • Web Services based – Move to improved and current base standard – To be system-independent • Now being prototyped
Starting now; OPC UA • “Unified Architecture” • Unifies the three OPC standards • Web Services based – Move to improved and current base standard – To be system-independent • Now being prototyped
 Topics • What OPC UA is ØWhat OPC UA is • Security objectives ØSecurity objectives • • OPC UA security architecture UA meets the objectives
Topics • What OPC UA is ØWhat OPC UA is • Security objectives ØSecurity objectives • • OPC UA security architecture UA meets the objectives
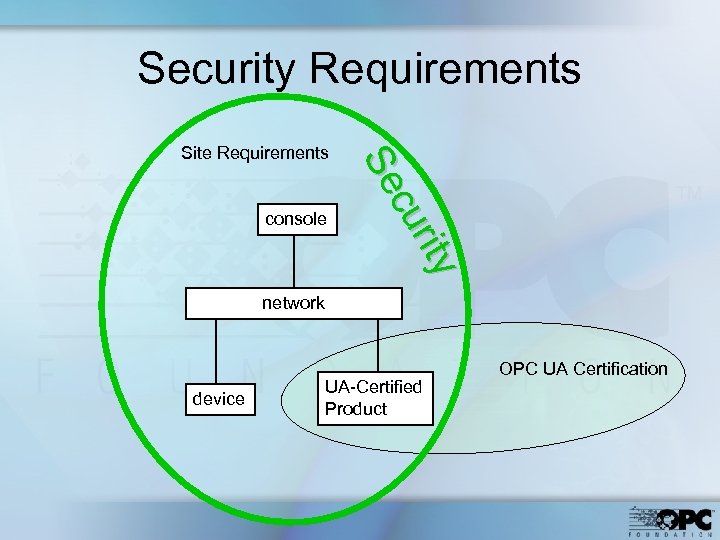 Security Requirements console r y riitty cu cu Se Se Site Requirements network device UA-Certified Product OPC UA Certification
Security Requirements console r y riitty cu cu Se Se Site Requirements network device UA-Certified Product OPC UA Certification
 Site Requirements Could include: • Policy • Procedures • Physical boundaries • Network zones • Access control • Malware countermeasures
Site Requirements Could include: • Policy • Procedures • Physical boundaries • Network zones • Access control • Malware countermeasures
 OPC UA Product Requirements • OPC UA certified products – must provide the OPC UA security functions • OPC UA security functions – are optional at the site – support site requirements
OPC UA Product Requirements • OPC UA certified products – must provide the OPC UA security functions • OPC UA security functions – are optional at the site – support site requirements
 OPC UA Security Objectives • • • Authentication Authorization Confidentiality Integrity Auditability Availability
OPC UA Security Objectives • • • Authentication Authorization Confidentiality Integrity Auditability Availability
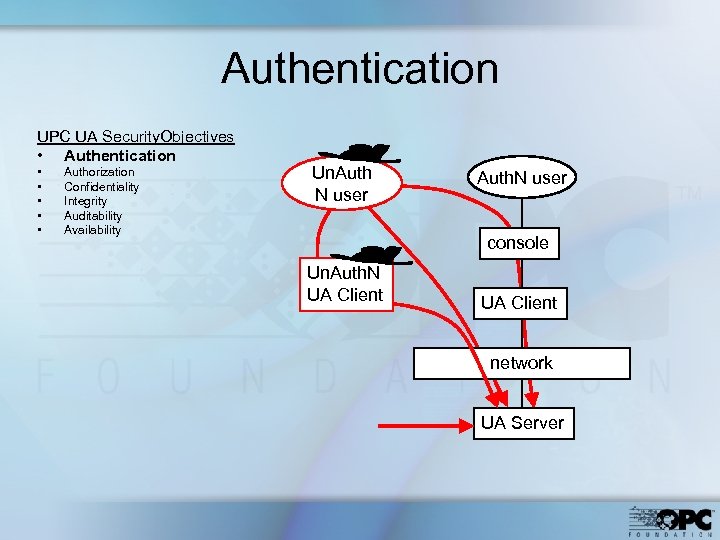 Authentication UPC UA Security. Objectives • Authentication • • • Authorization Confidentiality Integrity Auditability Availability Un. Auth N user Auth. N user console Un. Auth. N UA Client network UA Server
Authentication UPC UA Security. Objectives • Authentication • • • Authorization Confidentiality Integrity Auditability Availability Un. Auth N user Auth. N user console Un. Auth. N UA Client network UA Server
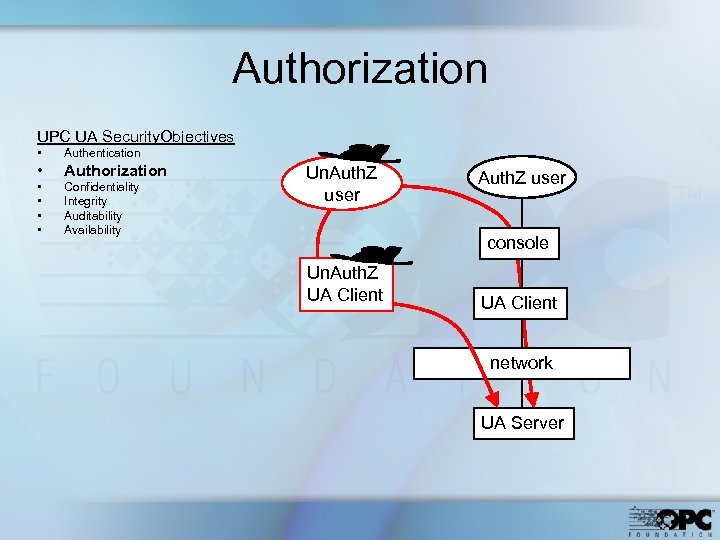 Authorization UPC UA Security. Objectives • Authentication • Authorization • • Confidentiality Integrity Auditability Availability Un. Auth. Z user console Un. Auth. Z UA Client network UA Server
Authorization UPC UA Security. Objectives • Authentication • Authorization • • Confidentiality Integrity Auditability Availability Un. Auth. Z user console Un. Auth. Z UA Client network UA Server
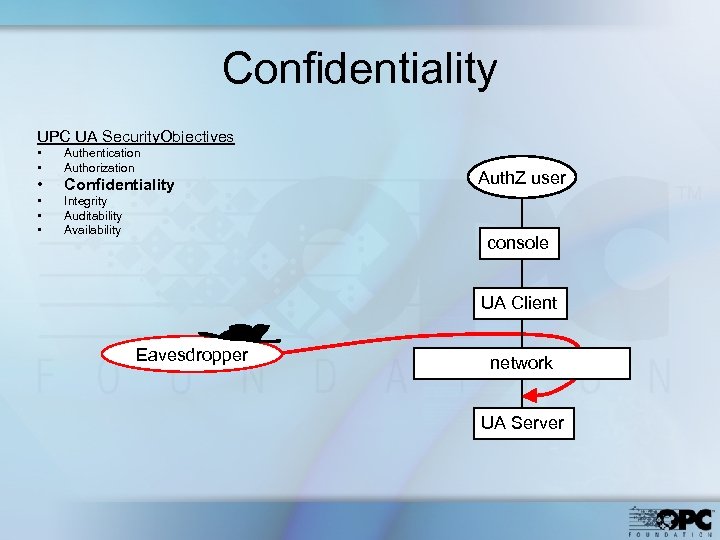 Confidentiality UPC UA Security. Objectives • • Authentication Authorization • Confidentiality • • • Integrity Auditability Availability Auth. Z user console UA Client Eavesdropper network UA Server
Confidentiality UPC UA Security. Objectives • • Authentication Authorization • Confidentiality • • • Integrity Auditability Availability Auth. Z user console UA Client Eavesdropper network UA Server
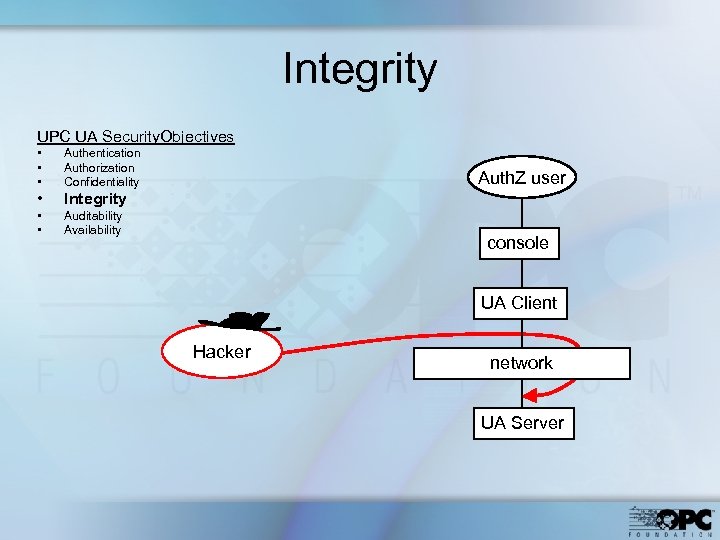 Integrity UPC UA Security. Objectives • • • Authentication Authorization Confidentiality • Integrity • • Auditability Availability Auth. Z user console UA Client Hacker network UA Server
Integrity UPC UA Security. Objectives • • • Authentication Authorization Confidentiality • Integrity • • Auditability Availability Auth. Z user console UA Client Hacker network UA Server
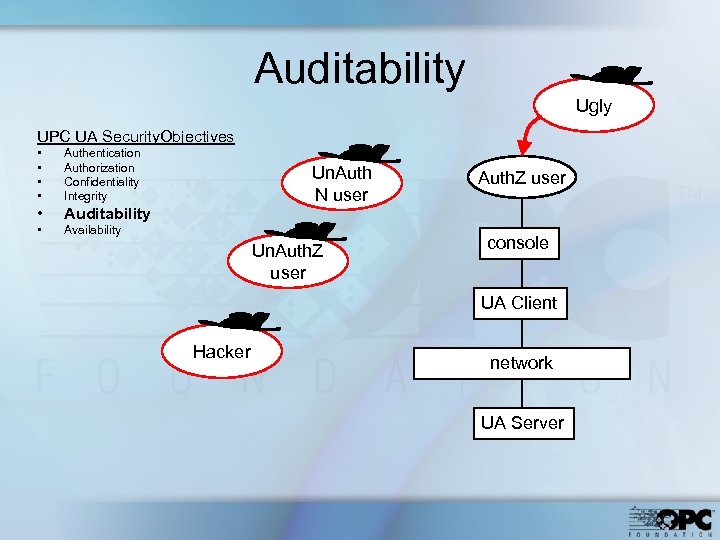 Auditability Ugly UPC UA Security. Objectives • • Authentication Authorization Confidentiality Integrity • Auditability • Availability Un. Auth N user Un. Auth. Z user console UA Client Hacker network UA Server
Auditability Ugly UPC UA Security. Objectives • • Authentication Authorization Confidentiality Integrity • Auditability • Availability Un. Auth N user Un. Auth. Z user console UA Client Hacker network UA Server
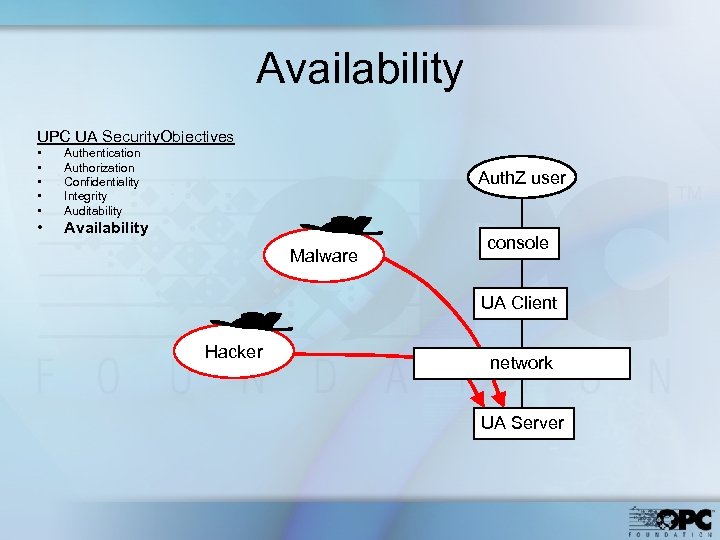 Availability UPC UA Security. Objectives • • • Authentication Authorization Confidentiality Integrity Auditability • Availability Auth. Z user Malware console UA Client Hacker network UA Server
Availability UPC UA Security. Objectives • • • Authentication Authorization Confidentiality Integrity Auditability • Availability Auth. Z user Malware console UA Client Hacker network UA Server
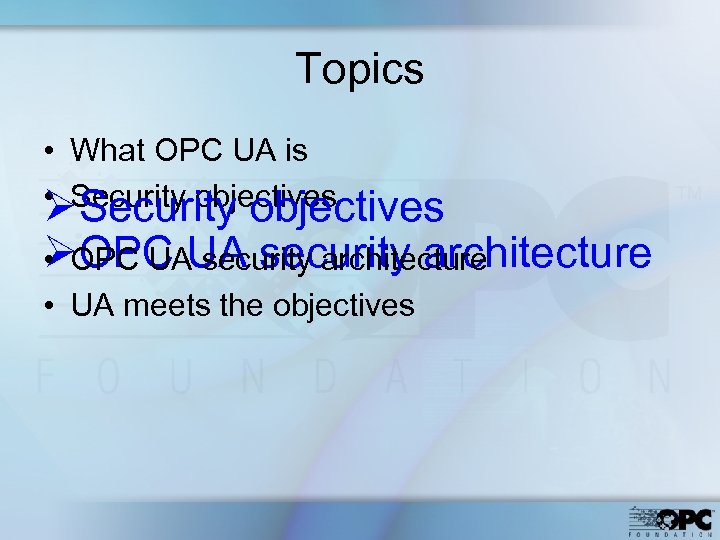 Topics • What OPC UA is • Security objectives ØOPC UAUA security architecture • OPC security architecture • UA meets the objectives
Topics • What OPC UA is • Security objectives ØOPC UAUA security architecture • OPC security architecture • UA meets the objectives
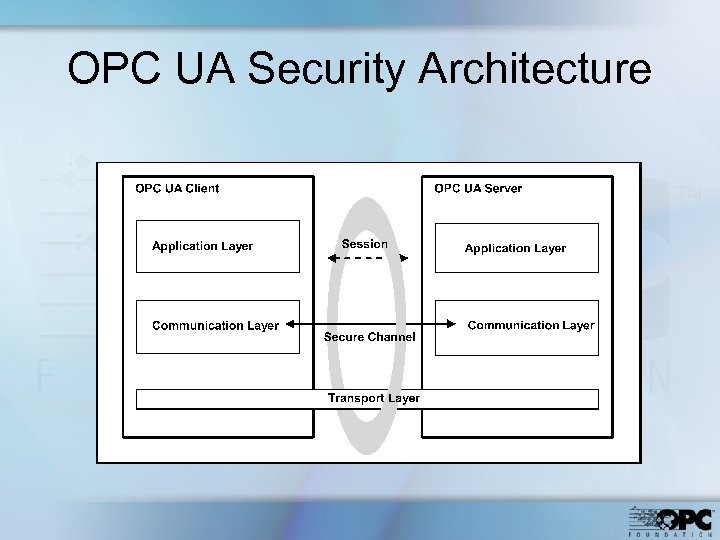 OPC UA Security Architecture
OPC UA Security Architecture
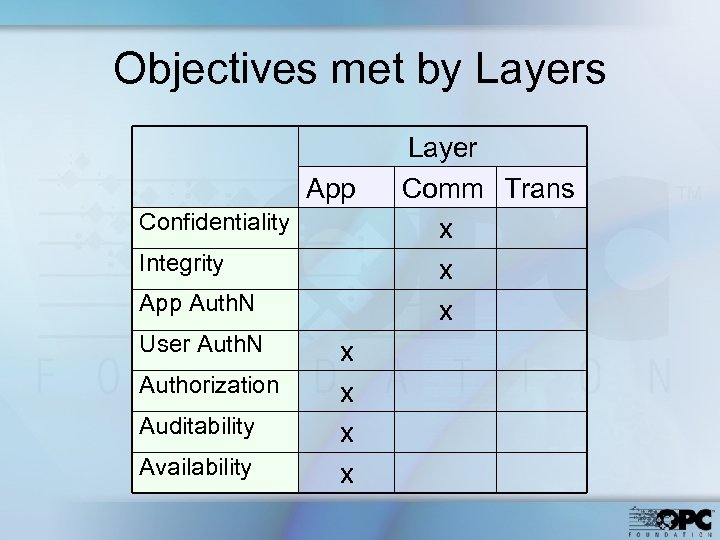 Objectives met by Layers App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm Trans x x x
Objectives met by Layers App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm Trans x x x
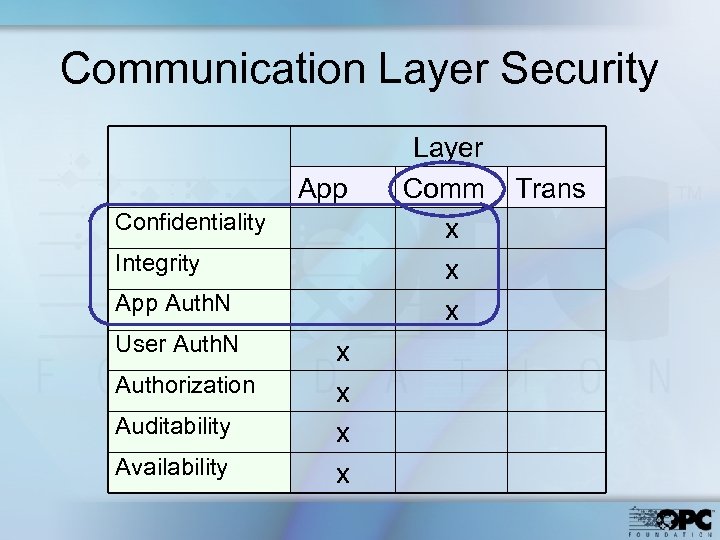 Communication Layer Security App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans
Communication Layer Security App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans
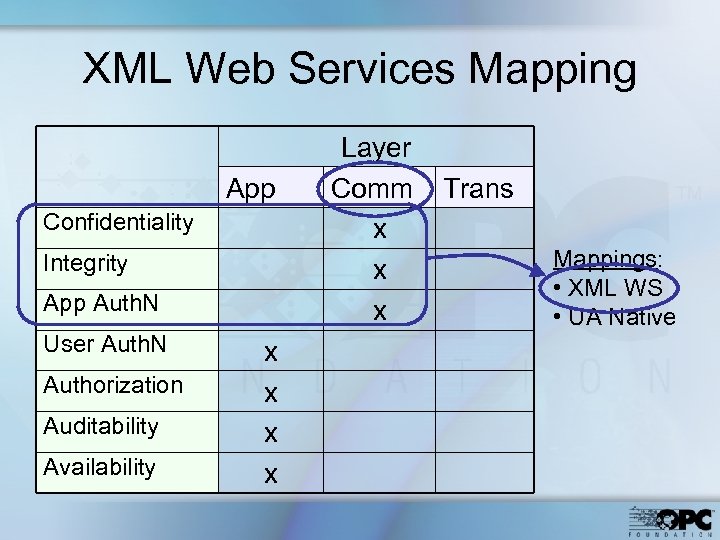 XML Web Services Mapping App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans Mappings: • XML WS • UA Native
XML Web Services Mapping App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans Mappings: • XML WS • UA Native
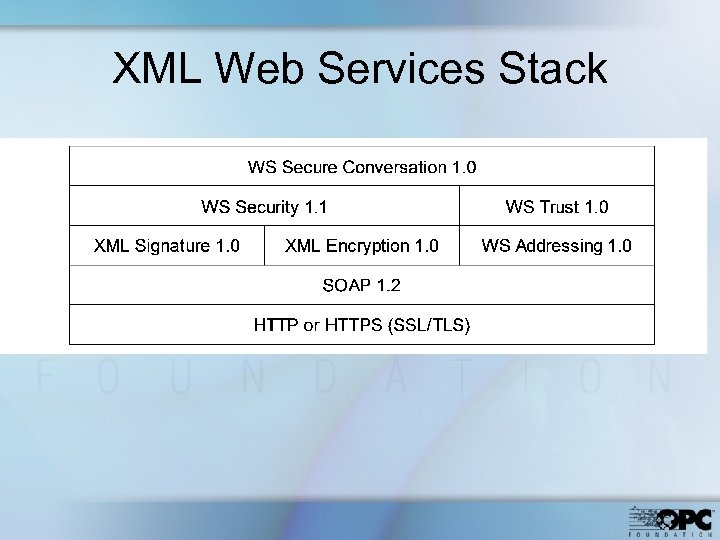 XML Web Services Stack
XML Web Services Stack
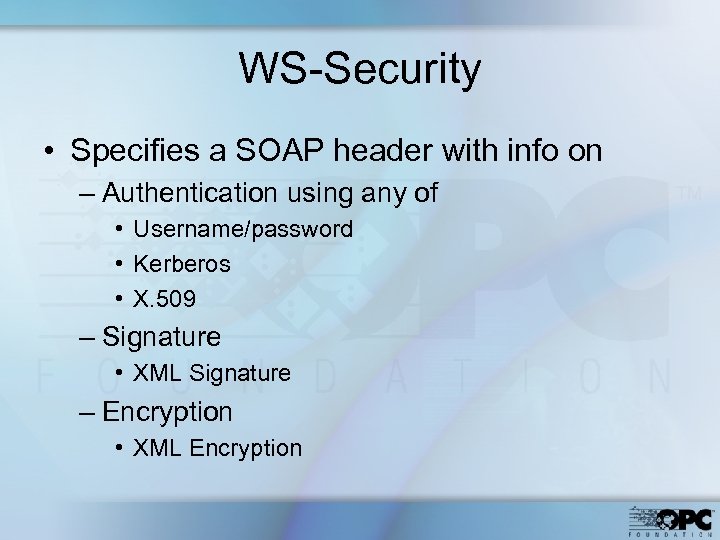 WS-Security • Specifies a SOAP header with info on – Authentication using any of • Username/password • Kerberos • X. 509 – Signature • XML Signature – Encryption • XML Encryption
WS-Security • Specifies a SOAP header with info on – Authentication using any of • Username/password • Kerberos • X. 509 – Signature • XML Signature – Encryption • XML Encryption
 WS-Trust • Validate credentials • Request and issue security tokens
WS-Trust • Validate credentials • Request and issue security tokens
 WS-Secure. Conversation • Security context establishment and sharing • Session key derivation
WS-Secure. Conversation • Security context establishment and sharing • Session key derivation
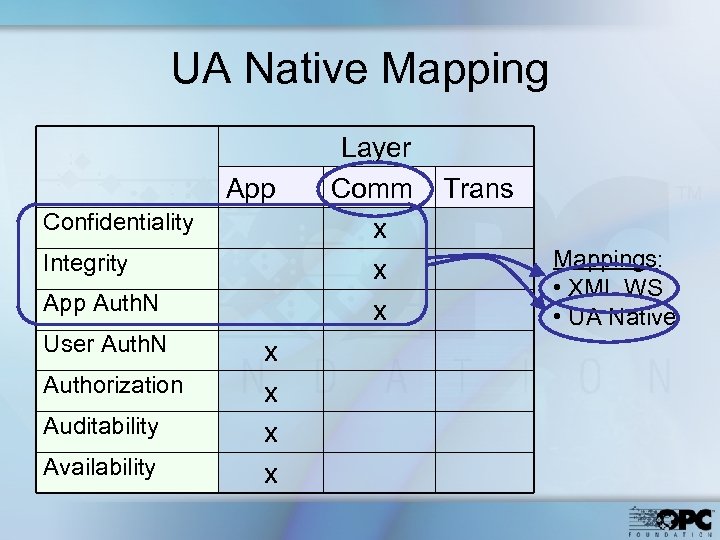 UA Native Mapping App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans Mappings: • XML WS • UA Native
UA Native Mapping App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans Mappings: • XML WS • UA Native
 UA Native Mapping • UA Native Mapping available when WS is not (controllers, etc. ) • The product supplier develops the implementations of these layers • Manages secure channel
UA Native Mapping • UA Native Mapping available when WS is not (controllers, etc. ) • The product supplier develops the implementations of these layers • Manages secure channel
 App Authentication – UA Native • Application X. 509 Certificates are exchanged when the secure channel is established
App Authentication – UA Native • Application X. 509 Certificates are exchanged when the secure channel is established
 Integrity – UA Native • No messages altered – sign the messages • HMAC or RSA encryption • SHA 1 hash – change the key periodically • Message sequence not altered – Nonce – Time stamp
Integrity – UA Native • No messages altered – sign the messages • HMAC or RSA encryption • SHA 1 hash – change the key periodically • Message sequence not altered – Nonce – Time stamp
 Confidentiality – UA Native • Options – Encrypt only channel management – Encrypt all messages • Encryption – AES if symmetric – RSA if asymmetric
Confidentiality – UA Native • Options – Encrypt only channel management – Encrypt all messages • Encryption – AES if symmetric – RSA if asymmetric
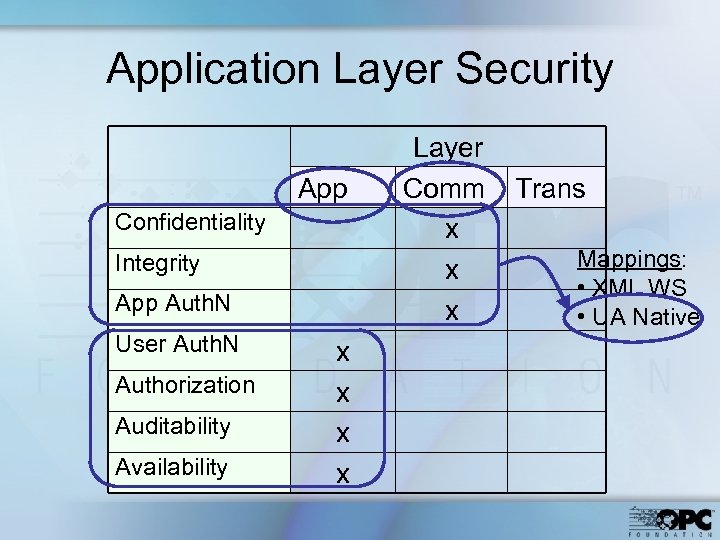 Application Layer Security App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans Mappings: • XML WS • UA Native
Application Layer Security App Confidentiality Integrity App Auth. N User Auth. N Authorization Auditability Availability x x Layer Comm x x x Trans Mappings: • XML WS • UA Native
 User Authentication • OPC UA defines optional user security token types – X. 509 – Username / password • Server application can validate the user’s token
User Authentication • OPC UA defines optional user security token types – X. 509 – Username / password • Server application can validate the user’s token
 User Authorization • Application product developer – specifies user authorization scheme – implements scheme in client application
User Authorization • Application product developer – specifies user authorization scheme – implements scheme in client application
 Auditing • All security events are recorded • Traceable through intermediate nodes • For interoperability – Minimum required set of logged parameters
Auditing • All security events are recorded • Traceable through intermediate nodes • For interoperability – Minimum required set of logged parameters
 Availability • Depends primarily on the Site for protection • Minimum processing before authentication
Availability • Depends primarily on the Site for protection • Minimum processing before authentication
 Topics • What OPC UA is • Security objectives • OPC UA security architecture ØUA meets the objectives • UA meets the objectives
Topics • What OPC UA is • Security objectives • OPC UA security architecture ØUA meets the objectives • UA meets the objectives
 UA meets Objectives • Authentication – Certificates – Challenge-response • Authorization – Implemented per product • Confidentiality – Encryption • Integrity – Changing keys • Auditability – Traceable log entries • Availability – Minimal processing before Auth. N
UA meets Objectives • Authentication – Certificates – Challenge-response • Authorization – Implemented per product • Confidentiality – Encryption • Integrity – Changing keys • Auditability – Traceable log entries • Availability – Minimal processing before Auth. N
 Further Info • Tom Burke presentation at 2: 00 today • www. OPCFoundation. org – Articles for non-members – UA specifications for members • dick_oyen@hotmail. com
Further Info • Tom Burke presentation at 2: 00 today • www. OPCFoundation. org – Articles for non-members – UA specifications for members • dick_oyen@hotmail. com


