64535ca52019b527adf4ad6a3b6bd4a4.ppt
- Количество слайдов: 40
 Security assessment of the E-valg system Erik Nordin erik. b. nordin@combitech. se Fredrik Holgersson fredrik. holgersson@combitech. se Emilie Barse emilie. barse@combitech. se 1
Security assessment of the E-valg system Erik Nordin erik. b. nordin@combitech. se Fredrik Holgersson fredrik. holgersson@combitech. se Emilie Barse emilie. barse@combitech. se 1
 Agenda § Evalg 2011 - Introduction § Technical solution § Security assessment and results § What happens next?
Agenda § Evalg 2011 - Introduction § Technical solution § Security assessment and results § What happens next?
 Introduction to Evalg 2011 On monday evening, September 12 th 2011, experts and observers from around the world gathered in the auditorium of the government district, building R 5, to witness the counting process of Norway's first electronic election for local governments. This presentation deals with project experience, technical solution, results and future. . .
Introduction to Evalg 2011 On monday evening, September 12 th 2011, experts and observers from around the world gathered in the auditorium of the government district, building R 5, to witness the counting process of Norway's first electronic election for local governments. This presentation deals with project experience, technical solution, results and future. . .
 Introduction film (7 min)
Introduction film (7 min)
![Customer § Ministry of local government and regional development § [Kommunal- og regionaldepartementet (KRD)] Customer § Ministry of local government and regional development § [Kommunal- og regionaldepartementet (KRD)]](https://present5.com/presentation/64535ca52019b527adf4ad6a3b6bd4a4/image-5.jpg) Customer § Ministry of local government and regional development § [Kommunal- og regionaldepartementet (KRD)] Christian Bull / responsible for security in Evalg project
Customer § Ministry of local government and regional development § [Kommunal- og regionaldepartementet (KRD)] Christian Bull / responsible for security in Evalg project
 Technical solution
Technical solution
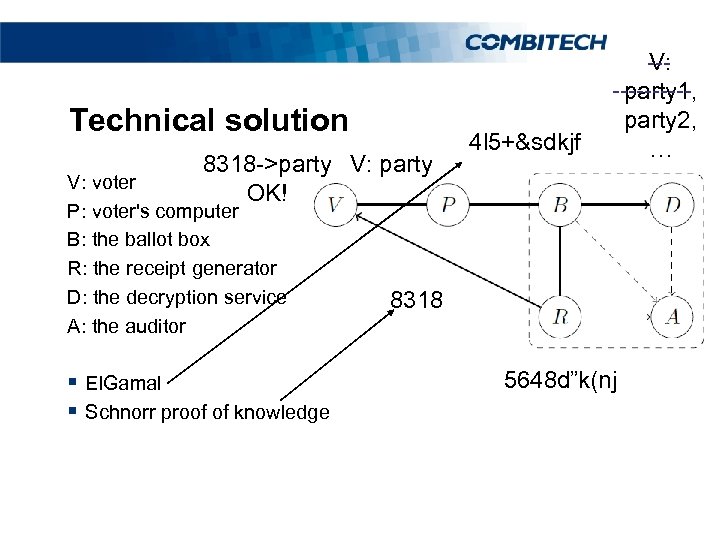 Technical solution 8318 ->party V: party OK! V: voter P: voter's computer B: the ballot box R: the receipt generator D: the decryption service A: the auditor § El. Gamal § Schnorr proof of knowledge 4 l 5+&sdkjf --V: -----party 1, party 2, … 8318 5648 d”k(nj
Technical solution 8318 ->party V: party OK! V: voter P: voter's computer B: the ballot box R: the receipt generator D: the decryption service A: the auditor § El. Gamal § Schnorr proof of knowledge 4 l 5+&sdkjf --V: -----party 1, party 2, … 8318 5648 d”k(nj
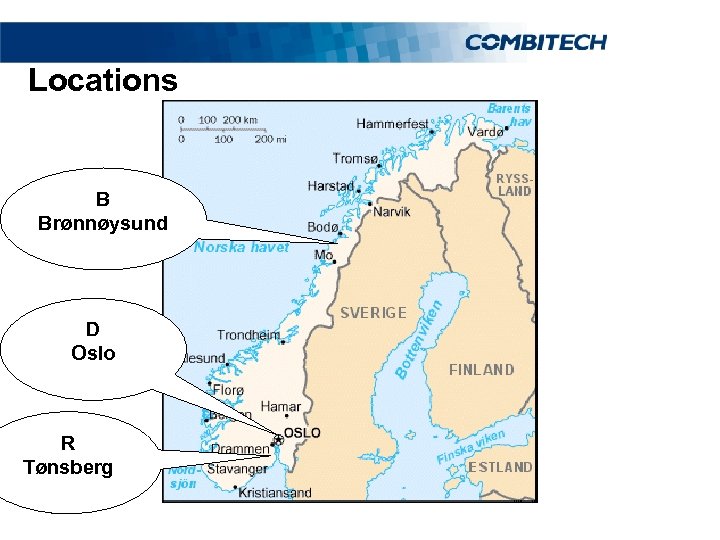 Locations B Brønnøysund D Oslo R Tønsberg
Locations B Brønnøysund D Oslo R Tønsberg
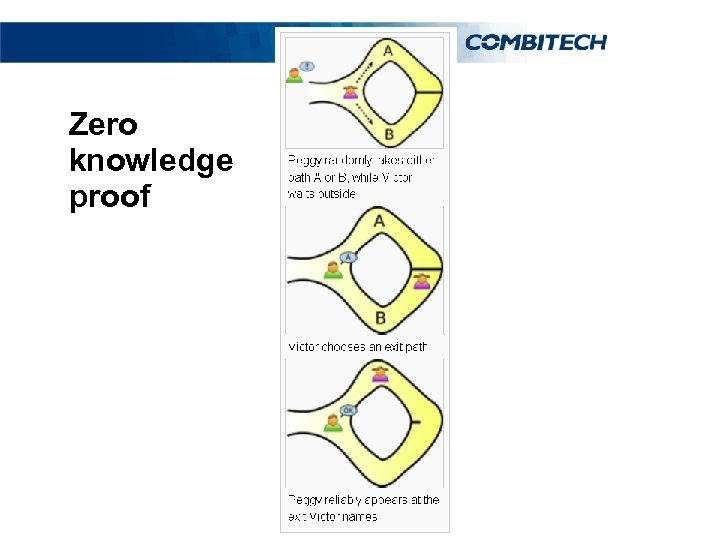 Zero knowledge proof
Zero knowledge proof
 EDB Ergogroup § Developed e-voting solution via the Internet. § EDB Ergo. Group SYSteam is one of the leading IT § players with approximately 10 000 employees and annual sales of almost SEK 16 billion. The company is listed on the Oslo Stock Exchange with headquarters in Oslo and has a significant presence in both the Norwegian and Swedish market with 135 offices in 16 countries worldwide. http: //www. edbergogroup. com/
EDB Ergogroup § Developed e-voting solution via the Internet. § EDB Ergo. Group SYSteam is one of the leading IT § players with approximately 10 000 employees and annual sales of almost SEK 16 billion. The company is listed on the Oslo Stock Exchange with headquarters in Oslo and has a significant presence in both the Norwegian and Swedish market with 135 offices in 16 countries worldwide. http: //www. edbergogroup. com/
 Scytl § Spanish company § Subcontractor to EDB Ergo. Group § Implementation of the security functions § Scytl, worldwide leader in the development of secure § solutions for electoral modernization. http: //www. scytl. com/
Scytl § Spanish company § Subcontractor to EDB Ergo. Group § Implementation of the security functions § Scytl, worldwide leader in the development of secure § solutions for electoral modernization. http: //www. scytl. com/
 Combitech § Swedish IT consulting company § Independent security evaluations § http: //www. combitech. se/
Combitech § Swedish IT consulting company § Independent security evaluations § http: //www. combitech. se/
 Security assessment § Transparency vs. Secrecy? § Source Code and documentation § Testing Methodology/Restrictions § Results § http: //source. evalg. stat. no
Security assessment § Transparency vs. Secrecy? § Source Code and documentation § Testing Methodology/Restrictions § Results § http: //source. evalg. stat. no
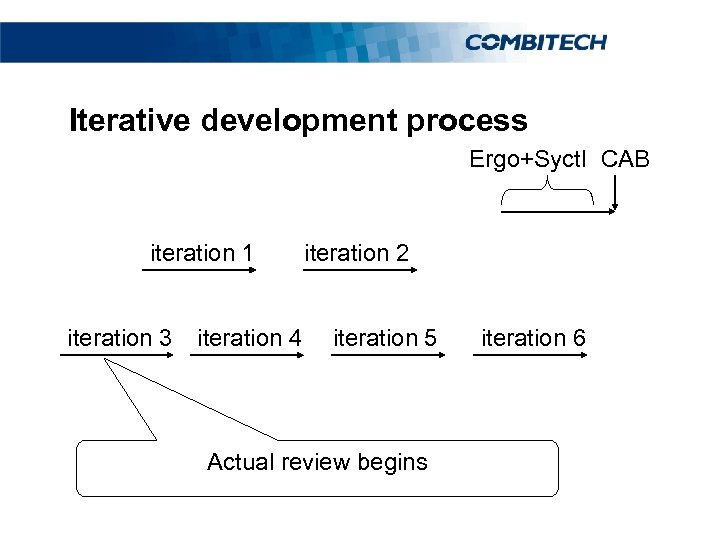 Iterative development process Ergo+Syctl CAB iteration 1 iteration 3 iteration 4 iteration 2 iteration 5 Actual review begins iteration 6
Iterative development process Ergo+Syctl CAB iteration 1 iteration 3 iteration 4 iteration 2 iteration 5 Actual review begins iteration 6
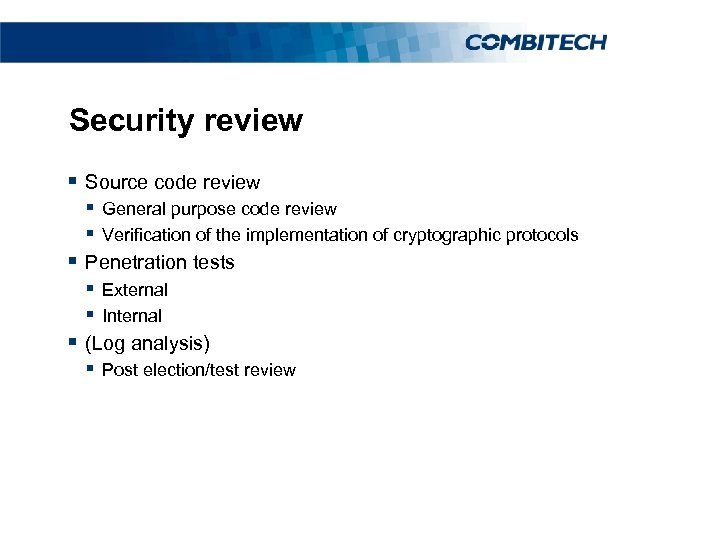 Security review § Source code review § General purpose code review § Verification of the implementation of cryptographic protocols § Penetration tests § External § Internal § (Log analysis) § Post election/test review
Security review § Source code review § General purpose code review § Verification of the implementation of cryptographic protocols § Penetration tests § External § Internal § (Log analysis) § Post election/test review
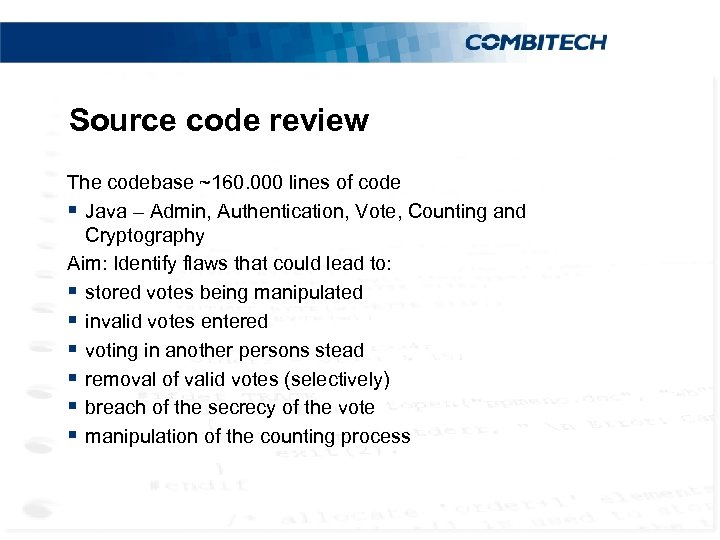 Source code review The codebase ~160. 000 lines of code § Java – Admin, Authentication, Vote, Counting and Cryptography Aim: Identify flaws that could lead to: § stored votes being manipulated § invalid votes entered § voting in another persons stead § removal of valid votes (selectively) § breach of the secrecy of the vote § manipulation of the counting process
Source code review The codebase ~160. 000 lines of code § Java – Admin, Authentication, Vote, Counting and Cryptography Aim: Identify flaws that could lead to: § stored votes being manipulated § invalid votes entered § voting in another persons stead § removal of valid votes (selectively) § breach of the secrecy of the vote § manipulation of the counting process
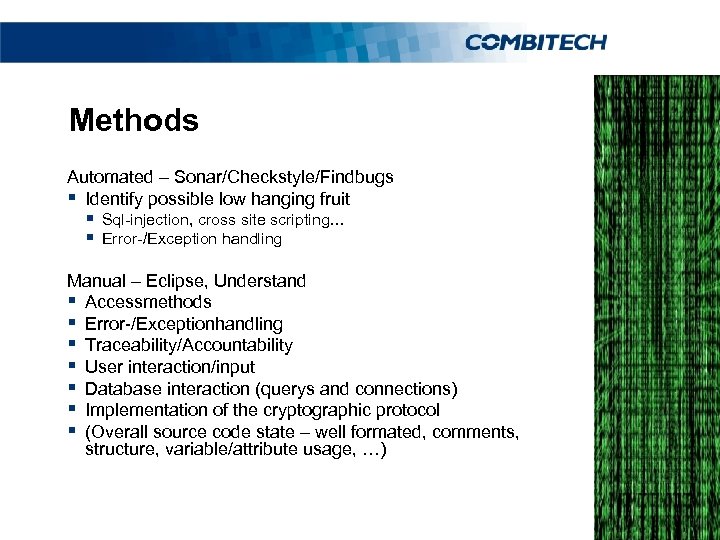 Methods Automated – Sonar/Checkstyle/Findbugs § Identify possible low hanging fruit § Sql-injection, cross site scripting… § Error-/Exception handling Manual – Eclipse, Understand § Accessmethods § Error-/Exceptionhandling § Traceability/Accountability § User interaction/input § Database interaction (querys and connections) § Implementation of the cryptographic protocol § (Overall source code state – well formated, comments, structure, variable/attribute usage, …)
Methods Automated – Sonar/Checkstyle/Findbugs § Identify possible low hanging fruit § Sql-injection, cross site scripting… § Error-/Exception handling Manual – Eclipse, Understand § Accessmethods § Error-/Exceptionhandling § Traceability/Accountability § User interaction/input § Database interaction (querys and connections) § Implementation of the cryptographic protocol § (Overall source code state – well formated, comments, structure, variable/attribute usage, …)
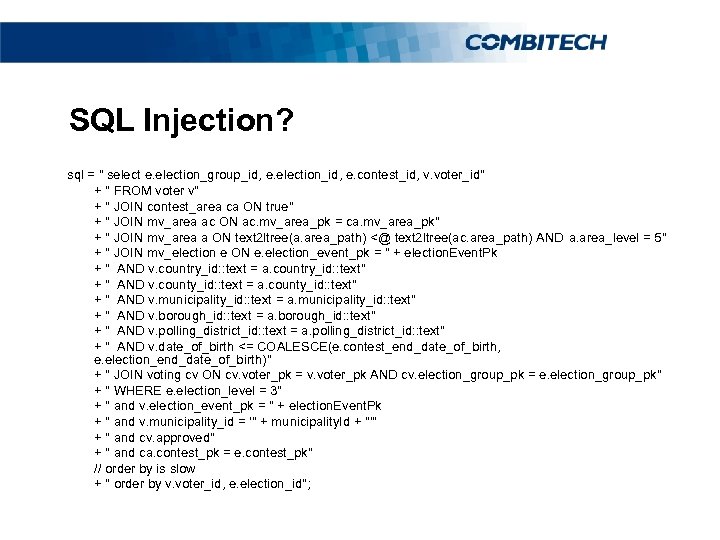 SQL Injection? sql = " select e. election_group_id, e. election_id, e. contest_id, v. voter_id" + " FROM voter v" + " JOIN contest_area ca ON true" + " JOIN mv_area ac ON ac. mv_area_pk = ca. mv_area_pk" + " JOIN mv_area a ON text 2 ltree(a. area_path) <@ text 2 ltree(ac. area_path) AND a. area_level = 5" + " JOIN mv_election e ON e. election_event_pk = " + election. Event. Pk + " AND v. country_id: : text = a. country_id: : text" + " AND v. county_id: : text = a. county_id: : text" + " AND v. municipality_id: : text = a. municipality_id: : text" + " AND v. borough_id: : text = a. borough_id: : text" + " AND v. polling_district_id: : text = a. polling_district_id: : text" + " AND v. date_of_birth <= COALESCE(e. contest_end_date_of_birth, e. election_end_date_of_birth)" + " JOIN voting cv ON cv. voter_pk = v. voter_pk AND cv. election_group_pk = e. election_group_pk" + " WHERE e. election_level = 3" + " and v. election_event_pk = " + election. Event. Pk + " and v. municipality_id = '" + municipality. Id + "'" + " and cv. approved" + " and ca. contest_pk = e. contest_pk" // order by is slow + " order by v. voter_id, e. election_id";
SQL Injection? sql = " select e. election_group_id, e. election_id, e. contest_id, v. voter_id" + " FROM voter v" + " JOIN contest_area ca ON true" + " JOIN mv_area ac ON ac. mv_area_pk = ca. mv_area_pk" + " JOIN mv_area a ON text 2 ltree(a. area_path) <@ text 2 ltree(ac. area_path) AND a. area_level = 5" + " JOIN mv_election e ON e. election_event_pk = " + election. Event. Pk + " AND v. country_id: : text = a. country_id: : text" + " AND v. county_id: : text = a. county_id: : text" + " AND v. municipality_id: : text = a. municipality_id: : text" + " AND v. borough_id: : text = a. borough_id: : text" + " AND v. polling_district_id: : text = a. polling_district_id: : text" + " AND v. date_of_birth <= COALESCE(e. contest_end_date_of_birth, e. election_end_date_of_birth)" + " JOIN voting cv ON cv. voter_pk = v. voter_pk AND cv. election_group_pk = e. election_group_pk" + " WHERE e. election_level = 3" + " and v. election_event_pk = " + election. Event. Pk + " and v. municipality_id = '" + municipality. Id + "'" + " and cv. approved" + " and ca. contest_pk = e. contest_pk" // order by is slow + " order by v. voter_id, e. election_id";
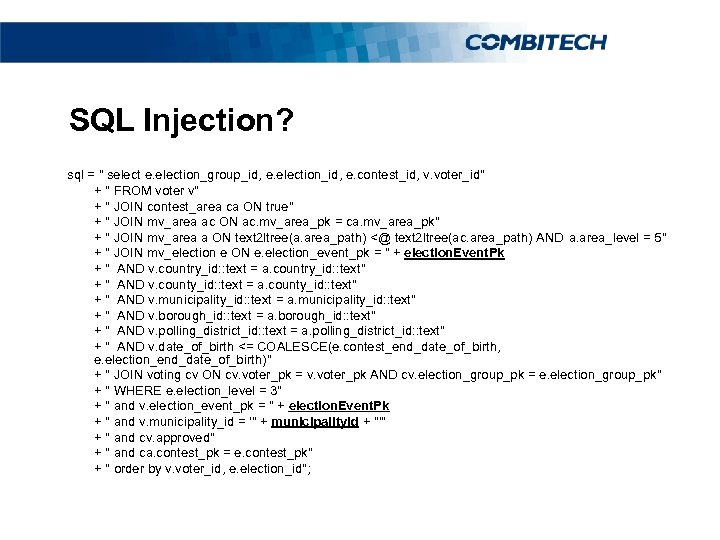 SQL Injection? sql = " select e. election_group_id, e. election_id, e. contest_id, v. voter_id" + " FROM voter v" + " JOIN contest_area ca ON true" + " JOIN mv_area ac ON ac. mv_area_pk = ca. mv_area_pk" + " JOIN mv_area a ON text 2 ltree(a. area_path) <@ text 2 ltree(ac. area_path) AND a. area_level = 5" + " JOIN mv_election e ON e. election_event_pk = " + election. Event. Pk + " AND v. country_id: : text = a. country_id: : text" + " AND v. county_id: : text = a. county_id: : text" + " AND v. municipality_id: : text = a. municipality_id: : text" + " AND v. borough_id: : text = a. borough_id: : text" + " AND v. polling_district_id: : text = a. polling_district_id: : text" + " AND v. date_of_birth <= COALESCE(e. contest_end_date_of_birth, e. election_end_date_of_birth)" + " JOIN voting cv ON cv. voter_pk = v. voter_pk AND cv. election_group_pk = e. election_group_pk" + " WHERE e. election_level = 3" + " and v. election_event_pk = " + election. Event. Pk + " and v. municipality_id = '" + municipality. Id + "'" + " and cv. approved" + " and ca. contest_pk = e. contest_pk" + " order by v. voter_id, e. election_id";
SQL Injection? sql = " select e. election_group_id, e. election_id, e. contest_id, v. voter_id" + " FROM voter v" + " JOIN contest_area ca ON true" + " JOIN mv_area ac ON ac. mv_area_pk = ca. mv_area_pk" + " JOIN mv_area a ON text 2 ltree(a. area_path) <@ text 2 ltree(ac. area_path) AND a. area_level = 5" + " JOIN mv_election e ON e. election_event_pk = " + election. Event. Pk + " AND v. country_id: : text = a. country_id: : text" + " AND v. county_id: : text = a. county_id: : text" + " AND v. municipality_id: : text = a. municipality_id: : text" + " AND v. borough_id: : text = a. borough_id: : text" + " AND v. polling_district_id: : text = a. polling_district_id: : text" + " AND v. date_of_birth <= COALESCE(e. contest_end_date_of_birth, e. election_end_date_of_birth)" + " JOIN voting cv ON cv. voter_pk = v. voter_pk AND cv. election_group_pk = e. election_group_pk" + " WHERE e. election_level = 3" + " and v. election_event_pk = " + election. Event. Pk + " and v. municipality_id = '" + municipality. Id + "'" + " and cv. approved" + " and ca. contest_pk = e. contest_pk" + " order by v. voter_id, e. election_id";
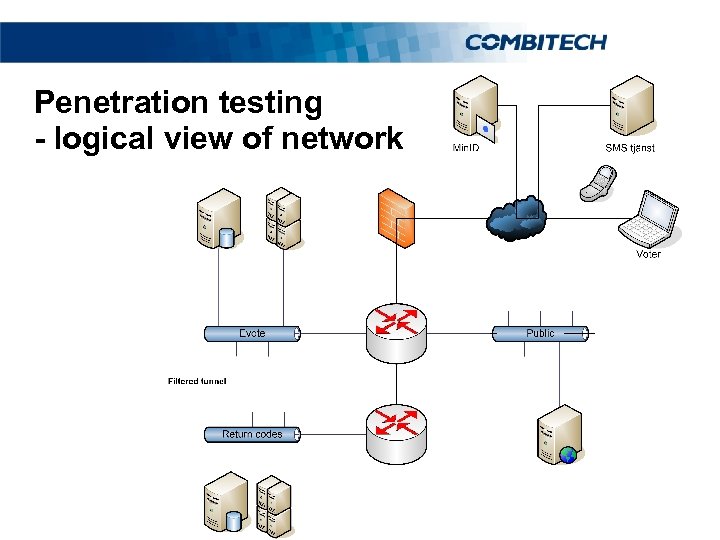 Penetration testing - logical view of network
Penetration testing - logical view of network
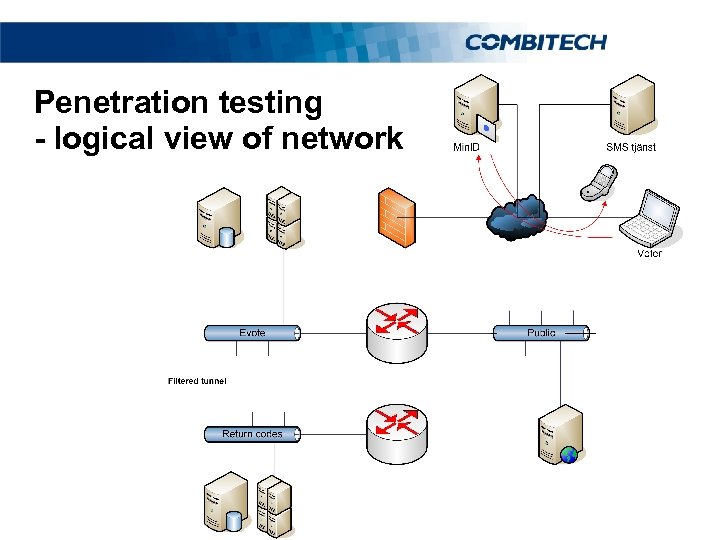 Penetration testing - logical view of network
Penetration testing - logical view of network
 Penetration testing - logical view of network
Penetration testing - logical view of network
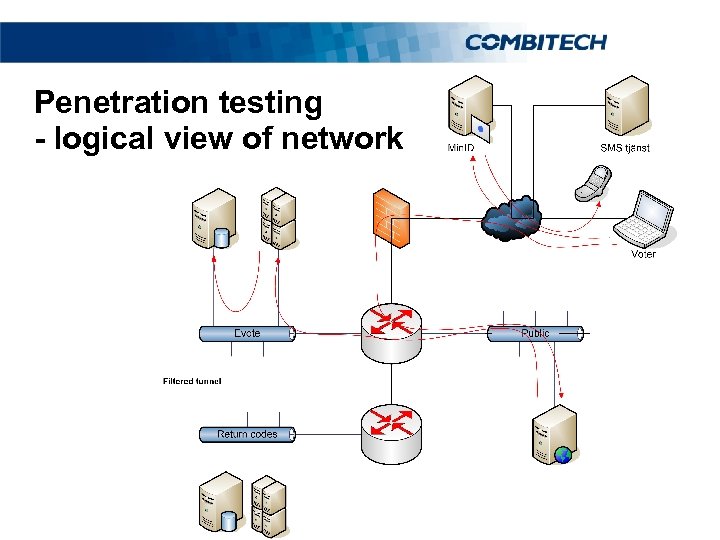 Penetration testing - logical view of network
Penetration testing - logical view of network
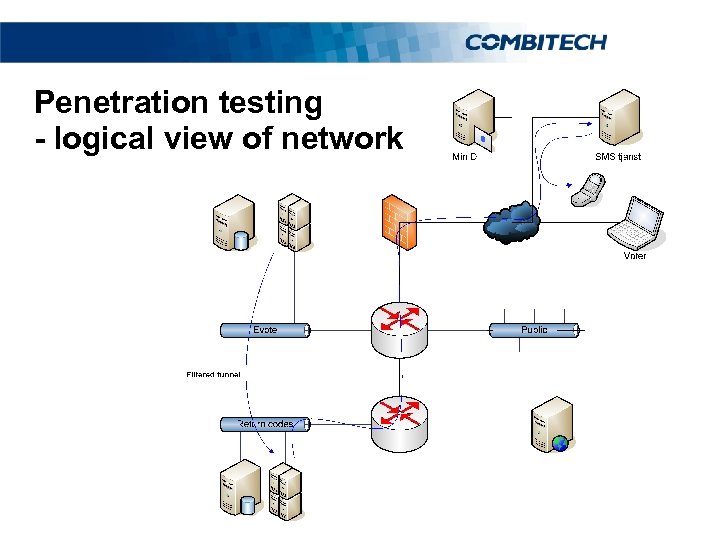 Penetration testing - logical view of network
Penetration testing - logical view of network
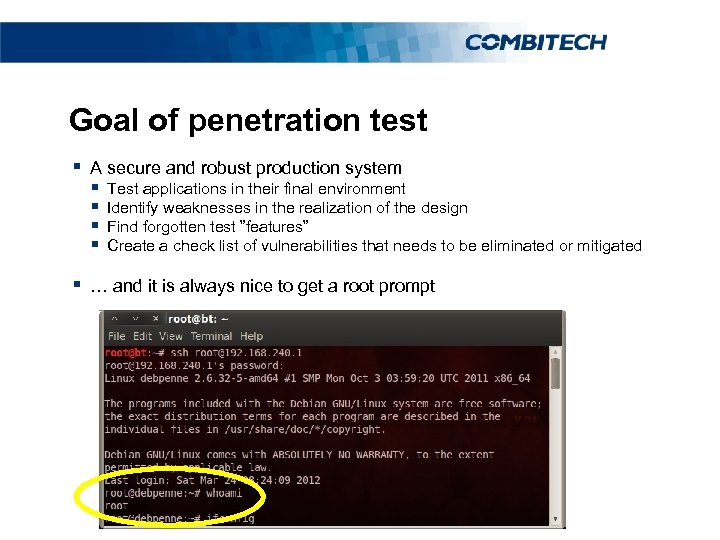 Goal of penetration test § A secure and robust production system § § Test applications in their final environment Identify weaknesses in the realization of the design Find forgotten test ”features” Create a check list of vulnerabilities that needs to be eliminated or mitigated § … and it is always nice to get a root prompt
Goal of penetration test § A secure and robust production system § § Test applications in their final environment Identify weaknesses in the realization of the design Find forgotten test ”features” Create a check list of vulnerabilities that needs to be eliminated or mitigated § … and it is always nice to get a root prompt
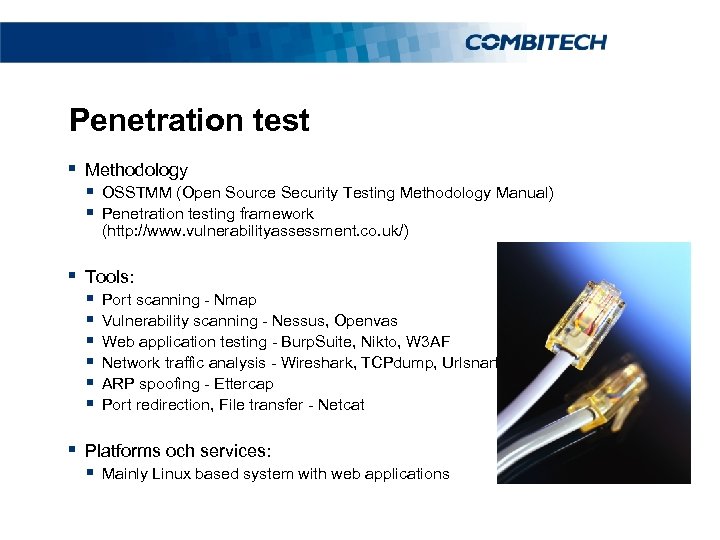 Penetration test § Methodology § OSSTMM (Open Source Security Testing Methodology Manual) § Penetration testing framework (http: //www. vulnerabilityassessment. co. uk/) § Tools: § § § Port scanning - Nmap Vulnerability scanning - Nessus, Openvas Web application testing - Burp. Suite, Nikto, W 3 AF Network traffic analysis - Wireshark, TCPdump, Urlsnarf ARP spoofing - Ettercap Port redirection, File transfer - Netcat § Platforms och services: § Mainly Linux based system with web applications
Penetration test § Methodology § OSSTMM (Open Source Security Testing Methodology Manual) § Penetration testing framework (http: //www. vulnerabilityassessment. co. uk/) § Tools: § § § Port scanning - Nmap Vulnerability scanning - Nessus, Openvas Web application testing - Burp. Suite, Nikto, W 3 AF Network traffic analysis - Wireshark, TCPdump, Urlsnarf ARP spoofing - Ettercap Port redirection, File transfer - Netcat § Platforms och services: § Mainly Linux based system with web applications
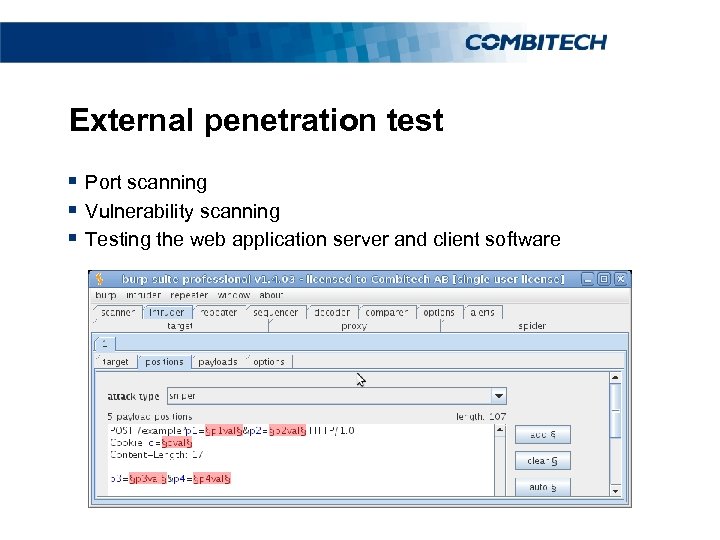 External penetration test § Port scanning § Vulnerability scanning § Testing the web application server and client software
External penetration test § Port scanning § Vulnerability scanning § Testing the web application server and client software
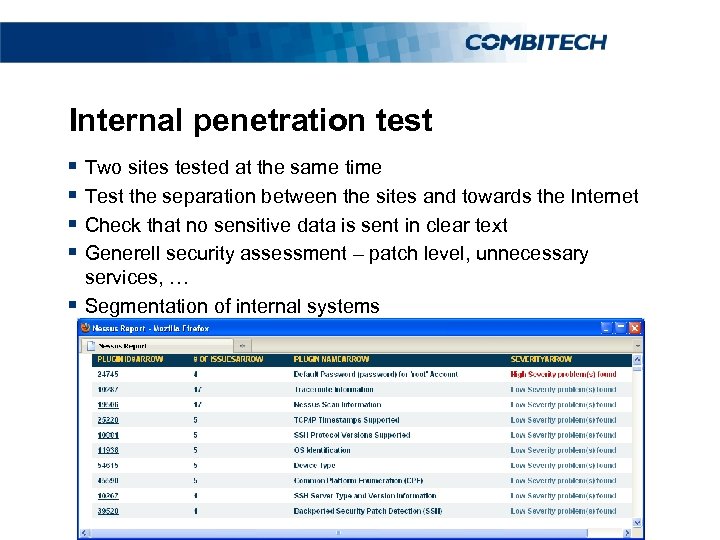 Internal penetration test § Two sites tested at the same time § Test the separation between the sites and towards the Internet § Check that no sensitive data is sent in clear text § Generell security assessment – patch level, unnecessary § services, … Segmentation of internal systems
Internal penetration test § Two sites tested at the same time § Test the separation between the sites and towards the Internet § Check that no sensitive data is sent in clear text § Generell security assessment – patch level, unnecessary § services, … Segmentation of internal systems
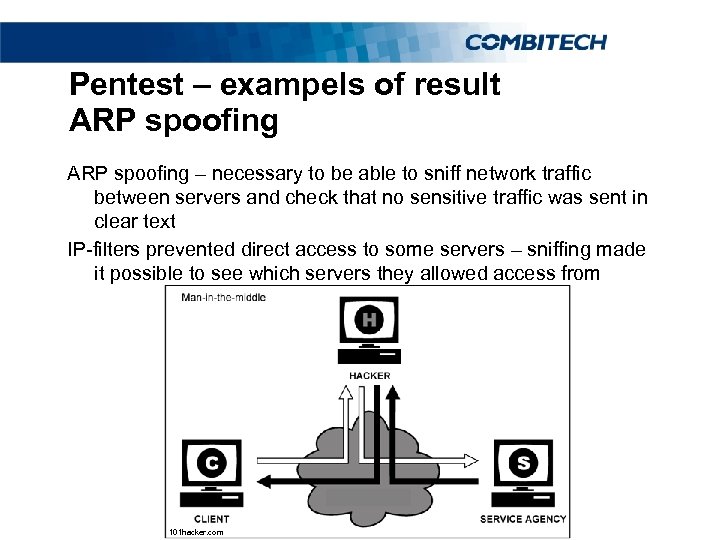 Pentest – exampels of result ARP spoofing – necessary to be able to sniff network traffic between servers and check that no sensitive traffic was sent in clear text IP-filters prevented direct access to some servers – sniffing made it possible to see which servers they allowed access from 101 hacker. com
Pentest – exampels of result ARP spoofing – necessary to be able to sniff network traffic between servers and check that no sensitive traffic was sent in clear text IP-filters prevented direct access to some servers – sniffing made it possible to see which servers they allowed access from 101 hacker. com
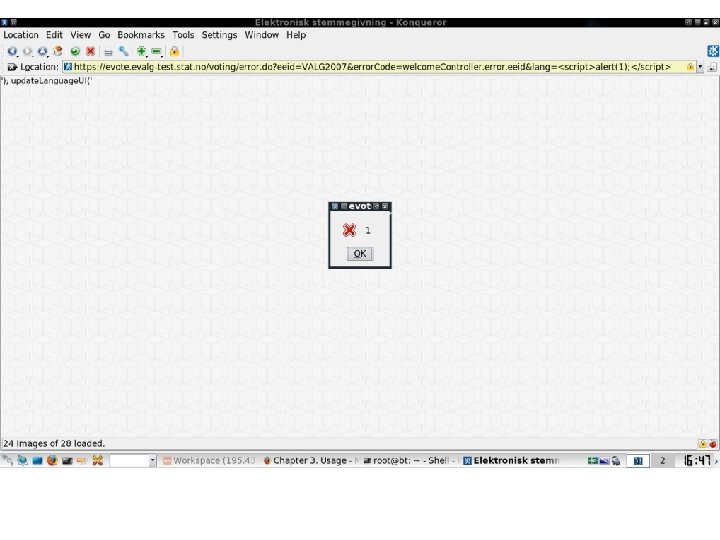 Kodgranskning – exempel på xss The vulnerable link which was identified during the test is the following: https: //195. 43. 61. 60/voting/applet/error. do? eeid=VALG 200 7&error. Code=welcome. Controller. error. eeid&lang=XSS (replacing XSS with a malicious script)
Kodgranskning – exempel på xss The vulnerable link which was identified during the test is the following: https: //195. 43. 61. 60/voting/applet/error. do? eeid=VALG 200 7&error. Code=welcome. Controller. error. eeid&lang=XSS (replacing XSS with a malicious script)
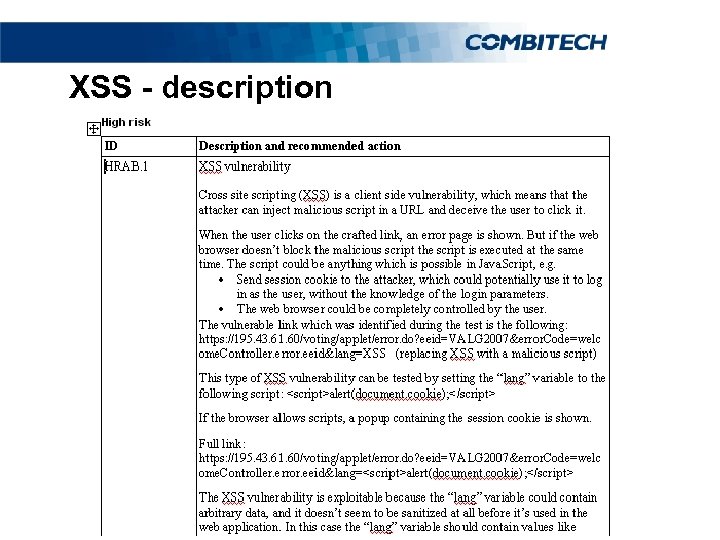 XSS - description
XSS - description
 Log analysis § Splunk § Collects web application logs § Debugging § Forensic/incident investigation
Log analysis § Splunk § Collects web application logs § Debugging § Forensic/incident investigation
 What happens next?
What happens next?
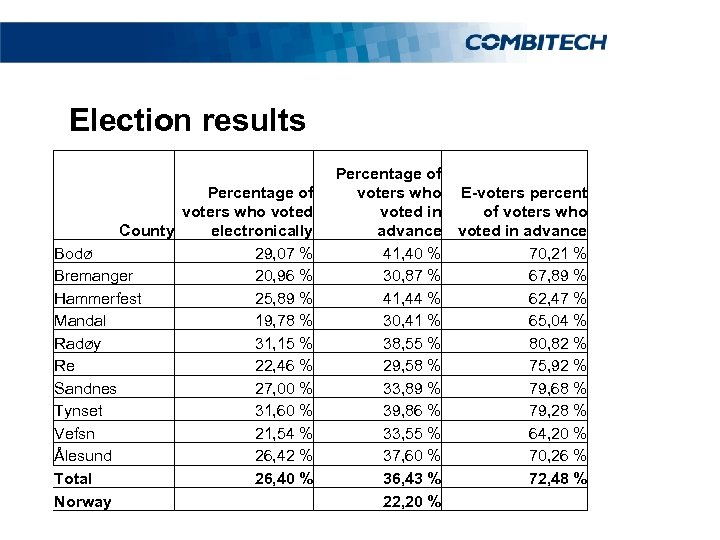 Election results Percentage of voters who voted County electronically Bodø 29, 07 % Bremanger 20, 96 % Hammerfest 25, 89 % Mandal 19, 78 % Radøy 31, 15 % Re 22, 46 % Sandnes 27, 00 % Tynset 31, 60 % Vefsn 21, 54 % Ålesund 26, 42 % Total 26, 40 % Norway Percentage of voters who voted in advance 41, 40 % 30, 87 % 41, 44 % 30, 41 % 38, 55 % 29, 58 % 33, 89 % 39, 86 % 33, 55 % 37, 60 % 36, 43 % 22, 20 % E-voters percent of voters who voted in advance 70, 21 % 67, 89 % 62, 47 % 65, 04 % 80, 82 % 75, 92 % 79, 68 % 79, 28 % 64, 20 % 70, 26 % 72, 48 %
Election results Percentage of voters who voted County electronically Bodø 29, 07 % Bremanger 20, 96 % Hammerfest 25, 89 % Mandal 19, 78 % Radøy 31, 15 % Re 22, 46 % Sandnes 27, 00 % Tynset 31, 60 % Vefsn 21, 54 % Ålesund 26, 42 % Total 26, 40 % Norway Percentage of voters who voted in advance 41, 40 % 30, 87 % 41, 44 % 30, 41 % 38, 55 % 29, 58 % 33, 89 % 39, 86 % 33, 55 % 37, 60 % 36, 43 % 22, 20 % E-voters percent of voters who voted in advance 70, 21 % 67, 89 % 62, 47 % 65, 04 % 80, 82 % 75, 92 % 79, 68 % 79, 28 % 64, 20 % 70, 26 % 72, 48 %
 More information § Project web site: http: //e-valg. dep. no § The source code is available on the Internet: http: //source. evalg. stat. no § The election system: http: //evalg. stat. no § 24/7 monitoring § Christian Bull was interviewed in Computer Sweden 2012 -0423 http: //computersweden. idg. se/2. 2683/1. 444711
More information § Project web site: http: //e-valg. dep. no § The source code is available on the Internet: http: //source. evalg. stat. no § The election system: http: //evalg. stat. no § 24/7 monitoring § Christian Bull was interviewed in Computer Sweden 2012 -0423 http: //computersweden. idg. se/2. 2683/1. 444711
 The future § 2017: Full scale national election in Norway? § Common criteria evaluation? § Sweden?
The future § 2017: Full scale national election in Norway? § Common criteria evaluation? § Sweden?
 Is E-valg secure?
Is E-valg secure?
 Is E-valg more secure than current systems?
Is E-valg more secure than current systems?
 Questions?
Questions?



