dfa1822fd34cdb4d844ff6a500105975.ppt
- Количество слайдов: 85
Security and Privacy 세종대학교 컴퓨터공학부 권태경
Contents n n n Introduction Security and privacy? Some related topics ¨ Authentication and Access Control n ¨ RFID Security n ¨ General Concepts Database Security n n Blocker Tag MANET Security n ¨ Identity Management and HCI Search on Encrypted Data Terms Revisited
Introduction
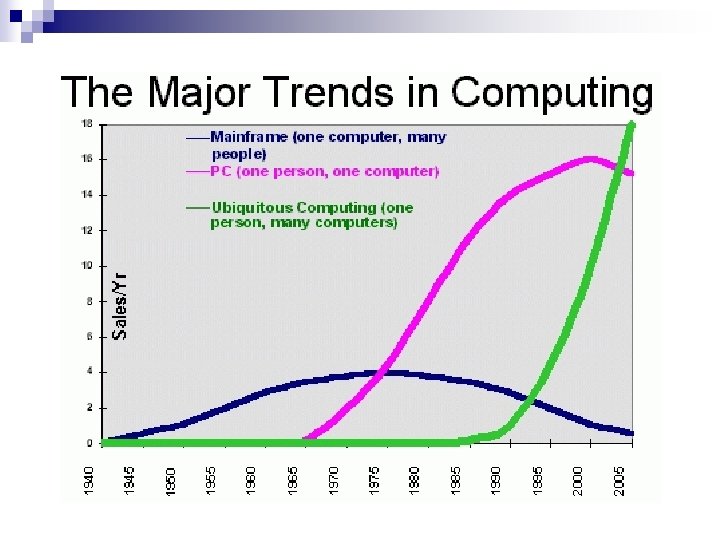

What is Ubiquitous Computing? n n “Wirelessly networked processors embedded in everyday objects” Smart environments characterized by: ¨ Transparent interaction ¨ Automated capture ¨ Context awareness ¨ Proactive and reactive n Example projects ¨ AT&T Active bat/badge, HP Cooltown, Microsoft Aura, Intel Place Lab and Personal. Server EQUATOR
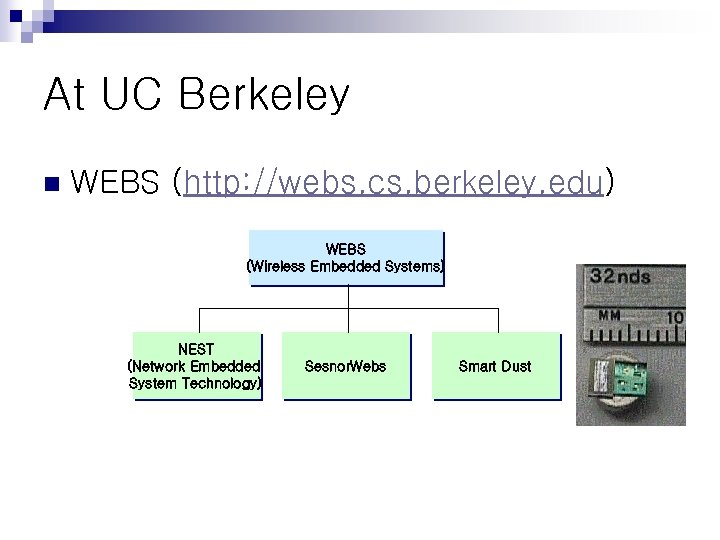
At UC Berkeley n WEBS (http: //webs. cs. berkeley. edu) WEBS (Wireless Embedded Systems) NEST (Network Embedded System Technology) Sesnor. Webs Smart Dust
Where Do We Currently Stand? n Ubiquitous devices (always “at hand”): Mobile phones, Personal Digital Assistants, Laptops, etc. ¨ Computationally bounded ¨ Limited battery ¨ n Ubiquitous networks (always available): (W)LAN/MAN (Ethernet & IEEE 802. 11) ¨ GSM/GPRS/3 G ¨ PANs (Bluetooth, Ir. DA, Audio. Net etc. ) ¨ n Ubiquitous services ¨ Currently mostly “location-based”
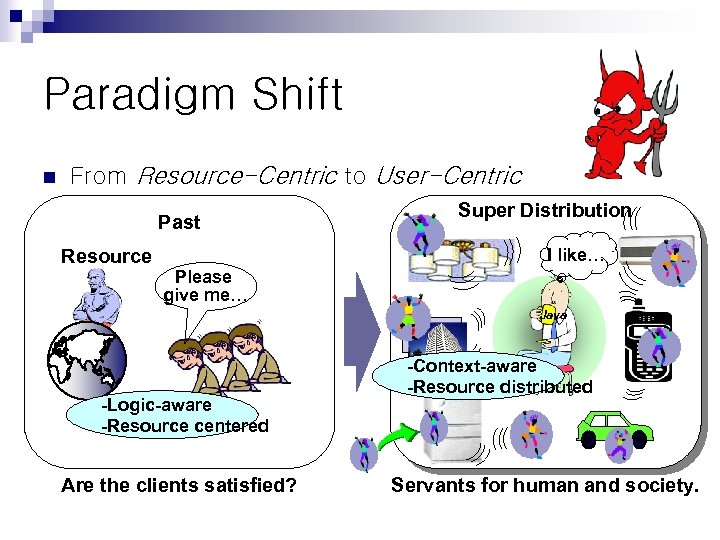
Paradigm Shift n From Resource-Centric to User-Centric Past Resource Super Distribution I like… Please give me… Java -Logic-aware -Resource centered Are the clients satisfied? -Context-aware -Resource distributed Servants for human and society.
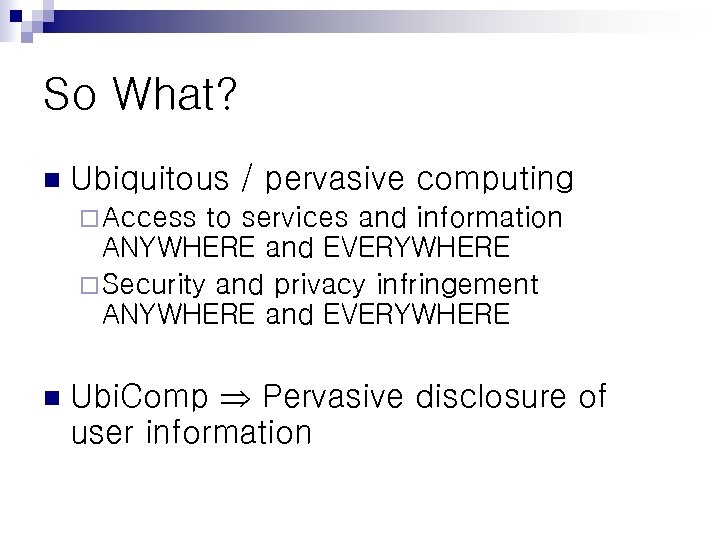
So What? n Ubiquitous / pervasive computing ¨ Access to services and information ANYWHERE and EVERYWHERE ¨ Security and privacy infringement ANYWHERE and EVERYWHERE n Ubi. Comp Pervasive disclosure of user information

Security and Privacy?
Security and Privacy? n The “Old Model” – a Castle ¨ Security perimeter, inside and outside ¨ Firewalls for access control ¨ Static security policy ¨ Static trust model ¨ Tendency to focus on network layer n Pre-evaluated, non- or slowly-evolving threat model.
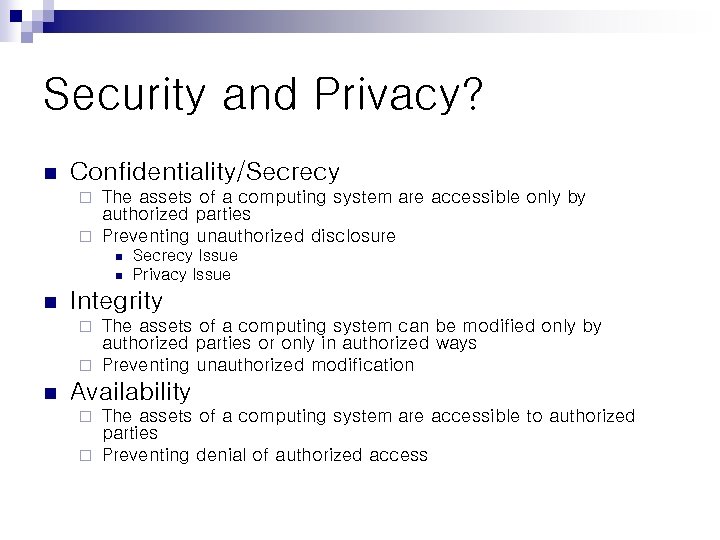
Security and Privacy? n Confidentiality/Secrecy The assets of a computing system are accessible only by authorized parties ¨ Preventing unauthorized disclosure ¨ n n n Secrecy Issue Privacy Issue Integrity The assets of a computing system can be modified only by authorized parties or only in authorized ways ¨ Preventing unauthorized modification ¨ n Availability The assets of a computing system are accessible to authorized parties ¨ Preventing denial of authorized access ¨
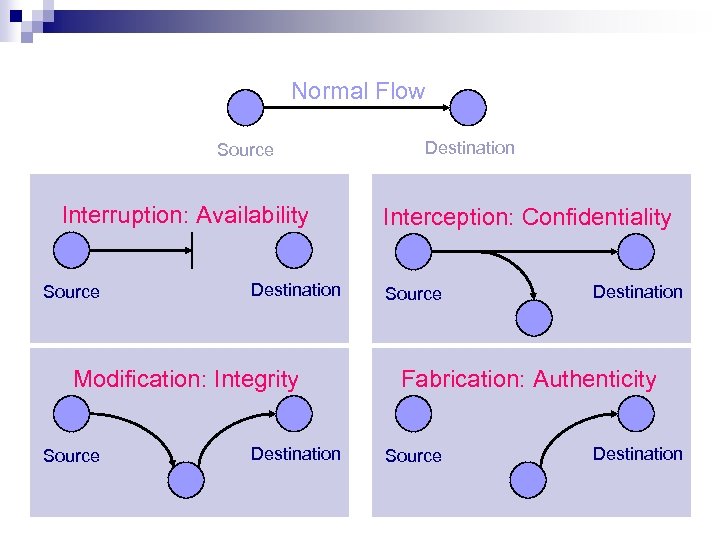
Normal Flow Source Interruption: Availability Source Destination Modification: Integrity Source Destination Interception: Confidentiality Source Destination Fabrication: Authenticity Source Destination
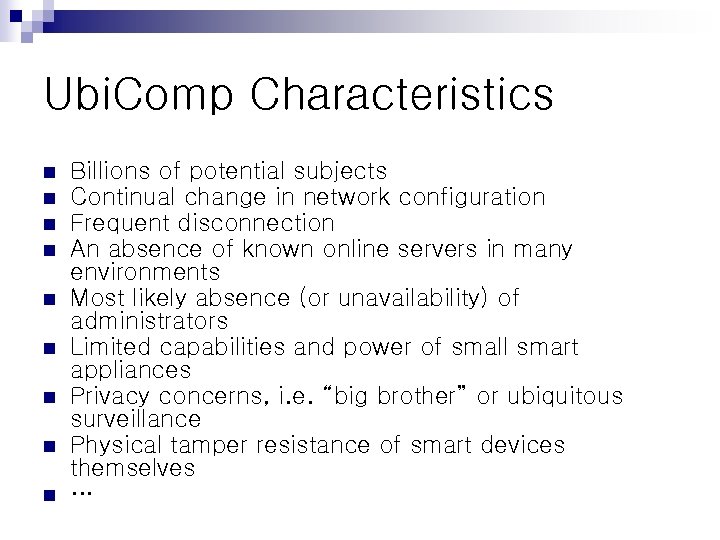
Ubi. Comp Characteristics n n n n n Billions of potential subjects Continual change in network configuration Frequent disconnection An absence of known online servers in many environments Most likely absence (or unavailability) of administrators Limited capabilities and power of small smart appliances Privacy concerns, i. e. “big brother” or ubiquitous surveillance Physical tamper resistance of smart devices themselves …
Security and Privacy! n The “New Model” which is flexible, adaptable, robust, effective and unobtrusive
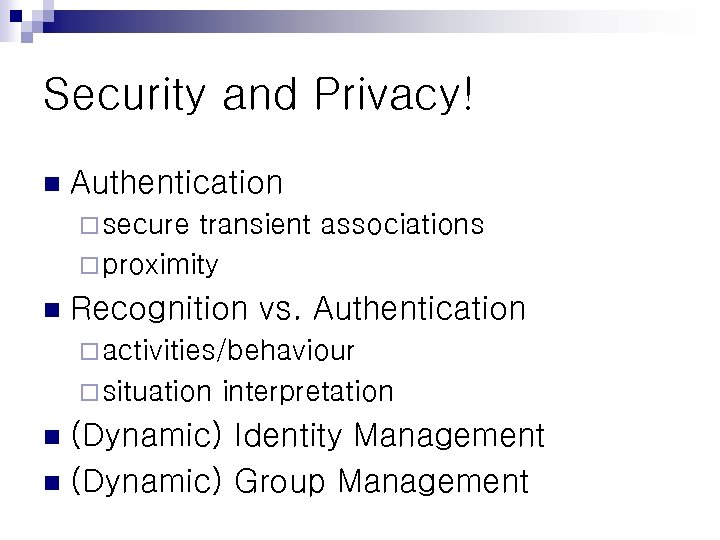
Security and Privacy! n Authentication ¨ secure transient associations ¨ proximity n Recognition vs. Authentication ¨ activities/behaviour ¨ situation interpretation (Dynamic) Identity Management n (Dynamic) Group Management n

Security and Privacy! n Confidentiality ¨ eavesdropping on wireless links not a major issue ¨ device capabilities (processor, battery etc. ) ¨ confidentiality of data and meta data on devices real problem n Integrity ¨ again, not messages in transit but devices ¨ tamper resistance/evidence
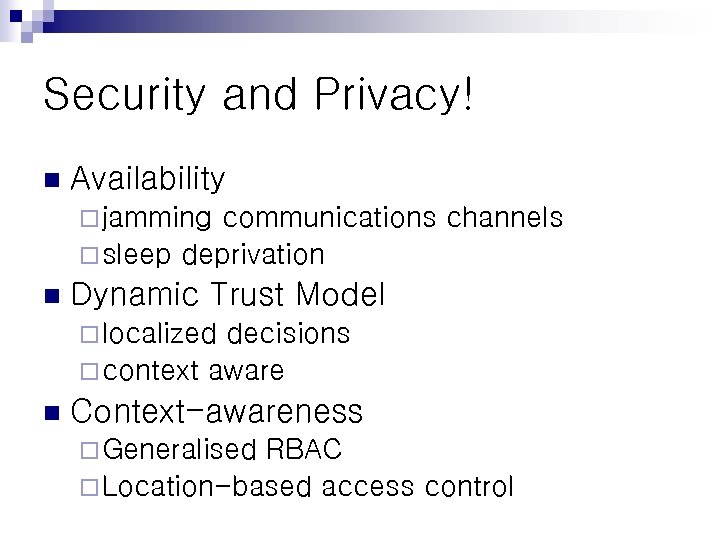
Security and Privacy! n Availability ¨ jamming communications channels ¨ sleep deprivation n Dynamic Trust Model ¨ localized decisions ¨ context aware n Context-awareness ¨ Generalised RBAC ¨ Location-based access control
Security and Privacy! n Security policies ¨ prevent formation of “evidence”: forming a link between contexts, objects, users and objectives. ¨ e. g. number, “credit card”, “foo bar”, credit limit n Location information privacy ¨ One of the burning issues

Authentication and Access Control
Authentication n n Ambient intelligent environments : roaming digital entities, most likely presence of strangers Collaboration with most likely unknown entities: enrolment needed for authentication is missing Identity in absolute terms is less meaningful than recognition of previous interaction to choose whether to collaborate or not New requirements lead to new schemes, e. g. the Resurrecting Duckling security model [Stajano. Anderson 1999] Any identifier can work as long as it allows for referencing the entity involved
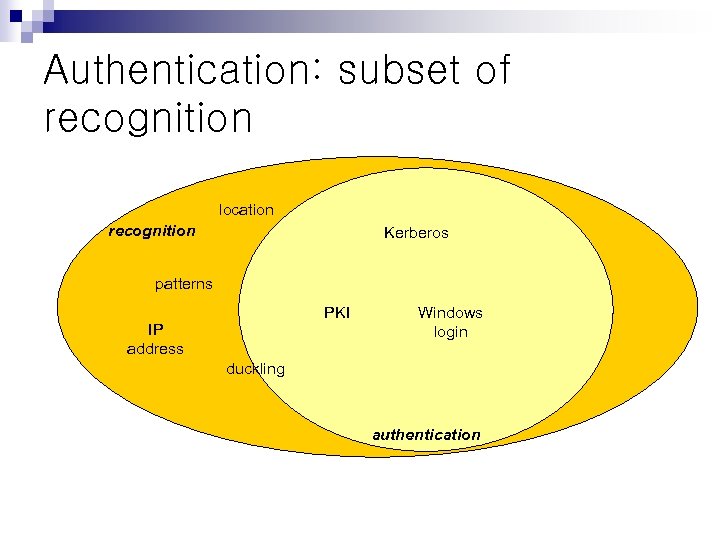
Authentication: subset of recognition location recognition Kerberos patterns PKI IP address Windows login duckling authentication
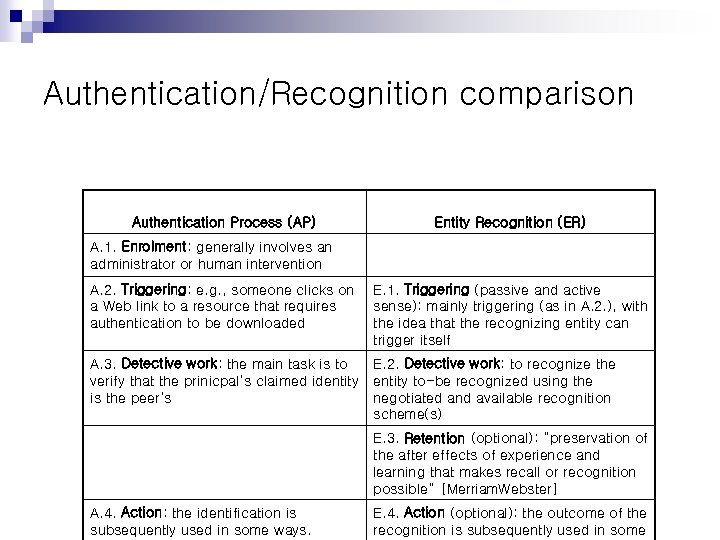
Authentication/Recognition comparison Authentication Process (AP) Entity Recognition (ER) A. 1. Enrolment: generally involves an administrator or human intervention A. 2. Triggering: e. g. , someone clicks on a Web link to a resource that requires authentication to be downloaded E. 1. Triggering (passive and active sense): mainly triggering (as in A. 2. ), with the idea that the recognizing entity can trigger itself A. 3. Detective work: the main task is to verify that the prinicpal’s claimed identity is the peer’s E. 2. Detective work: to recognize the entity to-be recognized using the negotiated and available recognition scheme(s) E. 3. Retention (optional): “preservation of the after effects of experience and learning that makes recall or recognition possible” [Merriam. Webster] A. 4. Action: the identification is subsequently used in some ways. E. 4. Action (optional): the outcome of the recognition is subsequently used in some
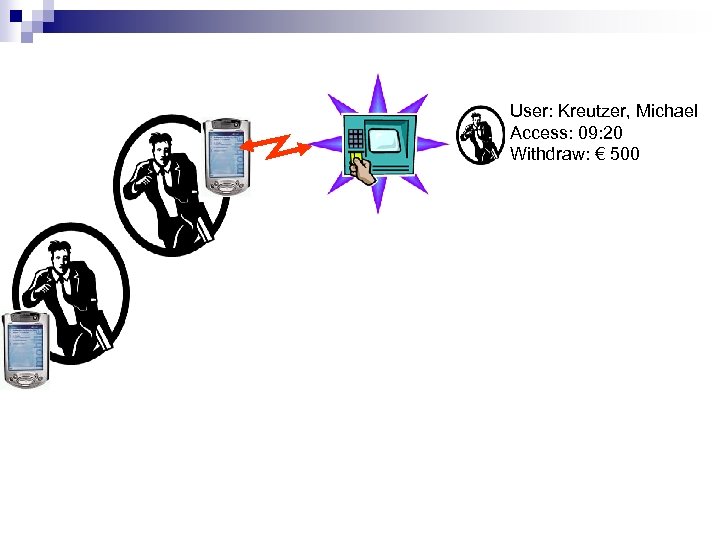
User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500
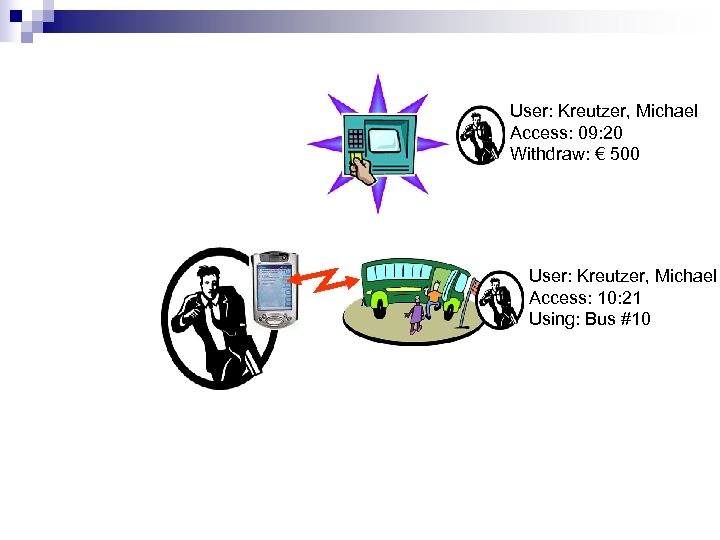
User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500 User: Kreutzer, Michael Access: 10: 21 Using: Bus #10
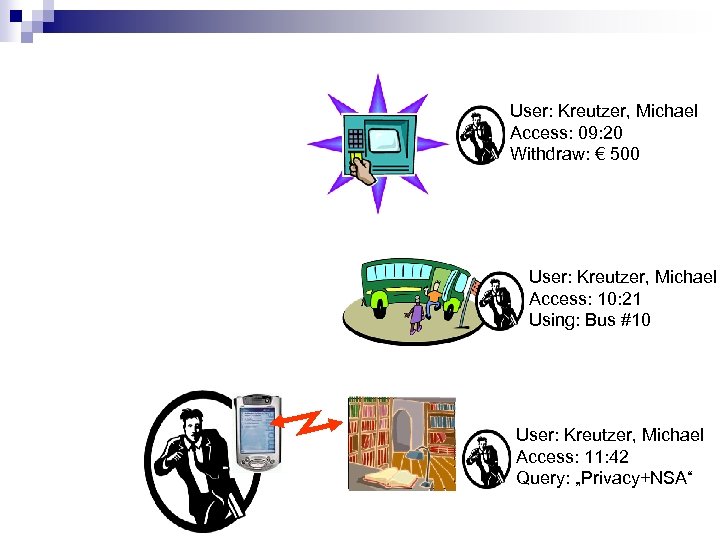
User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500 User: Kreutzer, Michael Access: 10: 21 Using: Bus #10 User: Kreutzer, Michael Access: 11: 42 Query: „Privacy+NSA“
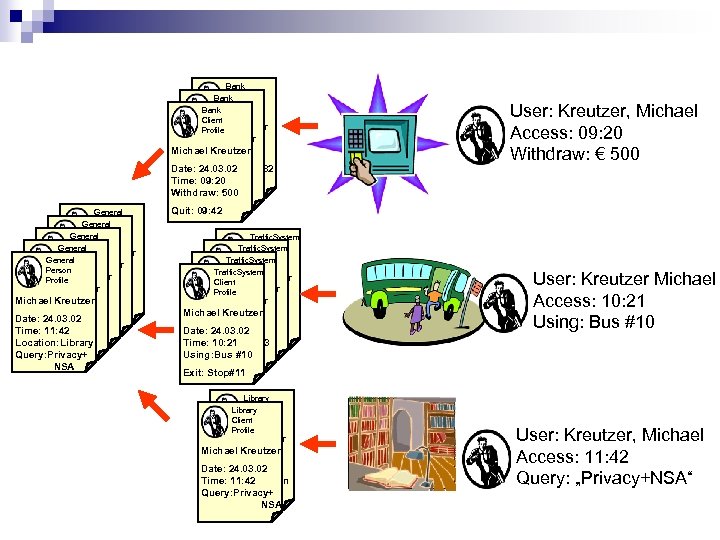
Bank Client Bank Profile Client Bruce Schneier Profile General Person General Profile Person General Bruce Schneier Profile 24. 03. 02 Person Date: Bruce Schneier Profile 24. 03. 02 Date: Time: 11: 42 Bruce Schneier Date: Location: Bus Time: 11: 42 24. 03. 02 Michael Kreutzer Date: Location: Bus Time: 11: 42 24. 03. 02 Exit: Stop#11 Time: 11: 42 Location: Bus Exit: Stop#11 Location: Library Exit: Stop#11 Query: Privacy+ NSA Bruce Schneier Date: 24. 03. 02 Michael Kreutzer Date: 24. 03. 02 Time: 09: 20 Date: Withdraw: 10032 Time: 09: 20 24. 03. 02 Time: 09: 20 100 Withdraw: Quit: 09: 42 Withdraw: 500 Quit: 09: 42 Traffic. System Client Traffic. System Profile Client Traffic. System Bruce Schneier Profile Client Bruce Schneier Profile Date: 24. 03. 02 Bruce Schneier Date: 24. 03. 02 Time: 10: 21 Michael Kreutzer Time: 10: 21 Date: Using: Bus #10 24. 03. 02 Time: 10: 21 Exit: Stop#11 Time: 10: 21 #103 Using: Bus Exit: Stop#11 Using: Bus #10 Exit: Stop#11 Library Client Library Profile Client Profile Bruce Schneier Michael Kreutzer Date: 24. 03. 02 Time: 11: 42 Query: Location Query: Privacy+ NSA User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500 User: Kreutzer Michael Access: 10: 21 Using: Bus #10 User: Kreutzer, Michael Access: 11: 42 Query: „Privacy+NSA“
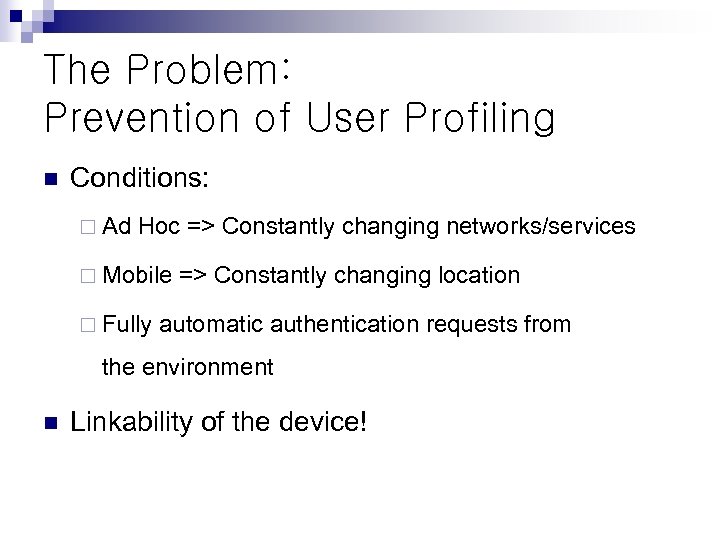
The Problem: Prevention of User Profiling n Conditions: ¨ Ad Hoc => Constantly changing networks/services ¨ Mobile ¨ Fully => Constantly changing location automatic authentication requests from the environment n Linkability of the device!
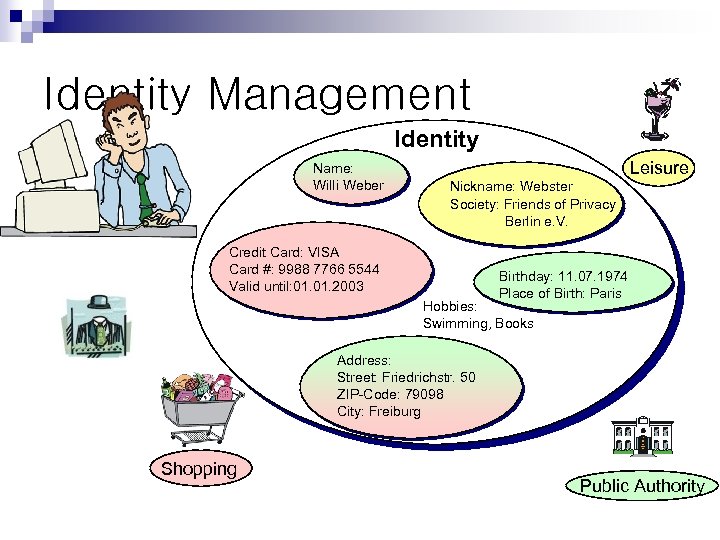
Identity Management Identity Name: Willi Weber Willi Webster Leisure Nickname: Webster Society: Friends of Privacy Berlin e. V. Credit Card: VISA Card #: 9988 7766 5544 Valid until: 01. 2003 Birthday: 11. 07. 1974 Place of Birth: Paris Hobbies: Swimming, Books Address: Street: Friedrichstr. 50 ZIP-Code: 79098 City: Freiburg Anonymous Shopping Public Authority
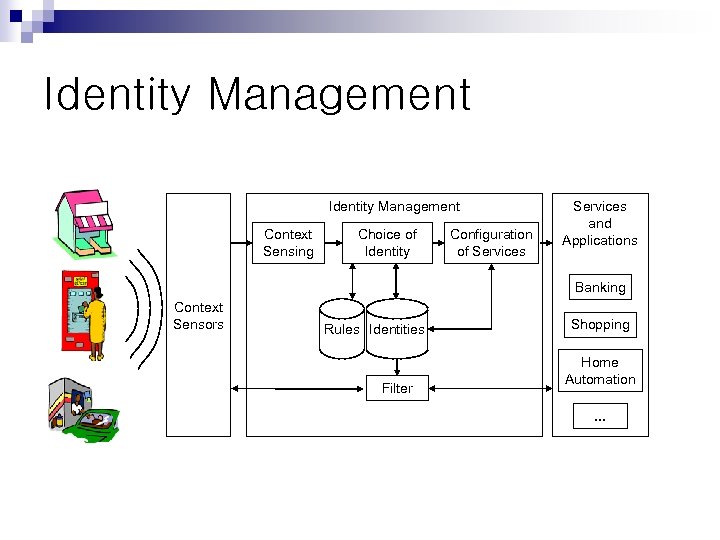
Identity Management Context Sensing Choice of Identity Configuration of Services and Applications Banking Context Sensors Rules Identities Filter Shopping Home Automation. . .
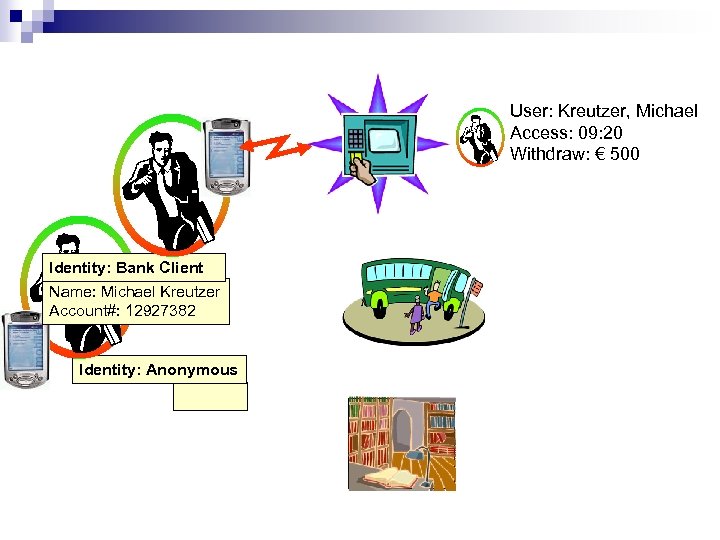
User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500 Identity: Bank Client Name: Michael Kreutzer Account#: 12927382 Identity: Anonymous
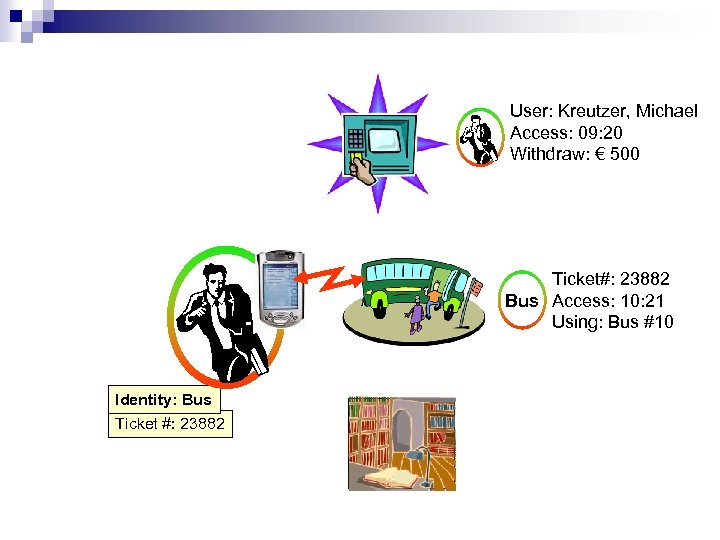
User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500 Ticket#: 23882 Bus Access: 10: 21 Using: Bus #10 Identity: Bus Ticket #: 23882
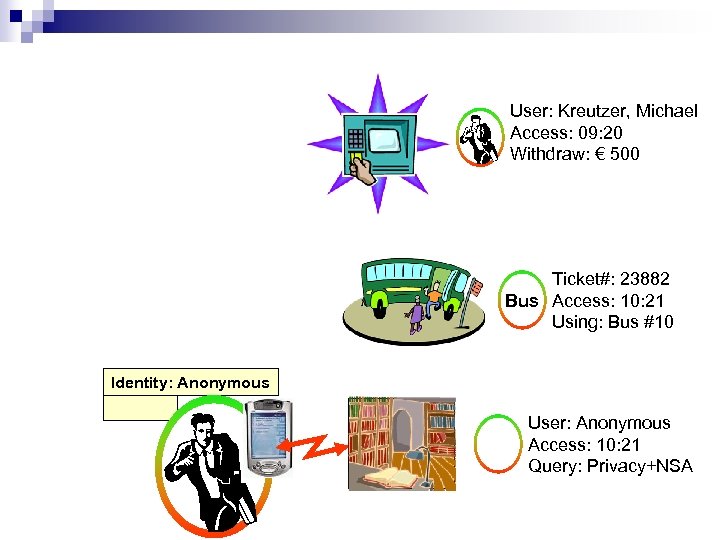
User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500 Ticket#: 23882 Bus Access: 10: 21 Using: Bus #10 Identity: Anonymous User: Anonymous Access: 10: 21 Query: Privacy+NSA
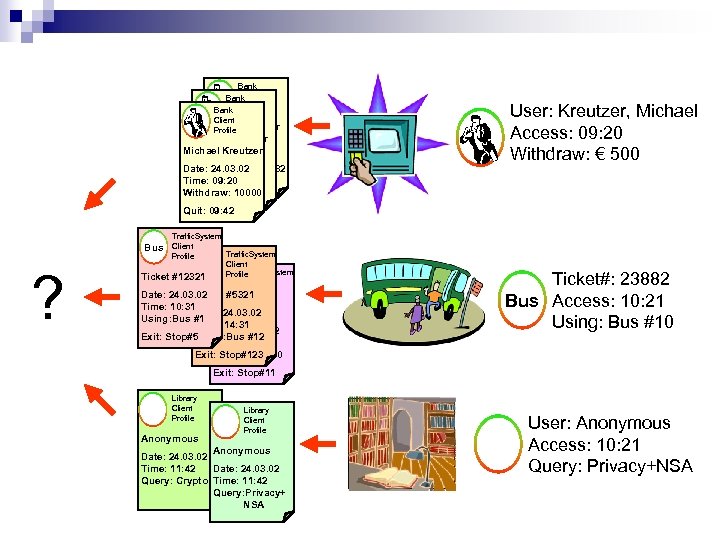
Bank Client Bank Profile Client Bruce Schneier Profile Bruce Schneier Date: 24. 03. 02 Michael Kreutzer Date: 24. 03. 02 Time: 09: 20 Date: Withdraw: 10032 24. 03. 02 Time: 09: 20 100 Withdraw: Quit: 09: 42 Withdraw: 10000 Quit: 09: 42 Traffic. System Client Traffic. System Profile Bus Client Traffic. System Profile Ticket #12321 Bus Client Profile Date: 24. 03. 02 Ticket #5321 User: Kreutzer, Michael Access: 09: 20 Withdraw: € 500 Bus ? Time: 10: 31 Date: 24. 03. 02 Ticket #23882 Using: Bus #1 Time: 14: 31 Date: 24. 03. 02 Exit: Stop#5 Using: Bus #12 Time: 10: 21 Exit: Stop#123 #10 Using: Bus Ticket#: 23882 Bus Access: 10: 21 Using: Bus #10 Exit: Stop#11 Library Client Profile Anonymous Date: 24. 03. 02 Time: 11: 42 Query: Crypto Time: 11: 42 Query: Privacy+ NSA User: Anonymous Access: 10: 21 Query: Privacy+NSA
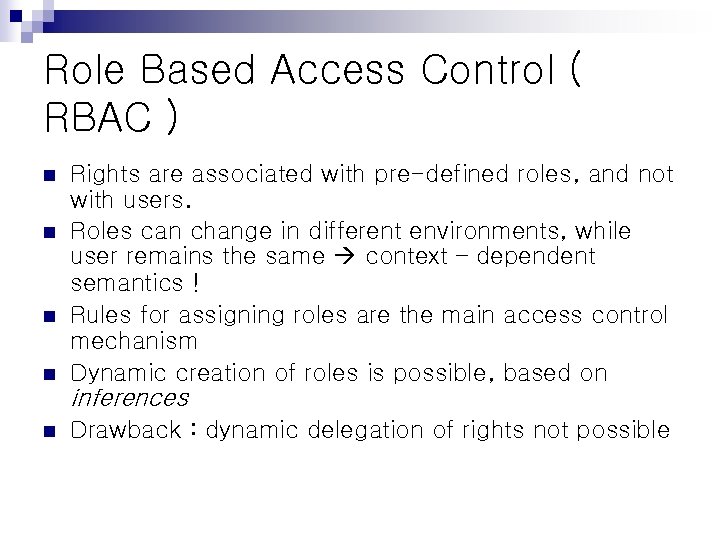
Role Based Access Control ( RBAC ) n n Rights are associated with pre-defined roles, and not with users. Roles can change in different environments, while user remains the same context – dependent semantics ! Rules for assigning roles are the main access control mechanism Dynamic creation of roles is possible, based on inferences n Drawback : dynamic delegation of rights not possible
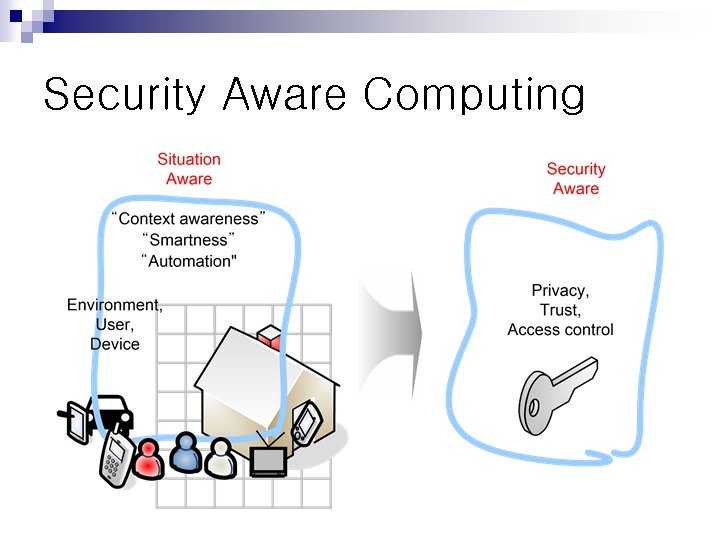
Security Aware Computing
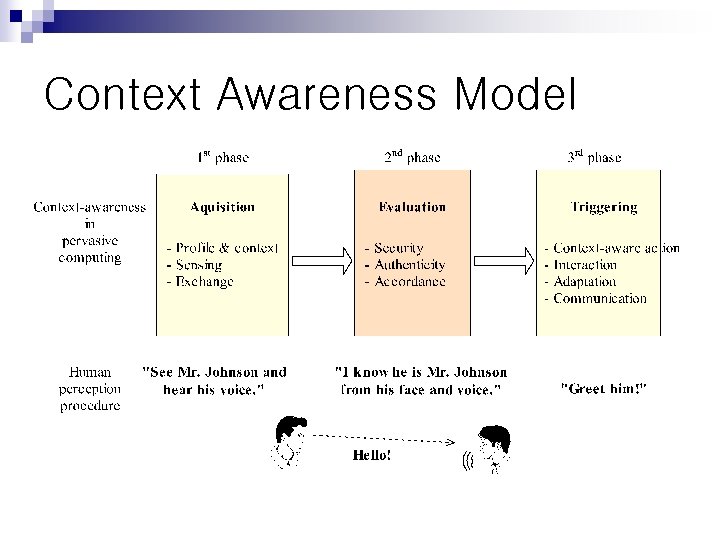
Context Awareness Model
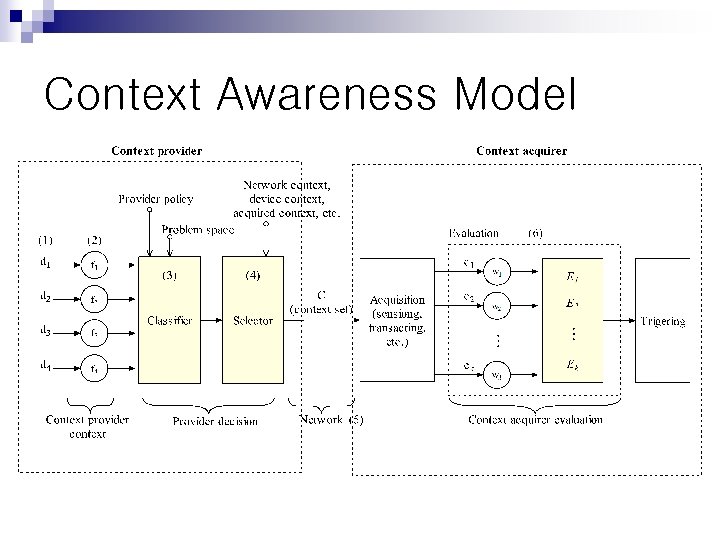
Context Awareness Model
Security vs. HCI n How does Security affect the userfriendliness of Ubi. Comp? n Can security be achieved without explicit interaction?

RFID Security
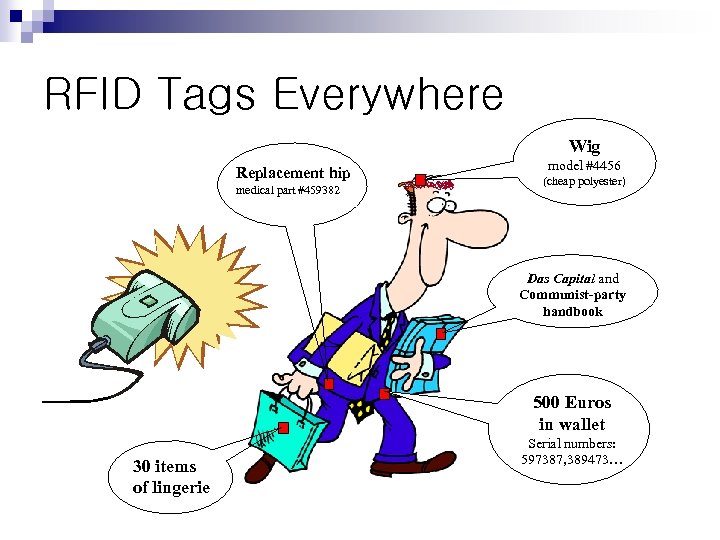
RFID Tags Everywhere Wig Replacement hip medical part #459382 model #4456 (cheap polyester) Das Capital and Communist-party handbook 500 Euros in wallet 30 items of lingerie Serial numbers: 597387, 389473…
Simple Approaches to Privacy Method 1: Place RFID-tags in protective mesh or foil Problem: makes locomotion difficult… perhaps useful for wallets
Simple Approaches to Privacy Method 2: “Kill” RFID tags Problem: RFID tags are much too useful…
One Example n European Central Bank has announced plans to implant RFID tags in banknotes by 2005 • Uses? – Anti-counterfeiting – Tracking of illicit monetary flows
Privacy Infringement n More efficient mugging “Just in case you want to know, she’s carrying 700 Euro…” • Fairly easy tracking of people and transactions by anyone! • Law-enforcement snooping capabilities made freely available
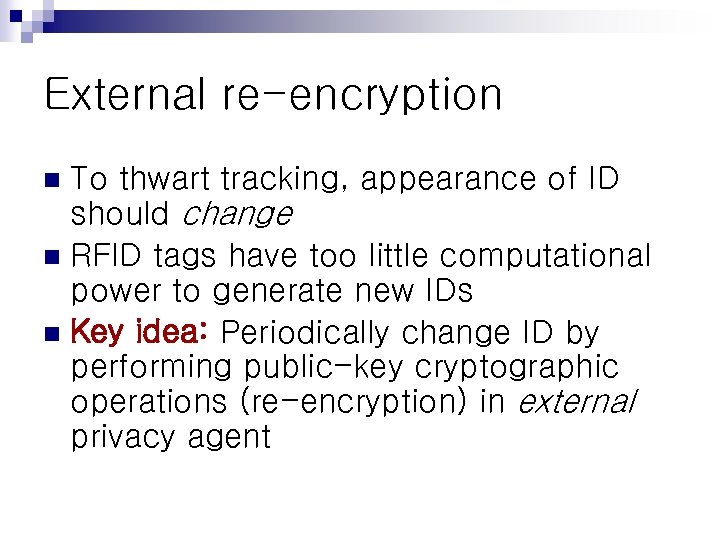
External re-encryption To thwart tracking, appearance of ID should change n RFID tags have too little computational power to generate new IDs n Key idea: Periodically change ID by performing public-key cryptographic operations (re-encryption) in external privacy agent n
![Cryptography performed by external privacy agent (e. g. , reader) E[ID] Cryptography performed by external privacy agent (e. g. , reader) E[ID]](https://present5.com/presentation/dfa1822fd34cdb4d844ff6a500105975/image-48.jpg)
Cryptography performed by external privacy agent (e. g. , reader) E[ID]
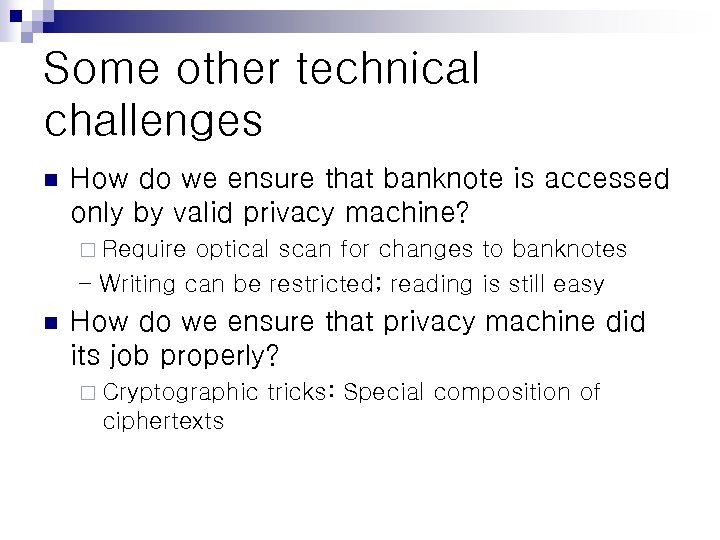
Some other technical challenges n How do we ensure that banknote is accessed only by valid privacy machine? ¨ Require optical scan for changes to banknotes – Writing can be restricted; reading is still easy n How do we ensure that privacy machine did its job properly? ¨ Cryptographic ciphertexts tricks: Special composition of
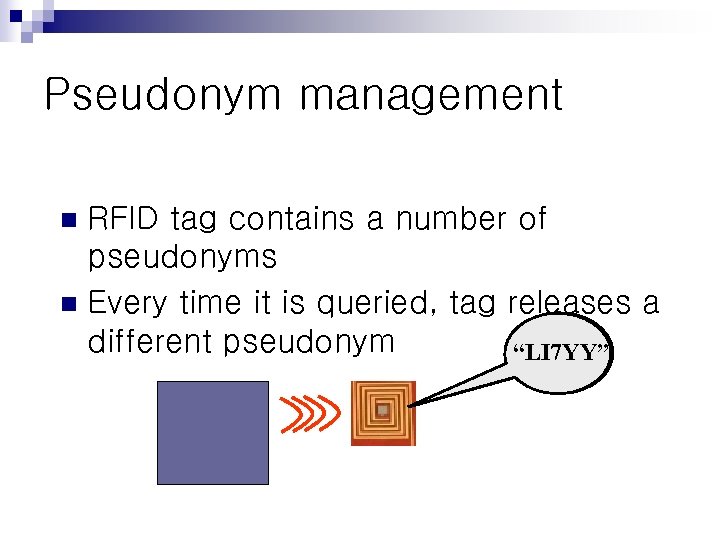
Pseudonym management RFID tag contains a number of pseudonyms n Every time it is queried, tag releases a different pseudonym “ 74 AB 8” “ 9 JHHS” “LI 7 YY” n
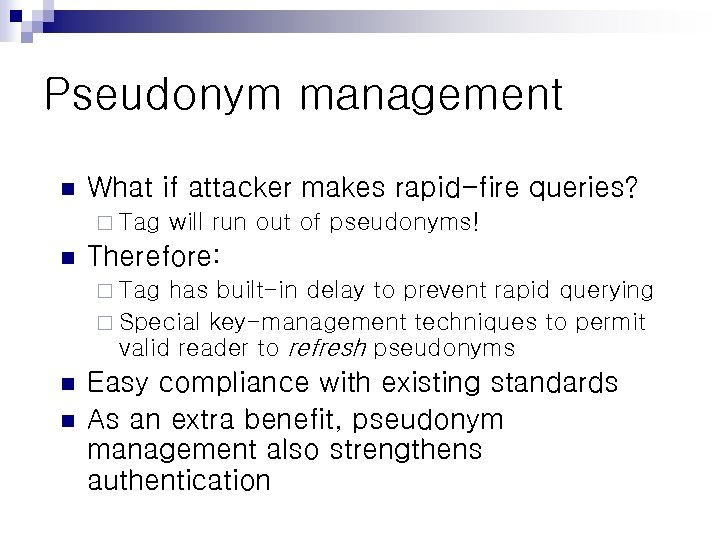
Pseudonym management n What if attacker makes rapid-fire queries? ¨ Tag n will run out of pseudonyms! Therefore: ¨ Tag has built-in delay to prevent rapid querying ¨ Special key-management techniques to permit valid reader to refresh pseudonyms n n Easy compliance with existing standards As an extra benefit, pseudonym management also strengthens authentication

Blocker Tag
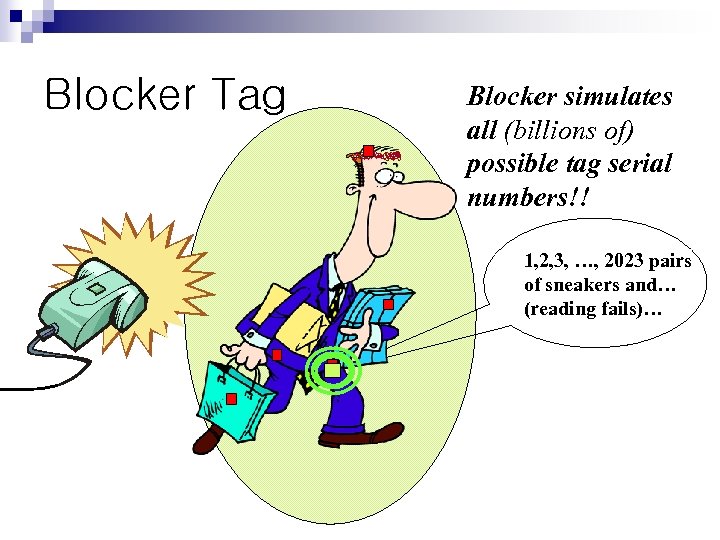
Blocker Tag Blocker simulates all (billions of) possible tag serial numbers!! 1, 2, 3, …, 2023 pairs of sneakers and… (reading fails)…
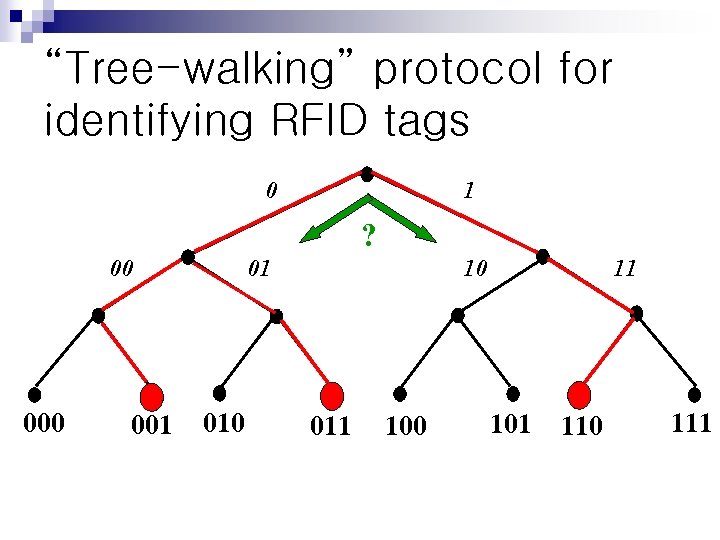
“Tree-walking” protocol for identifying RFID tags 0 1 ? 00 001 01 010 10 011 100 11 101 110 111
In a nutshell n “Tree-walking” protocol for identifying tags recursively asks questions: ¨ “Is there a tag whose next bit is a ‘ 1’? ¨ “Is there a tag whose next bit is a ‘ 0’? n Blocker tag always says yes to both questions it seem like all tags are present ¨ Thus reader cannot figure out which tags are actually present ¨ Number of possible tags is huge (at least a billion), so reader stalls ¨ Makes

Two bottles of Merlot #458790 Blocker tag system should protect privacy but still avoid blocking unpurchased items
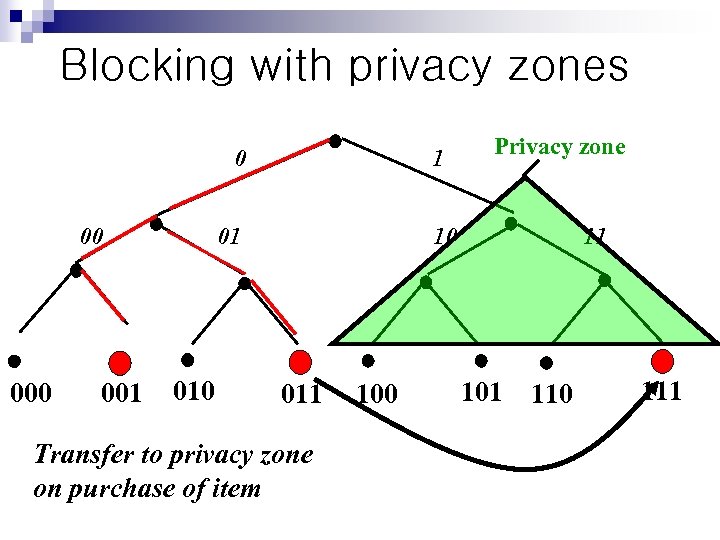
Blocking with privacy zones 0 00 001 1 01 010 Privacy zone 10 011 Transfer to privacy zone on purchase of item 100 11 101 110 111
More about blocker tags n Blocker tag can be cheap ¨ Essentially just a “yes” tag and “no” tag with a little extra logic ¨ Can be embedded in shopping bags, etc. n With multiple privacy zones, sophisticated, e. g. , graduated policies are possible

MANET Security
Mobile Ad-Hoc Networks n n n Collection of wireless mobile hosts forming a temporary network No fixed network infrastructure No (or limited) organization Military and Emergency Sensor Networks Civilian applications, ubiquitous computing
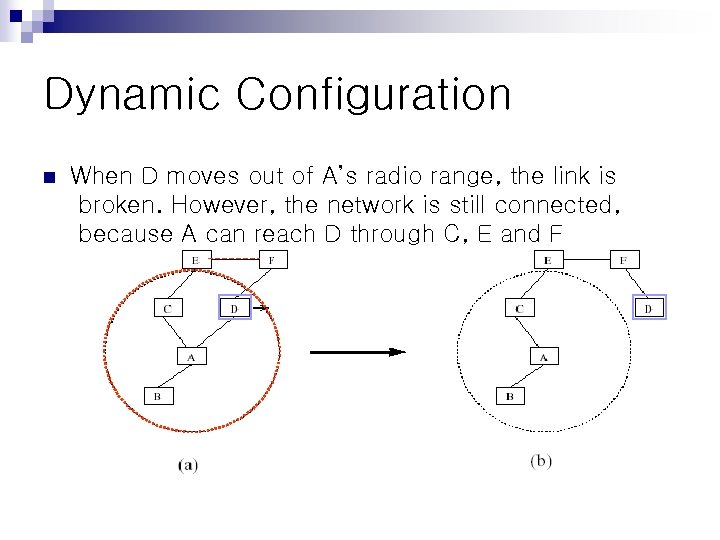
Dynamic Configuration n When D moves out of A’s radio range, the link is broken. However, the network is still connected, because A can reach D through C, E and F
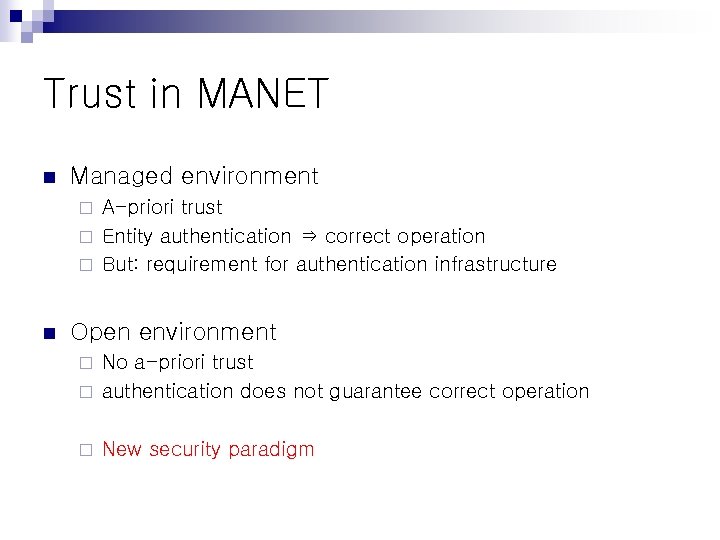
Trust in MANET n Managed environment A-priori trust ¨ Entity authentication ⇒ correct operation ¨ But: requirement for authentication infrastructure ¨ n Open environment No a-priori trust ¨ authentication does not guarantee correct operation ¨ ¨ New security paradigm
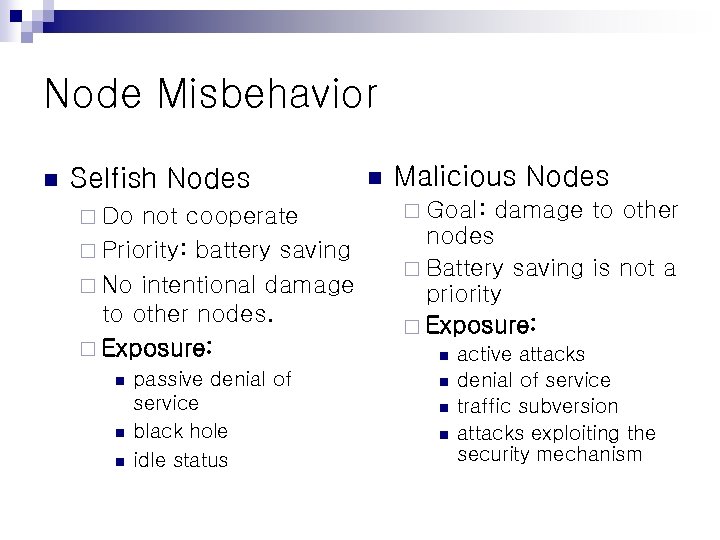
Node Misbehavior n Selfish Nodes ¨ Do not cooperate ¨ Priority: battery saving ¨ No intentional damage to other nodes. ¨ Exposure: n n n passive denial of service black hole idle status n Malicious Nodes ¨ Goal: damage to other nodes ¨ Battery saving is not a priority ¨ Exposure: n n active attacks denial of service traffic subversion attacks exploiting the security mechanism
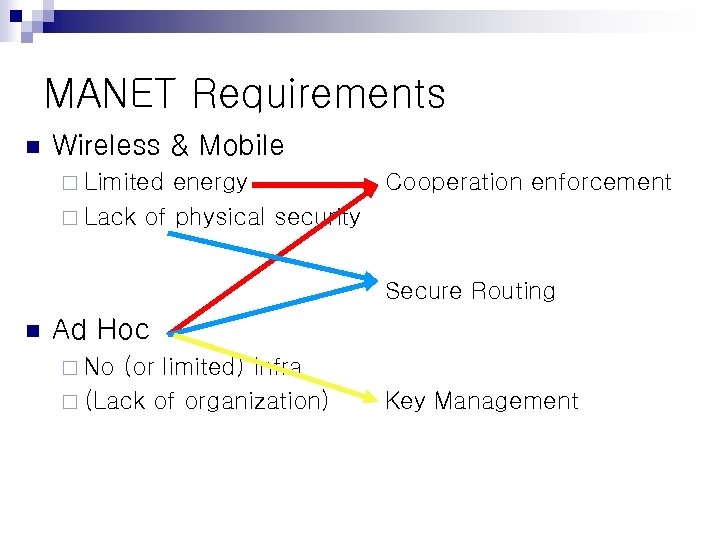
MANET Requirements n Wireless & Mobile ¨ Limited energy ¨ Lack of physical security Cooperation enforcement Secure Routing n Ad Hoc ¨ No (or limited) Infra ¨ (Lack of organization) Key Management
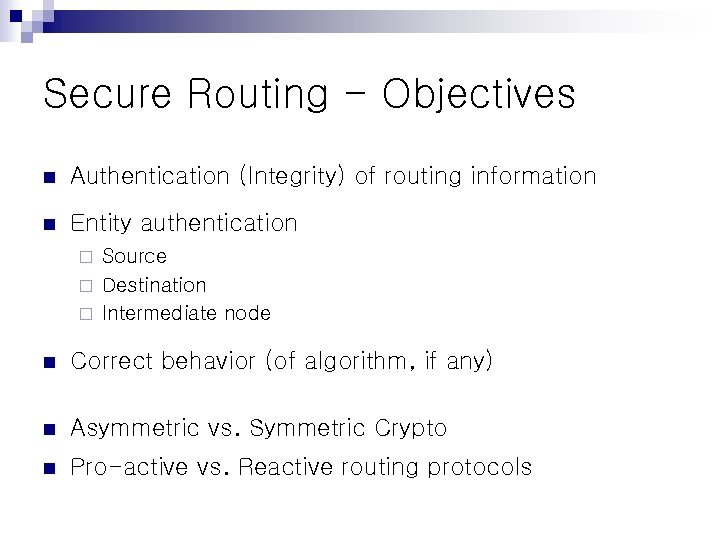
Secure Routing - Objectives n Authentication (Integrity) of routing information n Entity authentication Source ¨ Destination ¨ Intermediate node ¨ n Correct behavior (of algorithm, if any) n Asymmetric vs. Symmetric Crypto n Pro-active vs. Reactive routing protocols
Sensor Network? n Sensor An electronic device used to measure a physical quantity such as temperature, pressure or loudness and convert it into an electronic signal of some kind (e. g a voltage). ¨ A device that produces a measurable response to a change in a physical condition such as temperature or to a chemical condition such as concentration ¨ n Sensor Network Technical Challenges Energy constraints ¨ Level of dynamics (obstacles, weather, terrain, large number of nodes, failures, captures. ) ¨ Scaling challenges ¨
Current Applications n n n monitor factory instrumentation, pollution levels freeway traffic the structural integrity of buildings Other applications ¨ climate sensing ¨ control in office buildings ¨ home environmental sensing systems for temperature, light, moisture, and motion.
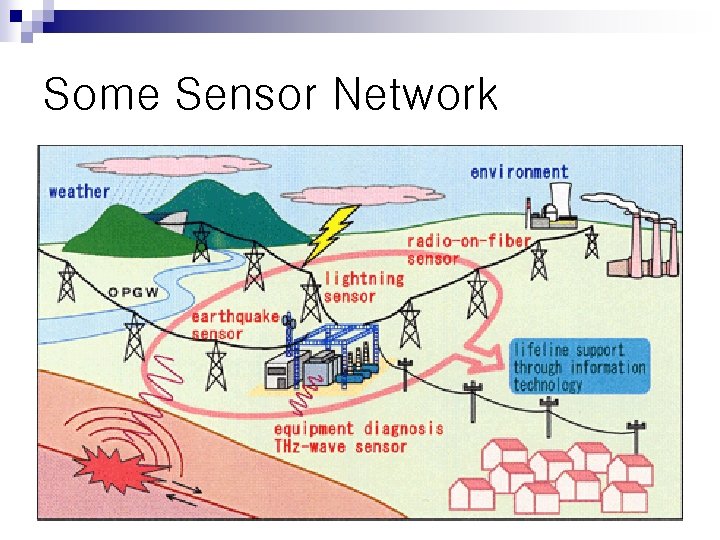
Some Sensor Network
Sensor Network Limitations n n n No PKC! Node capture Lack of a-priori knowledge of postdeployment configuration (Airplane) Limited memory resources Limited bandwidth and transmission power Over-reliance on base stations exposes vulnerability
Sensor Nodes Compromise n Why compromise? ¨ Each node: a potential point of attack n impractical to monitor and protect each individual sensor Dispersed over a large area ¨ Attackers obtain own commodity sensor nodes ¨ Attacker can claim multiple identities for an altered node. ¨ n Consequence of compromise? falsification of sensor data ¨ extraction of private sensed information from sensor network readings ¨ denial of service ¨ n Tamper-resistant: too expensive
Eavesdropping n Wireless = insecurity ¨ n n a few wireless receivers outside a house might be able to monitor light and temperature readings of sensor networks inside the house Encryption Good! Using which key? Requirement for key management maintain secrecy even when an adversary compromises a few sensor nodes ¨ Ideally, revocation of known exposed keys and rekey ¨ end-to-end encryption impractical ¨ n hop-by-hop encryption: each sensor node stores only encryption keys shared with its immediate neighbors.
Privacy n n Adversaries can use data to derive sensitive info if they know how to correlate multiple sensor inputs. More serious problem ¨ n they make large volumes of information easily available through remote access. (on purpose also) A Step toward Ensuring that sensed information stays within the sensor network, accessible only to trusted parties ¨ restrict the network’s ability to gather data at a detail level that could compromise privacy ¨ n n Database inference problem Privacy preserving data mining
Do. S n Defending against Do. S is extremely difficult Can occur at the physical layer, via radio jamming. ¨ malicious transmissions into the network to interfere with sensor network protocols ¨ Attackers can induce battery exhaustion: by sending a useless communications that the target will expend energy processing and may also forward to other nodes ¨ create routing loops that will eventually exhaust all nodes ¨ n Message authentication based on PKC highly computationally intensive ¨ attackers that can induce a large number of these can mount an effective energy-exhaustion attack. ¨

Database Security
Database Security n Issues ¨ Inference n occurs when users are able to piece together information at one security level to determine a fact that should be protected at a higher security level ¨ Access control ¨ Encrypted computation
Searches on Encrypted Data n Examples ¨ Mail Server n Fully trusted, i. e. sys admin can read my e-mail n Can build secure storage ¨ But need to sacrifice functionality ¨ Moving the computation to the data storage seems to be very difficult ¨ For example, how to search encrypted data?
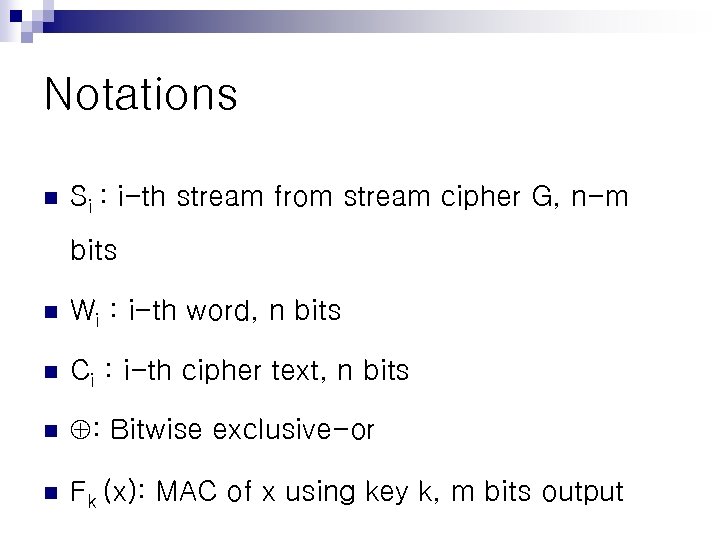
Notations n Si : i-th stream from stream cipher G, n-m bits n Wi : i-th word, n bits n Ci : i-th cipher text, n bits n : Bitwise exclusive-or n Fk (x): MAC of x using key k, m bits output
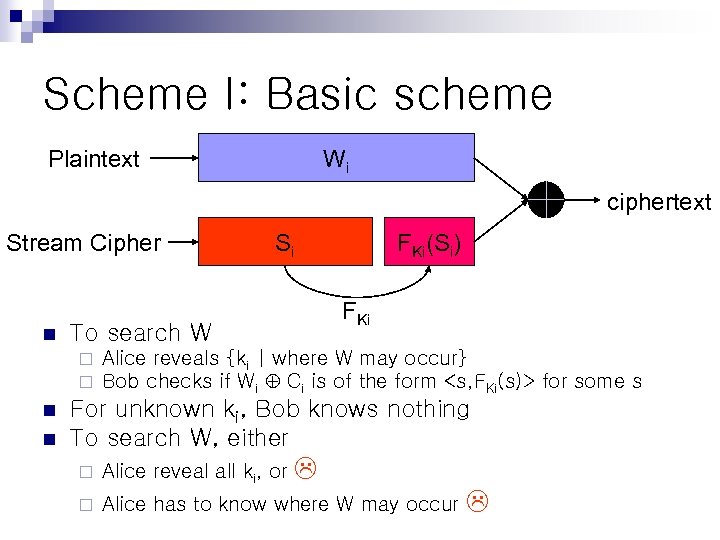
Scheme I: Basic scheme Wi Plaintext ciphertext Stream Cipher n n FKi(Si) FKi To search W ¨ ¨ n Si Alice reveals {ki | where W may occur} Bob checks if Wi Ci is of the form <s, FKi(s)> for some s For unknown ki, Bob knows nothing To search W, either ¨ Alice reveal all ki, or ¨ Alice has to know where W may occur
Scheme II: Controlled search n Replace ki = f k’ . (Wi) where k’ is secret, never revealed ¨ f is another MAC with output size = | ki | ¨ n Reveal only f n Bob identifies only location where W occurs n But reveals nothing on the locations i where W != Wi n Still does not support hidden search k’ (W) and W
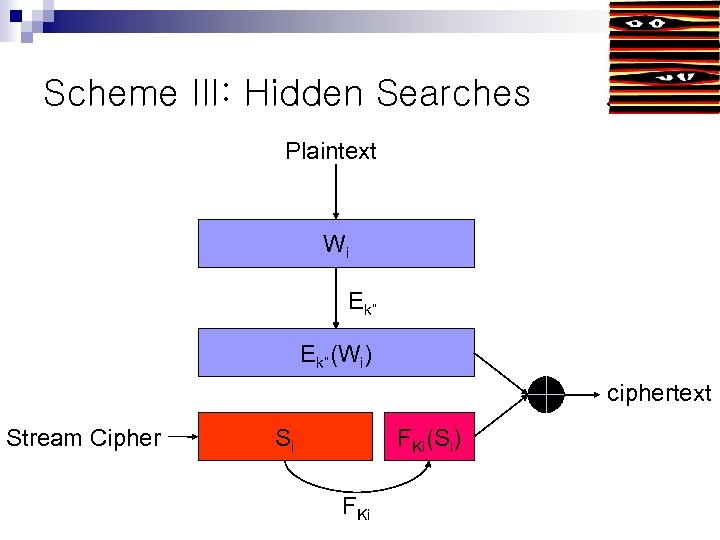
Scheme III: Hidden Searches . Plaintext Wi Ek”(Wi) ciphertext Stream Cipher Si FKi(Si) FKi
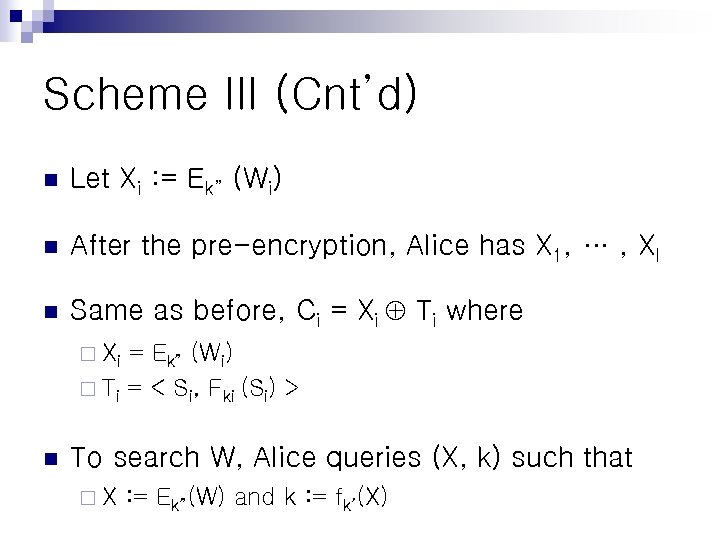
Scheme III (Cnt’d) n Let Xi : = Ek” (Wi) n After the pre-encryption, Alice has X 1, … , Xl n Same as before, Ci = Xi Ti where ¨ Xi = Ek” (Wi) ¨ Ti = < Si, Fki (Si) > n To search W, Alice queries (X, k) such that ¨X : = Ek”(W) and k : = fk’(X)
A problem of Scheme III n Scheme III has a problem… Guess what? n If Alice generates ki = fk’(Ek”(Wi)), she cannot recover the plaintext from the ciphertext. = Xi Ti where Ti = < Si, Fki (Si) > ¨ To compute Xi from Ci, we have to know Ti ¨ Si can be computed easily ¨ How about Fki (Si)? ¨ The problem is ki ¨ Ci n n To compute this, we have to know all Ek”(Wi) for all i Ups! If you know all of these, why do you need search?
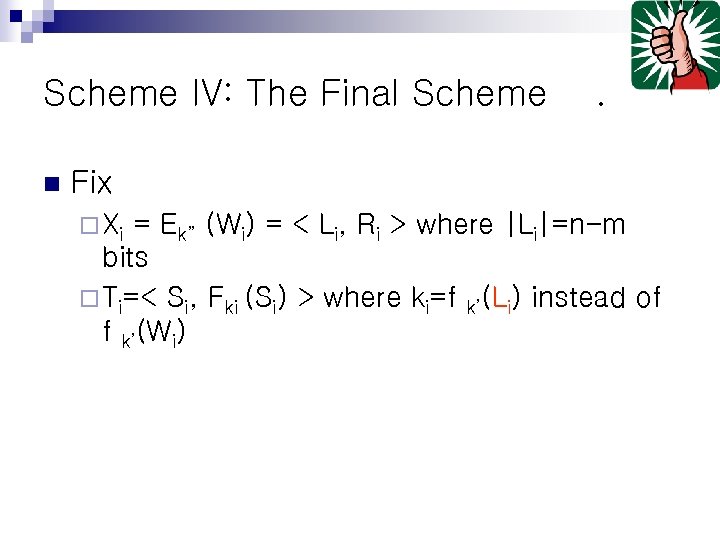
Scheme IV: The Final Scheme n . Fix ¨ Xi = Ek” (Wi) = < Li, Ri > where |Li|=n-m bits ¨ Ti=< Si, Fki (Si) > where ki=f k’(Li) instead of f k’(Wi)
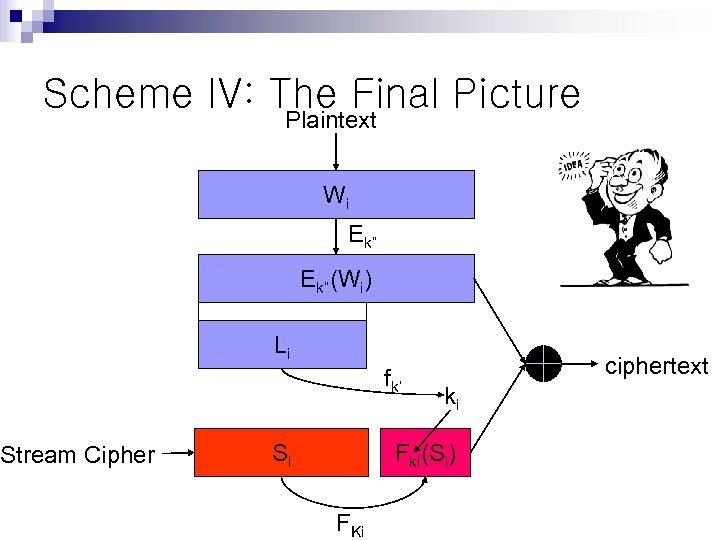
Scheme IV: The Final Picture Stream Cipher Plaintext Wi Ek”(Wi) Li fk’ Si ciphertext ki Fki(Si) FKi
Terms Revisited n n n n n Ubiquity - Who has access to my resources and services? Issues for confidentiality, authorization, and access control. Augmented Reality – How do we augment our risk management strategies to match augmented reality? Furthermore, can we exploit augmented reality in risk management? Context Awareness - Who else knows where I am and what’s going on around me? Matters for privacy and controlled information access including and beyond location. Invisible Computer - Who am I interacting with and when? Defining suitable authentication and trust frameworks for ubiquitous computing. Smart Items - But they’re so small, can they protect themselves and who owns these things anyway? Analysis and classification of existing micro crypto-algorithms, as well as issues surrounding ownership, accountability, and non-repudiation. Mobility and Portability – What happens to “end-to-end” security? Charting of IT landscapes and architectures representative of ubiquitous computing, and specification of goals for security. Security versus the Disappearing Computer – How do we manage the tradeoffs presented here? How are the novel disappearing computer interaction substrates maintained when security is introduced? Management of Augmented Environments – Identification of the management issues for ubiquitous systems and proposals for tools and utilities. Social Awareness, Legislation and Education – Agreement on what message is to be delivered to society regarding security in ubiquitous computing environments, and how.
dfa1822fd34cdb4d844ff6a500105975.ppt